Understanding Click Fix Attacks: How Hackers Target Windows Terminal for Malware [2025]
Last month, Microsoft sent shockwaves through the tech community when it revealed a new frontier in the world of cyber threats—Click Fix attacks targeting Windows Terminal. If you think about it, the audacity and creativity of cybercriminals are both impressive and terrifying. They’ve moved beyond the conventional, wreaking havoc by leveraging Windows Terminal instead of the traditional Run program. So, what does this mean for you and the security of your systems? Let’s dive deep.
TL; DR
- Click Fix Attacks: Cybercriminals are now targeting Windows Terminal instead of Run to trick users into installing malware, as noted by The Hacker News.
- Lumma Stealer Malware: This malware can compromise sensitive information and is part of the current Click Fix campaigns, as detailed in Qualys' research.
- Evolving Tactics: The Click Fix method is evolving, signaling a need for updated security protocols, according to Cybersecurity News.
- Protection Measures: Regular updates, awareness training, and advanced security tools are vital.
- Future Trends: Expect more sophisticated attacks leveraging overlooked system components, as projected by Cyble.
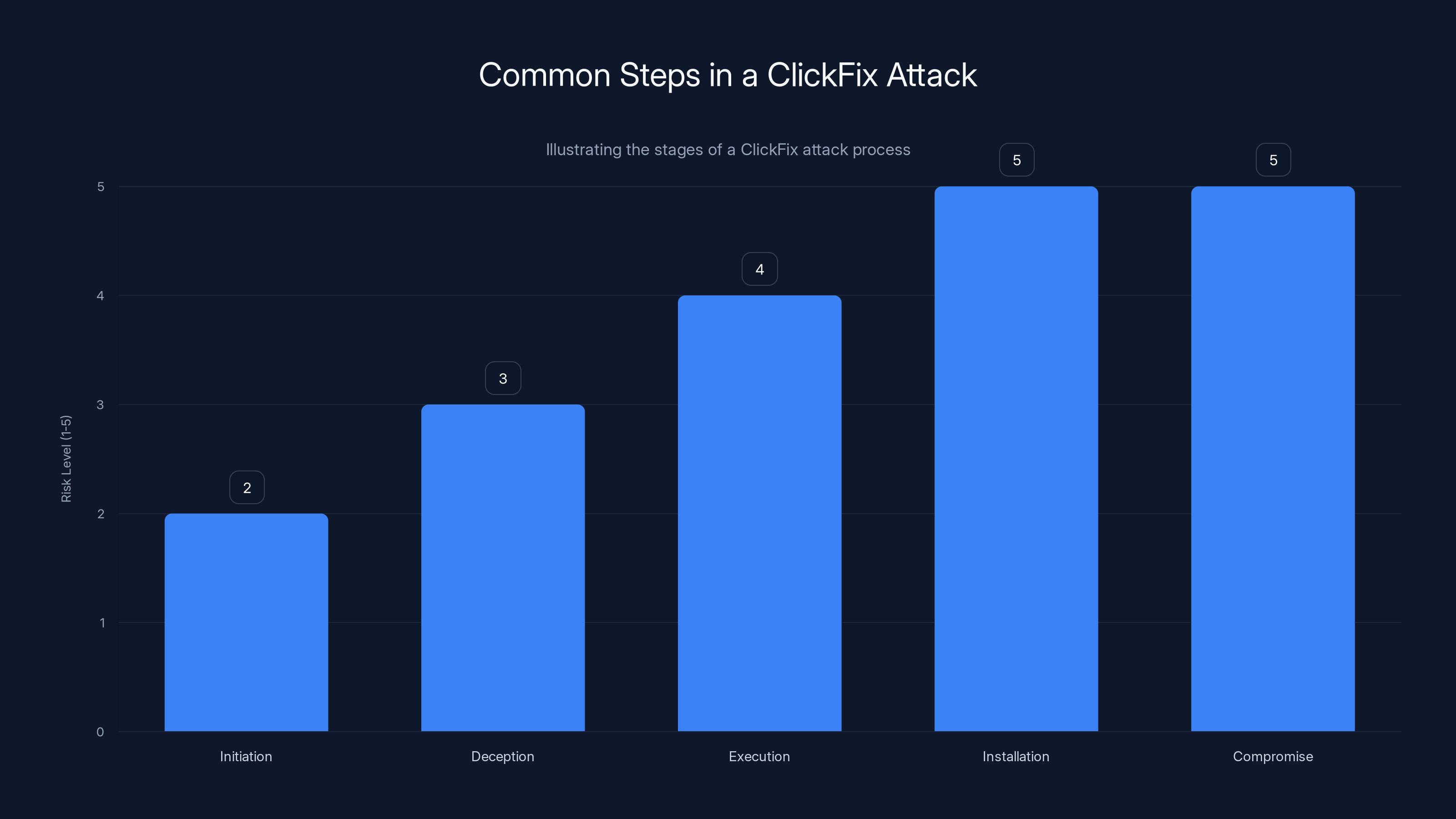
The risk level increases significantly from initiation to compromise, with the highest risk during installation and compromise stages. Estimated data.
What Are Click Fix Attacks?
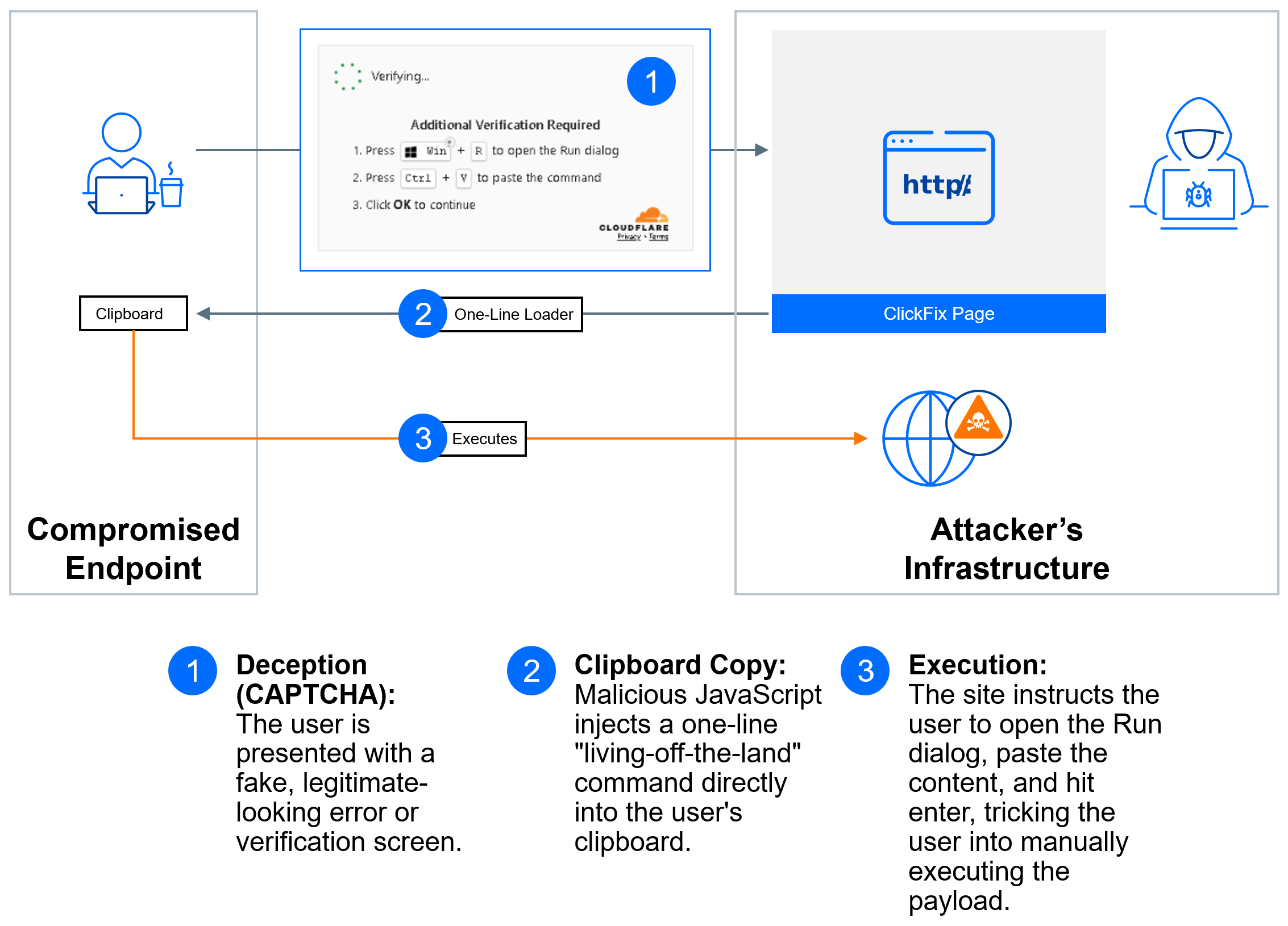
At its core, a Click Fix attack is a sophisticated form of social engineering designed to exploit human psychology rather than technical vulnerabilities. The attackers create fake warnings that look legitimate, urging users to click on a link or download a program to fix a nonexistent issue. Historically, these attacks manipulated the Windows Run feature, but now they target the Windows Terminal, as explained by SecurityWeek.
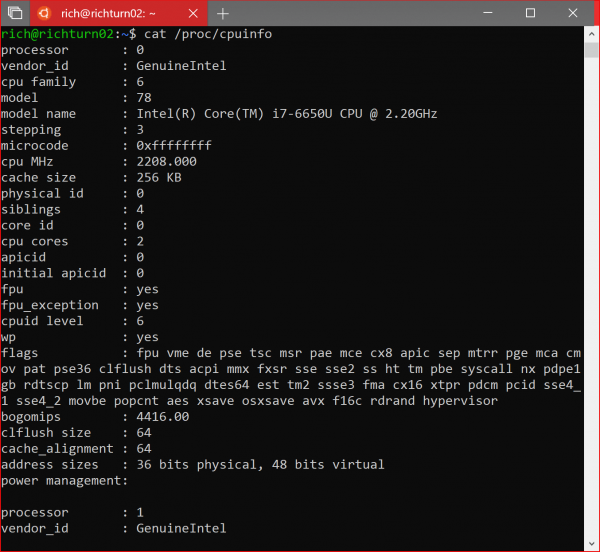
Why Windows Terminal?
Windows Terminal is a command-line interface tool that’s gaining popularity for its flexibility and power. Unlike Windows Run, which is more commonly associated with launching programs, Terminal allows for intricate command execution. This makes it a more lucrative target for attackers because it can be used to execute scripts and commands silently, as noted by Computerworld.
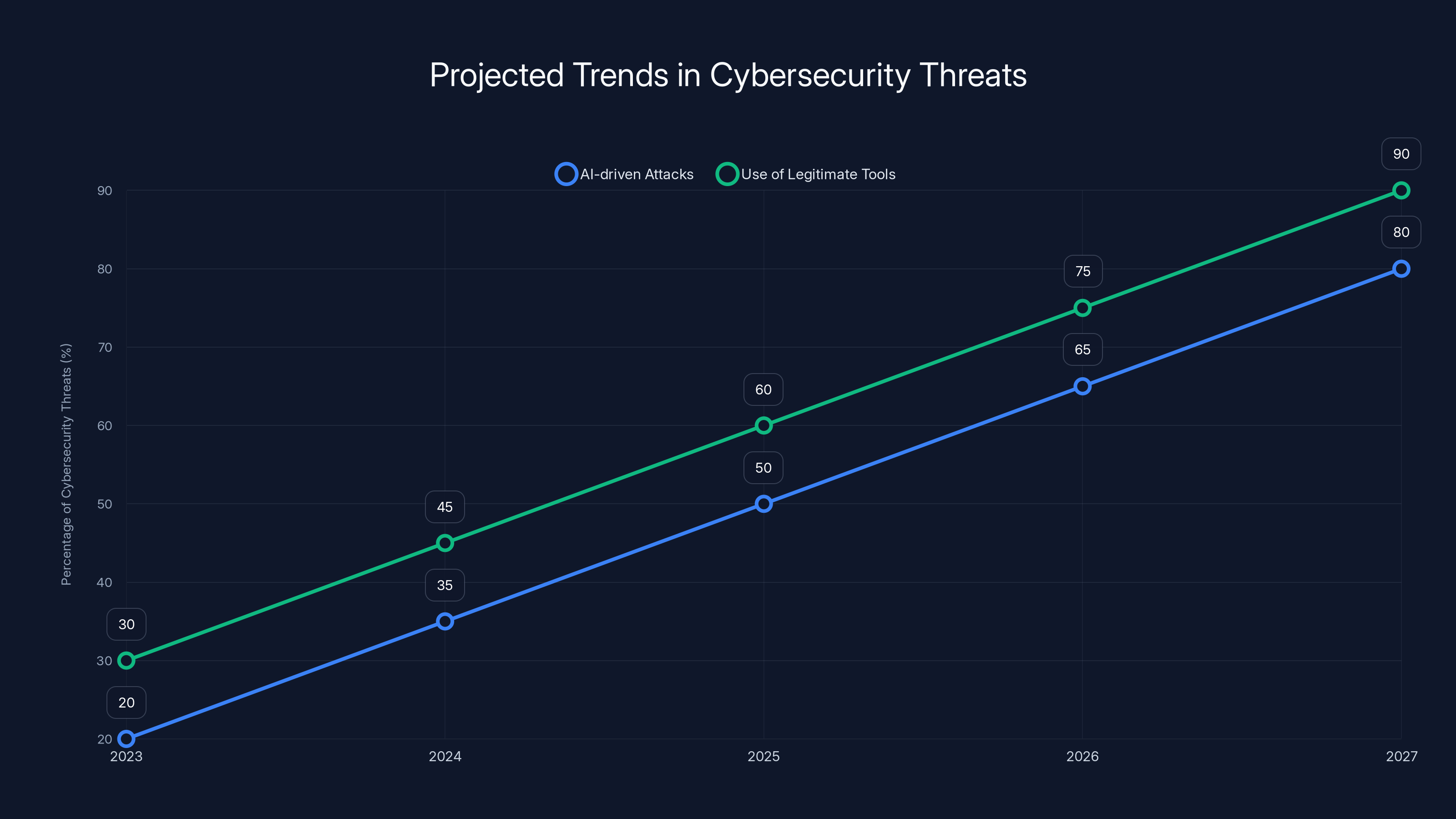
AI-driven attacks and the use of legitimate tools for malicious purposes are projected to increase significantly over the next five years. Estimated data.
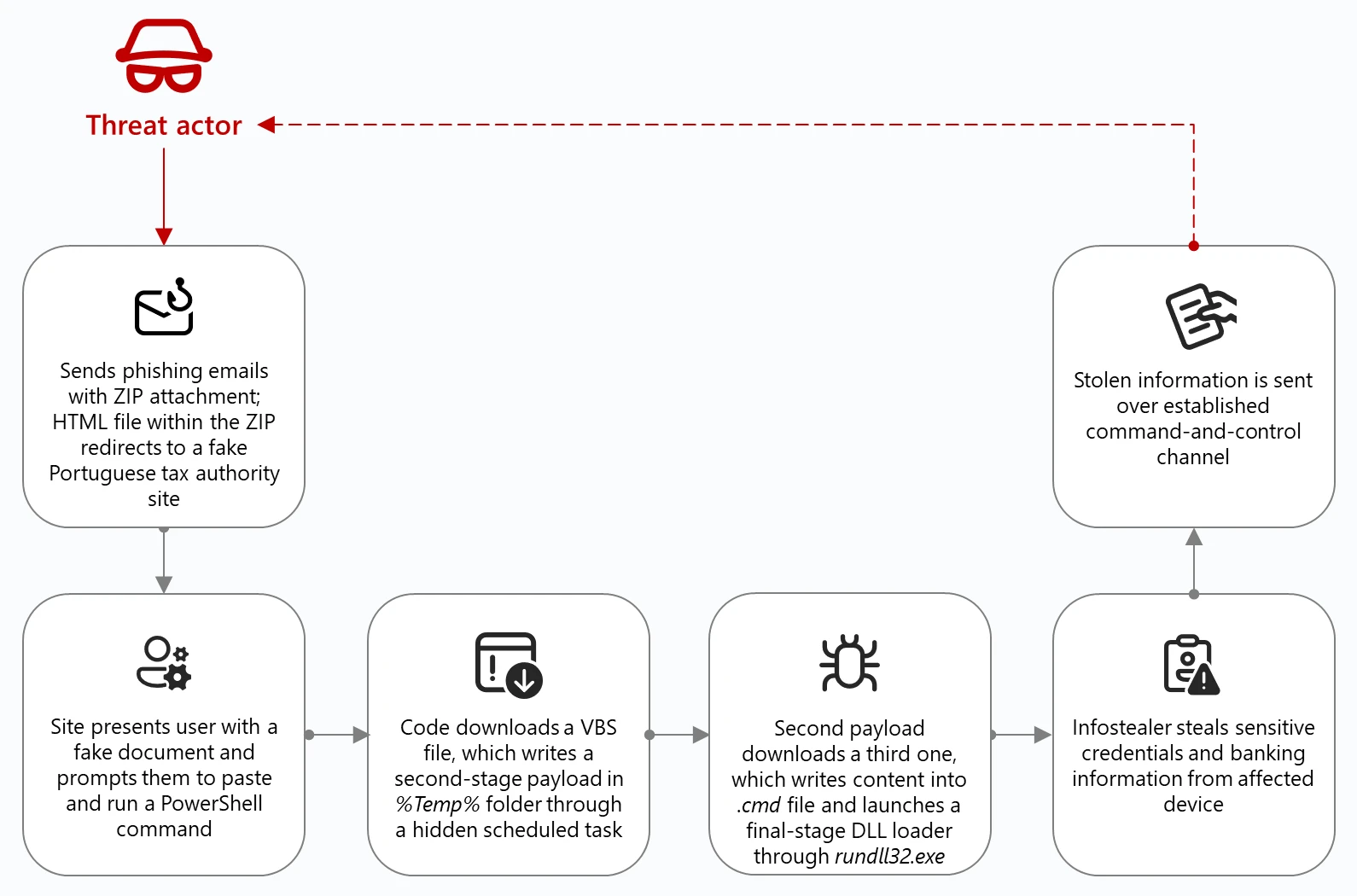
The Mechanics of a Click Fix Attack
Step-by-Step Breakdown
- Initiation: The attack usually begins with a phishing email or a compromised website that presents a fake security alert, as described by The Hacker News.
- Deception: The alert claims there’s an urgent issue requiring immediate attention, such as a virus or system vulnerability.
- Execution: Users are instructed to open Windows Terminal and enter a specific command, purportedly to fix the problem.
- Installation: The command actually downloads and executes malware, such as the Lumma Stealer, as highlighted in Qualys' analysis.
- Compromise: Once installed, the malware can steal sensitive data, monitor activities, or open backdoors for further exploitation.
Why This Works
The genius behind Click Fix attacks is their reliance on user trust and urgency. The attackers’ messages are crafted to induce panic, making users bypass their usual caution. Moreover, by using Terminal—a tool not typically associated with malware—attackers exploit a blind spot in many users’ defenses, as noted by Cybersecurity News.
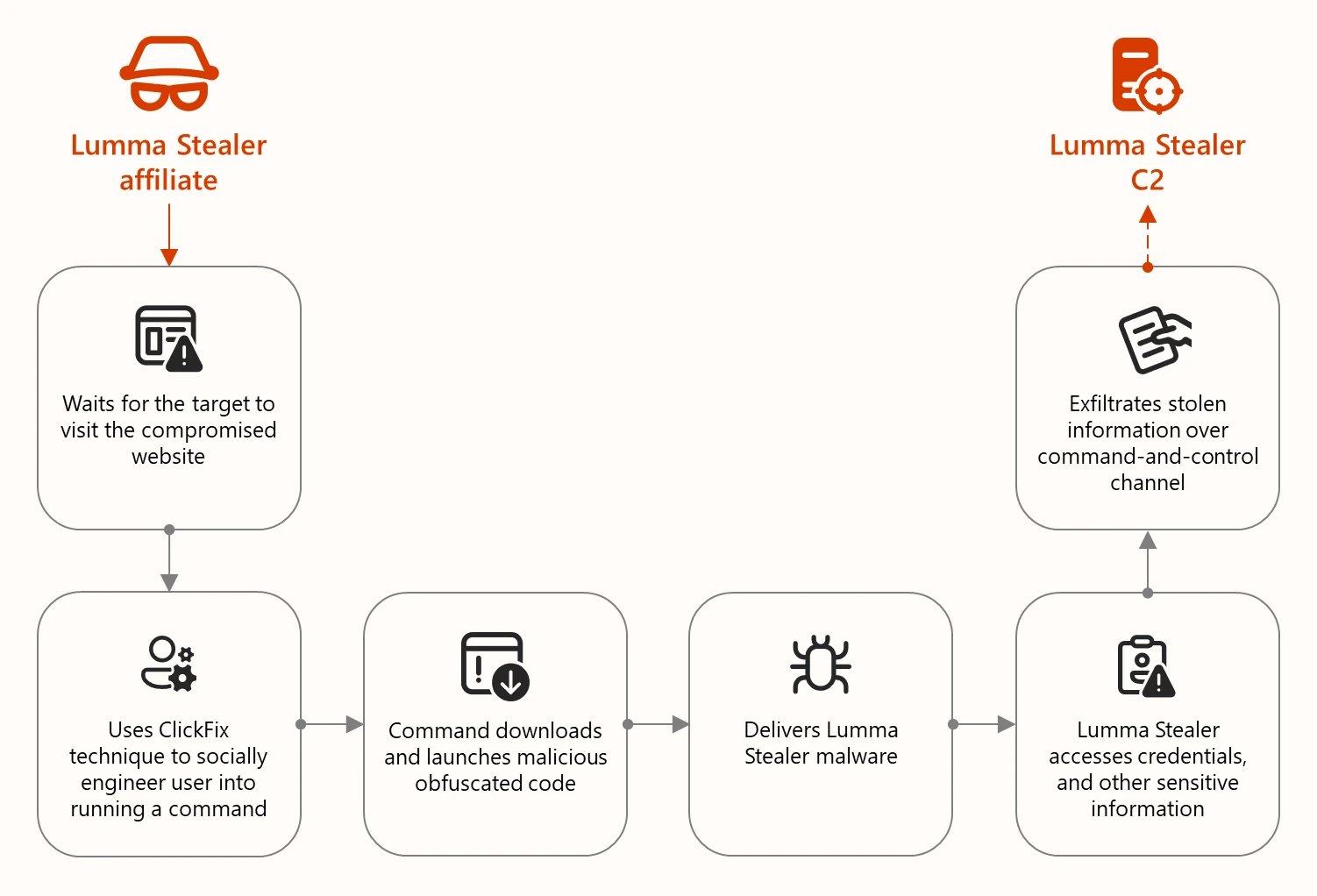
Lumma Stealer: The Current Threat
Lumma Stealer is a type of malware deployed in these attacks. It’s designed to extract passwords, cookies, and other sensitive information from infected systems.
Key Features of Lumma Stealer
- Data Extraction: Capable of extracting credentials from browsers, email clients, and FTP programs.
- Stealth Operations: Operates silently, often undetected by traditional antivirus software.
- Backdoor Access: Can open backdoors for remote attackers to further infiltrate the system, as detailed in CyberNews.

Lumma Stealer poses a significant threat with high data extraction capabilities, stealth operations, and backdoor access. Estimated data based on typical malware feature impact.
Protecting Your Systems
Best Practices
- User Education: Regular training sessions on recognizing phishing attempts and suspicious activities.
- Software Updates: Ensure all systems and security software are up-to-date to patch known vulnerabilities, as advised by Google Cloud.
- Advanced Security Tools: Utilize tools that offer real-time monitoring and detection capabilities.
- Restrict Terminal Use: Limit access to Windows Terminal to trusted users only.
- Backup Data Regularly: Maintain regular backups to minimize data loss in case of an attack.
Common Pitfalls
- Ignoring Alerts: Many users dismiss security alerts as false alarms, missing critical threats.
- Outdated Systems: Systems not regularly updated are more vulnerable to exploits.
- Weak Passwords: Simple passwords can be easily cracked, granting attackers access.
Future Trends in Cybersecurity
The Rise of AI in Attacks
With AI technology becoming more accessible, expect cybercriminals to use AI to automate and scale their attacks. This could mean more personalized phishing attempts and adaptive malware that learns from its environment, as discussed in Cybersecurity Ventures.
Increased Use of Legitimate Tools
The trend of using legitimate tools for malicious purposes will likely continue. Cybersecurity measures must evolve to monitor not just for known threats but also for unusual behaviors in legitimate software, as highlighted by Cyble.

Recommendations for Businesses
- Invest in Employee Training: Regular workshops on cybersecurity awareness can drastically reduce the risk of successful attacks.
- Implement Multi-Factor Authentication (MFA): Adding an extra layer of security can prevent unauthorized access even if credentials are compromised.
- Conduct Regular Security Audits: Identify vulnerabilities before attackers do.
- Use Endpoint Detection and Response (EDR) Tools: These tools can detect and respond to suspicious activities in real-time.
Conclusion
Click Fix attacks represent a shift in cybercriminal tactics, leveraging user trust and system tools like Windows Terminal. By understanding these threats and implementing robust security measures, individuals and organizations can better protect themselves against such evolving dangers. As technology progresses, staying informed and vigilant is your best defense.
FAQ
What is a Click Fix attack?
A Click Fix attack is a type of social engineering scam where attackers use fake alerts to trick users into executing commands that install malware.
How does Lumma Stealer work?
Lumma Stealer is malware that extracts sensitive information like passwords and cookies from infected systems, often operating undetected.
What are the benefits of using Windows Terminal?
Windows Terminal provides a flexible command-line interface for executing scripts and commands, offering more control over system functions.
How can I protect my system from Click Fix attacks?
Implement user training, keep software updated, use advanced security tools, and limit access to critical system functions like Windows Terminal.
What should I do if I suspect a Click Fix attack?
Immediately disconnect from the internet, run a full system scan with updated antivirus software, and contact your IT department for assistance.
Are Click Fix attacks common?
While not as common as other types of attacks, Click Fix campaigns are increasing in frequency and sophistication, making awareness crucial.
Can Click Fix attacks be prevented?
While no system is entirely immune, awareness training, regular system updates, and robust security protocols can significantly reduce the risk.
Why are attackers targeting Windows Terminal?
Windows Terminal is less monitored than other system components, providing attackers with a stealthier method to execute malicious commands.
Key Takeaways
- ClickFix attacks now target Windows Terminal instead of Run.
- Lumma Stealer malware can exfiltrate sensitive data from compromised systems.
- Regular system updates and user training are critical for security.
- Advanced tools and security audits help detect and prevent attacks.
- Future trends include AI-driven attacks and the use of legitimate tools for malicious purposes.
Related Articles
- Understanding Phishing Campaigns: How Fake Email Chains Exploit Urgency [2025]
- CBP Used Online Ad Data to Track Phone Locations | WIRED
- How to Watch Top Chef Season 23 Online from Anywhere [2025]
- How One Man's Accidental Hack Revealed Vulnerabilities in Modern Robotics [2025]
- Inside the FBI's Cybersecurity Breach: Unraveling the Hijacking of Wiretaps and Search Warrants [2025]
- TriZetto Data Breach: Lessons and Future Implications for Healthcare Security [2025]
![Understanding ClickFix Attacks: How Hackers Target Windows Terminal for Malware [2025]](https://tryrunable.com/blog/understanding-clickfix-attacks-how-hackers-target-windows-te/image-1-1773061609006.jpg)



