Flaming China Hacker Breach: Unpacking the Largest Data Heist in History [2025]
The recent breach at China’s National Supercomputing Center, allegedly perpetrated by the hacker known as ‘Flaming China’, has sent shockwaves through the global cybersecurity community. With claims of over 10 petabytes of advanced military data stolen, this incident could be unprecedented in scale and complexity.
TL; DR
- Massive Data Breach: Over 10 petabytes of sensitive military data compromised.
- Advanced Techniques: Utilized sophisticated hacking methods to infiltrate high-security systems.
- Global Implications: Potential shifts in geopolitical power dynamics.
- Cybersecurity Gaps: Exposed vulnerabilities in national defense systems.
- Future Strategies: Urgent need for enhanced cybersecurity protocols.

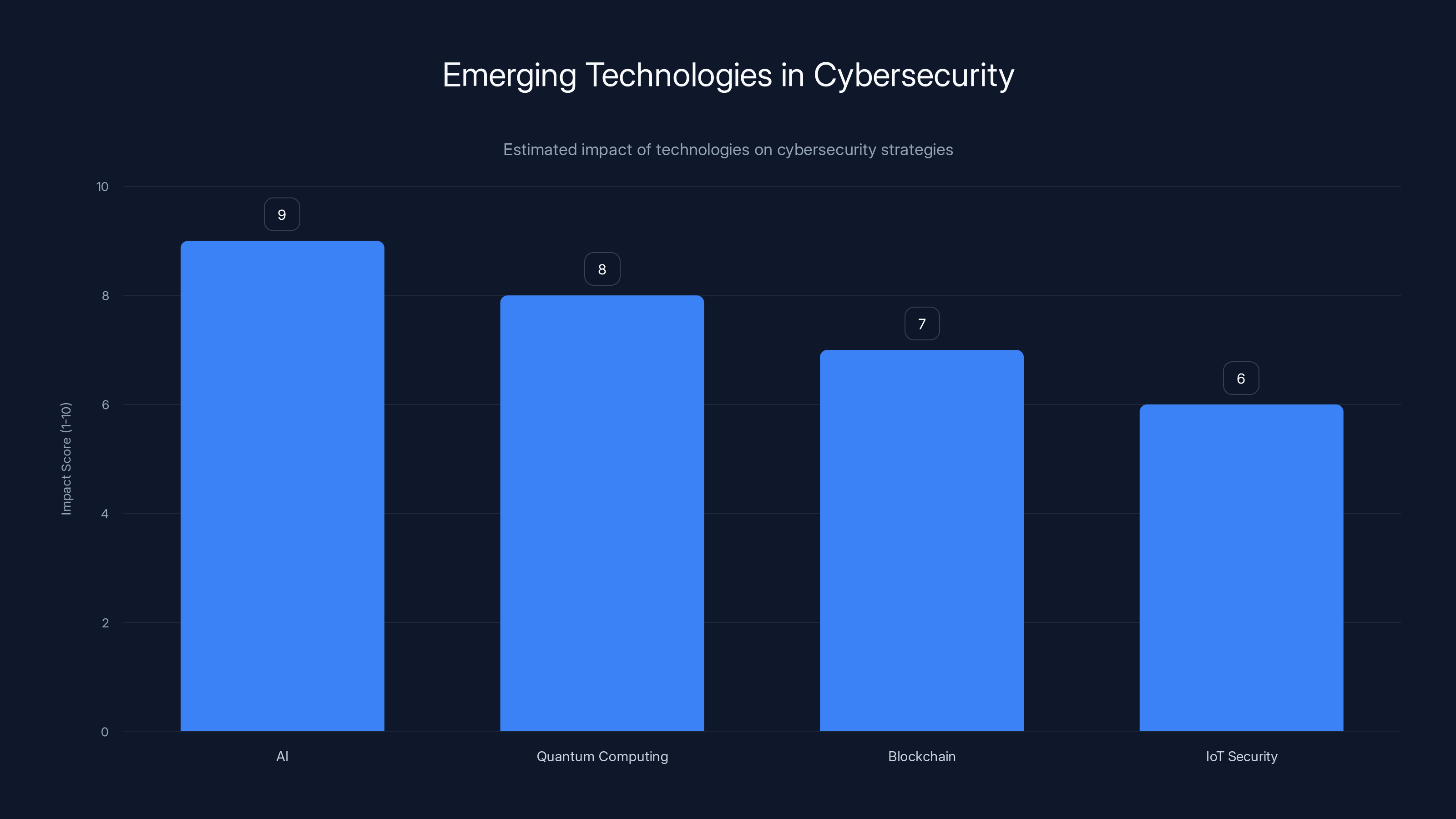
AI and Quantum Computing are projected to have the highest impact on future cybersecurity strategies. Estimated data.
Understanding the Scope of the Breach
The breach, involving data ranging from aircraft schematics to missile systems and military simulations, highlights the vulnerabilities even in the most secure facilities. The National Supercomputing Center, a critical node in China’s computing infrastructure, was thought to be impenetrable due to its advanced security measures.
The Data Stolen
The stolen data includes:
- Aircraft Schematics: Blueprints and design documents for advanced military aircraft.
- Missile Systems: Details about missile configurations and deployment strategies.
- Military Simulations: Real-time simulations used for strategic planning and training.
Such data, if in the wrong hands, could severely undermine national security and alter military balances.

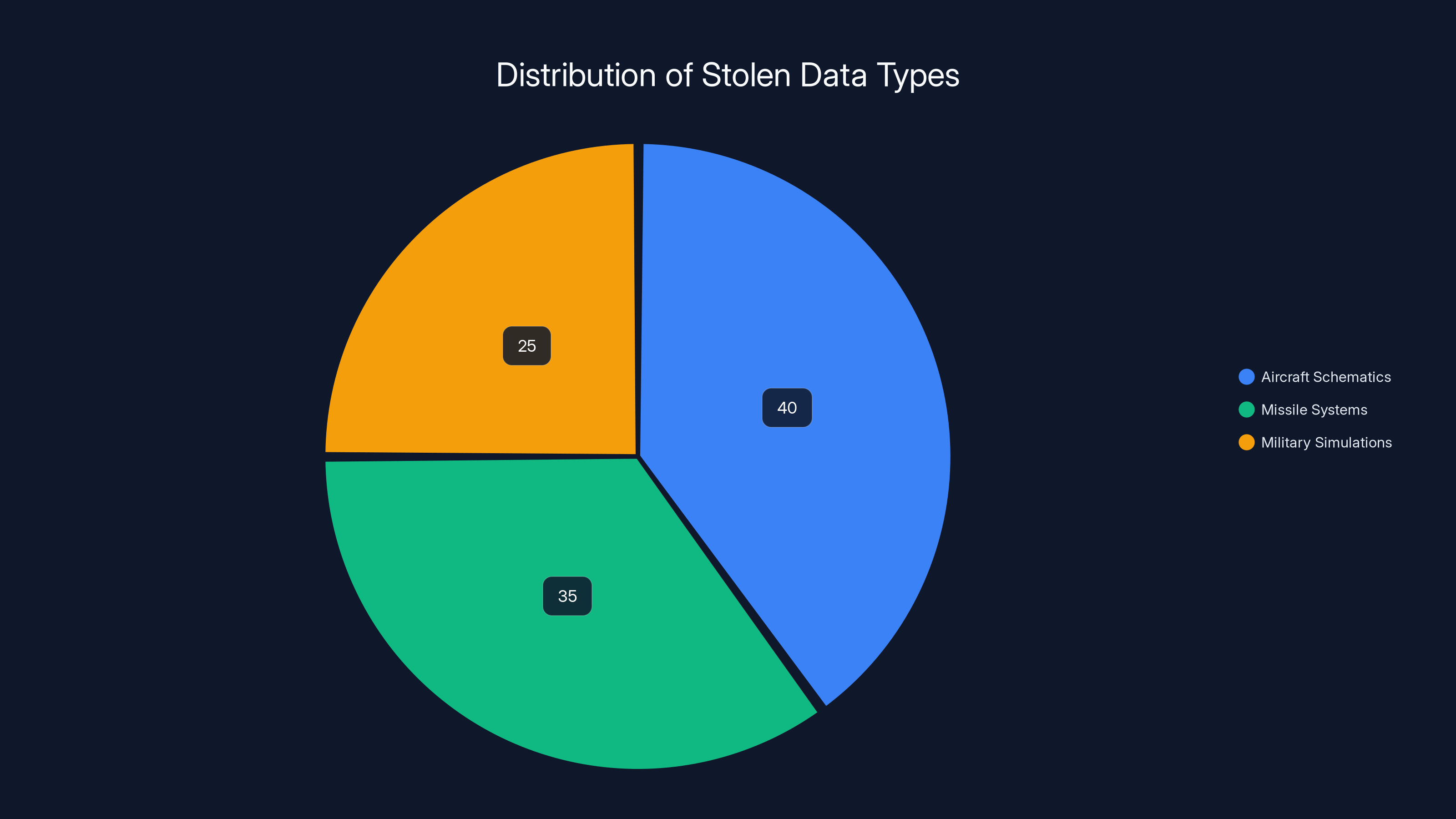
Estimated data shows that aircraft schematics make up the largest portion of the stolen data, followed by missile systems and military simulations. Estimated data.
How the Breach Occurred
Techniques Employed
The hacker, ‘Flaming China’, allegedly used a combination of social engineering, zero-day exploits, and advanced persistent threats (APTs) to gain access.
Social Engineering: Manipulating individuals to gain confidential information.
Zero-Day Exploits: Leveraging unpatched vulnerabilities in software.
Advanced Persistent Threats: Continuous long-term cyberattacks aimed at stealing data.
Step-by-Step Breakdown
- Initial Reconnaissance: Conducted extensive research to identify weak points in the network.
- Phishing Campaigns: Deployed targeted phishing emails to gather credentials.
- Exploitation of Vulnerabilities: Used zero-day exploits to bypass security measures.
- Establishing Backdoors: Created hidden access points for prolonged data extraction.
- Data Exfiltration: Transferred massive amounts of data without detection.

Technical Details and Best Practices
Enhancing Cybersecurity
In light of this breach, it’s crucial to reassess cybersecurity strategies:
- Implement Multi-Factor Authentication (MFA): Reduces risk by requiring multiple forms of verification.
- Regular Security Audits: Continuous evaluation of security systems to identify vulnerabilities.
- Employee Training: Educate employees on recognizing phishing attempts and other social engineering tactics.
- Network Segmentation: Isolates critical systems to limit access and reduce potential damage.
Common Pitfalls and Solutions
- Ignoring Software Updates: Always apply updates to patch vulnerabilities.
- Insufficient Monitoring: Implement real-time monitoring tools to detect suspicious activity.
- Weak Password Policies: Enforce strong, complex passwords and regular changes.
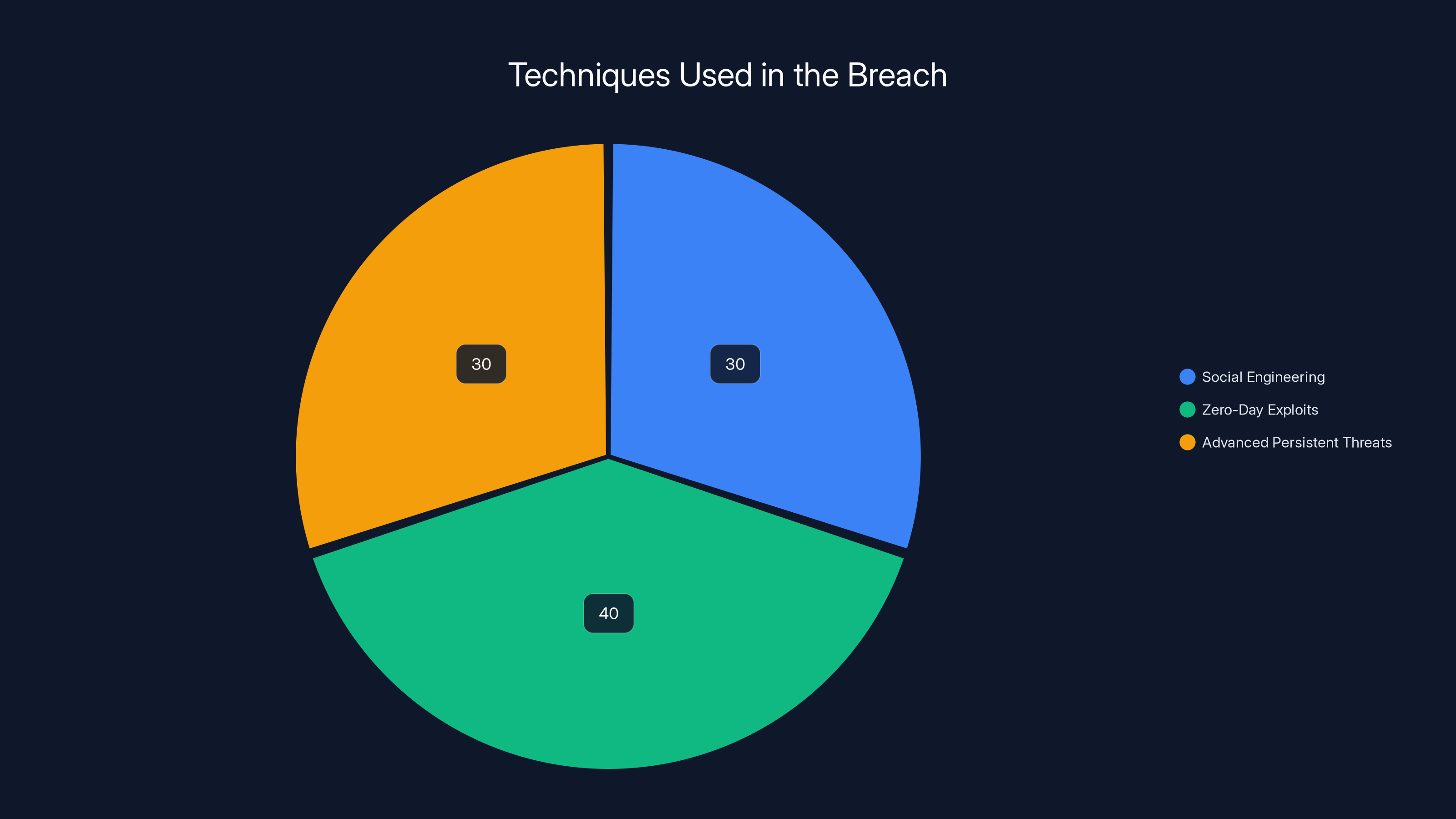
Estimated distribution shows a balanced use of social engineering, zero-day exploits, and APTs, highlighting the complexity of the attack.
Future Trends in Cybersecurity
The Rise of AI in Defense
AI is increasingly being integrated into cybersecurity protocols to predict and counteract threats. Machine learning algorithms can analyze patterns and detect anomalies faster than traditional methods.
- Predictive Analytics: AI can forecast potential attack vectors before they occur.
- Automated Response Systems: AI-driven systems can automatically neutralize threats in real-time.
Quantum Computing: A Double-Edged Sword
While quantum computing promises breakthroughs in various fields, it also poses significant risks to cybersecurity. Quantum computers could potentially break current encryption methods, necessitating the development of quantum-resistant algorithms.
Practical Implementation Guides
Setting Up a Robust Defense
- Assess Current Security Posture: Conduct a thorough analysis of your existing cybersecurity measures.
- Develop a Response Plan: Create a detailed plan outlining actions to take in the event of a breach.
- Utilize Threat Intelligence: Leverage global threat intelligence to stay informed about emerging threats.
- Deploy Intrusion Detection Systems (IDS): Monitor and detect unauthorized access attempts.
Case Study: Successful Breach Mitigation
An unnamed defense contractor faced a similar threat but managed to thwart the attackers by:
- Rapid Response: Immediately deploying their incident response team.
- Forensic Analysis: Conducting a detailed examination to understand the breach mechanism.
- Strengthening Defenses: Implementing additional security measures based on findings.

Conclusion: The Path Forward
The Flaming China breach serves as a stark reminder of the evolving threat landscape. Organizations must prioritize cybersecurity, continuously adapting to emerging threats. The integration of AI and quantum computing into security strategies will be crucial in maintaining a robust defense.
Use Case: Automate your cybersecurity monitoring with AI-powered tools to detect threats in real-time.
Try Runable For FreeFAQ
What was stolen in the Flaming China hack?
Over 10 petabytes of data, including sensitive military information like aircraft schematics and missile system details, were compromised.
How did the hacker gain access?
The hacker used a combination of social engineering, zero-day exploits, and advanced persistent threats (APTs) to infiltrate the system.
What are the implications of this breach?
The breach could alter geopolitical dynamics by exposing critical military data, potentially affecting national security.
How can organizations protect against such hacks?
Implement multi-factor authentication, conduct regular security audits, educate employees, and use AI for threat detection.
What role does AI play in cybersecurity?
AI aids in predictive analytics, anomaly detection, and automated threat responses, enhancing security measures.
Why is quantum computing a concern?
Quantum computing could break current encryption methods, necessitating the development of quantum-safe algorithms.
What measures should be taken in case of a breach?
Deploy an incident response team, conduct forensic analysis, and strengthen defenses based on breach findings.
How does Runable assist in cybersecurity?
Runable offers AI-powered automation tools to enhance monitoring and threat detection capabilities.
Key Takeaways
- Massive breach of over 10 petabytes of military data.
- Exploitation of advanced hacking techniques.
- Potential geopolitical shifts due to data exposure.
- Urgent need for enhanced cybersecurity protocols.
- Integration of AI and quantum computing in defense strategies.
Related Articles
- The Alinto Data Breach: Lessons in Cybersecurity for Enterprises [2025]
- Understanding the LAPD Data Breach: Lessons and Future Safeguards [2025]
- Mac Malware Defense: Safeguarding Against Evolving Threats [2025]
- The Dark Side of Cybersecurity: NHS Scotland Domains and the Hidden Threats [2025]
- How Emojis Are Reshaping Cybercrime Tactics: A Deep Dive [2025]
- US Agencies Alert: Iranian Hackers Targeting American Critical Infrastructure [2025]
![FlamingChina Hacker Breach: Unpacking the Largest Data Heist in History [2025]](https://tryrunable.com/blog/flamingchina-hacker-breach-unpacking-the-largest-data-heist-/image-1-1775759902286.jpg)



