The Extradition of Xu Zewei: A Deep Dive into Cyber Espionage and Global Security [2025]
The digital age has ushered in unprecedented opportunities for innovation and connectivity. But with these opportunities come new risks, particularly in the realm of cybersecurity. One of the most pressing concerns is cyber espionage, where state-sponsored hackers infiltrate foreign networks to steal sensitive data. This article delves into the case of Xu Zewei, a hacker allegedly working for the Chinese government, who was recently extradited to the United States.
TL; DR
- Xu Zewei, accused of cyberattacks on behalf of China, was extradited to the U.S. as reported by TechCrunch.
- Cyber espionage is a growing threat, targeting sensitive research and infrastructure, as highlighted by the World Economic Forum.
- State-sponsored hacking groups like Hafnium are increasingly sophisticated, according to Homeland Security Today.
- Global cooperation is essential for effective cybersecurity measures, emphasized by CISA.
- Future trends suggest a rise in AI-driven cyberattacks, as noted by Harvard Business Review.

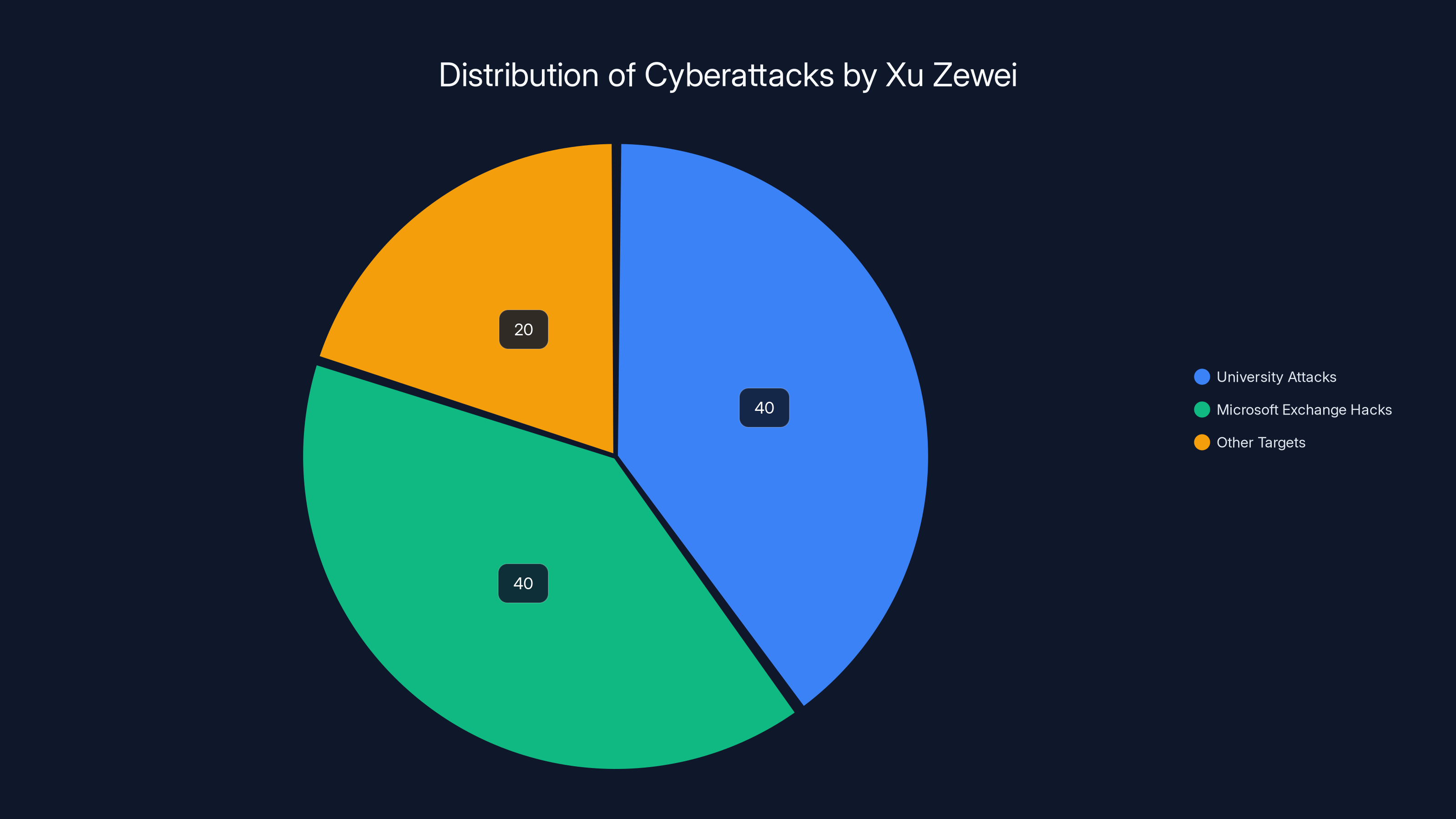
Estimated distribution of Xu Zewei's cyberattacks shows a focus on universities and Microsoft Exchange servers, each comprising 40% of the attacks. Estimated data.
The Background of Cyber Espionage
Cyber espionage involves the use of computer networks to gain illicit access to confidential information held by a government or organization. This practice has become a significant concern for national security agencies worldwide.
What Is Cyber Espionage?
Cyber espionage refers to the act of using digital means to conduct espionage activities. Unlike traditional espionage, which might involve covert operations by physical agents, cyber espionage is conducted through network infiltration, malware, and phishing attacks.
Historical Context
Cyber espionage is not a new phenomenon. It dates back to the early days of the internet, but it has evolved significantly over the decades. In the 1990s, cyber espionage was primarily focused on military targets. However, as the internet became an integral part of business and government operations, the targets expanded to include private companies and critical infrastructure.
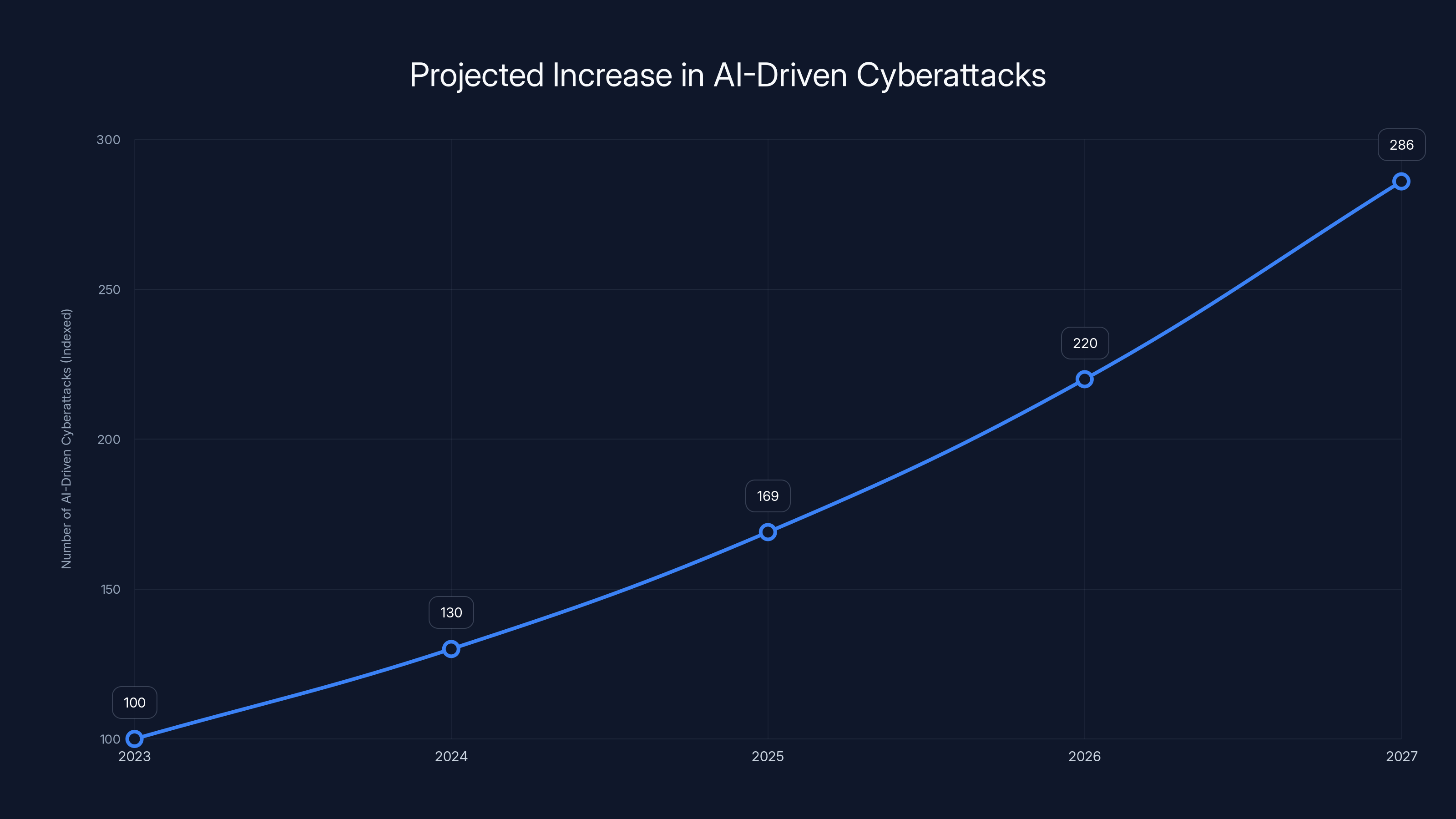
AI-driven cyberattacks are projected to increase by 30% annually, highlighting the growing threat and need for advanced cybersecurity measures. (Estimated data)
Case Study: The Extradition of Xu Zewei
Xu Zewei's extradition is a landmark case in the fight against cybercrime. It highlights the complexities of international law and the challenges of prosecuting cybercriminals across borders.
Who Is Xu Zewei?
Xu Zewei is accused of being a key player in a series of cyberattacks carried out on behalf of the Chinese Ministry of State Security (MSS). These attacks targeted U.S. universities and businesses, aiming to steal sensitive information, including research related to the COVID-19 pandemic, as detailed by The Record.
The Allegations
According to U.S. prosecutors, Xu, along with his co-conspirator Zhang Yu, participated in several high-profile cyberattacks. These included:
- University Attacks: Targeting universities to access COVID-19 research.
- Microsoft Exchange Hacks: Exploiting vulnerabilities in Microsoft Exchange servers to access thousands of email accounts.
The Significance of Extradition
Xu's extradition from Italy to the U.S. underscores the importance of international cooperation in combating cybercrime. It also raises questions about the effectiveness of current cybersecurity measures and the need for more robust international treaties, as discussed by War on the Rocks.

Understanding State-Sponsored Hacking
State-sponsored hacking groups are often behind the most sophisticated and damaging cyberattacks. These groups are typically well-funded and have access to cutting-edge technology.
Hafnium and Silk Typhoon
The Hafnium group, allegedly linked to China's government, has been implicated in numerous cyberattacks. Their tactics often involve exploiting software vulnerabilities to gain access to sensitive systems, as reported by Gulf Business.
Key Characteristics of State-Sponsored Hacking:
- Advanced Persistent Threats (APTs): Long-term, targeted attacks designed to remain undetected.
- Zero-Day Exploits: Using undisclosed software vulnerabilities to infiltrate systems.
- Sophisticated Techniques: Employing social engineering, spear-phishing, and malware.
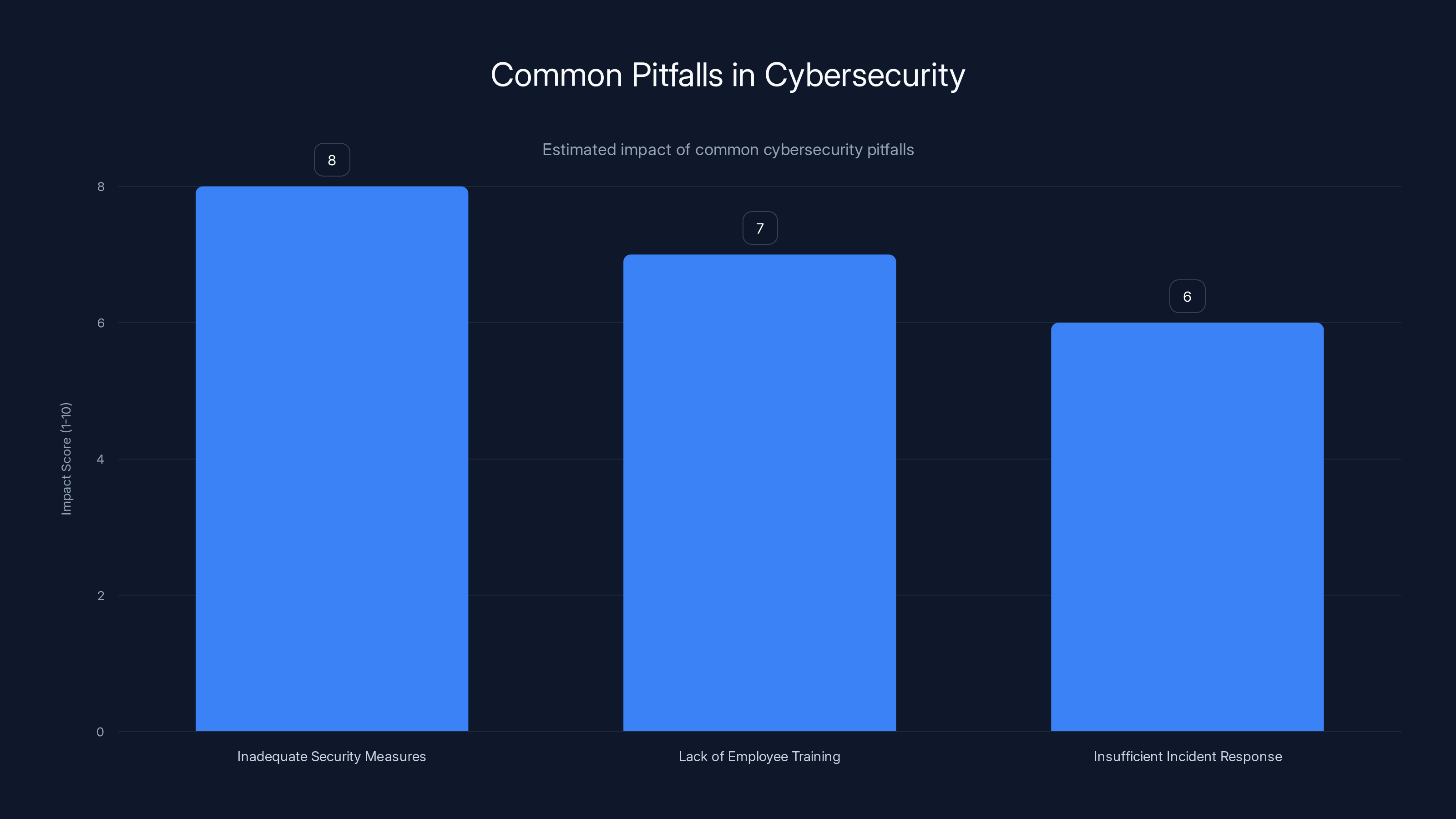
Inadequate security measures are the most impactful pitfall in cybersecurity, followed by lack of employee training and insufficient incident response planning. (Estimated data)
Technical Details of the Cyberattacks
Understanding the technical aspects of these attacks can provide insights into how they were executed and how similar threats can be mitigated in the future.
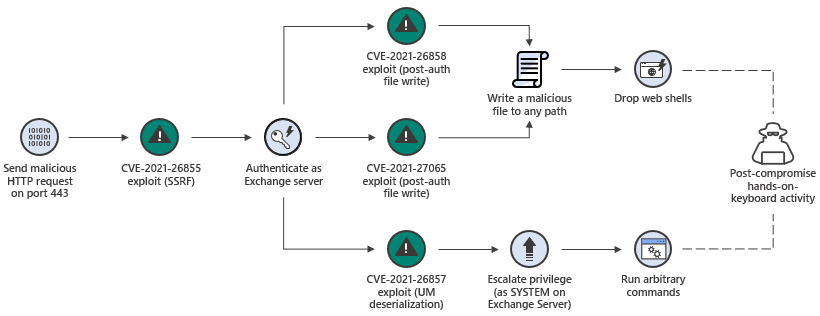
Microsoft Exchange Server Exploits
The Microsoft Exchange attacks involved exploiting vulnerabilities known as Proxy Logon. This allowed hackers to bypass authentication and execute arbitrary commands on the server, as documented by CISA.
Tools and Techniques
Hackers used a combination of tools and techniques, including:
- Web Shells: To maintain persistent access to compromised servers.
- Credential Dumping: To harvest usernames and passwords.
- Lateral Movement: Moving through a network to access additional resources.
Common Pitfalls in Cybersecurity
Despite advancements in cybersecurity technology, many organizations fall victim to cyberattacks due to common pitfalls and oversights.
Inadequate Security Measures
Many organizations fail to implement basic security measures, such as:
- Firewalls: To block unauthorized access.
- Encryption: To protect sensitive data.
- Multi-Factor Authentication (MFA): To add an extra layer of security.
Lack of Employee Training
Phishing attacks are still one of the most common methods used by hackers. Training employees to recognize and report phishing attempts can significantly reduce the risk of a successful attack, as noted in the FBI Internet Crime Report.

Best Practices for Cybersecurity
Implementing best practices can help organizations protect themselves from cyber threats.
Regular Audits and Assessments
Conducting regular security audits and vulnerability assessments can identify potential weaknesses in your network.
Incident Response Planning
Having a well-defined incident response plan can minimize damage and recovery time in the event of a cyberattack.
Future Trends in Cybersecurity
As technology continues to evolve, so do the tactics of cybercriminals. Staying ahead of these trends is crucial for effective cybersecurity.
Rise of AI-Driven Attacks
AI technology is being used by both cybersecurity professionals and hackers. While AI can enhance defense mechanisms, it also enables more sophisticated attacks.
Increased Focus on Supply Chain Security
Supply chain attacks, where hackers target a third-party vendor to gain access to a primary target, are becoming more common. Strengthening supply chain security is essential.
Recommendations for Organizations
Organizations can take several steps to enhance their cybersecurity posture.
Invest in Advanced Threat Detection
Using advanced threat detection systems can help identify and neutralize threats before they cause significant damage.
Collaborate with Law Enforcement
Building strong relationships with law enforcement and other organizations can facilitate information sharing and improve response times.
Continuous Education and Awareness
Keeping employees informed about the latest cybersecurity threats and best practices is crucial in creating a culture of security.
Conclusion
The extradition of Xu Zewei marks a significant step in the global fight against cybercrime. It highlights the importance of international cooperation and the need for robust cybersecurity measures.
As cyber threats continue to evolve, organizations must remain vigilant and proactive in their defense strategies. By understanding the tactics of cybercriminals and implementing best practices, businesses and governments can better protect themselves from future attacks.
FAQ
What is cyber espionage?
Cyber espionage involves using digital means to conduct espionage activities, typically by infiltrating computer networks to access confidential information without authorization.
How does state-sponsored hacking work?
State-sponsored hacking involves government-backed groups using advanced techniques to conduct cyberattacks, often targeting sensitive information for geopolitical or commercial advantage.
What are the common pitfalls in cybersecurity?
Common pitfalls include inadequate security measures, lack of employee training, and insufficient incident response planning.
How can organizations improve their cybersecurity?
Organizations can improve cybersecurity by conducting regular audits, implementing advanced threat detection systems, and continuously educating employees about potential threats.
What are the future trends in cybersecurity?
Future trends include a rise in AI-driven attacks and increased focus on supply chain security.
How does AI impact cybersecurity?
AI impacts cybersecurity by enhancing defense mechanisms but also enabling more sophisticated cyberattacks by malicious actors.
What role does international cooperation play in cybersecurity?
International cooperation is crucial for effective cybersecurity, as it facilitates information sharing, coordinates responses to threats, and aids in the prosecution of cybercriminals.
Key Takeaways
- Xu Zewei's extradition underscores the importance of international cooperation in combating cybercrime.
- Cyber espionage remains a significant threat to national security and technological innovation.
- State-sponsored hacking groups employ sophisticated techniques that require advanced defense measures.
- AI-driven attacks are projected to grow, necessitating enhanced cybersecurity strategies.
- Organizations must focus on supply chain security to prevent indirect attacks.
- Continuous employee education is crucial in recognizing and mitigating cybersecurity threats.
Related Articles
- Unveiling the Precursor: The Hidden Malware Before Stuxnet [2025]
- Understanding the Itron Cyberattack: Impacts and Lessons [2025]
- Inside the New Cyber Scam: How Hackers Exploit Microsoft Teams to Steal Your Data [2025]
- Discord Sleuths Gained Unauthorized Access to Anthropic’s Mythos | WIRED
- How to Choose a Business Internet Provider [2025]
- Understanding Data Breaches: Lessons from the Rituals Membership Database Breach [2025]
![The Extradition of Xu Zewei: A Deep Dive into Cyber Espionage and Global Security [2025]](https://tryrunable.com/blog/the-extradition-of-xu-zewei-a-deep-dive-into-cyber-espionage/image-1-1777311385513.jpg)




