Car Gurus Data Breach: Shiny Hunters' Latest 1.7M Record Heist and What It Means for Enterprise Security [2025]
Let's be real: another major data breach. Another headline screaming about millions of stolen records. Another company going quiet while the world waits for a statement that might never come.
But here's what makes the Car Gurus breach different—and honestly, more terrifying. This wasn't a traditional ransomware attack or some sophisticated zero-day exploit. Shiny Hunters pulled off 1.7 million record theft using something almost embarrassingly simple: a phone call.
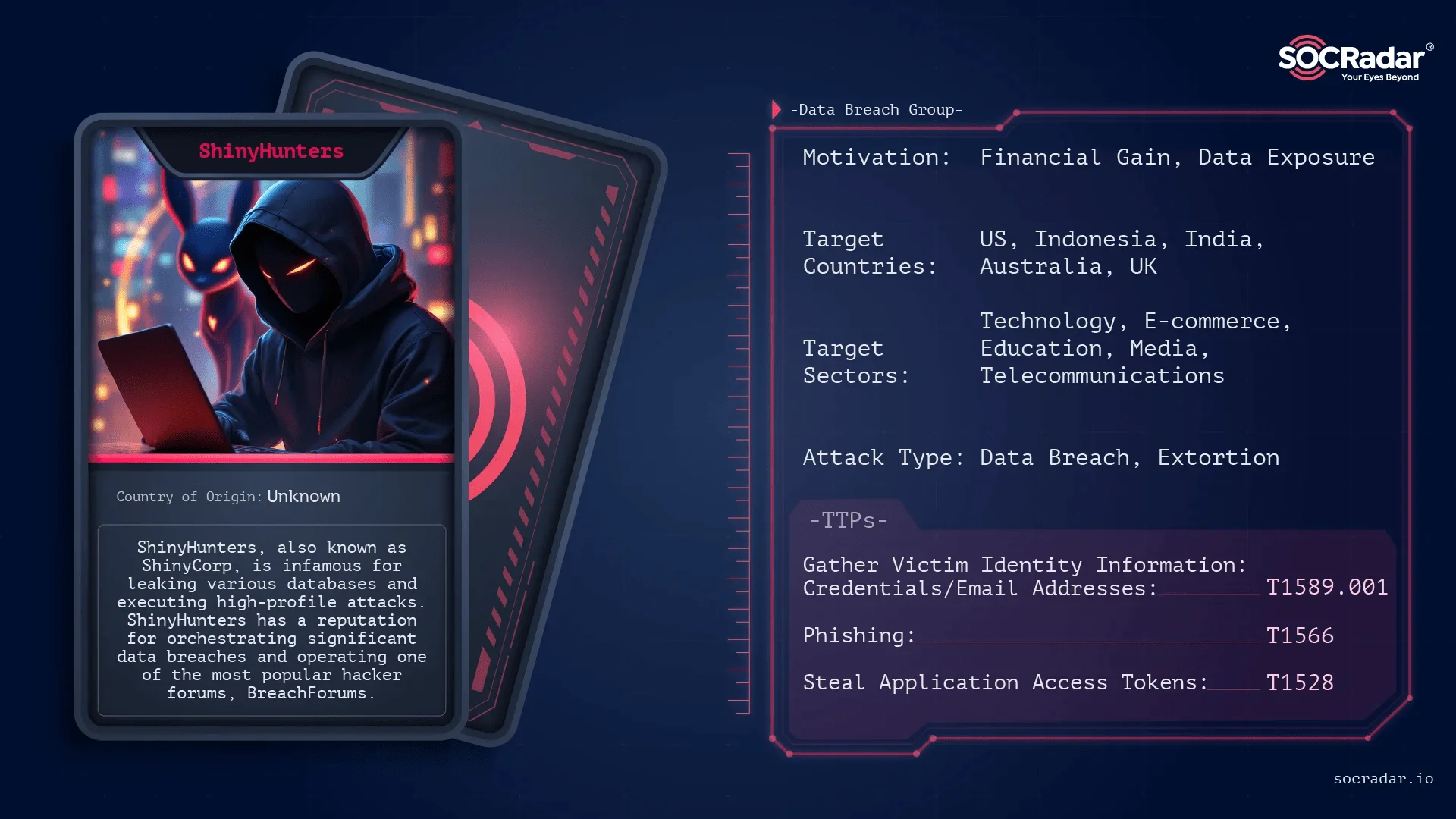
I'm talking about vishing attacks. Social engineering at scale. And they're working with such devastating effectiveness that this marks the 15th major company Shiny Hunters has breached using the exact same playbook in recent months.
The list reads like a who's who of major enterprises: Canada Goose, Match Group, Panera Bread, Carvana, Edmunds, Mercer Advisors, Beacon Pointe Advisors, Figure Technology Solutions, Betterment, and now Car Gurus. These aren't small startups. These are Fortune 500 companies and well-funded tech firms. And they all fell victim to the same basic attack vector.
What makes this breach particularly unsettling isn't just the number of records stolen or the companies affected. It's the sophistication of the attack combined with its simplicity. Shiny Hunters didn't need zero-days. They didn't need to crack passwords or exploit unpatched vulnerabilities. They needed a convincing phone call, some customized phishing pages, and knowledge of how enterprise authentication systems work.
In this guide, I'm breaking down exactly what happened, how Shiny Hunters pulled it off, what organizations can learn from this incident, and—most critically—how to actually defend against vishing attacks when they're this well-executed.
TL; DR
- The Breach: Shiny Hunters stole 1.7 million records from Car Gurus including personally identifiable information and corporate data
- The Method: Vishing attacks (voice phishing) combined with customized phishing infrastructure to compromise SSO systems
- The Scale: This is the 15th major company compromised by Shiny Hunters using identical attack techniques in recent months
- The Impact: If confirmed, affects Car Gurus employees, customers, and potentially impacts the broader automotive marketplace
- The Timeline: Shiny Hunters issued a deadline of February 20, 2026 before promising to leak data on the dark web


ShinyHunters generates significant revenue through direct extortion, dark web sales, and insurance claims. Estimated data shows direct extortion as the most lucrative method.
Understanding the Car Gurus Breach: What Actually Happened
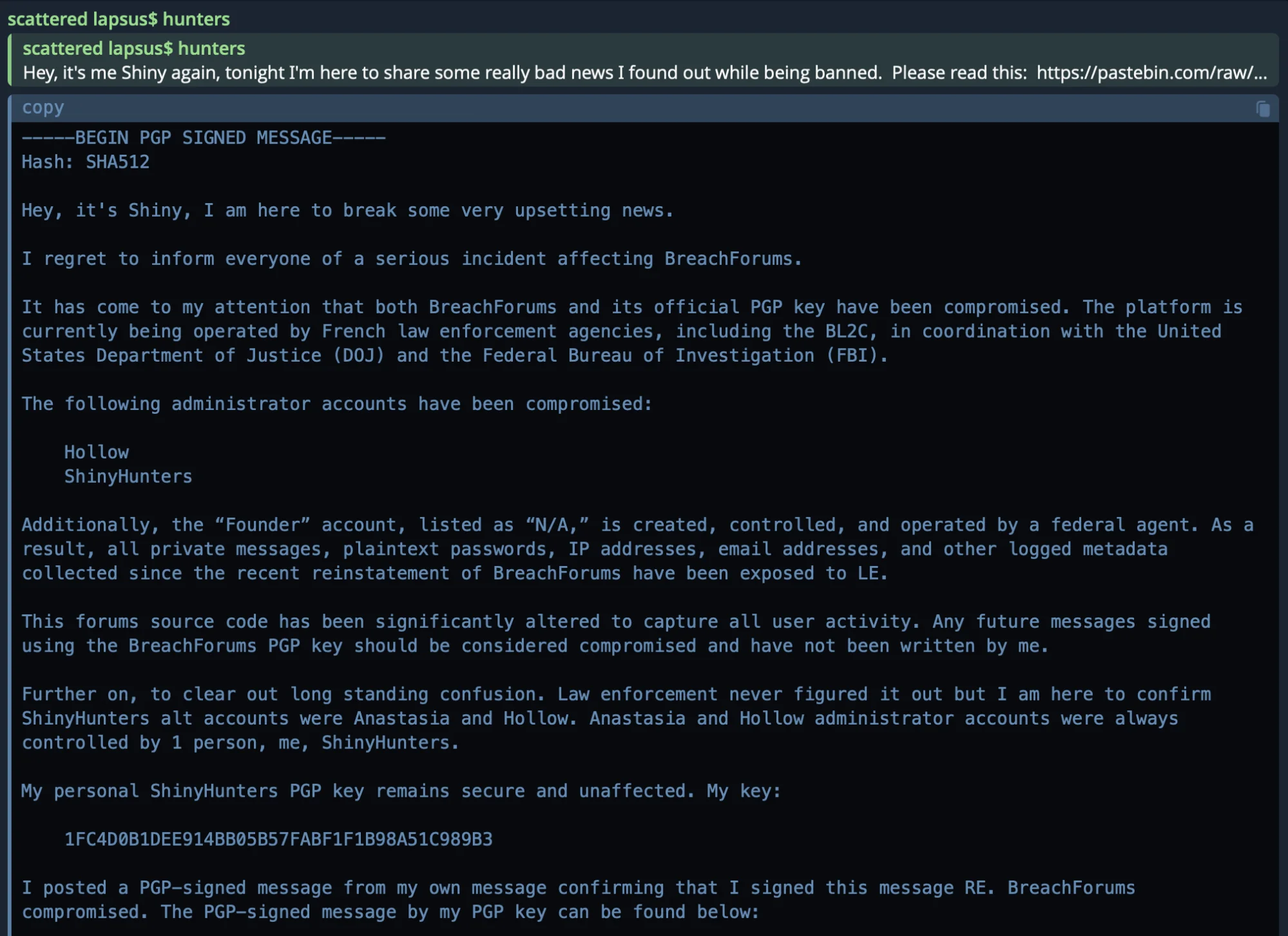
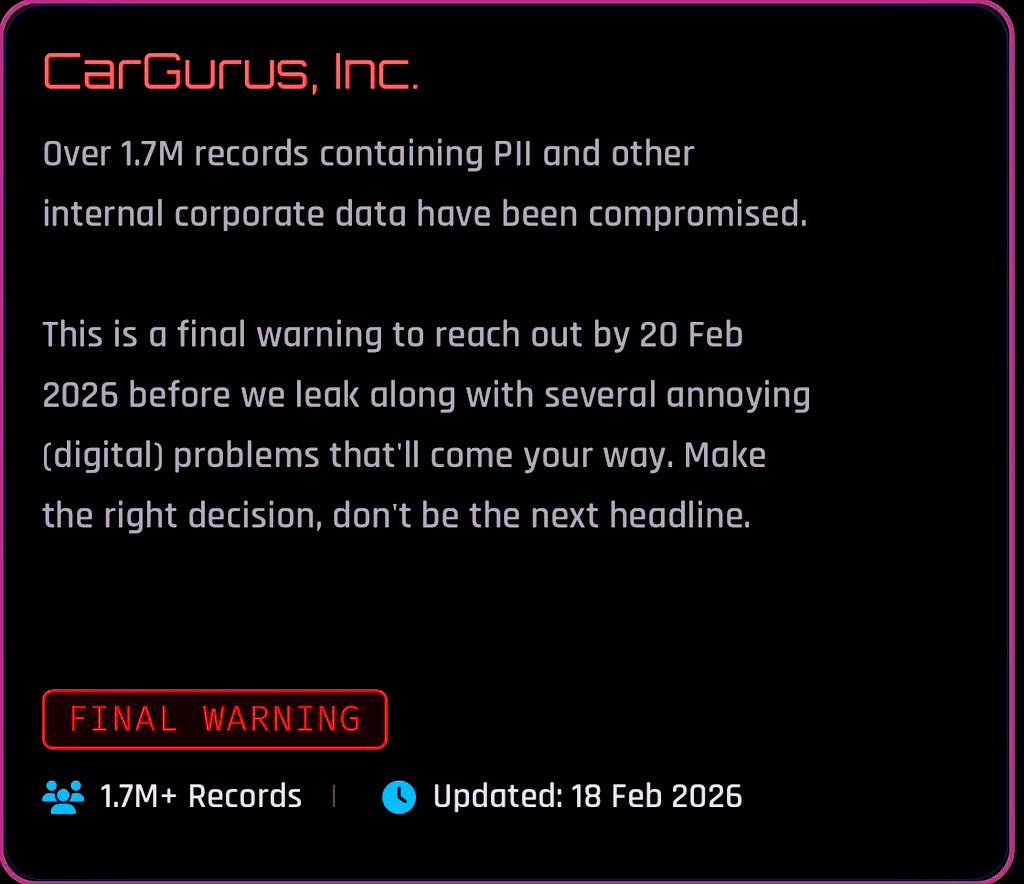
On its surface, the Car Gurus breach announcement came from an unexpected source: Shiny Hunters themselves. This notorious hacking collective, known for targeting enterprise organizations, posted a notice on their data leak site claiming responsibility for the compromise. No initial statement from Car Gurus. No press release. Just a message on the dark web.
"This is a final warning to reach out by 20 Feb 2026 before we leak along with several annoying (digital) problems that'll come your way," the group wrote in their announcement. Translation: pay up, or we'll publicly release your data and potentially launch additional attacks.
The claimed compromise includes personally identifiable information—names, email addresses, phone numbers, potentially financial data—along with what Shiny Hunters describes as "other internal corporate data." That second category is vague on purpose. It could include customer lists, employee records, salary information, proprietary business documents, or anything valuable enough to attract buyers on dark web marketplaces.
1.7 million records is a massive number. Put it in perspective: that's roughly equivalent to the entire population of New Zealand. Or about 0.5% of the entire US population. For a single company to have that many records stolen in one incident represents a catastrophic security failure at some level of the organization.
Car Gurus, for its part, has remained publicly silent. As of the time of reporting, the company's official website says nothing about a potential breach. No notification to customers. No acknowledgment to shareholders. No public statement addressing the allegations. That silence could mean several things: the company is investigating internally, the breach hasn't been verified, negotiations are happening behind the scenes, or the company is hoping the story dies down without widespread media coverage.
However, the company's silence also sends a message to customers, employees, and partners. In an era where transparency is expected—and often required by law—public radio silence about a breach of this magnitude breeds distrust.

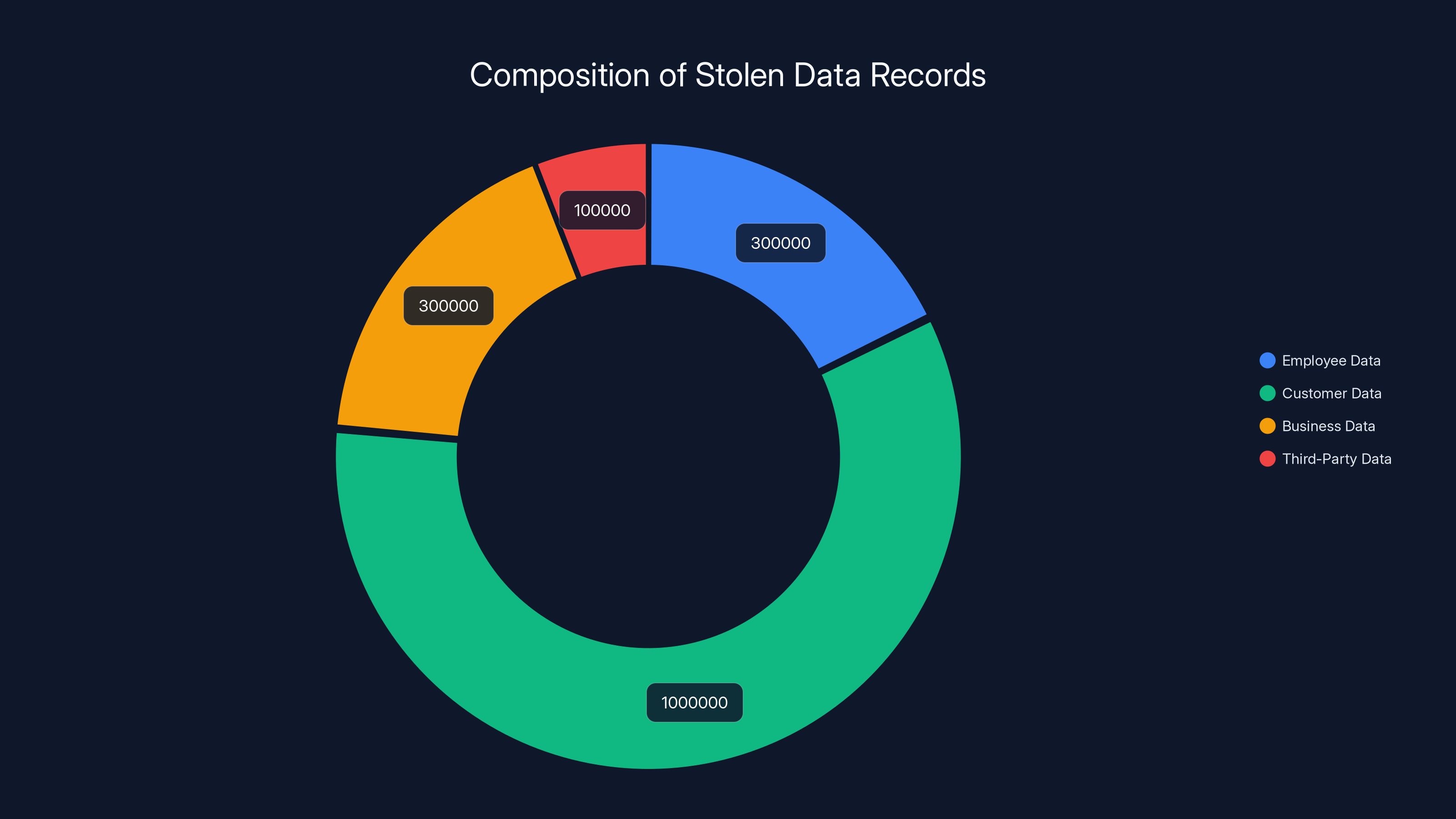
Estimated data shows customer data likely forms the largest portion of the 1.7 million stolen records, followed by employee and business data.
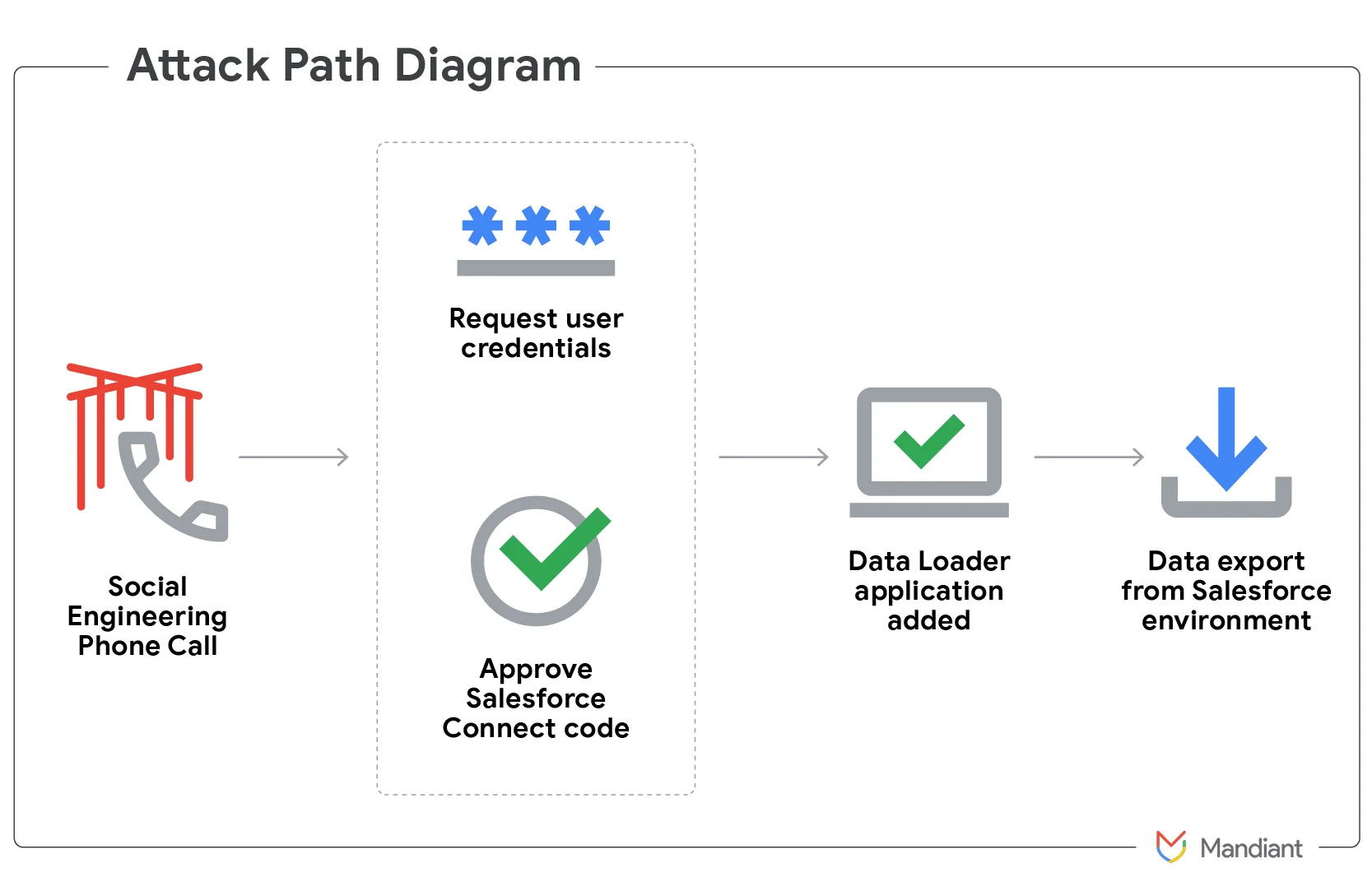
How Shiny Hunters Actually Pulled Off the Attack: The Vishing Playbook
Here's where the breach gets really interesting. Because the method Shiny Hunters used wasn't rocket science. It was something far more dangerous: it was repeatable, scalable, and devastatingly effective.
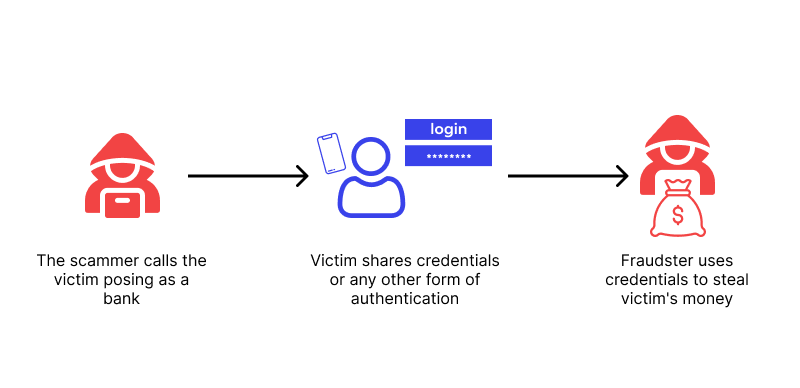
The attack starts with a phone call. A victim—typically someone in IT, HR, finance, or another access-critical role—receives a call from someone claiming to be IT support or a tech operative from their company. The caller has done their homework. They might know the victim's name, their department, recent company events, or details that make the call sound legitimate.
The message is simple: "We need to update your MFA settings. There's been a security incident and we need you to verify your credentials." Or something similar. The urgency is manufactured. The threat feels real.
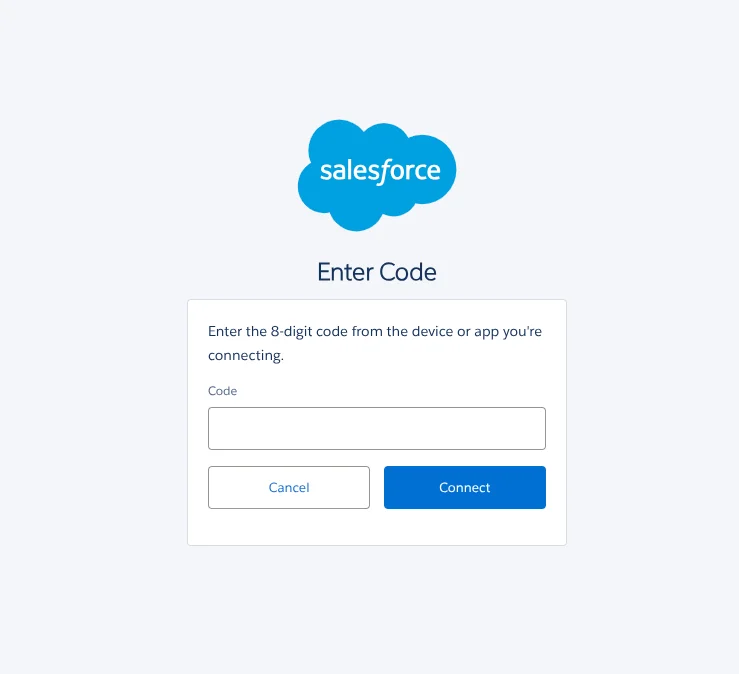
But here's the genius part: Shiny Hunters doesn't just use any phishing page. They've built customized, modular phishing infrastructure. Think of it like a phishing page factory. They have templates that can instantly transform based on what type of authentication system you use.
If you use Google Workspace SSO, you get a Google SSO phishing page that looks indistinguishable from the real thing. If your company uses Microsoft Entra (formerly Azure AD), you get an Entra-specific page. If you're on Okta, same thing. The pages don't just look similar—they're tailored down to the specific MFA method your company deployed.
So when an employee visits the fake login page and enters their credentials, the attacker captures them in real time. The employee might see an error message: "Your MFA provider is temporarily unavailable. Please try again in five minutes." The employee, thinking they'll retry, hangs up. They don't know their credentials were just stolen.
Meanwhile, Shiny Hunters now has legitimate credentials tied to a real employee account at an enterprise organization. Combined with knowledge of the company's network topology, they can begin lateral movement. They can explore file shares. They can access customer data. They can find where the crown jewels are stored.
Then comes the exfiltration. Shiny Hunters pulls whatever data is valuable. Databases get copied. Files get staged for download. Then the attack enters its final phase: the threat.
A sample of stolen data gets posted to the Shiny Hunters leak site. A message gets sent to the victim organization: "We have your data. Pay us, or we leak everything." It's extortion, pure and simple. And it's working.
The Shiny Hunters Track Record: A Pattern of Sophisticated Attacks
The Car Gurus breach isn't an isolated incident. It's part of a devastating pattern that shows Shiny Hunters has essentially weaponized vishing attacks to an industrial scale.
Before Car Gurus, the group successfully compromised companies including Mercer Advisors (a major wealth management firm), Beacon Pointe Advisors (another financial advisory giant), Canada Goose (the luxury outerwear company), Figure Technology Solutions (a fintech platform), Betterment (a robo-advisor with millions of customers), Match Group (owner of Tinder, Match, Ok Cupid, and other dating platforms), Panera Bread (the restaurant chain), Carvana (the online car dealer), and Edmunds (the automotive marketplace).
That's nine confirmed victims before Car Gurus. And these aren't random targets. They're strategic choices. These are organizations with:
- Large customer bases: More records stolen means more marketable data
- Valuable employee data: Financial firms, tech companies, and retailers have employees with high salaries and access
- Customer financial information: Car dealers, financial advisors, and restaurants have payment data
- Sensitive business data: Proprietary information, customer lists, and pricing data from enterprises
The progression shows escalating sophistication. Early attacks might have been opportunistic. But by the time we get to Match Group and Panera Bread, these are clearly well-researched, targeted operations. Shiny Hunters knows which employees to target, which systems they use, and how their authentication infrastructure is configured.
Google and Mandiant, the threat intelligence division of Google Cloud, have done detailed research into Shiny Hunters' operations. They discovered that the group isn't just effective—they're extremely organized. They have:
- Dedicated call infrastructure: Phone numbers that spoof legitimate corporate numbers
- Research capabilities: They're doing reconnaissance to identify targets and high-value employees
- Real-time adaptation: They can modify phishing pages on the fly based on what victim organizations use
- Professional operations: They're running this like a business, not like random hackers
The concerning part is that this attack vector—vishing combined with customized phishing—doesn't require zero-day exploits, sophisticated malware, or long-term access. A single compromised credential can be the entry point for an entire enterprise takeover. And the success rate is disturbingly high.
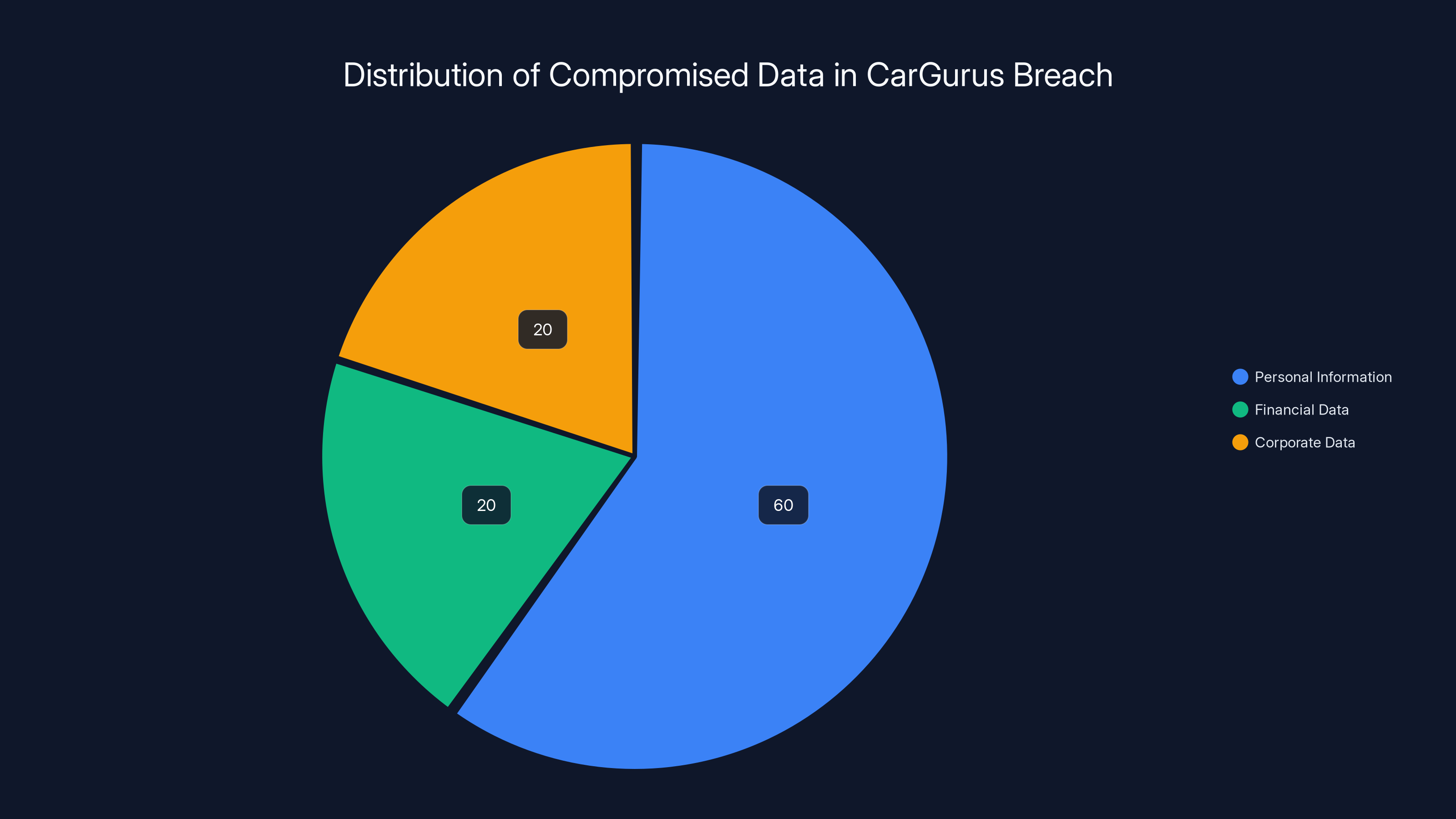
Estimated data shows that personal information makes up the majority of the compromised records, followed by financial and corporate data.
Why Vishing Attacks Are So Devastatingly Effective
Pause for a second and think about why this attack works. It's not because people are stupid. It's because the attack exploits fundamental human psychology.
When you receive a phone call, your brain treats it differently than an email. A phone call feels more legitimate. More urgent. More personal. If the caller has done their homework—if they know your name, your department, recent security incidents at your company—the call feels even more credible.
MFA is supposed to protect against compromised credentials. But vishing doesn't compromise credentials at login time. It compromises them during the social engineering phase. By the time the attacker uses the stolen credentials, MFA is effectively bypassed because the attacker has both the password AND the person's ability to respond to MFA challenges (since they're capturing the credential during the fake MFA update call).
It's security theater meeting social engineering. The security controls are working exactly as designed, but they're being circumvented before they ever have a chance to engage.
Here's another psychological angle: urgency and authority. The attacker frames the call as necessary. "There's been a security incident." "We need to update your MFA immediately." "You'll lose access if we don't do this now." These statements activate a person's threat response. They bypass critical thinking.
Authority plays a role too. If the caller sounds professional, knows details about your company, and speaks with confidence, most people assume they're talking to someone legitimate. Humans are hardwired to trust authority figures, especially in moments of uncertainty.
The third factor is familiarity with the technology. Many employees don't fully understand how their company's authentication systems work. They don't know what a legitimate MFA update process looks like versus a fake one. So when someone calls and says "we need to update your MFA," the employee thinks, "Okay, that sounds like a technical thing IT does. I'll go along with it."
This creates a perfect storm of vulnerabilities. The attack leverages psychological principles that humans evolved to respond to. You can train people, you can implement policies, but you can never completely eliminate the human element.

The Technical Infrastructure Behind Shiny Hunters' Success
What separates Shiny Hunters from amateur phishers is their technical sophistication. They've built infrastructure that rivals legitimate security operations centers.
Customized phishing pages are the foundation. But we're not talking about simple copies of login pages. We're talking about pages that:
- Redirect dynamically: The page detects which SSO provider you're using and automatically adjusts
- Clone MFA flows: If your company uses specific MFA methods, the fake page recreates those flows exactly
- Capture in real-time: Stolen credentials are immediately transmitted to attacker infrastructure, allowing for fast follow-up
- Handle edge cases: What if an employee has hardware security keys? The page can adapt
This infrastructure requires knowledge of how Google Workspace, Microsoft Entra, and Okta SSO systems actually work. Not just surface-level knowledge, but deep technical understanding.
Shiny Hunters also maintains calling infrastructure. That means:
- Spoofed phone numbers: They can make their calls appear to come from internal corporate numbers
- Professional call handling: They're training the people making calls to sound credible
- Research on targets: They're identifying which employees to call and what details to drop
- Timing coordination: They're calling when targets are most likely to be at their desks and in a responsive state of mind
The data exfiltration side is equally sophisticated. Once they have credentials, they need to:
- Navigate enterprise networks: Understanding Windows domains, file structures, database locations
- Identify valuable data: They know what to look for and where to find it
- Exfiltrate at scale: Moving terabytes of data without triggering security alerts
- Anonymize the theft: Using legitimate tools and methods to avoid detection
Then there's the marketplace side. Shiny Hunters doesn't just collect data and sit on it. They:
- Sample and advertise: Post portions of stolen data to prove legitimacy
- Negotiate with victims: Conduct extortion campaigns with backup threats
- Sell to other buyers: Monetize data through dark web marketplaces
- Maintain reputation: Ensure victims and buyers trust they'll follow through on threats and sales
This is an actual criminal enterprise with division of labor, specialization, and operational discipline.

Vishing attacks have a significantly higher success rate (50-70%) compared to email phishing (3-5%), making them more effective for attackers. Estimated data.
Why Traditional Security Controls Failed
You'd think companies like Canada Goose, Panera Bread, and Car Gurus would have robust security controls in place. And they probably do. So why did they fall to vishing attacks?
The first issue is that traditional security controls are designed to stop intrusions at the perimeter or during credential use. They're not designed to stop social engineering before credentials are entered.
Network segmentation, intrusion detection systems, endpoint protection, threat intelligence platforms—these all work great against attacks that happen in the network. But vishing happens before the network. It happens on a phone call, in the victim's home office or at their desk, with no digital component until after the credential is already compromised.
Multi-factor authentication should theoretically help, but only if the MFA enrollment and recovery processes are bulletproof. Here's where it gets tricky: attackers can sometimes:
- Intercept MFA codes: If they have access to email or phone, they can receive MFA codes
- Use MFA evasion techniques: Social engineering the MFA process itself
- Manipulate trusted device lists: If they access the account during a trusted device window
Second, most organizations have security training. Annual or quarterly training about phishing, social engineering, and best practices. But here's the problem: training is inconsistent. Some employees pay attention. Some click through and forget immediately. Some never receive the training. And even well-trained employees can be fooled by a sophisticated, personalized attack.
Third, organizations often have gaps between what security policies say and what actually happens. Maybe the policy says "MFA updates will never be requested by phone." But if employees have never heard this clearly communicated, if IT has ever actually made unexpected calls for legitimate reasons, if there's ambiguity in the culture, then that policy doesn't provide much protection.
Fourth, insider threat detection systems are designed to catch employees doing bad things. They're not designed to catch employees being victims of social engineering. So even if a compromised employee starts accessing files they've never accessed before, the activity might not trigger alarms because the actual employee account is the one doing the accessing.
Fifth, there's an assumption that single compromised credentials aren't dangerous because of MFA and segmentation. That assumption is correct for random compromised credentials. But when the attacker also has the password and has conducted reconnaissance to understand the network topology, a single account can be a devastating entry point.

The Psychology of the Attack: Why People Fall For It
I keep coming back to this because it's critical to understanding why vishing is so effective. The technical controls are almost irrelevant compared to the psychological controls.
Human beings are inherently trusting. We evolved in small groups where most people we met were trustworthy. We're primed to believe authority figures, to respond to urgency, and to help when someone presents a problem. These are mostly positive traits that allow societies to function. But in a digital context where attackers can impersonate anyone, these traits become vulnerabilities.
When someone calls and says, "Hi, this is Marcus from IT security. We've detected some unusual activity on your account and need to update your MFA right now," your brain goes through a rapid decision process. But that process isn't fully rational. It's running on heuristics:
- Authority heuristic: The caller sounds professional and knows details about me and my company
- Consensus heuristic: Lots of companies do have security incidents; this sounds plausible
- Urgency heuristic: If there's unusual activity, delaying would be risky
- Liking heuristic: The caller is friendly and helpful
- Reciprocity heuristic: They're helping me avoid a security problem, so I should help them
These heuristics are evolutionary features, not bugs. But they can be exploited. And Shiny Hunters is an expert at creating the social context that activates these heuristics.
There's also research showing that people are MORE likely to fall for social engineering if they've recently received legitimate security communications from their IT department. Paradoxically, good security communication and training can make people more vulnerable to sophisticated social engineering because they lower their defenses to messages that seem to be from internal security teams.
This isn't a character flaw in employees who fall for these attacks. It's a structural problem in how humans process information under pressure.
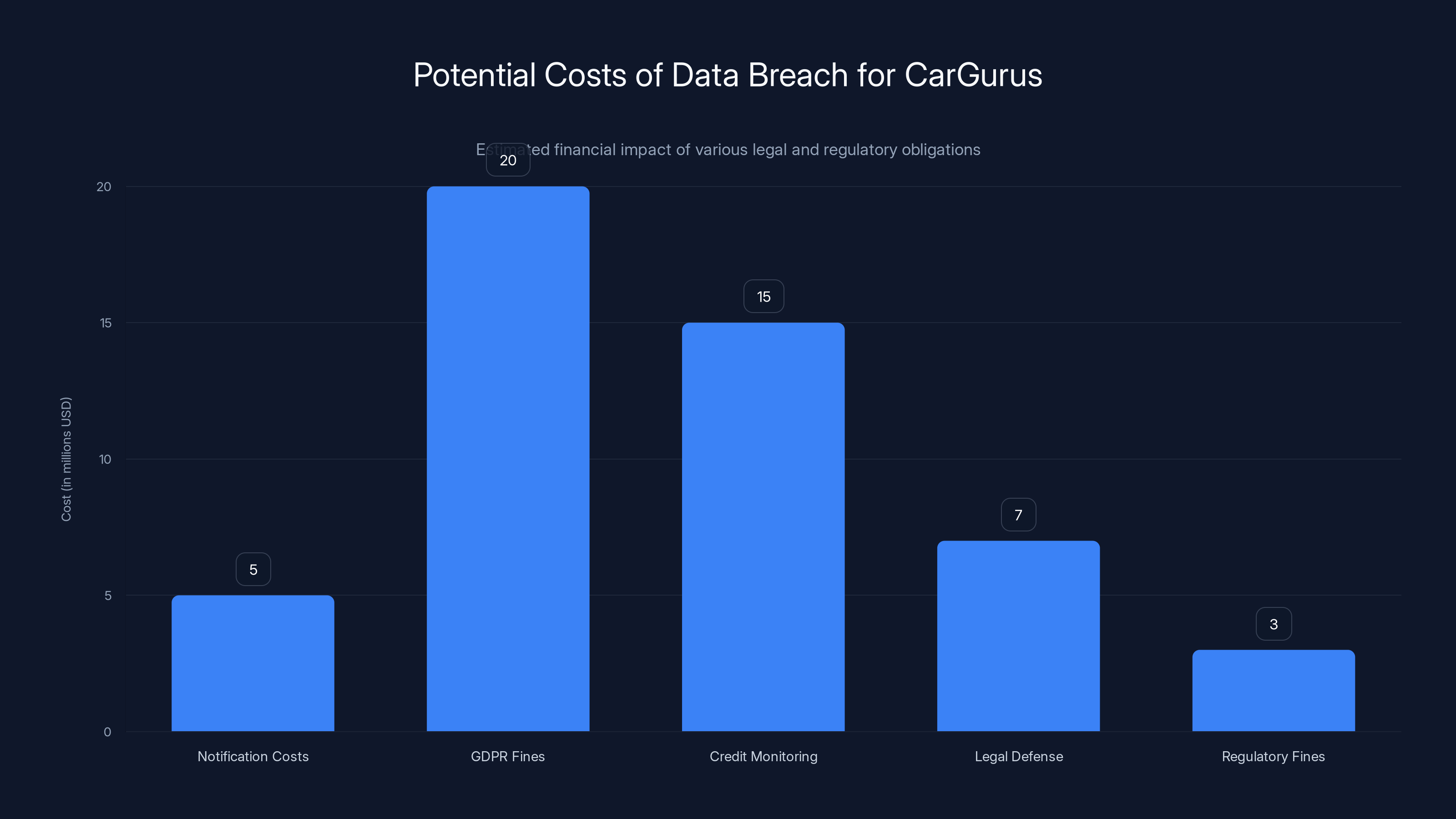
Estimated data suggests that the total cost of a data breach for CarGurus could exceed $50 million, with GDPR fines and credit monitoring being the largest expenses.
The Data That Was Actually Stolen: What Does 1.7 Million Records Mean?
Shiny Hunters claims they stole 1.7 million records. But what does that actually include? Without Car Gurus's public disclosure, we can only speculate.
The announcement mentions "personally identifiable information" and "other internal corporate data." That's vague enough to cover a lot of ground. Here's what likely got stolen:
Employee Data: Names, email addresses, phone numbers, potentially employment histories, departments, and role information for all Car Gurus employees and contractors. For a company Car Gurus's size, that could be tens of thousands of records.
Customer Data: Car Gurus is a marketplace for cars. Customer records likely include names, email addresses, phone numbers, and potentially home addresses. Browsing histories. Cars viewed or reviewed. If customers created accounts with payment information, that's compromised too.
Business Data: Internal communications about pricing, strategy, new initiatives. Partnerships and vendor information. Financial data. Proprietary algorithms or business processes.
Third-Party Data: If Car Gurus maintains records of dealers, lenders, or other partners, that data is also at risk.
To put this in perspective, 1.7 million records is approximately:
- 0.5% of the total US population
- 10–20% of major US companies have breaches of this scale
- Tens of thousands of dollars per record sold on dark web markets
A typical record (name + email + phone number) sells for
But that's not usually the primary extortion angle. The primary angle is the extortion letter: "Pay us $X or we publish all of this."
Car Gurus's Response (Or Lack Thereof): What the Silence Means
As of reporting, Car Gurus has not made any public statement about the breach. The company's website doesn't mention it. No press release. No notification to customers. No acknowledgment to employees.
There are several possible explanations:
Investigation Phase: The company might be investigating whether the breach actually occurred. Shiny Hunters sometimes makes false claims, and companies verify before responding publicly. However, with a breach this significant, some public acknowledgment would typically come quickly.
Negotiation Phase: The company might be in active negotiation with Shiny Hunters. Paying a ransom is frequently done quietly, and companies have an incentive to keep negotiations confidential. If you publicly acknowledge an extortion threat, you might encourage copycat attacks from other groups.
Legal Advice: The company's lawyers might have advised them to remain silent until the situation is fully understood. Saying something wrong publicly can increase liability.
Minimization Strategy: The company might be hoping the news cycle moves on before they have to make a statement. This is a risky strategy but it's been attempted before.
Verification Delays: It might actually take time to verify a breach of this scope. Examining 1.7 million records, confirming they're authentic, understanding the scope of compromise—these aren't instant processes.
Regardless of the reason, the silence has consequences. Customers and employees don't know if they're affected. People can't take protective measures. Trust erodes. And in the court of public opinion, silence often suggests guilt or incompetence.
From a crisis communication perspective, this is suboptimal. Companies that respond quickly and transparently to breaches recover better than those that stay silent.

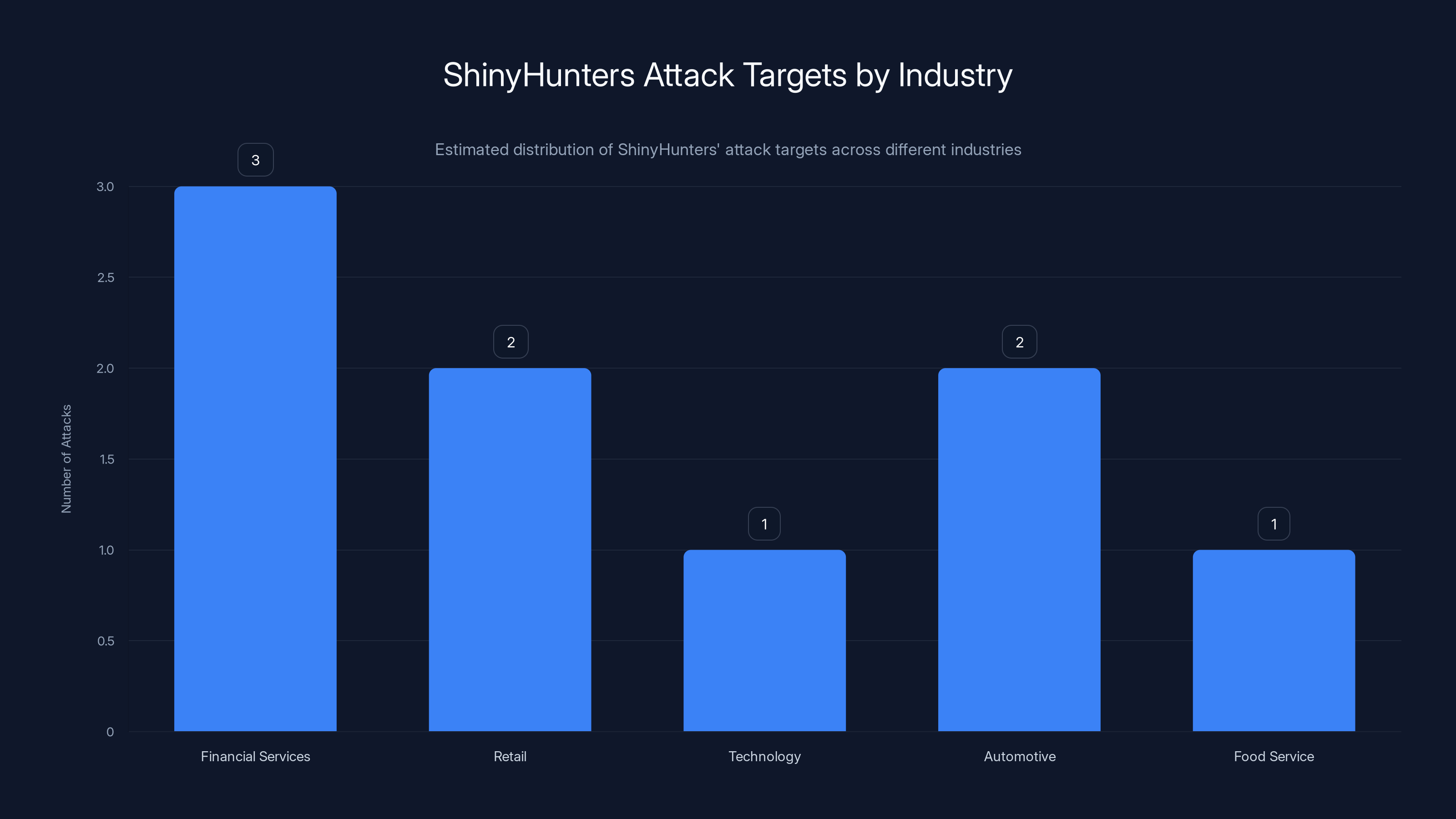
Estimated data shows that ShinyHunters primarily targets financial services, followed by retail and automotive industries. This indicates a strategic focus on sectors with valuable data.
Legal and Regulatory Implications: What Car Gurus Faces
If the breach is confirmed, Car Gurus faces significant legal and regulatory consequences. Here's what's likely coming:
Breach Notification Laws: Every US state has laws requiring companies to notify affected individuals within a specific timeframe (usually 30–60 days). Car Gurus will be required to send notifications to everyone whose data was compromised. That means legal fees, notification costs, and exposure to class action lawsuits.
GDPR Implications: If any EU residents' data was stolen, Car Gurus must comply with GDPR breach notification rules, which are stricter than US laws. Notification must occur within 72 hours of discovering the breach. The company could face fines up to 4% of global annual revenue.
Credit Monitoring Obligations: Companies typically have to pay for credit monitoring services for affected individuals for 1–2 years. For 1.7 million people, that's millions of dollars in direct costs.
SEC Disclosure: If Car Gurus is a publicly traded company or plans to go public, they likely have obligations to disclose the breach to shareholders. Securities law requires disclosure of material information that could affect company value.
Class Action Lawsuits: You can virtually guarantee class action lawsuits will be filed. Even if the company prevails, legal defense costs are substantial.
Regulatory Investigations: State attorneys general, the FTC, and potentially Congress might investigate. The company could face consent decrees requiring them to implement specific security measures and undergo regular audits.
Insurance Claims: If Car Gurus has cybersecurity insurance, they'll file claims. But insurance typically has high deductibles and doesn't cover everything. And insurers are increasingly pushing back on coverage for breaches caused by inadequate security practices.
The total cost of a breach this size typically exceeds $50 million when you add up notification costs, credit monitoring, legal fees, regulatory fines, and business impact.
How Organizations Can Actually Defend Against Vishing Attacks
Here's what's genuinely effective against vishing attacks. Not theoretical measures, but practical ones:
1. Security Training That Actually Works
Standard annual security training is ineffective. Most people forget it immediately. What works is:
- Simulated vishing attacks: Have a company hire an organization to conduct simulated vishing attacks against your employees. See who falls for it. Then provide targeted training to vulnerable employees.
- Ongoing reinforcement: Brief monthly security messages, not annual hour-long trainings. Repetition works.
- Real-world examples: Use actual attack examples from your industry, not generic phishing scenarios.
- Clear escalation procedures: Employees should know exactly what to do if they receive a suspicious call. And this procedure should not involve hanging up and trying to call the company back using a number the attacker provided.
2. Hardened Credential Protection Processes
Make it difficult for attackers to collect credentials in the first place:
- Declare clearly: IT will never ask for your password or MFA codes over the phone. Ever. This should be repeated regularly.
- Verify identity: When someone claims to be from IT, employees should verify by calling a known IT phone number directly, not using a number the caller provides.
- Separate verification from action: Don't have IT call asking to update credentials. Instead, have IT email employees with instructions to log into a secure portal to make changes themselves.
- Hardware security keys: For critical employees, implement hardware security keys instead of SMS or app-based MFA. These can't be phished.
3. Behavioral Analytics and Insider Threat Detection
This is where companies can detect compromised credentials quickly:
- Unusual access patterns: If someone's account is accessing files they've never accessed before, at times they usually don't work, from unusual locations, that should trigger alerts.
- Impossible travel detection: If an account logs in from two impossible-to-travel-between locations within a short timeframe, that's suspicious.
- New device authentication: If an account is authenticating from a new device for the first time, verify with the actual user.
- Unusual data exfiltration: Monitor for large-scale downloads of sensitive data, especially to cloud storage or external services.
4. Network Segmentation
Even with compromised credentials, minimize the damage:
- Limit user access: Employees should only have access to the systems they need for their jobs. Don't give everyone access to everything.
- Segment sensitive data: Customer databases, financial records, and intellectual property should be in separate network segments with additional access controls.
- Privileged access management: Admin accounts should be separate from regular employee accounts. Use temporary elevation for admin tasks.
- Monitor lateral movement: Any employee account trying to access systems outside their normal scope should require additional verification.
5. Incident Response Capabilities
When (not if) attacks happen, you need to respond fast:
- Credential reset procedures: Be able to reset all potentially compromised credentials within minutes, not hours.
- Forensic capabilities: Have the ability to determine what data was accessed and exfiltrated.
- Communication plans: Know who to contact, in what order, and what to communicate.
- Legal preparation: Have lawyers ready for breach notifications, regulatory inquiries, and potential lawsuits.
6. Threat Intelligence and External Monitoring
Know what's happening in the threat landscape:
- Dark web monitoring: Subscribe to services that monitor dark web marketplaces and leak sites for mentions of your company.
- Threat intelligence feeds: Subscribe to threat intelligence that alerts you when your company or industry is being targeted.
- Incident response retainers: Have a contract with an incident response firm that can be activated immediately if you're compromised.

The Economics of Extortion: Why Shiny Hunters Keeps Winning
Let's talk about the uncomfortable truth: Shiny Hunters is profitable. They're operating at scale. And they're unlikely to stop until something changes economically.
Here's the basic math:
Attack costs: A vishing campaign might cost a few thousand dollars. Hiring people to make calls, setting up infrastructure, purchasing spoofed phone numbers. But once the infrastructure is built, the marginal cost of the next attack is almost zero.
Compromise rate: Based on reported attacks, Shiny Hunters's success rate seems to be around 50–60% across different organizations. Some companies fall to the attack, some don't.
Exfiltration value: Even if they only successfully compromise 30% of targets and only manage to steal partial data from 30% of those successes, they're still getting significant data from most attacks.
Monetization: They make money three ways:
-
Direct extortion: "Pay us or we leak the data." If even 5% of targeted companies pay a modest ransom of
500,000 from a batch of 100 targets. -
Dark web sales: Stolen data gets sold to other criminals, identity thieves, competitors, or people looking for specific information. A database of 1.7 million customer records might fetch tens of thousands of dollars.
-
Insurance claims: Some companies pay rather than deal with notification costs, and they claim it on insurance. This indirectly subsidizes the attackers.
The ROI on vishing attacks is probably 100:1 or better. Spend
What would make Shiny Hunters stop? Several things could theoretically help:
- Effective law enforcement: Actual arrests and prosecutions. But Shiny Hunters likely operates from jurisdictions where extradition is unlikely.
- Payment disruption: Making it harder for victims to pay ransoms. Some countries have started restricting ransom payments, but it's not widely enforced.
- Sanctions: Financial sanctions against countries harboring cybercriminals. This might reduce infrastructure access.
- Market reduction: If companies stop paying, the economics collapse. But that requires industry-wide coordination.
- Attribution and retaliation: If targets can identify and retaliate against attackers. But retaliation creates escalation risks.
For now, Shiny Hunters operates in a relatively low-risk, high-reward environment. That's unlikely to change in the short term.
What This Means for Your Organization: Practical Next Steps
If you work in cybersecurity or lead an organization, here's what the Car Gurus breach means for you:
Immediate Actions (This Week)
-
Assess your vishing vulnerability: How susceptible is your organization to vishing attacks? Run a simulated vishing campaign. See how many employees fall for it.
-
Review your MFA processes: Are there any processes where employees legitimately enter credentials after an unexpected call? Eliminate those processes.
-
Check for active compromises: Look at your authentication logs for suspicious activity. Are there accounts being used from unusual locations? At unusual times? Accessing unusual resources?
-
Brief your security team: Make sure your security team understands Shiny Hunters's methods and is watching for indicators of compromise.
Short-Term Actions (Next Month)
-
Strengthen credential protection: Implement hardware security keys for high-risk users. Implement proper MFA recovery processes that don't rely on phone calls.
-
Improve behavioral analytics: Make sure you have the tools to detect unusual account activity. If you don't, acquire them.
-
Communication to employees: Send a clear message about vishing. Explain the Shiny Hunters attack. Tell employees exactly what to do if they receive a suspicious call.
-
Incident response plan: Ensure you have a current incident response plan. Test it. Make sure everyone knows their role.
Long-Term Actions (Next Quarter)
-
Security training programs: Implement ongoing simulated vishing attacks and training. Make it a regular part of your security culture.
-
Network segmentation: Review your network architecture. Implement or improve network segmentation so a single compromised credential doesn't grant access to everything.
-
Insider threat program: Implement user and entity behavioral analytics to catch compromised accounts quickly.
-
Regulatory compliance: Review your obligations under GDPR, state breach notification laws, and industry-specific regulations. Make sure you're compliant.
-
Insurance review: Ensure your cyber insurance adequately covers extortion, breach notification, and regulatory fines. Consider increasing limits.
The Broader Trend: Why Vishing Attacks Are the New Normal
The Car Gurus breach isn't an anomaly. It's part of a larger trend where attackers have moved away from technical exploits and toward social engineering.
Here's why:
Lower risk: You can't get arrested for making phone calls and running a phishing page. But you can get arrested for deploying a zero-day or writing malware.
Higher success rate: Vishing beats technical exploits in terms of success rate. Humans are the weakest link.
Easier scaling: Once you've developed the social engineering playbook, you can run it against dozens of organizations simultaneously with minimal incremental cost.
Less dependent on technical expertise: You don't need to be a world-class security researcher to run vishing attacks. You need to be good at social engineering and willing to break the law.
Regulatory complexity: Companies struggle with security because it's complex. But defending against vishing is about training and process, not just technology. Many organizations haven't adapted.
What's particularly concerning is that vishing attacks are becoming more targeted. Shiny Hunters isn't just making random calls. They're researching organizations, identifying high-value targets, and crafting personalized attacks.
This trend will likely continue and intensify. We'll probably see more industries targeted. More sophisticated social engineering techniques. More organization failures.
The organizations that survive this wave are the ones that treat security as primarily a human and process challenge, with technology playing a supporting role.

Building a Vishing-Resistant Security Culture
Technology alone can't stop vishing attacks. You need a security culture that emphasizes skepticism, verification, and clear processes.
What does that look like?
Healthy Paranoia: Employees should be trained to question unexpected calls, especially those asking for credentials or sensitive information. This should be normalized, not seen as rude or paranoid.
Clear Procedures: When IT needs to contact employees about security, use established channels. Send an email first. Have employees log into a secure portal. Don't request credentials or MFA codes over the phone.
Verification Protocols: If someone claims to be from IT, employees should verify by calling a known IT number directly. This is standard procedure, not something that needs explanation.
Safety in Reporting: Employees should feel safe reporting suspected vishing attempts. If someone reports a suspicious call and gets punished or mocked, that kills the reporting culture.
Executive Commitment: Security culture flows from the top. If executives take security seriously, employees will too. If executives dismiss it, employees will ignore it.
Regular Reinforcement: Security messaging should be regular and brief, not annual and tedious. Monthly reminders work better than annual trainings.
Real Consequences for Attackers: This is outside any single organization's control, but the broader ecosystem needs to make cybercriminals face actual consequences. Until then, organizations can only control their own defenses.
The Path Forward: What Actually Gets Better
Here's my honest assessment of where we're headed.
Shiny Hunters will likely continue operating until they're arrested or decide the risk isn't worth the reward. Law enforcement has been largely ineffective at stopping international cybercriminal groups, especially those operating from countries with poor extradition treaties.
More companies will be compromised. More data will be stolen. More ransoms will be paid (sometimes quietly). The trend will likely accelerate for the next 1-3 years.
Organizations that want to protect themselves have a clear path:
- Accept that vishing attacks are inevitable
- Implement the defenses outlined above
- Assume compromises will happen despite your defenses
- Build detection and response capabilities
- Create a security culture that supports all of this
The organizations that do these things will likely avoid being compromised or will detect compromises quickly and minimize damage. The organizations that don't will keep showing up in breach headlines.
Car Gurus is probably the first company in its sector to be hit by Shiny Hunters this way. But it won't be the last. Other online marketplaces, financial companies, and retailers should be taking defensive action right now.
Because vishing attacks don't require zero-days or sophisticated malware. They just require a phone call, some social engineering, and knowledge of how enterprise authentication works. Those things are readily available to anyone willing to break the law and take the risk.
FAQ
What is vishing and how is it different from other phishing attacks?
Vishing (voice phishing) is a social engineering attack that happens over the phone rather than through email or text. Unlike traditional phishing, vishing doesn't rely on clicking a malicious link or opening an attachment. Instead, attackers use psychological manipulation to trick victims into revealing credentials or sensitive information directly during a phone conversation. The advantage for attackers is that voice calls feel more personal and legitimate, making them significantly more effective than email phishing, with success rates of 50-70% compared to 3-5% for email phishing.
How does Shiny Hunters gain access to corporate systems if they steal credentials?
Once Shiny Hunters captures credentials through vishing, they gain initial access to the organization's network or cloud systems. From there, they conduct reconnaissance to understand the company's infrastructure, locate valuable data, and identify which systems contain what information. They can move laterally through the network using legitimate access, explore file servers and databases, and eventually locate and exfiltrate the most valuable data. The stolen credentials also enable them to access email systems, which provides additional reconnaissance opportunities and helps them understand company communications.
Why is MFA not sufficient protection against vishing attacks?
MFA is designed to protect accounts at the point of authentication, but vishing attacks circumvent this protection by capturing credentials before authentication even occurs. Shiny Hunters uses customized phishing pages that mimic legitimate MFA update processes, tricking employees into entering both their password and MFA recovery codes voluntarily. Additionally, if attackers gain access to email accounts, they can receive MFA codes sent to that email. The fundamental issue is that MFA assumes the credential is safe—vishing exposes that assumption as false.
What should I do if I receive a suspicious call claiming to be from my company's IT department?
Never provide passwords, MFA codes, or sensitive information over the phone, even if the caller sounds legitimate and claims to be from IT. Instead, hang up and call your IT department directly using a phone number from your company directory or your company's official website. Do not use any phone number the caller provides. If the call was legitimate, IT will have a record of it or can explain the situation when you call them back. Legitimate IT staff will never ask you to provide credentials over the phone.
How can organizations detect if they've been compromised by Shiny Hunters or similar vishing attacks?
Organizations can detect compromises by monitoring for behavioral anomalies in account access patterns, such as accounts accessing files they've never accessed before, logging in from unusual geographic locations, accessing systems at unusual times, or downloading unusually large amounts of data. Impossible travel detection (account logins from geographically distant locations within impossible travel timeframes) is a strong indicator. Additionally, monitoring dark web leak sites and threat intelligence feeds for mentions of your organization can provide early warning that your data may have been stolen.
What is the typical timeline for identifying a vishing-based breach?
The average time to detect a breach is approximately 207 days, but vishing breaches might be detected faster if the organization has good behavioral analytics in place. However, because vishing attacks don't involve malware or network anomalies, they can go undetected for extended periods. Many vishing breaches are only discovered when the stolen data appears on dark web leak sites, when the victim receives an extortion demand, or when compromised customers report fraud. Organizations with robust insider threat detection systems and behavioral analytics can reduce this timeline significantly.
What are the financial costs associated with a breach like the Car Gurus incident?
The total cost of a breach involving 1.7 million records would likely exceed $50 million when accounting for all factors. This includes breach notification costs (notifying millions of customers and providing credit monitoring services), legal fees for handling lawsuits and regulatory inquiries, regulatory fines (which can be substantial under GDPR and state laws), business disruption costs, and damage to reputation and customer trust. Additionally, some companies pay ransom demands to prevent data publication or face extortion costs for negotiating with attackers.
Can an organization defend against vishing attacks completely?
No organization can completely eliminate the risk of vishing attacks because they fundamentally exploit human psychology and social engineering. However, organizations can significantly reduce their vulnerability through a combination of technical controls (hardware security keys, behavioral analytics, network segmentation), process improvements (clear MFA update procedures that don't involve phone calls), and human factors (ongoing security training, simulated vishing attacks, clear escalation procedures). The goal isn't to eliminate risk entirely, but to reduce the probability of compromise and the damage if compromise occurs.
Why is the automotive industry a target for attackers like Shiny Hunters?
The automotive industry, including platforms like Car Gurus and Carvana, is attractive to attackers because these organizations maintain valuable customer data including personally identifiable information, phone numbers, email addresses, home addresses, and financial information. Additionally, automotive retail involves significant financial transactions, making customer financial data valuable to criminals. The industry also employs a large workforce with varying security awareness, creating more attack surface for vishing attempts.
What should companies do if they're the victim of a vishing-based breach?
Companies should immediately activate their incident response plan, engage breach notification counsel, initiate forensic investigations to determine the scope of the compromise, notify affected parties in compliance with applicable laws, contact law enforcement and cyber insurance providers, implement remedial security measures, and prepare for potential extortion demands. Transparency with customers and stakeholders is generally more effective than silence, as it helps manage reputation damage and allows affected parties to take protective action.
The Car Gurus breach represents a maturation of attacker capabilities and a sobering reality for the enterprise security community. Vishing attacks have moved from opportunistic tactics to sophisticated, repeatable, highly effective attack operations. And until organizations fundamentally change how they approach credential protection and security culture, breaches like this will continue to happen.
The good news? The defenses exist. Organizations that implement them will dramatically improve their resilience. The question is whether enough organizations will act before they become victims.
Key Takeaways
- CarGurus suffered a breach exposing 1.7 million records through vishing attacks, marking the 15th company compromised by ShinyHunters using identical techniques
- Vishing attacks have 10-20x higher success rates than email phishing by exploiting human psychology rather than technical vulnerabilities
- ShinyHunters uses customized phishing infrastructure that adapts to different SSO providers in real-time, making them nearly impossible to distinguish from legitimate authentication flows
- MFA does not protect against vishing attacks because credentials are compromised before authentication occurs, during the social engineering phase
- Organizations can defend against vishing through behavioral analytics, simulated vishing campaigns, hardware security keys, and security culture changes
- A single compromised credential obtained through vishing can enable complete enterprise network access through lateral movement and reconnaissance
- The average cost of a breach this size exceeds $50 million including notification, credit monitoring, legal fees, and regulatory fines
Related Articles
- Figure Data Breach: What Happened to 967,000 Customers [2025]
- Billions of Exposed Social Security Numbers: The Identity Theft Crisis [2025]
- Abu Dhabi Finance Summit Data Breach: 700+ Passports Exposed [2025]
- EU Parliament's AI Ban: Why Europe Is Restricting AI on Government Devices [2025]
- Honeywell CCTV Camera Vulnerability: Complete Security Guide [2025]
- Texas Sues TP-Link Over China Links and Security Vulnerabilities [2025]
![CarGurus Data Breach: 1.7M Records Stolen by ShinyHunters [2025]](https://tryrunable.com/blog/cargurus-data-breach-1-7m-records-stolen-by-shinyhunters-202/image-1-1771547854494.jpg)




