Understanding Data Breaches: Lessons from the Rituals Membership Database Breach [2025]
In April, Dutch cosmetic giant Rituals confirmed a significant data breach involving its "My Rituals" membership database. While the company has yet to disclose the exact number of customers affected, the breach underscores the critical importance of cybersecurity in today’s digital age.
TL; DR
- Rituals' membership breach exposed personal data, including names and contact details.
- Data breaches are increasingly common and costly for businesses.
- Implementing robust security measures is crucial to prevent future incidents.
- Consumers should protect themselves with strong passwords and vigilance.
- Cybersecurity trends indicate a growing emphasis on AI and automation for threat detection.

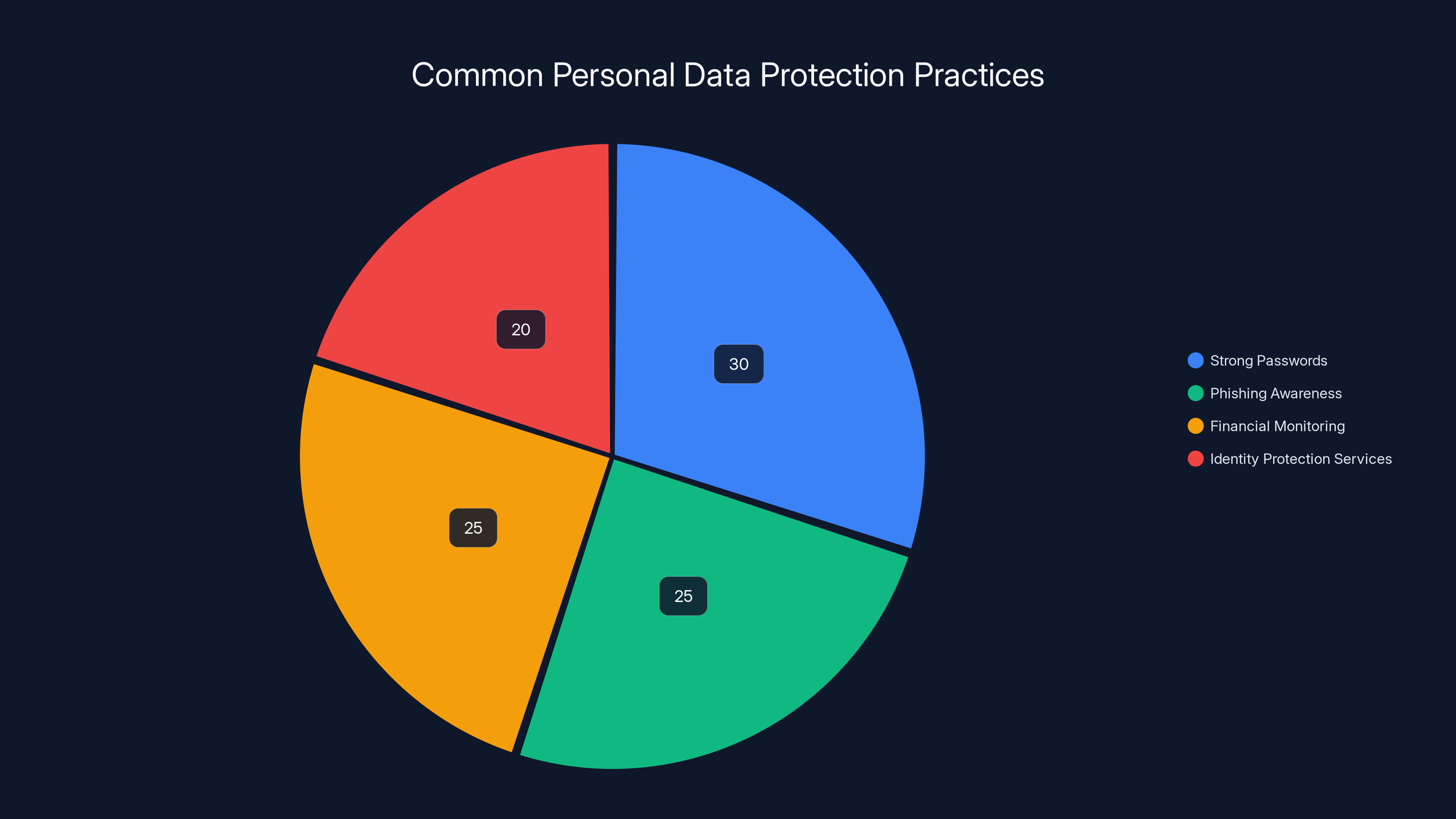
Estimated data suggests that consumers primarily focus on using strong passwords and being aware of phishing attempts, with financial monitoring and identity protection services also being significant areas of attention.
What Happened?
The breach at Rituals exposed sensitive customer information from their "My Rituals" membership database. This included data such as names, contact details, and birth dates. While financial information was not reportedly stolen, the exposure of personally identifiable information (PII) still poses significant risks for affected individuals as reported by SC World.
The Impact of Data Breaches
Data breaches have become a regular occurrence, affecting businesses across various sectors. The consequences can be severe, including financial losses, reputational damage, and legal liabilities. Companies like Rituals must navigate the aftermath carefully, balancing transparency with security measures to restore customer trust.
Key Points:
- Financial Losses: Companies often face hefty fines and legal fees, as noted in a study by Morgan Lewis.
- Reputation Damage: Loss of customer trust can impact brand loyalty.
- Operational Disruption: Breaches can disrupt normal business operations, which is a growing concern according to Industrial Cyber.
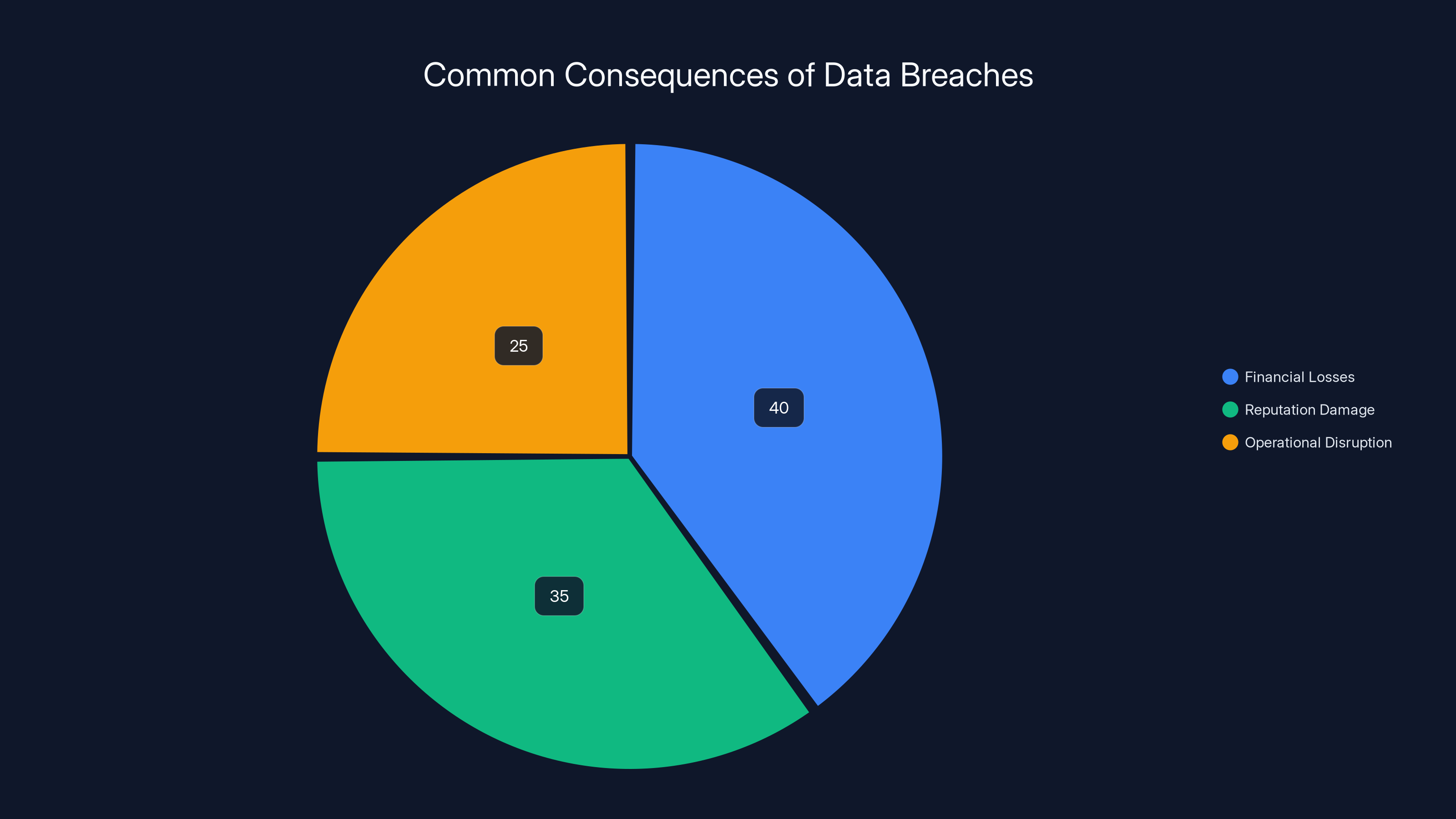
Estimated data shows financial losses (40%), reputation damage (35%), and operational disruption (25%) as key impacts of data breaches.
Understanding Cybersecurity Threats
To comprehend the significance of the Rituals breach, it is essential to understand the broader landscape of cybersecurity threats.
Common Types of Cyber Attacks
- Phishing Attacks: Deceptive emails or messages designed to trick recipients into revealing sensitive information, as detailed in a HIPAA Journal webinar.
- Ransomware: Malicious software that encrypts data until a ransom is paid, a threat highlighted in Acronis' blog.
- SQL Injection: Exploiting vulnerabilities in a website's database to access or manipulate data.
- Denial-of-Service (Do S): Overwhelming a system with traffic to disrupt its services.
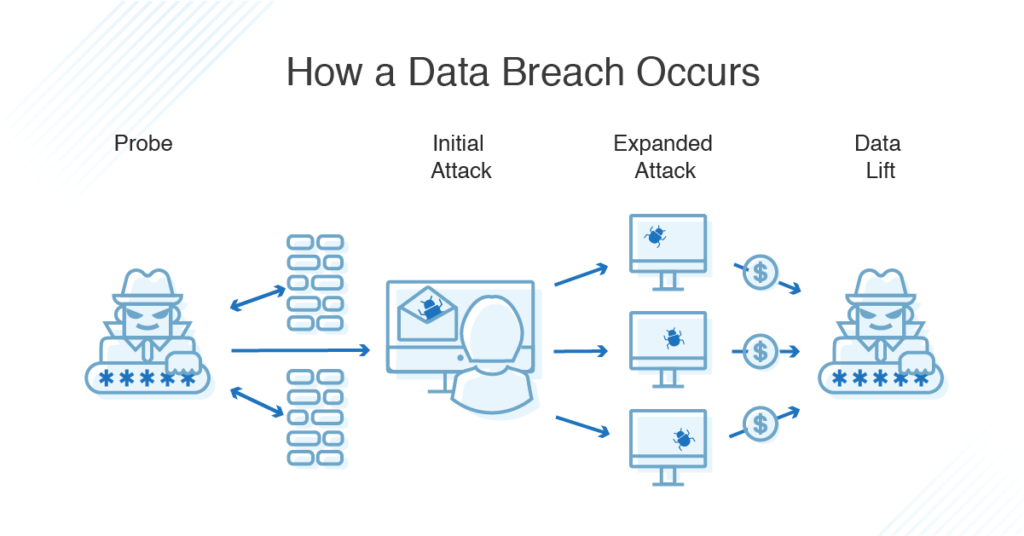
How Data Breaches Occur
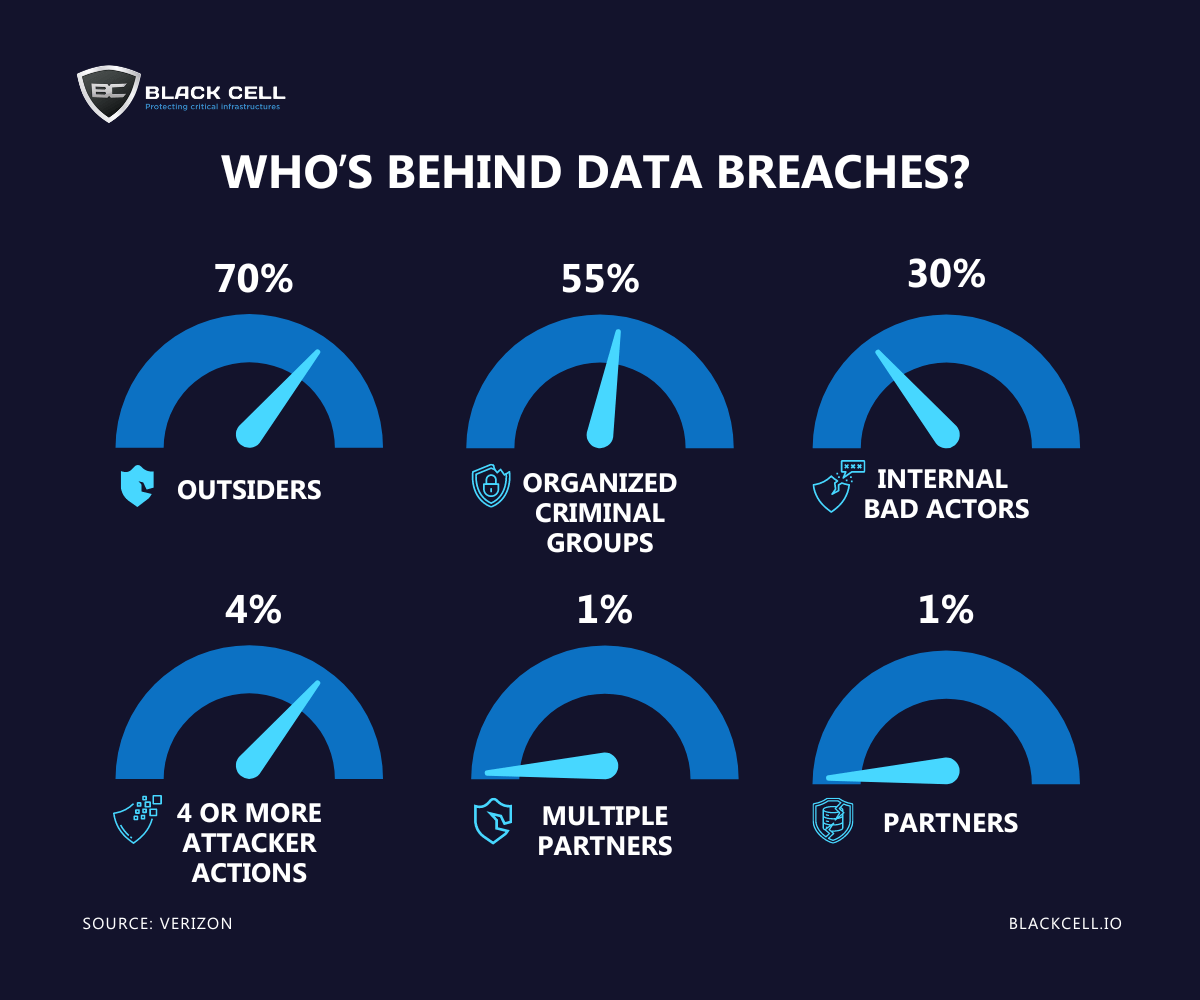
Data breaches can result from various causes, including:
- Weak Passwords: Easily guessable passwords remain a common entry point for attackers, as discussed in BizTech Magazine.
- Software Vulnerabilities: Outdated software can contain vulnerabilities that hackers exploit, a major concern according to Barracuda's blog.
- Insider Threats: Employees with access to sensitive data can intentionally or unintentionally cause breaches.
- Third-Party Vendors: Partners with inadequate security can be a weak link, as noted by Financier Worldwide.
Practical Tips for Companies
Strengthening Security Measures
To prevent incidents like the Rituals breach, companies should implement robust security protocols. Here are some best practices:
- Regular Security Audits: Conduct frequent audits to identify vulnerabilities.
- Employee Training: Educate staff about cybersecurity best practices and phishing awareness.
- Data Encryption: Use strong encryption methods to protect data at rest and in transit.
- Multi-Factor Authentication (MFA): Require MFA to add an extra layer of security.
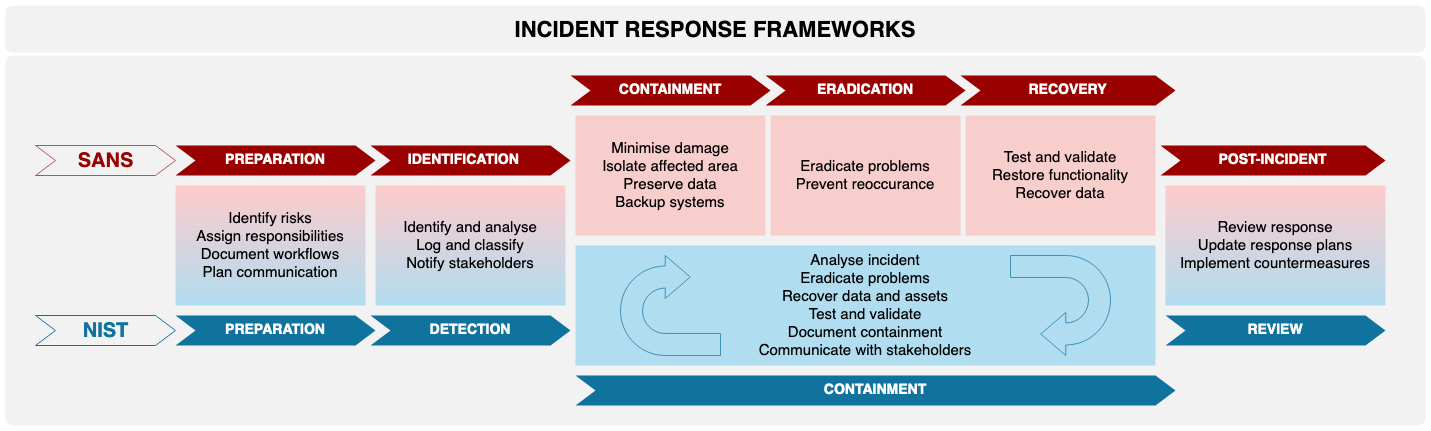
Incident Response and Management
Having an incident response plan is crucial for minimizing damage during a breach:
- Preparation: Establish a response team and define roles.
- Detection and Analysis: Quickly identify and analyze the breach.
- Containment: Isolate affected systems to prevent further damage.
- Eradication and Recovery: Remove the threat and restore systems.
- Post-Incident Review: Analyze the response to improve future readiness.
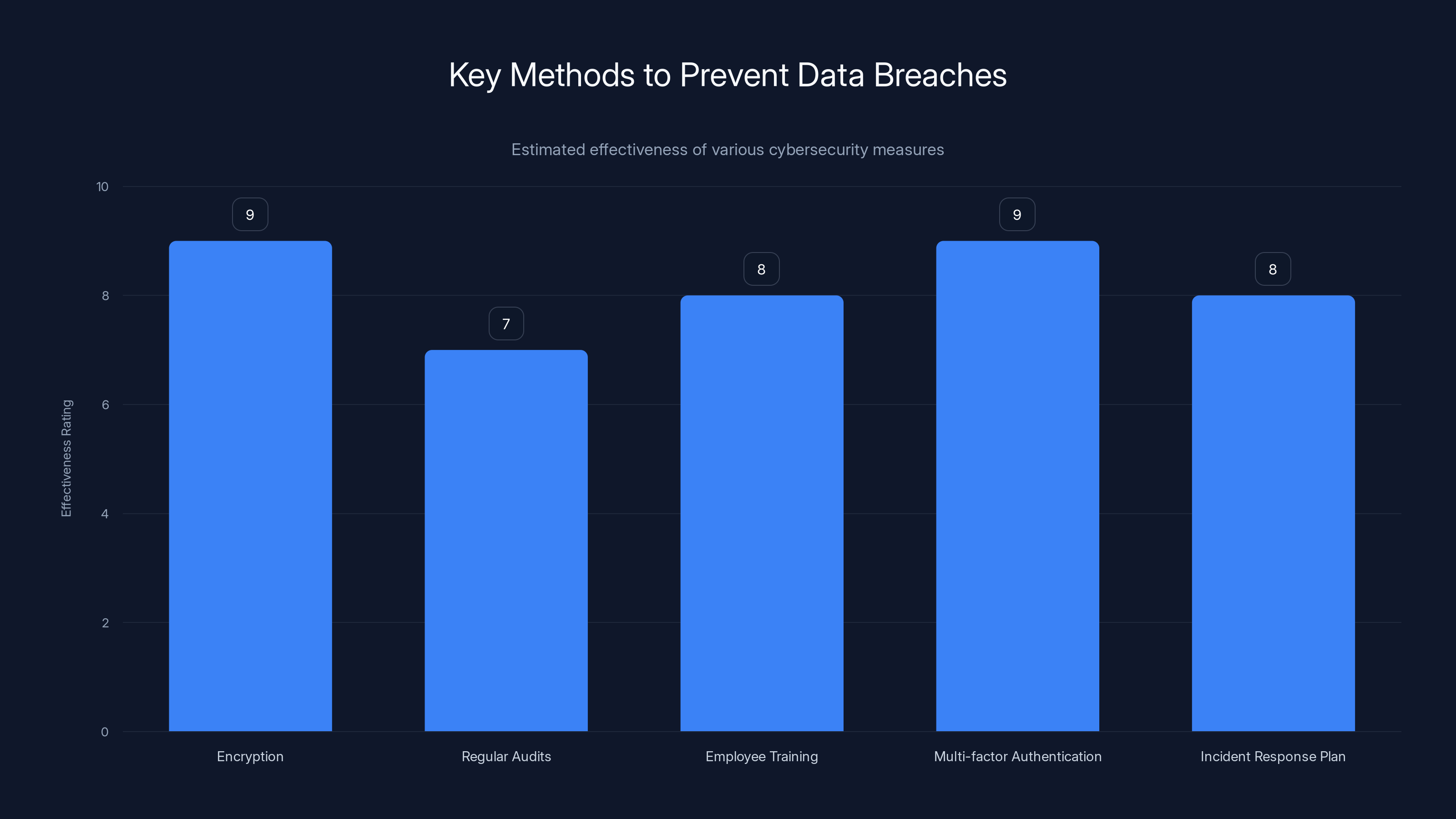
Encryption and multi-factor authentication are among the most effective methods to prevent data breaches, with high effectiveness ratings. (Estimated data)
Protecting Consumer Data
While companies work to secure their systems, consumers must also take steps to protect their personal information.
Personal Data Protection Tips
- Use Strong Passwords: Create complex passwords and change them regularly.
- Be Wary of Phishing Attempts: Verify the sender’s identity before clicking links.
- Monitor Financial Statements: Regularly check bank and credit card statements for unauthorized charges.
- Use Identity Theft Protection Services: Consider services that monitor your credit and alert you to suspicious activity.

The Role of Technology in Cybersecurity
AI and Machine Learning
Artificial Intelligence (AI) and Machine Learning (ML) are transforming cybersecurity by enabling quicker threat detection and response. These technologies analyze vast amounts of data to identify patterns and anomalies indicative of a breach.
- Automated Threat Detection: AI systems can scan for threats 24/7, reducing response times.
- Behavioral Analytics: ML can detect unusual behavior that signals a potential threat, as noted in the Trend Micro report.
Blockchain Technology
Blockchain offers promising applications for cybersecurity:
- Decentralized Security: Blockchain's distributed ledger technology ensures data integrity.
- Smart Contracts: Automate security protocols and responses.

Future Trends in Cybersecurity
Increasing Regulation
Governments worldwide are implementing stricter regulations to protect consumer data and penalize companies that fail to comply. Examples include the General Data Protection Regulation (GDPR) in Europe and the California Consumer Privacy Act (CCPA).
Cybersecurity as a Service
As threats evolve, more companies are turning to cybersecurity as a service (CaaS) to manage their security needs. This approach provides access to expert resources without the need for in-house expertise, as highlighted by SC World.

Conclusion
The Rituals data breach highlights the ongoing challenges businesses face in securing customer data. By understanding the nature of cyber threats and implementing robust security measures, companies can protect their data and maintain customer trust. As technology evolves, staying informed about cybersecurity trends and best practices will be crucial for both businesses and consumers.
FAQ
What is a data breach?
A data breach is an incident where unauthorized individuals gain access to sensitive, protected, or confidential data. The data can include personal information, financial records, or business secrets.
How can companies prevent data breaches?
Companies can prevent data breaches by implementing strong security measures, such as encryption, regular audits, employee training, and multi-factor authentication. They should also have a comprehensive incident response plan.
What should consumers do if their data is breached?
Consumers should monitor their financial accounts for suspicious activity, change passwords regularly, and consider using identity theft protection services. Contacting the companies involved for guidance is also advisable.
How does AI help in cybersecurity?
AI helps in cybersecurity by automating threat detection and response, analyzing large datasets for patterns, and identifying anomalies that could indicate a breach. It allows for faster and more accurate security management.
What are the future trends in cybersecurity?
Future trends in cybersecurity include the increased use of AI and machine learning, the incorporation of blockchain technology, the rise of cybersecurity as a service, and more stringent data protection regulations.
Why is multi-factor authentication important?
Multi-factor authentication (MFA) is important because it adds an extra layer of security by requiring users to provide multiple forms of verification before accessing sensitive data or systems.
What is the role of blockchain in cybersecurity?
Blockchain technology enhances cybersecurity by providing decentralized security, ensuring data integrity, and enabling secure smart contracts.
How do phishing attacks work?
Phishing attacks involve sending deceptive emails or messages that appear legitimate to trick individuals into revealing sensitive information, such as passwords or credit card numbers.
Key Takeaways
- Rituals faced a significant data breach exposing member data.
- Data breaches can lead to financial and reputational damage.
- Strong security measures are essential to prevent breaches.
- Consumers should practice personal data protection strategies.
- AI and blockchain are crucial for future cybersecurity.
- Cybersecurity regulations are becoming more stringent.
- Cybersecurity as a service is gaining traction.
Related Articles
- China-Nexus Cyber Actors Turning IoT Infrastructure into Botnets [2025]
- Unveiling the Precursor: The Hidden Malware Before Stuxnet [2025]
- Why Your IT Helpdesk is Getting Weird Calls: LinkedIn Data Threats [2025]
- Operating at Scale in the Age of AI: Insights from Uber's CTO Praveen Neppalli Naga [2025]
- Unmasking Spyware: How Fake Android Apps Are Weaponized [2025]
- The Morning After: Polymarket and a Hairdryer [2025]
![Understanding Data Breaches: Lessons from the Rituals Membership Database Breach [2025]](https://tryrunable.com/blog/understanding-data-breaches-lessons-from-the-rituals-members/image-1-1777043097155.jpg)



