The Dark Side of Cybersecurity: NHS Scotland Domains and the Hidden Threats [2025]
In a world where digital presence defines operational efficiency, the recent compromise of NHS Scotland domains raises significant concerns. While the breach did not involve patient data, the exploitation of these domains to serve adult content and illegal sports streams highlights vulnerabilities that can no longer be ignored, as reported by The Register.
TL; DR
- NHS Scotland domains were found hosting adult content and illegal streams, reflecting cybersecurity gaps, according to TechRadar.
- Legacy systems are often targets due to outdated security measures, making them vulnerable to exploitation.
- Robust cybersecurity frameworks are essential to protect sensitive data and maintain trust.
- Regular audits and updates are critical to safeguarding digital assets.
- The incident serves as a wake-up call for public health systems globally to prioritize cybersecurity.

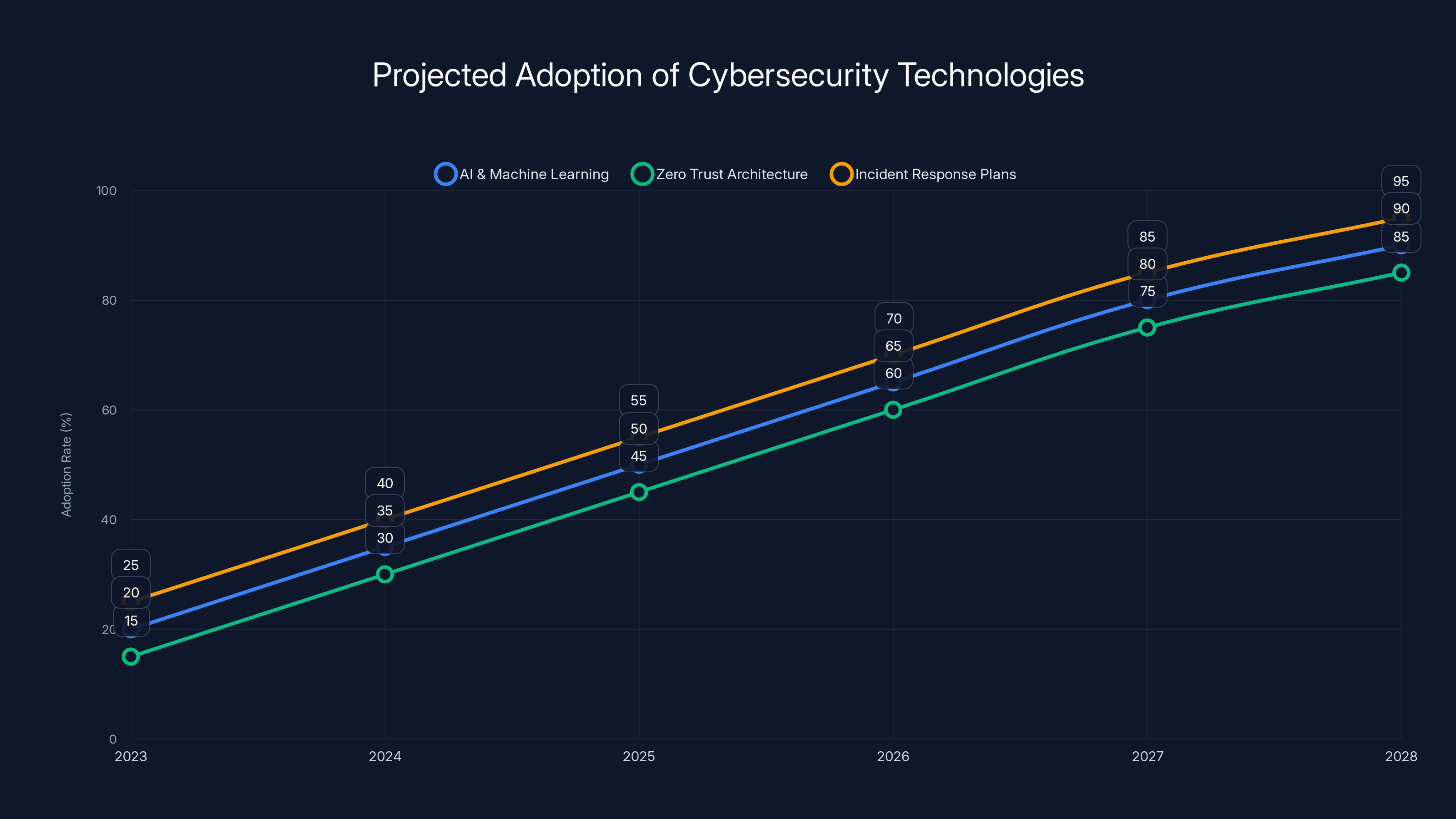
The adoption of AI, Zero Trust, and Incident Response Plans in cybersecurity is projected to significantly increase by 2028. (Estimated data)
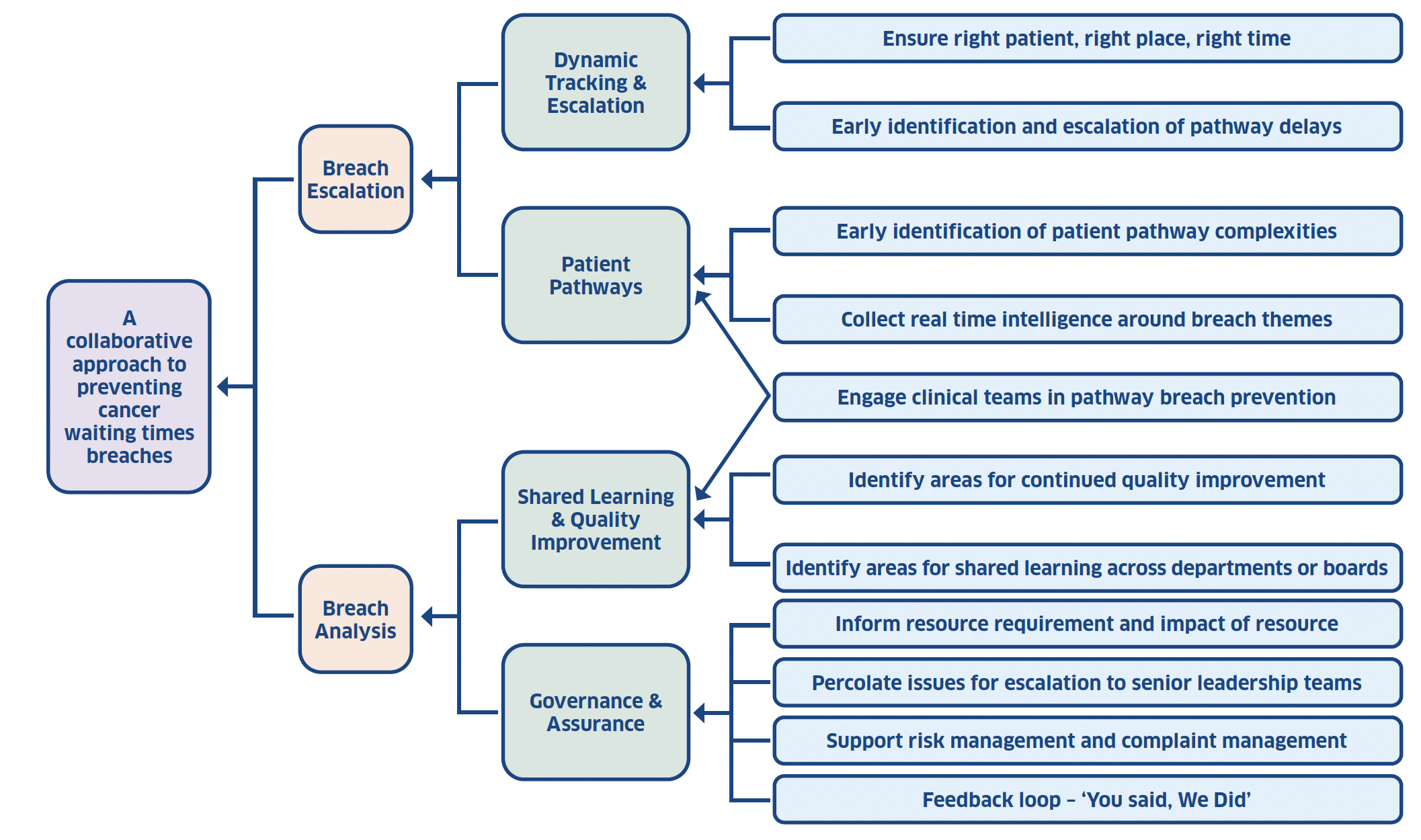
Understanding the Breach: What Happened?
The breach involved NHS Scotland domains, which were reportedly found serving unauthorized content such as adult material and illegal sports streams. This incident, while not involving patient data, points to a critical oversight in cybersecurity measures for legacy systems, as highlighted by Bisnis Update.
The Role of Legacy Systems
Legacy systems are often the backbone of many organizations, especially in the public sector. However, they can become a liability if not properly maintained. These systems are typically running on outdated software that is no longer supported by vendors, leaving them susceptible to exploitation, as discussed in Healthcare in Europe.
How Cybercriminals Exploit Vulnerabilities
Cybercriminals often target legacy systems due to their known vulnerabilities. These systems lack the latest security patches, making them easy targets for attackers looking to gain unauthorized access.
Common Tactics Include:
- SQL Injection: Manipulating database queries to execute unauthorized commands.
- Cross-Site Scripting (XSS): Injecting malicious scripts into web pages viewed by users.
- Phishing: Trick users into providing sensitive information through deceptive emails.
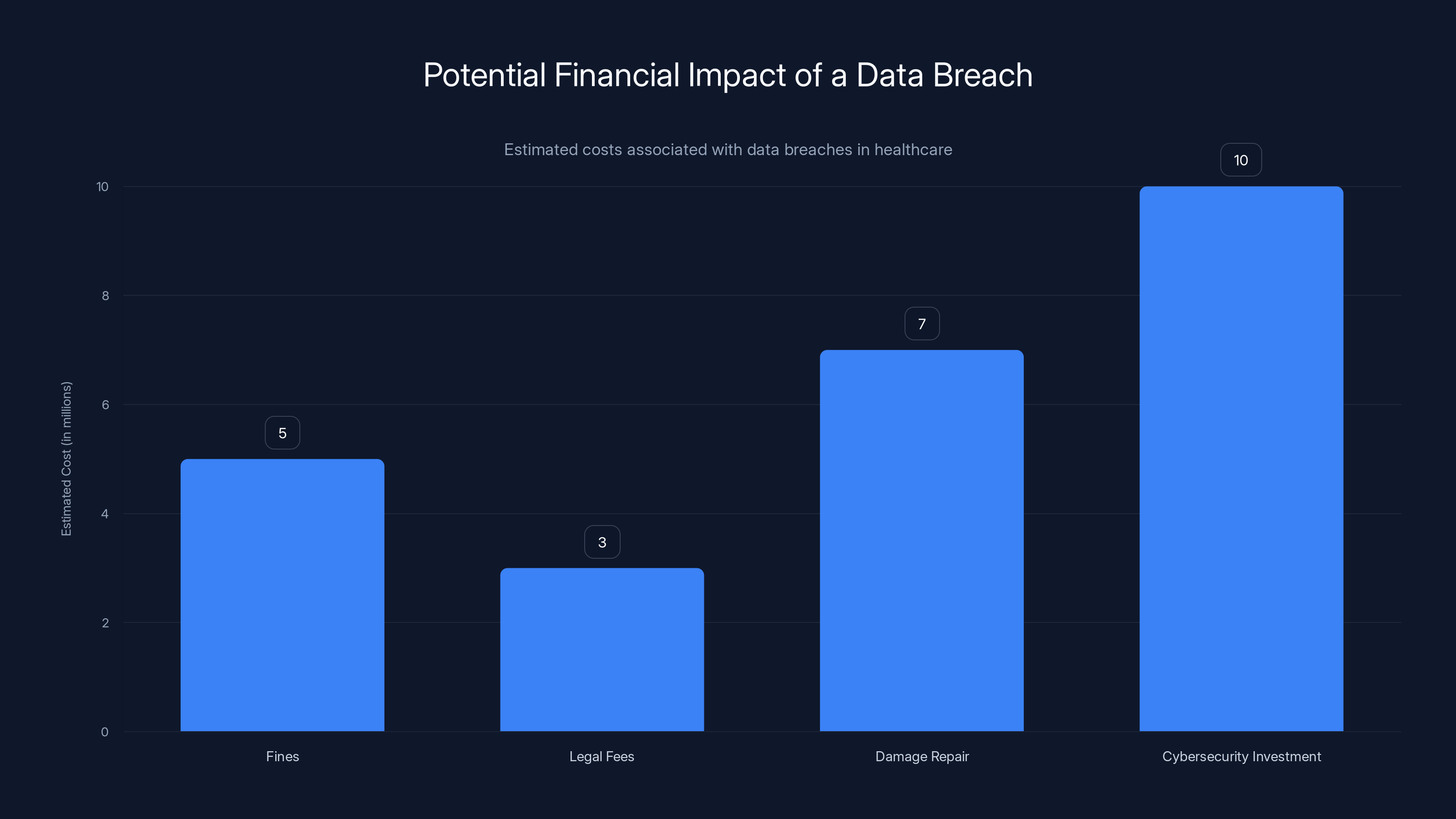
Estimated data shows that cybersecurity investments post-breach can be the highest cost, reaching up to $10 million.
The Implications of the Breach
While the NHS Scotland breach did not compromise patient data, the potential for such an outcome in future incidents cannot be overlooked. The incident highlights the importance of securing all aspects of an organization's digital infrastructure.
Risks to Public Trust
Public trust is paramount, especially in healthcare. Breaches can erode trust, leading to hesitancy in using digital services and reluctance to share information, as noted by Industrial Cyber.
Financial and Legal Consequences
The financial implications of a breach can be significant. Organizations may face fines, legal fees, and the costs associated with repairing the damage. Additionally, they may be required to invest more in cybersecurity measures post-incident, as reported by Fortune Business Insights.

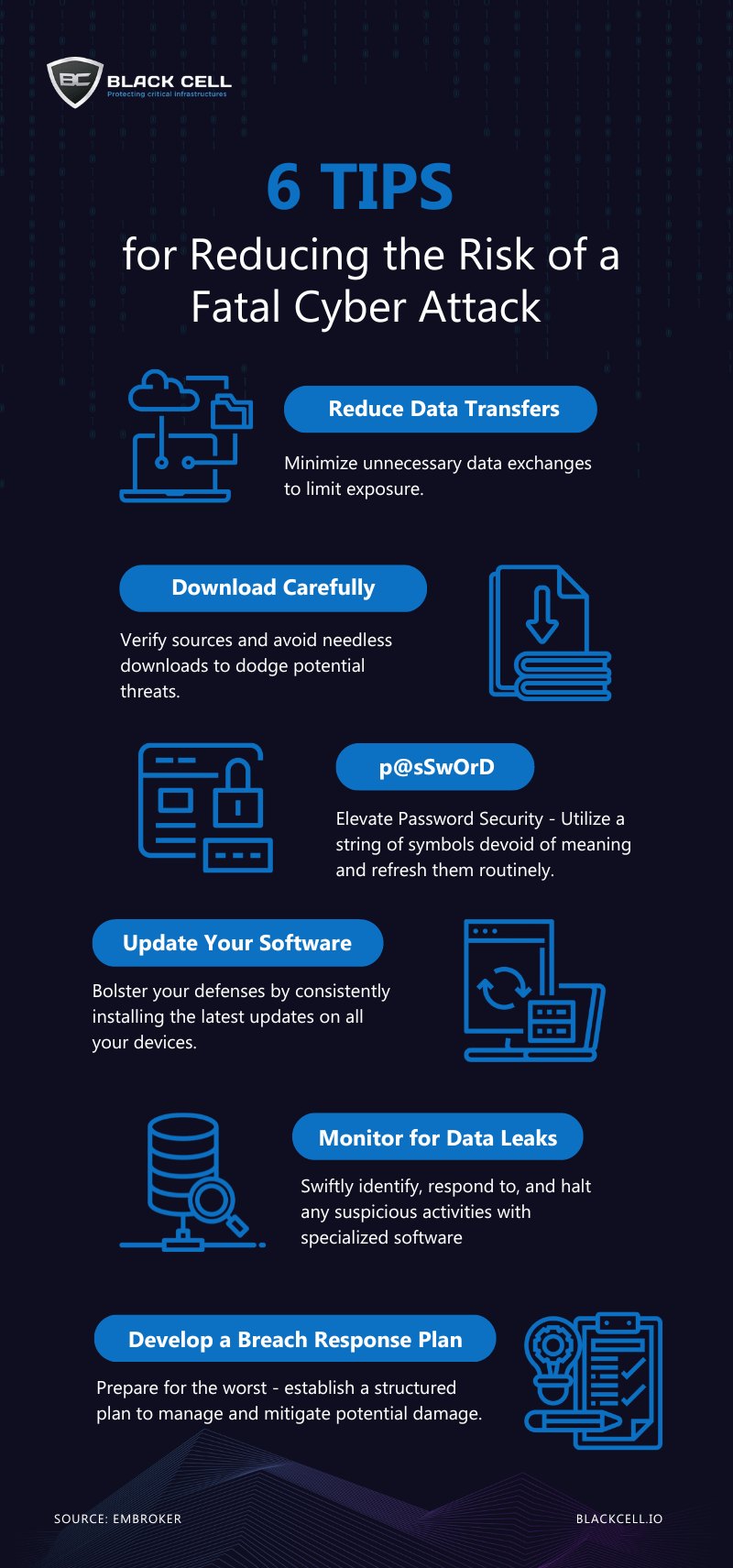
Best Practices for Cybersecurity in Public Health Systems
To prevent similar incidents, public health systems must adopt comprehensive cybersecurity strategies that protect against both current and emerging threats.
Implementing Stronger Security Protocols
- Regular Software Updates: Ensure all systems are running the latest security patches.
- Network Segmentation: Isolate critical systems to prevent lateral movement during a breach.
- Multi-Factor Authentication (MFA): Add an extra layer of security to sensitive accounts.
Conducting Regular Audits
Regular audits can help identify vulnerabilities before they are exploited. These audits should include both internal and external assessments to provide a comprehensive view of the organization's security posture, as advised by HIPAA Journal.
Training and Awareness
Human error remains a significant factor in many breaches. Training staff to recognize phishing attempts and other common tactics can significantly reduce the risk of a successful attack, as emphasized by UNICEF.
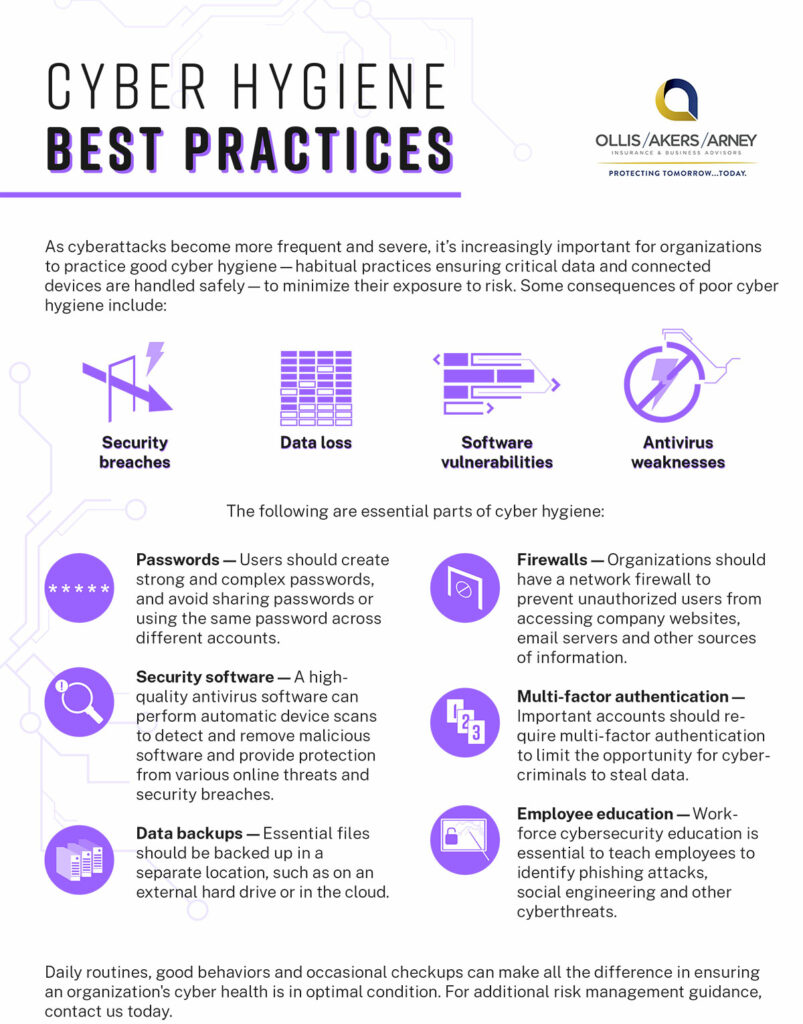

Outdated security protocols and complacency are among the highest impact pitfalls in cybersecurity. Estimated data.
Future Trends in Cybersecurity
As technology evolves, so do the threats. Staying ahead of cybercriminals requires continuous adaptation and innovation in security practices.
Embracing AI and Machine Learning
AI and machine learning offer new ways to detect and respond to threats in real-time. By analyzing large volumes of data, these technologies can identify patterns and anomalies indicative of a cyberattack, as outlined by IAPP.
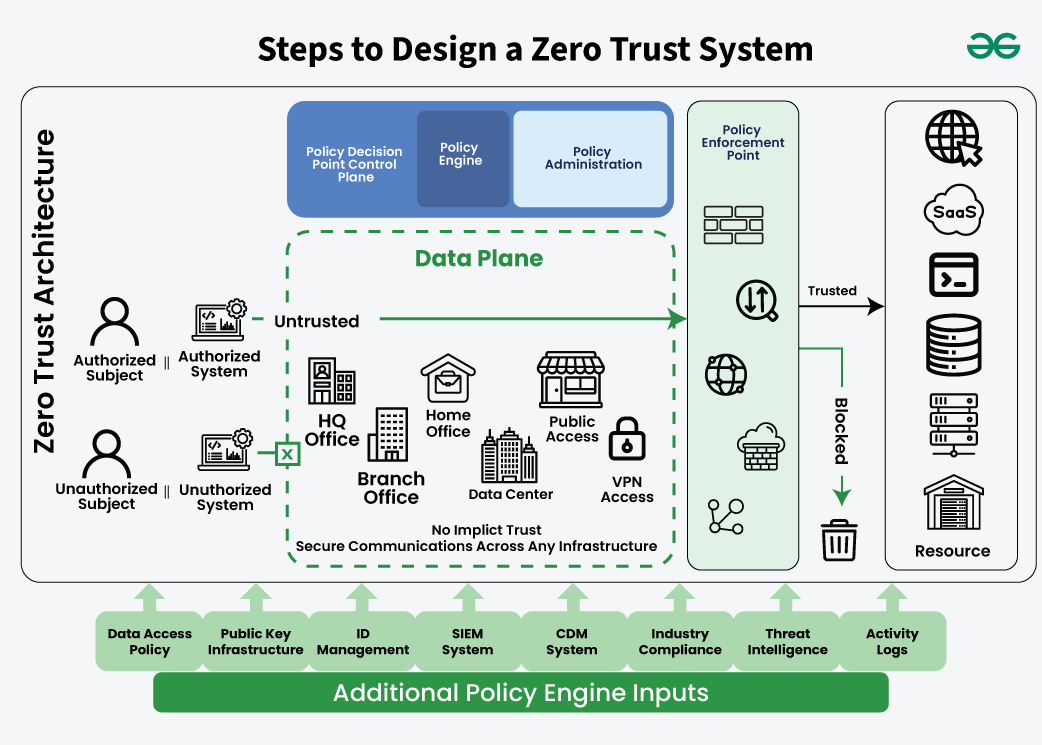
The Rise of Zero Trust Architecture
Zero Trust is a security model that assumes no user or system, internal or external, is inherently trustworthy. By enforcing strict identity verification and access controls, organizations can better protect their networks.
The Importance of Incident Response Plans
Having a well-defined incident response plan can mitigate the impact of a breach. This plan should include steps for identifying, containing, and recovering from an incident, as well as communication strategies for stakeholders.

Common Pitfalls and Solutions
Despite best efforts, organizations often fall into common pitfalls that can leave them vulnerable.
Pitfall 1: Complacency
Assuming that existing security measures are sufficient can lead to complacency. Regularly reviewing and updating security protocols is essential.
Solution: Continuous Improvement
Adopt a proactive approach to cybersecurity, continuously seeking improvements and staying informed about new threats and technologies.
Pitfall 2: Underestimating Insider Threats
Internal threats, whether intentional or accidental, can be just as damaging as external attacks.
Solution: Comprehensive Monitoring
Implement monitoring tools to detect unusual behavior by employees and other internal users.
Case Study: A Real-World Example
Consider a major hospital network that implemented a comprehensive cybersecurity strategy after experiencing a breach. By deploying advanced threat detection systems and conducting regular staff training, they were able to prevent future incidents and restore trust with their patients.
The Path Forward: Recommendations for NHS Scotland
To prevent future incidents, NHS Scotland and similar organizations must prioritize cybersecurity as a core component of their operations.
Recommendation 1: Invest in Modern Infrastructure
Upgrading legacy systems to modern, secure alternatives can reduce vulnerabilities and improve overall efficiency.
Recommendation 2: Establish a Culture of Security
Foster an organizational culture that values security by providing ongoing training and emphasizing its importance at all levels.
Recommendation 3: Collaborate with Industry Experts
Partnering with cybersecurity firms and experts can provide valuable insights and resources to enhance security measures.
The Global Perspective: Cybersecurity in Healthcare
NHS Scotland's experience is not unique. Healthcare organizations worldwide face similar challenges and must adopt comprehensive strategies to protect their digital assets.
Global Collaboration
International collaboration and information sharing can strengthen cybersecurity efforts across borders, providing a united front against cyber threats.
Regulatory Compliance
Adhering to global cybersecurity standards and regulations can ensure that organizations are prepared to meet the challenges of an increasingly digital world.
Conclusion: A Call to Action
The NHS Scotland breach serves as a stark reminder of the importance of cybersecurity in all sectors, especially healthcare. By adopting robust security measures, conducting regular audits, and fostering a culture of security, organizations can protect their digital assets and maintain the trust of their stakeholders.

FAQ
What is a legacy system?
A legacy system is an older software or hardware platform that remains in use despite the availability of newer versions. These systems are often maintained because they play a critical role in an organization's operations.
How can organizations prevent cyber breaches?
Organizations can prevent breaches by implementing strong security protocols, conducting regular audits, and training employees to recognize potential threats.
What are the benefits of adopting a Zero Trust security model?
Zero Trust security models enhance protection by assuming no user or system is inherently trustworthy, enforcing strict identity verification and access controls.
How does AI improve cybersecurity?
AI improves cybersecurity by analyzing large datasets to identify patterns and anomalies indicative of threats, enabling real-time detection and response.
What are common cybersecurity pitfalls to avoid?
Common pitfalls include complacency, underestimating insider threats, and failing to update security protocols regularly.
How can healthcare organizations enhance their cybersecurity?
Healthcare organizations can enhance cybersecurity by investing in modern infrastructure, fostering a culture of security, and collaborating with industry experts.
Why is public trust important in cybersecurity?
Public trust is crucial because breaches can erode confidence in digital services, leading to reluctance in sharing information and using these services.
What role does international collaboration play in cybersecurity?
International collaboration strengthens cybersecurity efforts by providing a unified response to threats, sharing information, and establishing global standards.
Key Takeaways
- Legacy systems are vulnerable to cyber attacks due to outdated security measures.
- Strong cybersecurity frameworks are crucial for protecting sensitive data.
- Regular audits and updates can help prevent breaches in public health systems.
- AI and machine learning can enhance threat detection and response capabilities.
- Zero Trust Architecture provides robust network security.
- Human error is a significant factor in breaches, highlighting the need for training.
- Public trust is vital for the success of digital healthcare services.
- International collaboration can strengthen global cybersecurity efforts.
Related Articles
- Understanding the Snowflake Data Theft Incident: Lessons and Future Safeguards [2025]
- How Emojis Are Reshaping Cybercrime Tactics: A Deep Dive [2025]
- Understanding the LAPD Data Breach: Lessons in Cybersecurity [2025]
- How Digital Devices Endanger Our Privacy Rights [2025]
- US Agencies Alert: Iranian Hackers Targeting American Critical Infrastructure [2025]
- Understanding Anthropic's Mythos AI Model: A New Era in Cybersecurity [2025]
![The Dark Side of Cybersecurity: NHS Scotland Domains and the Hidden Threats [2025]](https://tryrunable.com/blog/the-dark-side-of-cybersecurity-nhs-scotland-domains-and-the-/image-1-1775731085257.jpg)



