Introduction: The Identity Management Market Inflection Point
The identity and access management landscape is experiencing a fundamental transformation. For decades, CyberArk has dominated the privileged access management (PAM) market, commanding premium pricing and multi-year implementations that have become virtually synonymous with enterprise identity security. Yet in early 2025, a 35-person startup called Venice emerged from stealth with a bold assertion: they're already replacing these industry incumbents at Fortune 500 companies—and doing it in weeks, not years.
This isn't hyperbole born from startup enthusiasm. Venice's claim arrives backed by $20 million in Series A funding led by top-tier venture capital firm IVP, with participation from Index Ventures, signaling serious investor conviction in the company's technical approach and market timing. The fundraising announcement came as the broader cybersecurity market faces a seismic shift driven by artificial intelligence and autonomous systems that traditional identity platforms simply weren't designed to handle.
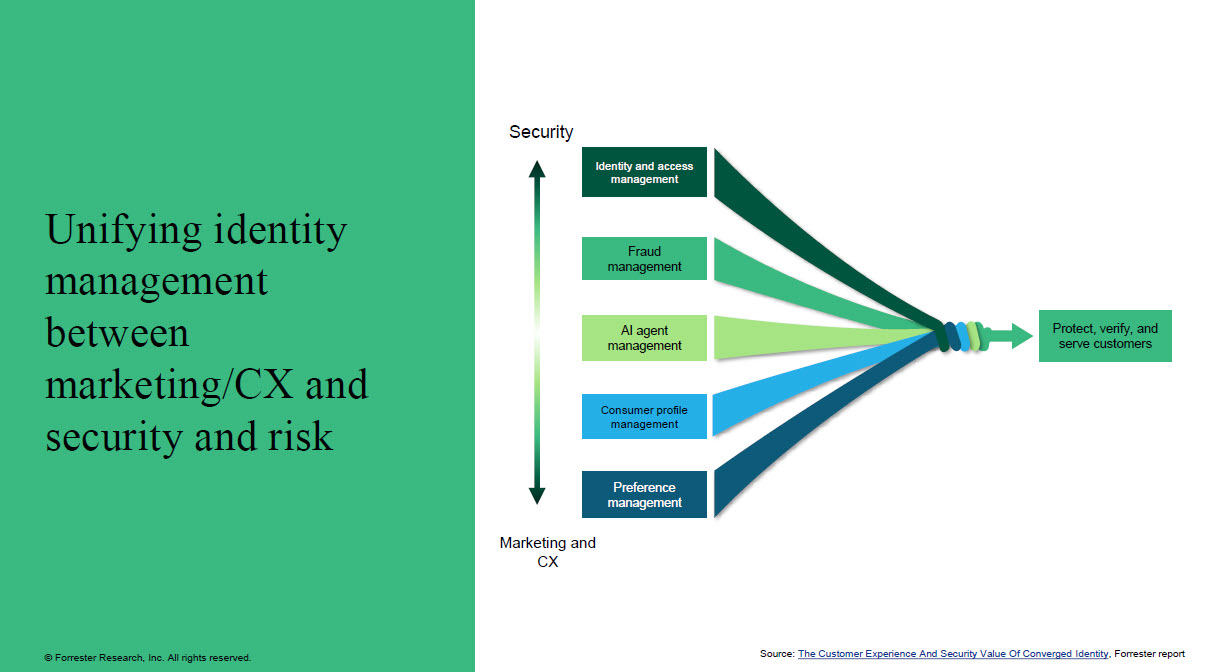
The core problem is both straightforward and profound: the digital workforce has fundamentally changed. For the past two decades, identity and access management systems were engineered around a relatively static assumption—human employees logging into corporate systems with individual credentials. These systems worked well enough when the access matrix was relatively simple: admin or user, on-premises or cloud, with predictable permission patterns established during initial setup.
Today's environment looks radically different. AI agents, automated workflows, chatbots, and non-human systems require credentials and permissions just like traditional users. A single knowledge worker might now have dozens of AI agents acting on their behalf, each needing granular, time-limited, task-specific access to various corporate systems. This explosion of non-human identities has created what industry observers call the "permissions crisis"—a situation where traditional identity management tools become bottlenecks rather than enablers of digital transformation.
Venice's entry into this market represents something more interesting than another well-funded startup chasing a large TAM (total addressable market). The company's founding team and technical approach suggest a genuine architectural rethinking of how identity and access management should work in an AI-first world. The company's founding CEO, Rotem Lurie, 31, brings an unusual pedigree that bridges military-grade security expertise, enterprise software experience at Microsoft, and hands-on knowledge of what it takes to displace incumbent vendors.
This comprehensive guide explores Venice's approach to identity management, examines why the market appears ready for disruption, analyzes the technical and business factors that might enable this startup to gain traction against entrenched competitors, and discusses where alternative solutions—including other emerging platforms—fit within this evolving ecosystem.
The Rise of Rotem Lurie: Building a PAM Insurgency
From Israeli Intelligence to Microsoft Identity
Rotem Lurie's professional trajectory reads like a masterclass in positioning oneself to start a consequential cybersecurity company. Born in Israel to two programmer parents—her mother was among the country's first female software engineers—Lurie grew up in an environment where deep technical knowledge and problem-solving were foundational. She spent four-and-a-half years as a lieutenant in Unit 8200, Israel's elite military intelligence and cyberwarfare unit, where she gained exposure to systems thinking at scale and the security challenges that emerge when protecting critical infrastructure against sophisticated adversaries.
After her military service, Lurie moved to the United States and joined Microsoft as a product manager working on what would become Microsoft Defender for Identity. This role gave her direct exposure to how one of the world's largest software companies approaches identity security—and critically, to the gaps in existing approaches. At Microsoft, she witnessed firsthand how enterprises struggled to implement comprehensive identity strategies across their hybrid IT environments, and how legacy vendors sometimes perpetuated problems rather than solving them through innovation.
Lurie's next move proved equally instructive. She became the first product hire at Axis Security, an access management startup founded by Israeli security veterans with deep expertise in cloud access and zero-trust principles. Axis Security's $500 million acquisition by Hewlett Packard Enterprise in 2022 validated the market opportunity but also provided Lurie with crucial insights into what attracts enterprise buyers, how acquisition processes work, and—most importantly—what technical and go-to-market approaches actually win in this space.
Just before the Axis Security acquisition closed, Lurie made an unconventional move: she joined YL Ventures, a cybersecurity-focused venture capital firm, as an investor rather than continuing the traditional founder path. This decision proved strategically brilliant. From her vantage point as a venture investor, Lurie spent approximately a year meeting with early-stage cybersecurity founders and learning how they approached market entry, technical development, and scaling.
The experience crystallized a crucial insight about startup dynamics in cybersecurity. Many early-stage companies optimize their entire strategy around acquisition by larger firms rather than building durable, independent businesses. Product decisions, go-to-market approaches, and even technical architecture choices are often made with an acquirer in mind—typically a large security platform vendor or consulting firm—rather than with genuine customer success as the north star. Lurie recognized that this acquisition-first mentality frequently led to suboptimal products that didn't truly solve customer problems at scale.
Identifying the Market Gap
From her unique vantage point at YL Ventures, Lurie began asking different questions: What if you built a company to truly dominate a market rather than to be acquired from it? What if you optimized for customer success and market dominance from day one, rather than treating acquisition as the implicit endpoint? These questions led her to identify a critical gap in the identity management market.
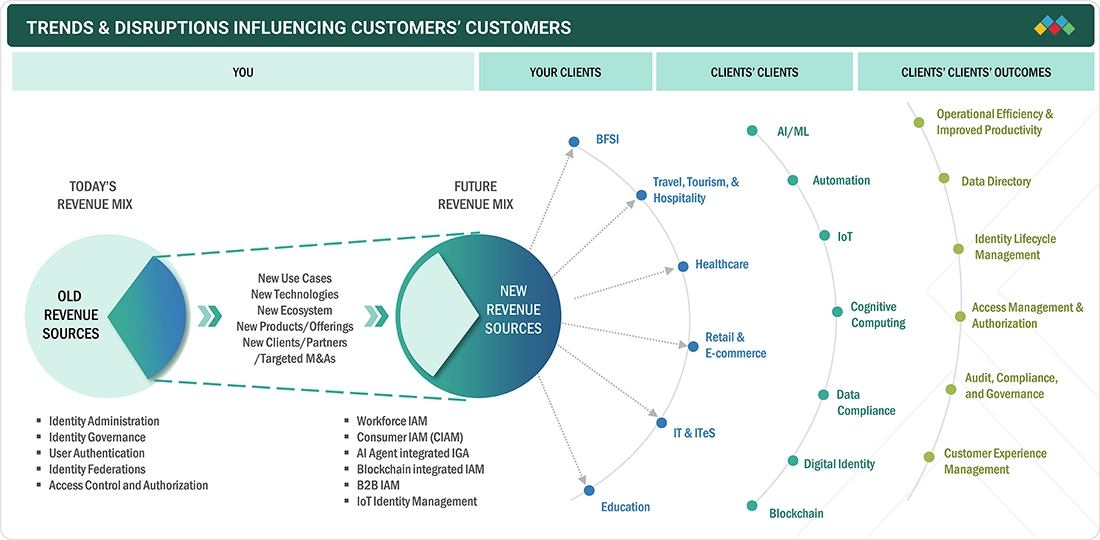
The gap wasn't in the traditional privileged access management space, though that area remained lucrative. Rather, it existed at the intersection of three market forces colliding simultaneously: (1) the acceleration toward hybrid IT environments combining on-premises infrastructure with cloud services, (2) the explosion of non-human entities requiring credential management, and (3) the recognition that traditional multi-tool identity stacks were becoming unmanageable.
In enterprise IT departments, identity and access management teams typically juggle roughly 10-15 different tools to manage who and what has access to corporate systems. Some tools specialize in privileged access for humans on on-premises systems. Others focus on SaaS application access. Still others handle cloud infrastructure permissions. A few manage just-in-time access. Most organizations have no unified view of permissions across these disparate systems, creating both security blind spots and operational complexity that drives up costs and extends implementation timelines.
Venice's founding thesis identified this fragmentation as the core problem. Rather than building another point solution in this crowded landscape, Lurie and her co-founder Or Vaknin—who brings deep technical expertise in identity systems and cybersecurity architecture—began designing a platform that could consolidate this sprawling toolchain into a single system.

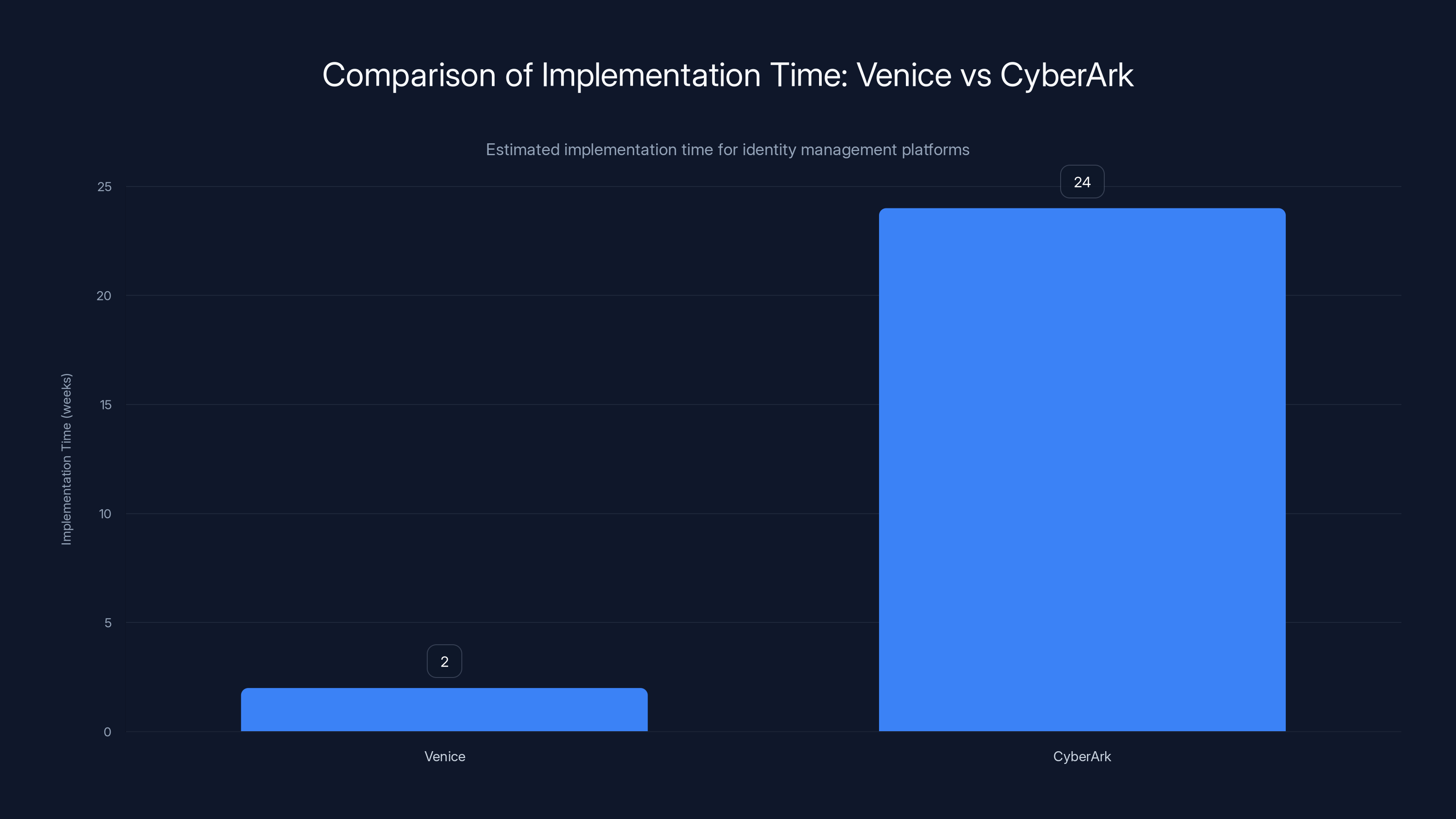
Venice's AI-powered automation significantly reduces implementation time from up to 24 weeks with CyberArk to just 1-2 weeks. Estimated data.
The Identity Management Market Landscape: Understanding the Incumbents
CyberArk's Dominance and Market Position
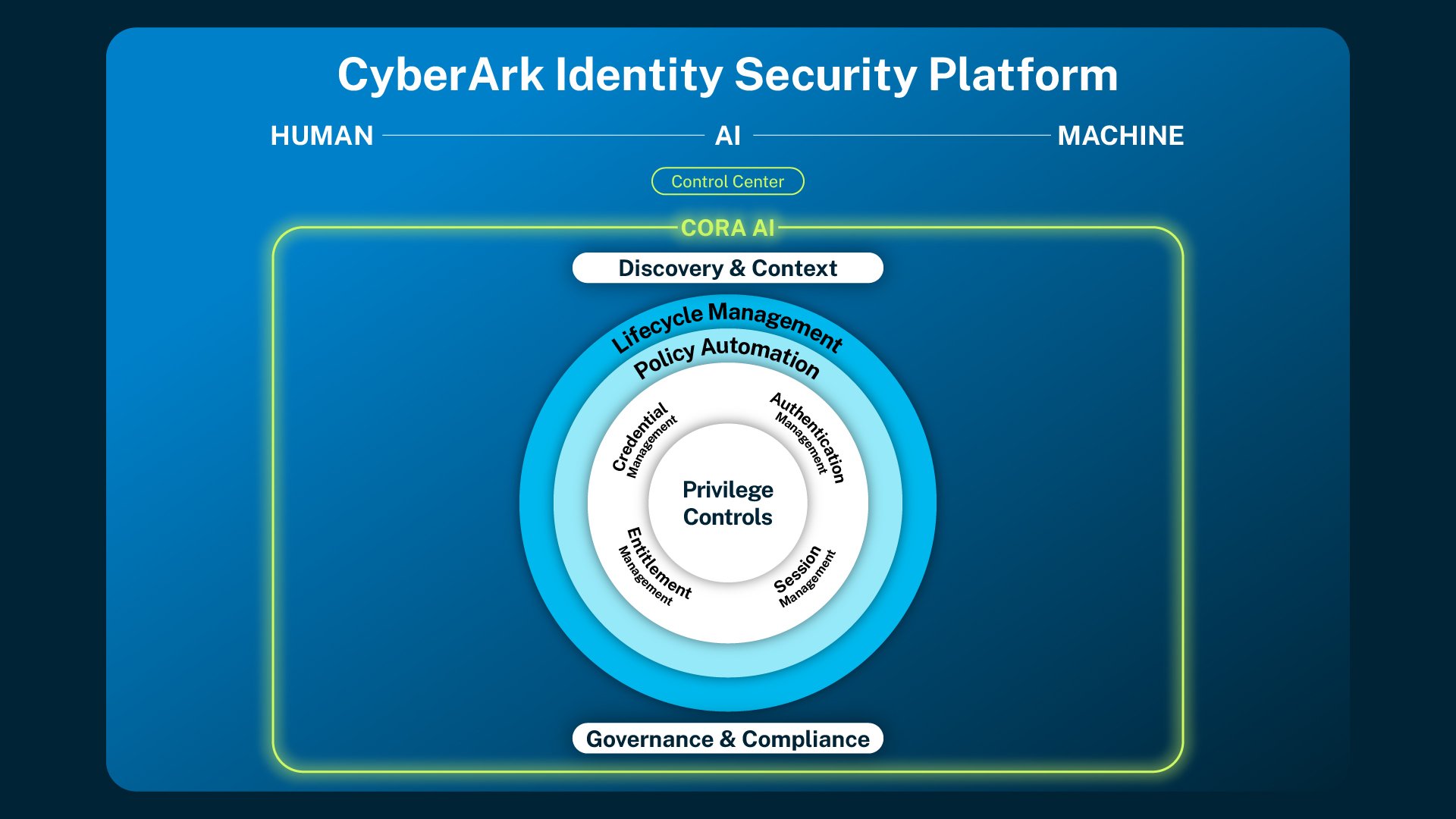
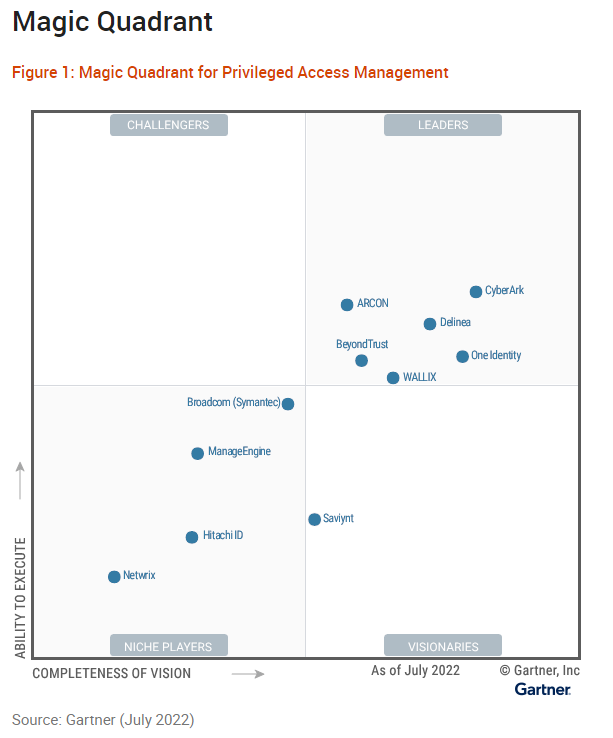
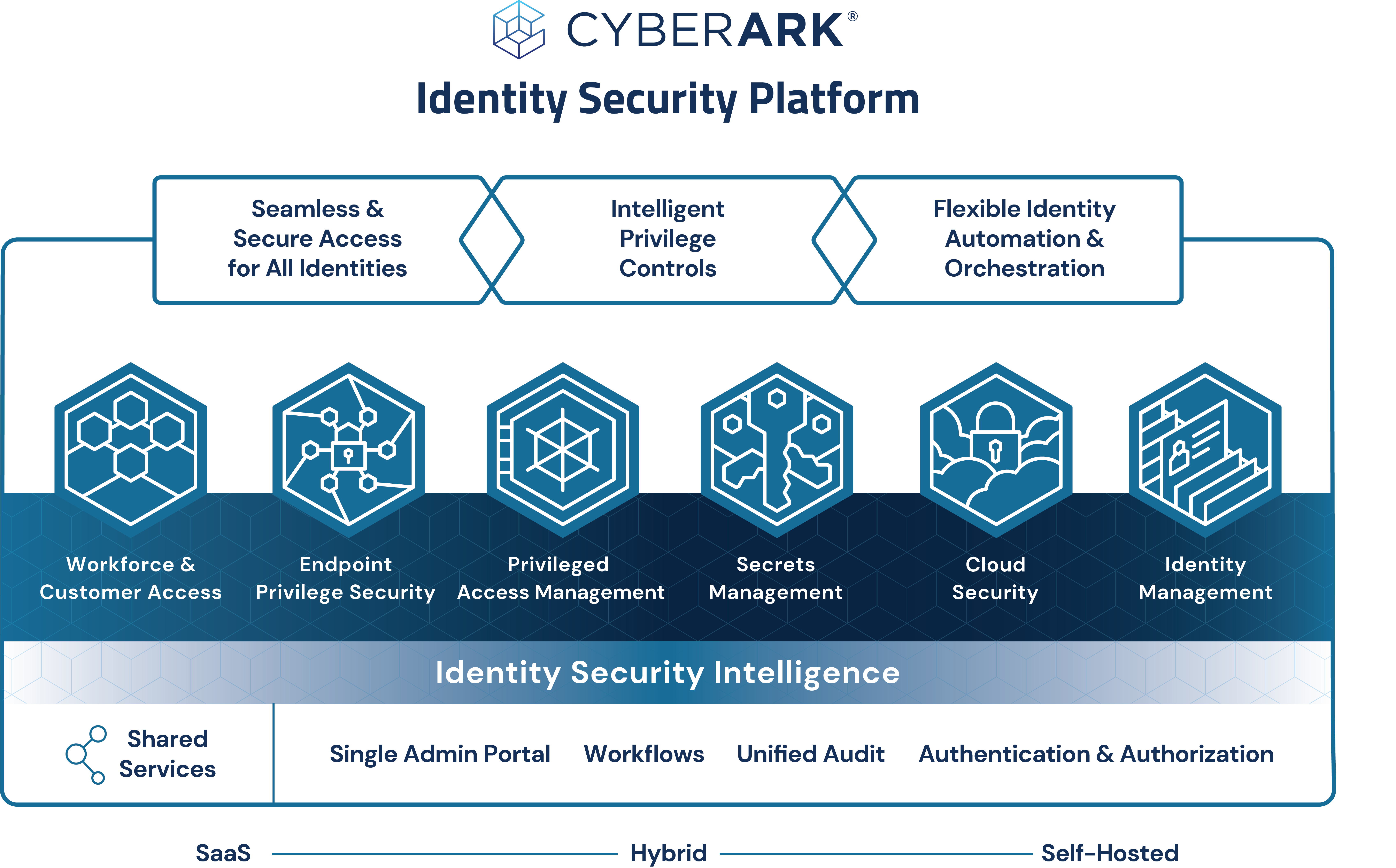
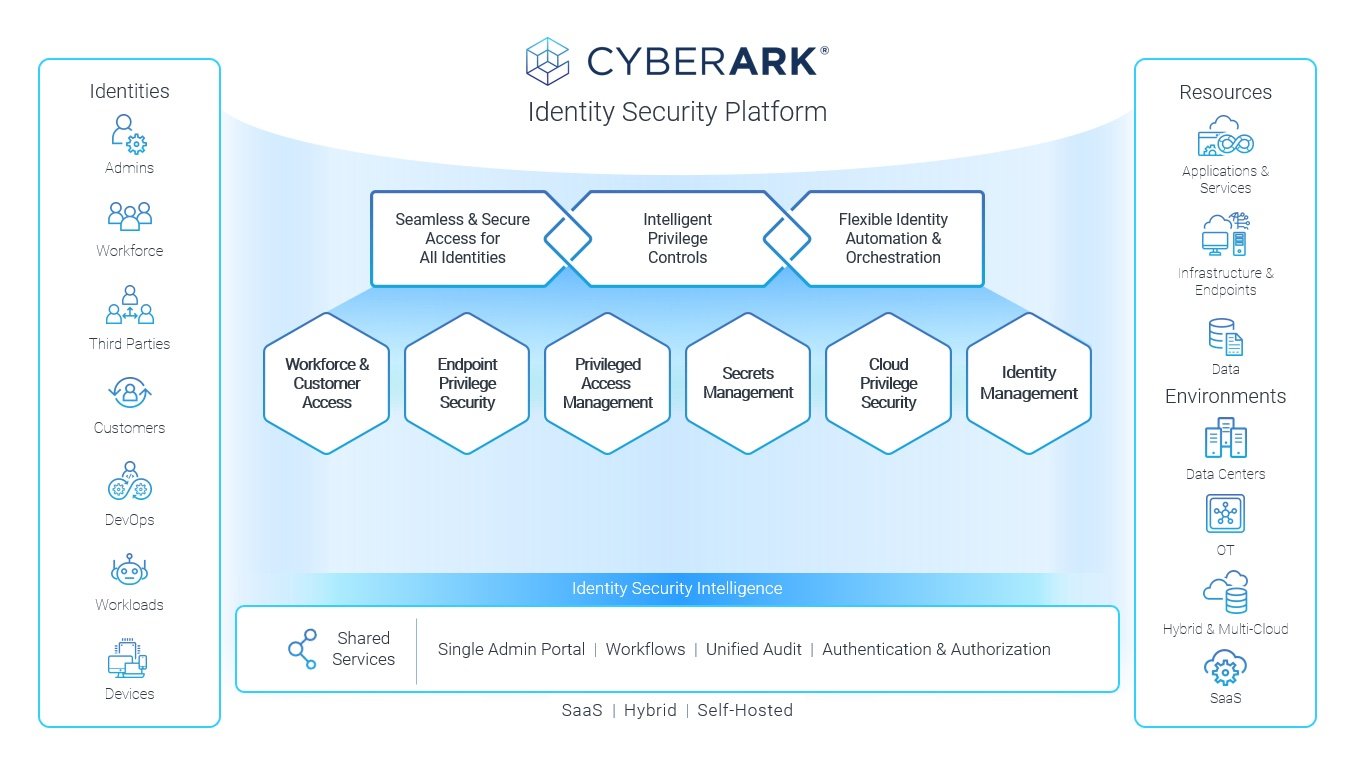
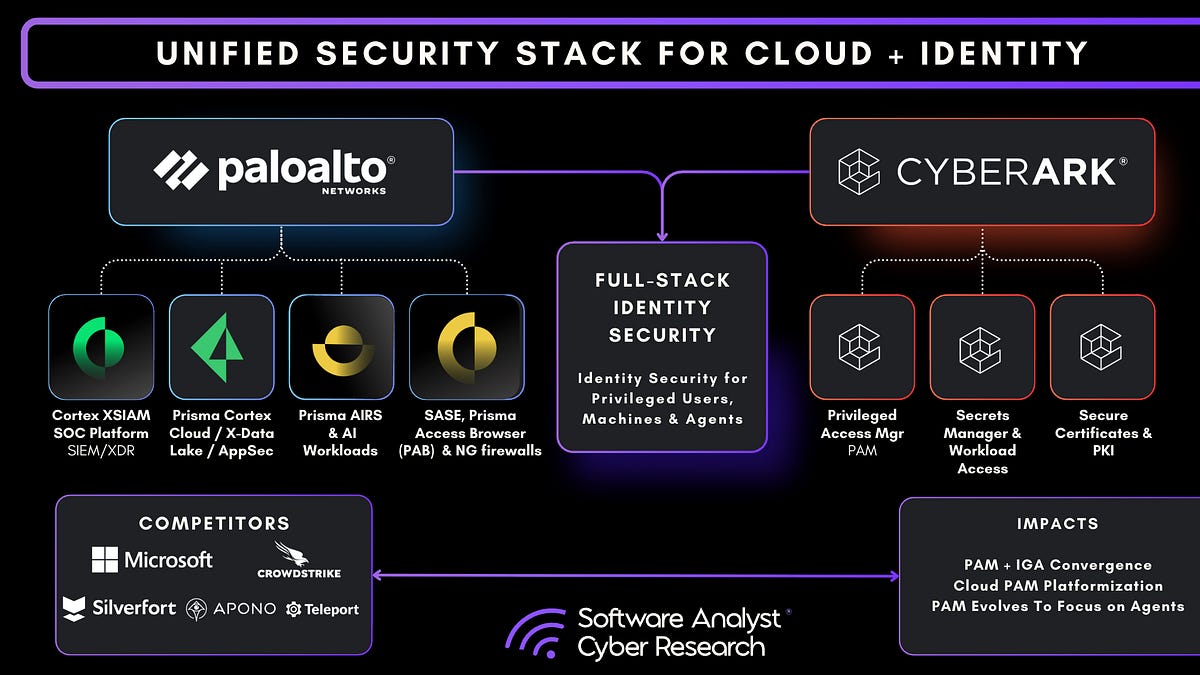
CyberArk has long occupied the leadership position in the privileged access management market, commanding the largest market share and highest valuation multiples among PAM vendors. The company's dominance rests on several foundational strengths that have accumulated over two decades of market leadership.
First, CyberArk pioneered the modern PAM category itself. The company's Privileged Account Security solution established many of the market conventions and expectations around how PAM systems should function. When CyberArk IPO'd in 2014, it signaled the venture capital and enterprise software worlds that privileged access management represented a massive, sustained market opportunity.
Second, CyberArk has built a moat through integration depth and extensive customization capabilities. Large enterprises have invested millions in CyberArk implementations, often customized to fit their specific infrastructure idiosyncrasies. These implementations create switching costs—the burden of ripping out a CyberArk system and replacing it with an alternative is substantial, requiring significant engineering effort, downtime planning, and extensive testing.
Third, CyberArk benefits from entrenched channel partnerships and security consulting relationships. Many enterprises encounter CyberArk through relationships with major system integrators and security consultancies. These partnerships create a self-reinforcing cycle where recommendations flow toward the incumbent.
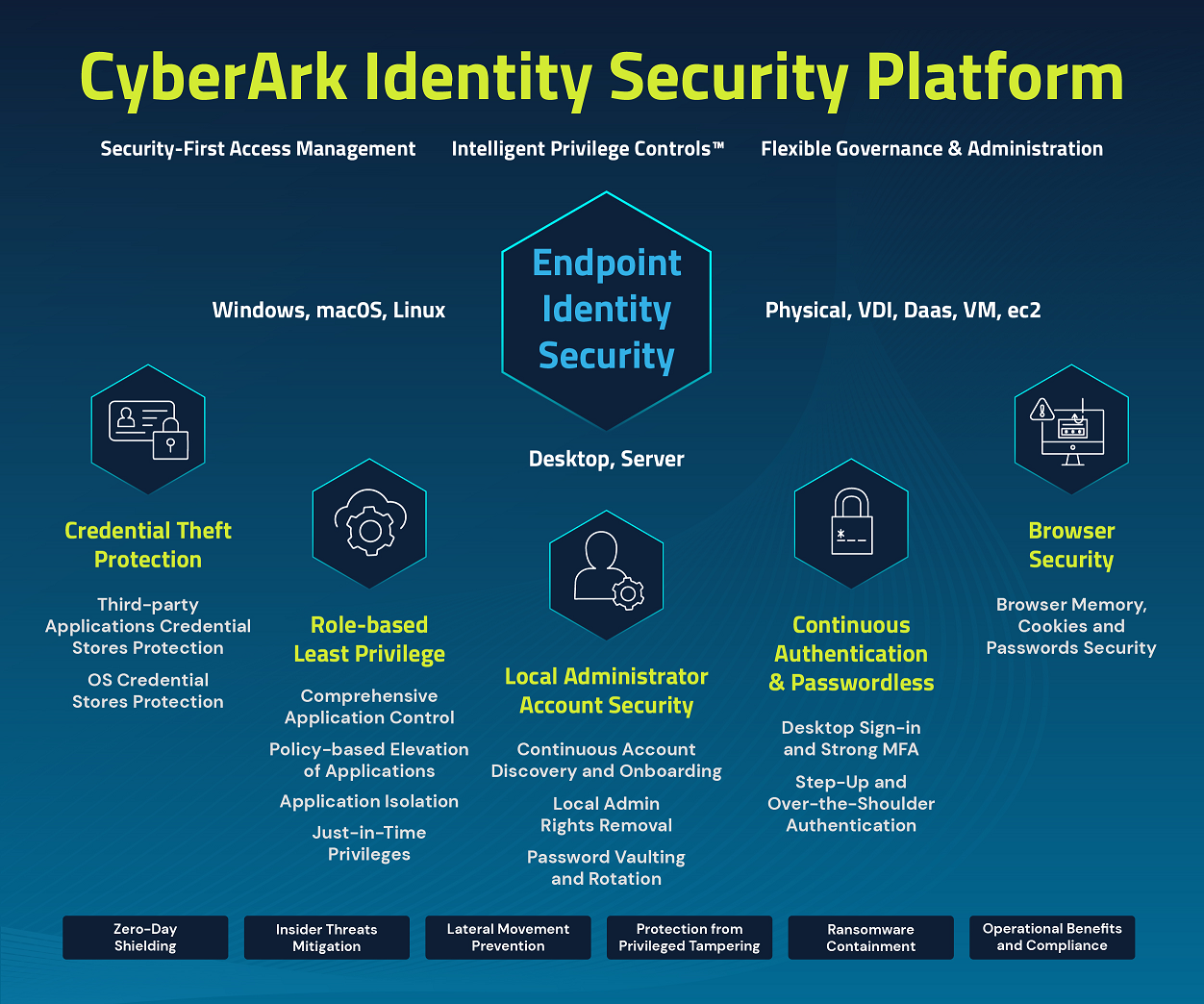
Yet CyberArk's dominance also reflects historical constraints that increasingly limit its applicability. The company's architecture was optimized for a previous era of IT management—one characterized by relatively static permission models, human-centric access patterns, and slower change cycles. The platform's strength in managing privileged access for on-premises systems becomes something of a limitation in an increasingly cloud-first world.
Okta's Evolution and Market Positioning
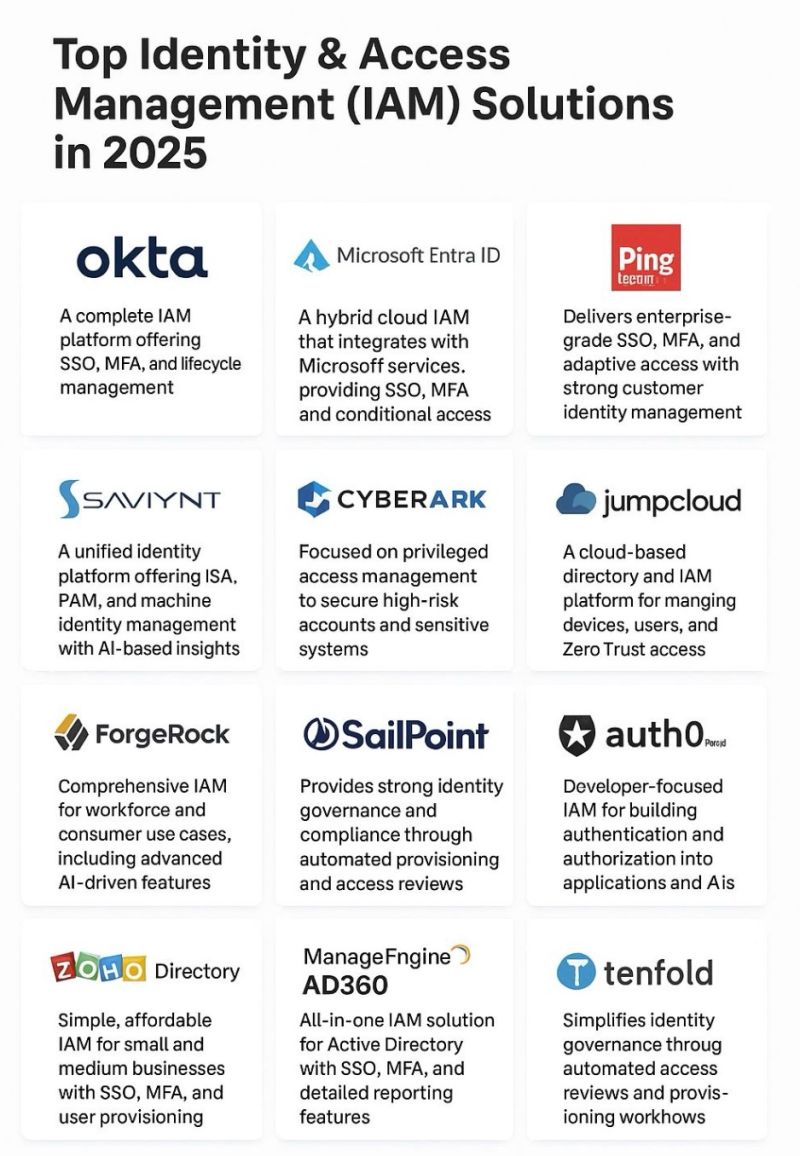
Okta represents the second major force in the identity management landscape, though operating in a somewhat different niche than CyberArk. While CyberArk dominates privileged access management, Okta has established strong market position in identity and access management more broadly, with particular strength in SaaS application access and cloud infrastructure.
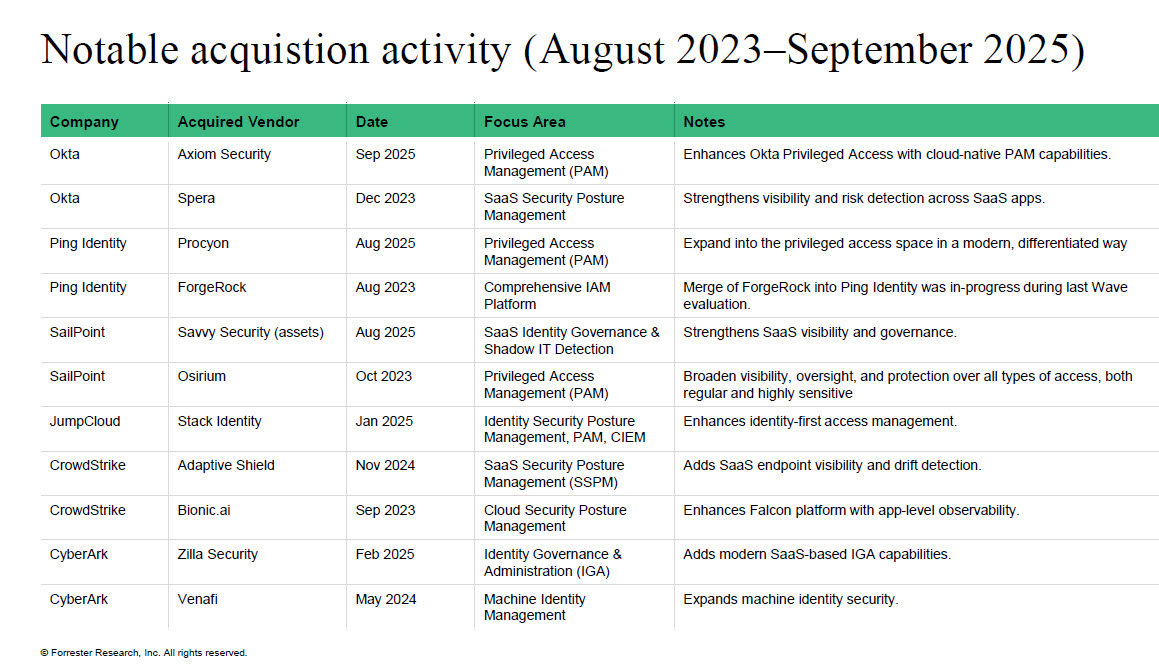
Okta's platform was engineered from the ground up for the cloud era, giving the company advantages in cloud-native environments where CyberArk's on-premises legacy creates friction. Okta has successfully positioned itself as the identity platform for modern cloud infrastructure and SaaS ecosystems, and the company's ecosystem of integrations and partner relationships reflects this cloud-first orientation.
Okta's market strength has attracted competition and growth challenges over recent years, but the company remains a formidable incumbent with deep customer relationships across enterprise, mid-market, and increasingly, government segments. The company's acquisition spree—including purchases of Auth0, Okta's existing identity infrastructure, and various specialized identity vendors—reflects an ambition to create increasingly comprehensive identity platforms.
Emerging Competitors: Persona, Veza, and GitGuardian
The identity management market has attracted considerable venture capital investment, spawning a cohort of well-funded startups attempting to challenge incumbents or establish new categories within the broader identity ecosystem.
Persona focuses on identity verification and fraud detection, raising a $200 million Series D in April 2024, and has established strong market position in regulated industries where identity verification represents a critical requirement. The company's focus on consumer identity and compliance represents a different market than Venice's enterprise PAM approach, though the broader category remains identity infrastructure.
Veza closed a $108 million Series D in May 2025, positioning itself around cloud authorization and infrastructure access. Veza's approach centers on providing visibility and control over permissions in cloud environments—addressing the exact problem space where traditional on-premises-focused vendors struggle. The company competes more directly with Venice's ambitions to address cloud and hybrid environments, though Veza's approach emphasizes visibility and governance rather than consolidation.
GitGuardian raised $50 million to focus on secrets management and protection—detecting exposed credentials across code repositories and infrastructure. This represents an adjacent market to identity management, addressing the downstream consequences of poor credential hygiene rather than the upstream access management problem that Venice tackles.
These emerging competitors reflect a market understanding that the incumbent vendors—while still dominant—are vulnerable to disruption. The venture capital flowing into identity management startups signals investor conviction that new approaches and architectures can win in this space.
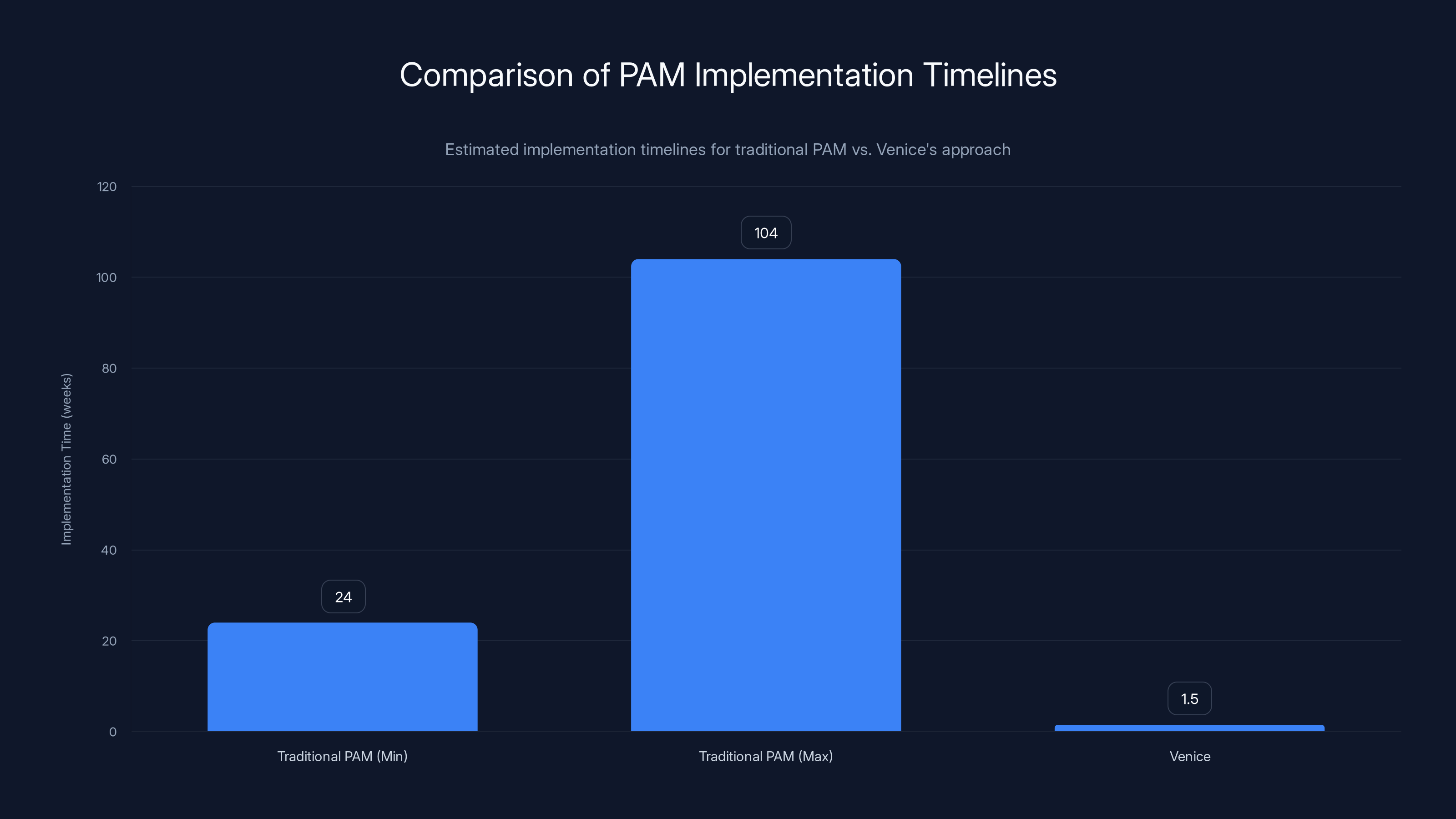
Venice claims to reduce PAM implementation time from a range of 6 months to 2 years to just 1.5 weeks, potentially transforming the economic viability for smaller organizations. Estimated data.
Venice's Technical Architecture: Consolidating Sprawl
The Multi-Layer Integration Challenge
Venice's fundamental technical challenge is genuinely difficult: building a system that spans on-premises infrastructure, SaaS applications, and cloud infrastructure—all with unified governance, visibility, and access controls. This breadth explains why most identity vendors choose to specialize in one layer of this stack rather than attempting comprehensive coverage.
On-premises privileged access management demands deep integration with Windows Active Directory, Unix/Linux systems, database servers, and legacy applications. These systems were built when network boundaries were meaningful and security models emphasized network perimeter defense. Integrating with these systems requires understanding decades of accumulated conventions, peculiar authentication mechanisms, and custom access control models that vary widely across enterprises.
SaaS application access represents a completely different technical problem. Rather than managing access to systems your organization controls, SaaS access management requires integrating with external systems via APIs, managing federated identity, and dealing with the fact that the vendor controls the platform while you control only how your users interact with it. Each SaaS application implements identity and access management slightly differently, creating complex integration requirements.
Cloud infrastructure access adds another layer of complexity entirely. Public cloud platforms like AWS, Azure, and Google Cloud have developed sophisticated, API-first identity and access models that are fundamentally different from either on-premises or SaaS approaches. Managing permissions across multiple cloud accounts, regions, and resource types requires understanding cloud-native concepts that didn't exist in the on-premises PAM world.
AI-Powered Automation and Implementation Acceleration
Venice's approach to condensing multi-year implementations into weeks relies heavily on AI-powered automation of the discovery, classification, and migration process. The company's promise is that AI can automatically identify existing permissions across these disparate systems, understand the relationships between them, and intelligently map permissions from legacy systems into Venice's unified model.
This capability addresses one of the primary reasons PAM implementations historically take 6-24 months: the painstaking manual process of discovering what permissions currently exist, understanding why they exist, identifying dependencies, and ensuring that migrations don't break critical business processes. When done manually by consulting teams, this discovery and migration process becomes prohibitively expensive and time-consuming.
By automating this process with AI, Venice can potentially compress a 6-month discovery phase into days or weeks. The AI system learns to recognize permission patterns, understand organizational hierarchies, identify outliers that might indicate security risks, and suggest optimal mappings into the new system architecture.
This acceleration addresses a critical pain point in traditional PAM deployments. Many enterprises begin PAM projects with genuine urgency—responding to security incidents, compliance requirements, or board-level directives. Yet the glacial pace of traditional implementations means security needs often outpace implementation progress. By the time a CyberArk deployment is complete, the organizational structure has changed, new applications have been deployed, and new security requirements have emerged, partially negating the benefits of the original project.
Unified Visibility Across Identity Silos
Beyond consolidation and automation, Venice's value proposition includes providing unified visibility into permissions across these previously-isolated systems. This visibility is genuinely important. Most enterprises, if asked directly, cannot answer basic questions about their access posture: How many users have administrative access? Which permissions are actually in use versus vestigial and forgotten? What's the path from a compromised standard user account to critical infrastructure? Which systems have permissions that don't align with approved role definitions?
Traditional PAM systems provide detailed visibility into the systems they manage—but only those systems. A user might have adequate visibility into on-premises privileged access through CyberArk while remaining nearly blind to SaaS application access patterns and cloud infrastructure permissions. Venice's consolidation approach enables security teams to see the full picture of who can do what across their entire infrastructure.
This unified visibility enables new security capabilities. Rather than treating just-in-time access as a concept that applies only to on-premises PAM, Venice can extend just-in-time, least-privilege principles across cloud infrastructure, SaaS applications, and on-premises systems. Users (and AI agents) request access to specific resources for specific time periods, and the system grants exactly what's needed, nothing more, revoking access automatically when the time period expires.
The AI Agent Imperative: Reshaping Identity Requirements
Non-Human Identities and Autonomous Systems
One of the most compelling drivers of Venice's market timing is the acceleration of AI agents and autonomous systems in enterprise environments. Traditional identity management systems were built assuming that users were human beings with relatively predictable access patterns. An admin logs in to change a configuration. A developer uses their credentials to access code repositories. A database administrator connects to database servers.
AI agents fundamentally change this picture. An AI agent managing customer support queries might need simultaneous access to multiple SaaS systems (CRM, knowledge base, ticketing system), cloud infrastructure (for analytics and logging), and even on-premises databases (for customer historical data). A robotic process automation system might need scheduled access to dozens of systems, each at specific times, with precise permissions for specific tasks.
Traditional identity systems weren't designed for this scenario. Giving an AI agent a standard user account with broad permissions violates least-privilege principles. Yet managing time-limited, task-specific access for dozens or hundreds of AI agents across multiple systems becomes impossible with traditional PAM approaches designed for dozens of human administrators.
Venice's architecture—specifically its emphasis on just-in-time access and non-human identity support—was explicitly designed with this AI agent reality in mind. The platform can provision and deprovision AI agent credentials dynamically, granting exactly the permissions needed for a specific task and automatically revoking them when the task completes.
The Privileged Access Problem for Agents
Ironically, AI agents and automation systems often require privileged access to accomplish their tasks. A data pipeline might need administrative access to a data warehouse to restructure tables. A security automation system might need root access to servers to patch vulnerabilities. An AI system managing infrastructure might need to provision and deprovision cloud resources.
Granting AI agents privileged access without proper controls and visibility is a security nightmare. If an AI agent's credentials are compromised—or if the AI system itself is compromised—an attacker gains exactly the kind of privileged access that causes catastrophic breaches. Properly managing privileged access for AI agents and ensuring that access is time-limited, audit-logged, and properly revoked is a critical security requirement that traditional PAM systems weren't designed to address.
Venice's approach to this problem involves several components: (1) treating AI agents as first-class identity subjects alongside human users, (2) implementing granular, time-limited access controls specifically designed for non-human entities, (3) providing comprehensive audit logging that tracks what AI agents accessed and what they did, and (4) enabling automated policy enforcement that can revoke access if unexpected behavior is detected.
This capability matters increasingly as enterprises deploy more sophisticated automation and AI systems. The company's positioning around this specific problem—one that's newly critical but not yet well-addressed by incumbents—represents a genuine insight into market evolution.
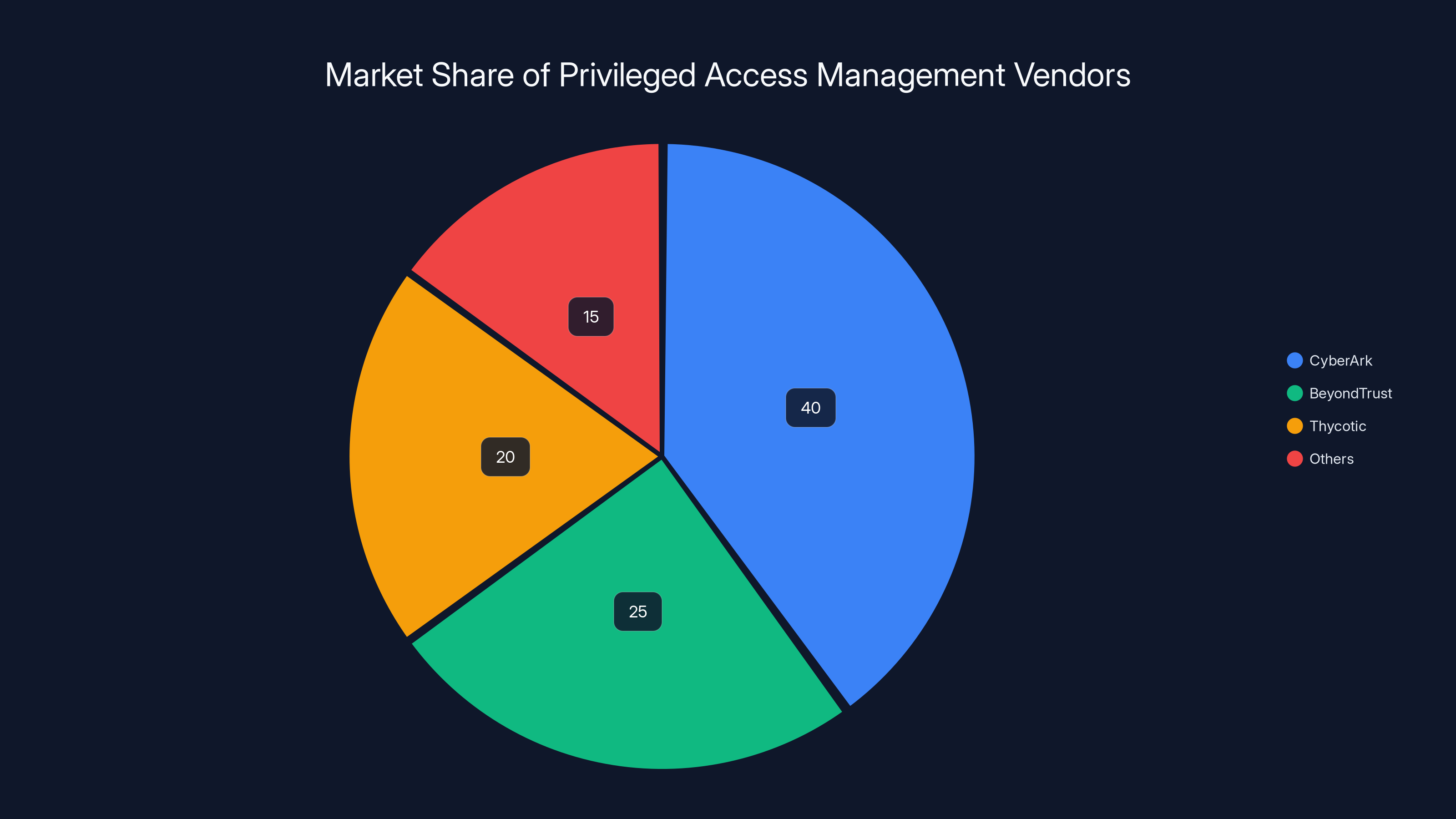
CyberArk leads the PAM market with an estimated 40% share, followed by BeyondTrust and Thycotic. Estimated data based on industry insights.
Implementation Speed and Operational Impact
The Professional Services Tax in Traditional PAM
One of the most interesting aspects of Venice's value proposition involves what CEO Lurie calls the "professional services tax"—the reality that traditional PAM implementations typically require extensive consulting engagement and multi-month implementation timelines. This isn't a peculiarity of CyberArk specifically; it's endemic to complex identity management deployments across multiple vendors.
The reasons are rooted in the legitimate complexity of these implementations. Discovering existing permissions across heterogeneous infrastructure requires domain expertise. Designing access policies that maintain security while enabling business processes requires understanding organizational structures and risk profiles. Migrating existing permissions from legacy systems without disrupting business-critical functions demands careful planning and testing.
Yet the net result is that enterprises often spend
Venice's claim that it can compress implementation timelines to 1.5 weeks—from the typical 6 months to 2 years—would fundamentally alter the economics of PAM deployment. If the claim is accurate, it would reduce total cost of ownership dramatically, making PAM deployment economically viable for organizations below the Fortune 500 level where traditional PAM implementations remain common.
Automation of Discovery and Migration
The mechanisms enabling this acceleration deserve examination. Venice's approach relies on several automation layers that traditional PAM deployments handle manually or semi-manually.
Automated discovery is the first layer. Rather than having consultants manually query Active Directory, scan LDAP directories, inventory SSH access patterns, and catalog SaaS application assignments, Venice's platform includes automated discovery agents that can scan infrastructure and automatically identify existing permissions, access patterns, and role definitions.
AI-powered analysis of discovered permissions represents the next layer. Rather than having security architects manually review discovered permissions and categorize them into role definitions, AI can analyze patterns, identify natural groupings, and suggest role structures that align with discovered permissions. This analysis can identify outlier permissions that don't fit standard patterns, potentially indicating security risks or policy violations.
Automated migration completes the process. Once permissions are discovered and understood, the platform can automatically generate migration scripts and actions to move permissions from legacy systems into Venice's unified model. This reduces the manual effort required to perform the actual migration.
The net effect is that a process traditionally requiring dozens of person-weeks of consulting effort can potentially be reduced to a few person-weeks of Venice staff and customer IT coordination. Assuming consulting costs of $200-300 per hour, this reduction translates to millions of dollars in avoided professional services costs.

Market Dynamics and Customer Traction
Fortune 500 and Fortune 1000 Customer Base
Venice's fundraising announcement includes claims of customer traction that would be remarkable if accurate. Lurie stated that Venice is "completely replacing" legacy vendors like CyberArk and Okta at Fortune 500 and Fortune 1000 customers, though the company did not name these customers publicly (citing customer confidentiality agreements).
Off the record, Lurie mentioned specific examples: a 170-year-old publicly traded manufacturing company and a global music conglomerate were among early customers. If these accounts represent typical customer profiles, Venice is targeting precisely the enterprises that represent the most valuable customers for CyberArk and other incumbents—large, complex organizations with significant identity management needs and budgets to fund sophisticated security solutions.
Landing Fortune 500 customers in a startup's first two years is extraordinarily challenging. These customers typically evaluate vendors extensively, require proven security credentials, demand comprehensive feature sets, and often insist on vendor viability assessments to mitigate procurement risk. That Venice claims to have landed such customers suggests either exceptional execution, compelling technical differentiation, or strategic luck in identifying early champions within target accounts.
Market Receptiveness to Alternative Solutions
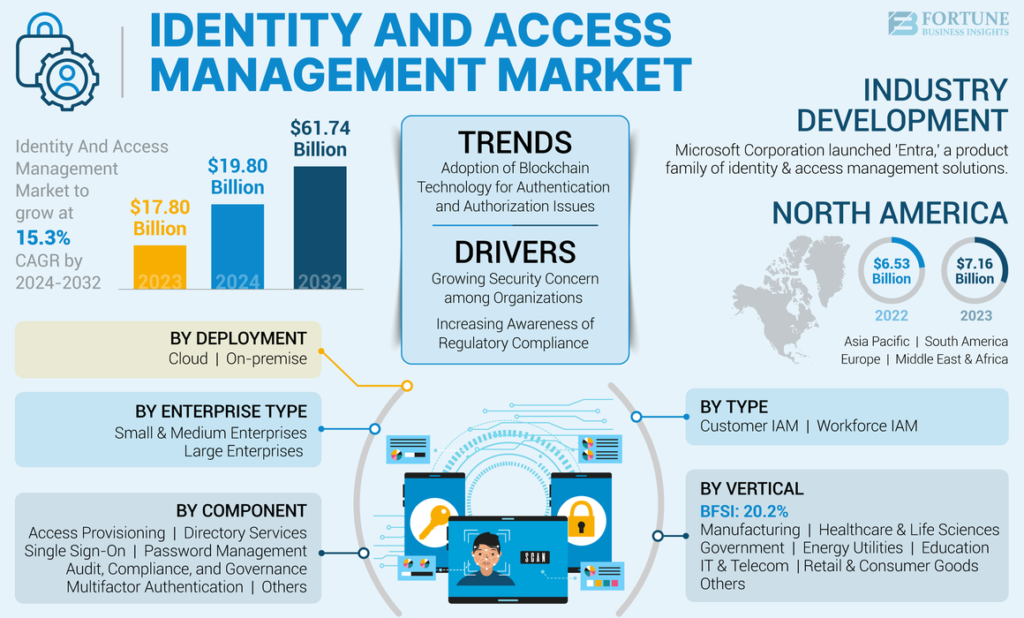
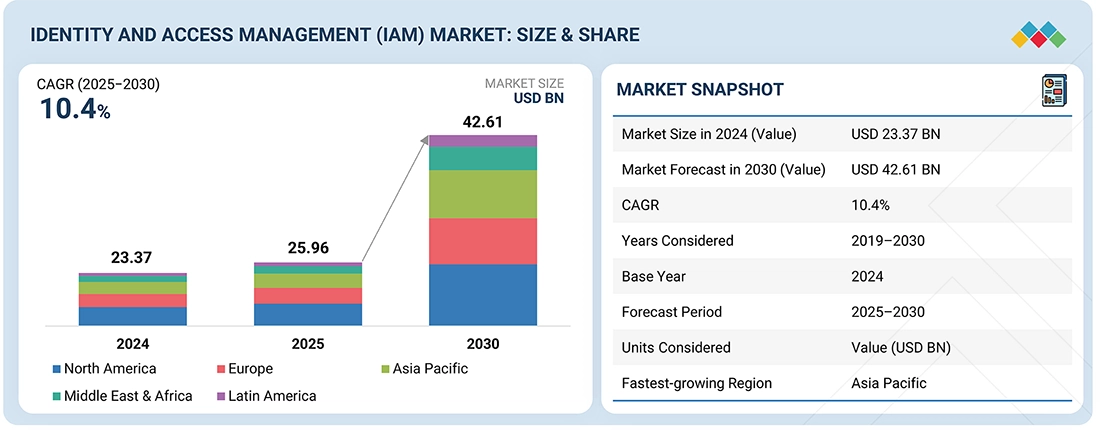
The broader identity management market appears increasingly receptive to alternative approaches and new entrants. The $24 billion market size for identity and access management in 2025, with 13% year-over-year growth, reflects strong underlying demand. This growth rate—outpacing overall enterprise software growth—suggests that identity management remains a prioritized budget category for enterprises.
Moreover, the venture capital flowing into identity management startups signals that institutional investors perceive incumbent solutions as vulnerable. Multiple funding rounds for Persona, Veza, and GitGuardian, combined with $20 million in Series A funding for Venice, reflect conviction among sophisticated investors that the market is fragmented enough to support new entrants.
This receptiveness likely reflects several factors: (1) the genuine complexity and cost of PAM implementations creating demand for simpler alternatives, (2) the mismatch between legacy vendor architectures and cloud-native requirements, (3) the emergence of AI agents as a new use case that existing platforms weren't designed to address, and (4) the general fatigue among enterprise customers with complex, expensive implementations that don't fully solve their problems.

Estimated market share distribution in 2025 shows significant presence of new entrants like Venice, indicating a shift in the identity management landscape. Estimated data.
Competitive Positioning: How Venice Compares
Head-to-Head with CyberArk: Architecture and Approach
While Venice and CyberArk operate in related market spaces, their architectural approaches diverge in meaningful ways. CyberArk's strength lies in comprehensive privileged access management for on-premises infrastructure combined with deep integration capabilities that address years of accumulated enterprise complexity. The platform handles credential management, session recording, analytics, and policy enforcement in ways that reflect two decades of iterative refinement targeting large enterprises.
Venice's approach explicitly trades some depth in on-premises specificity for breadth across the full stack of on-premises, cloud, and SaaS infrastructure. Rather than attempting to be the comprehensive solution for everything within a single category, Venice positions itself as the consolidation layer that sits across multiple systems.
This architectural choice has interesting implications. CyberArk can claim comprehensive depth in PAM and point to capabilities that Venice might need years to match. Yet Venice can argue that comprehensive depth in a single layer matters less when enterprises still need solutions for managing cloud infrastructure and SaaS access—exactly where CyberArk's on-premises focus creates friction.
The comparison is roughly analogous to the evolution from specialized email servers (Microsoft Exchange) to cloud-based communication platforms (Microsoft Teams/Slack). The specialized solution might have advantages in specific capabilities, but the consolidation solution wins if the trade-off of some depth for breadth makes sense for customer use cases.
Comparison with Okta
Venice and Okta operate with somewhat different scopes, though there's meaningful overlap. Okta's strength lies in cloud identity and access management, particularly for SaaS applications and cloud infrastructure. The platform was engineered for cloud from inception, giving it architectural advantages in cloud-native environments.
Venice's advantage lies in the specific combination of on-premises, cloud, and SaaS coverage—addressing the hybrid IT environment that remains prevalent in large enterprises. Most Fortune 500 companies cannot simply shut down their on-premises infrastructure and move entirely to cloud. They operate hybrid environments combining legacy on-premises systems, cloud infrastructure from one or more providers, and hundreds of SaaS applications.
Okta has attempted to address the on-premises gap through various approaches, including identity bridge technologies and API integration, but these approaches introduce complexity and potential security boundaries. Venice's native support for both on-premises and cloud infrastructure potentially addresses this gap more elegantly.
Differentiation Through AI and Implementation Speed
Beyond architectural scope, Venice's primary differentiation claim centers on AI-powered automation and the resulting implementation speed. This differentiation is genuinely difficult to evaluate without hands-on experience with the product, but the claim is compelling if accurate.
Reducing PAM implementation timelines from 6-24 months to 1-2 weeks would represent a genuine breakthrough in addressing a critical pain point. If Venice can deliver on this promise consistently, it creates a powerful competitive advantage that's difficult for incumbents to counter. CyberArk could theoretically accelerate its own implementations, but doing so might destabilize the professional services relationships and ecosystem partnerships that contribute substantially to CyberArk's revenue model.
Market Drivers and Industry Trends
Cloud Infrastructure Proliferation
The shift toward cloud infrastructure represents one of the most significant market drivers benefiting platforms like Venice. Most large enterprises are mid-journey through cloud migration, with complex hybrid environments combining multiple public cloud providers (AWS, Azure, Google Cloud), private cloud infrastructure, and on-premises systems.
This proliferation creates identity management challenges that on-premises-focused PAM solutions weren't designed to address. Managing access to resources spread across multiple cloud accounts and providers, each with distinct identity models, requires fundamentally different approaches than managing access to on-premises infrastructure.
Venice's platform was architected with multi-cloud environments in mind, giving it advantages in this increasingly important scenario. Enterprises migrating workloads to cloud infrastructure face difficult choices: rip-and-replace their existing PAM infrastructure with cloud-native alternatives (losing on-premises management capabilities), or attempt to extend existing on-premises solutions into cloud environments (creating integration complexity and potential blind spots).
Venice's offering to address this challenge—a single platform providing unified access management across on-premises and multi-cloud infrastructure—directly addresses this market inflection point.
The Shift to Zero Trust Security Models
Zero trust security, a model that treats network boundaries as irrelevant and assumes breach, requires comprehensive identity and access management as a foundational component. Rather than relying on network perimeter security (the castle-and-moat model), zero trust requires verifying every access request against policy, regardless of network location.
Zero trust models naturally favor solutions that provide comprehensive visibility and fine-grained control across all access vectors—precisely what Venice claims to offer. While incumbents like CyberArk can certainly support zero trust implementations, solutions built explicitly with zero trust principles often have architectural advantages.
Compliance and Regulatory Evolution
Compliance requirements continue to evolve, with regulators increasingly focused on identity and access management as a critical control. SOC 2, HIPAA, PCI-DSS, GDPR, and industry-specific regulations all include identity management requirements. Enterprise customers often undertake PAM implementations specifically to satisfy compliance requirements.
As regulatory requirements become more stringent, the ability to demonstrate comprehensive access management, fine-grained policy enforcement, and complete audit trails becomes more important. Venice's positioning around unified visibility and enforcement across the full stack of infrastructure aligns with evolving compliance requirements that single-layer solutions struggle to address.
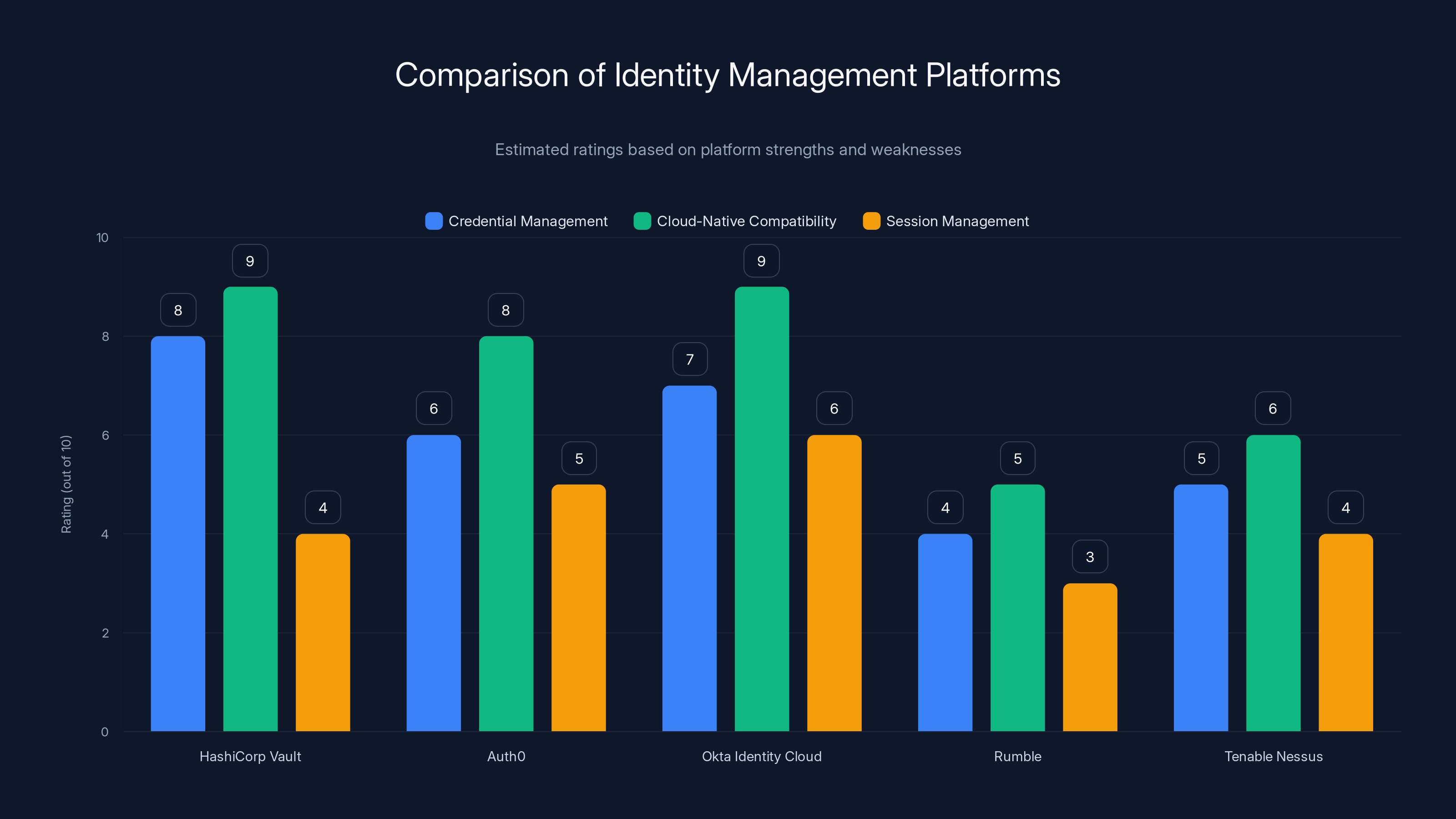
This chart compares various identity management platforms based on estimated ratings for credential management, cloud-native compatibility, and session management. Estimated data highlights the strengths and weaknesses of each platform.
Alternative Solutions and Complementary Approaches
Other Identity Management Platforms Worth Considering
While Venice and the incumbent vendors represent the most prominent options in the identity management space, several alternative approaches and platforms deserve consideration depending on specific organizational needs.
HashiCorp Vault represents a different approach to credential management, focusing on dynamic credentials and secrets management rather than traditional PAM. Vault is particularly popular in cloud-native and DevOps environments where static credentials create security risks. Organizations with strong infrastructure-as-code practices and CI/CD pipelines often find Vault's approach more aligned with their operational models than traditional PAM solutions. Vault's strength lies in managing secrets and rotating credentials programmatically, while its weakness involves the lack of comprehensive session management and endpoint privilege management features that mature PAM solutions provide.
Auth0 (owned by Okta) and Okta's Identity Cloud represent Okta's broader identity platform play, particularly strong for SaaS application access and cloud-native authentication scenarios. For organizations primarily concerned with managing access to SaaS applications and modern cloud infrastructure, Okta's approach often involves less complexity and cost than traditional PAM solutions. However, Auth0 struggles with on-premises infrastructure access and privileged access management at the depth that CyberArk provides.
Rumble and Tenable Nessus represent yet another approach—vulnerability and asset management platforms that include some identity and access visibility components. These solutions excel at understanding what systems and applications exist in your environment and identifying security misconfigurations, but lack the active access management and enforcement capabilities of dedicated PAM solutions. They work well as complementary tools that feed discovery data into dedicated PAM solutions.
JumpCloud Directory Platform represents a cloud-native identity management approach specifically designed for organizations with distributed workforces and bring-your-own-device (BYOD) environments. JumpCloud's strengths lie in user lifecycle management, device trust, and modern multi-factor authentication, making it particularly suitable for organizations with limited on-premises infrastructure. The platform lacks the depth in privileged access management and session recording that enterprise PAM solutions provide.
Evaluating Runable as a Complementary Automation Layer
For teams building modern applications and managing complex identity infrastructures, complementary automation platforms like Runable offer interesting capabilities that work alongside dedicated identity management solutions. Runable provides AI-powered workflow automation and developer productivity tools starting at $9/month, enabling teams to automate aspects of identity and access management operations that would otherwise require manual effort.
While Runable is not a primary identity management solution, its capabilities in automated documentation, AI-powered reporting, and workflow automation could serve as useful complements to Venice, CyberArk, or other PAM solutions. For example, Runable's AI agents could potentially automate the generation of access reports, automatically document permission structures, or orchestrate routine access management workflows.
Organizations evaluating comprehensive identity management solutions might consider whether complementary automation platforms could help address the implementation and operational efficiency challenges that traditional solutions struggle with. This represents a different approach than consolidating everything into a single platform—instead, it involves strategic specialization where platforms focus on core capabilities while automation layers handle operational efficiency.

Evaluation Criteria for Choosing an Identity Platform
Core Capability Assessment
When evaluating identity management solutions, organizations should begin by assessing what systems require identity management. Do you operate primarily on-premises infrastructure? Heavily cloud-based with minimal on-premises systems? A hybrid environment combining both? The answer fundamentally shapes which solution architecture makes sense.
Organizations with primarily cloud-based infrastructure and SaaS-heavy application portfolios should evaluate cloud-native solutions like Okta carefully, as these platforms were designed for exactly this scenario. Organizations with significant on-premises infrastructure and complex legacy system requirements might find traditional PAM solutions like CyberArk better suited to immediate needs, even if long-term architecture transitions toward newer approaches.
Hybrid organizations face the most complex choices, as they often cannot find a single solution optimally designed for all their requirements. This scenario is precisely where Venice positions itself—as the single platform designed to span hybrid environments without requiring multiple specialized solutions and the integration complexity they create.
Implementation Considerations
Beyond the platform itself, evaluate the implementation approach and support model carefully. Does the vendor require extensive consulting engagement or can the platform be implemented primarily through self-service? Do you have internal staff with requisite expertise or will you depend on vendor-provided implementation services?
Venice's claim around rapid implementation is valuable primarily if you can actually capitalize on it. If your team lacks expertise in identity management and requires vendor support regardless, the theoretical speed advantage might not translate to practical benefits. Conversely, if you have strong internal expertise and want to move quickly with minimal consulting dependency, speed becomes a primary differentiator.
Total Cost of Ownership
Compute total cost of ownership across software licensing, implementation services, ongoing support, and operational staff time. A lower-cost licensing solution that requires extensive consulting and ongoing manual operations might have a higher TCO than a higher-cost solution that includes comprehensive automation and minimal operational overhead.
Venice's positioning around reduced implementation costs is particularly relevant to TCO calculations. If the company can genuinely reduce implementation from 18 months and
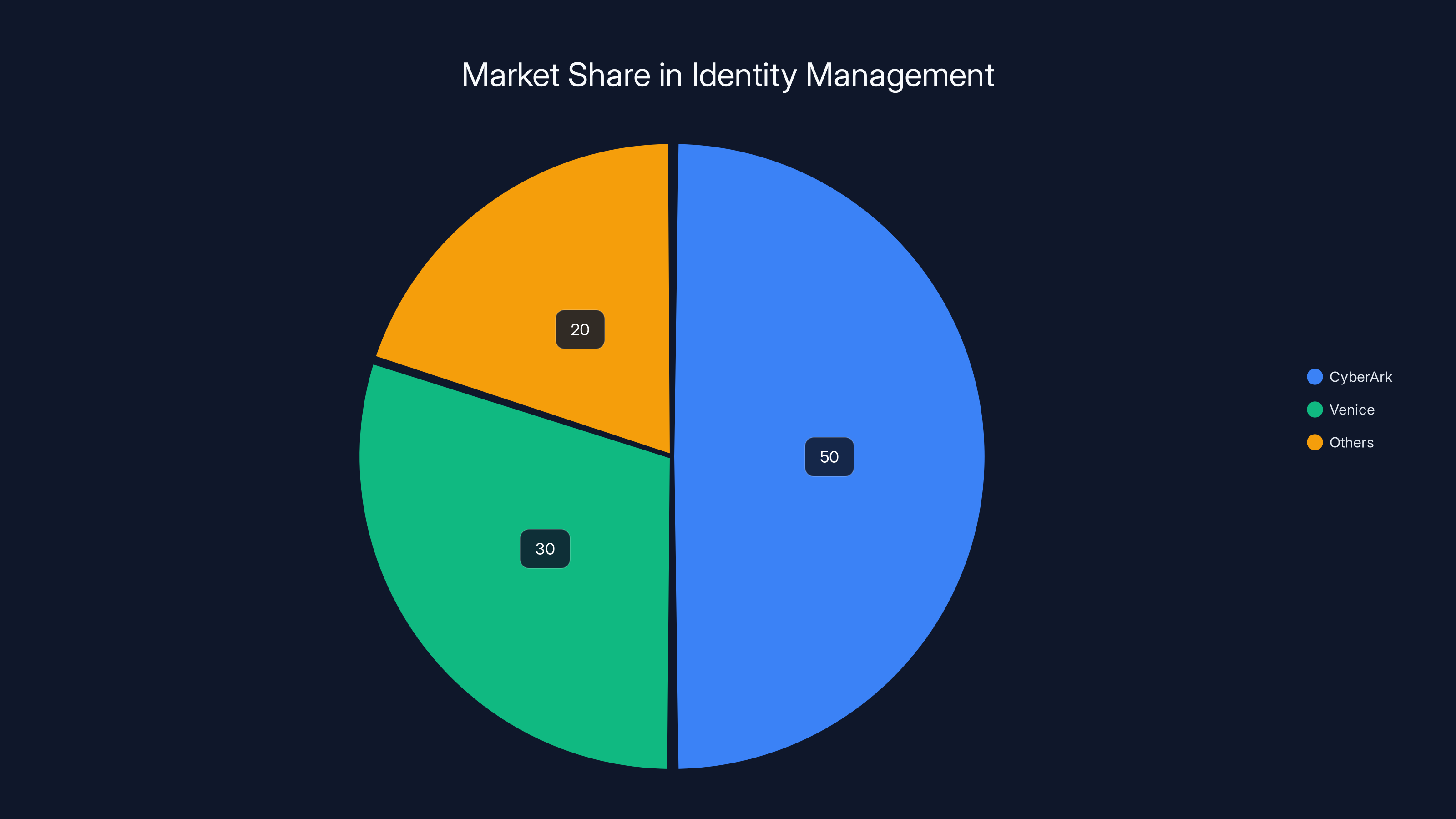
Estimated data shows CyberArk still holds a significant portion of the market, but Venice is rapidly gaining traction with 30% market share in 2025.
Investment Thesis and Market Outlook
Why IVP and Index Ventures Backed Venice
The decision by sophisticated venture capital firms like IVP and Index Ventures to invest in Venice at a meaningful valuation provides useful signal about investor perspectives on the opportunity. Cack Wilhelm, the IVP partner who led Venice's Series A, provided insight into the investment thesis.
Wilhelm articulated that most cybersecurity pitches address problems that, while real, are too small to ever generate truly material returns. The defining characteristic of massive exits like CrowdStrike and Palo Alto Networks, according to Wilhelm's analysis, is that they tackled audacious problems from inception—problems big enough and important enough to justify billion-dollar market capitalizations.
Wilhelm's thesis suggests that privileged access management, particularly as it scales to address AI agents and autonomous systems, represents exactly this category of audacious problem. Rather than another point solution in an already-crowded market, Venice is positioning itself around a fundamental reframing of identity management for an AI-first world.
The AI Agent Catalyst
Wilhelm specifically highlighted the emergence of AI agents as the key factor driving IVP's conviction in Venice. As enterprises deploy increasing numbers of AI agents, each requiring credentials and permissions to operate, the inadequacy of traditional static access control models becomes apparent. If every knowledge worker will eventually have dozens of AI agents working on their behalf—as many industry observers predict—then the existing framework for thinking about access control needs fundamental rethinking.
This framing creates a genuine inflection point in the identity management market. Companies that have built their platforms around human-centric access models face architectural challenges addressing this new reality. Companies that have explicitly designed their platforms around supporting both human and non-human entities from inception gain advantages as this transition accelerates.
Venice's explicit design around AI agent support, combined with the company's timing (launching into market as AI agent deployment accelerates), positions the company to capture value from this transition if it occurs as anticipated.
Challenges and Realistic Assessment
The Difficult Business of Displacing Incumbents
Despite the compelling market dynamics and thoughtful platform architecture, Venice faces genuinely difficult challenges in displacing CyberArk and other incumbents. History demonstrates that displacing entrenched vendors in enterprise security is possible but exceptionally challenging and requires sustained focus and execution.
CyberArk's installed base includes thousands of enterprises with years of investment, custom integrations, and staff trained on CyberArk's specific tools and processes. Convincing these organizations to undertake risky migrations to unproven alternatives—no matter how compelling the value proposition—requires overcoming substantial organizational inertia and risk aversion.
Moreover, CyberArk is not static. The incumbent vendor has observed the same market trends Venice is responding to and is presumably investing in AI-powered automation, cloud infrastructure improvements, and support for AI agents. CyberArk's substantial resources could potentially enable rapid feature development to address the gaps that Venice is exploiting.
Execution Risk
Venice's bold claims around implementation speed and feature breadth depend on flawless product execution across multiple complex domains. Building a system that successfully spans on-premises, SaaS, and multi-cloud infrastructure at the depth required for enterprise security is technically sophisticated and leaves room for implementation mistakes, security vulnerabilities, or architectural limitations that become apparent only under real-world customer use.
The company's 35-person team, while including strong talent, is substantially smaller than established competitors. Scaling the team and maintaining engineering excellence while growing customer base and handling customer-specific customization demands represents a familiar challenge in enterprise software—one that many promising startups have struggled with.
Market Timing Risks
While Venice's timing appears fortunate—entering market as AI agent proliferation accelerates and enterprises increasingly question incumbent vendors—market timing can also move in unfavorable directions. If enterprise AI adoption proceeds more slowly than anticipated, or if incumbents successfully address AI agent requirements, Venice's primary differentiation might diminish.
Additionally, broader enterprise software trends toward consolidation could work against Venice. Rather than replacing multiple vendors with a single new platform, enterprises might increasingly favor integrated suites from giants like Microsoft, Google, or cloud providers, marginalizing independent vendors regardless of technical quality.
Future Directions and Market Evolution
The Likely Evolution of Identity Management
Based on current market trends and technology developments, identity management is likely to evolve in several directions over the next 3-5 years. Consolidation of previously-siloed access management domains—PAM, SaaS access management, cloud infrastructure access—seems increasingly likely as the costs of maintaining multiple systems become prohibitive.
This consolidation trend could favor either established vendors that successfully broaden their platforms or new entrants like Venice that are architected for breadth from inception. The transition won't be painless or swift, as most large enterprises operate legacy systems that will remain in place for years.
AI-powered automation will likely become table stakes in identity management solutions. The ability to automatically discover permissions, suggest policy configurations, detect anomalies, and enforce just-in-time access controls using machine learning will become expected rather than differentiating. Vendors that can deliver genuinely superior automation will have advantages, while those with mediocre AI capabilities might see automation become a liability if it creates false positives or security issues.
The Non-Human Identity Transformation
The emergence of sophisticated non-human identities—AI agents, service accounts, application identities, and infrastructure automation systems—will likely force fundamental reconceptualization of access control models. Traditional role-based access control (RBAC) and attribute-based access control (ABAC) models were designed around human users and organizational structures. Scaling these models to thousands of AI agents each with distinct permission requirements and lifecycle patterns may require new approaches entirely.
Platforms that can elegantly handle this transition—treating human and non-human identities as first-class subjects and providing appropriate policy enforcement and audit mechanisms for each—will likely have significant advantages as this transition progresses.
The Integration vs. Point Solution Question
One of the most interesting questions for the market involves whether consolidated platforms like Venice will succeed in displacing specialized point solutions or whether the market will favor best-of-breed approaches combined through robust APIs and integrations. This question remains genuinely unsettled.
Historically, enterprise software has cycled between periods favoring consolidation and periods favoring specialization. Integration complexity created by point solutions eventually drives enterprises toward consolidated platforms, which then create dissatisfaction through compromised capability depth, motivating the next wave of specialized solutions that excel in specific domains.
Venice's success likely depends on whether the company can deliver sufficient capability depth across all three domains (on-premises, cloud, SaaS) while maintaining simplicity and ease of implementation. If Venice becomes a jack-of-all-trades-master-of-none across these domains, enterprises might prefer specialized solutions even at the cost of integration complexity. Conversely, if Venice delivers genuine excellence across all three domains, consolidation becomes compelling.
Strategic Recommendations for Different Organization Types
For Large Enterprises with Hybrid IT Environments
Large enterprises operating hybrid infrastructure combining on-premises systems, multi-cloud infrastructure, and hundreds of SaaS applications represent Venice's core target market. Organizations in this category should carefully evaluate Venice's offering, particularly if they're dissatisfied with their current identity management approach or facing large-scale PAM implementations.
The evaluation should focus on: (1) Does Venice's approach genuinely address your hybrid environment challenges better than incumbent solutions? (2) Are you confident that Venice can deliver on rapid implementation claims? (3) What switching costs would you incur moving from an incumbent vendor? (4) How risk-averse is your organization regarding unproven vendors in security-critical systems?
For organizations that value speed, consolidation, and reduced professional services dependency, Venice warrants serious evaluation despite the vendor maturity and market position advantages of incumbents.
For Cloud-Native Organizations
Organizations that have successfully migrated most workloads to cloud and operate minimal on-premises infrastructure should evaluate whether Venice's hybrid focus translates to unnecessary complexity. In these scenarios, cloud-native solutions like Okta or specialized solutions like HashiCorp Vault might better serve actual requirements without the overhead of managing on-premises capabilities that aren't needed.
The advantage of cloud-native solutions lies in architectural alignment with cloud-first operational models. If you operate cloud-first, a cloud-first identity platform often integrates more smoothly than a hybrid platform that accommodates on-premises as a primary use case.
For Smaller Organizations or Those with Limited Internal Expertise
Smaller organizations or those with limited internal identity management expertise should carefully evaluate any vendor's implementation speed claims. If your organization will depend on vendor-provided consulting regardless, the theoretical speed advantages of platforms like Venice might not translate to practical benefits.
In these scenarios, focus evaluation on: (1) What's the total consulting budget required for successful deployment? (2) What's the vendor's commitment to success in smaller customer scenarios? (3) Does the platform provide intuitive management interfaces that your existing team can reasonably learn? (4) What's the ecosystem of integration partners and professional services available?
For smaller organizations, sometimes simpler, more focused solutions prove better aligned with actual needs and budgets than comprehensive platforms.
The Competitive Landscape: Comparative Analysis
Feature and Capability Comparison
| Capability | Venice | CyberArk | Okta | Vault |
|---|---|---|---|---|
| On-Premises PAM | Native | Comprehensive | Limited | Limited |
| Cloud Infrastructure Access | Native | Limited | Good | Excellent |
| SaaS Application Access | Native | Limited | Excellent | Limited |
| AI-Powered Automation | Core | Emerging | Emerging | Limited |
| Implementation Speed | Weeks | Months-Years | Months | Weeks |
| Just-in-Time Access | Yes | Yes | Partial | Yes |
| Non-Human Identity Support | First-class | Traditional | Traditional | First-class |
| Session Recording | Yes | Comprehensive | Limited | No |
| Audit & Compliance | Comprehensive | Comprehensive | Good | Good |
| Hybrid Environment Support | Optimized | On-Prem Focused | Cloud Focused | Cloud Focused |
Use Case Alignment
Different solutions excel for different use cases. Large enterprises with significant on-premises infrastructure that have successfully deployed CyberArk might find incremental upgrades and capability additions more compelling than rip-and-replace migrations, even if Venice offers superior architecture for hybrid environments.
Cloud-native organizations might find Okta or Vault more naturally aligned with their operational models than Venice's broader but potentially less specialized approach. Organizations heavily dependent on secrets management and infrastructure-as-code practices might prefer Vault's specialization to Venice's broader platform.
Organizations beginning identity management projects from scratch and building cloud-first, hybrid environments from inception might find Venice's purpose-built approach particularly compelling—avoiding the inheritance of legacy assumptions and constraints that plague migrations.
FAQ
What is Venice and how does it differ from CyberArk?
Venice is an emerging identity and access management platform founded in 2023 by Rotem Lurie and Or Vaknin, designed to consolidate identity management across on-premises, cloud, and SaaS infrastructure into a single platform. Unlike CyberArk, which focused primarily on on-premises privileged access management, Venice was architected from inception to handle hybrid environments combining legacy systems with modern cloud infrastructure, with particular emphasis on managing access for both human users and AI agents. Venice claims to compress implementations from 6-24 months to 1-2 weeks through AI-powered automation, fundamentally changing the economics of identity management deployment.
How does Venice's AI-powered automation enable rapid implementation?
Venice leverages artificial intelligence across three key stages of implementation: automated discovery (AI identifies existing permissions across legacy systems), intelligent analysis (AI categorizes permissions and suggests policy structures), and automated migration (AI generates and executes migration scripts). This automation replaces the traditionally manual, consultant-intensive process where security architects manually discover permissions, understand relationships, and plan migrations. By automating what traditionally requires dozens of person-weeks of expert consulting, Venice can potentially reduce implementation from months to weeks, with corresponding reduction in implementation costs. Organizations using this approach report accelerated time-to-value and reduced professional services dependency.
What are the main advantages of Venice's approach for enterprises with hybrid IT environments?
Venice's primary advantage for hybrid environments lies in unified visibility and governance across on-premises, cloud infrastructure, and SaaS applications—something that most enterprises currently achieve only through multiple point solutions. Rather than deploying separate tools for on-premises PAM (like CyberArk), cloud infrastructure access (like solutions built on HashiCorp Vault), and SaaS access management, Venice offers consolidated governance through a single platform. This consolidation eliminates the integration complexity and visibility blind spots created by multiple tools, enables consistent just-in-time access policies across all infrastructure layers, and reduces the total operational overhead of managing identity across a complex environment.
What should organizations consider before migrating from CyberArk to Venice?
Organizations considering migration from established vendors like CyberArk should carefully evaluate: (1) Switching costs—what disruption and resource investment does migration require? (2) Feature gap analysis—does Venice provide all critical capabilities currently used in CyberArk? (3) Vendor maturity—does your organization's risk tolerance allow moving to a younger, less proven vendor in security-critical systems? (4) Customer reference checks—can Venice provide customers in similar industries/environments willing to discuss production experiences? (5) Integration requirements—does Venice integrate appropriately with existing infrastructure and tools? (6) Migration timeline—does Venice's claimed rapid implementation timeline actually apply to your specific environment? Honest assessment of these factors helps determine whether Venice's advantages outweigh the risks and disruption of migration.
How does Venice approach managing access for AI agents and non-human identities?
Venice treats AI agents and non-human identities as first-class subjects alongside human users, rather than attempting to fit them into traditional access control models designed for human administrators. The platform enables provisioning temporary, task-specific credentials for AI agents that automatically expire when tasks complete, provides granular policy controls specifically designed for non-human access patterns, maintains comprehensive audit logs of what agents accessed and what they did, and enables automated policy enforcement that can revoke access if unexpected behavior is detected. This approach addresses the reality that modern enterprises increasingly deploy AI agents requiring privileged access (data access, infrastructure management, system automation) while maintaining security controls preventing credential compromise or unauthorized access.
How does Venice's pricing compare to CyberArk and other competitors?
Venice operates on a SaaS subscription model though the company has not publicly disclosed pricing details in available materials. CEO Lurie emphasized that Venice competes not primarily on license cost but on total cost of ownership, specifically through dramatic reduction in implementation costs and professional services dependency. A CyberArk deployment might involve
What are the main risks of deploying Venice versus established identity management vendors?
Venice carries greater execution risk than established vendors—the company is younger, smaller (35 people), and less battle-tested in production environments. Key risks include: architectural limitations that become apparent only under heavy customer load, security vulnerabilities in a system designed for comprehensive access across critical infrastructure, inability to execute on promised rapid implementation timelines in complex customer environments, limited ecosystem of integration partners and professional services compared to established vendors, and potential vendor viability concerns—though the company's funding and backing suggests reasonable long-term confidence. Organizations deploying Venice should implement appropriate risk mitigation including comprehensive security audits, staged rollout approaches, and contingency plans for addressing issues that might emerge in production. The benefits of Venice's approach must outweigh these risks given your organization's risk tolerance and circumstances.
How should organizations evaluate which identity management solution to choose?
Effective evaluation should begin by mapping your actual infrastructure and access management requirements. Document what systems require identity management (on-premises, cloud providers, SaaS applications), the approximate number of users and entities, current pain points with existing solutions, compliance requirements that identity management must support, and your organization's appetite for implementation disruption and vendor risk. Then evaluate candidate solutions against these actual requirements rather than against theoretical feature lists. Assess implementation requirements and timelines (request detailed SOWs rather than relying on claimed timelines), request customer references in similar industries and environments, understand total cost of ownership including implementation and operational costs, and honestly evaluate your organization's ability to manage the implementation and migration process. Different solutions excel for different scenarios—a solution perfect for a cloud-native startup might be inappropriate for a large enterprise with substantial legacy infrastructure.
What complementary tools or platforms should organizations consider alongside identity management solutions like Venice?
While dedicated identity and access management solutions provide core capabilities, organizations might benefit from complementary platforms addressing specific aspects of identity management operations. AI-powered workflow automation platforms like Runable can help teams automate routine identity operations like generating access reports, documenting permission structures, and orchestrating routine access management workflows. Secrets management solutions like HashiCorp Vault excel at managing dynamic credentials and automated credential rotation, complementing PAM solutions focused on access control. Vulnerability management tools help identify where identity controls might be weak or misconfigured. Asset discovery and inventory management tools feed data into identity management systems. Cloud security solutions provide visibility into cloud infrastructure access patterns. Rather than viewing identity management as an isolated capability, comprehensive security architecture typically involves several specialized tools, each optimized for specific aspects of the broader identity and security strategy.
What does the identity management market look like in 2025 and beyond?
The identity and access management market is experiencing significant evolution driven by several forces: consolidation of previously-siloed domains (PAM, SaaS access, cloud infrastructure) as the costs of multiple point solutions become prohibitive, emergence of AI agents and autonomous systems as first-class identity subjects requiring new access control models, shift toward cloud infrastructure and zero-trust security creating architectural pressure on traditional vendors, and increasing regulatory requirements around identity management and access control. Platforms that can elegantly span hybrid environments, provide AI-powered automation, support both human and non-human identities, and dramatically reduce implementation complexity will likely gain market share. Conversely, solutions perceived as overly complex, dependent on extensive consulting, or architecturally misaligned with cloud-first or AI-first requirements will likely face increasing pressure. The identity management market appears genuinely unsettled—established vendors retain advantages but face genuine vulnerabilities to thoughtfully-architected alternatives.

Conclusion: Navigating Identity Management in 2025
The identity and access management market stands at an inflection point. For two decades, CyberArk and similar on-premises-focused PAM vendors dominated the landscape, establishing conventions, building switching costs, and creating incumbent advantages that seemed insurmountable. Yet the accelerating shift toward cloud infrastructure, the emergence of AI agents as critical-but-hard-to-manage identity subjects, and enterprise dissatisfaction with expensive, complex implementations have created genuine opportunities for alternative approaches.
Venice's emergence from stealth with compelling technology, strong founder pedigree, and meaningful venture capital backing represents one significant alternative to incumbent vendors. The company's specific positioning—around hybrid environments, AI-powered automation, implementation speed, and non-human identity support—directly addresses pain points that traditional vendors struggle to solve effectively.
Yet declaring Venice the inevitable winner over incumbents would be premature and unrealistic. CyberArk and Okta retain substantial advantages through installed base, integration depth, partner ecosystems, and financial resources enabling rapid response to competitive threats. Incumbent vendors are not static—they're presumably responding to the same market trends that created Venice's opportunity, investing in cloud capabilities, AI-powered automation, and agent-friendly architectures.
The more likely scenario involves market evolution where consolidation and specialization coexist alongside each other. Some enterprises will consolidate onto unified platforms like Venice; others will prefer specialized best-of-breed solutions; still others will maintain heterogeneous approaches that involve multiple vendors and integration complexity. The outcome depends less on any single vendor's capabilities and more on how market evolution actually unfolds—will AI agent proliferation accelerate as quickly as anticipated? Will enterprises actually prioritize implementation speed and TCO reduction or continue accepting traditional slow, expensive implementations? Will hybrid environments remain prevalent or does cloud migration accelerate faster than expected?
For organizations evaluating identity management solutions in 2025, the most important principles involve: (1) Start with actual requirements, not feature lists or vendor positioning. Map your specific infrastructure, use cases, and constraints. (2) Evaluate total cost of ownership honestly, including implementation, operations, and opportunity costs of delayed deployments or failed implementations. (3) Request detailed proof of vendor claims. If Venice claims rapid implementation, request SOWs, timelines, and customer references for similar scenarios. (4) Assess vendor-specific risks appropriately. Younger vendors offer potential advantages but carry greater execution risk; understand your organization's risk tolerance. (5) Plan for integration and evolution. Assume your identity management solution will need to evolve as your infrastructure and organizational requirements change. (6) Understand that there's no universal best solution. Different solutions excel for different scenarios; the best solution for a cloud-native startup differs from the optimal solution for a large enterprise with substantial legacy infrastructure.
Venice's specific value proposition—rapid implementation, AI-powered automation, and unified hybrid environment management—creates genuine competitive pressure on incumbents while appealing to a meaningful segment of enterprises dissatisfied with current approaches. Whether Venice ultimately succeeds in meaningfully displacing CyberArk, Okta, and other incumbents remains genuinely uncertain and depends on factors ranging from product execution to market evolution to incumbent responses.
What seems clear is that the identity and access management market is no longer settled terrain where incumbents can assume perpetual dominance. Thoughtfully-architected alternatives addressing genuine customer pain points can gain traction. Organizations that have invested years in existing identity management infrastructure should carefully evaluate whether alternatives like Venice truly offer sufficient advantages to justify migration disruption. Organizations beginning identity management projects from scratch have genuine flexibility to choose solutions optimally aligned with their specific needs and architecture rather than constrained by incumbent assumption and legacy investments.
The identity management market of 2025-2026 offers more choices, more competitive dynamics, and more potential for innovation than the relatively settled market of a few years ago. This creates both opportunities for enterprises to dramatically improve their identity management capabilities and challenges to evaluate options effectively rather than defaulting to incumbent vendors out of habit or perceived safety.
Your organization's identity management decisions should be driven by honest assessment of actual requirements, not by assumptions about market leadership or vendor permanence. The era of identity management markets being dominated by single vendors appears to be ending; the next era will likely feature greater specialization, more viable alternatives, and more meaningful choice for enterprise customers.
Key Takeaways
- Venice is a well-funded startup challenging CyberArk's PAM dominance through AI-powered automation and hybrid environment support
- Rotem Lurie's unique background (Unit 8200, Microsoft, Axis Security) positions her to understand enterprise identity challenges deeply
- Venice claims to compress PAM implementations from 6-24 months to 1.5 weeks through automated discovery and migration
- Market drivers including cloud proliferation, AI agents, and zero-trust security are creating opportunities for alternative identity platforms
- No single identity solution works optimally for all scenarios; evaluate based on actual requirements, infrastructure, and risk tolerance
- Incumbent vendors like CyberArk retain significant advantages but face genuine competitive pressure from thoughtfully-architected alternatives
- Total cost of ownership matters more than license cost when evaluating identity management solutions
- Supporting both human and non-human (AI agent) identities is becoming critical for modern identity platforms
- Complementary automation platforms can enhance operational efficiency alongside dedicated identity management solutions
Related Articles
- VMware Exit Strategy: Turn Vendor Lock-In Into Competitive Advantage
- Privacy-by-Design 2026: The AI & Blockchain Shift
- Orbital AI Data Centers: The $42B Problem & Economics
- Google-Apple AI Deal: Why Alphabet Won't Talk About It
- SpaceX Acquires xAI: The Strategic Merger Reshaping AI Infrastructure
- India's Zero-Tax Cloud Policy Until 2047: What It Means [2025]
![Venice vs CyberArk: Identity Management Disruption [2025]](https://tryrunable.com/blog/venice-vs-cyberark-identity-management-disruption-2025/image-1-1771429408382.jpg)



