Introduction
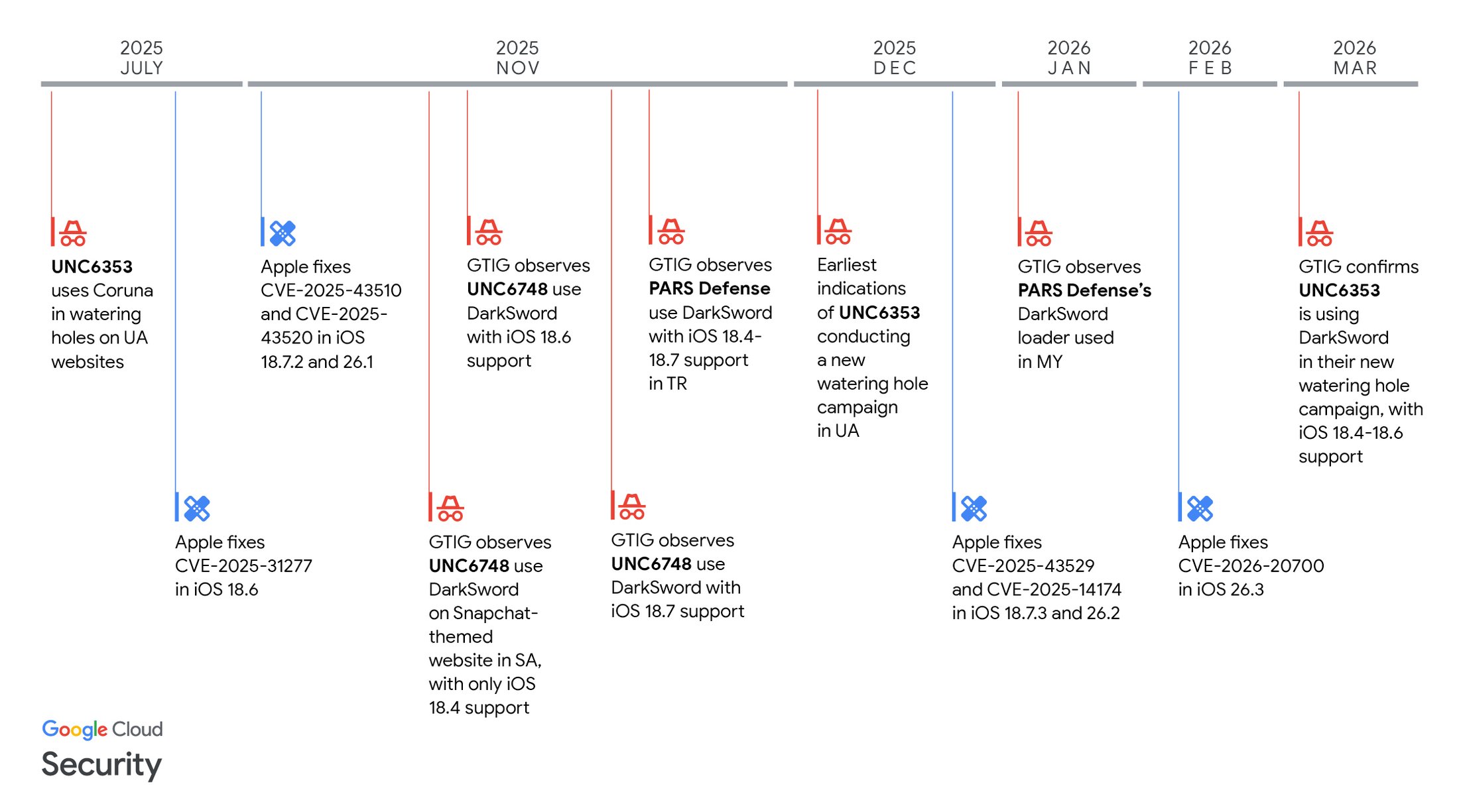
In recent years, Apple has consistently emphasized its commitment to user privacy and security, branding itself as a leader in the tech industry's battle against digital threats. With the release of iOS 26, Apple introduced a suite of security enhancements designed to shield iPhone users from the increasingly sophisticated landscape of cyber threats. However, the emergence of potent spyware tools like Coruna and Dark Sword has revealed that even with these advancements, vulnerabilities remain.
TL; DR
- Enhanced Security: iOS 26 introduced significant security features, yet challenges persist.
- Spyware Exposure: Leaked tools like Coruna and Dark Sword exploit unpatched systems.
- Global Impact: Russian and Chinese hackers target users worldwide.
- User Vigilance: Staying updated and cautious online is crucial.
- Future Trends: AI-driven security measures are poised to play a bigger role.

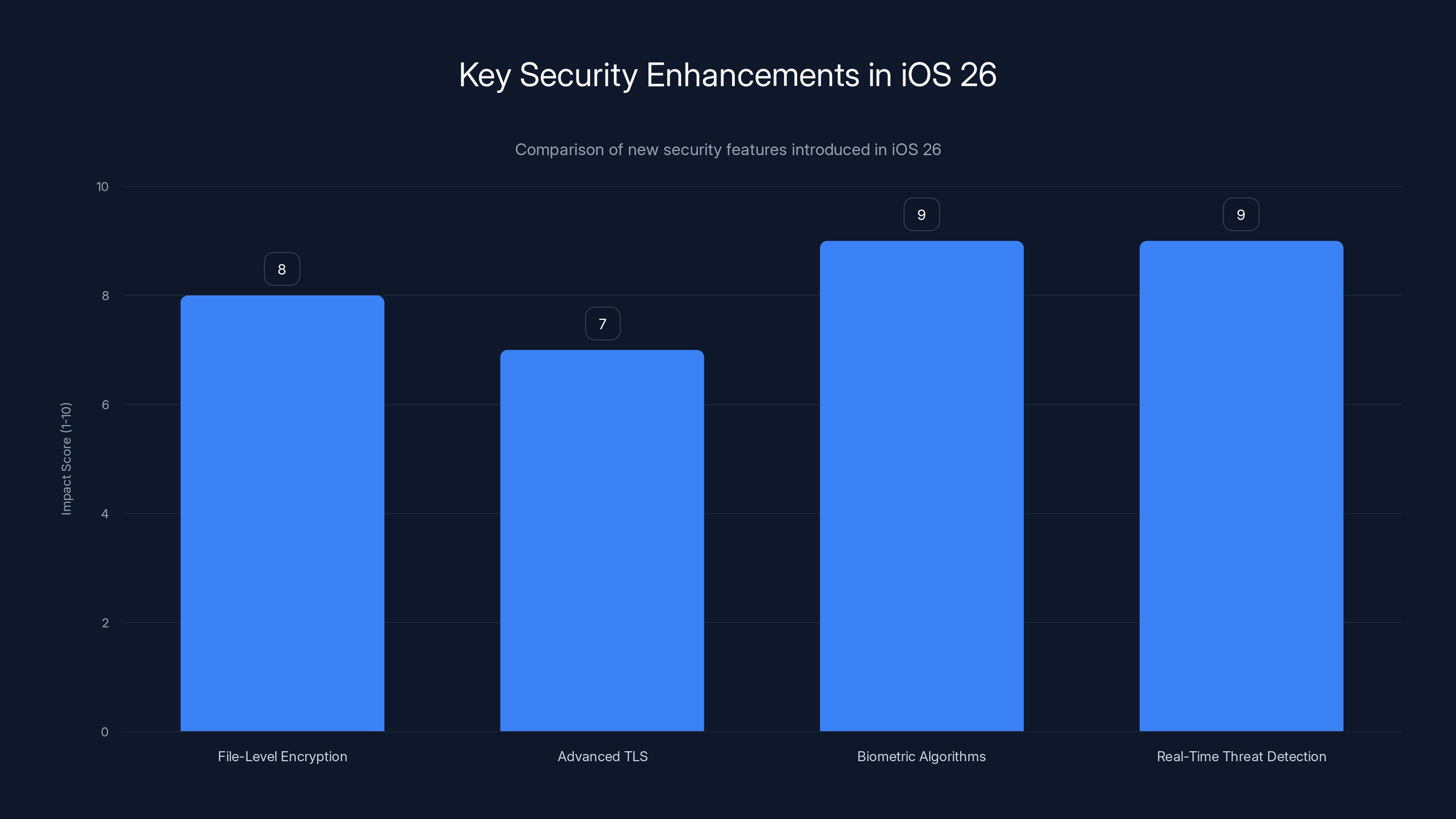
iOS 26 introduces significant security enhancements, with real-time threat detection and biometric algorithm improvements scoring highest in impact. Estimated data.
The Evolution of iOS Security
Apple's approach to security has always been a layered one, incorporating both hardware and software measures. The release of iOS 26 saw the introduction of several new features aimed at fortifying this defense:
Enhanced Encryption Protocols
The latest iOS update features improved encryption protocols that aim to protect data at rest and in transit. By advancing its end-to-end encryption capabilities, Apple ensures that even if data is intercepted, it remains inaccessible without the appropriate decryption keys.
- File-Level Encryption: Each file is encrypted with its own unique key, preventing unauthorized access in case of a breach.
- Advanced TLS: The adoption of the latest Transport Layer Security (TLS) version for secure communications.
Biometric Authentication Advancements
With Face ID and Touch ID, Apple has made biometric authentication a cornerstone of its security strategy. iOS 26 introduces enhanced algorithms that improve the speed and accuracy of these systems, reducing the risk of spoofing.
- Neural Engine Enhancements: Improved processing power for quicker and more reliable facial recognition.
Real-Time Threat Detection
Incorporating machine learning, iOS 26 can now detect potential threats in real-time, alerting users to malicious activity such as phishing attempts or suspicious app behavior.
- AI-Powered Alerts: Real-time notifications of potential threats, utilizing neural networks to analyze patterns instantly.
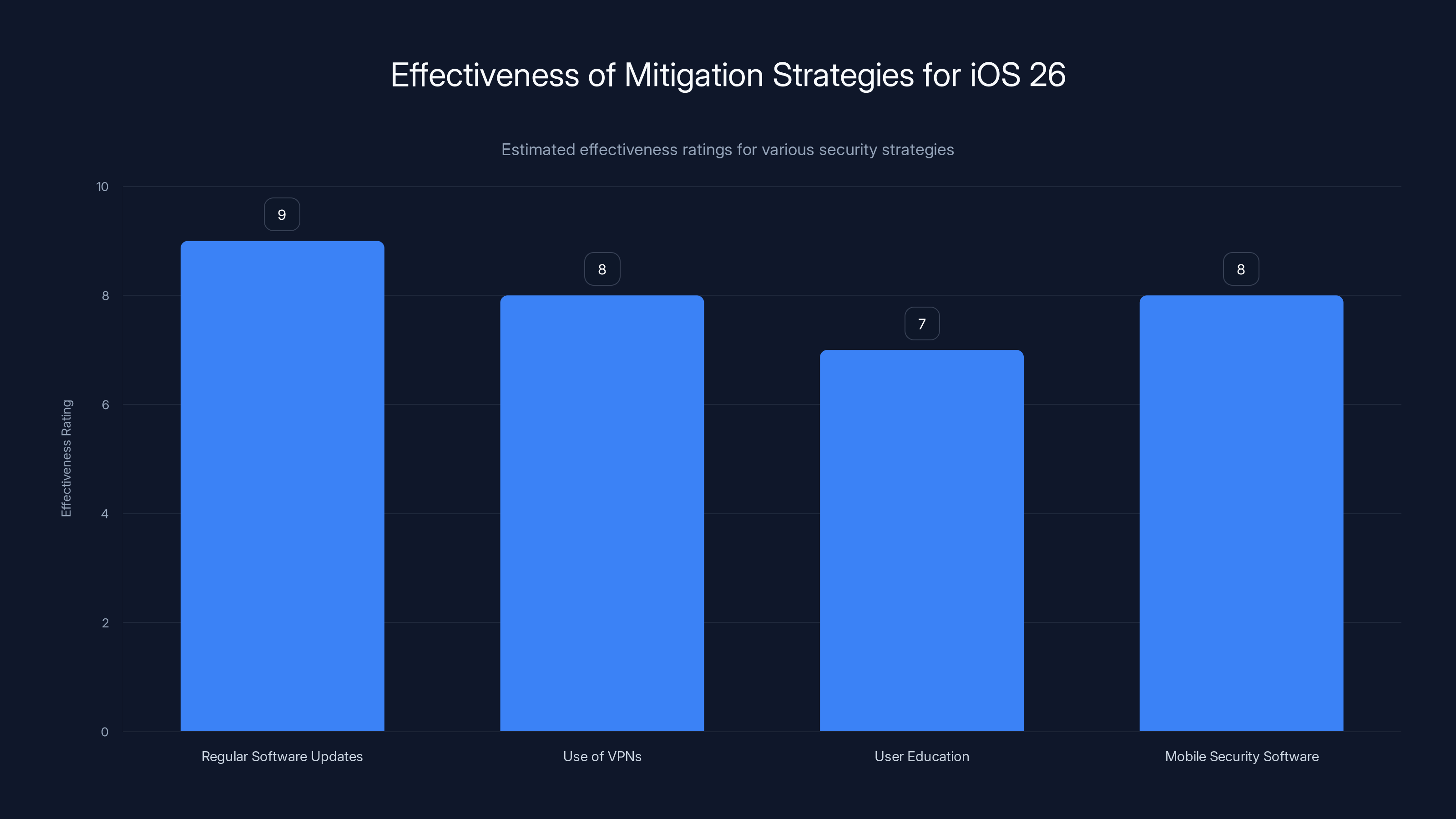
Regular software updates are the most effective strategy, scoring 9/10, while user education is also crucial with a score of 7/10. (Estimated data)
Leaked Tools and Their Threat
Despite these advancements, the recent exposure of hacking tools like Coruna and Dark Sword has highlighted a persistent challenge: the existence of zero-day vulnerabilities.
Understanding Zero-Day Vulnerabilities
A zero-day vulnerability refers to a flaw in software that is unknown to the vendor. Hackers exploit these vulnerabilities before developers can issue a patch, making them highly valuable in the cybercrime world.
- Exploitation Path: Hackers often use phishing emails or malicious websites to deploy spyware, leveraging these vulnerabilities.
The Role of Coruna and Dark Sword
These tools have been responsible for several large-scale campaigns, taking advantage of users who have not updated to the latest iOS version:
- Coruna: Primarily targets communication apps, allowing hackers to intercept messages and calls.
- Dark Sword: Focuses on data extraction, pulling information from contacts, photos, and browsing history.
Global Implications
The ramifications of these threats are global. State-sponsored actors from Russia and China have been implicated in deploying these tools, with the potential to affect millions of users worldwide.
- Espionage and Data Theft: These campaigns are often politically motivated, aiming at espionage or data theft.

Strategies for Mitigation
While iOS 26 represents a significant step forward, users and organizations must adopt complementary strategies to safeguard against these evolving threats.
Regular Software Updates
Keeping devices updated is the first line of defense against known vulnerabilities. Apple's swift response to patching known issues is only effective if users install these updates promptly.
- Automatic Updates: Enable automatic updates to ensure devices are always running the latest software.
Use of VPNs and Secure Networks
Virtual Private Networks (VPNs) can encrypt internet traffic, making it harder for hackers to intercept data.
- Trusted VPN Providers: Select reputable VPN services with strong encryption standards.
Educating Users
Awareness is a powerful tool. Users should be educated about the risks of phishing emails and suspicious links that could lead to spyware installation.
- Phishing Awareness Programs: Regular training sessions for users to recognize and avoid phishing attempts.
Deploying Mobile Security Software
Investing in additional security applications can provide an extra layer of protection. These apps offer features like malware scanning and app permission management.
- Top Mobile Security Apps: Lookout and iVerify are popular choices with robust malware detection capabilities.

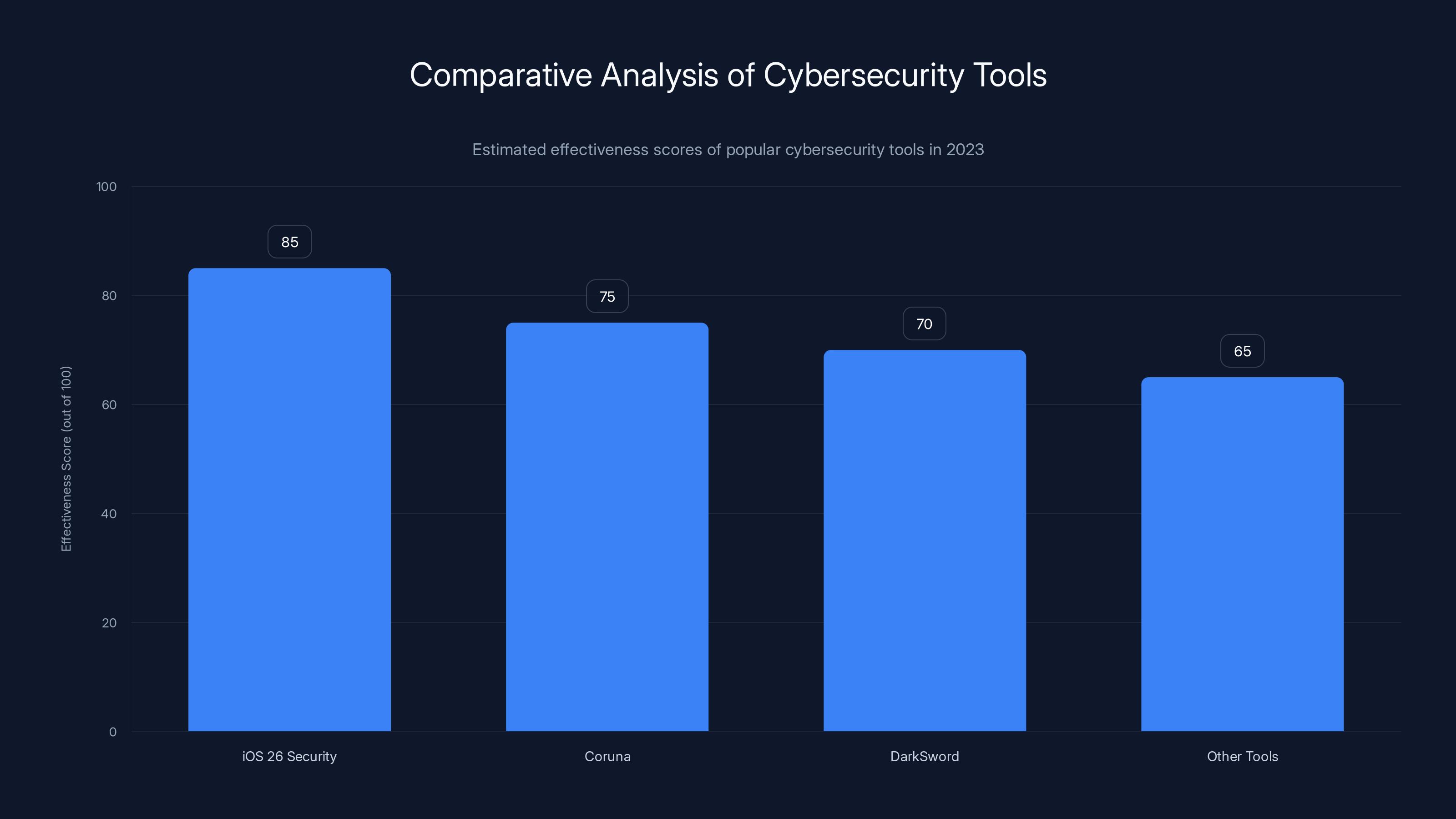
iOS 26 leads in security effectiveness with an estimated score of 85, surpassing tools like Coruna and Dark Sword. Estimated data.
Future Trends in Mobile Security
The landscape of mobile security is ever-evolving, with new challenges and innovations on the horizon.
AI and Machine Learning
Artificial intelligence is set to play a larger role in threat detection and response, enabling systems to learn from historical data and adapt to new threats.
- Predictive Analytics: AI models predicting potential vulnerabilities based on usage patterns.
Blockchain Technology
Blockchain could revolutionize mobile security by providing decentralized and tamper-proof authentication methods.
- Decentralized Identity Management: Using blockchain for secure identity verification without centralized repositories.
Quantum-Resistant Encryption
As quantum computing advances, the need for quantum-resistant encryption becomes critical to protect data from being easily decrypted.
- Post-Quantum Cryptography: Developing encryption methods that can withstand quantum computing attacks.

Conclusion
While Apple's iOS 26 has made significant strides in enhancing mobile security, the battle against cyber threats is far from over. The emergence of tools like Coruna and Dark Sword underscores the need for continuous vigilance and innovation. By staying informed and adopting proactive measures, users can better protect their data in an increasingly connected world.

FAQ
What are zero-day vulnerabilities?
Zero-day vulnerabilities are software flaws unknown to the vendor, exploited by hackers before they can be patched.
How can iOS users protect themselves from spyware?
Regularly update your iOS, use VPNs, and install trusted mobile security apps to enhance protection.
Why is biometric authentication important?
Biometric authentication provides a secure and convenient method of verifying user identity, reducing reliance on passwords.
How does AI enhance mobile security?
AI improves threat detection by analyzing patterns in real-time, enabling faster identification of potential threats.
What is quantum-resistant encryption?
It's an encryption method designed to withstand decryption by quantum computers, ensuring data security against future threats.
Key Takeaways
- iOS 26 introduced significant security enhancements but challenges remain.
- Spyware tools like Coruna and Dark Sword exploit unpatched systems.
- Global hacking campaigns highlight the need for constant vigilance.
- Regular updates and user education are crucial for mobile security.
- AI and blockchain technology are future trends in cybersecurity.
Related Articles
- The Unveiling of Coruna and DarkSword: How These Leaked Hacking Tools Threaten Millions of iPhones [2025]
- Silicon Valley's Biggest Dramas: The Intersection of LiteLLM and Delve [2025]
- How Virtual Cloud Phones Are Reshaping Digital Fraud Economics [2025]
- Unveiling VPN Transparency: A Deep Dive Into User Data Privacy [2025]
- British Businesses Struggling to Recover from Cyberattacks: Strategies for Resilience [2025]
- Industrializing Deception: How Cybercriminals Are Infiltrating Trusted Domains [2025]
![Unpacking iOS 26 Security: Progress Made, Challenges Persist in the Face of New Spyware Threats [2025]](https://tryrunable.com/blog/unpacking-ios-26-security-progress-made-challenges-persist-i/image-1-1774546493962.jpg)



