Unraveling the EU Cyberattack: A Deep Dive into the Breach and Its Implications [2025]
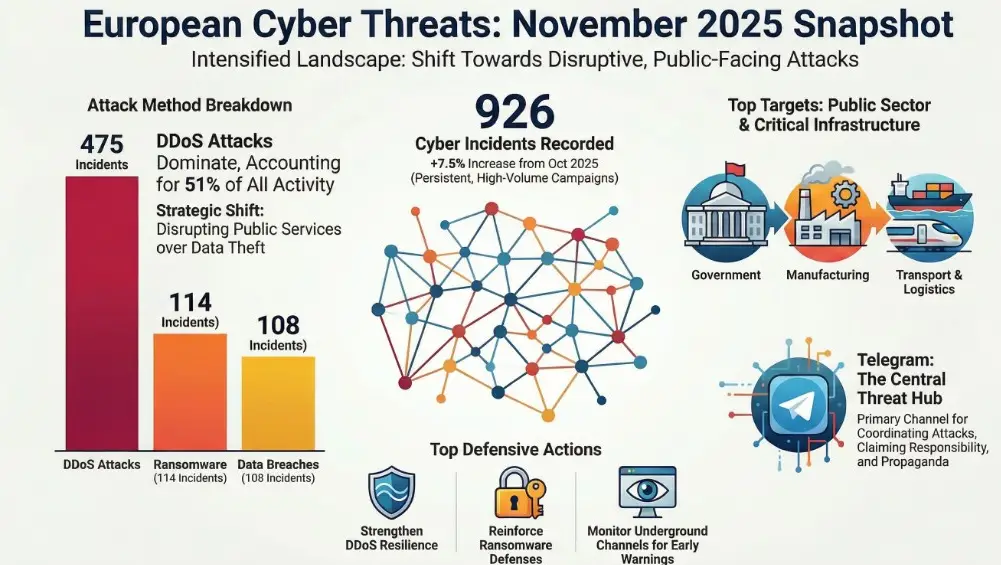
The recent cyberattack on the European Union has sent shockwaves throughout the global cybersecurity community. With 90GB of sensitive data published online and nearly 30 entities compromised, it's clear that the attack was more severe than initially thought. This article will explore the technical details of the breach, its implications for cybersecurity practices, and what organizations can do to protect themselves from similar threats in the future.
TL; DR
- 90GB of sensitive data was leaked, affecting 30 EU entities as reported by TechRadar.
- The breach exploited AWS keys, leading to mass data exfiltration, according to Rescana.
- Team PCP is believed to be behind the attack, utilizing a Trivy update as detailed by Wiz.io.
- Organizations must enhance cloud security measures to prevent similar attacks, a sentiment echoed in Cyfirma's weekly intelligence report.
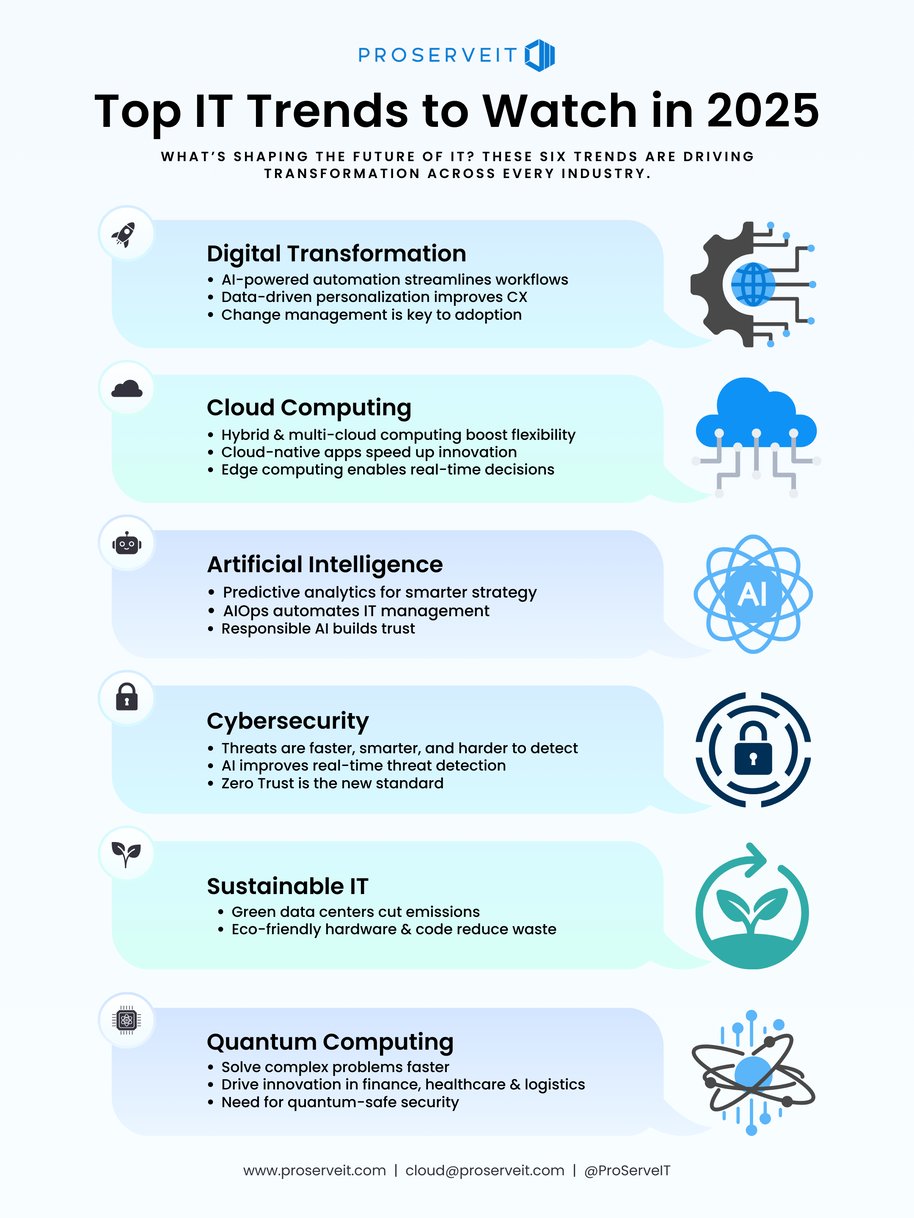
- Future trends in cybersecurity will focus on AI-driven threat detection and zero-trust architectures, as discussed in Cybersecurity Insiders.

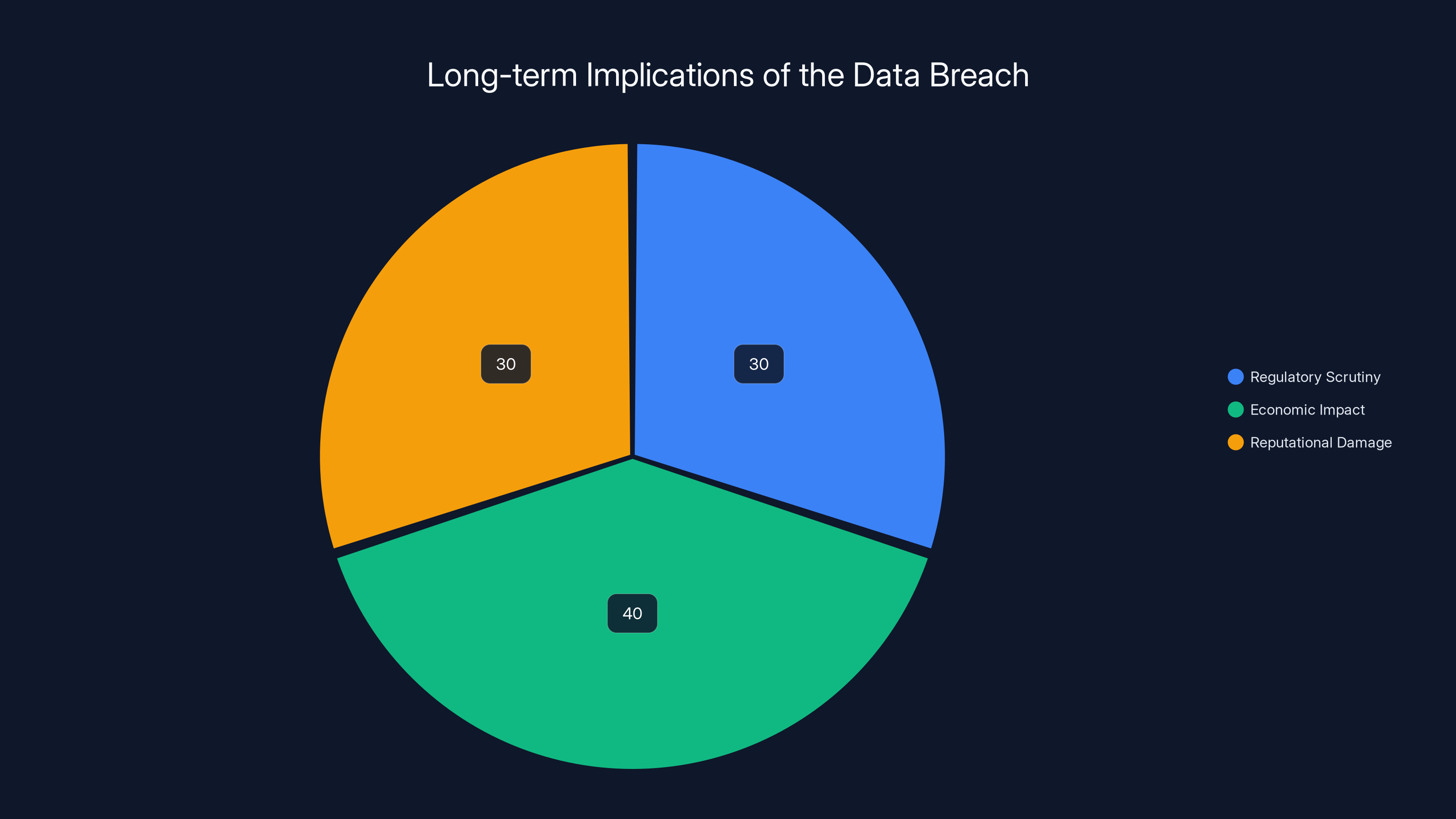
Estimated data suggests that economic impact and reputational damage are equally significant, with regulatory scrutiny also playing a major role in the long-term implications of the breach.
Understanding the Breach
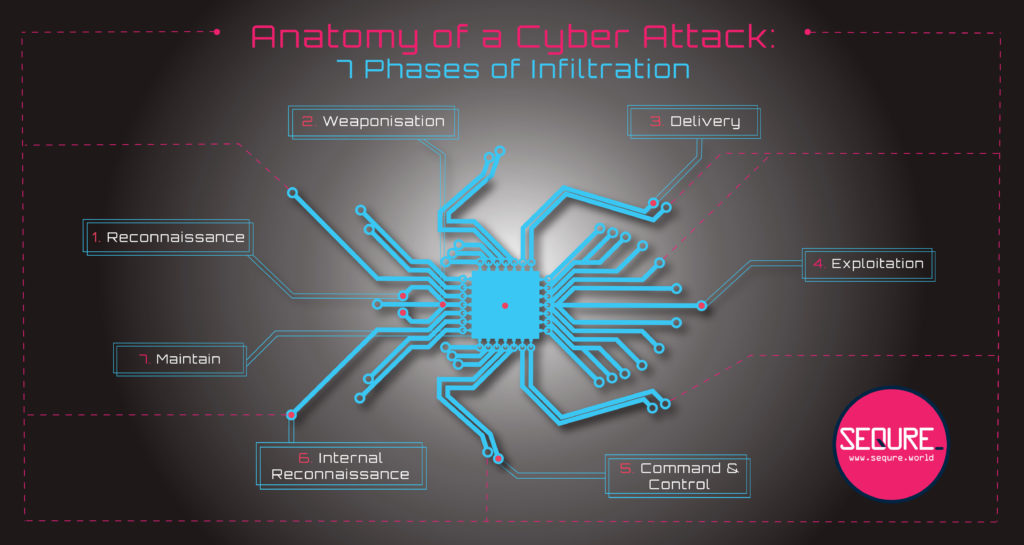
The Anatomy of the Attack
On the surface, the attack seemed like a typical data breach. However, the reality was far more complex. The attackers, identified as Team PCP, exploited vulnerabilities in a software update process for Trivy, a popular open-source vulnerability scanner. By injecting malicious code into the update, they gained unauthorized access to AWS credentials, allowing them to infiltrate various systems across the EU, as detailed by Palo Alto Networks.
What exactly happened? The attackers managed to insert their payload during a routine update, which then propagated across multiple systems, each unwittingly granting access to sensitive data. This highlights a critical flaw in the update security chain, underscoring the need for rigorous vetting processes, as noted by Microsoft.
Key Technical Aspects
The breach leveraged advanced tactics, including:
- Credential Harvesting: Once inside, Team PCP harvested AWS keys, enabling them to exfiltrate data at scale, according to Talos Intelligence.
- Data Exfiltration Techniques: They used sophisticated methods to bypass traditional security measures, including encrypted communication channels and obfuscation techniques, as reported by SecurityWeek.
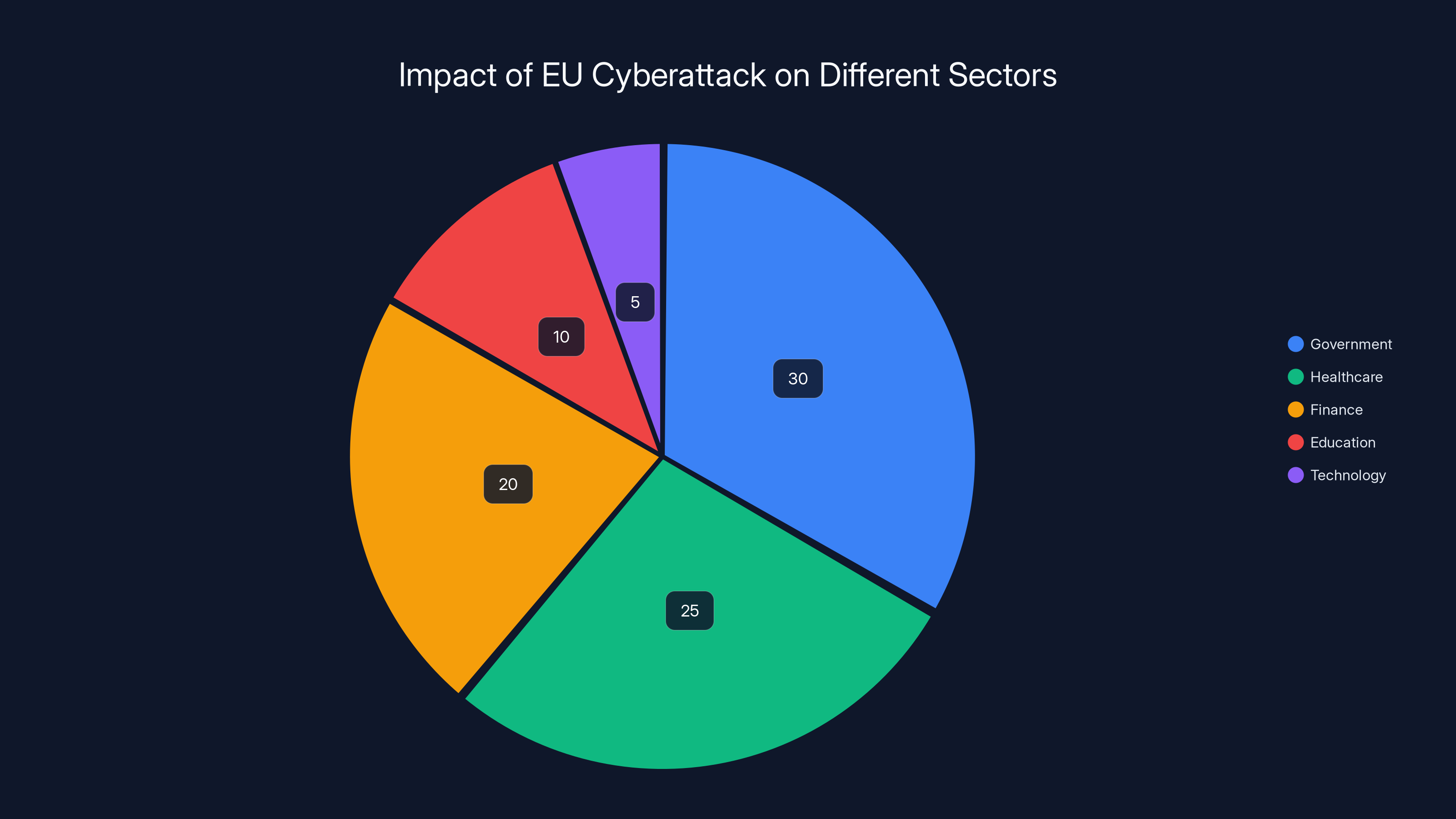
Estimated data shows that the government sector was most affected by the EU cyberattack, with 30% of the breached data originating from this sector.
The Impact of the Breach
Immediate Consequences
The leak of 90GB of data has immediate ramifications for the entities involved, including compromised personal information, strategic documents, and possibly classified communications. The breach not only affects the entities directly but also poses a broader threat to EU operations and public trust, as highlighted by MSN News.
Long-term Implications
Over the long term, this breach may lead to:
- Increased Regulatory Scrutiny: Governments may impose stricter regulations on data handling and security protocols, as discussed by Morgan Lewis.
- Economic Impact: Potential financial losses and increased security costs for affected entities, as estimated by Vocal Media.
- Reputational Damage: Loss of trust among stakeholders and the public, as noted in Ropes & Gray.
Best Practices for Mitigating Future Risks
Enhancing Cloud Security
Given the role of AWS credentials in this breach, strengthening cloud security is paramount. Organizations should consider implementing the following measures:
- Multi-Factor Authentication (MFA): Enforce MFA for all cloud access to add an extra layer of security, as recommended by BizTech Magazine.
- Regular Key Rotation: Regularly rotate API keys and credentials to minimize the risk of compromised keys being misused.
- Audit Logs: Maintain comprehensive audit logs to track access and changes in real-time.
Securing the Software Supply Chain
To prevent similar attacks through software updates:
- Code Signing: Utilize digital signatures to verify the integrity of software updates.
- Continuous Monitoring: Implement continuous monitoring of software supply chains for anomalies, as advised by Cyfirma.

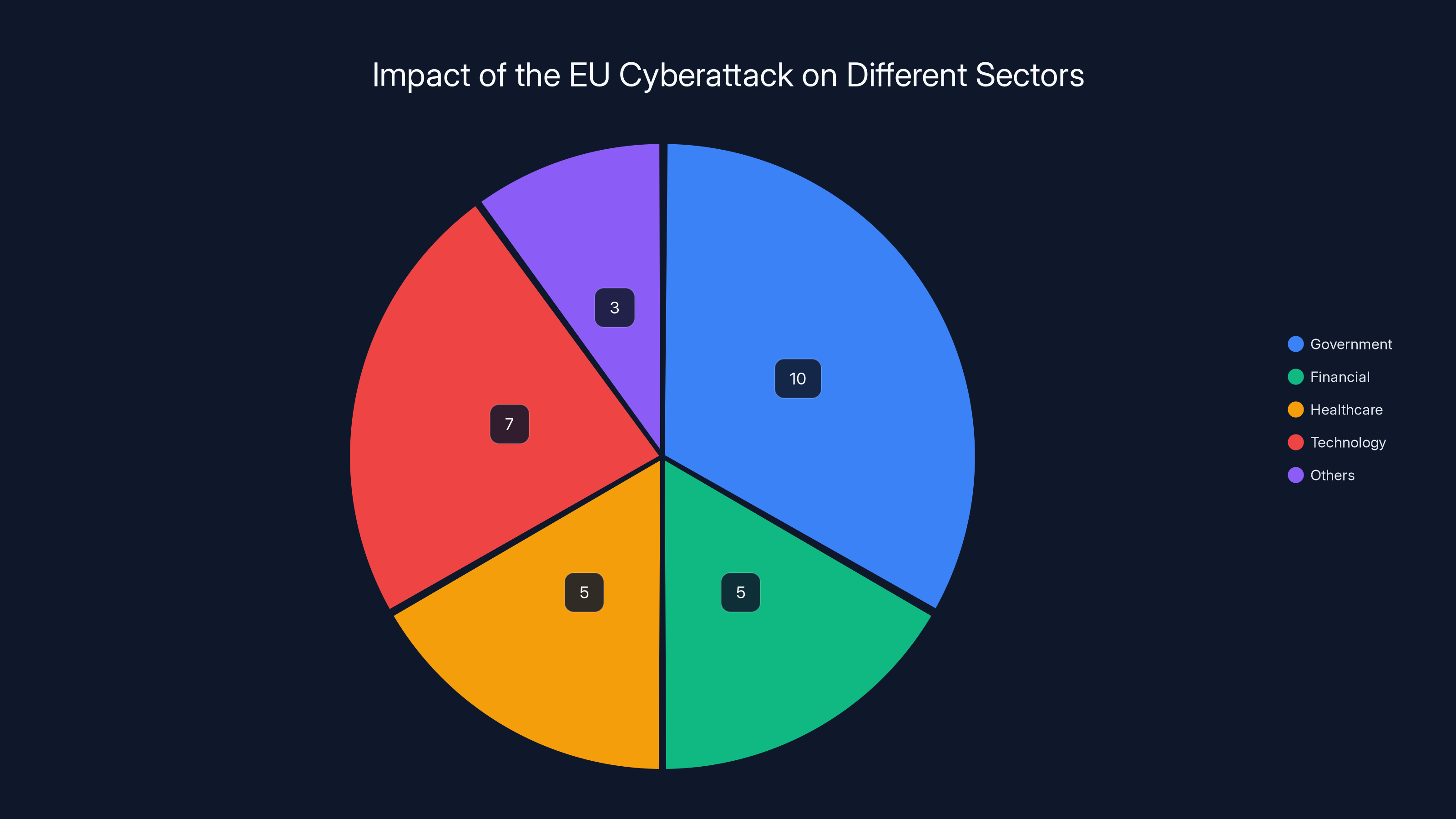
The EU cyberattack affected various sectors, with government and technology sectors being the most impacted. Estimated data based on typical sector vulnerabilities.
Common Pitfalls and Solutions
Overlooking Insider Threats
While external threats are a primary concern, insider threats can be equally damaging. Organizations must:
- Conduct Background Checks: Perform thorough checks on employees, contractors, and partners.
- Implement Access Controls: Limit access to sensitive information based on the principle of least privilege.
Inadequate Incident Response Plans
A robust incident response plan is crucial. Ensure your plan includes:
- Clear Communication Protocols: Establish clear lines of communication during a breach.
- Regular Drills: Conduct regular drills to ensure readiness.
Future Trends in Cybersecurity
Embracing AI and Machine Learning
AI and machine learning will play a pivotal role in future cybersecurity strategies. These technologies can:
- Enhance Threat Detection: Identify patterns and anomalies that may indicate a breach.
- Automate Responses: Quickly respond to threats with minimal human intervention, as discussed by Cybersecurity Insiders.
Adopting Zero-Trust Architectures
Zero-trust architectures are becoming the gold standard in security. By assuming that threats can come from both inside and outside the network, organizations can:
- Verify Every Access Request: Authenticate and authorize every request, regardless of its origin.
- Segment Networks: Divide networks into smaller, manageable segments to limit the spread of threats.

Conclusion
The EU cyberattack serves as a stark reminder of the vulnerabilities that exist in our interconnected world. By understanding the intricacies of the breach and implementing robust security measures, organizations can better protect themselves against future threats. As technology evolves, so must our approach to cybersecurity, with a focus on proactive measures and cutting-edge technologies.

FAQ
What is the EU cyberattack?
The EU cyberattack refers to a recent breach where Team PCP exploited vulnerabilities in a Trivy update, leading to the exposure of 90GB of sensitive data from nearly 30 EU entities, as reported by TechRadar.
How did the attackers gain access?
The attackers gained access by injecting malicious code into a Trivy software update, which then allowed them to harvest AWS credentials and exfiltrate data, as detailed by Wiz.io.
What are the immediate consequences of the breach?
Immediate consequences include compromised personal and strategic data, potential financial losses, and increased regulatory scrutiny, as highlighted by MSN News.
How can organizations enhance cloud security?
Organizations can enhance cloud security by implementing multi-factor authentication, regular key rotation, and maintaining comprehensive audit logs, as recommended by BizTech Magazine.
What are zero-trust architectures?
Zero-trust architectures are security frameworks that assume threats can come from both inside and outside the network, requiring verification for every access request, as discussed in Cybersecurity Insiders.
What role will AI play in future cybersecurity?
AI will play a crucial role in enhancing threat detection and automating responses, making cybersecurity systems more efficient and effective, as noted by Cybersecurity Insiders.
Key Takeaways
- 90GB Data Leak: Highlighting the scale and severity of the breach.
- AWS Exploitation: The critical role of stolen AWS credentials.
- Regulatory Impact: Potential changes in cybersecurity regulations.
- Cloud Security Measures: Importance of strengthening cloud security.
- AI in Cybersecurity: Future trends in threat detection and response.
- Zero-Trust Importance: Adoption of zero-trust architectures.
- Proactive Measures: The need for continuous monitoring and incident response.

Related Articles
- Hasbro Cyberattack: Lessons and Strategies for Cyber Resilience [2025]
- Laughing RAT: The New Malware Threat in 2025
- Understanding Telehealth Security: Lessons from the Hims & Hers Data Breach [2025]
- The Hidden Dangers of AI: What If Your AI Agent Is Working Against You? [2025]
- CBP Facility Codes Sure Seem to Have Leaked Via Online Flashcards | WIRED
- The Role of Spyware in Modern Law Enforcement: A Deep Dive into ICE's Use of Paragon's Tools [2025]
![Unraveling the EU Cyberattack: A Deep Dive into the Breach and Its Implications [2025]](https://tryrunable.com/blog/unraveling-the-eu-cyberattack-a-deep-dive-into-the-breach-an/image-1-1775219648867.jpg)



