Introduction
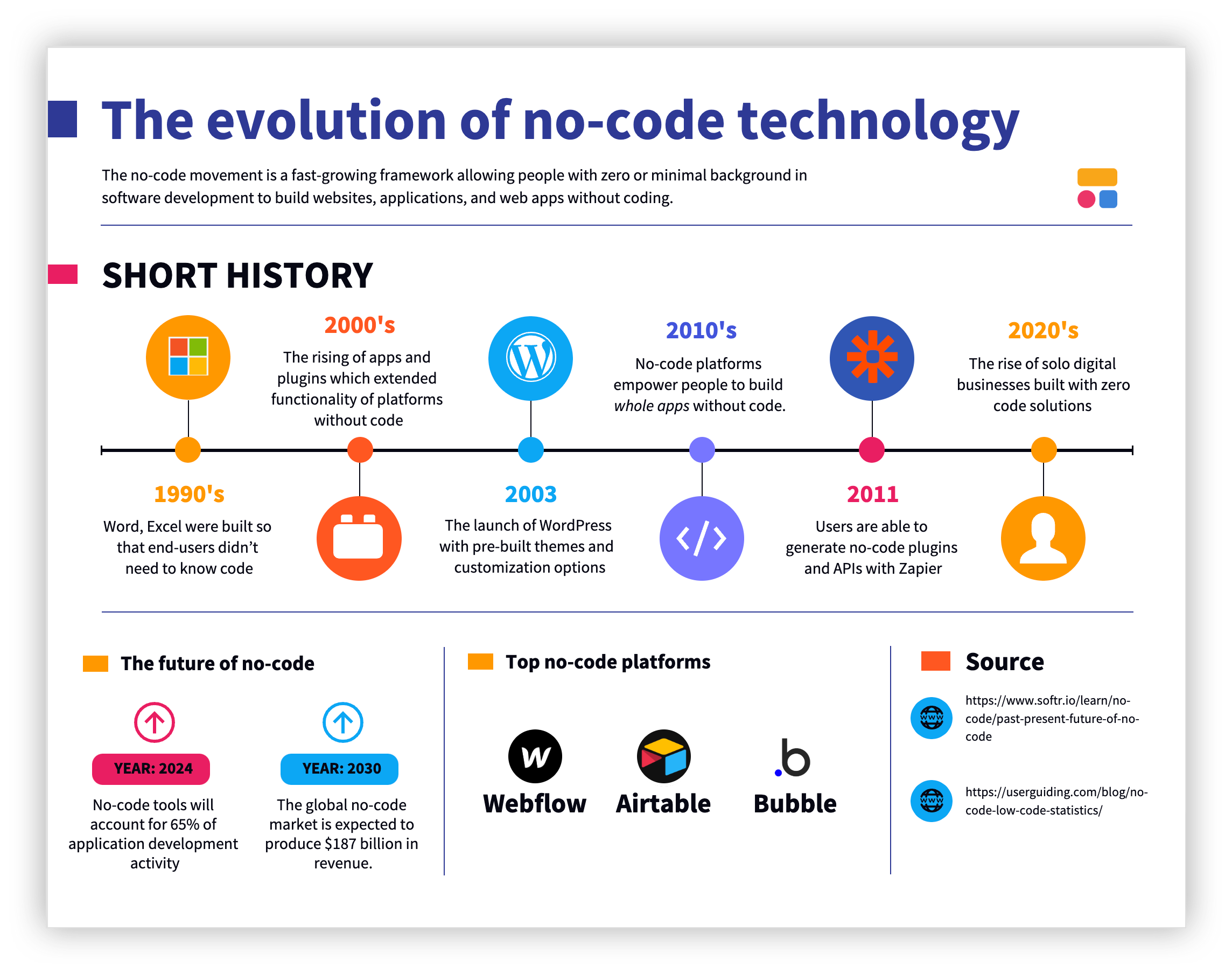
No-code platforms have revolutionized app development by empowering non-developers to create applications without writing a single line of code. But with great power comes great responsibility—and risk. Recently, cybercriminals have found a way to exploit these platforms, specifically targeting Bubble.io, a popular no-code app builder, to steal Microsoft account credentials. This article delves into the intricacies of how these attacks work, the implications for users, and how to safeguard against such threats.

The no-code development platform market is projected to grow significantly, from
TL; DR
- No-code platforms are being exploited: Cybercriminals use platforms like Bubble.io to create phishing sites that bypass traditional security measures, as reported by Kaspersky.
- Microsoft accounts targeted: These phishing sites aim to steal Microsoft 365 credentials, a tactic highlighted in Microsoft's security blog.
- Security loopholes exist: The trusted nature of these domains helps attackers evade email security filters, as noted by Microsoft.
- Protective measures are crucial: Implementing multi-factor authentication and educating users can mitigate risks, as advised by PCMag.
- Future outlook: As no-code platforms grow, so does the need for robust security protocols, as discussed in CIO.
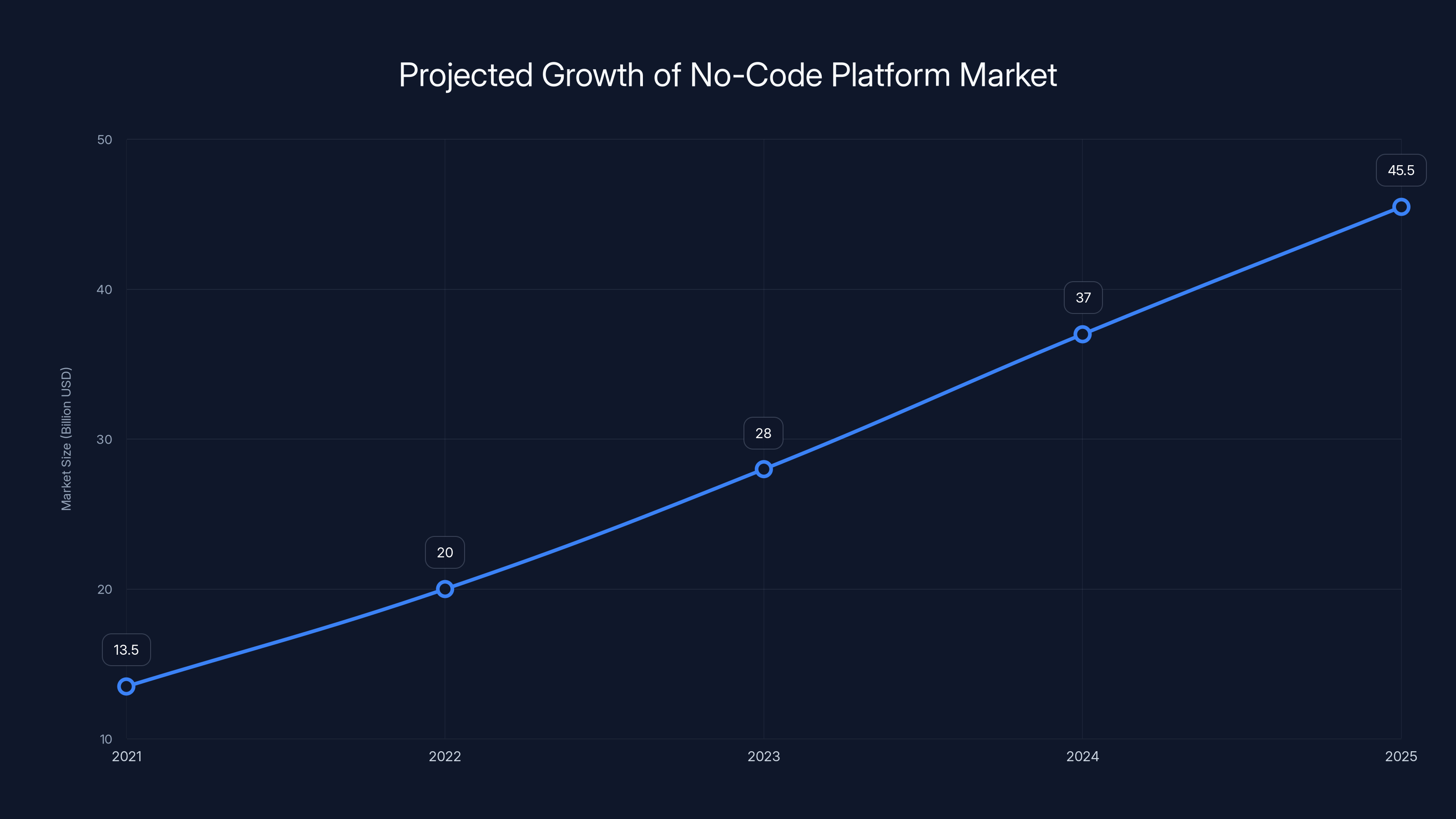
The no-code platform market is projected to grow from
Understanding No-Code Platforms
No-code platforms like Bubble.io allow users to build fully-functional applications through a visual interface. They abstract the complexity of coding into a drag-and-drop system, enabling rapid prototyping and deployment.
Key Features of No-Code Platforms
- Visual Development: Users can create applications visually, using a drag-and-drop interface.
- Pre-Built Templates: A variety of templates expedite the development process.
- Integrations: Easy integration with APIs and third-party services.
- Scalability: Applications can scale with user requirements without needing to rewrite code.
The Hijacking Incident
How Attackers Exploit No-Code Platforms
Attackers have started using no-code platforms to create phishing sites that mimic legitimate login pages. These are hosted on trusted domains, which helps them bypass email security filters and land directly in users' inboxes, as detailed in Kaspersky's analysis.
Why This Works
- Trusted Domains: No-code platforms often use subdomains of their main website, which are inherently trusted by email filters.
- Ease of Use: Attackers can quickly set up phishing sites without technical expertise.
- Scalability: Phishing sites can be rapidly deployed, targeting multiple victims simultaneously.
Real-World Example
In one reported incident, attackers used Bubble.io to host a fake Microsoft 365 login page. Victims received emails directing them to the site, where they unknowingly entered their credentials, which were then harvested by the attackers, as highlighted in Microsoft's blog.
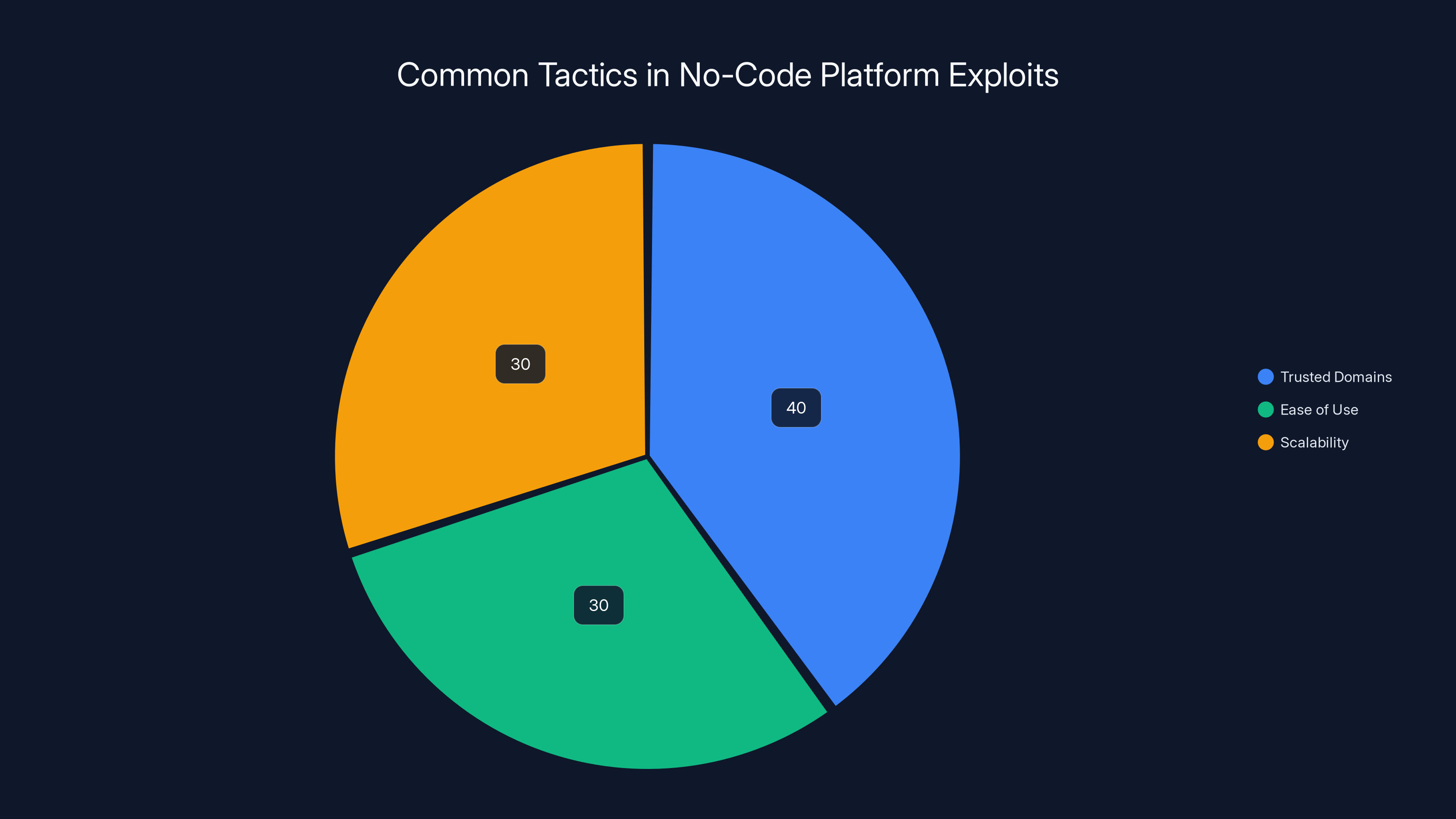
Attackers exploit no-code platforms primarily through trusted domains (40%), ease of use (30%), and scalability (30%). Estimated data.
Protecting Your Microsoft Account
Multi-Factor Authentication (MFA)
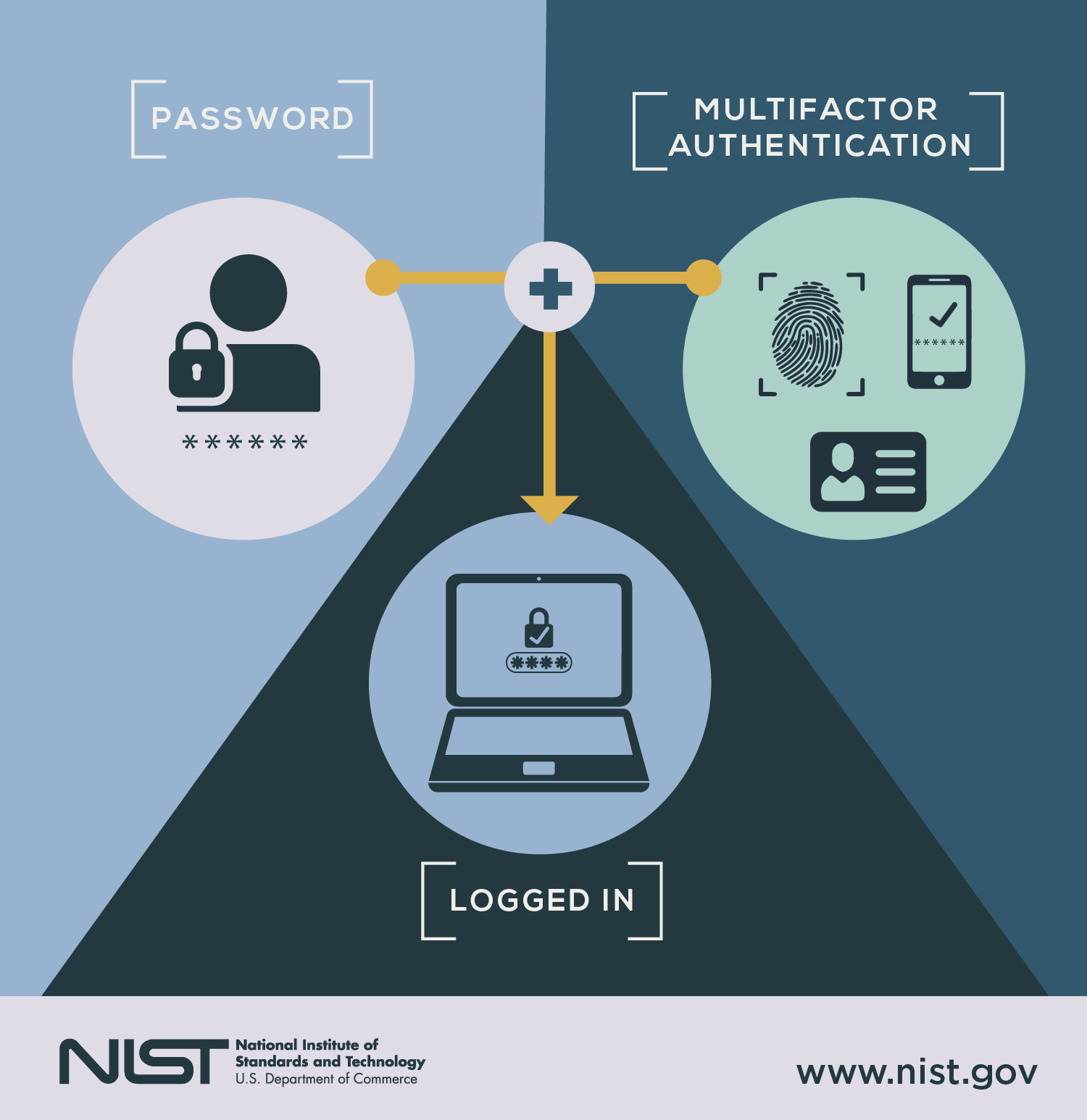
Implementing MFA is one of the most effective ways to protect your accounts. It requires users to provide two or more verification factors to gain access, as recommended by PCMag.
How to Set Up MFA
- Log into your Microsoft account.
- Navigate to Security settings.
- Select 'Two-step verification' and follow the prompts.
- Choose your preferred method (SMS, authenticator app, etc.).
Recognizing Phishing Attempts
Educating users to recognize phishing attempts is crucial. Here are some red flags:
- Unexpected Requests: Emails asking for urgent action on your account.
- Suspicious Links: URLs that don’t match the official domain.
- Poor Grammar and Spelling: Often indicative of phishing attempts.
Technical Safeguards
Implementing Security Protocols
For developers and IT teams, implementing security protocols within the no-code platform environment is essential.
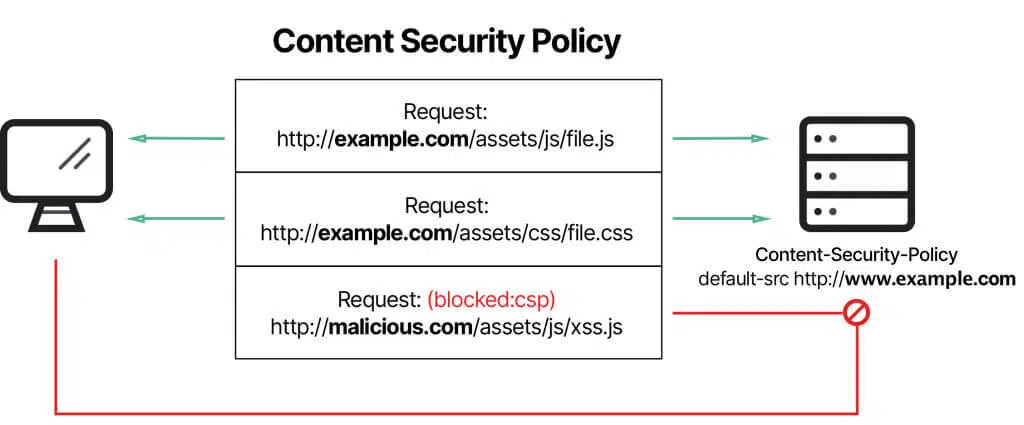
Use Content Security Policy (CSP)
CSP is a security feature that helps prevent a variety of attacks, such as cross-site scripting (XSS) and data injection, as explained in Imperva's guide.
html<meta http-equiv="Content-Security-Policy" content="default-src 'self'; img-src 'self' https://trusted.com;">
Regular Security Audits
Conducting regular audits can help identify vulnerabilities before they are exploited.
- Automated Tools: Use tools like Qualys or Tenable for continuous monitoring.
- Manual Reviews: Periodic manual reviews offer insights that automated tools might miss.
Future Trends in No-Code Security
Growth of No-Code Platforms
As no-code platforms continue to grow, they will likely become more appealing targets for cybercriminals. This growth necessitates stronger security measures, as discussed in Fortune Business Insights.
Predicted Trends
- Increased Use of AI: AI could be used to detect and prevent suspicious activities within no-code environments, as noted in AI Magazine.
- Enhanced User Education: More resources will be devoted to educating users about potential threats.
Recommendations for Users and Developers
- Stay Informed: Keep up with the latest security news and updates related to your platform.
- Use Strong Passwords: Implement password managers to generate and store complex passwords.
- Report Suspicious Activity: If you suspect a phishing attempt, report it to your IT department immediately.
Conclusion
The hijacking of no-code platforms like Bubble.io to steal Microsoft account details is a stark reminder of the vulnerabilities that come with new technologies. While these platforms offer incredible opportunities for innovation, they also require us to remain vigilant about security. By understanding the risks and implementing robust security measures, we can protect ourselves and our organizations from these emerging threats.
FAQ
What are no-code platforms?
No-code platforms are tools that allow users to create applications through a visual interface without writing code, as explained by CIO.
How are no-code platforms exploited by cybercriminals?
Cybercriminals use these platforms to create phishing sites on trusted domains, bypassing security filters and capturing user credentials, as detailed in Kaspersky's report.
How can I protect my Microsoft account from phishing attacks?
Use multi-factor authentication, recognize phishing red flags, and regularly update your security settings, as advised by PCMag.
What role does AI play in future no-code security?
AI can help detect and mitigate suspicious activities within no-code environments, enhancing overall security, as noted in AI Magazine.
Why are phishing attacks on the rise?
The rise in phishing attacks is due to increased digital interaction and the ease with which attackers can exploit no-code platforms, as discussed in Kaspersky's analysis.
What should I do if I suspect a phishing attempt?
Report it immediately to your IT department and avoid clicking on any suspicious links, as recommended by Microsoft.
Are there tools for conducting security audits on no-code platforms?
Yes, tools like Qualys and Tenable can be used for continuous monitoring and security audits, as mentioned by Qualys and Tenable.
Can no-code platforms be used securely?
Yes, with proper security measures, user education, and regular audits, no-code platforms can be used securely, as highlighted in CIO.
Is the no-code platform market expected to grow?
Yes, it's projected to grow significantly, reaching $45.5 billion by 2025, as reported by Fortune Business Insights.
Key Takeaways
- No-code platforms like Bubble.io are being exploited for phishing.
- Microsoft 365 accounts are prime targets for these attacks.
- Implementing MFA can significantly enhance account security.
- User education is vital in recognizing phishing attempts.
- AI and regular security audits are future trends in combating these threats.
Related Articles
- British Businesses Struggling to Recover from Cyberattacks: Strategies for Resilience [2025]
- Unpacking iOS 26 Security: Progress Made, Challenges Persist in the Face of New Spyware Threats [2025]
- Silicon Valley's Biggest Dramas: The Intersection of LiteLLM and Delve [2025]
- How Virtual Cloud Phones Are Reshaping Digital Fraud Economics [2025]
- The Unveiling of Coruna and DarkSword: How These Leaked Hacking Tools Threaten Millions of iPhones [2025]
- Unveiling VPN Transparency: A Deep Dive Into User Data Privacy [2025]
![The Dark Side of No-Code: How App Builders Are Being Hijacked to Steal Microsoft Account Details [2025]](https://tryrunable.com/blog/the-dark-side-of-no-code-how-app-builders-are-being-hijacked/image-1-1774546720942.jpg)



