The Rise of Kad Nap: Understanding and Combating a Resilient Router Botnet [2025]
Last month, a friend of mine called in a panic. Her internet was crawling, and her smart devices were acting up. After a bit of digging, we found her Asus router was part of a botnet. This wasn't just any botnet—this was Kad Nap, a malware that's turning thousands of routers into cybercrime tools. Let's dive into how Kad Nap operates and, more importantly, how you can protect your network from becoming its next victim.
TL; DR
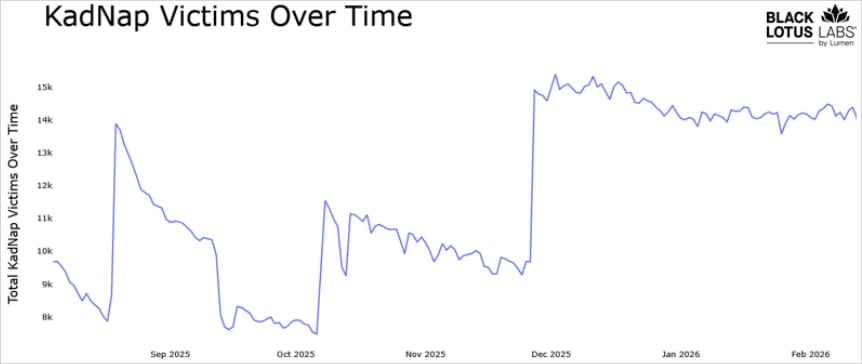
- Kad Nap Botnet: Infects around 14,000 routers daily, primarily Asus models.
- Entry Point: Exploits unpatched firmware vulnerabilities.
- Proxy Network: Used for anonymous cybercrime traffic.
- Resilience: Difficult to dismantle due to its decentralized nature.
- Protection: Regular updates and strong passwords are your first defense.
- Future Trends: Io T expansion may increase botnet targets.
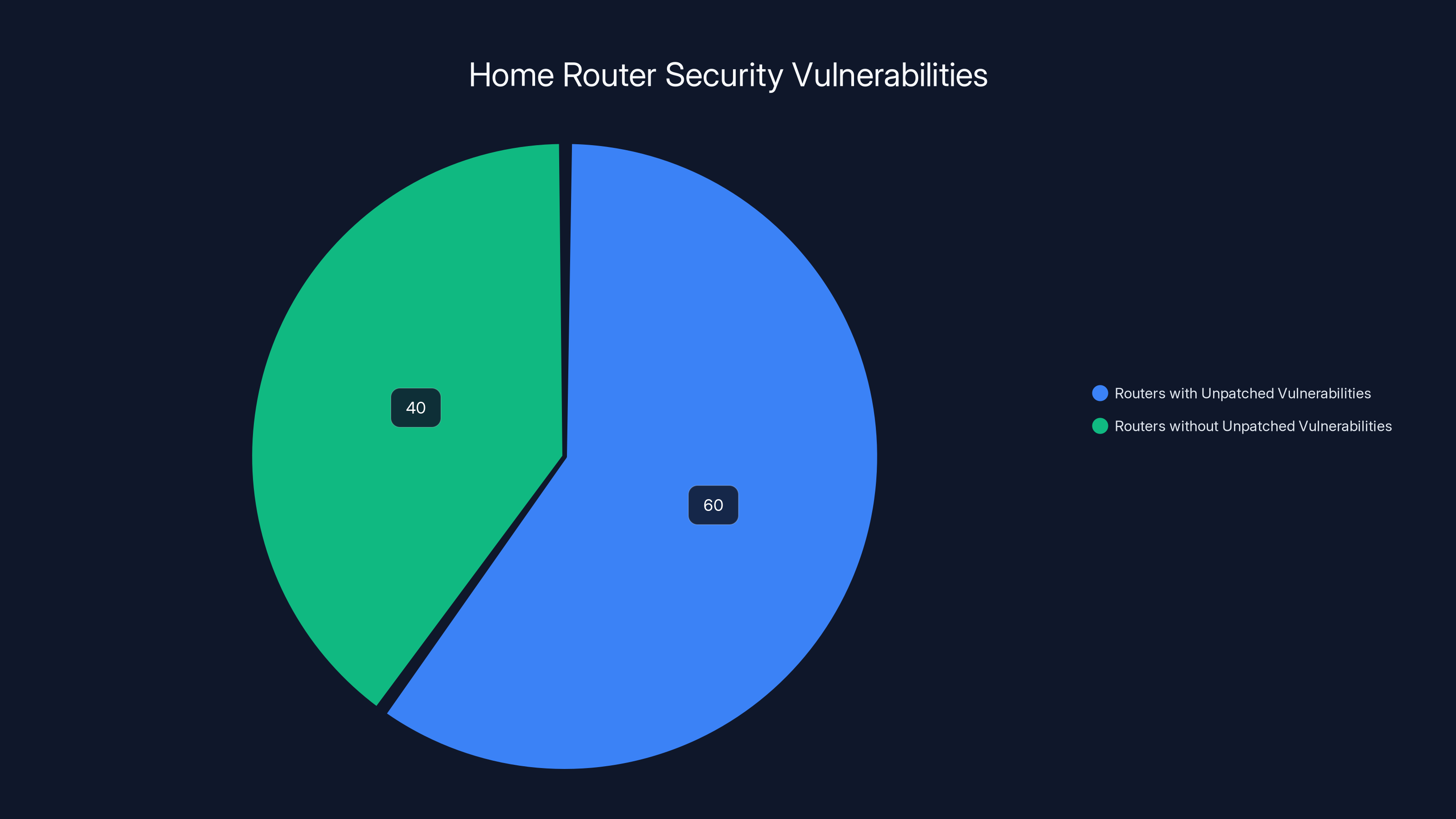
A significant 60% of home routers have unpatched security vulnerabilities, highlighting a critical area for improvement in network security.
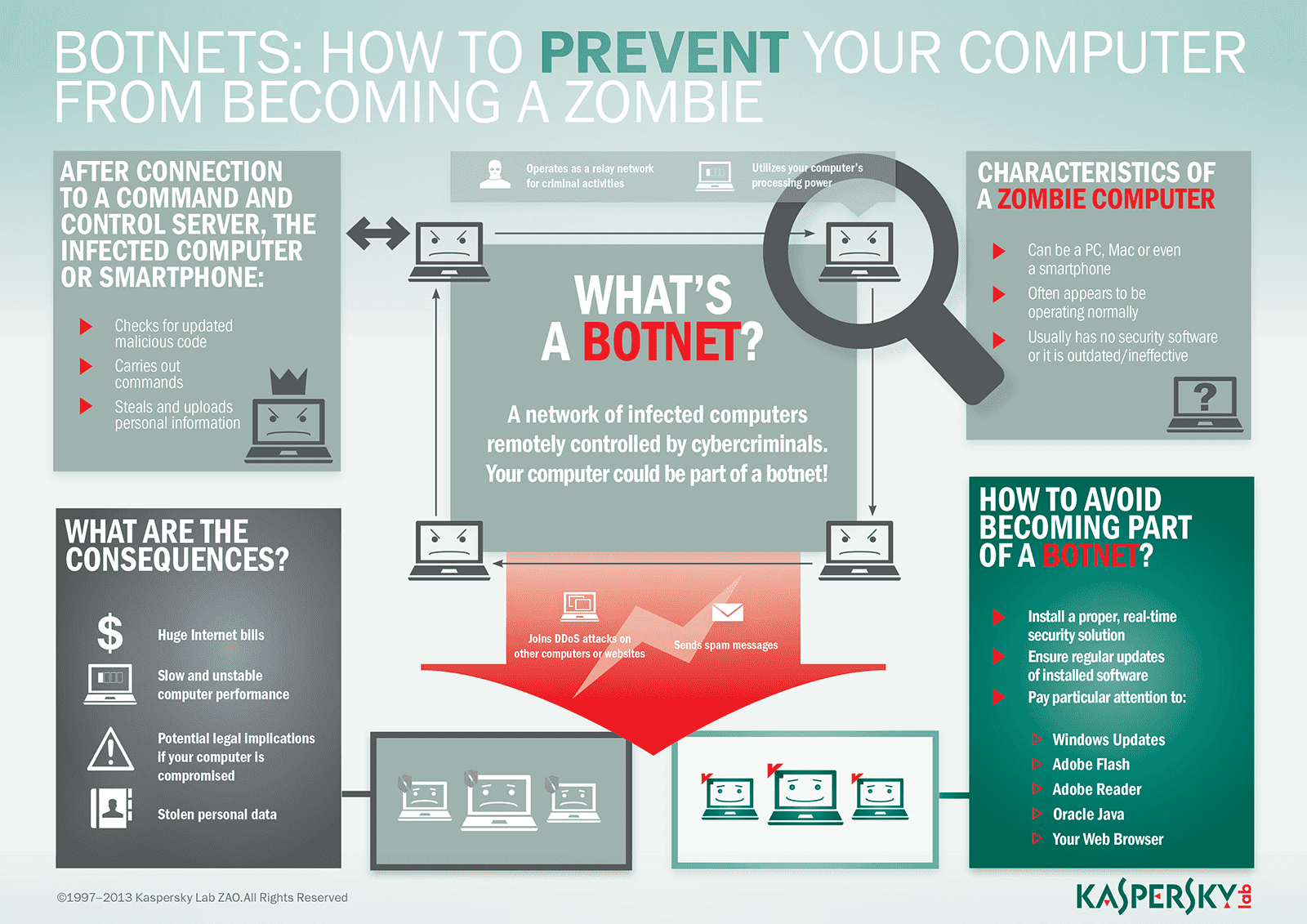
What is Kad Nap?
Kad Nap is a botnet that currently infects approximately 14,000 routers daily, with a significant concentration in Asus devices. It leverages existing vulnerabilities in router firmware, which many users neglect to patch. This negligence creates an opportunity for the botnet to thrive.
How It Works
Kad Nap takes advantage of known vulnerabilities in router firmware. Once inside, it turns these routers into proxies, rerouting traffic to mask the true origin of cybercriminal activities.
Key Characteristics of Kad Nap:
- Decentralized Control: The botnet operates without a central command, making it tougher to dismantle.
- Proxy Usage: Primarily used to anonymize traffic for cybercriminals.
- Persistent Infection: Remains active even after attempts to remove it.

Firmware updates are the most effective measure against botnets, followed by using strong passwords. Estimated data based on typical security practices.
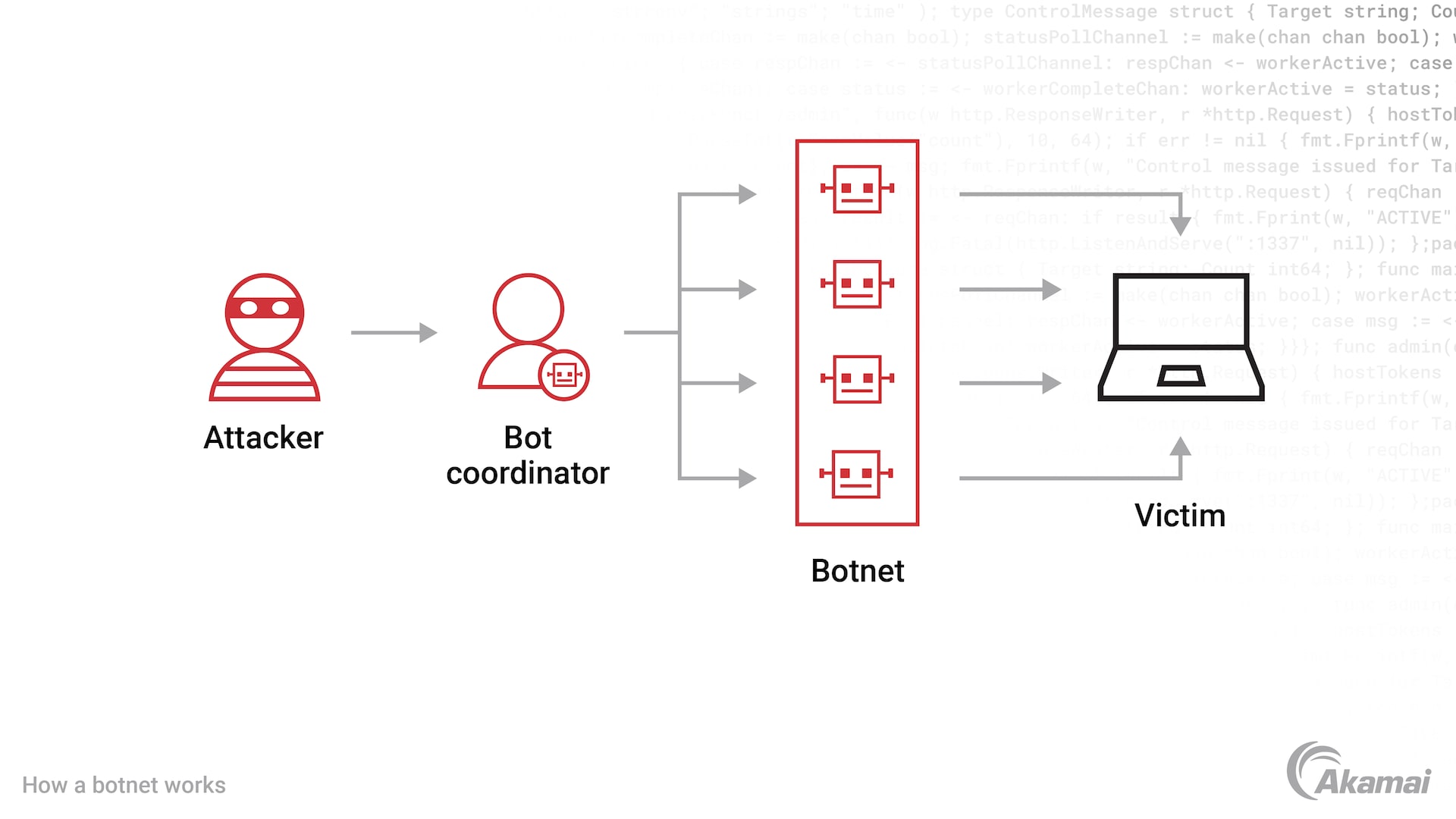
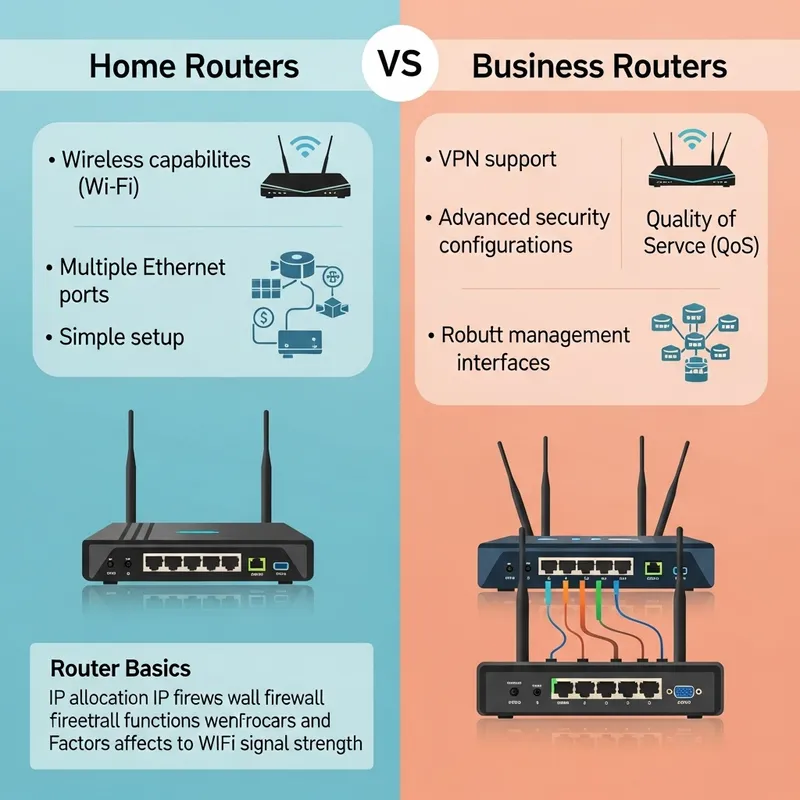
The Anatomy of a Router Botnet
Understanding how a botnet like Kad Nap infiltrates and operates can provide insights into prevention and mitigation.
Vulnerability Exploitation
Routers often come with firmware that users rarely update. Kad Nap exploits this weakness, targeting known vulnerabilities in the firmware of Asus routers.
Infection Process
- Scanning: The botnet scans for routers with open ports and outdated firmware.
- Exploitation: It uses known exploits to gain access.
- Deployment: Installs the malware, turning the router into a botnet node.
Command and Control
Unlike traditional botnets, Kad Nap uses a peer-to-peer architecture, where each infected device communicates with others, sharing updates and instructions.

Protecting Your Network
Best Practices
- Regular Firmware Updates: Keep your router's firmware up-to-date to close vulnerabilities.
- Strong Passwords: Use complex passwords and change them regularly.
- Network Segmentation: Separate your network to limit exposure.
Implementation Guide
- Step 1: Log into your router's admin panel.
- Step 2: Check for firmware updates and apply them.
- Step 3: Change default login credentials.
- Step 4: Disable remote management unless necessary.
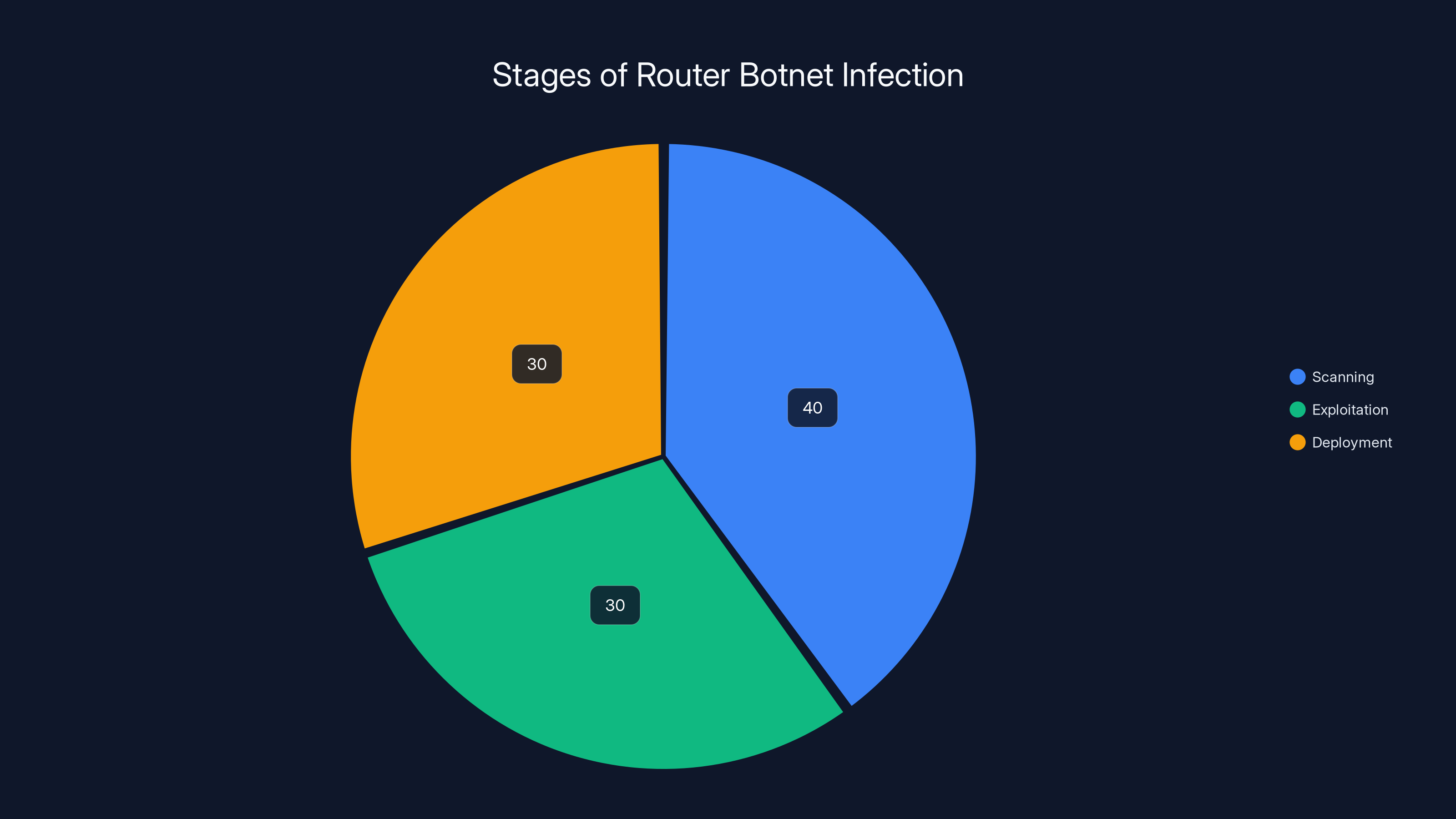
The scanning stage takes up the largest portion of time in KadNap's infection process, highlighting the importance of securing open ports. (Estimated data)
Common Pitfalls and Solutions
Neglecting Updates
Many users ignore firmware updates, assuming their routers are secure out of the box. Solution: Set reminders to check for updates monthly.
Weak Passwords
Using simple or default passwords makes it easy for botnets to gain access. Solution: Use password managers to generate and store strong passwords.
Future Trends in Router Security
As the Internet of Things (Io T) expands, more devices will connect to home networks, increasing potential targets for botnets like Kad Nap.
Predictions
- Increased Targeting: More connected devices mean more opportunities for infection.
- Enhanced Security Measures: Manufacturers will likely implement better security features in routers.

The Bigger Picture
Router botnets like Kad Nap are a wake-up call for both manufacturers and consumers. While manufacturers need to prioritize security in their devices, consumers must take an active role in securing their networks.
Long-Term Recommendations
- Education: Increase awareness about router security among consumers.
- Collaboration: Encourage collaboration between cybersecurity firms and manufacturers to develop robust security protocols.
Conclusion
Kad Nap's resilience highlights a broader issue in network security. By understanding how these botnets operate and taking proactive steps, you can protect your network from falling prey to such threats.

FAQ
What is Kad Nap?
Kad Nap is a botnet that infects routers, primarily Asus models, using known firmware vulnerabilities to create a network that anonymizes cybercrime traffic.
How does Kad Nap work?
Kad Nap exploits unpatched vulnerabilities to gain control of routers, turning them into nodes within a decentralized proxy network.
What are the benefits of securing my router?
Securing your router prevents unauthorized access, reduces the risk of becoming part of a botnet, and protects your personal information.
How can I protect my router from botnets?
Regularly update your router's firmware, use strong passwords, and disable unnecessary features like remote management.
What future trends should I be aware of regarding botnets?
With the rise of Io T, expect more targets for botnets. However, enhanced security measures and consumer awareness can mitigate these threats.
Why are Asus routers specifically targeted by Kad Nap?
Asus routers are often targeted due to the availability of reliable exploits for their firmware vulnerabilities.
Key Takeaways
- KadNap infects approximately 14,000 routers daily, primarily Asus models.
- The botnet exploits unpatched firmware vulnerabilities to operate.
- Regular firmware updates and strong passwords are critical defenses.
- The decentralized nature of KadNap makes it resistant to takedowns.
- As IoT expands, more devices may become targets for botnets.
- Consumer education is vital in preventing router-based cyber threats.
Related Articles
- Asus Routers Hijacked to Power a Cybercrime Proxy Network: What We Know [2025]
- Unmasking BlackSanta: The Malware Targeting HR Departments [2025]
- The $30 Malware Threat: How Ancient Visual Basic Powers Modern Cybercrime [2025]
- WhatsApp Introduces Parent-Linked Accounts for Pre-Teens: A Comprehensive Guide [2025]
- How Meta is Fighting Back Against Scammers with Advanced Technology [2025]
- Meta's New Scam Protection Features: Safeguarding Users in 2025
![The Rise of KadNap: Understanding and Combating a Resilient Router Botnet [2025]](https://tryrunable.com/blog/the-rise-of-kadnap-understanding-and-combating-a-resilient-r/image-1-1773264855592.jpg)



