How AI Like Anthropic’s Mythos is Revolutionizing Cybersecurity [2025]
In the realm of cybersecurity, a new contender is challenging the status quo: AI-driven tools. Among these, Anthropic’s Mythos has emerged as a formidable player, reportedly matching the capabilities of the world’s best security researchers. After a successful experiment with Mozilla’s Firefox, Mythos demonstrated that the era of AI-powered cybersecurity is not just a future possibility—it’s happening now.
TL; DR
- Anthropic’s Mythos: An AI tool that rivals top human security researchers.
- Mozilla Experiment: Mythos identified numerous vulnerabilities in Firefox, showcasing its potential.
- Zero-day Threats: AI tools like Mythos are changing the game in identifying and mitigating zero-day vulnerabilities.
- Implementation Challenges: Integrating AI in cybersecurity demands careful consideration of ethical and practical issues.
- Future Outlook: AI in cybersecurity promises enhanced protection but requires ongoing human oversight and adaptation.
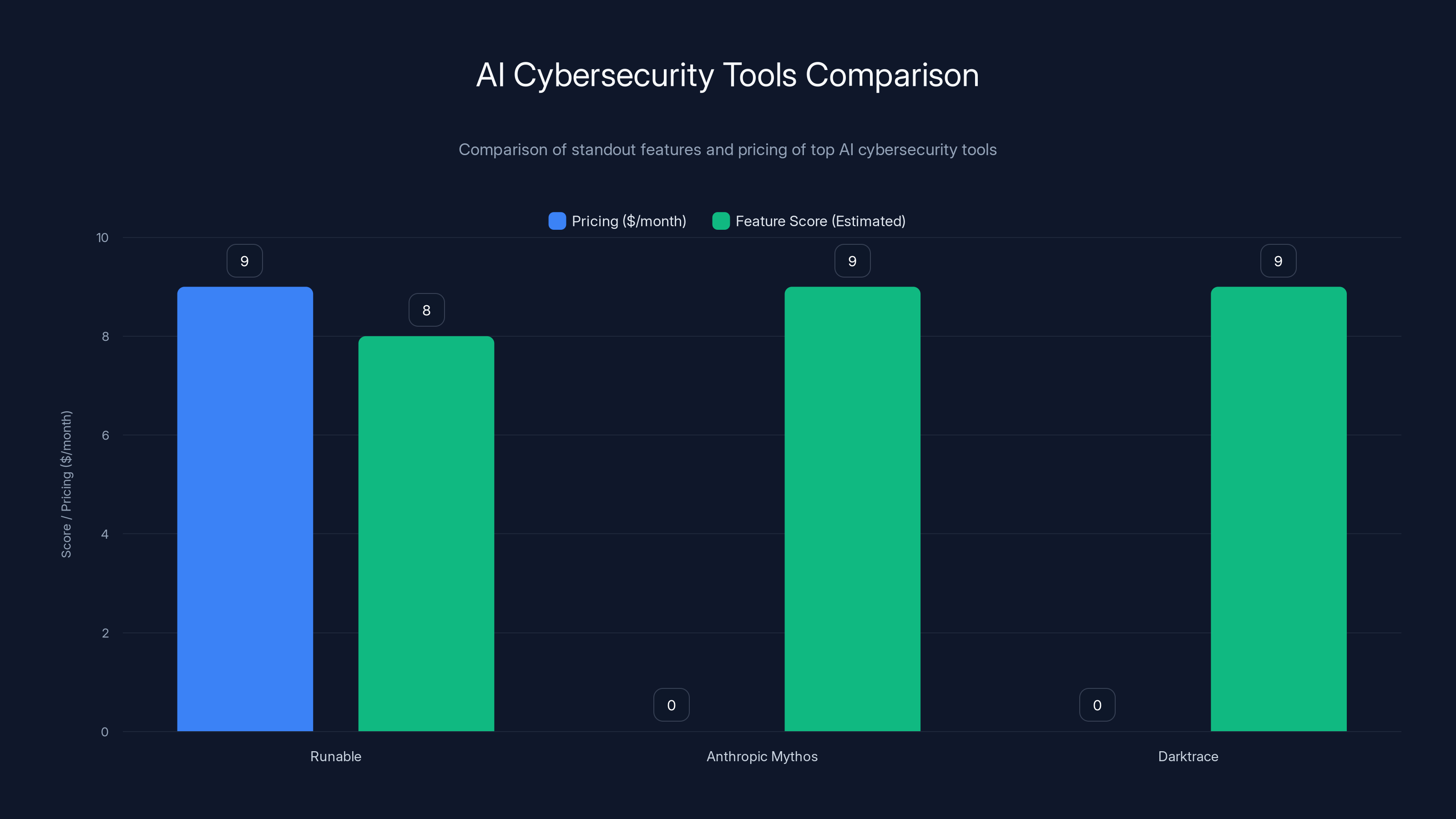
Runable offers affordable pricing at $9/month, while Anthropic Mythos and Darktrace focus on high-end features with custom pricing. Feature scores are estimated based on standout capabilities.
Introduction to AI in Cybersecurity
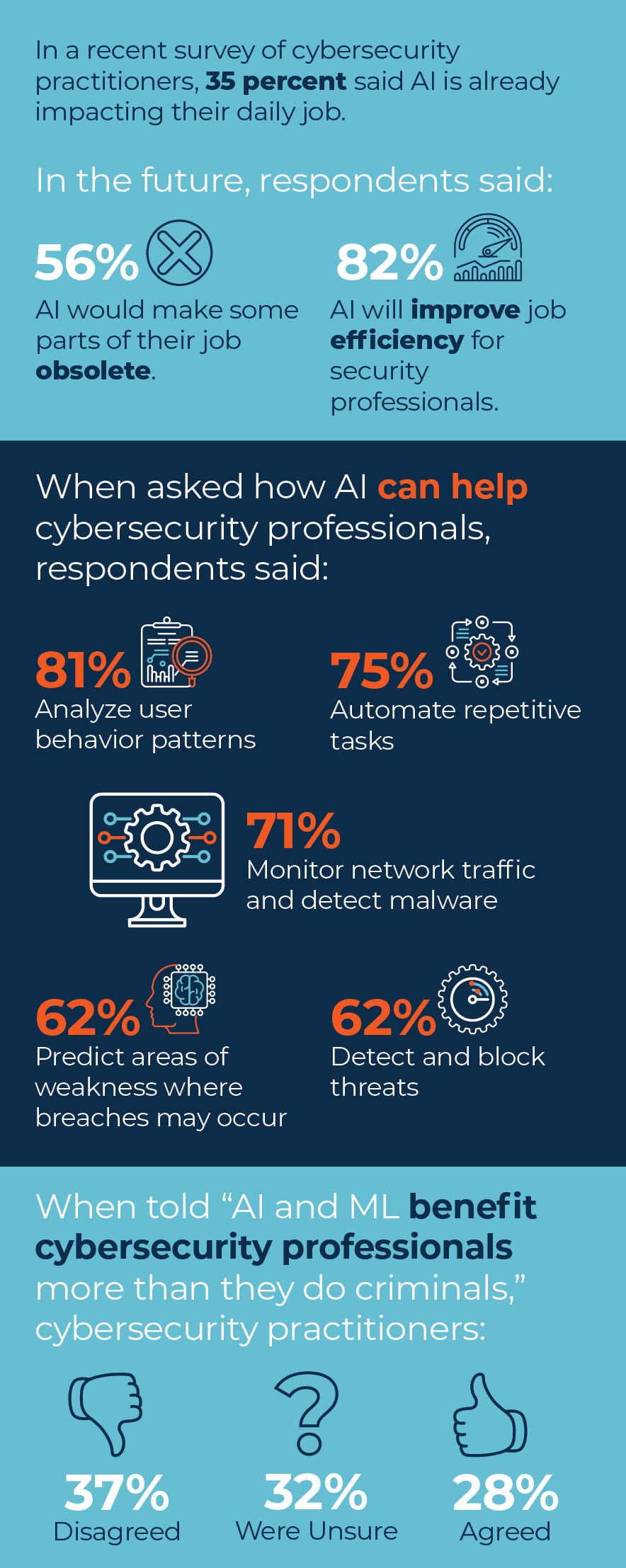
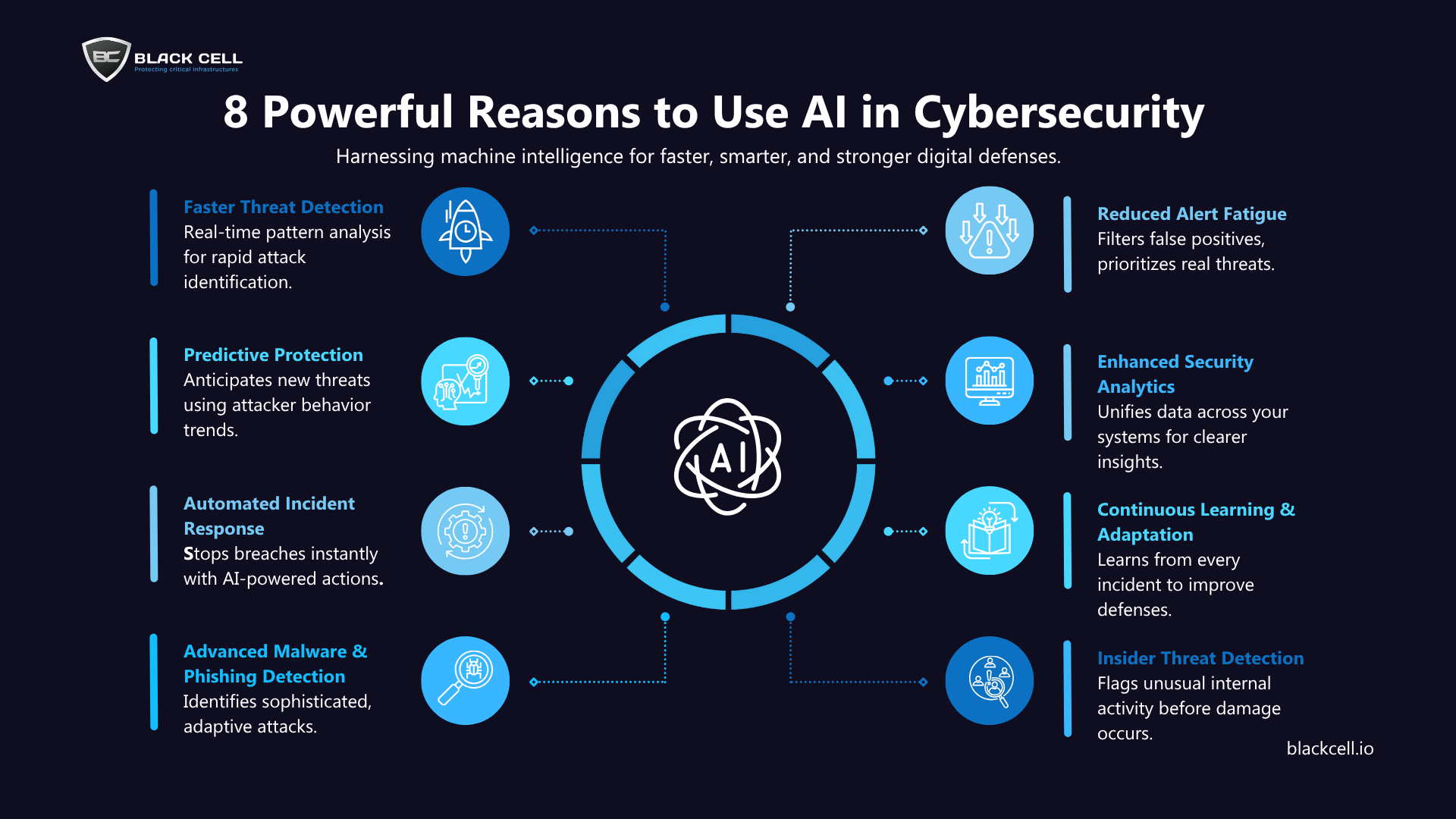
The integration of artificial intelligence (AI) in cybersecurity is a groundbreaking development. With the increasing complexity and volume of cyber threats, traditional methods are often inadequate. AI offers the ability to automate threat detection and response, continuously learning and adapting to new threats.
The Rise of AI Tools
AI-driven cybersecurity tools are becoming essential. They provide real-time analysis and can predict and prevent attacks before they occur. Tools like Anthropic’s Mythos are leading this charge, setting new standards for what AI can achieve in this field.

Mozilla’s Experiment with Mythos
Mozilla’s decision to test Mythos with Firefox was a significant step. The AI was tasked with identifying vulnerabilities within the browser, a complex and critical application used by millions globally.
The Results
Mythos discovered hundreds of vulnerabilities, proving its efficacy. This experiment highlighted AI’s potential to complement human researchers, enhancing the speed and accuracy of vulnerability detection.
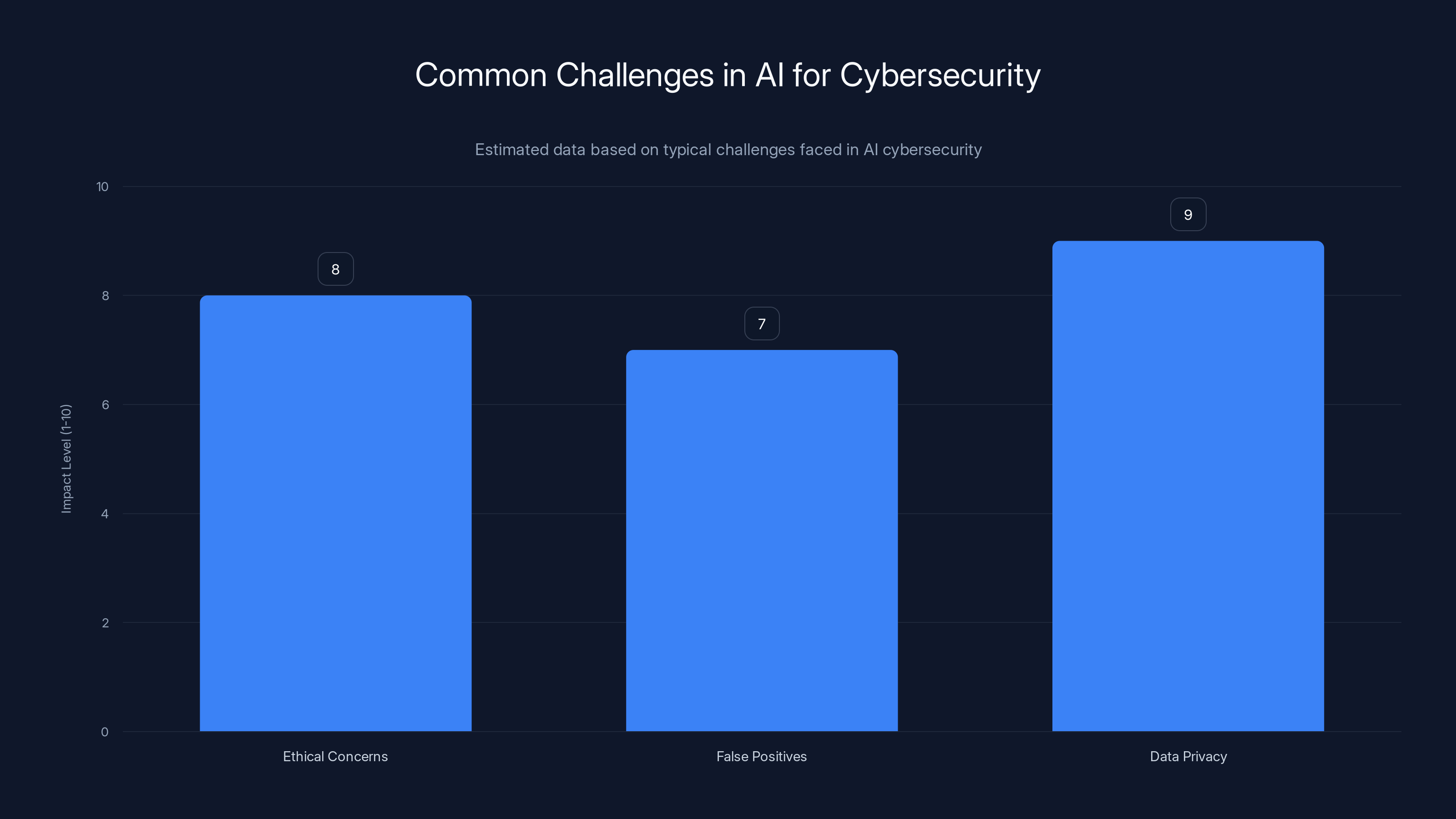
Data privacy poses the highest impact challenge in AI cybersecurity, followed closely by ethical concerns and false positives. (Estimated data)
How AI Detects Vulnerabilities
AI tools analyze vast amounts of data at speeds unattainable by humans. They use machine learning algorithms to identify patterns and anomalies that may indicate a security threat.
Machine Learning in Action
Machine learning models are trained on historical data, learning to recognize the signatures of known threats and predict potential vulnerabilities. Over time, these models improve, becoming more adept at spotting even subtle signs of trouble.

Real-World Use Cases
Use Case 1: Network Security
AI can monitor network traffic, identifying unusual patterns that might suggest an intrusion. For example, Mythos can detect a spike in network activity that aligns with known attack patterns.
Use Case 2: Endpoint Security
On individual devices, AI can detect malware by analyzing behavior rather than relying solely on signatures. This proactive approach allows for the detection of new, unknown malware types.
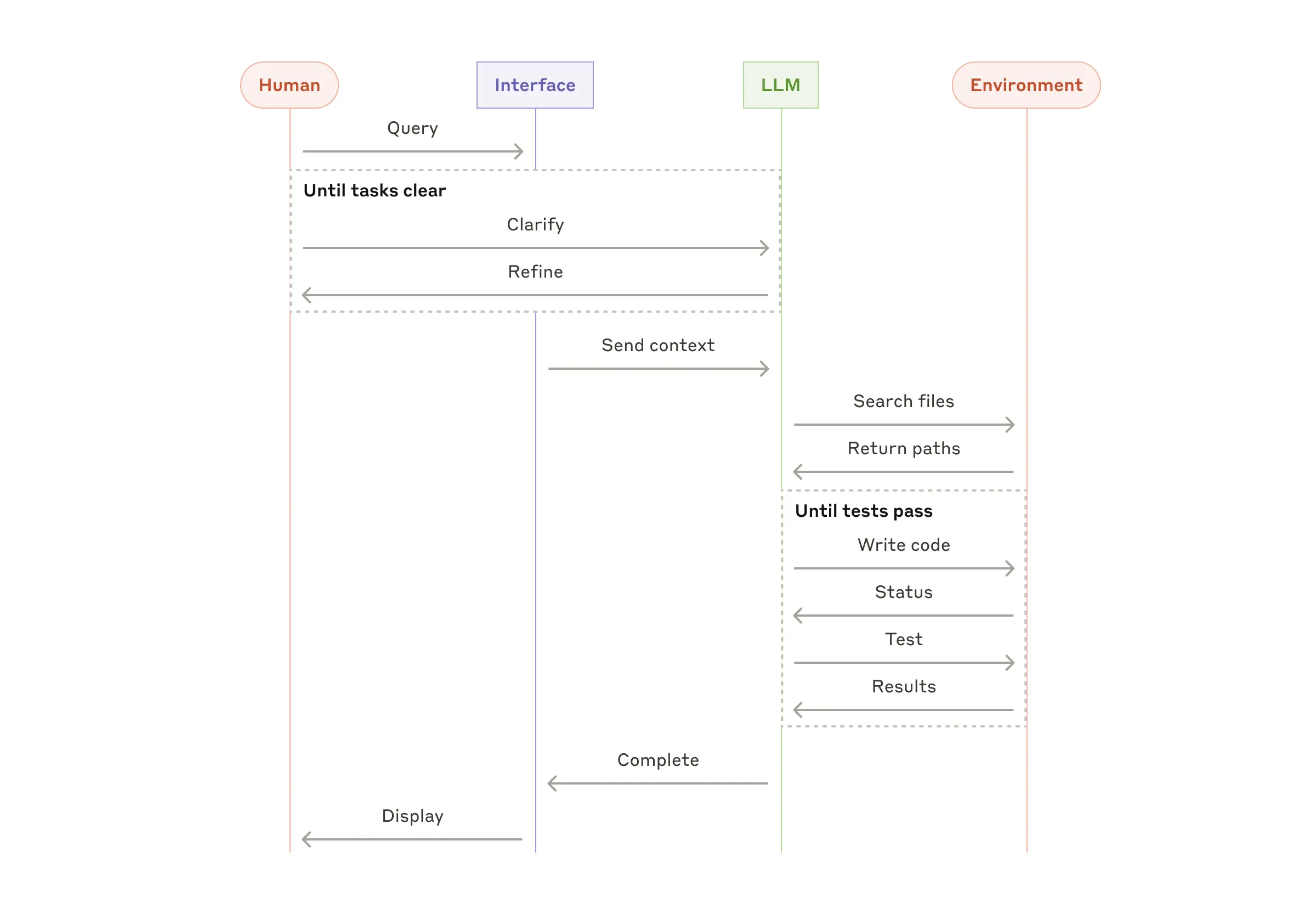
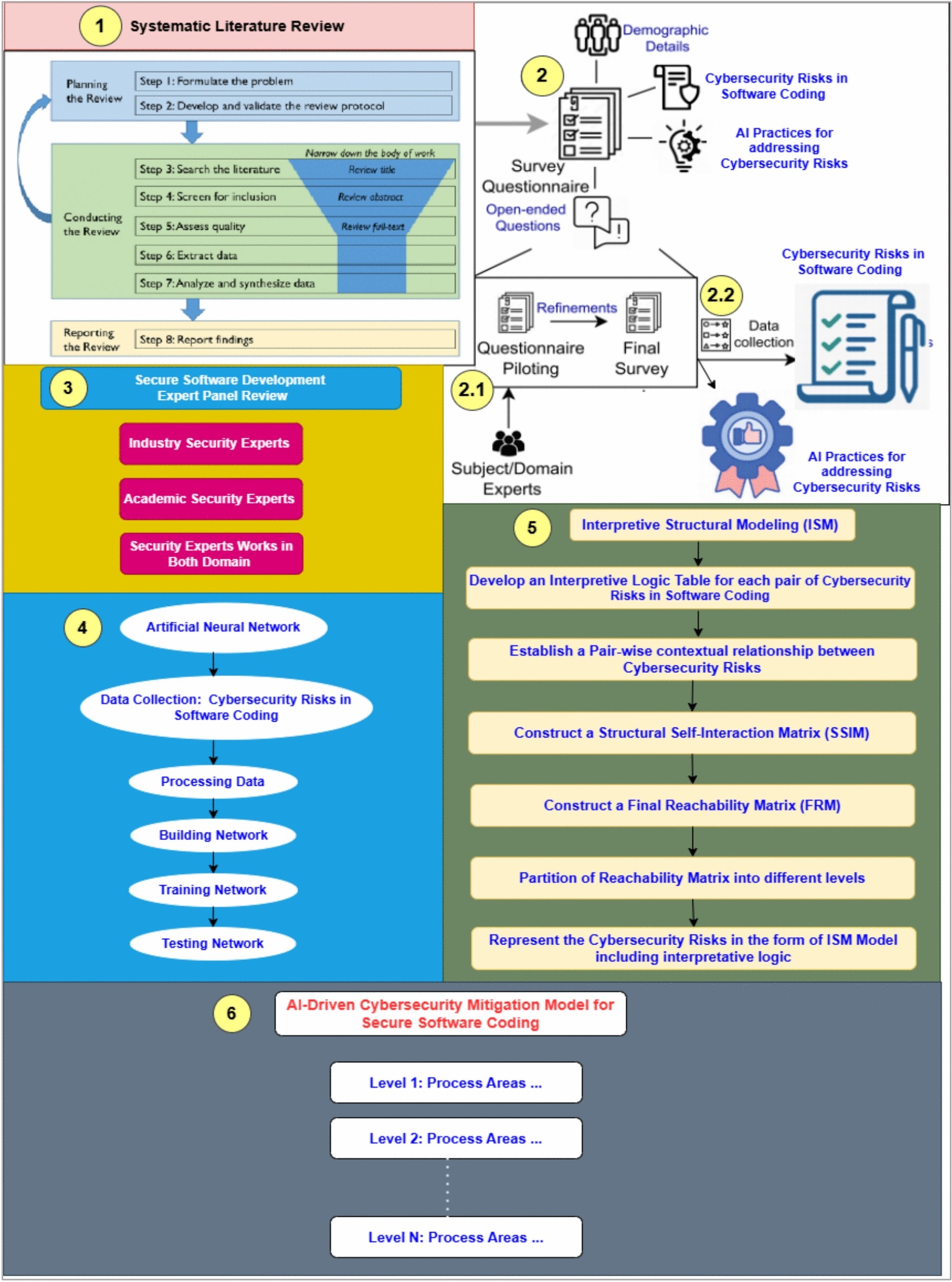
Practical Implementation of AI in Cybersecurity
Step 1: Data Collection
Gathering comprehensive data is crucial. AI systems require vast datasets to train effectively. This includes logs from network traffic, endpoint behavior, and historical attack data.
Step 2: Model Training
Training involves feeding the AI system with this data, allowing it to learn patterns associated with normal and abnormal activities. The quality of the training data directly impacts the effectiveness of the AI.
Step 3: Deployment and Monitoring
Once trained, the AI is deployed in a real-world environment. Continuous monitoring is essential to ensure it adapts to new threats and changing conditions.
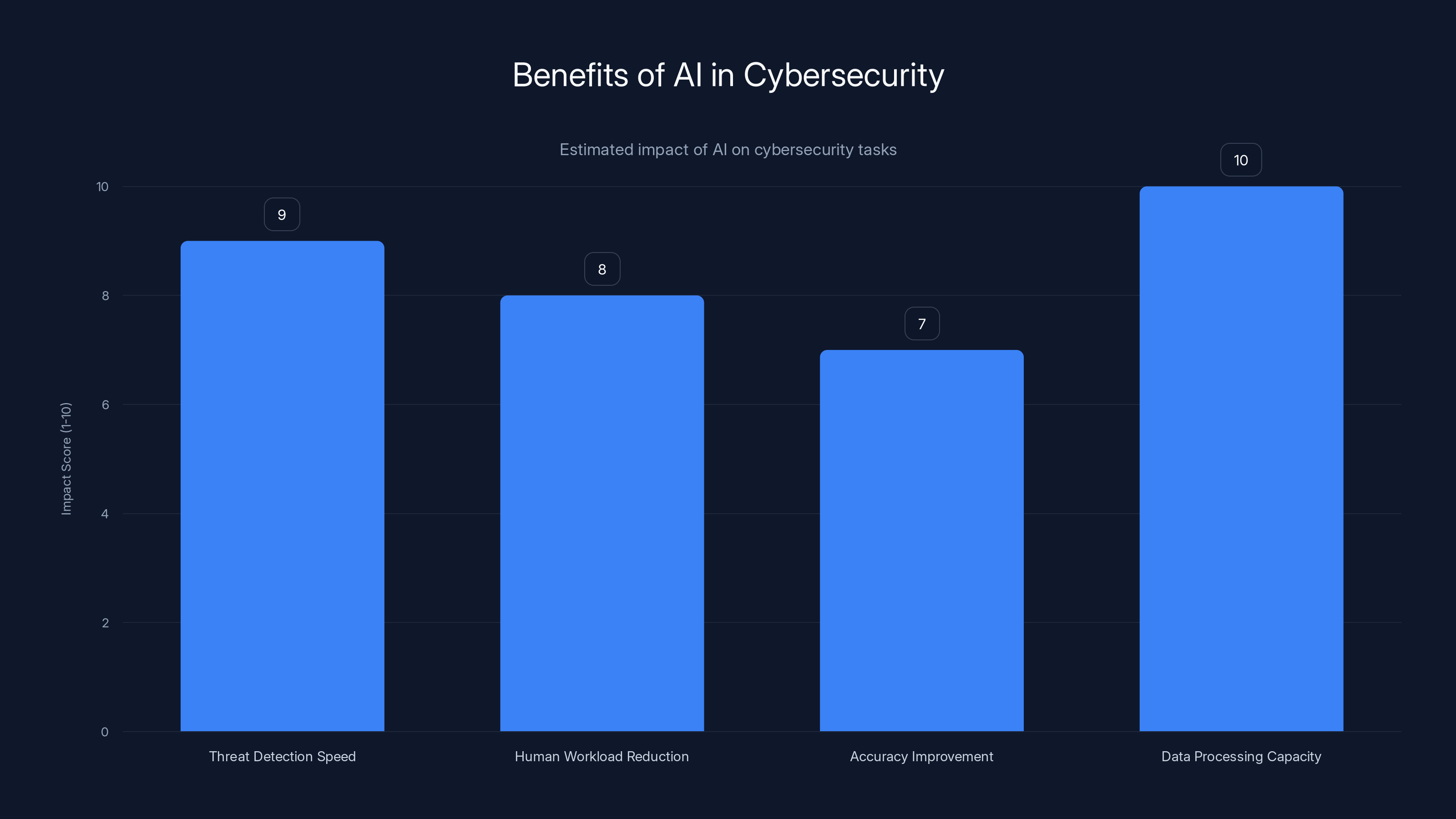
AI significantly enhances threat detection speed and data processing capacity, making it a vital tool in modern cybersecurity. (Estimated data)
Challenges and Pitfalls
Ethical Considerations
The use of AI in cybersecurity raises ethical issues. There’s a risk of misuse, where AI tools could be used for surveillance or to infringe on privacy.
False Positives
AI systems can sometimes generate false positives, misidentifying benign activities as threats. This can lead to unnecessary interventions and wasted resources.
Data Privacy
Training AI requires access to large datasets, which can include sensitive information. Ensuring data privacy and compliance with regulations like GDPR is a critical challenge.

Solutions to Common Challenges
Improving Accuracy
Regular updates and retraining of AI models help improve accuracy. Incorporating feedback loops where human analysts verify AI-generated alerts can reduce false positives.
Balancing Privacy
Data anonymization techniques can help protect privacy while still providing the necessary data for AI training.
Future Trends in AI-Powered Cybersecurity
Increased Automation
As AI tools become more sophisticated, we’ll see increased automation in threat detection and response. This will free human researchers to focus on more complex and strategic tasks.
Enhanced Collaboration
AI will enhance collaboration between security teams by providing shared insights and coordinated responses across different organizations and sectors.
Adaptive Learning
Future AI systems will feature adaptive learning capabilities, allowing them to evolve in real-time as new threats emerge.
Recommendations for Organizations
Start Small
Organizations should start with pilot projects, gradually integrating AI into their existing security frameworks. This allows for testing and refinement before full-scale deployment.
Invest in Training
Investing in training for both AI systems and human personnel is crucial. Security teams need to understand AI’s capabilities and limitations to effectively leverage these tools.
Foster a Culture of Security
Creating a security-first culture within the organization ensures that everyone is aware of and vigilant against potential threats.
Conclusion
AI tools like Anthropic’s Mythos are not just reshaping cybersecurity—they’re redefining it. By matching the capabilities of top human researchers, these tools promise a future where digital threats are identified and neutralized faster than ever before. However, this power comes with responsibilities, and organizations must tread carefully, ensuring ethical use and continual adaptation to new challenges.
FAQ
What is Anthropic’s Mythos?
Anthropic’s Mythos is an AI tool designed to identify vulnerabilities in software and systems, reportedly matching the capabilities of human security researchers.
How does Mythos detect vulnerabilities?
Mythos uses machine learning algorithms to analyze data patterns, identifying anomalies that may indicate security threats.
What are the benefits of using AI in cybersecurity?
Benefits include faster detection of threats, reduced human workload, and improved accuracy in identifying vulnerabilities. AI can process vast amounts of data and learn from each interaction.
What challenges does AI face in cybersecurity?
Challenges include ethical concerns, data privacy issues, and the potential for false positives. Ensuring accurate and ethical use of AI is essential.
How can organizations integrate AI into their cybersecurity systems?
Organizations should start with pilot projects, invest in training, and create a culture of security to effectively integrate AI tools into their cybersecurity systems.
What future trends are expected in AI-powered cybersecurity?
Future trends include increased automation, enhanced collaboration, and adaptive learning capabilities in AI systems.
Why is AI important in cybersecurity?
AI is important because it can handle the massive scale and complexity of modern cyber threats, providing a faster and more comprehensive response than human teams alone.
The Best AI Cybersecurity Tools at a Glance
| Tool | Best For | Standout Feature | Pricing |
|---|---|---|---|
| Runable | AI automation | AI agents for presentations, docs, reports, images, videos | $9/month |
| Anthropic Mythos | Vulnerability detection | Matches top researchers | By request |
| Darktrace | Threat detection | Autonomous response | Custom pricing |
Quick Navigation:
- Runable for AI-powered presentations, documents, reports, images, videos
- Anthropic Mythos for vulnerability detection
- Darktrace for autonomous threat detection
Internal Links
- AI automation guide for workflow optimization insights
- Cybersecurity best practices to enhance your security strategy
- AI presentations to create compelling visual content
Pillar Suggestions
- AI in Cybersecurity for a comprehensive guide on AI integration
- Machine Learning Applications to explore various use cases
- Data Privacy and AI for insights into maintaining privacy in AI systems

Key Takeaways
- AI tools like Mythos are revolutionizing cybersecurity by matching top human researchers.
- Mythos identified numerous vulnerabilities in Firefox, showcasing AI's potential in cybersecurity.
- AI can significantly reduce the time needed to identify zero-day vulnerabilities.
- Integrating AI in cybersecurity requires careful consideration of ethical and data privacy issues.
- Future trends include increased automation and adaptive learning capabilities in AI systems.
Related Articles
- How AI Tools Empower North Korean Hackers to Steal Millions [2025]
- Understanding the French Government Data Breach: Implications, Mitigation, and Future Steps [2025]
- Understanding the Rise of SIM Farms: A Deep Dive into Global Network Exploitation [2025]
- Custom AI Bots: OpenAI's New Frontier for Autonomous Workflow [2025]
- AI Models: The New Generation of Scammers [2025]
- How a Tiny Beam-Steering Chip Could Revolutionize Quantum Computing [2025]
![How AI Like Anthropic’s Mythos is Revolutionizing Cybersecurity [2025]](https://tryrunable.com/blog/how-ai-like-anthropic-s-mythos-is-revolutionizing-cybersecur/image-1-1776940591052.jpg)



