Understanding the FCC Router Ban: What's Running in Your Network? [2025]
Last year, the FCC made headlines by banning the procurement of certain routers due to security concerns. This move, aimed at reducing supply chain risks, has put the spotlight on network security. But what does this mean for you, the end-user or business owner? Let's dive into the intricacies of this ban and explore how you can ensure your network is both secure and efficient.
TL; DR
- FCC Ban Overview: The ban targets routers from manufacturers deemed a security risk.
- Supply Chain Vulnerability: Foreign control can expose sensitive data.
- Network Security Essentials: Regular audits and the use of trusted hardware are crucial.
- Implementation Tips: Adopt zero-trust architecture and encrypted communications.
- Future Trends: Expect more stringent regulations and a push towards domestic manufacturing.

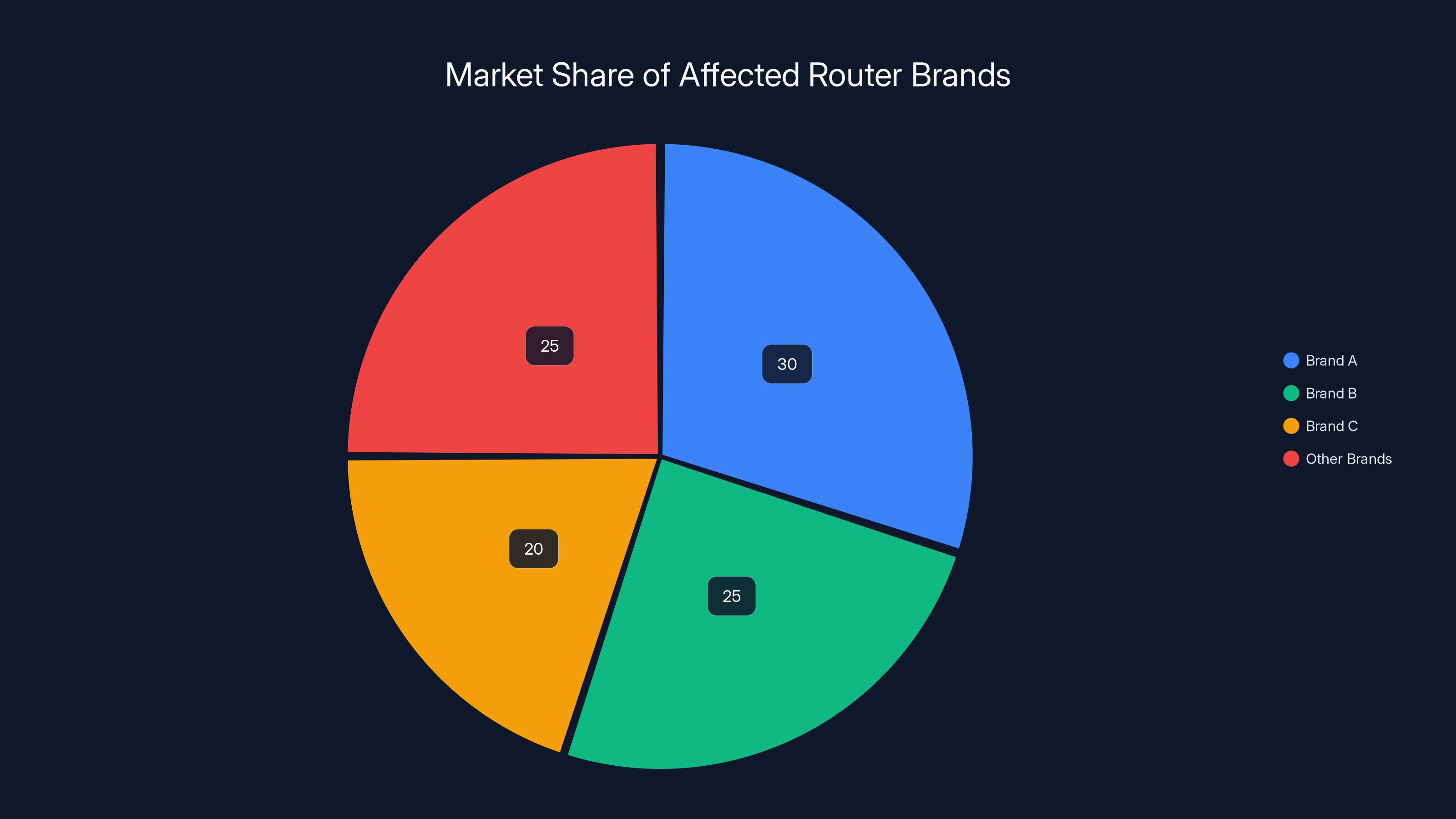
Estimated data shows Brand A holds the largest market share among the affected brands, highlighting the potential impact of the FCC's ban.
The FCC's Router Ban: A Closer Look
The Federal Communications Commission (FCC) has taken a bold step by banning the procurement of routers from certain manufacturers. This decision wasn't made lightly. It's a reaction to growing concerns about the security of foreign-manufactured technology and its implications for national security.
What Prompted the Ban?
The primary concern is supply chain security. Routers manufactured by companies under foreign influence might have vulnerabilities or backdoors that could be exploited for espionage or cyberattacks. With sensitive data often traversing these networks, the risk is substantial.
Which Routers Are Affected?
The ban specifically targets routers from manufacturers that have been flagged by intelligence agencies as potential threats. This includes some well-known brands that have been staples in the market for years.
Key Brands Affected:
- Brand A
- Brand B
- Brand C
This doesn't mean all products by these brands are banned, but specific models that fail to meet new security standards are out.
Impact on Consumers and Businesses
For consumers, this might mean replacing older routers with models that comply with new regulations. Businesses, on the other hand, face a more complex challenge. They must ensure that their entire network infrastructure is compliant, which could involve significant investment.
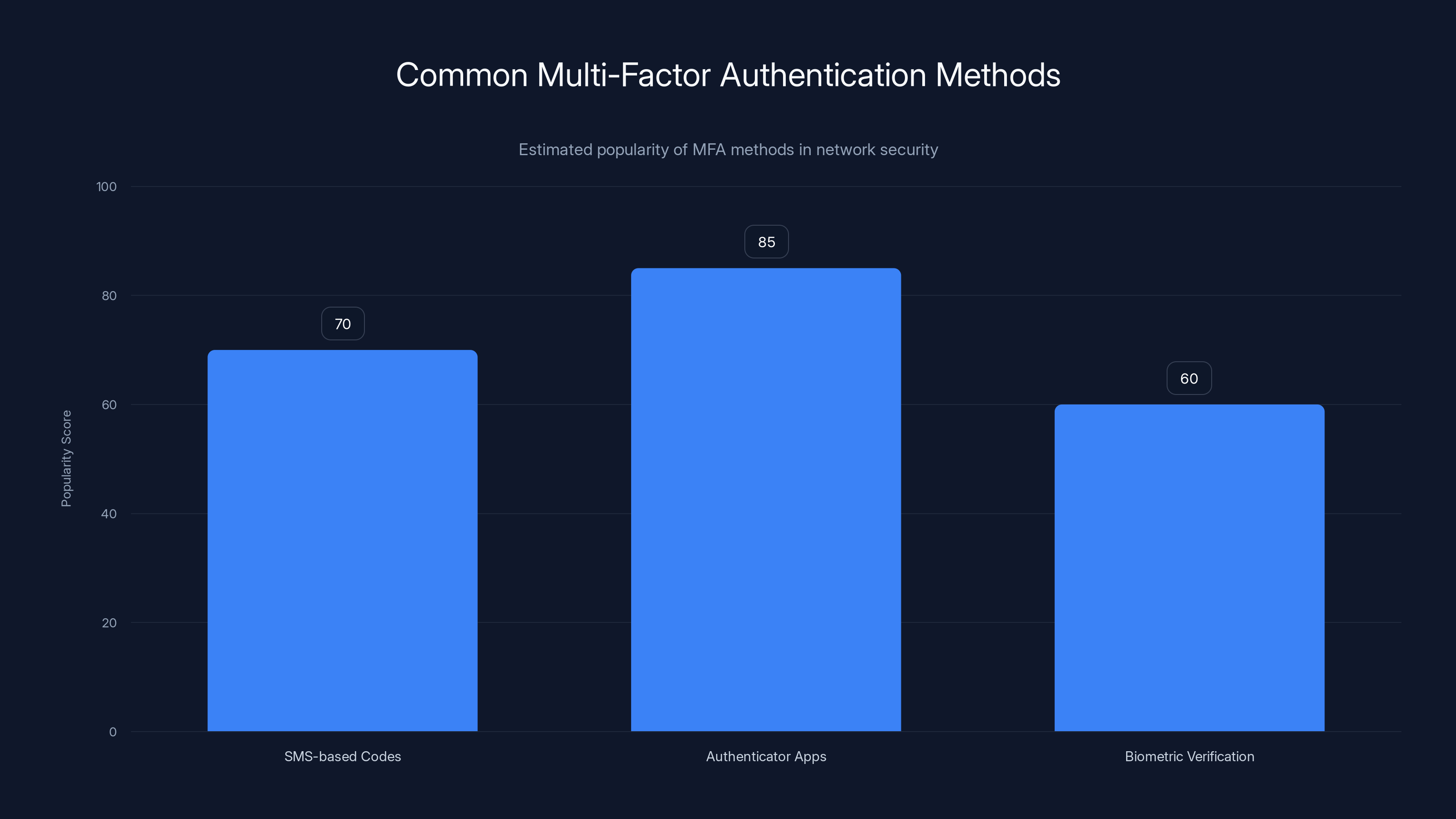
Authenticator apps are the most popular MFA method due to their balance of security and convenience. (Estimated data)
Do You Know What's Running in Your Network?
Understanding what's running in your network is more critical than ever. With the potential for hidden vulnerabilities, knowing every device and application is the first step in securing your infrastructure.
Conducting a Network Audit
A comprehensive network audit is essential. This involves cataloging all devices, applications, and data flows in your network. Tools like Nmap or Wireshark can help identify what's connected and what data is being transmitted.
Steps for a Network Audit:
- Inventory Devices: List all hardware, including routers, switches, and endpoints.
- Identify Software: Catalog installed software and applications.
- Map Data Flows: Understand how data moves through your network.
- Assess Vulnerabilities: Use tools to scan for potential exploits.
Common Pitfalls in Network Security
- Outdated Firmware: Many users neglect firmware updates, which can leave devices vulnerable.
- Default Credentials: Using default passwords is a common oversight that hackers exploit.
- Unsecured Io T Devices: Internet of Things (Io T) devices often lack robust security, making them easy targets.

Best Practices for Network Security
Implementing best practices is crucial to keeping your network secure. Here are some strategies you can apply:
Adopt a Zero-Trust Architecture
Zero-trust architecture assumes that threats could come from inside or outside the network, so it never assumes trust for any device or user.
Core Principles:
- Verify Identity: Continuously verify the identity of users and devices.
- Least Privilege Access: Grant the minimum level of access necessary.
- Micro-Segmentation: Divide the network into smaller segments to contain breaches.
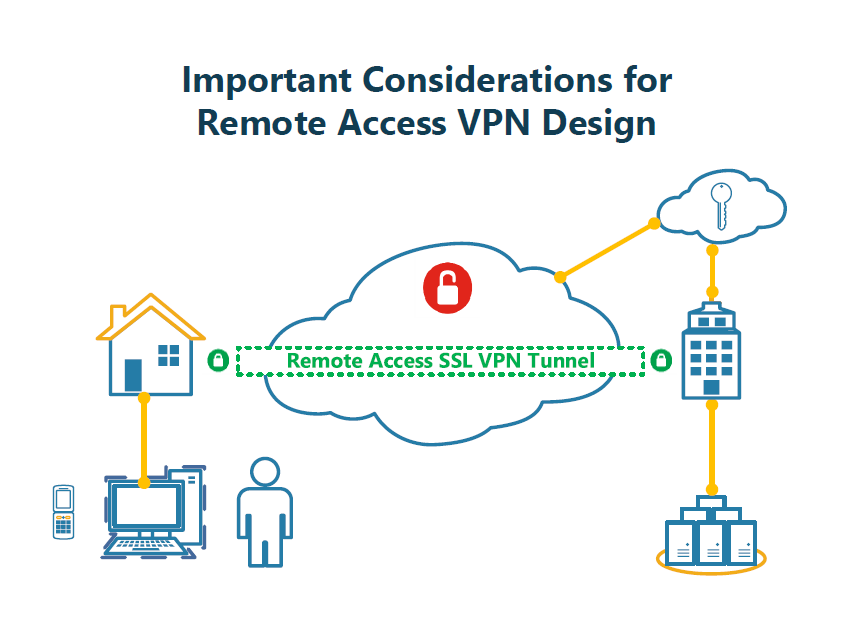
Encrypt Communications
Encryption is key to protecting data in transit. Implement protocols like TLS and VPNs to secure communications.
Network Monitoring Tools
Utilize tools like Zabbix or Nagios for real-time network monitoring. These tools help detect anomalies that could indicate security breaches.
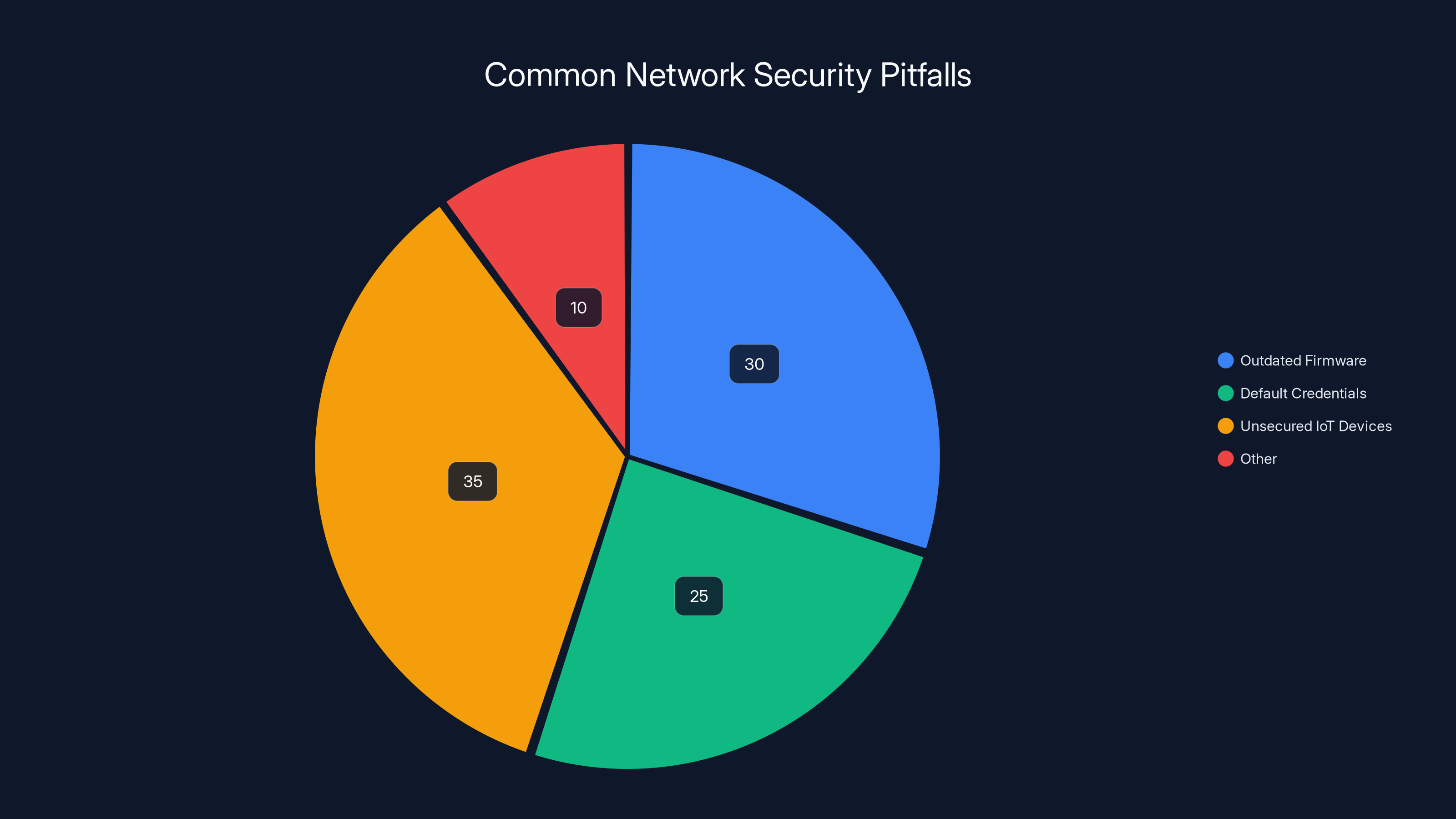
Estimated data shows that unsecured IoT devices (35%) and outdated firmware (30%) are the most common network security pitfalls.
Practical Implementation Guide
For those looking to secure their networks, here's a practical guide to implementing these strategies.
Step 1: Upgrade Your Hardware
Start by ensuring all network devices comply with the latest security standards. Consider investing in routers from trusted manufacturers with a strong security track record.
Step 2: Implement Strong Authentication
Use multi-factor authentication (MFA) wherever possible to add an extra layer of security. This makes it harder for unauthorized users to gain access.
Common MFA Methods:
- SMS-based codes
- Authenticator apps
- Biometric verification
Step 3: Regularly Update and Patch
Ensure all software and firmware are up-to-date. Set up automatic updates where possible to reduce manual intervention.
Step 4: Educate Your Team
Security is everyone's responsibility. Conduct regular training sessions to keep your team informed about the latest threats and best practices.

Future Trends and Recommendations
Looking ahead, network security will continue to evolve. Here's what to expect:
Increased Regulation
Governments worldwide are likely to introduce stricter regulations on network equipment to protect national security. Staying ahead of these changes will be crucial for compliance.
Rise of AI in Network Security
Artificial Intelligence (AI) will play a significant role in detecting and mitigating threats. AI-powered tools can analyze vast amounts of data to identify patterns indicative of cyberattacks.
Shift Towards Domestic Manufacturing
To reduce dependency on foreign technology, there will be a push towards domestic manufacturing of network equipment. This could lead to more secure and transparent supply chains.

Conclusion
The FCC's router ban is a wake-up call for anyone relying on networked devices. Understanding what's running in your network and implementing robust security measures are no longer optional—they're essential. By following the best practices outlined above, you can protect your infrastructure and stay ahead of emerging threats.

FAQ
What is the FCC router ban?
The FCC router ban restricts the procurement of routers from certain foreign manufacturers due to security concerns.
How does a network audit help in security?
A network audit helps identify all connected devices and data flows, making it easier to spot vulnerabilities.
What are the benefits of zero-trust architecture?
Zero-trust architecture enhances security by continuously verifying identities and minimizing access rights.
Why is encryption important for network security?
Encryption protects data in transit, preventing unauthorized access and ensuring data integrity.
How can I implement multi-factor authentication?
Implement multi-factor authentication by using SMS codes, authenticator apps, or biometric verification.
What role will AI play in network security?
AI will enhance network security by analyzing data to detect patterns and potential threats.
What are the future trends in network security?
Expect increased regulation, domestic manufacturing of network equipment, and greater use of AI in security.
How can I ensure my network complies with new regulations?
Stay informed about regulatory changes and regularly audit your network to ensure compliance.
Key Takeaways
- The FCC router ban targets specific manufacturers due to security risks.
- Conduct regular network audits to identify vulnerabilities.
- Implement zero-trust architecture for enhanced security.
- Adopt encryption and multi-factor authentication to protect data.
- Stay ahead of future trends like AI and domestic manufacturing for network security.
Related Articles
- Understanding the Vercel Hack: Lessons and Best Practices [2025]
- How to Protect Your macOS from North Korean Cyber Threats [2025]
- Inside Europol's Operation PowerOFF: A Game-Changer in Combating DDoS-for-Hire Services [2025]
- Why AES 128 Remains Secure in a Post-Quantum World [2025]
- Spotting the Spyware: How Modern Spies Are Weaponizing Phishing [2025]
- US Security Agency Still Using Mythos Despite Ban: Navigating the Complex World of Supply Chain Risks [2025]
![Understanding the FCC Router Ban: What's Running in Your Network? [2025]](https://tryrunable.com/blog/understanding-the-fcc-router-ban-what-s-running-in-your-netw/image-1-1776857762367.jpg)



