Understanding the Threat: Russian Hackers Target Signal and WhatsApp Users [2025]
Last month, a senior journalist received an alarming message on Signal. It claimed to be from the app's support team, warning of suspicious activity on his account. The message seemed legitimate, asking for a verification code to secure his account. Unbeknownst to him, he was the target of a sophisticated phishing attempt orchestrated by Russian government-backed hackers.
TL; DR
- Russian hackers are targeting Signal and WhatsApp using phishing techniques and social engineering.
- Government officials, military personnel, and journalists are the primary targets.
- Hackers pose as support teams to deceive users into sharing verification codes.
- Dutch intelligence agencies have exposed a global hacking campaign.
- User vigilance and enhanced security measures are necessary to mitigate these threats.
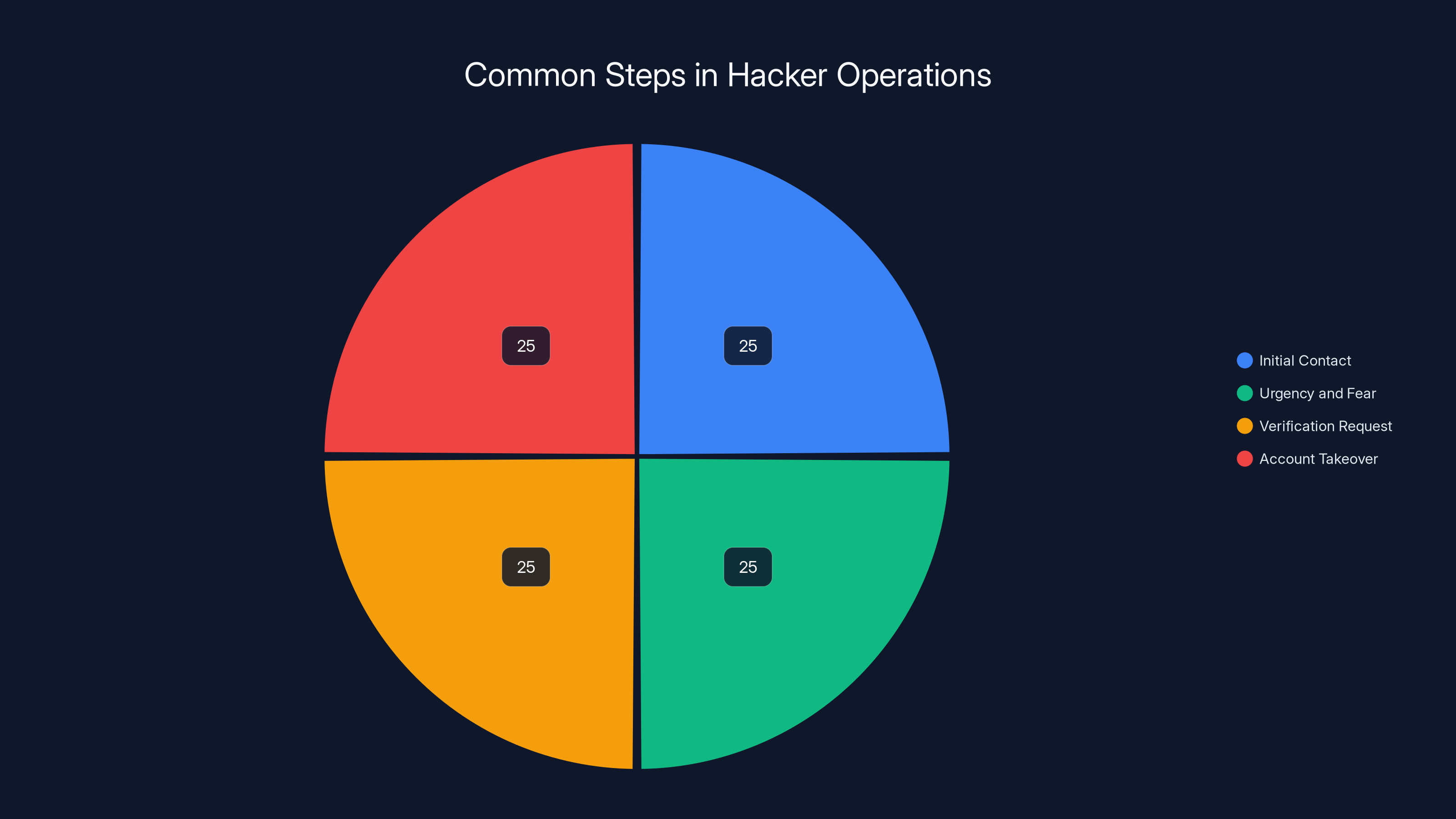
Each step in a typical hacking operation is estimated to require equal effort, highlighting the systematic approach hackers use. Estimated data.
Introduction
The rise in cyber threats from state-sponsored actors has reshaped the global security landscape. Recently, Dutch intelligence agencies warned about Russian government hackers targeting users of secure messaging apps like Signal and WhatsApp. This article delves into the details of this threat, exploring the techniques used, the implications for users, and the measures needed to protect against such attacks.
The Tactics of Targeted Attacks
Russian hackers are known for their sophisticated strategies, and their latest campaign leverages both phishing and social engineering. Unlike traditional malware attacks, these methods rely on human error, making them particularly insidious.
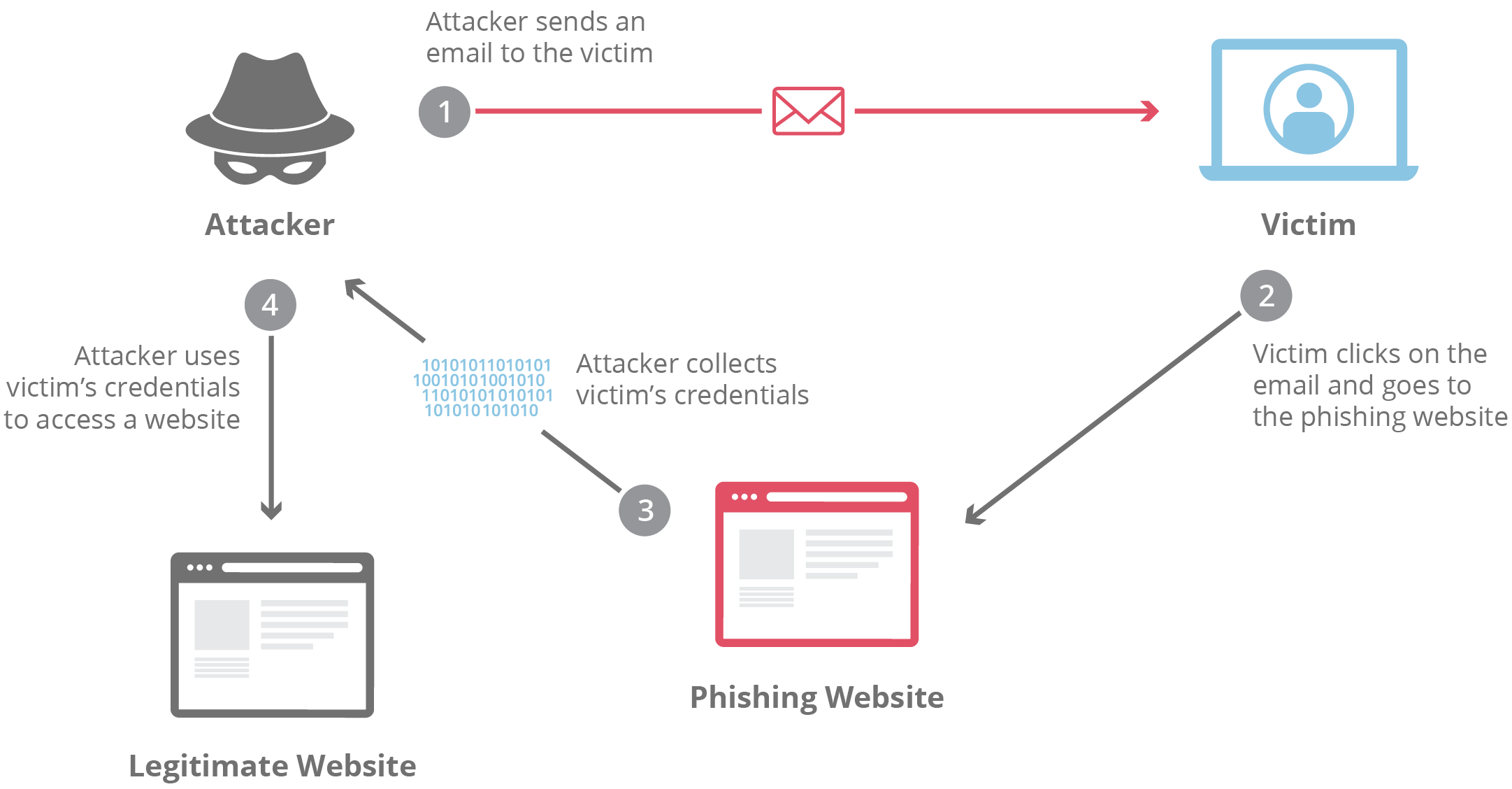
Phishing Techniques
Phishing is a form of cyberattack where attackers impersonate trusted entities to steal sensitive information. In this case, hackers pose as support staff from messaging apps, sending messages that prompt users to share their verification codes. These codes, once obtained, allow hackers to take over the victim's account. According to Simplilearn, phishing is one of the most common types of cyberattacks.
Social Engineering Exploits
Social engineering involves manipulating individuals into divulging confidential information. Hackers exploit trust by crafting messages that appear urgent and legitimate. For instance, they might claim there is a security threat or a data leak, prompting users to act quickly without verifying the message's authenticity. Tech Times highlights the importance of recognizing these tactics to prevent falling victim to scams.

Phishing and social engineering are the most common tactics used in targeted attacks, accounting for 65% of the methods employed by hackers. (Estimated data)
Targeted Demographics
The primary targets of these attacks include:
- Government Officials: Accessing sensitive communications could provide valuable intelligence.
- Military Personnel: Information from military communications can be strategically advantageous.
- Journalists: Gaining access to journalists' accounts can help control narratives and suppress information.
Case Study: A Journalist's Ordeal
Consider Sarah, an investigative journalist covering political corruption. She received a message on WhatsApp claiming to be from the app's security team, warning her of unusual login attempts. In a panic, Sarah shared her verification code, and within minutes, her account was compromised. Sensitive sources and communications were at risk, demonstrating the potential fallout from such breaches.

How Hackers Operate
Understanding the modus operandi of these hackers is crucial for defense. The process generally follows these steps:
- Initial Contact: The hacker sends a message impersonating the app's support team.
- Urgency and Fear: The message creates a sense of urgency, such as a security breach.
- Verification Request: The user is asked to provide a verification code sent via SMS.
- Account Takeover: With the code, hackers gain access to the account.
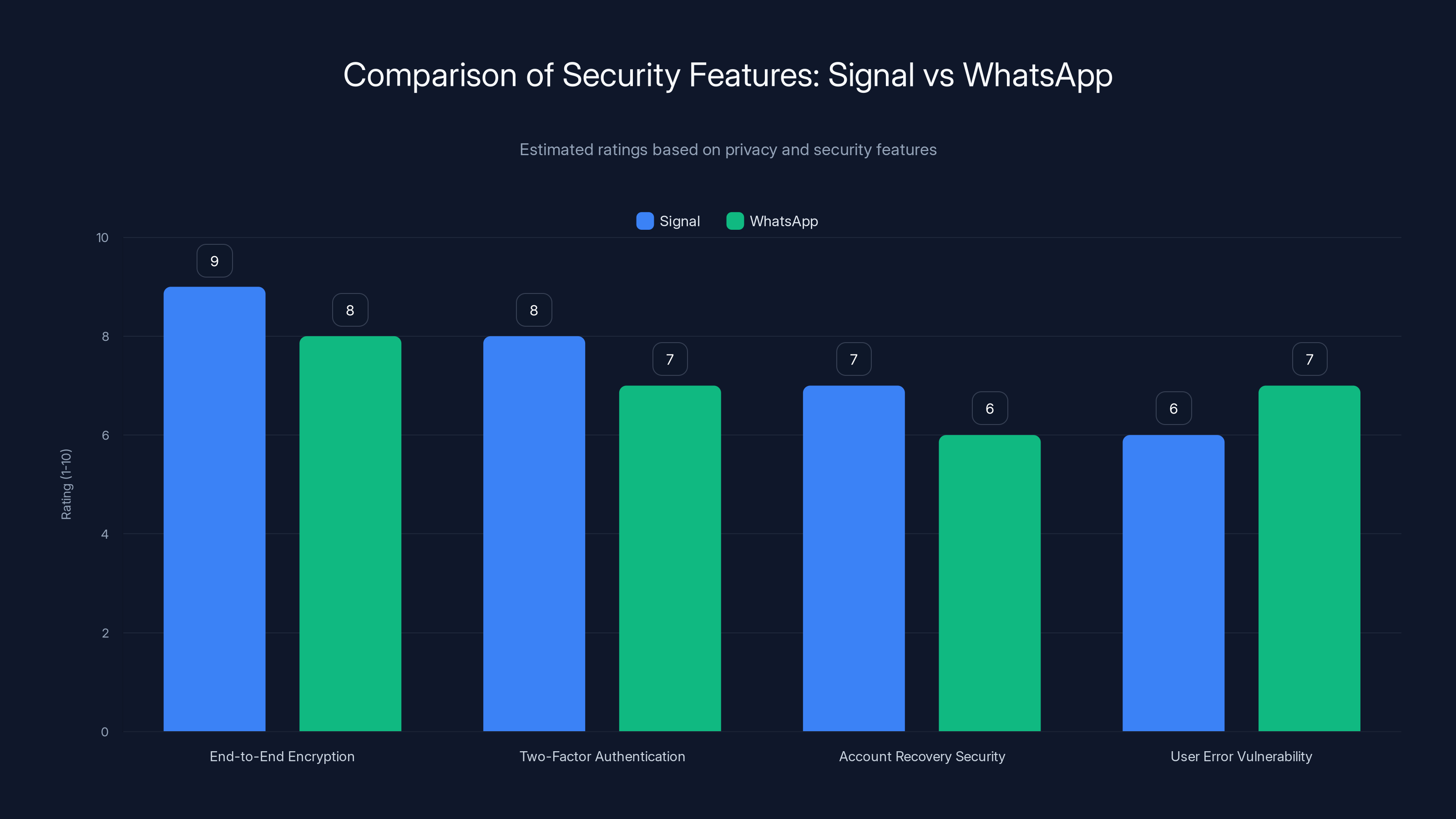
Signal generally scores higher in end-to-end encryption and account recovery security, while both apps are vulnerable to user error in 2FA. Estimated data based on typical feature assessments.
Technical Insights
Why Signal and WhatsApp?
Both Signal and WhatsApp are end-to-end encrypted messaging platforms, known for their privacy and security features. However, the security of these apps can be undermined if hackers gain access through user error. Help Net Security discusses how these platforms are targeted due to their widespread use and perceived security.
Exploiting Two-Factor Authentication (2FA)
Two-factor authentication is a security measure that requires users to provide two forms of verification. Hackers exploit this system by tricking users into sharing their second factor, usually a code sent via SMS. The Record reports on similar phishing campaigns targeting government officials and journalists.
Bypassing Account Recovery
Once hackers gain access, they may alter recovery options, making it difficult for the rightful owner to regain control. This often involves changing associated email addresses or phone numbers.
Best Practices for Users
To safeguard against these threats, users should adopt the following best practices:
- Verify Messages: Always verify the legitimacy of messages claiming to be from support teams.
- Enable 2FA: Use two-factor authentication and never share authentication codes.
- Educate Yourself: Stay informed about common phishing tactics and how to recognize them.
- Use Strong Passwords: Ensure your passwords are complex and unique.
Quick Tips for Enhanced Security
Common Pitfalls and Solutions
Despite best efforts, users can still fall victim to these attacks. Here are some common pitfalls and how to address them:
Falling for Fake Support Messages
Solution: Cross-check with official support channels before responding to suspicious messages.
Sharing Verification Codes
Solution: Never share verification codes with anyone, even if the request seems legitimate.
Delayed Response to Account Changes
Solution: Act immediately if you receive notifications of account changes you did not authorize.
Future Trends in Cybersecurity
As cyber threats evolve, so too must our defenses. Here are some trends to watch:
- Advanced Phishing Detection: AI-driven tools that detect phishing attempts in real-time could become standard.
- Biometric Authentication: Beyond passwords and codes, biometric data may offer more secure verification.
- Decentralized Storage: Storing sensitive data in decentralized networks could reduce the impact of breaches. Britannica discusses the potential of decentralized storage in enhancing data security.
Recommendations for Organizations
Organizations can implement these strategies to bolster security:
- Regular Training: Conduct regular cybersecurity training for employees, focusing on phishing and social engineering.
- Incident Response Plans: Develop and maintain incident response plans to quickly address breaches.
- Collaborate with Experts: Work with cybersecurity experts to assess vulnerabilities and strengthen defenses.
Conclusion
The threat from Russian government hackers targeting Signal and WhatsApp users underscores the importance of vigilance in digital communication. By understanding the tactics employed and implementing robust security measures, users and organizations can better protect themselves from these sophisticated attacks.
FAQ
What are Russian hackers targeting Signal and WhatsApp users?
Russian government-backed hackers are targeting users of Signal and WhatsApp through phishing and social engineering tactics to gain unauthorized access to accounts.
How do Russian hackers conduct these attacks?
Hackers pose as support teams, sending messages that prompt users to share verification codes, enabling them to take over accounts.
Who are the primary targets of these attacks?
The primary targets include government officials, military personnel, and journalists, as these groups often handle sensitive information.
How can users protect themselves from these threats?
Users can protect themselves by verifying messages, enabling two-factor authentication, staying informed about phishing tactics, and using strong passwords.
What measures can organizations take to enhance cybersecurity?
Organizations should conduct regular cybersecurity training, develop incident response plans, and collaborate with experts to assess and strengthen security defenses.
What are the future trends in cybersecurity?
Future trends include advanced phishing detection, biometric authentication, and decentralized storage to enhance security against evolving threats.
Key Takeaways
- Russian hackers use phishing and social engineering to target Signal and WhatsApp users.
- Government officials, military personnel, and journalists are the primary targets.
- Hackers impersonate support teams to deceive users into sharing verification codes.
- Dutch intelligence agencies have revealed a global hacking campaign.
- User vigilance and enhanced security measures are crucial for protection.
Related Articles
- Understanding ClickFix Attacks: How Hackers Target Windows Terminal for Malware [2025]
- Understanding Phishing Campaigns: How Fake Email Chains Exploit Urgency [2025]
- CBP Used Online Ad Data to Track Phone Locations | WIRED
- How to Watch Top Chef Season 23 Online from Anywhere [2025]
- How One Man's Accidental Hack Revealed Vulnerabilities in Modern Robotics [2025]
- Unmasking Grammarly: Identity Concerns and the Future of AI Writing Assistance [2025]
![Understanding the Threat: Russian Hackers Target Signal and WhatsApp Users [2025]](https://tryrunable.com/blog/understanding-the-threat-russian-hackers-target-signal-and-w/image-1-1773072306664.jpg)



