Beyond Trust RCE Vulnerability CVE-2026-1731: Complete Security Guide
Last month, a critical remote code execution flaw dropped like a bomb into enterprise security teams' inboxes. Beyond Trust, the identity and access management giant trusted by over 20,000 customers across 100+ countries, disclosed a vulnerability that lets attackers run OS commands without even logging in.
We're talking about a 9.9 out of 10 severity score. That's the kind of thing that makes security teams cancel their Friday afternoon plans and start running emergency patching sessions.
The flaw affects Remote Support (RS) versions 25.3.1 and earlier, plus older versions of Privileged Remote Access (PRA). According to researchers from Hacktron AI, roughly 11,000 instances are exposed to the internet. About 8,500 of those are on-premises deployments, which means they won't patch themselves automatically. If the administrators don't act, they're sitting ducks.
Here's the brutal part: this isn't some obscure feature nobody uses. Beyond Trust's Remote Support and Privileged Remote Access products are core tools for IT teams managing critical infrastructure. Banks use them. Healthcare systems rely on them. Tech companies deploy them across their entire infrastructure. A vulnerability here isn't just bad, it's a potential company-ending disaster if exploited.
In this guide, we're breaking down exactly what happened, why it matters, who's at risk, and what you need to do right now if you're running either product.
TL; DR
- CVE-2026-1731 is a critical OS command injection flaw in Beyond Trust Remote Support and PRA
- CVSS score: 9.9/10 (critical severity, unauthenticated, low attack complexity)
- No login required to exploit the vulnerability from the network
- Patch released February 2, 2026 for cloud customers, manual updates needed for self-hosted instances
- ~11,000 exposed instances, mostly on-premises deployments
- No known active exploitation in the wild (yet)
- Immediate action required if you're running Remote Support 25.3.1 or earlier, or PRA 24.3.4 or earlier

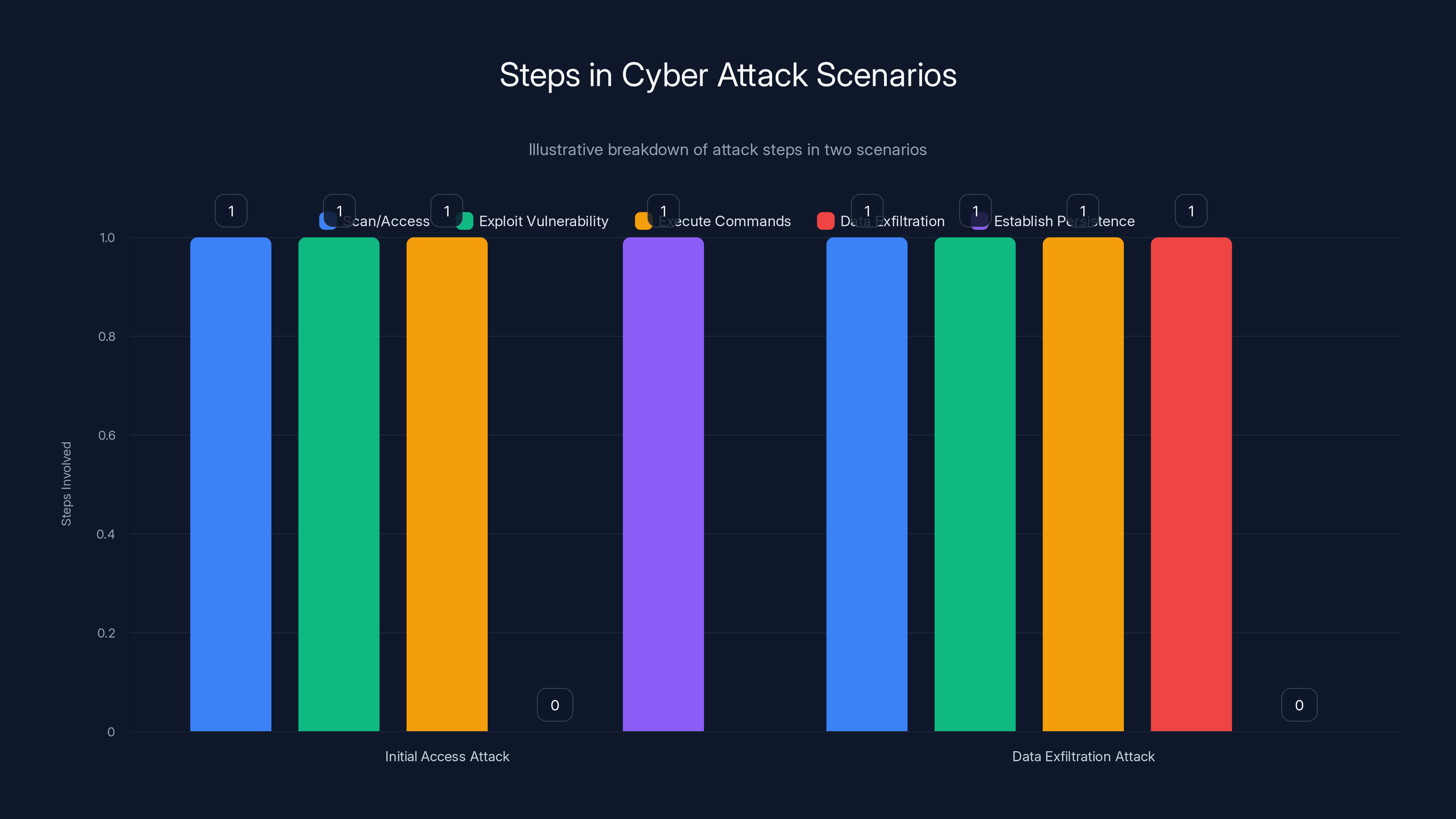
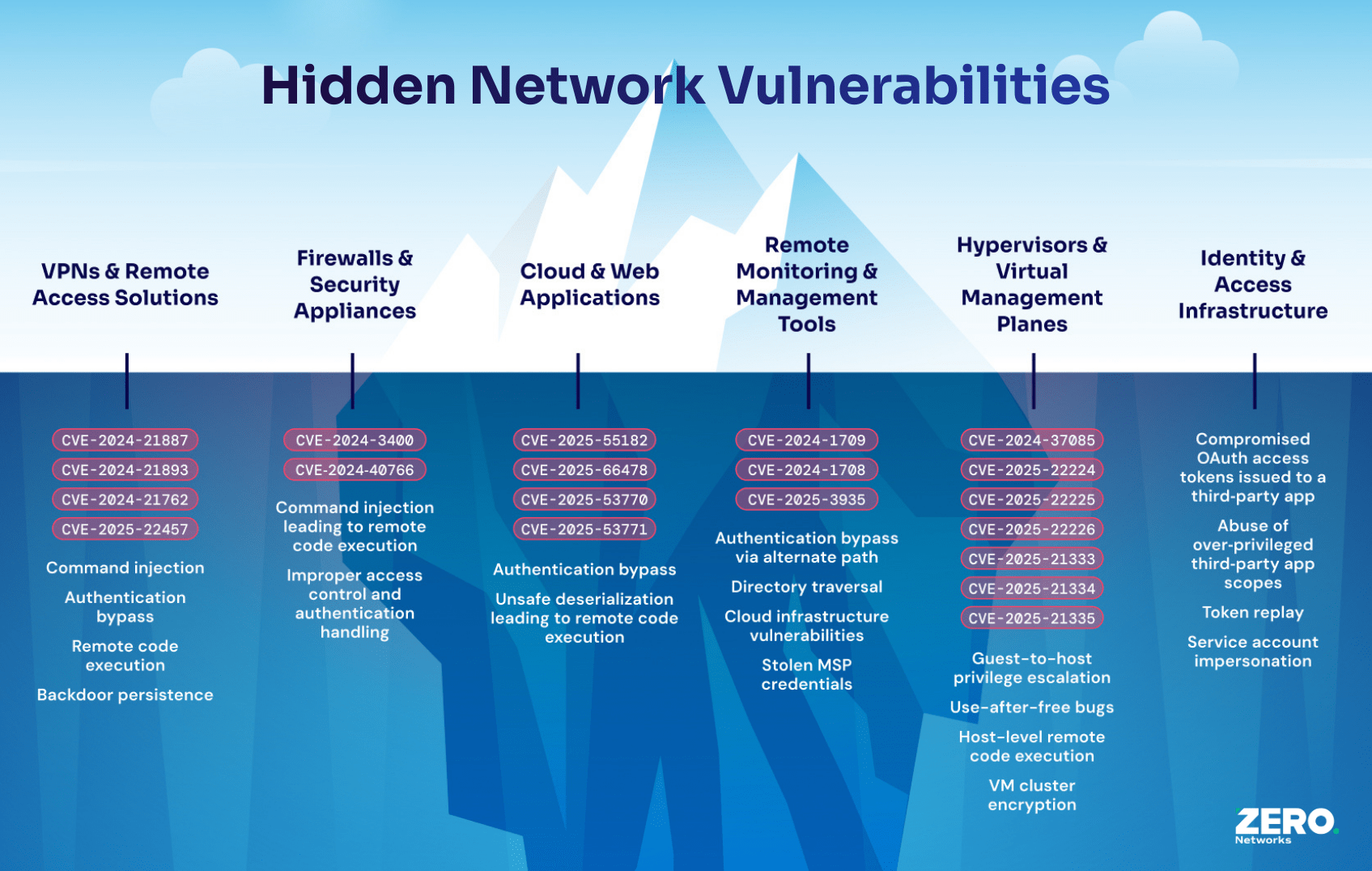
Both attack scenarios involve scanning and exploiting vulnerabilities, but differ in their final objectives: persistence vs. data exfiltration.
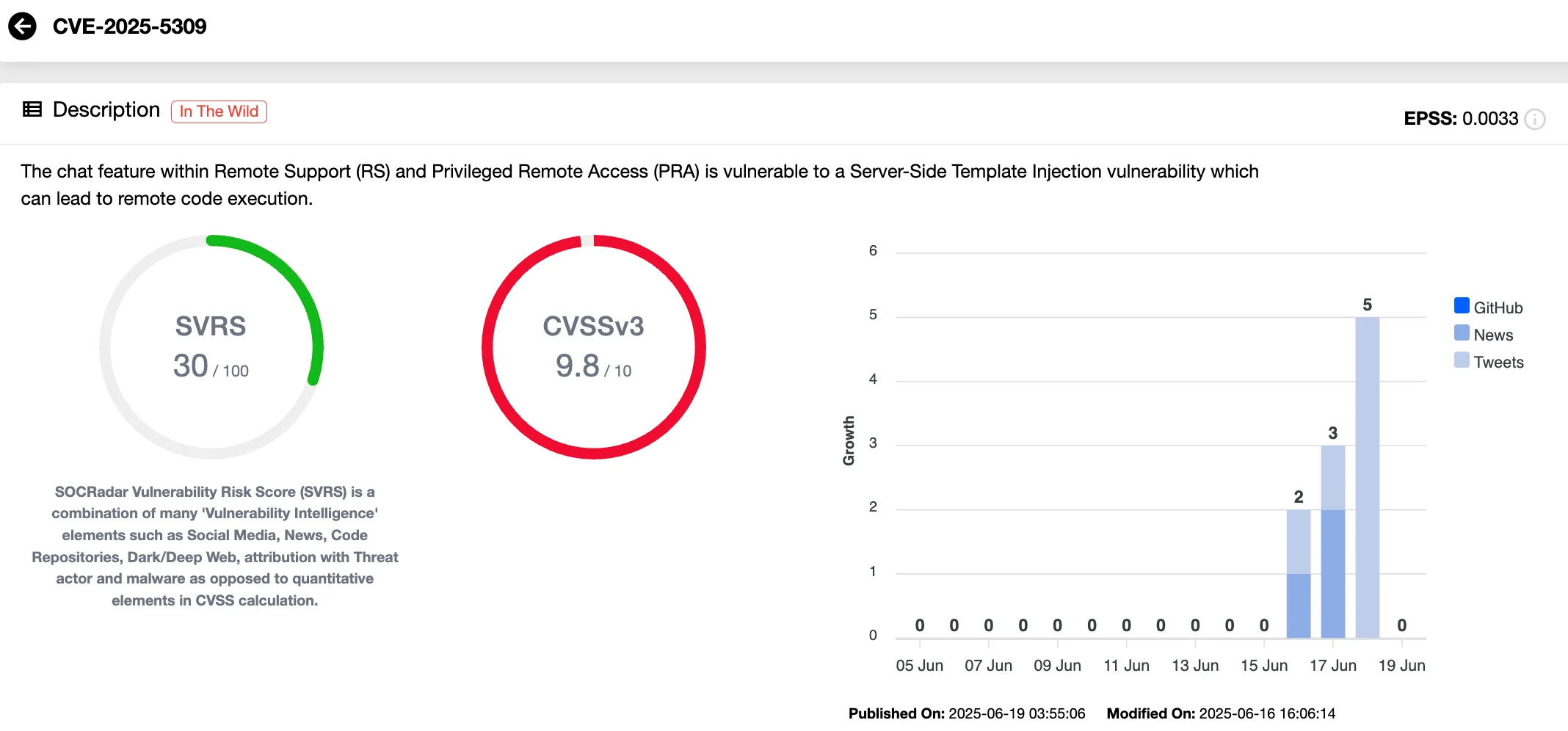
What Exactly Is CVE-2026-1731?
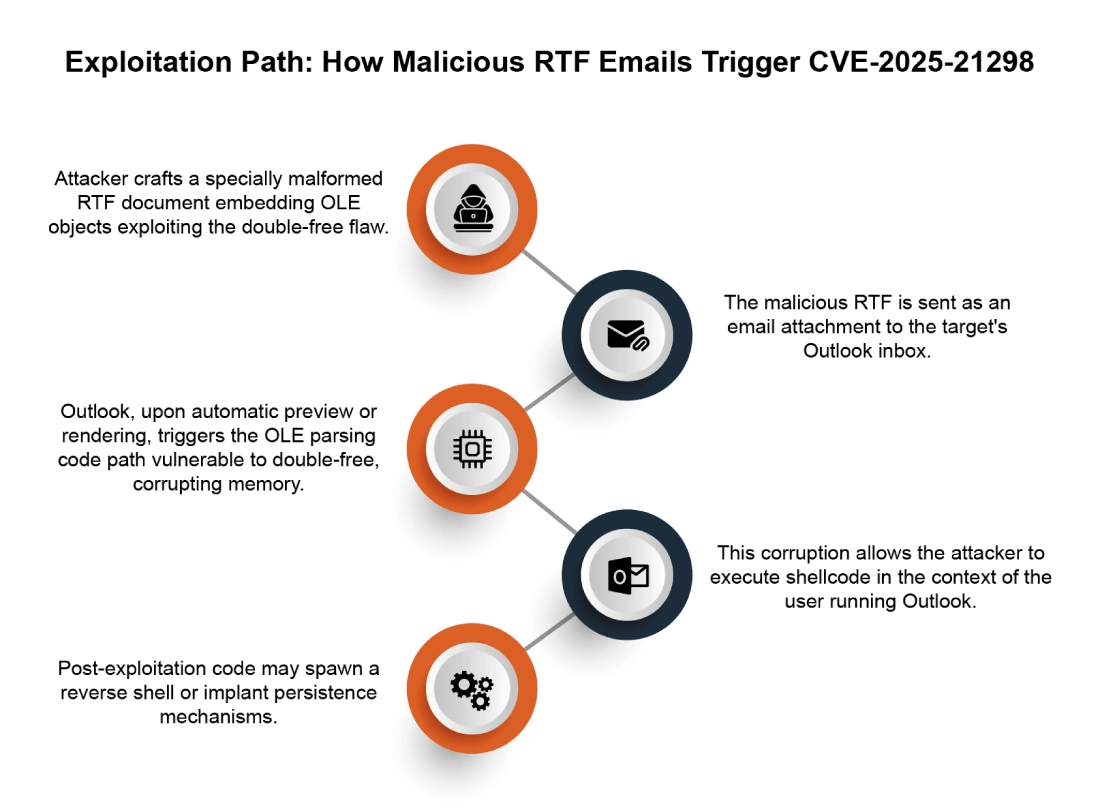
Let's start with the technical basics. CVE-2026-1731 is an OS command injection vulnerability lurking in Beyond Trust's Remote Support product and certain older versions of Privileged Remote Access.
Command injection sounds technical, but here's the simple version: somewhere in the code, user input gets passed directly to an operating system command without proper validation or escaping. An attacker can craft malicious input that tricks the application into executing arbitrary commands.
Think of it like this. Imagine a restaurant manager asks a chef to "make what the customer requested." If a customer says "pasta and also delete the inventory system," and the chef just executes both commands without thinking, you've got a problem. That's command injection.
In the Beyond Trust case, the vulnerability exists in how the application processes certain requests. An attacker can send a specially crafted request through the network. The application doesn't properly validate the input. Instead of executing what it should, it runs whatever the attacker embedded in their request. And because this is an unauthenticated vulnerability, the attacker doesn't need valid credentials to pull it off.
The vulnerability allows attackers to execute OS commands in the context of the site user. Depending on what user the application runs as (which is often a high-privileged account), an attacker could potentially gain significant control over the system.
The Attack Surface
What makes this vulnerability particularly dangerous is where it lives. Beyond Trust Remote Support and PRA are specifically designed to provide remote access to systems. They sit on the edge of your network, often exposed to the internet for legitimate remote work scenarios.
They're not buried deep in your internal infrastructure. They're accessible from the outside by design. That accessibility is their strength for legitimate use cases, but it becomes a massive liability when an unauthenticated RCE flaw exists.
An attacker doesn't need to break through your firewall. They don't need to compromise an employee's credentials first. They can find your Beyond Trust instance on the internet and start executing commands almost immediately.
Why This Happened
The root cause is an OS command injection weakness. Somewhere in the application's code, there's a function that builds and executes system commands based on user input. The developers didn't properly sanitize that input.
This is a classic, well-understood vulnerability class. It's been around for decades. Every secure coding guideline warns against it. Yet here we are, in 2026, and it still shows up in major enterprise software.
The irony is thick. Beyond Trust's entire business model is built on security. Their pitch to enterprises is "trust us with your privileged access management." And then a command injection vulnerability undermines that entire promise.

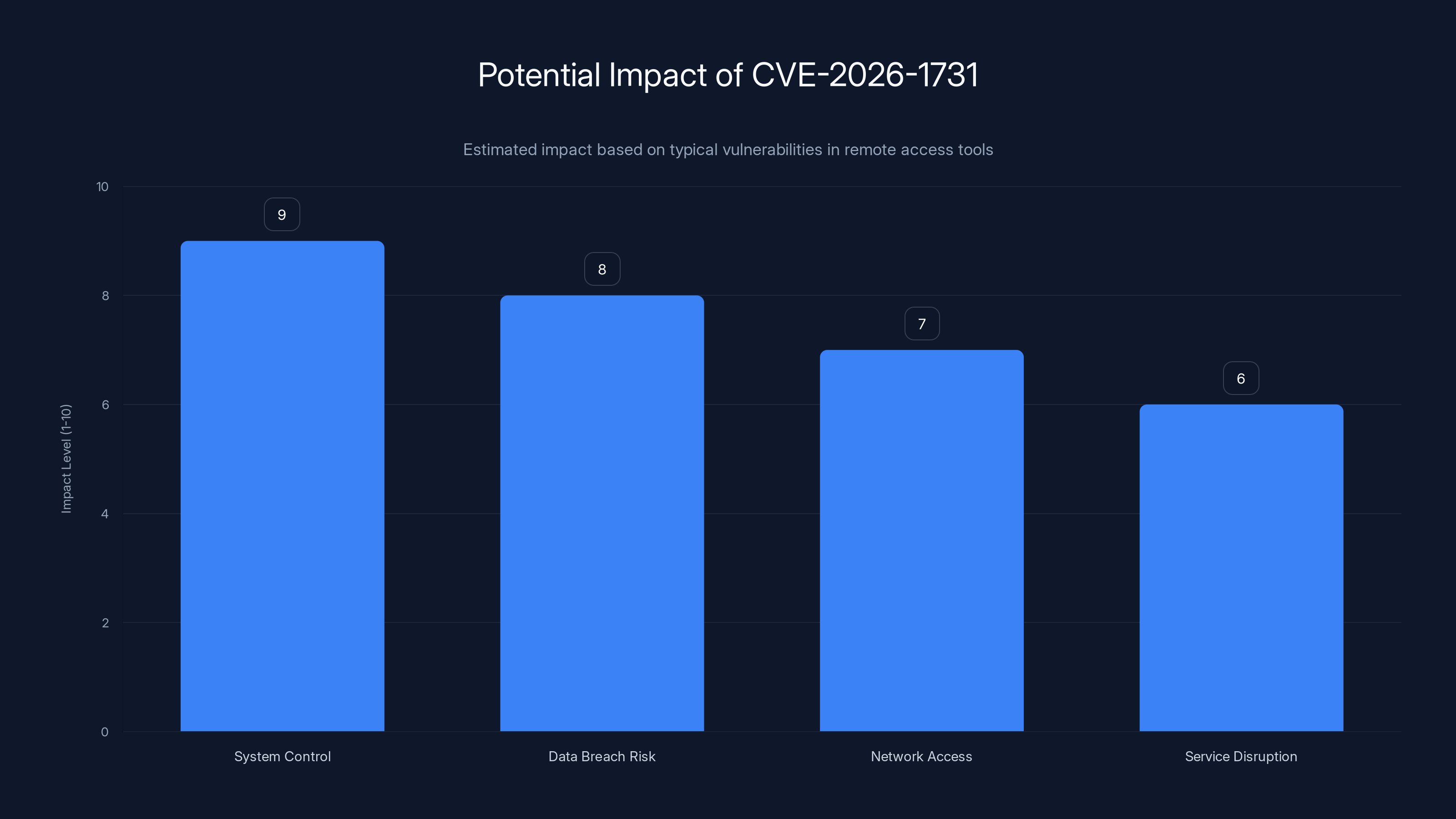
CVE-2026-1731 poses a high risk of system control and data breaches due to its unauthenticated nature. Estimated data.
The Severity Score Explained: 9.9 Out of 10
Let's talk about what a 9.9/10 CVSS score actually means in practical terms.
CVSS (Common Vulnerability Scoring System) is the industry standard way to rate vulnerability severity. It ranges from 0 (no risk) to 10 (absolute catastrophe). Most vulnerabilities fall in the 5-7 range. A 9.9 is extremely rare and indicates a near-worst-case scenario.
Here's how CVSS factors work:
Attack Vector: Network (highest score). The vulnerability can be exploited over the network without physical access or local network access. An attacker in Mumbai can attack a Beyond Trust instance in New York.
Attack Complexity: Low (highest score). No special conditions or advanced techniques required. A moderately skilled attacker could exploit this. You don't need to be a security genius or have deep knowledge of Beyond Trust internals.
Privileges Required: None (highest score). No authentication needed. No valid credentials. No account. Nothing. Send a malicious request and it works.
User Interaction: None (highest score). The victim doesn't need to click a link or take any action. The vulnerability triggers automatically when the right request is sent.
Scope: Unchanged (slightly lower score). The impact is limited to the vulnerable system, not the broader network. This is what keeps it from being a perfect 10.
Confidentiality: High. An attacker can read sensitive data: user credentials, session tokens, configuration files, database backups, whatever's on that system.
Integrity: High. An attacker can modify data: create backdoors, change configurations, inject malicious code, plant ransomware.
Availability: High. An attacker can take the service offline: crash the application, fill up disk space, delete critical files.
When you add all that up, you get 9.9. It's essentially saying: "This is as bad as things get. Attack it immediately."
How CVSS Compares to Other Recent CVEs
For context, let's look at some other notable vulnerabilities:
- Log 4j (CVE-2021-44228): 10/10. Similar RCE, but slightly broader impact
- MOVEit Transfer (CVE-2023-34362): 9.8/10. Also an RCE with no auth required
- Pulse Secure VPN (CVE-2020-8118): 9.8/10. Remote code execution via VPN interface
- Cisco ASA (CVE-2020-3452): 9.8/10. Path traversal and RCE
CVE-2026-1731 sits right in that terrifying neighborhood. It's not quite Log 4j level, but it's closer than most vulnerabilities get.
Affected Products and Versions
Let's be specific about what's vulnerable. Vague information leads to bad decisions.
Remote Support (RS)
Vulnerable: Version 25.3.1 and all earlier versions
Fixed: Version 25.3.2 and later
Remote Support is Beyond Trust's flagship remote access product. IT teams use it to:
- Provide tech support to end users
- Access remote computers for troubleshooting
- Run background jobs on remote systems
- Transfer files between systems
- Execute scripts and automation
If you're running Remote Support and haven't patched to 25.3.2 or later, you're vulnerable right now.
Privileged Remote Access (PRA)
Vulnerable: Version 24.3.4 and all earlier versions
Fixed: Version 25.1.1 and later
PRA is their enterprise-grade privileged access management solution. It's heavier than Remote Support but more powerful for managing infrastructure at scale. Organizations use it to:
- Control who accesses which systems
- Enforce just-in-time access policies
- Log and audit all privileged sessions
- Manage API keys and secrets
- Enforce MFA for sensitive access
Here's where it gets tricky. If you're running PRA version 22.1 through 24.3.4, you have options:
- Patch to 25.1.1 or later (recommended if possible)
- Patch to a patched version of your current major version (check Beyond Trust's advisory for specific version numbers)
- If you're on PRA older than 22.1, you need to upgrade entirely. They're not patching ancient versions.
Cloud vs. On-Premises
This distinction matters enormously.
Beyond Trust Cloud Customers: If you're running Beyond Trust in the cloud (their hosted SaaS offering), you're already patched. Beyond Trust pushed patches to all cloud instances automatically on February 2, 2026. You woke up that morning already protected.
On-Premises Customers: You need to manually apply patches. Your Remote Support or PRA instance won't auto-update unless you've specifically configured automatic updates. If you haven't, you're vulnerable until you manually patch.
According to Hacktron AI's research, roughly 8,500 of the 11,000 exposed instances are on-premises. That means most vulnerable organizations haven't patched yet.
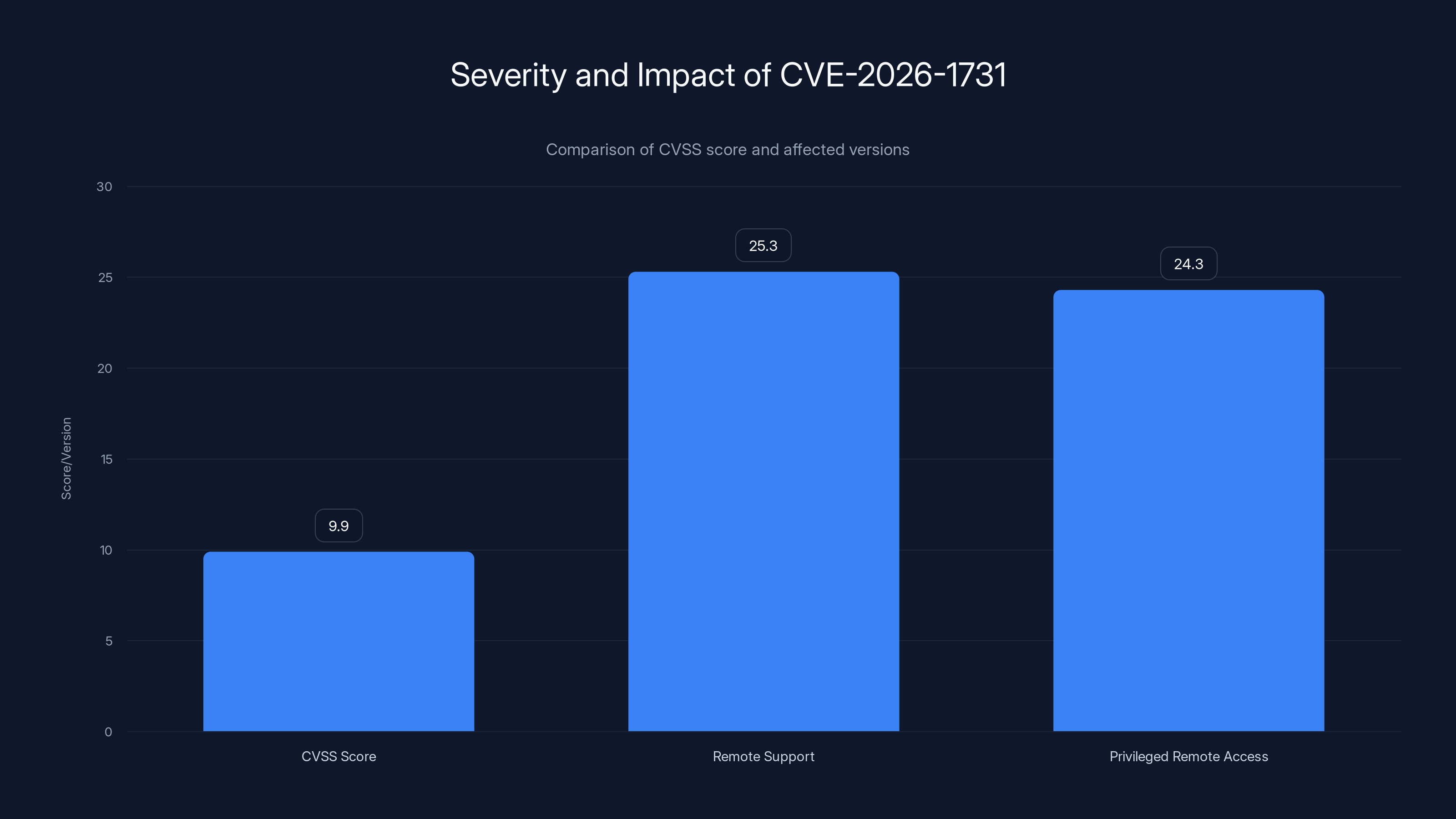
CVE-2026-1731 has a critical CVSS score of 9.9, affecting Remote Support versions up to 25.3 and Privileged Remote Access versions up to 24.3, indicating severe vulnerability across multiple versions.
Exposed Instances: The Numbers
Hacktron AI researchers found approximately 11,000 Beyond Trust instances exposed to the internet. That's not an estimate based on sampling. That's actual instances they discovered with network scanning tools.
Here's the breakdown:
- ~8,500 on-premises deployments (77%)
- ~2,500 cloud deployments (23%)
The fact that so many on-premises instances are exposed tells a story. These organizations deliberately opened Beyond Trust to the internet because:
- Employees work remotely and need access from anywhere
- They use Remote Support to help external customers
- They didn't restrict access to a VPN or private network
- Some probably just didn't think about it and exposed the default ports
That internet-facing exposure becomes catastrophic when an unauthenticated RCE vulnerability exists.
Geographic Distribution
While the advisory didn't specify exact geographic breakdowns, Beyond Trust disclosed that customers are spread across more than 100 countries. The vulnerability affects all of them equally.
Major industries represented likely include:
- Financial services (banks, insurance, investment firms)
- Healthcare (hospitals, pharmaceuticals, insurance companies)
- Technology (SaaS companies, cloud providers, software vendors)
- Government (federal, state, local agencies)
- Manufacturing (industrial companies, supply chain organizations)
- Telecommunications (ISPs, telecom providers)
Every single one of these organizations is taking this seriously right now.
The Timeline: From Discovery to Patch
Understanding the timeline helps you understand where we are right now.
Before February 2, 2026: Vulnerability exists in the wild, unknown to Beyond Trust. Hacktron AI researchers independently discover it and responsibly report it to Beyond Trust rather than selling it or publishing it publicly.
February 2, 2026: Beyond Trust releases patches for all affected products. Cloud instances update automatically. Beyond Trust issues a security advisory and starts notifying customers.
February 2-7, 2026: Security researchers, threat intelligence firms, and attackers begin analyzing the patches to understand the vulnerability. This is "patch diffing" – comparing the vulnerable code to the patched code to reverse-engineer what was broken.
February 7-14, 2026 (projected): First proofs-of-concept likely released. Security researchers publish detailed technical analysis. More sophisticated attackers develop reliable exploitation code.
February 14, 2026-ongoing: Attacks in the wild are likely already happening. Sophisticated attackers don't wait months. They exploit vulnerabilities while they're still hot, before most organizations patch.
Right now: If you haven't patched, you're in active danger.
Vulnerability Disclosure History
Beyond Trust hasn't confirmed public reports about how many systems were compromised before the patch. They did state there was "no evidence of exploitation in the wild" at the time of disclosure. However:
- That statement was made on February 2, 2026. It's now over two weeks later.
- "No evidence" at disclosure time doesn't mean "no actual exploitation." It means "we haven't found proof yet."
- Sophisticated attackers don't leave obvious tracks.
History suggests attacks are likely happening now, whether or not Beyond Trust has detected them.

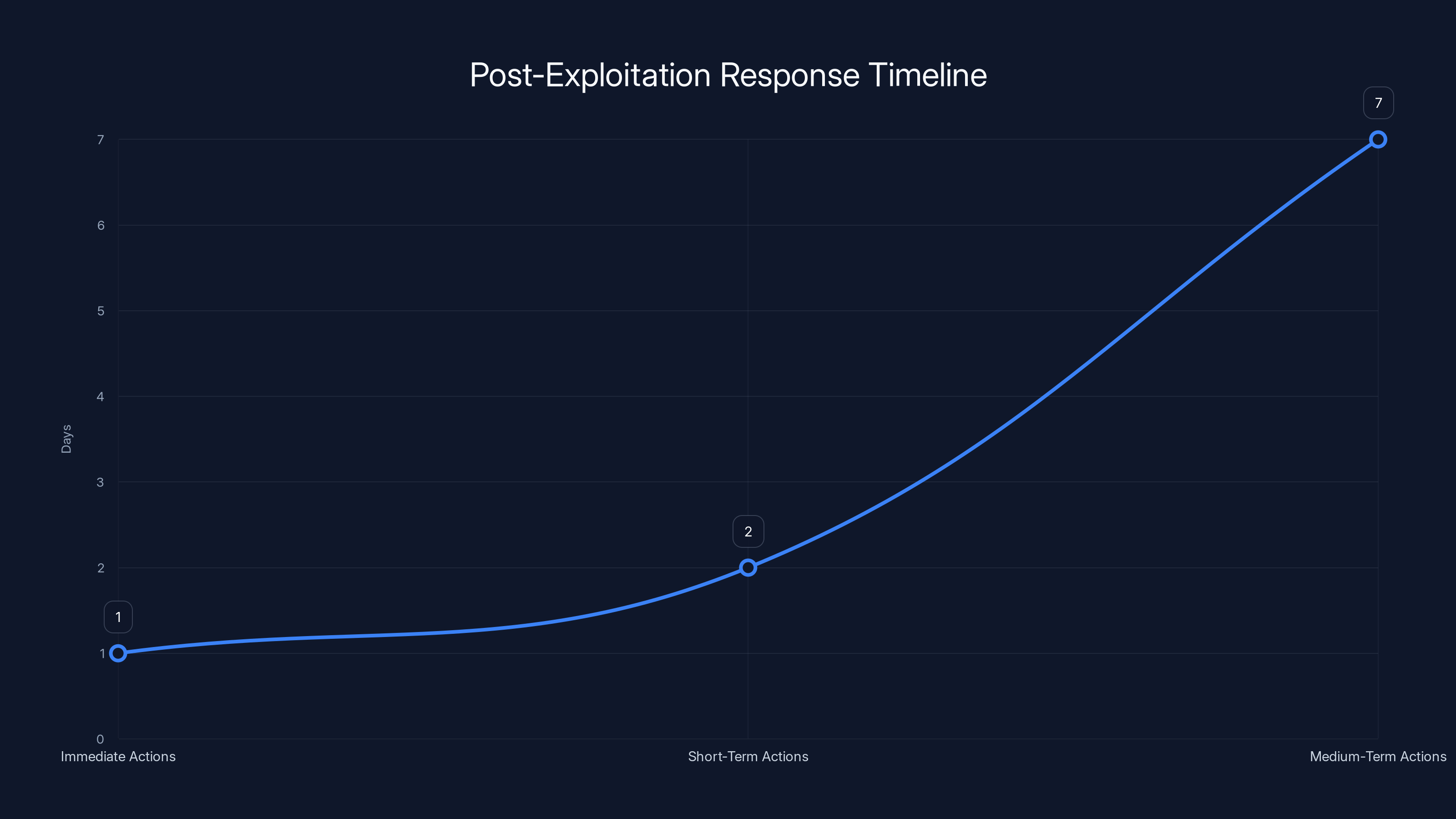
Estimated data shows the progression of actions from immediate response to medium-term strategies over a two-week period.
Who's at Risk? A Detailed Breakdown
The honest answer is: if you're running Remote Support or PRA without the latest patches, you're at risk.
But let's be more specific about threat levels.
Highest Risk Organizations
These groups should be panicking right now:
1. Publicly Exposed Beyond Trust Instances
If your Remote Support or PRA portal is accessible from the internet without VPN, you're extremely exposed. Attackers are probably already scanning your instance.
2. Financial Services
Banks, insurance companies, and fintech firms are prime targets. Why? Because accessing these systems gives attackers immediate path to money and sensitive financial data. A compromised Beyond Trust instance could give attackers credentials to banking systems, investment platforms, or payment processors.
3. Healthcare Organizations
Hospitals and medical device companies can't afford downtime. If attackers compromise a Remote Support instance, they can:
- Take down critical medical systems
- Encrypt patient databases for ransomware
- Extract HIPAA-protected health information
- Disrupt critical care workflows
A healthcare organization would likely pay ransom quickly to restore access.
4. Government Agencies
Federal, state, and local government systems are actively targeted by nation-state actors. A vulnerability in a remote access tool is exactly what they look for.
5. Critical Infrastructure Providers
Energy companies, water utilities, and telecommunications firms control systems that affect millions of people. A Beyond Trust compromise could lead to:
- Power outages
- Water supply disruption
- Telecommunications blackouts
- Supply chain attacks
Medium Risk Organizations
1. Technology Companies
SaaS companies, cloud providers, and software vendors manage significant customer infrastructure. A compromised Beyond Trust instance could give attackers backdoor access to customer environments.
2. Managed Service Providers (MSPs)
MSPs manage IT infrastructure for hundreds or thousands of small businesses. One compromised MSP could result in attacks across their entire customer base.
3. Large Enterprises
Any organization with significant IT infrastructure using Beyond Trust faces substantial risk, though they typically have better detection and response capabilities.
Lower Risk Organizations
1. Small Companies with Restricted Access
Small businesses that:
- Restrict Beyond Trust to internal networks only
- Require VPN to access Remote Support
- Use it minimally for occasional support
- Have modern intrusion detection
These organizations have lower risk, but not zero risk.
2. Organizations Patched and Monitoring
If you've patched to the latest version AND you're monitoring for suspicious activity, you're in pretty good shape. Not perfect, but good.
Attack Scenarios: How Exploitation Would Work
Let's walk through realistic attack scenarios so you understand what's at stake.
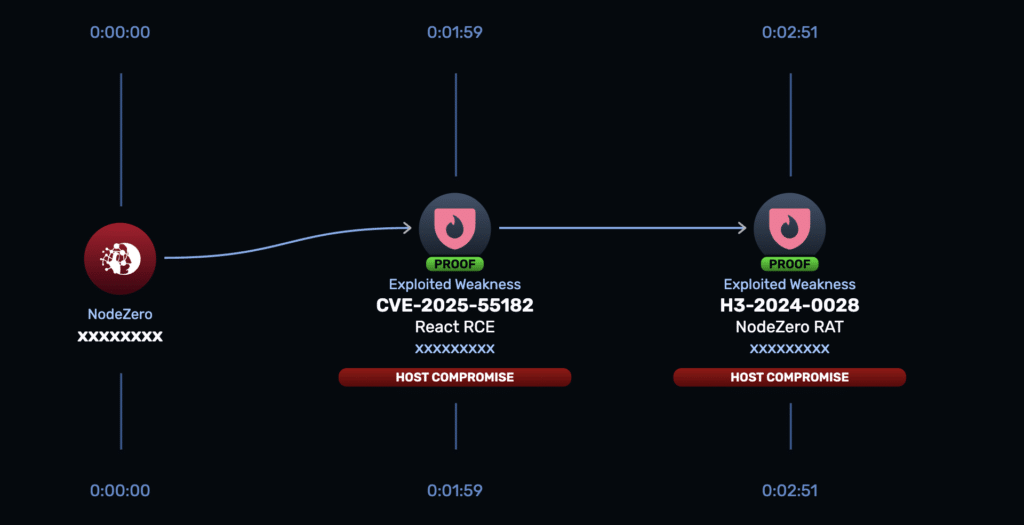
Scenario 1: The Initial Access Attack
Attacker starts with the goal of gaining initial access to your network.
Step 1: Attacker scans the internet for publicly exposed Beyond Trust instances. They use search engines like Shodan, passive DNS records, or active network scanning. They find yours on port 443 (HTTPS).
Step 2: Attacker crafts a malicious request containing an OS command injection payload. For example, a request that looks like normal Remote Support traffic but contains embedded commands:
GET /api/support?system=main`; rm -rf /critical/data;`
The backticks tell the shell to execute the enclosed command.
Step 3: Beyond Trust's vulnerable code receives this request. It doesn't properly validate the input. It executes the command: rm -rf /critical/data (delete critical files).
Step 4: Attacker has code execution. From here, they can:
- Create a persistent backdoor (modified startup script, new admin user, etc.)
- Exfiltrate database credentials and configuration
- Launch attacks on internal systems
- Plant ransomware or destructive malware
The entire attack takes maybe 15 minutes from initial scan to persistent access.
Scenario 2: The Data Exfiltration Attack
Attacker's goal is stealing sensitive data.
Step 1: Attacker finds your exposed Beyond Trust instance and gains code execution using the RCE flaw.
Step 2: Inside the Beyond Trust server, the attacker discovers:
- Configuration files with database credentials
- Session keys and access tokens
- SSH keys for other systems
- API keys for cloud services
- Recent access logs showing which systems are important
Step 3: Attacker uses stolen credentials to access other systems in your network. Maybe they find your customer database, your source code repository, your API infrastructure.
Step 4: Attacker exfiltrates data to an external server. Depending on your organization:
- Customer PII and payment information
- Proprietary source code and trade secrets
- Healthcare records or financial data
- Strategic business information
Step 5: Attacker either sells the data on the dark web or uses it for targeted attacks on your customers (supply chain attack).
This scenario takes days or weeks from initial compromise to complete exfiltration, but it starts with the same 15-minute initial exploitation.
Scenario 3: The Ransomware Attack
Attacker's goal is maximum disruption and ransom payment.
Step 1: Attacker gains code execution through the RCE vulnerability.
Step 2: Attacker establishes persistence (creating hidden admin accounts, installing rootkits, etc.) so they maintain access even after reboots.
Step 3: Attacker maps your entire network, identifying:
- Critical systems
- Backup systems
- Air-gapped networks
- Authentication servers
Step 4: Attacker disables or encrypts backup systems first (this is crucial for attackers, because backups are how you recover from ransomware).
Step 5: Attacker deploys ransomware to all critical systems simultaneously. Your entire infrastructure gets encrypted in a coordinated strike.
Step 6: Ransom note appears. You can't access patient records, you can't process transactions, you can't serve customers. Attackers demand payment in Bitcoin.
For critical infrastructure companies, this scenario results in tens of millions in damages through downtime alone, separate from ransom amounts.
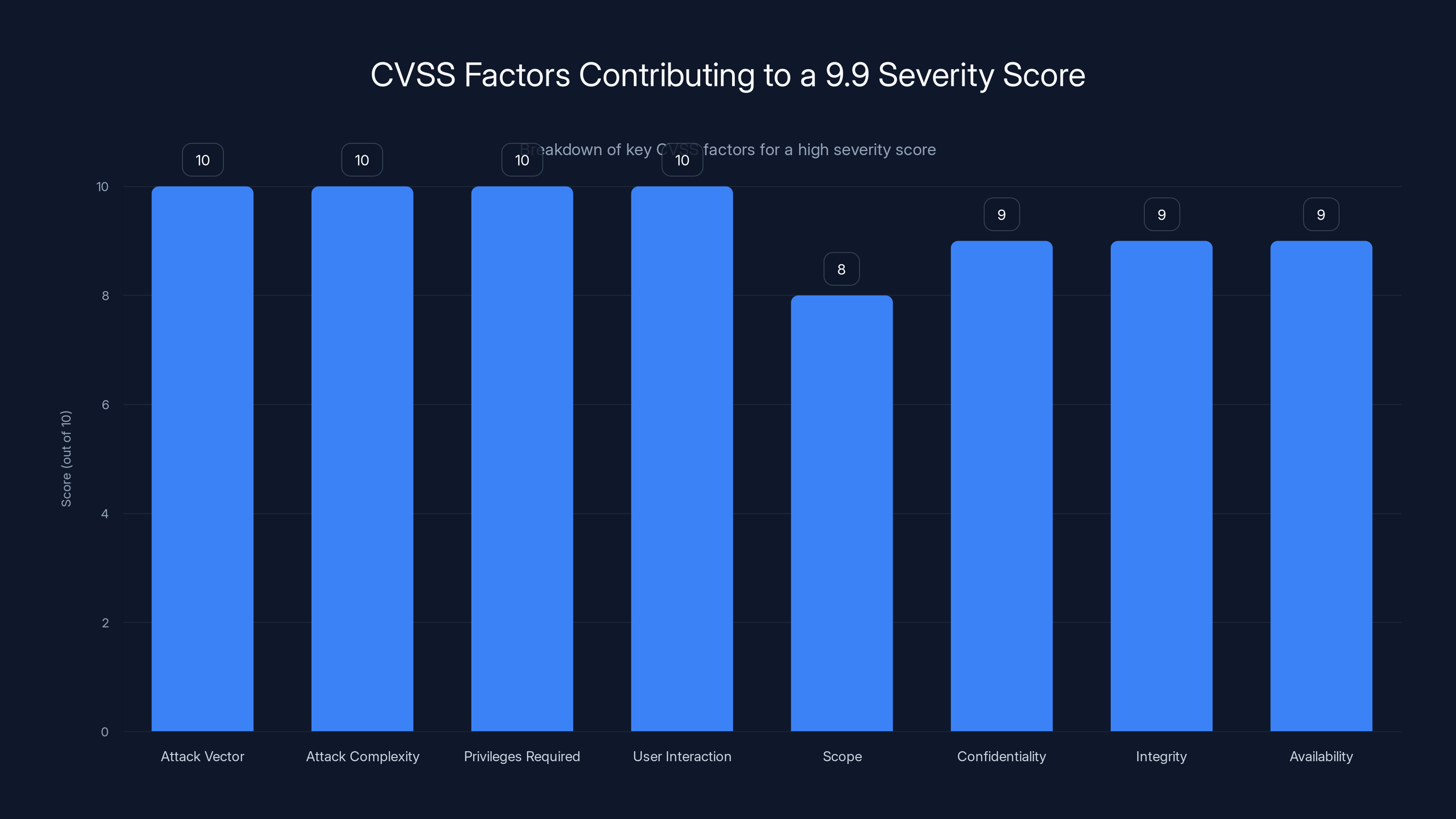
The CVSS score of 9.9 is driven by maximum scores in most factors, indicating severe vulnerability with minimal barriers to exploitation.
Patches Available: What You Need to Do
Beyond Trust released patches on February 2, 2026. Here's exactly what you need to do.
For Cloud Customers
If you use Beyond Trust's cloud service, you're already patched. Your instances updated automatically. No action needed from you, though you should still:
- Log in to verify your version number matches the patched version
- Check your access logs for suspicious activity dating back to February 2
- Verify your MFA and IP restrictions are still enabled
- Change privileged account passwords as a precaution
For On-Premises Remote Support
Current Version (25.3.x): Update to 25.3.2 or later
Older Versions: Check Beyond Trust's advisory for your specific version. They've released patches for multiple versions:
- 25.3.2
- 25.2.x (patched versions available)
- 25.1.x (patched versions available)
- 25.0.x (patched versions available)
- Older versions (likely need major version upgrade)
Process:
- Download the latest patch from Beyond Trust's support portal
- Schedule maintenance window (patching requires restart)
- Back up your Remote Support configuration and database
- Stop the Remote Support service
- Apply the patch
- Verify the service starts and functions normally
- Test remote connections to ensure functionality
Timeline: Aim to complete this within 48-72 hours. Not "within the week." Now.
For On-Premises PRA
Current Version (24.3.4): Upgrade to 25.1.1 or later
Versions 22.1 through 24.3.3: Check Beyond Trust's advisory for available patches
Versions Older than 22.1: You need to contact Beyond Trust. They may not provide patches for versions this old. You'll need to plan a major upgrade.
Process:
- Schedule significant maintenance window (PRA upgrades take longer)
- Backup all PRA data, certificates, and configurations
- Test the upgrade in a staging environment first
- Follow Beyond Trust's documented upgrade procedure
- Verify all components function (user portal, administration interface, audit logging)
- Restore normal operations
Timeline: Plan for this within one week. PRA upgrades are complex and risky if rushed, but waiting longer increases risk of exploitation.
If You Don't Have the Patch Yet
If Beyond Trust hasn't released a patch for your specific version, do this immediately:
1. Restrict Network Access
Remove internet exposure:
- Place Beyond Trust behind a VPN gateway
- Add IP whitelisting (only allow specific known IPs to access it)
- Require additional authentication before reaching Beyond Trust
- Disable Remote Support access temporarily if you can live without it
2. Increase Monitoring
Watch for exploitation:
- Monitor CPU and disk I/O for unusual spikes
- Check logs for failed command executions
- Alert on any new user account creations
- Monitor network connections to external IPs
- Set up email alerts for failed authentications
3. Contact Beyond Trust Support
Demand timeline information:
- When will a patch be available for your version?
- Are they aware of any active exploitation attempts?
- What workarounds do they recommend?
- What additional monitoring should you enable?
4. Prepare for Upgrade
Even if upgrading is painful, you may need to:
- Allocate resources now
- Schedule maintenance windows
- Plan testing procedures
- Notify stakeholders
Post-Exploitation: What to Do If You Were Compromised
If you've had Beyond Trust exposed to the internet for the last two weeks without patching, you should assume you might be compromised.
Immediate Actions (Today)
1. Isolate the System
- Disconnect Beyond Trust from the network if you can do so safely
- Redirect traffic to a maintenance page
- Notify users that the service is temporarily offline
2. Preserve Evidence
- Don't reboot the system (this clears memory-based evidence)
- Take disk images for forensic analysis
- Export all logs (system logs, application logs, authentication logs)
- Document the current state
3. Contact Incident Response
If your organization has:
- Internal security operations center (SOC): Alert them immediately
- Chief information security officer (CISO): Notify them
- Incident response team: Activate them
- Legal department: Brief them (this might involve breaches)
- Executive leadership: Prepare briefing
Short-Term Actions (24-48 Hours)
1. Forensic Analysis
Work with security professionals to:
- Examine logs for evidence of exploitation
- Check for backdoors or persistence mechanisms
- Identify what systems the attacker accessed
- Determine what data was accessed or exfiltrated
- Establish timeline of compromise
2. Credential Review
Assuming attacker had code execution, they could have accessed:
- Database passwords in configuration files
- SSH keys for remote systems
- API credentials for cloud services
- Session tokens and authentication keys
Reset all credentials for systems that Beyond Trust could access.
3. System Hardening
Apply security hardening immediately:
- Change local admin passwords
- Update firewall rules
- Enable additional authentication factors
- Patch all other vulnerabilities on the system
Medium-Term Actions (1-2 Weeks)
1. Affected Systems Audit
- Identify every system that was accessed through Beyond Trust
- Check each system for signs of compromise
- Look for modified files, new accounts, suspicious processes
- Review authentication logs for suspicious access
2. User Notification
If customer data was potentially accessed, you may need to notify users under various regulations:
- GDPR (European residents)
- CCPA (California residents)
- HIPAA (healthcare data)
- GLBA (financial data)
- State notification laws
Consult legal counsel on notification requirements.
3. Third-Party Assessment
Consider hiring external security firm to:
- Conduct full forensic investigation
- Perform penetration testing to identify other vulnerabilities
- Review security controls and response procedures
- Provide recommendations for future prevention
Long-Term Actions (Ongoing)
1. Process Improvements
- Implement just-in-time access for critical systems
- Require MFA for all remote access tools
- Monitor for unusual Remote Support/PRA usage patterns
- Implement network segmentation to limit blast radius
2. Security Culture
- Training on supply chain risk management
- Regular vulnerability scanning
- Patch management procedures
- Incident response drills
3. Monitoring and Detection
- Continuous monitoring for exploitation attempts
- Behavioral analytics on privileged access
- Alerting on suspicious Beyond Trust activities
- Regular log reviews and analysis

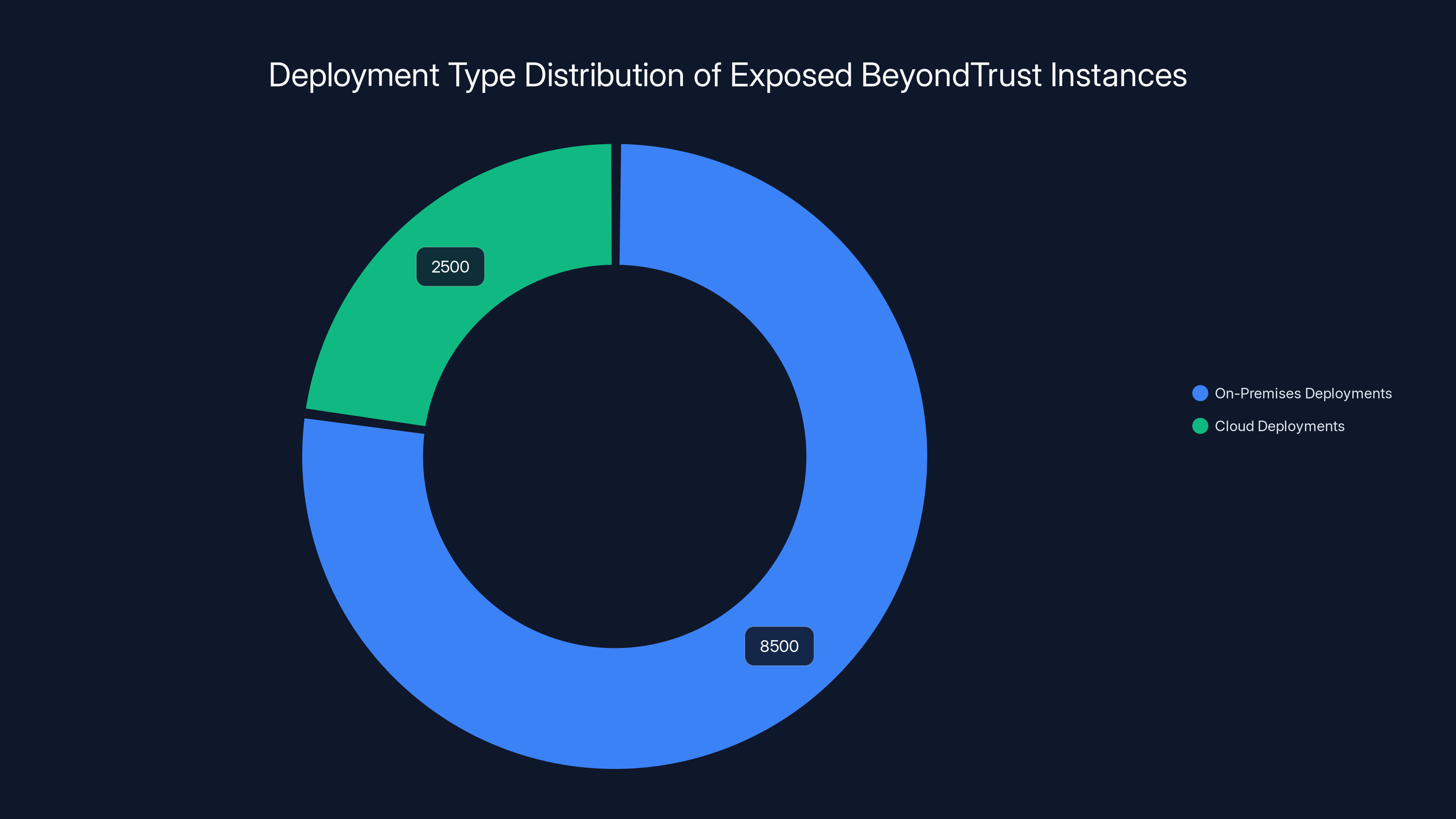
A significant 77% of exposed BeyondTrust instances are on-premises, highlighting a potential security oversight in remote access setups.
Defensive Strategies Beyond Patching
Patching is necessary but not sufficient. Here's how to defend comprehensively.
Network Segmentation
Even if an attacker gains code execution on your Beyond Trust instance, network segmentation limits their ability to move laterally.
Implementation:
- Place Beyond Trust on its own network segment (VLAN)
- Restrict network traffic FROM Beyond Trust to only necessary destinations
- Use firewalls to control what systems Beyond Trust can communicate with
- Segment critical systems (databases, domain controllers) on separate networks
Example: Beyond Trust can access File Server A and User Workstations, but cannot access your core database servers or domain controller. Even if compromised, the attacker's ability to escalate is limited.
Multi-Factor Authentication (MFA)
Even if attackers steal credentials from Beyond Trust configuration files, MFA prevents them from using those credentials.
Implementation:
- Require MFA to access Beyond Trust itself
- Require MFA for any systems that Beyond Trust can access
- Use hardware security keys for high-value systems
- Enforce MFA for all privileged accounts
Privileged Access Management (PAM)
If you're not already using PAM across your infrastructure, the existence of this vulnerability should convince you.
PAM systems:
- Store privileged credentials in encrypted vaults
- Require additional authorization to access them
- Record all usage of privileged accounts
- Rotate passwords automatically
- Restrict access by time and location
Instead of storing database passwords in plain text in Beyond Trust config files, they're stored in a vault. Even if an attacker gains code execution, they can't easily extract credentials.
Intrusion Detection and Response
Network-level detection:
- Monitor for unusual command execution patterns
- Alert on outbound connections from Beyond Trust to unexpected IPs
- Watch for suspicious DNS queries
- Monitor for data exfiltration attempts
Host-level detection:
- File integrity monitoring (alert when system files change)
- Process monitoring (alert on unusual child processes)
- Authentication monitoring (alert on new account creation)
- Log aggregation and analysis
Zero Trust Architecture
Instead of trusting that internal systems are safe, zero trust assumes every request could be malicious.
Principles:
- Verify every connection, even internal ones
- Encrypt all traffic, including internal traffic
- Log and monitor everything
- Assume breach and design accordingly
- Grant minimum necessary access
In a zero trust environment, even if an attacker gains code execution on Beyond Trust, they're still restricted by strict access controls on every internal system they try to access.
Lessons Learned: Why This Matters
CVE-2026-1731 isn't just another vulnerability. It's a symptom of systemic issues in enterprise software security.
Command Injection Is Still Common
Command injection vulnerabilities are well-understood and relatively easy to prevent. Yet they keep showing up in production code from major companies.
The solution is basic secure coding practices:
- Never pass user input directly to system commands
- Use parameterized APIs instead of string concatenation
- Validate and sanitize all input
- Use whitelists instead of blacklists
- Use least privilege principles (run code as non-root user)
These are not new ideas. They're taught in every cybersecurity program. Yet they're still violated regularly.
Trust Boundaries Keep Expanding
Beyond Trust's business model requires exposing Remote Support to the internet. That's not inherently bad, but it requires perfect security.
Perfect security is impossible. So organizations need to assume exposure tools will eventually have vulnerabilities, and design accordingly.
Supply Chain Risk Is Real
When Beyond Trust is compromised, every organization using it becomes a potential attack vector.
This vulnerability didn't just expose 11,000 Beyond Trust instances. It exposed every system those instances could access. Potentially hundreds of thousands of computers and data stores.
A vulnerability in a widely-deployed tool like Beyond Trust has cascade effects across the entire technology ecosystem.
Speed Matters
The organizations that patch today get ahead of attacks. The organizations that patch in two weeks are likely already compromised.
Speedily patching critical vulnerabilities isn't optional. It's existential.
FAQ
What is CVE-2026-1731?
CVE-2026-1731 is a critical (9.9/10 severity) remote code execution vulnerability in Beyond Trust Remote Support and Privileged Remote Access products. It's an OS command injection flaw that allows unauthenticated attackers to execute arbitrary operating system commands on affected systems, potentially leading to complete system compromise, data exfiltration, and service disruption without requiring any credentials or user interaction.
How does the vulnerability work?
The vulnerability exists because Beyond Trust's code processes user input and passes it directly to operating system commands without proper validation or escaping. An attacker can craft a specially formatted request containing embedded OS commands. When the vulnerable code executes the request, it unwittingly executes the attacker's injected commands with the privileges of the Beyond Trust application. Since the vulnerability is unauthenticated, attackers don't need credentials to trigger it.
Which versions are affected?
Remote Support versions 25.3.1 and earlier are vulnerable. Privileged Remote Access versions 24.3.4 and earlier are vulnerable. Specific patch versions are: Remote Support 25.3.2 and later, PRA 25.1.1 and later, or patched versions of intermediate releases. Organizations running older versions may need to upgrade entirely rather than patch.
Why is a 9.9/10 CVSS score so critical?
A 9.9/10 CVSS score indicates the vulnerability has the most severe characteristics possible: network-accessible (can be attacked remotely), low attack complexity (easy to exploit), no authentication required, no user interaction needed, and full impact on confidentiality, integrity, and availability. This combination means attackers don't need any special knowledge or access to exploit it. The vulnerability is as severe as real-world vulnerabilities get, short of a hypothetical 10/10.
How many systems are exposed?
According to researchers from Hacktron AI, approximately 11,000 Beyond Trust instances are exposed to the internet, including both cloud and on-premises deployments. Roughly 8,500 of these are on-premises systems, which means they won't automatically patch themselves unless administrators manually apply the update. This represents a significant exposed attack surface.
Has this vulnerability been exploited in the wild?
Beyond Trust stated there was no evidence of active exploitation at the time of public disclosure (February 2, 2026), but this statement should be treated cautiously. Sophisticated attackers don't always leave obvious traces, and the statement was made over two weeks ago. Given the severity and simplicity of exploitation, active attacks are likely occurring now, especially against high-value targets like financial institutions and critical infrastructure.
What should I do if I'm running vulnerable Beyond Trust software?
Immediate actions: Update to the patched version as soon as possible (within 24-48 hours for cloud instances, 48-72 hours for on-premises Remote Support, and within a week for PRA). Until you patch, restrict network access by placing Beyond Trust behind a VPN, enabling IP whitelisting, and monitoring closely for signs of compromise. Check your access logs for suspicious activity dating back to February 2, 2026. If you discover evidence of exploitation, activate your incident response procedures immediately.
What if I've been exposed for weeks without knowing?
You should assume your system may have been compromised if it was accessible to the internet and unpatched. Immediately isolate the Beyond Trust system, preserve logs and forensic evidence, involve your incident response team and legal counsel, and conduct a thorough forensic investigation. Assume attackers accessed any credentials or data stored on the Beyond Trust system and reset all related passwords. Review all systems that Beyond Trust could access for signs of compromise. You may be required to notify users under applicable data protection regulations.
How can I defend against this in the future?
Beyond patching, implement network segmentation to limit lateral movement, enforce multi-factor authentication on all remote access tools and critical systems, use privileged access management for credential storage, implement intrusion detection systems to monitor for exploitation attempts, and adopt zero trust architecture principles. Most importantly, establish rapid patching procedures for critical vulnerabilities. Speed is the difference between being safe and being compromised.
Is Beyond Trust still trustworthy after this vulnerability?
A single vulnerability doesn't necessarily mean you should abandon a vendor, but it does warrant reassessment. Beyond Trust is a major player in identity and access management serving 20,000+ customers. The question is whether they responded appropriately: did they disclose promptly, provide patches quickly, and communicate clearly? By those measures, their response was reasonable. However, you should evaluate whether their security practices justify the trust you place in them, especially given that their entire business model depends on security.
Final Recommendations
Here's what needs to happen now:
If you haven't patched: Schedule patching for this week. Right now, before you finish reading this. Treat it as a critical business priority. Not "when we have time," but actually schedule it. If you don't have bandwidth, request emergency resources.
If you've already patched: Verify the patch actually applied by checking version numbers in the admin console. Review logs for any suspicious activity before the patch date. Consider rotating credentials that the Beyond Trust system could access. Consider implementing additional security layers like MFA and network segmentation.
If you don't know whether you're running Beyond Trust: Find out. Right now. Check your infrastructure documentation, ask your systems team, search your security tool inventory. If you discover Beyond Trust anywhere, you now have a critical patching task.
Going forward: Establish processes for rapid response to critical vulnerabilities. Subscribe to security advisories for your critical infrastructure. Implement automated patch management where possible. Use network segmentation and zero trust principles to limit blast radius when (not if) vulnerabilities are exploited.
CVE-2026-1731 is a wake-up call. The question is whether your organization will actually wake up.
Key Takeaways
- CVE-2026-1731 is a 9.9/10 critical unauthenticated RCE in BeyondTrust Remote Support and PRA allowing attackers to execute OS commands without credentials
- Approximately 11,000 BeyondTrust instances are internet-exposed, with 8,500 being on-premises deployments requiring manual patching
- Patches released February 2, 2026; cloud instances auto-updated, but on-premises systems need immediate manual patching within 24-72 hours
- Exploitation allows complete system compromise including data exfiltration, ransomware deployment, and lateral movement to internal networks
- Defense-in-depth strategy combining patching, network segmentation, multi-factor authentication, and privilege management limits blast radius from compromise
Related Articles
- DNS Malware Detour Dog: How 30K+ Sites Harbor Hidden Threats [2025]
- Vega Security Raises $120M Series B: Rethinking Enterprise Threat Detection [2025]
- Authentication Beyond MFA in 2026: Phishing-Resistant Methods [2025]
- Proton VPN's Android Update Excludes Countries From Quick Connect [2025]
- Quishing: The QR Code Phishing Scam Taking Over [2025]
- AI Security Breaches: How AI Agents Exposed Real Data [2025]
![BeyondTrust RCE Vulnerability CVE-2026-1731: What You Need to Know [2025]](https://tryrunable.com/blog/beyondtrust-rce-vulnerability-cve-2026-1731-what-you-need-to/image-1-1770741766550.jpg)



