Why Traditional Metrics Give CISOs a False Sense of Security [2025]
The role of the Chief Information Security Officer (CISO) is more critical than ever, as cyber threats continue to evolve at an alarming pace. However, many CISOs rely on traditional metrics that no longer adequately reflect the complex landscape of modern cybersecurity risks. These outdated metrics can foster a dangerous illusion of security, leaving organizations vulnerable to breaches and attacks, as discussed in a TechRadar article.
TL; DR
- Outdated Metrics: Traditional security metrics often fail to capture the full scope of modern cyber threats.
- Complex Threat Landscape: Emerging threats and sophisticated attack vectors require new measurement approaches.
- Dynamic Metrics Needed: Real-time, contextual metrics provide a more accurate security posture.
- Behavioral Analytics: Shifting focus to user and entity behavior analytics can unveil unseen vulnerabilities.
- Bottom Line: Adopting modern metrics is crucial for CISOs to effectively safeguard their organizations.

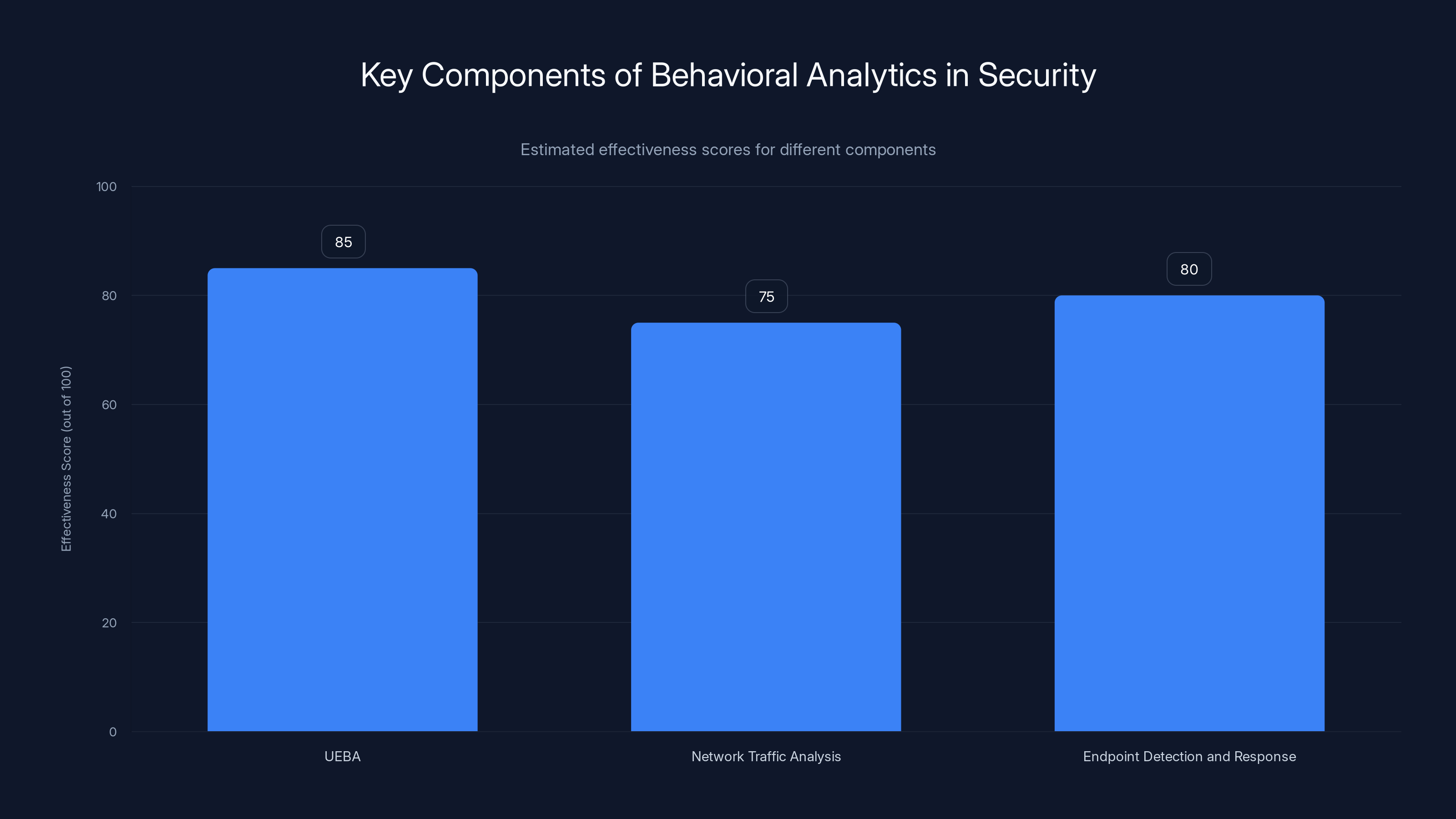
User and Entity Behavior Analytics (UEBA) is estimated to be the most effective component in detecting anomalies, followed closely by Endpoint Detection and Response (EDR). Estimated data.
The Limitations of Traditional Security Metrics
Traditional security metrics, such as the number of antivirus detections or firewall logs, have long been the cornerstone of cybersecurity strategies. However, these metrics provide a limited view of an organization's security posture and can lead to a false sense of security.
Why Traditional Metrics Fall Short
Traditional metrics typically focus on quantifiable data points, such as:
- Number of detected threats
- Firewall rule violations
- Patch management statistics
While these metrics offer some insights, they often overlook the complexity and sophistication of modern cyber threats. Attackers are increasingly adept at bypassing conventional security measures, rendering these metrics ineffective in detecting advanced persistent threats (APTs) or zero-day exploits, as noted in a Recorded Future report.
The Mirage of Security Through Numbers
A high number of blocked threats might suggest that security measures are effective. However, it can also indicate that attackers are persistently targeting the organization, and some attacks might already be successful without detection. The focus on numbers can obscure the need for deeper analysis of security incidents.

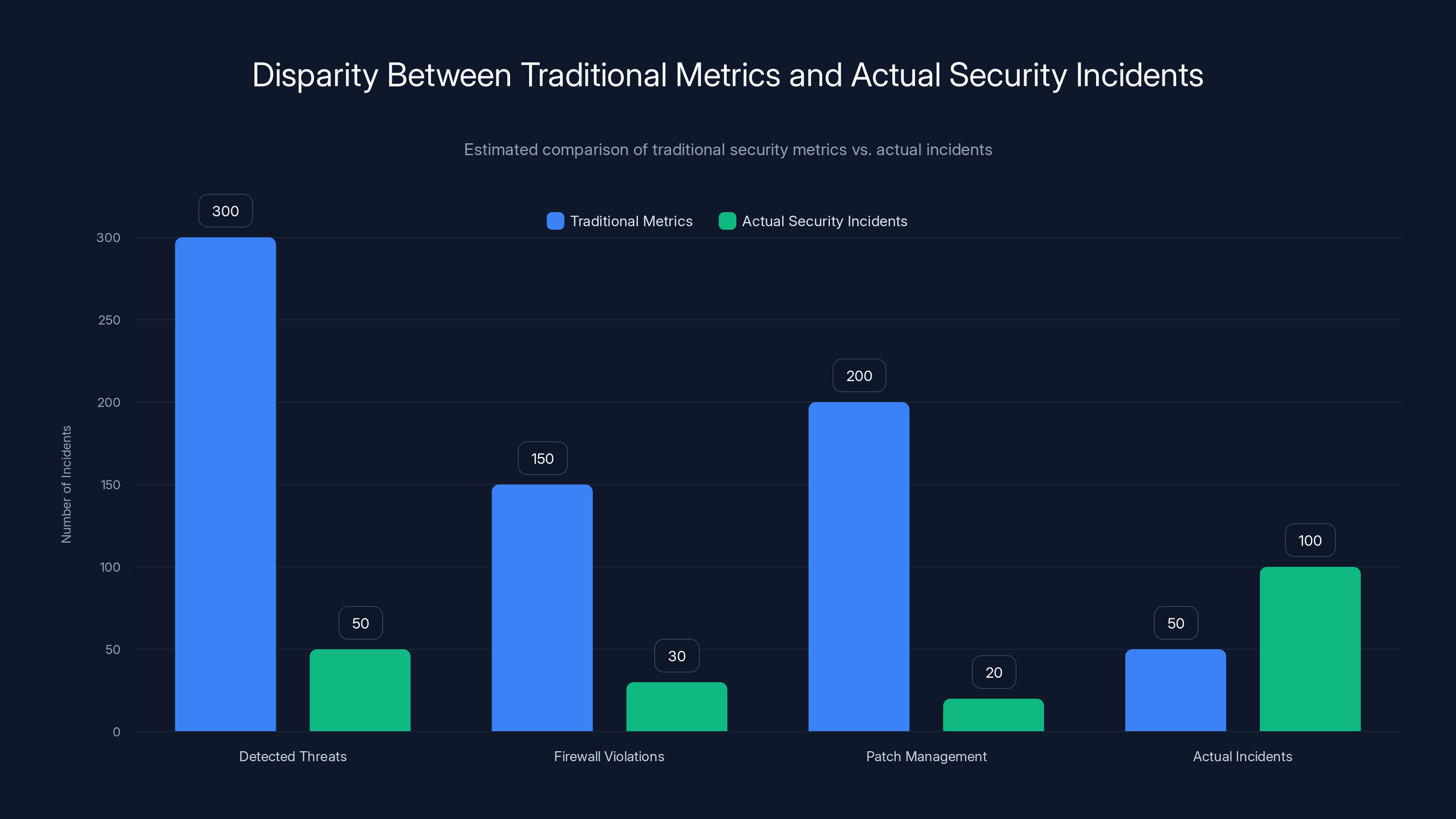
Estimated data shows that while traditional metrics report high numbers, actual security incidents often go undetected, highlighting the limitations of relying solely on these metrics.
The Evolving Threat Landscape
The cyber threat landscape is continually evolving, with attackers developing new techniques to exploit vulnerabilities. Traditional metrics are ill-equipped to keep pace with these changes, leaving CISOs blind to emerging risks.
Emerging Threats
- Advanced Persistent Threats (APTs): These are long-term targeted attacks that aim to infiltrate and exfiltrate data over extended periods. Traditional metrics often fail to capture the stealthy nature of APTs.
- Zero-Day Exploits: Attacks that occur on the same day a vulnerability is discovered, before a patch is available. These exploits can slip through traditional detection metrics, as highlighted in a Qualys blog post.
- Ransomware Evolution: Ransomware has evolved to target not just files, but entire systems, demanding higher ransoms and causing significant operational disruptions.
The Need for Adaptive Metrics
To combat these threats, CISOs need metrics that are adaptive and contextual. Metrics should:
- Reflect real-time threat intelligence
- Adapt to the organization's specific risk profile
- Incorporate insights from threat hunting and red teaming exercises
Implementing Modern Security Metrics
Transitioning to modern security metrics involves adopting a more holistic approach to measuring cybersecurity effectiveness. This includes integrating behavioral analytics, threat intelligence, and continuous monitoring into security strategies.
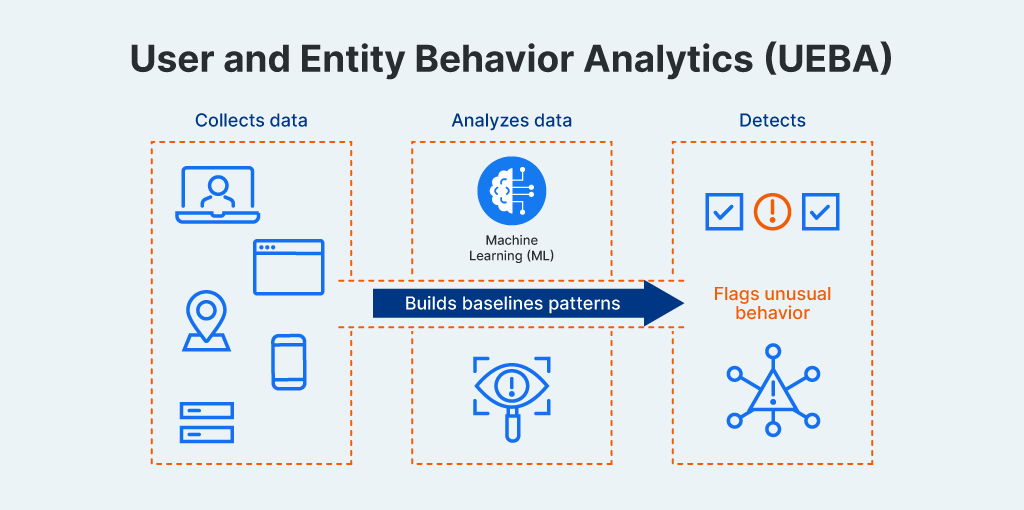
Behavioral Analytics
Behavioral analytics focus on understanding the behaviors of users, entities, and networks within an organization. This approach helps identify anomalies that traditional metrics might miss.
Key Components of Behavioral Analytics:
- User and Entity Behavior Analytics (UEBA): Detects deviations from established user behavior patterns, which can indicate potential insider threats or compromised accounts, as detailed in a TechTarget article.
- Network Traffic Analysis: Monitors network traffic to identify unusual patterns that might signal a breach.
- Endpoint Detection and Response (EDR): Provides visibility into endpoint activities, enabling rapid detection and response to threats.
Real-World Implementation
Consider an organization implementing UEBA to monitor for anomalies indicative of insider threats. By establishing a baseline of normal user behavior, the system can flag deviations, such as unusual login times or access to sensitive data by unauthorized users.
Integrating Threat Intelligence
Threat intelligence involves gathering and analyzing information about current and emerging threats. This data can be used to inform security policies and prioritize responses to potential risks.
Steps to Integrate Threat Intelligence:
- Collect Data: Gather threat data from various sources, including threat feeds, industry reports, and dark web monitoring.
- Analyze and Correlate: Use machine learning algorithms to correlate threat data with internal network activity.
- Actionable Insights: Develop actionable insights to inform security policy adjustments and incident response.
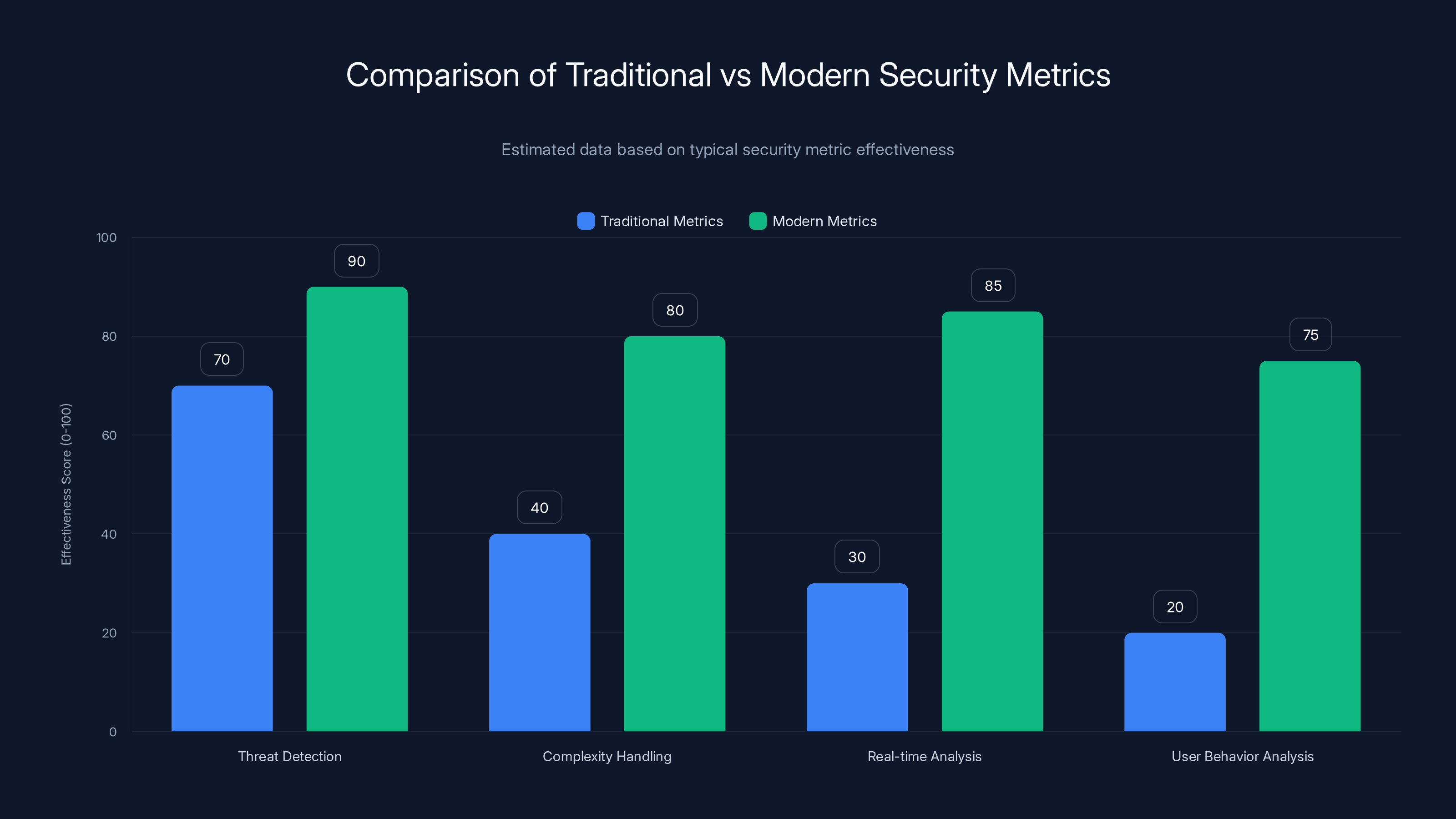
Modern security metrics significantly outperform traditional metrics in handling complexity, real-time analysis, and user behavior analysis. Estimated data based on typical effectiveness.
Overcoming Implementation Challenges
Switching to modern metrics is not without challenges. Organizations may face resistance to change, budget constraints, and skill shortages. Here are some strategies to overcome these barriers.
Addressing Resistance to Change
Resistance to change is a common hurdle when implementing new security metrics. To address this, CISOs can:
- Communicate Benefits: Clearly articulate the advantages of modern metrics to stakeholders, emphasizing improved threat detection and response capabilities.
- Provide Training: Offer training sessions to upskill staff on new tools and methodologies.
- Pilot Programs: Start with pilot programs to demonstrate the effectiveness of new metrics before full-scale implementation.
Budget Constraints
Budget constraints can limit the ability to invest in new tools and technologies. CISOs can:
- Leverage Existing Tools: Maximize the capabilities of existing security tools through configuration and integration.
- Prioritize Investments: Focus on high-impact areas that offer the greatest return on investment, such as EDR and UEBA.
- Seek Vendor Partnerships: Partner with vendors to explore flexible pricing models and trial periods.
Skill Shortages
The cybersecurity skills gap is a significant challenge. To address this, organizations can:
- Invest in Training and Development: Provide continuous education opportunities for security staff.
- Utilize Managed Security Services: Engage managed security service providers (MSSPs) to supplement internal capabilities.
- Foster Collaboration: Encourage collaboration between IT and security teams to share knowledge and skills.

Future Trends in Security Metrics
The future of security metrics lies in harnessing advanced technologies and methodologies to enhance threat detection and response.
Artificial Intelligence and Machine Learning
AI and machine learning will play a pivotal role in the development of next-generation security metrics. These technologies can:
- Automate Threat Detection: Use machine learning algorithms to identify patterns and anomalies in real-time data.
- Predict Threats: Leverage AI to forecast potential threats based on historical data and trends.
- Enhance Response Capabilities: Automate incident response processes to reduce response times and minimize impact.
Zero Trust Architecture
The adoption of zero trust architecture is reshaping security metrics by eliminating the distinction between internal and external threats. Key principles include:
- Verify Explicitly: Continuously verify user identities and device security before granting access.
- Limit Access: Enforce least privilege access policies to minimize potential attack surfaces.
- Assume Breach: Design systems with the assumption that breaches will occur, and focus on minimizing damage.
Increased Focus on Data Privacy
Data privacy regulations, such as GDPR and CCPA, are influencing security metrics by emphasizing the protection of personal data. Metrics now need to account for:
- Data Minimization: Limiting data collection to essential information only.
- Access Controls: Implementing strict access controls to safeguard sensitive data.
- Compliance Monitoring: Continuously monitoring compliance with data privacy regulations.

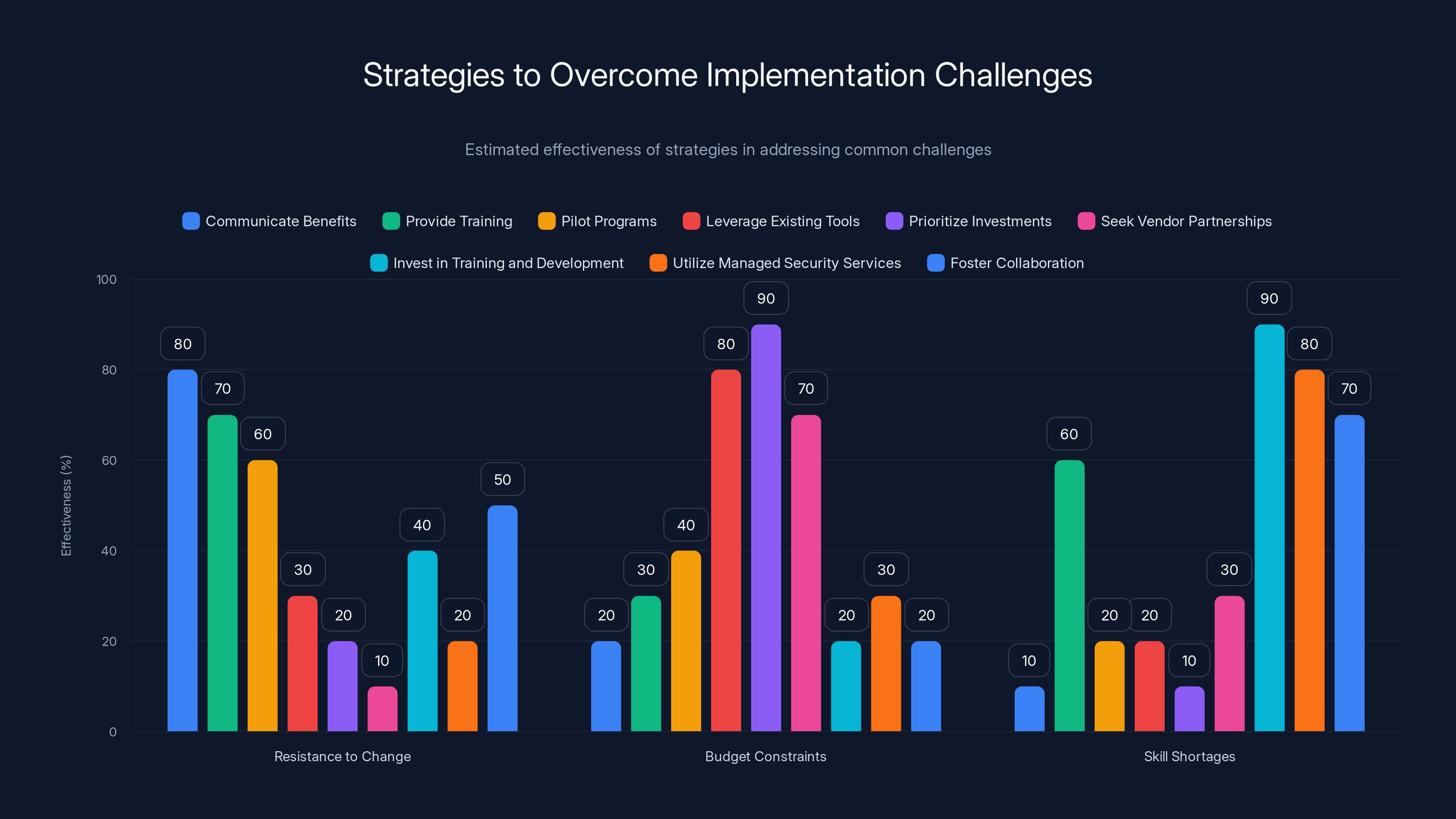
Estimated effectiveness of various strategies shows that 'Prioritize Investments' is most effective for budget constraints, while 'Invest in Training and Development' addresses skill shortages best. 'Communicate Benefits' is crucial for overcoming resistance to change. Estimated data.
Conclusion
Traditional security metrics are no longer sufficient to protect organizations from modern cyber threats. By adopting dynamic, contextual metrics and leveraging advanced technologies, CISOs can gain a more accurate understanding of their security posture. This proactive approach will enable organizations to better anticipate and respond to evolving threats, ultimately enhancing their resilience in the face of cyberattacks.
Use Case: Implementing AI-driven analytics to improve threat detection and response.
Try Runable For Free
FAQ
What are traditional security metrics?
Traditional security metrics focus on quantifiable data points, such as the number of detected threats and firewall rule violations. They provide a limited view of an organization's security posture.
Why do traditional metrics give a false sense of security?
Traditional metrics often fail to capture the complexity of modern cyber threats, leading to an incomplete understanding of security risks and a false sense of security.
What are some examples of modern security metrics?
Modern security metrics include behavioral analytics, threat intelligence integration, user and entity behavior analytics (UEBA), and endpoint detection and response (EDR).
How can CISOs implement modern security metrics?
CISOs can implement modern security metrics by integrating threat intelligence, adopting behavioral analytics, and leveraging AI and machine learning for real-time threat detection.
What challenges are associated with transitioning to modern metrics?
Challenges include resistance to change, budget constraints, and skill shortages. Strategies to overcome these challenges include communication, training, and leveraging managed security services.
How do AI and machine learning enhance security metrics?
AI and machine learning automate threat detection, predict potential threats, and enhance response capabilities by identifying patterns and anomalies in real-time data.
What is zero trust architecture?
Zero trust architecture is a security framework that assumes breaches will occur and focuses on minimizing damage through continuous verification, limited access, and strict access controls.
How do data privacy regulations impact security metrics?
Data privacy regulations influence security metrics by emphasizing the protection of personal data through data minimization, access controls, and compliance monitoring.

Key Takeaways
- Traditional metrics fail to capture complex modern threats.
- Dynamic, real-time metrics provide a more accurate security posture.
- Behavioral analytics can reveal hidden vulnerabilities.
- AI and machine learning enhance threat detection and response.
- Zero trust architecture reshapes security metrics.
Related Articles
- Unraveling the EU Cyberattack: A Deep Dive into the Breach and Its Implications [2025]
- Laughing RAT: The New Malware Threat in 2025
- Hasbro Cyberattack: Lessons and Strategies for Cyber Resilience [2025]
- The Rise of AI in Healthcare: Chatbots Prescribing Psychiatric Drugs [2025]
- CBP Facility Codes Sure Seem to Have Leaked Via Online Flashcards | WIRED
- Understanding Telehealth Security: Lessons from the Hims & Hers Data Breach [2025]
![Why Traditional Metrics Give CISOs a False Sense of Security [2025]](https://tryrunable.com/blog/why-traditional-metrics-give-cisos-a-false-sense-of-security/image-1-1775226859178.jpg)



