Abu Dhabi Finance Summit Data Breach: 700+ Passports Exposed [2025]
In early 2025, one of the world's most prestigious financial conferences became the center of a sprawling data security nightmare. Abu Dhabi Finance Week (ADFW), a massive event organized by the Abu Dhabi Global Market that typically attracts more than 35,000 attendees from across the globe, inadvertently exposed the personal identification documents of approximately 700 high-profile individuals. We're talking passports, government-issued ID cards, and sensitive biographical data belonging to some of the world's most influential people in finance, politics, and cryptocurrency.
This wasn't a sophisticated hacking operation. No dark web marketplaces. No ransomware group claiming responsibility. Instead, it was something far more embarrassing and, frankly, far more common than anyone wants to admit: a misconfigured database sitting openly on the internet, protected by nothing more than a digital lock that was never actually engaged. A freelance security researcher stumbled across it almost by accident, found what amounts to a digital treasure trove of identity documents, and responsibly reported it. The organizers scrambled to secure it. End of story. Or is it?
Here's the thing—this incident exposes something much bigger about how major events handle attendee data in the digital age. When you register for a conference, provide your passport details for travel coordination, and trust organizers with your most sensitive identification documents, you're operating under an assumption: that these organizations have basic cybersecurity fundamentals in place. The Abu Dhabi Finance Week breach proves that assumption can be dangerously wrong, even at the highest levels of the financial industry.
But this isn't just about what happened at one event. It's a window into how data breaches happen across the entire event industry, how third-party vendors become single points of failure, and what you should actually do if you've attended a major conference and wonder if your data is floating around on the internet somewhere.
TL; DR
- 700+ high-profile attendees had passports and ID card scans exposed in a misconfigured database at Abu Dhabi Finance Week 2025
- Notable victims included former British Prime Minister David Cameron, US investor Anthony Scaramucci, Binance co-CEO Richard Teng, and EU ambassador Lucie Berger
- Root cause was simple: A third-party vendor managing attendee data left the storage environment unprotected with no password requirements
- No evidence of malicious exploitation, but the database was publicly accessible for an unknown period
- This is the sixth major finance event breach in the past three years, indicating systemic industry failures
- Misconfigured databases remain the #1 cause of enterprise data breaches, accounting for 27% of all incidents

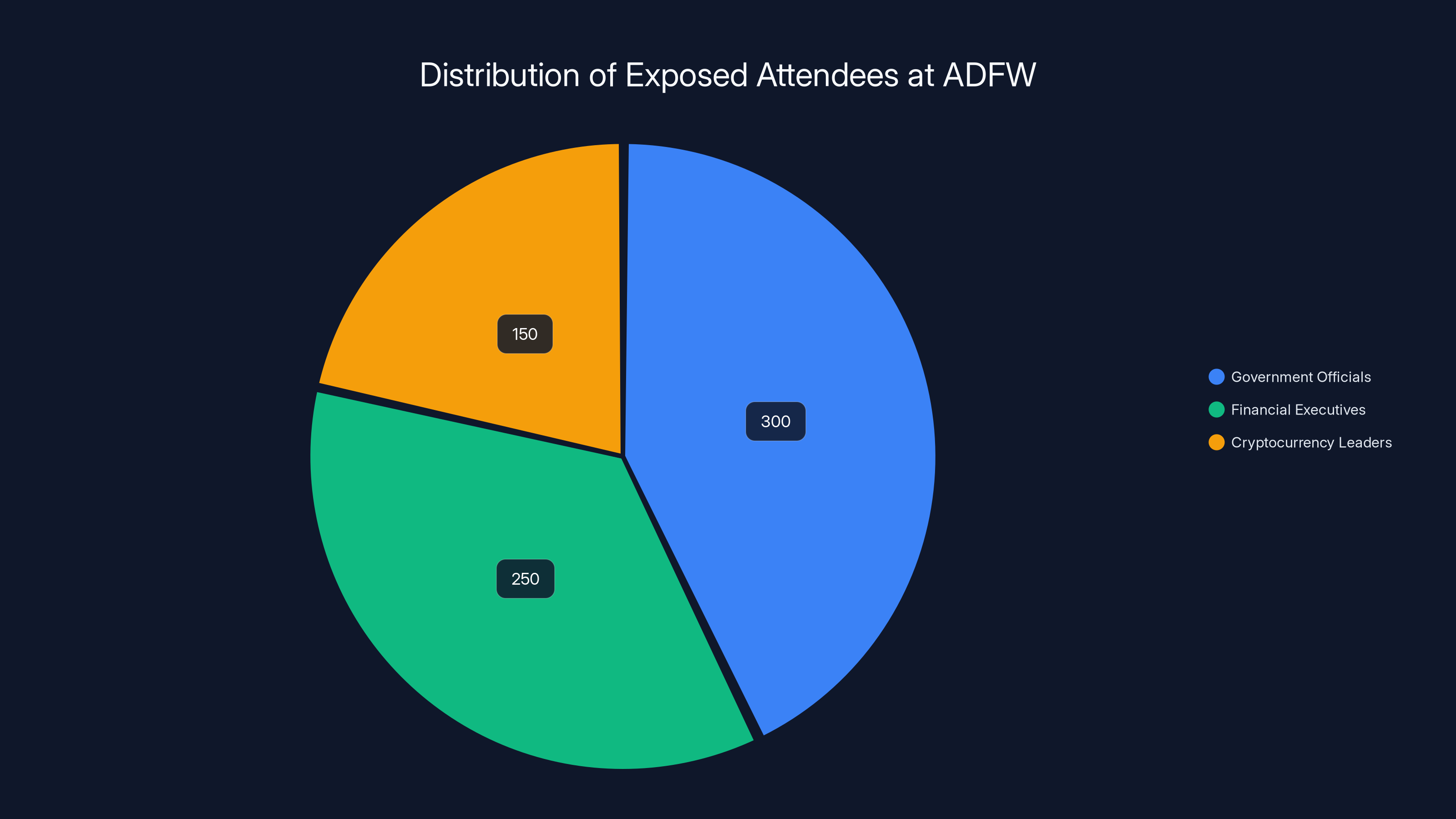
Estimated data shows that government officials, financial executives, and cryptocurrency leaders are the primary categories affected by the breach, highlighting the significant security risks involved.
What Actually Happened at Abu Dhabi Finance Week
Let's walk through the timeline because understanding how this happened matters more than just knowing that it happened.
Abu Dhabi Finance Week 2025 was supposed to be business as usual. The event, held under the patronage of senior UAE leadership, brings together global leaders in finance, investment, policy, technology, and markets. Attendees range from government officials and central bank leaders to hedge fund billionaires and cryptocurrency executives. For most attendees, the registration process was straightforward: provide basic information, agree to terms, maybe snap a photo for a badge. But for international attendees, the event coordinators needed more. They needed proof of identity. They needed passport scans and government-issued ID documents.
This is where the chain of trust broke.
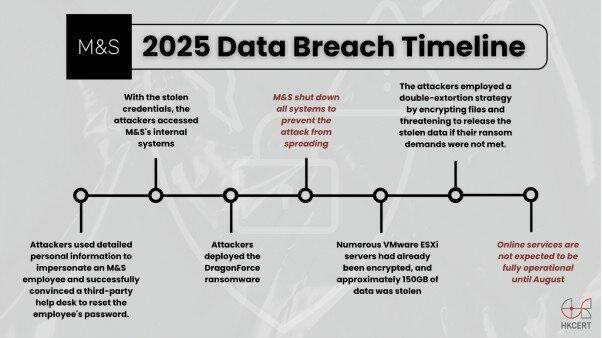
Instead of managing these documents directly, ADFW relied on a third-party vendor. This isn't unusual. Most large events outsource data management to specialized service providers. The problem is, you're only as secure as your weakest vendor. And in this case, the vendor didn't just have a weak link—they had no link at all. The database containing all those identity documents wasn't locked. It wasn't behind a password. It wasn't even obscured. It was just sitting there on the internet, publicly accessible, like a filing cabinet in the middle of Times Square with the drawers wide open.
Security researcher Roni Suchowski discovered it. According to reports, Suchowski found the database through routine security research and immediately did the right thing: notified ADFW and the vendor instead of publicizing the breach or selling the information. The organizers secured the database immediately. But here's the critical question nobody seems to want to answer clearly: how long was it exposed?
ADFW won't say. They've stated that "access activity was limited to the researcher who identified the issue," which technically tells us that no hackers appear to have found it before Suchowski did. But they haven't disclosed when the database first went live or for how long it was vulnerable. That's a gap in transparency that raises questions about what really happened and when they really knew about it.
The High-Profile Victims: Who Got Caught in the Crossfire
What makes this breach particularly newsworthy isn't just the scale—it's the caliber of people whose data was exposed.
The leak included passport and ID documents from David Cameron, the former British Prime Minister who served as UK PM from 2010 to 2016 and now holds significant influence in global political circles. Anthony Scaramucci, the US investor who famously served as White House communications director (though for just 11 days during the Trump administration), had his documents exposed. He's since built a significant profile as a media personality and political commentator, making his identification documents a particularly sensitive piece of information to have floating around.
Richard Teng, the co-chief executive of Binance (the world's largest cryptocurrency exchange by trading volume), was also caught in the leak. What makes Teng's exposure particularly significant is his previous role as chief executive of the Abu Dhabi Global Market—the very organization that organized ADFW. He knows how this system is supposed to work. He knows the level of security that should be in place. Having his passport leaked by the organization he used to lead is, well, awkward.
Alan Howard, a hedge fund billionaire with substantial influence in cryptocurrency and traditional finance, was among those exposed. Lucie Berger, the European Union's ambassador to the UAE, had her diplomatic credentials compromised. The list extends to other high-net-worth individuals, C-suite executives, and government officials from countries including the US, UK, Singapore, Denmark, Finland, Norway, Sweden, Germany, the Netherlands, Belgium, France, Spain, Canada, Mexico, Australia, and New Zealand.
What's striking is that none of these individuals have publicly commented. No lawsuits announced. No regulatory filings demanding answers. No calls for investigations. It's as if the world's most influential people are just... accepting that their passport data got leaked and moving on. Which, frankly, is the most concerning thing about this entire incident. It suggests a level of resignation about data security that shouldn't be acceptable at this level.
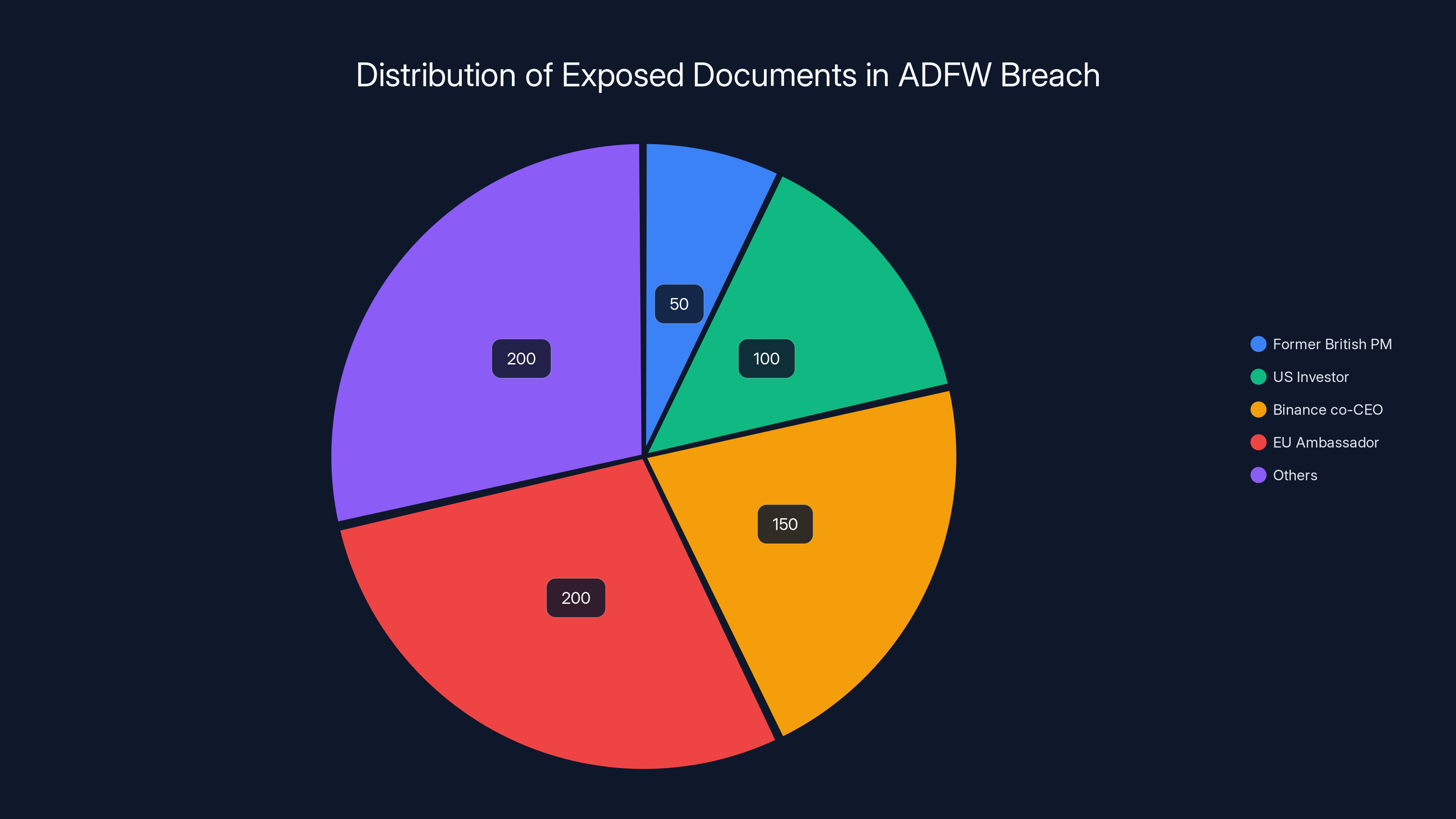
Estimated data shows a diverse range of high-profile individuals affected by the breach, with the majority being from various global financial and political sectors.
The Third-Party Vendor Problem: Why Outsourcing Creates Risk
Here's what we know: ADFW didn't manage the data directly. A third-party vendor did. This is a critical distinction because it reveals a systemic problem in how large organizations approach data security when they don't want to handle sensitive information themselves.
The logic makes sense from an operational perspective. Event organizers don't want to become data security experts. They want to focus on speakers, sponsors, logistics, and attendee experience. They contract with a specialized vendor who supposedly knows how to handle sensitive documents securely. Problem solved, right?
Not exactly.
Third-party vendors create what security professionals call "the extended attack surface." Instead of one organization being responsible for data security, you now have multiple organizations with access to the same sensitive information. Each one is a potential point of failure. And unlike a dedicated data security company, many event management vendors aren't primarily focused on cybersecurity. They're focused on getting the event organized efficiently.
The misconfiguration that led to the Abu Dhabi breach wasn't complex. It was basic infrastructure setup done incorrectly. Someone set up a cloud storage bucket or database without enabling authentication. Maybe they planned to add security later and forgot. Maybe they didn't understand how the cloud platform's default settings worked. Maybe they rushed the implementation. The result was the same: sensitive data was exposed.
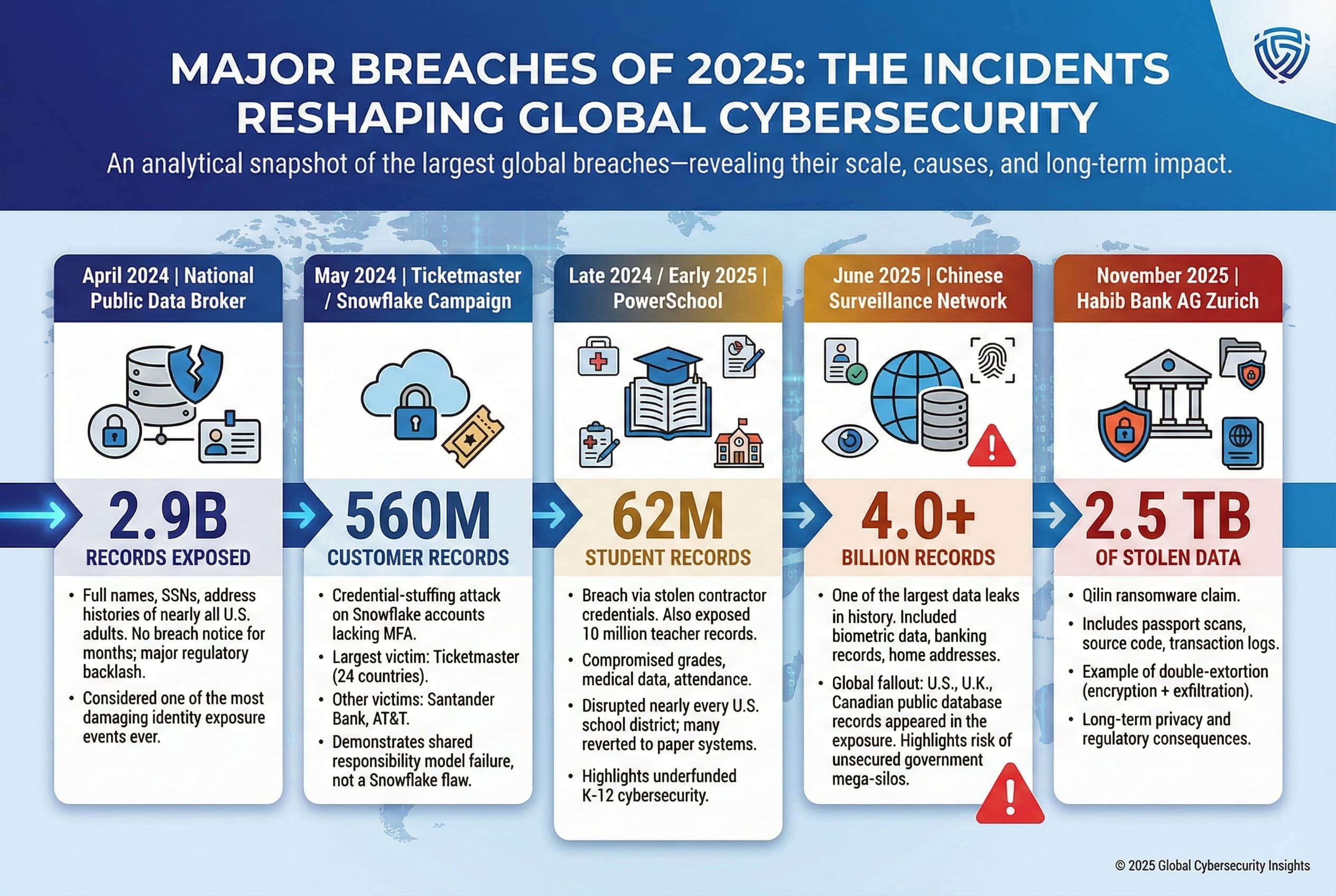
This isn't unprecedented. When you look at major data breaches from the past five years, the pattern is consistent. Capital One's 2019 breach exposed over 100 million credit card applications because of a misconfigured AWS firewall. Twitter's 2022 breach affected 5.4 million users due to a misconfigured API. The list goes on. Organizations contract out critical functions, lose direct oversight of security implementation, and then discover (often through researchers rather than through their own monitoring) that everything's exposed.
How Data Breaches Happen at Major Events
Abu Dhabi Finance Week wasn't unique in getting breached. It's actually part of a troubling pattern.
Large conferences and financial summits collect sensitive data by design. Attendees need to register. International attendees need to provide passport information. VIP attendees might provide additional biographical details. Exhibitors share contact information. Sponsors gain access to attendee lists. All of this data flows through various systems, databases, and third-party platforms.
Each touchpoint is a potential vulnerability. Here's the typical architecture: attendees register through a website (managed by one vendor), submit documents through a different platform (managed by another vendor), badges are printed by a third vendor, check-in processes are managed by a fourth vendor, and follow-up emails are sent through a fifth vendor. Now you've got five different organizations with access to attendee data, five different security policies, and five different potential failure points.
The regulatory landscape doesn't help. Event organizers are generally not classified as data controllers under regulations like GDPR or similar privacy laws in the Middle East. They're not treated like banks or healthcare providers that face heavy compliance requirements. As a result, security practices are often minimal.
Researchers who specialize in conference security have documented this pattern. Events ranging from technology conferences to financial summits to medical conventions have experienced similar misconfiguration issues. Most never make headline news because the organizations pay researchers to quietly fix the issues without public disclosure. Abu Dhabi Finance Week only became public because the Financial Times reported on it.
The Scale of the Problem: 700 People Out of 35,000
ADFW organizers have been quick to point out that 700 exposed attendees out of 35,000+ participants represents just 2% of the event's total attendance. They use this percentage to downplay the breach's significance. But that framing is misleading.
First, 700 people is still 700 people whose identity documents are now in the public record. One exposed passport is a problem. Seven hundred is a significant breach by any measure.
Second, the selection of those 700 attendees wasn't random. According to available information, the exposed individuals tend to skew toward higher-profile, higher-security-risk categories: government officials, financial executives, and cryptocurrency leaders. These are precisely the people who should have the strongest privacy protections, not the weakest.
Third, the percentage comparison only works if you assume all 35,000 attendees were equally likely to be affected. But the data suggests the breach affected a specific subset—likely the VIP attendees or those who required document verification. If the exposed group represents all international attendees or all VIP guests, then the breach percentage could be much higher.
Think about the ripple effects. Each exposed passport creates identity theft risk. Government officials with leaked credentials become targets for social engineering and fraud. Cryptocurrency executives with leaked documents become targets for kidnapping, extortion, and other physical security threats. Financial leaders with exposed information become targets for corporate espionage. These aren't abstract privacy violations—they're real security threats to real people.
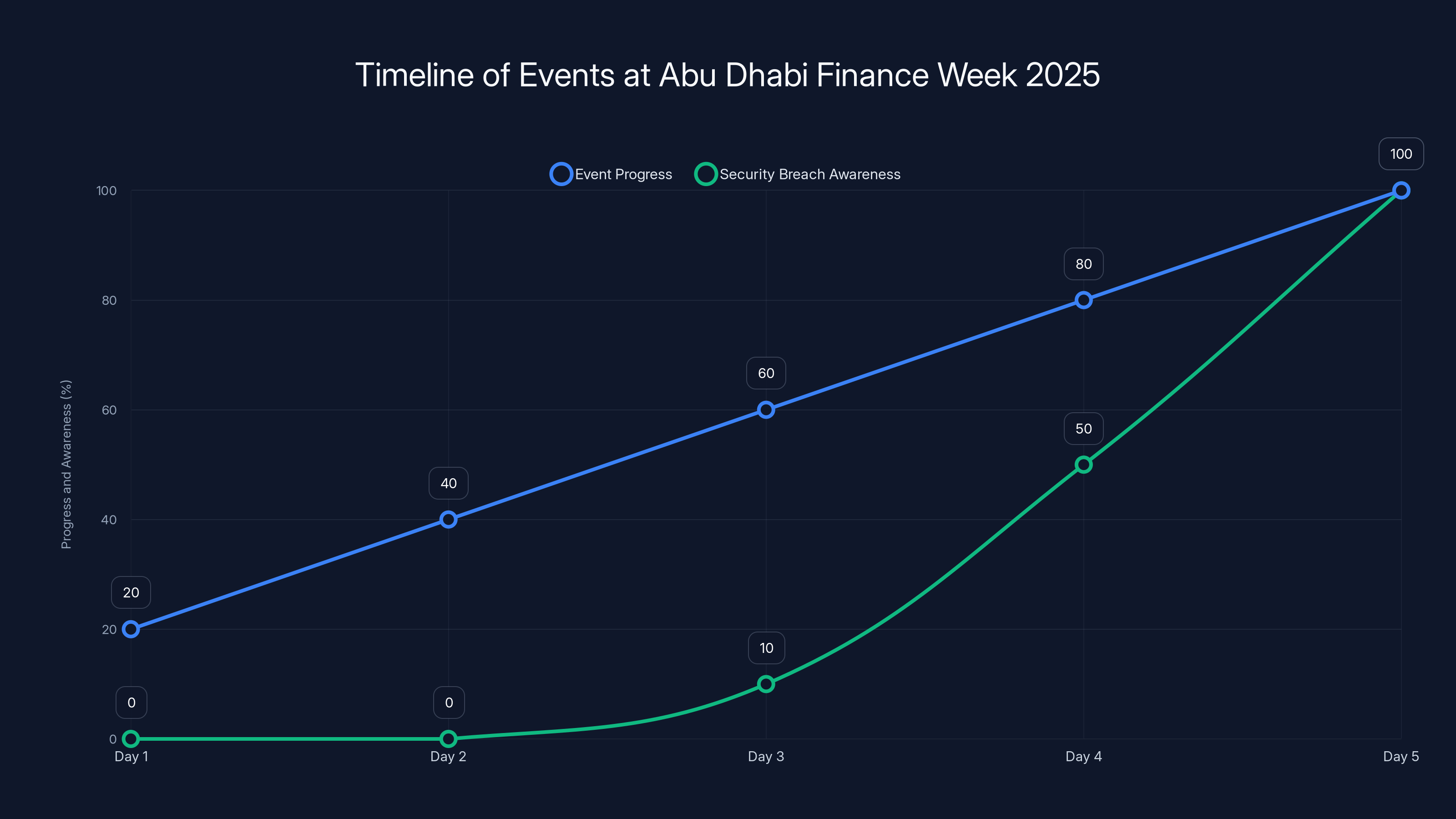
The timeline illustrates the progression of Abu Dhabi Finance Week 2025 and the increasing awareness of the security breach. Estimated data suggests that the breach was identified midway through the event.
Understanding Cloud Storage Security: Why Misconfiguration Happens
To understand how something like this happens at a sophisticated organization like Abu Dhabi Finance Week, you need to understand how cloud storage actually works and where the security gaps typically emerge.
Most organizations use cloud providers like Amazon S3, Google Cloud Storage, or Microsoft Azure to store sensitive files. These platforms are incredibly powerful and flexible. They allow organizations to upload documents, scale storage instantly, and access files from anywhere. But with flexibility comes complexity. And with complexity comes configuration options that can go wrong.
Here's a simplified version of how the Abu Dhabi breach likely unfolded: A third-party vendor needed to store passport scans from attendees. They set up a cloud storage bucket. They configured it to accept file uploads from a web form. But when they configured it, they left the bucket's access controls set to "public." In Amazon S3, for example, this means anyone on the internet with the bucket's URL can list all the files inside and download them.
This isn't a sophisticated attack. It's not exploiting a zero-day vulnerability or using advanced hacking techniques. It's just... bad configuration. And the scary part is how common this is.
Cloud security researchers regularly scan the internet for publicly accessible buckets containing sensitive data. They find millions of them. Databases containing customer records, health information, financial data, and yes, identity documents. Most of these buckets aren't intentionally public. They're just misconfigured.
Why does this happen? Several reasons:
Complexity of configuration options - Cloud providers offer dozens of ways to control access. It's easy to make a mistake.
Rapid development cycles - Vendors rush to implement systems and plan to secure them later. Then "later" never comes.
Default settings - Some cloud services default to insecure settings. Developers need to actively change them to secure settings, which requires knowledge and diligence.
Lack of security training - Many developers and operations teams don't have formal security training. They don't know what they don't know.
Assumption of obscurity - Some teams think that as long as the URL isn't publicized, the data is safe. This "security through obscurity" fails when researchers systematically scan for exposed buckets.
The Abu Dhabi Finance Week breach hits all these points. A third-party vendor managing attendee data without adequate security expertise, rushing to implement a system before the event, leaving default settings unchanged, and hoping nobody would find the bucket.
The Security Researcher Discovery: How This Actually Got Found
Roni Suchowski, the freelance security researcher and consultant who discovered the breach, found it through methods that are now standard in security research: systematic scanning and enumeration of cloud storage buckets.
Suchowski and other security researchers use tools that attempt to find publicly accessible cloud storage by testing common naming patterns. Event organizers might name their storage bucket something like "adfw-2025-attendees" or "abu-dhabi-finance-week-documents." Researchers scan for these patterns and test them for public accessibility.
When Suchowski found the bucket, it wasn't through some advanced exploit. They simply accessed a URL and were able to list all the files inside. The directory listing showed file names like "cameron_david_passport.pdf" and "scaramucci_anthony_id.pdf." Anyone with the bucket URL could download all of them.
The responsible disclosure process that followed is actually the right way for this to work, even though it's not glamorous. Suchowski reported the vulnerability to ADFW and the vendor. The vendor secured the bucket. ADFW issued a statement. The Financial Times reported on it. And now we're discussing it here.
Compare this to how many breaches actually unfold: data exposed for months or years, discovered only when criminals start selling it on darknet forums, organizations learning about breaches from journalists rather than from their own systems. In that context, the Abu Dhabi breach's discovery and response process was actually relatively good. It's just that the initial failure was so basic that it's embarrassing even by data breach standards.
What Evidence Actually Suggests About Malicious Access
ADFW's statement that "access activity was limited to the researcher who identified the issue" requires some unpacking. This claim tells us something important, but it also has limits in what it can tell us.
Cloud platforms like Amazon S3 maintain access logs. These logs record who accessed what files and when. If ADFW checked the logs carefully, they can determine whether anyone other than Suchowski actually accessed the exposed data. If the only access logs show Suchowski's IP address and the vendor's own access patterns, then technically the claim is accurate: no malicious actors accessed the data.
But there are caveats. Access logs can be disabled. An attacker with sufficient privileges could delete access logs. Some cloud configurations don't enable logging by default. If logs weren't enabled from the start, then ADFW and the vendor have no way of knowing whether other people accessed the data or not. They'd be making an educated guess, not a fact-based determination.
Additionally, "access activity was limited" could mean different things. It could mean nobody else accessed the bucket. Or it could mean nobody downloaded the files but people may have listed them. Or it could mean one person accessed it who wasn't Suchowski. The language is carefully constructed to suggest good news while leaving room for other interpretations.
For the victims—Cameron, Scaramucci, Teng, Berger, and the other 695 exposed individuals—the distinction might not matter much. Whether the data was exposed to hackers or just researchers, it was still exposed. Their passport information is still potentially compromised. If someone were going to use that information for identity theft or fraud, they could have already done it while the bucket was public.

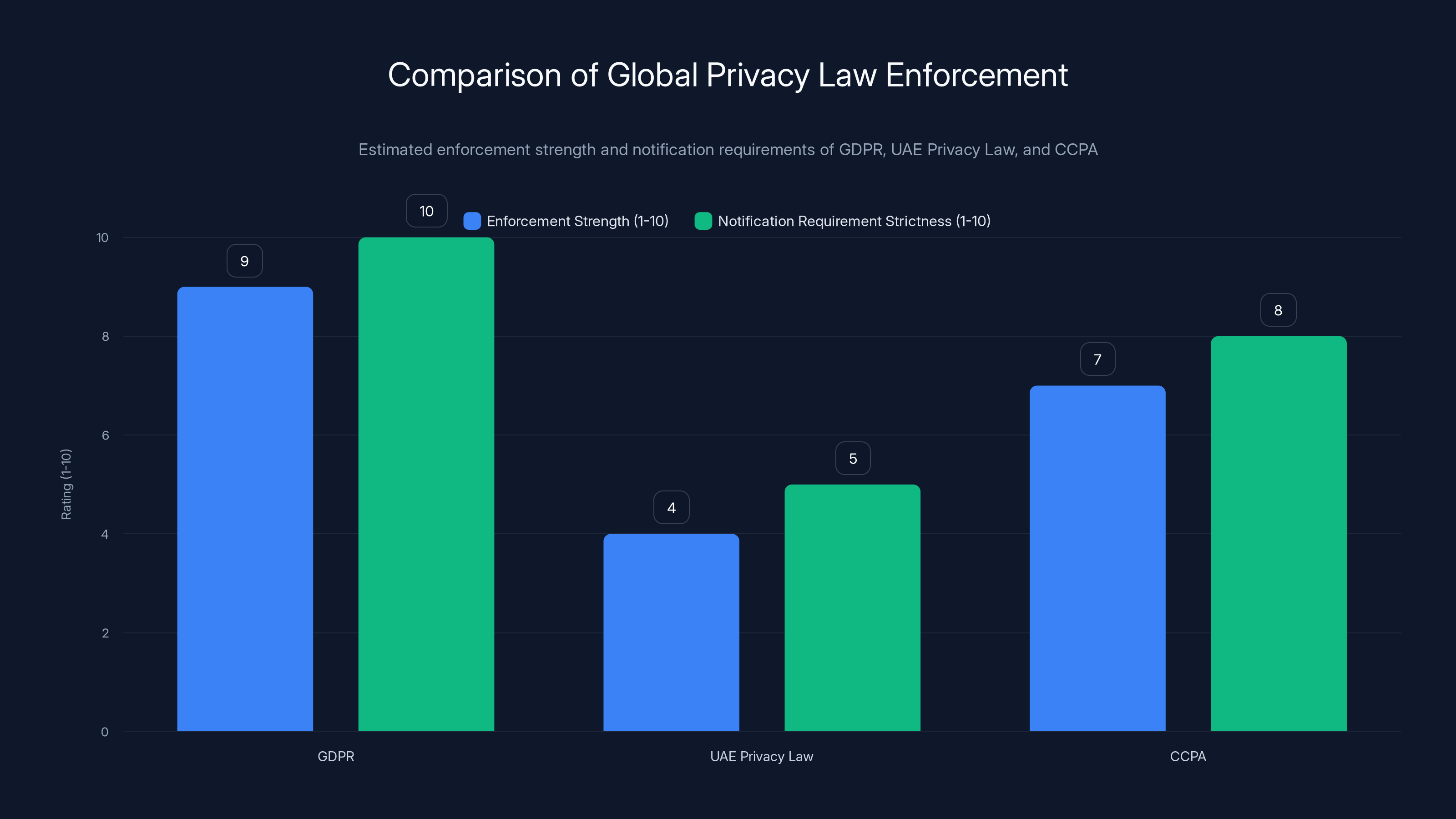
GDPR is the most stringent in enforcement and notification requirements, followed by CCPA. UAE Privacy Law is less developed in enforcement. Estimated data based on typical legal analysis.
Global Regulations: GDPR, Privacy Laws, and Abu Dhabi's Framework
When a breach like this happens, the first question from a legal standpoint is: what regulations apply?
For events happening in the United Arab Emirates, the relevant framework is the UAE's Privacy Law (Federal Law No. 6 of 2020). This law, modeled somewhat after GDPR, requires organizations to protect personal data, obtain proper consent for processing, and notify individuals if their data is breached. However, enforcement is less developed than GDPR's, and the government hasn't published detailed guidance on breach notification requirements.
For individuals from European Union countries, GDPR applies. Organizations processing EU citizen data must follow GDPR's strict requirements. That includes notifying people of breaches within 72 hours (unless the breach is unlikely to create risk), documenting what happened, and potentially paying fines up to €20 million or 4% of annual revenue. Since David Cameron and other EU citizens are among the exposed individuals, GDPR's requirements apply to any organization processing their data, including ADFW.
For US-based individuals like Scaramucci, requirements vary by state. California's CCPA is the strictest US privacy law, requiring breach notification and offering individuals rights similar to GDPR. Other states have weaker requirements. But increasingly, state laws are moving toward California's model, so expectations around breach notification are rising.
The question is: did ADFW properly notify the affected individuals? The public statements don't clearly indicate that individual notifications were sent. If affected individuals found out about the breach through media reports rather than through official ADFW notification, then ADFW likely violated GDPR and potentially other privacy laws.
Regulators in Europe and the US haven't announced investigations into the breach, but that doesn't mean they won't. These investigations can take months or years to conclude. If they do investigate and find violations, fines could be significant.
Event Industry Best Practices: What Should Have Happened
Security professionals and event management experts have been discussing conference data security for years. Several best practices have emerged that would have prevented the Abu Dhabi breach.
Principle 1: Data minimization - Only collect the data you actually need. Do you really need a full passport scan, or would a passport number be sufficient? If you need document verification, can you use a third-party verification service instead of storing the actual documents?
Principle 2: Encryption in transit and at rest - Any data sent to servers should be encrypted (HTTPS). Any data stored should be encrypted so that even if someone accesses the database, they can't read the contents.
Principle 3: Access controls - Only the people who need access to attendee documents should have access. That's not everyone on the vendor's team. It's a small group of people with documented justification for needing access.
Principle 4: Authentication requirements - Every system containing sensitive data should require authentication. Not just private URLs. Not security through obscurity. Actual logins with strong passwords or API keys.
Principle 5: Regular security audits - Before the event, during the event, and after the event, security professionals should test the systems for vulnerabilities. This isn't a one-time check; it's an ongoing process.
Principle 6: Vendor security assessment - Before contracting with a vendor, organizations should assess their security practices. Ask about certifications (SOC 2, ISO 27001), security policies, and incident response procedures.
Principle 7: Data retention policies - How long do you actually need to keep attendee data? If you can delete it after the event, that's safer than storing it indefinitely. Many events delete attendee data within 30 days of the event ending.
Principle 8: Incident response plan - Have a documented plan for responding to breaches. Who do you notify? What do you check? How do you communicate with affected individuals and regulators? This should be written down and tested before an incident occurs.
None of these practices are particularly advanced. They're not expensive or complex. They're just basic data security hygiene. The fact that Abu Dhabi Finance Week, a major financial event, didn't follow them is the real problem.
The Bigger Picture: Why This Matters Beyond Abu Dhabi
The Abu Dhabi Finance Week breach matters for reasons that extend far beyond the 700 individuals whose documents were exposed.
First, it demonstrates that even sophisticated, well-funded organizations with strong reputations can suffer basic security failures. If Abu Dhabi Finance Week—organized by a global financial market under UAE leadership, attended by the world's most influential financial figures—can leave sensitive data unprotected, then no organization can assume it's too important or too professional to fail.
Second, it highlights how third-party vendors create systemic risk. ADFW didn't fail because of internal incompetence; they failed because they trusted a vendor who was incompetent. As organizations increasingly outsource data handling to specialized vendors, the security of your data depends on the security practices of organizations you have no direct control over.
Third, it reveals the gap between public perception and actual security practices in event management. Most attendees assume that major conferences have serious security protocols in place. They assume passport documents are handled with care equivalent to airport security or government agencies. In reality, event security is often minimal.
Fourth, it shows that security researchers are essential infrastructure. Roni Suchowski deserves credit not just for finding the breach but for responsibly disclosing it. Without independent researchers systematically testing systems, most of these breaches would remain undiscovered indefinitely.
Fifth, it suggests that current regulatory frameworks aren't sufficient. Despite GDPR and increasing privacy regulations, organizations are still exposing sensitive data because violations are rare and fines are often absorbed as a cost of business. When organizations prioritize speed and cost over security, and when violations carry modest penalties, breaches will continue.
Sixth, it highlights the need for better incident response transparency. ADFW has been vague about the details: when the bucket was created, when it was exposed, exactly how many people accessed it before Suchowski found it, whether individuals were properly notified. Organizations should be required to disclose specific timelines and findings, not just general statements.
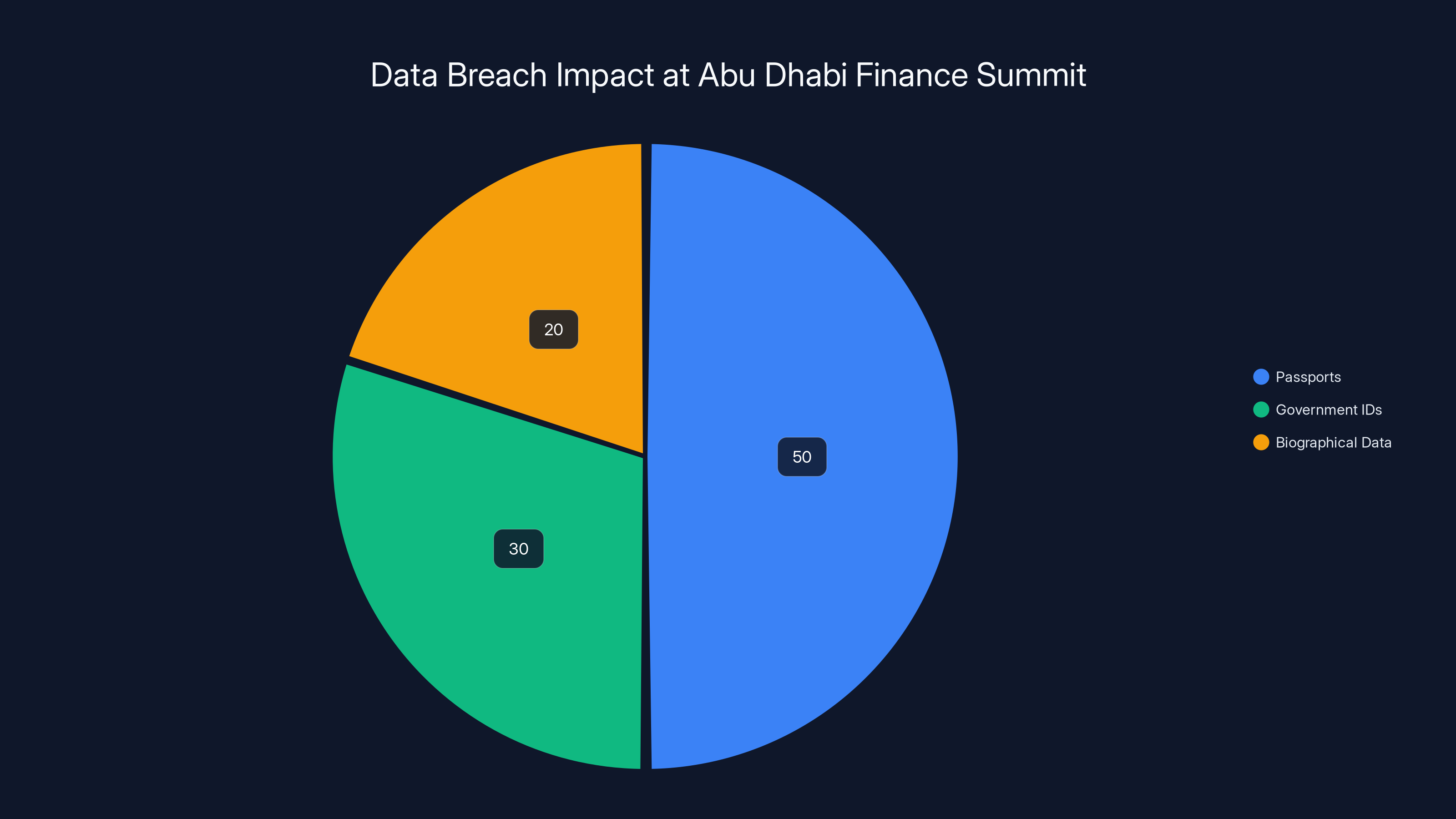
Estimated distribution of exposed documents shows passports as the most affected, highlighting the risk of identity theft in such breaches.
What You Should Do If You Attended Abu Dhabi Finance Week
If your name appears in the list of exposed attendees, or if you attended ADFW 2025 and submitted passport or ID documents, here are concrete steps you should take.
Step 1: Monitor your identity - Enroll in a credit monitoring service like Equifax, Experian, or Trans Union (these are free in many countries). These services will alert you if someone tries to open accounts in your name. Alternatively, use the free services like Have I Been Pwned to check if your credentials appear in any known breach databases.
Step 2: Check your credit reports - Request a free credit report from the major reporting agencies. Review them for accounts you don't recognize or inquiries you didn't authorize. You're entitled to one free report per year from each agency.
Step 3: Consider a credit freeze - If you're concerned about identity theft, you can freeze your credit with the major reporting agencies. This prevents creditors from accessing your credit report without your permission, which blocks most identity theft attempts. You can unfreeze it temporarily when you actually apply for credit.
Step 4: Monitor your financial accounts - Review bank statements, credit card statements, and investment accounts regularly for unauthorized transactions. Set up alerts for large transactions so you're notified immediately.
Step 5: Be cautious of phishing and social engineering - Criminals who have your passport information might use it to construct convincing phishing emails or phone calls. Be suspicious of unexpected messages claiming to be from government agencies or financial institutions. Verify by calling official numbers, not numbers provided in the message.
Step 6: Change important passwords - If you used the same password for your conference registration that you use elsewhere, change it immediately. Use unique, strong passwords for important accounts (email, banking, investment platforms).
Step 7: Document the breach - Keep records of this incident. Save the Financial Times report, the ADFW statement, and any other documentation. This will be useful if identity theft occurs and you need to prove that your information was compromised.
Step 8: File a complaint if necessary - If you discover fraudulent activity tied to the exposed information, file reports with the FTC (in the US), the relevant data protection authority in your country (like the ICO in the UK or CNIL in France), and local law enforcement.

How Organizations Should Respond to Breaches
ADFW's response to the breach, while better than complete silence, has some notable gaps. Here's what a textbook breach response should look like, and where ADFW falls short.
Immediate response (first 24-48 hours):
- Confirm the breach actually occurred and assess scope
- Secure the compromised system to prevent further access
- Preserve evidence for investigation
- Notify key stakeholders internally
ADFW did this. They secured the database when Suchowski reported it and initiated an investigation.
Short-term response (48 hours to 1 week):
- Conduct a thorough investigation to understand what was exposed and for how long
- Determine the impact on different types of individuals
- Develop a detailed timeline
- Draft communications for affected individuals
- Notify regulators if required by law
ADFW partially did this. They conducted an investigation, but the results haven't been fully transparent. They haven't provided detailed timelines or complete explanations of scope.
Medium-term response (1-2 weeks):
- Send notifications to affected individuals with specific details about what was exposed, when it was exposed, and what they should do
- Offer free credit monitoring or identity theft protection services
- Set up a dedicated response hotline or email
- Publish detailed findings from the investigation
ADFW hasn't clearly done this. There's no evidence that affected individuals received detailed notifications. There's no mention of credit monitoring services being offered.
Long-term response (ongoing):
- Implement security improvements to prevent similar breaches
- Conduct a third-party security audit to verify improvements
- Work with regulators on compliance requirements
- Provide regular updates to affected individuals
Too early to tell if ADFW will do this, but it's critical.
Transparency component (throughout):
- Be specific about what happened, not vague
- Provide timelines: when was data collected? When was it exposed? When was it discovered? When was it secured?
- Explain root causes
- Detail the investigation findings
- Describe remediation steps
This is where ADFW's response falls short. The statements have been vague: "limited subset of attendees," "access activity was limited," "vulnerability in a third-party vendor." More specific information would better serve affected individuals.
The Cryptocurrency Connection: Richard Teng and Binance
One particular aspect of the Abu Dhabi breach deserves closer examination: the exposure of Richard Teng's credentials.
Teng serves as co-chief executive of Binance, the world's largest cryptocurrency exchange by trading volume. But his history with Abu Dhabi is even more relevant: he previously served as the chief executive of the Abu Dhabi Global Market, the very organization that organized ADFW.
This creates a particularly awkward situation. Teng helped build the ADGM and presumably helped establish its organizational culture and security practices. Having his passport leaked by ADGM's signature event is professionally embarrassing. It also raises questions about whether Teng had any involvement in approving the data handling practices that led to the breach.
Moreover, Teng's credentials in the hands of bad actors create specific security threats. As a major figure in cryptocurrency, his identity documents could be used to:
- Phishing attacks targeting Binance employees, claiming to represent Teng
- Social engineering attacks against banks or other financial institutions he does business with
- Creating fraudulent accounts or credentials using his identity
- Targeted kidnapping or extortion attempts (Teng is a high-net-worth individual)
For Binance, the fact that one of its top executives had credentials exposed at a high-profile financial event could be reputationally damaging. It raises questions about whether Binance's own internal security practices are as robust as claimed.

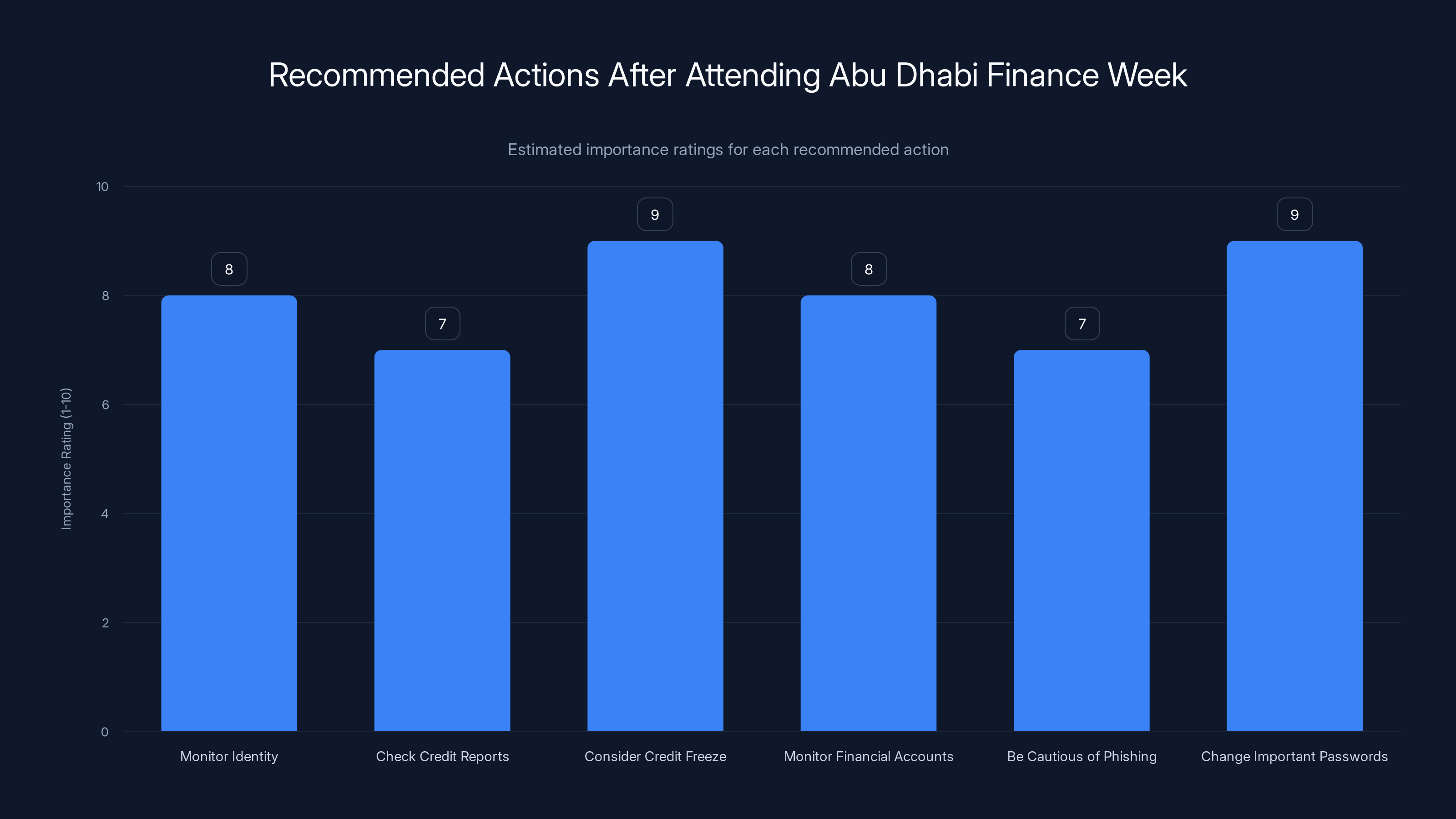
Estimated data: Credit freeze and changing important passwords are rated highest in importance for protecting against identity theft after attending ADFW.
Long-Term Risks: Identity Theft, Fraud, and Targeted Attacks
When your passport is exposed, the immediate risk isn't credit card fraud. It's something worse: identity theft that's harder to detect and harder to reverse.
With your passport information, criminals can:
Create synthetic identities - Combine your real passport information with fake information to open accounts. This is harder to detect because the passport number is real, creating a veneer of legitimacy.
Apply for government benefits - In some jurisdictions, criminals can apply for benefits in your name using your passport information.
Fraudulently establish residency - Some countries allow address changes and other administrative changes with minimal verification. Criminals could potentially change your address or establish additional documentation in your name.
Facilitate money laundering - Your identity could be used to open accounts or facilitate financial transactions that are actually criminal money laundering.
Enable international fraud - Passport information makes it easier for criminals to conduct cross-border fraud using your identity.
The timeline for these risks is also concerning. Identity theft from passport exposure isn't like credit card fraud, where fraudulent charges appear within days. Identity theft can take months or even years to manifest. Criminals might hold onto your information and use it later, at a time when the breach is no longer in your mind. This is why ongoing vigilance is important.
For public figures like Cameron, Scaramucci, Teng, and Berger, there's an additional risk: targeted attacks. Criminals and hostile state actors maintain databases of compromised credentials on high-value individuals. The Abu Dhabi passport data is now potentially part of those databases, making these individuals targets for more sophisticated attacks in the future.
The Broader Trend: Event Industry Data Breaches
Abu Dhabi Finance Week isn't an isolated incident. It's part of a broader trend of major events suffering data breaches due to misconfiguration and inadequate security practices.
Consider some other major breaches in the event industry:
Marriott Conference Breach (2020) - Marriott's conference registration system was compromised, exposing attendee information including credit card data. The company hadn't implemented adequate segmentation between its conference system and its main customer database.
CES Attendee Data Leak (2019) - The Consumer Electronics Show, one of the world's largest tech conferences, exposed attendee data through a misconfigured database that security researchers found while scanning for vulnerabilities.
Global Corporate Events Breach (2021) - A data broker serving multiple large corporate events left customer information exposed on misconfigured AWS buckets. Thousands of event attendees were affected.
SXSW Data Exposure (2018) - SXSW, the massive film and interactive conference, suffered multiple data exposures through third-party vendors and misconfigured systems.
The pattern is clear: large events collect sensitive data, rely on third-party vendors to manage that data, and frequently fail to implement adequate security. When researchers look for breached data, events are consistently among the low-hanging fruit.
Part of the problem is regulatory arbitrage. Event organizers aren't classified like banks or healthcare providers that face heavy compliance requirements. They can get away with minimal security because regulators don't focus on them. But as breaches increase and become more public, that's starting to change.

Lessons for Organizations: Security Design Principles
For organizations planning events or managing attendee data, the Abu Dhabi breach offers concrete lessons in security design.
Lesson 1: Never trust third parties by default - If you must use a vendor, verify their security practices before signing. Ask for SOC 2 audits, incident response procedures, and references from other organizations they work with. Build security requirements into vendor contracts.
Lesson 2: Default to secure configurations - If you implement any system, the default should be the most restrictive configuration. If databases are set to private by default, that's good. If they're public by default and require manual configuration to secure them, that's bad. Design systems where the secure choice is the easy choice.
Lesson 3: Document and automate your security policies - Security shouldn't depend on individual developers remembering to do things correctly. Use infrastructure as code, automated testing, and policy enforcement to ensure security practices are consistent.
Lesson 4: Monitor continuously - After you implement security controls, monitor whether they're actually working. Run regular scans for publicly accessible databases. Test your authentication systems. Have security researchers periodically assess your systems. Don't just implement security once and assume it's working forever.
Lesson 5: Plan for incidents - Even with perfect security, incidents happen. Have a plan for responding: who to notify, what to investigate, how to communicate with affected individuals and regulators. Test this plan so people know their roles when an actual incident occurs.
Lesson 6: Be transparent - When breaches happen, communicate clearly about what you know and what you're still investigating. Vague statements like "limited subset" and "minimal access" raise more suspicion than honest explanations of what happened and what you're doing about it.
Lesson 7: Prioritize security in culture - Security isn't a checkbox. It's something that should be embedded in how your organization makes decisions. When development speed conflicts with security, the decision should usually favor security. When a vendor offers cheaper services but has weaker security practices, that should factor into your decision.
Future Prevention: Technology and Process Improvements
Where do we go from here? How can the event industry prevent breaches like Abu Dhabi from happening again?
From a technology perspective, several approaches could help:
Zero-knowledge architecture - Instead of storing actual passport documents, use services that verify documents without storing them. The verification service holds the document temporarily, verifies it, and discards it. You never store sensitive documents.
Hardware security tokens - For high-security events involving government officials and sensitive attendees, require multi-factor authentication using hardware tokens. This prevents account takeovers even if credentials are compromised.
End-to-end encryption - All communications and document transfers should use encryption that only sender and recipient can decrypt. Even if the database is breached, encrypted documents are useless without the encryption keys.
Homomorphic encryption - This advanced technique allows organizations to perform operations on encrypted data without decrypting it. A system could verify passport validity without ever decrypting the actual document.
Blockchain verification - Instead of storing documents, store cryptographic hashes on a blockchain. This creates an immutable record of document verification without storing sensitive documents.
From a process perspective, improvements include:
Security by default frameworks - Use frameworks like NIST Cybersecurity Framework or CIS Controls to systematize security implementation. Don't rely on individual decisions.
Vendor certification requirements - Require vendors to maintain SOC 2 Type II certification or equivalent. Make this a condition of contract, with penalties for losing certification.
Regular penetration testing - Hire external security firms to regularly test your systems for vulnerabilities. Do this before events, during events, and after events. Fix vulnerabilities immediately.
Data minimization by default - Establish policies that minimize data collection. If you can verify attendees without storing their documents, do that. If you must store documents, set automatic deletion policies (delete data 30 days after the event ends).
Insurance requirements - Require cyber liability insurance and verify that vendors carry appropriate coverage. This aligns financial incentives with security.

The Regulatory Future: Stricter Requirements Ahead
The Abu Dhabi breach is likely to trigger stricter regulatory requirements for event management and vendor data handling.
In the EU, regulators are already becoming more aggressive about GDPR enforcement. The fines from the GDPR violations can reach up to €20 million or 4% of revenue, whichever is higher. For large event management companies, this could represent millions in penalties. Irish regulators have recently levied fines against Google, Meta, and others for GDPR violations, establishing a pattern of serious enforcement.
In the US, state-level privacy laws are increasingly strict. California's CCPA applies to any company processing California residents' data. Virginia's VCDPA, Colorado's CPA, and similar laws in other states apply to different populations. Collectively, these create a patchwork of requirements. Federal regulation might eventually standardize this, but until then, organizations must comply with multiple state regimes.
In the Middle East, regulators are developing frameworks. The UAE's Privacy Law, though less detailed than GDPR, is increasingly enforced. Saudi Arabia is developing privacy requirements. The trend globally is toward stricter data protection.
Expect to see regulatory focus on:
Vendor accountability - Regulators will increasingly hold organizations liable for vendor breaches, not just accepting "it was the vendor's fault." Contracts will need to include specific security requirements and liability clauses.
Data retention minimization - Regulations will likely require organizations to minimize data retention. If you don't need data, you shouldn't keep it. This is already in GDPR; it will expand.
Breach notification timelines - Regulations will push toward faster notification requirements. The EU's 72-hour requirement might become more universal.
Third-party audit requirements - Regulators will increasingly require organizations to document security audits and maintain compliance certifications.
Personal liability - Some jurisdictions are moving toward holding individual executives personally liable for data breaches. This creates stronger incentives for boards and C-suites to prioritize security.
For event organizers, this means security will become a cost of business rather than an optional add-on. The organizations that adapt earliest will gain competitive advantage.
Closing Thoughts: Trust and Accountability
When you attend a major conference like Abu Dhabi Finance Week, you're making a trust decision. You trust that organizers will handle your data responsibly. You trust that third-party vendors are competent and secure. You trust that if something goes wrong, you'll be notified and helped.
The Abu Dhabi breach violated all three of these trust relationships. The organizers failed to verify their vendors' security practices. The vendor failed to implement basic security. And the aftermath hasn't included transparent communication with affected individuals.
What makes this particularly concerning is that nothing about what went wrong is surprising to security professionals. Misconfigured databases are the leading cause of data breaches. Third-party vendors are frequent points of failure. Organizations are often vague about breach details. These are known problems with established solutions. The Abu Dhabi breach happened not because the security landscape is unsolved but because organizations chose not to implement known solutions.
This suggests the solution isn't technological—it's organizational and cultural. Security requires resources, expertise, and priority. Some organizations have these. Most don't. Until there's sufficient regulatory pressure or market pressure to make security a priority, breaches like Abu Dhabi will continue.
For individuals, the lesson is practical: be cautious about what data you share with event organizers. Provide the minimum required. Ask questions about how data will be protected. Monitor your accounts and credit afterward. Don't assume that just because an event is prestigious and well-organized, its data security practices are adequate. Past breaches suggest they often aren't.
For event organizers and vendors, the lesson should be clear: invest in security now or face larger costs later. The cost of a penetration test and security improvements is far less than the cost of a breach, regulatory fines, and damaged reputation.
The Abu Dhabi Finance Week breach is a wake-up call. Whether the industry heeds it remains to be seen.

FAQ
What exactly was exposed in the Abu Dhabi Finance Week breach?
Approximately 700 passport and government-issued ID card scans from ADFW 2025 attendees were exposed in a publicly accessible, misconfigured cloud database. The exposed documents belonged to high-profile individuals including former British Prime Minister David Cameron, US investor Anthony Scaramucci, Binance co-CEO Richard Teng, and EU Ambassador to the UAE Lucie Berger, among many others from financial and political sectors globally.
How did the breach happen technically?
A third-party vendor hired by ADFW to manage attendee data set up a cloud storage bucket without enabling authentication or access controls. The storage environment was left publicly accessible on the internet, meaning anyone with the bucket's URL could list all files and download them. This is a misconfiguration, not a sophisticated hack, and represents basic data security failure rather than advanced exploitation.
Was there evidence that hackers accessed the exposed data?
ADFW stated that "access activity was limited to the researcher who identified the issue," based on reviewing access logs. However, this claim has limitations: access logs may not have been enabled from the start, logs could potentially be deleted by attackers with sufficient privileges, and the vague language leaves room for interpretation. For the affected individuals, whether hackers accessed the data or just researchers, the fact remains that their documents were exposed.
What should people do if they attended the summit and submitted documents?
Enroll in credit monitoring services, request free credit reports from major bureaus, monitor financial accounts for fraudulent activity, be cautious of phishing attempts targeting you personally, consider placing a credit freeze with reporting agencies, maintain strong unique passwords for important accounts, and save documentation of the breach for future reference. Monitor your accounts continuously for the next 2-3 years, as identity theft often manifests months or years after data exposure.
What regulations apply to this breach?
ADFW must comply with UAE Privacy Law since the organization operates in the UAE. Additionally, since EU citizens including David Cameron were affected, GDPR applies to processing of their personal data, requiring breach notification within 72 hours and potential regulatory fines. US state privacy laws including California's CCPA may apply for affected US residents. Each jurisdiction has different notification timelines and penalties for non-compliance.
Why do misconfigured databases cause so many breaches?
Cloud platforms like Amazon S3 offer tremendous flexibility in configuring access controls, but this complexity creates opportunities for configuration errors. Default settings aren't always secure, developers often lack formal security training, rapid development cycles lead to security being deferred, and many teams rely on obscurity rather than proper access controls. Security researchers regularly find millions of publicly accessible cloud buckets containing sensitive information, suggesting misconfiguration is industry-wide.
Could this have been prevented?
Yes. Basic security practices would have prevented this breach: encrypting data both in transit and at rest, requiring authentication for all access, performing regular security audits before events, assessing vendor security practices before contracting with them, and maintaining strict access controls. None of these are cutting-edge or expensive. They're fundamental data security hygiene that major organizations should implement as standard practice.
What are the long-term risks for people whose data was exposed?
Beyond immediate identity theft risk, exposed passport information creates vulnerability to synthetic identity fraud, social engineering attacks targeting banks and other institutions, government benefit fraud, cross-border financial fraud, and for public figures, targeted attacks from criminals and hostile actors. Identity theft from passport exposure often takes months or years to manifest, so vigilance should continue long after the initial breach.
Will individuals affected by this breach receive compensation?
None has been publicly announced. ADFW has stated it will cover costs related to the breach investigation and response, but specific details about victim compensation aren't clear. In some jurisdictions, individuals might be able to pursue civil claims, though this requires legal action. Credit monitoring might be offered, though as of now this hasn't been clearly communicated.
What changes will the event industry make based on this breach?
Expect stricter security requirements for vendors, mandatory security certifications, more frequent penetration testing, reduced data retention (deleting attendee data sooner after events), and potentially regulatory requirements for event management. Organizations that implement security improvements first will gain competitive advantage. However, industry-wide change typically happens gradually and requires regulatory or market pressure to accelerate.
The Abu Dhabi Finance Week data breach represents a critical moment for the event industry. As conferences collect increasingly sensitive data and rely more heavily on third-party vendors, the risks multiply. But so do the solutions. Organizations that prioritize security now will protect their attendees, reduce their regulatory risk, and build lasting trust. Those that don't will face increasing breaches, regulatory fines, and damaged reputations. The choice is becoming clearer every day.
Key Takeaways
- 700+ high-profile attendees at Abu Dhabi Finance Week had passports and ID documents exposed through a misconfigured, publicly accessible cloud database managed by a third-party vendor
- Exposed individuals included former British PM David Cameron, US investor Anthony Scaramucci, Binance co-CEO Richard Teng, and EU Ambassador Lucie Berger, representing approximately 2% of 35,000+ total attendees
- Root cause was basic security failure: a cloud storage bucket left unprotected without authentication requirements, exemplifying the #1 cause of enterprise data breaches (misconfigured databases, 27% of all breaches)
- Security researcher Roni Suchowski discovered the breach through routine scanning and responsibly disclosed it before hackers could exploit it; no evidence of malicious access but transparency about exposure duration remains lacking
- Organizations must implement fundamental security practices: encryption, access controls, vendor verification, regular audits, and data minimization; current event industry practices fall far short of these standards
Related Articles
- EU Parliament's AI Ban: Why Europe Is Restricting AI on Government Devices [2025]
- EU Parliament Bans AI on Government Devices: Security Concerns [2025]
- Tenga Data Breach 2025: How a Phishing Email Exposed Customer Data
- Japanese Hotel Chain Hit by Ransomware: What You Need to Know [2025]
- Dell Zero-Day Vulnerability: Hardcoded Credentials Exploited for 2 Years [2025]
- Tesla Stops Using 'Autopilot' in California: What Changed [2025]
![Abu Dhabi Finance Summit Data Breach: 700+ Passports Exposed [2025]](https://tryrunable.com/blog/abu-dhabi-finance-summit-data-breach-700-passports-exposed-2/image-1-1771432899813.jpg)



