Trump’s Cyber Strategy: A New Era for U.S. Cyber Power [2025]
Last month, the United States took a significant step forward in its approach to cybersecurity. President Donald Trump unveiled his administration's comprehensive National Cyber Strategy, a blueprint designed to fortify America's presence in the digital realm. The strategy is not just about defending the nation's critical infrastructure but also about leveraging offensive capabilities to deter adversaries. This article delves into the strategic pillars of the plan, its implementation roadmap, and its potential impact on both national security and global cyber dynamics.
TL; DR
- Strategic Pillars: The strategy outlines six key pillars focusing on defense, offense, innovation, and international cooperation.
- Offensive Capabilities: Emphasizes the use of offensive cyber operations to deter and respond to threats.
- Regulatory Streamlining: Aims to reduce bureaucratic hurdles, fostering innovation and collaboration between public and private sectors.
- Global Alliances: Strengthens ties with international partners to combat global cyber threats.
- Future-Proofing: Plans to adapt technologically and strategically to future cyber challenges.
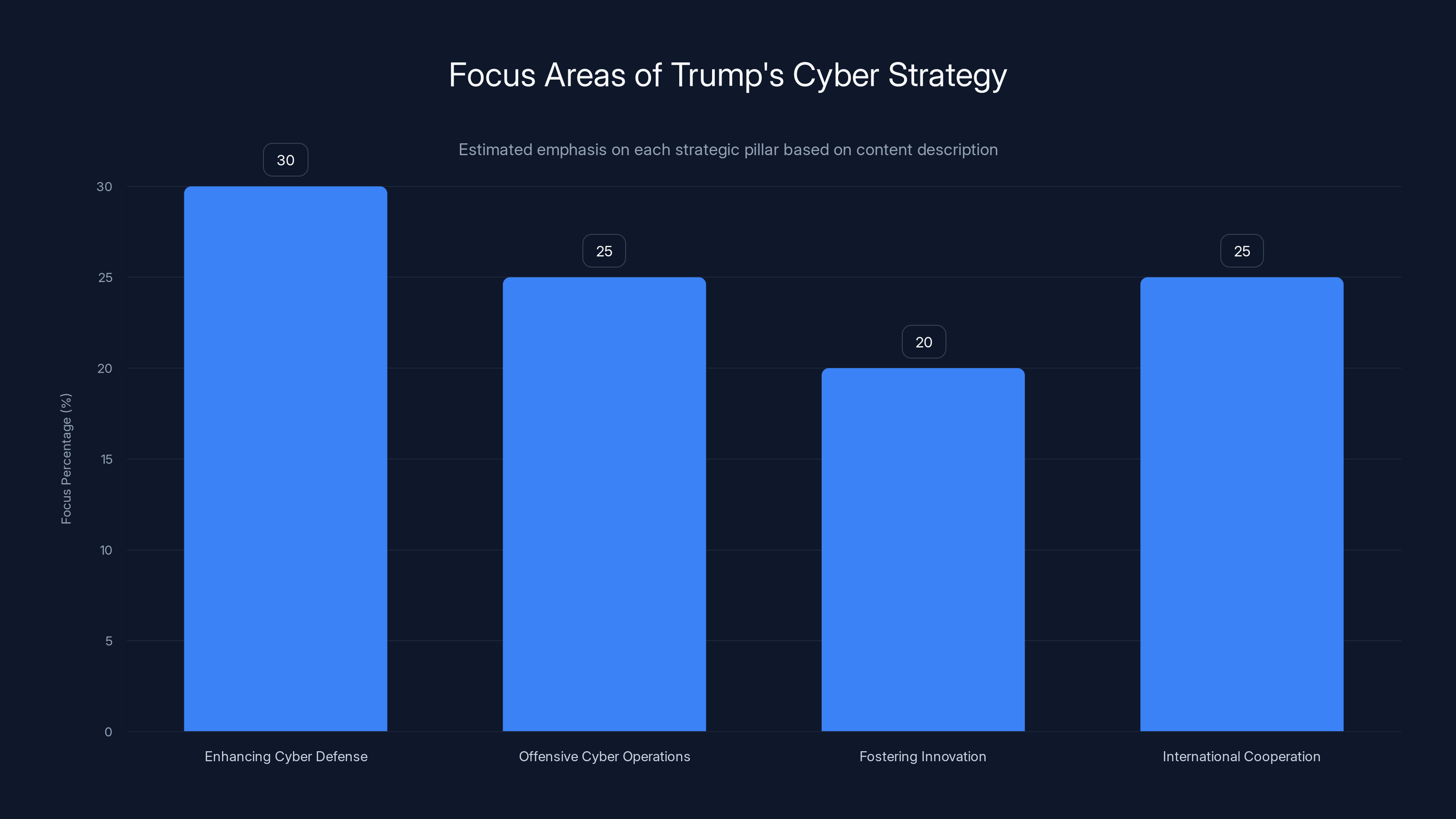
Estimated data shows a balanced focus across the strategic pillars, with a slight emphasis on enhancing cyber defense and international cooperation.
The Six Strategic Pillars
Trump’s cyber strategy is built on six foundational pillars, each addressing a unique aspect of the nation's cyber posture:
1. Enhancing Cyber Defense
The first pillar underscores the importance of strengthening the nation’s cyber defenses. This involves bolstering the security of critical infrastructure such as power grids, financial systems, and communication networks. The strategy proposes the use of advanced technologies like AI and machine learning to detect and neutralize threats in real-time.
Key Initiatives:
- AI-Driven Defense Systems: Deploying AI to predict and mitigate attacks before they materialize.
- Public-Private Partnerships: Collaborating with private tech companies to leverage cutting-edge security solutions.
2. Offensive Cyber Operations
In a departure from previous strategies, this plan explicitly discusses the deployment of offensive cyber operations. By developing a robust offensive capability, the U.S. aims to deter adversaries and retaliate against cyber aggressions effectively. According to Nextgov, this approach marks a significant shift in U.S. cyber policy.
Examples of Offensive Operations:
- Ransomware Dissolution: Targeting and dismantling ransomware infrastructure.
- State-Sponsored Hack Deterrence: Conducting counter-operations against state-sponsored cyber threats.
3. Fostering Innovation and Resilience
A significant focus is placed on fostering innovation within the cybersecurity sector. The strategy pushes for reduced regulatory burdens and encourages the development of new technologies. As noted by Palo Alto Networks, this is crucial for maintaining a competitive edge in cybersecurity.
Innovation Strategies:
- Cyber Sandboxes: Creating safe environments for testing new cyber defenses.
- Incentives for Startups: Offering grants and tax incentives for cybersecurity startups.
4. International Cooperation
Acknowledging that cyber threats are global, the strategy calls for stronger international alliances. Sharing intelligence and resources with allies is seen as crucial for a comprehensive defense posture. Industrial Cyber highlights the importance of these alliances in enhancing global cybersecurity efforts.
International Collaboration Efforts:
- Joint Cyber Exercises: Conducting regular cyber drills with NATO allies.
- Global Cyber Threat Intelligence Sharing: Establishing platforms for real-time threat information exchange.
5. Workforce Development
Recognizing the need for a skilled workforce, the strategy emphasizes education and training in cybersecurity. This includes initiatives to integrate cybersecurity education into school curricula and provide reskilling programs for adults. Cybersecurity Dive reports that these initiatives are critical for building a robust cybersecurity workforce.
Workforce Initiatives:
- Cybersecurity Education Grants: Funding programs for cybersecurity degrees and certifications.
- Retraining Programs: Offering training for transitioning workers into cybersecurity roles.
6. Adaptive Security Posture
The final pillar focuses on maintaining an adaptive security posture. The strategy is designed to evolve with emerging threats and technological advancements. As detailed by CyberScoop, this adaptability is essential for staying ahead of potential cyber threats.
Adaptive Measures:
- Continuous Threat Analysis: Regularly updating threat models based on the latest intelligence.
- Dynamic Policy Adjustments: Flexibly adapting policies to address new cyber challenges.
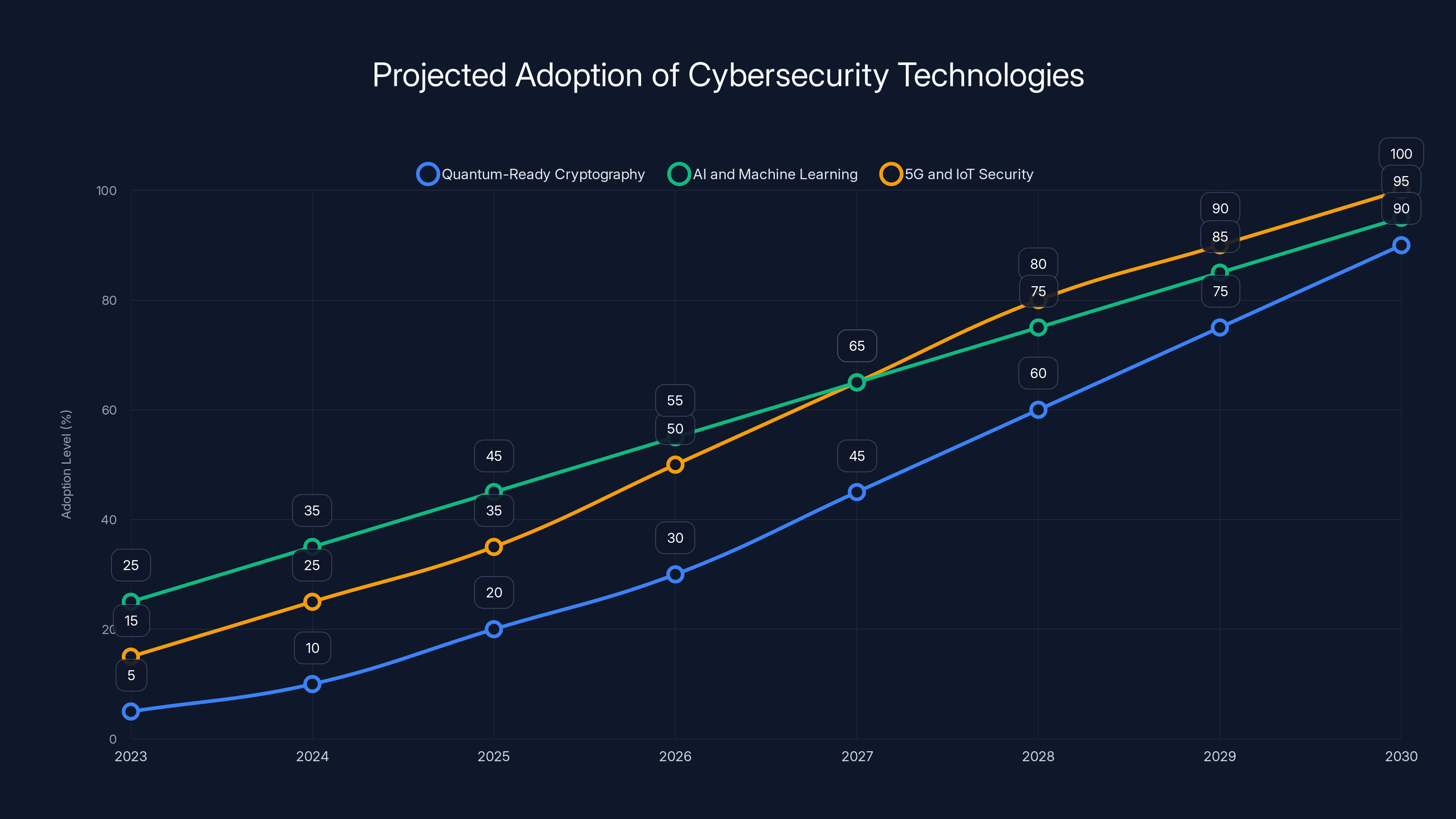
The adoption of quantum-ready cryptography, AI, and IoT security is projected to grow significantly by 2030, with AI reaching near-universal integration. Estimated data.
Implementing the Strategy: A Practical Guide
Implementation of the cyber strategy requires a coordinated effort across multiple sectors. Here’s how it can be practically rolled out:
Government and Military
- Centralized Command: Establish a centralized cyber command responsible for both defensive and offensive operations.
- Interagency Collaboration: Foster collaboration between various government agencies to streamline cyber efforts.
Private Sector
- Security Audits: Conduct regular security audits of infrastructure operated by private entities.
- Technology Transfer: Encourage the transfer of innovative technologies from private companies to government use.
Education and Workforce
- Curriculum Development: Develop standardized cybersecurity curricula for schools and universities.
- Certification Programs: Promote industry-recognized certification programs to ensure workforce readiness.

Common Pitfalls and Solutions
While the strategy is ambitious, several pitfalls must be addressed:
- Resource Allocation: Ensuring adequate funding and resources are available for implementation.
- Bureaucratic Hurdles: Streamlining processes to avoid delays in policy execution.
- Public-Private Trust: Building trust between public and private sectors to facilitate collaboration.
Solutions:
- Dedicated Funding Streams: Establish dedicated funding channels for cyber initiatives.
- Cross-Sector Committees: Form committees with members from both sectors to oversee implementation.
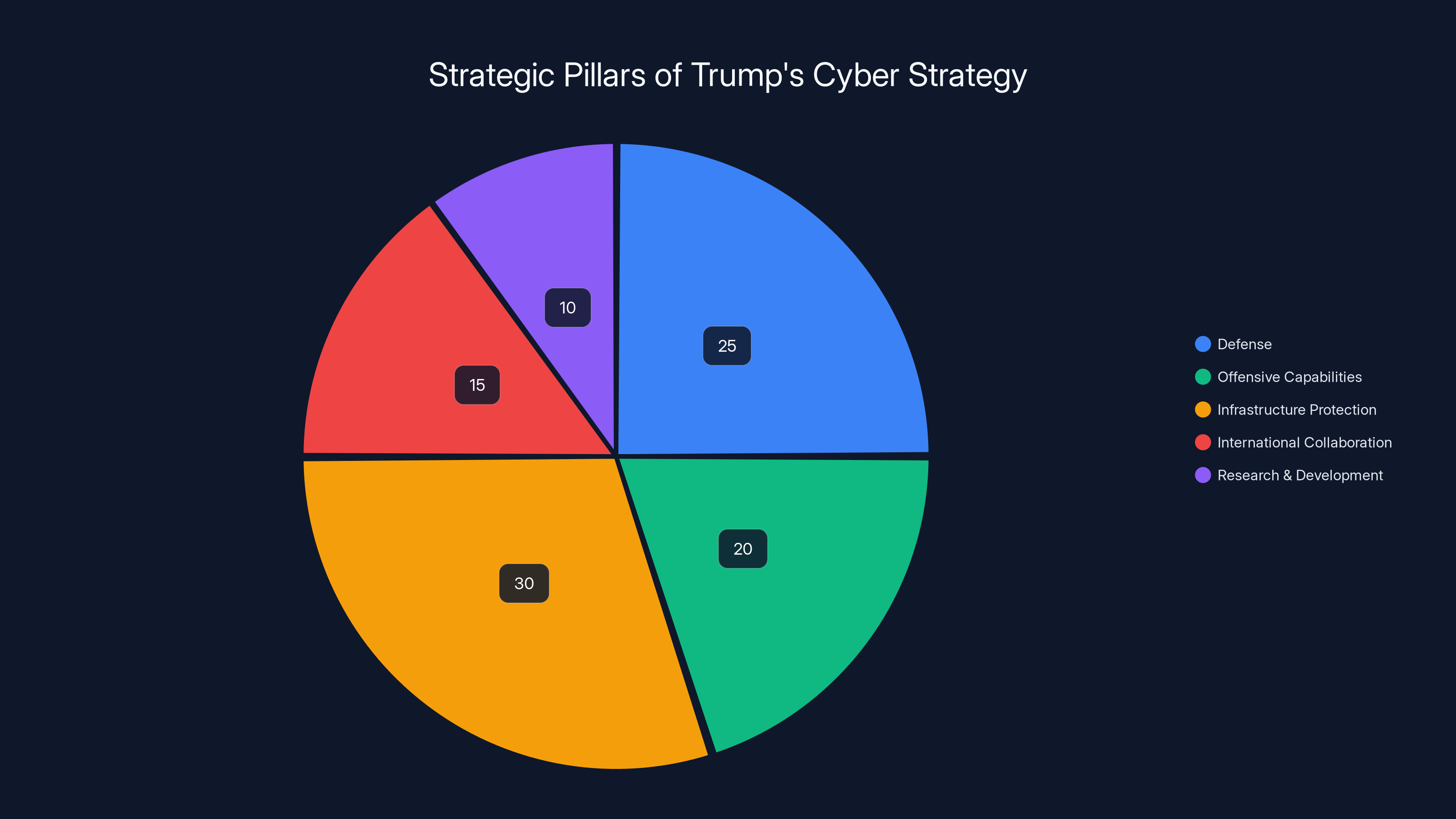
The 2025 National Cyber Strategy emphasizes infrastructure protection (30%) and defense (25%), with significant attention to offensive capabilities (20%). Estimated data.
Future Trends and Recommendations
Looking ahead, several future trends will shape the cyber landscape:
Quantum Computing
Quantum computing poses both opportunities and threats to cybersecurity. The strategy should prepare for quantum-resistant cryptography and leverage quantum capabilities for enhanced security.
AI and Machine Learning
AI will continue to be a central component of cyber strategies. Future iterations of the strategy should focus on integrating AI for predictive threat analysis and autonomous defense mechanisms.
5G and IoT
The proliferation of 5G and IoT devices presents new security challenges. The strategy should incorporate specific measures to secure these technologies.
Recommendations:
- Quantum-Ready Cryptography: Invest in research for quantum-safe encryption methods.
- AI Integration Frameworks: Develop frameworks for integrating AI into existing cybersecurity infrastructures.
Conclusion
Trump’s National Cyber Strategy marks a bold step towards securing America’s digital future. By focusing on both defense and offense, fostering innovation, and enhancing international cooperation, the strategy aims to establish the U.S. as a dominant cyber power. As the strategy unfolds, its success will depend on effective implementation and the ability to adapt to an ever-evolving cyber landscape.

FAQ
What is the main goal of Trump's Cyber Strategy?
The main goal is to enhance the U.S. cyber defense and offense capabilities, ensuring national security in the digital realm.
How does the strategy propose to use offensive cyber operations?
By developing robust offensive capabilities to deter and respond to cyber threats effectively, targeting adversaries’ infrastructures.
What role does international cooperation play in the strategy?
International cooperation is crucial for sharing intelligence and conducting joint cyber exercises to combat global threats.
How does the strategy aim to foster innovation?
By reducing regulatory burdens and providing incentives for cybersecurity startups and innovations.
What are the workforce development initiatives in the strategy?
The strategy emphasizes cybersecurity education and training, offering grants for degrees and certifications.
What future trends should the strategy address?
The strategy should address quantum computing, AI integration, and the security challenges posed by 5G and IoT.
Key Takeaways
- Strategic pillars enhance defense, offense, and innovation.
- Offensive cyber operations deter adversaries effectively.
- Regulatory streamlining fosters public-private collaboration.
- International cooperation strengthens global cyber defenses.
- Adaptation to future technologies is crucial for strategy success.
Related Articles
- Inside the FBI's Cybersecurity Breach: Unraveling the Hijacking of Wiretaps and Search Warrants [2025]
- OpenAI's Acquisition of Promptfoo: Securing AI Agents for the Future [2025]
- Understanding the Conflict: Anthropic's Legal Battle with the Defense Department [2025]
- Understanding the Threat: Russian Hackers Target Signal and WhatsApp Users [2025]
- Understanding ClickFix Attacks: How Hackers Target Windows Terminal for Malware [2025]
- Unveiling the Mysteries of Alien Files: What to Really Expect [2025]
![Trump's Cyber Strategy: A New Era for U.S. Cyber Power [2025]](https://tryrunable.com/blog/trump-s-cyber-strategy-a-new-era-for-u-s-cyber-power-2025/image-1-1773084899804.jpg)



