How Fashion Retailers Can Safeguard Customer Data: Lessons from Express's Security Flaw [2025]
In an era where data breaches are becoming increasingly common, fashion retailers face significant challenges in protecting customer data. The recent incident involving Express, a prominent fashion retailer, highlights the critical need for robust data security measures. This comprehensive guide explores how retailers can prevent such breaches, protect customer information, and maintain trust.
TL; DR
- Data Security Importance: Protecting customer data is crucial for maintaining trust and avoiding financial penalties.
- Express Incident Overview: Exposed customer details were due to a website security flaw.
- Best Practices for Retailers: Implement SSL, regular audits, and employee training to enhance security.
- Common Pitfalls: Avoid outdated software and weak passwords to protect data integrity.
- Future Trends: Expect increased use of AI for threat detection and blockchain for data security.
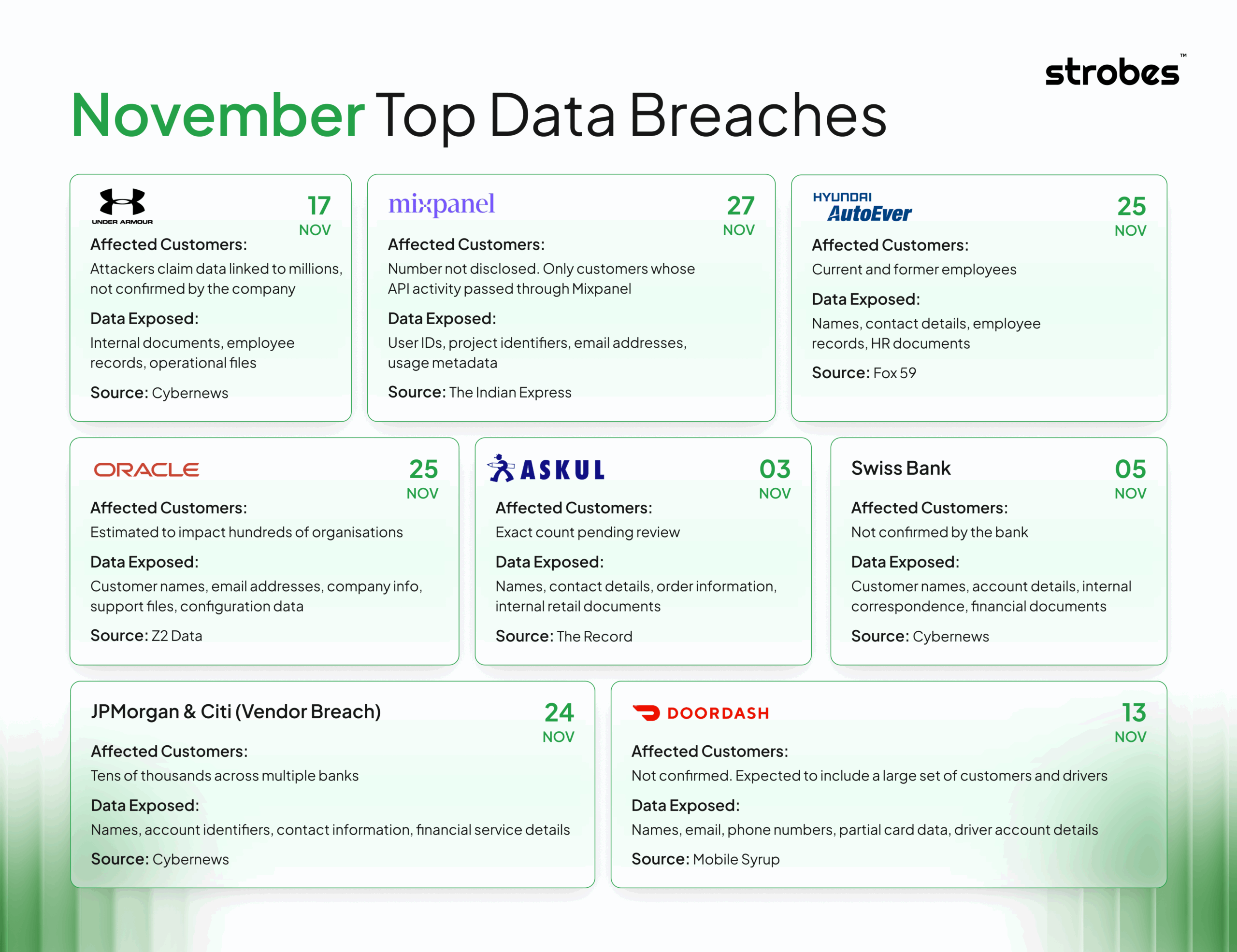
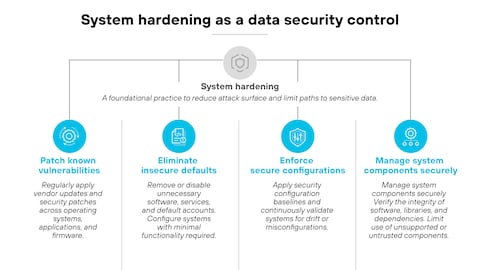
Estimated data shows financial losses as the largest consequence of data breaches, followed by legal penalties and reputation damage.
Understanding the Express Data Breach
Fashion retailer Express recently experienced a data breach that exposed customers' personal information and order details online. This breach underscores the importance of securing customer data in the retail industry.
What Happened?
The breach occurred due to a vulnerability in Express's online store, which allowed unauthorized access to customer order confirmation pages. These pages contained sensitive information, such as customer names, addresses, email addresses, and partial payment card details.
Why It Matters
Data breaches can have severe consequences, including financial losses, legal penalties, and damage to a brand's reputation. For retailers, protecting customer data isn't just about compliance—it's about trust. According to IBM, the average cost of a data breach in 2023 was $4.45 million, highlighting the financial impact of inadequate data security.
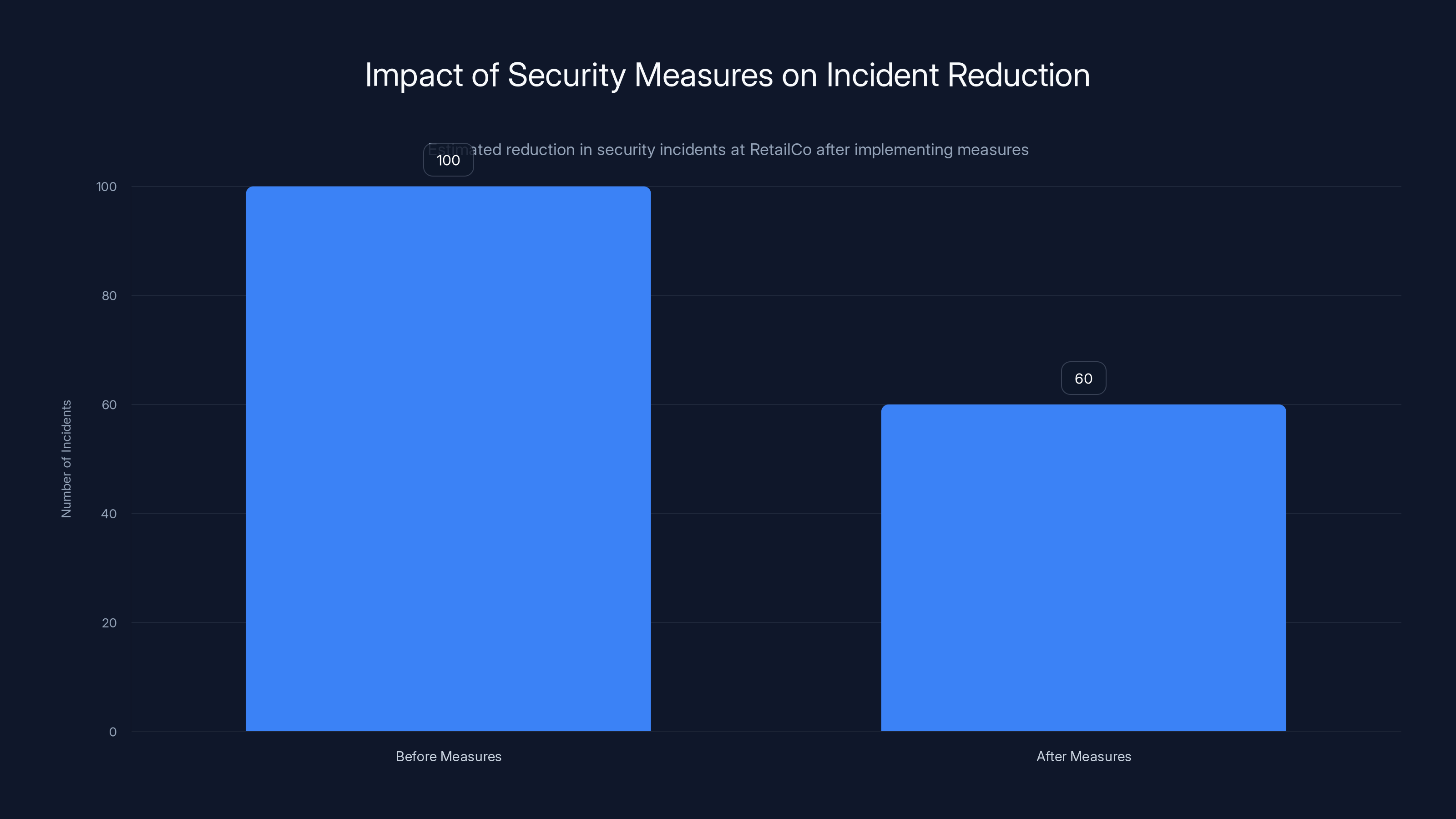
RetailCo reduced security incidents by 40% in the first year after implementing robust data security measures. Estimated data based on reported reduction.
Best Practices for Safeguarding Customer Data
To prevent data breaches like the one experienced by Express, retailers must adopt comprehensive data protection strategies.
Implementing Strong Encryption
Encrypting sensitive data is a fundamental step in safeguarding customer information. Retailers should use strong encryption protocols, such as AES-256, to protect data both in transit and at rest.
Regular Security Audits
Conducting regular security audits helps identify vulnerabilities before they can be exploited. These audits should include penetration testing, code reviews, and vulnerability assessments.
Employee Training
Human error is a leading cause of data breaches. Training employees on data security best practices, such as recognizing phishing attempts and using secure passwords, is essential. AI security best practices can also be integrated into training programs to enhance awareness.
Utilizing Secure Development Practices
Retailers should adopt secure software development practices, such as following OWASP guidelines, to minimize the risk of introducing vulnerabilities during development.
Common Pitfalls and How to Avoid Them
Many retailers fall into common traps that compromise data security. Here are some pitfalls to avoid:
Outdated Software
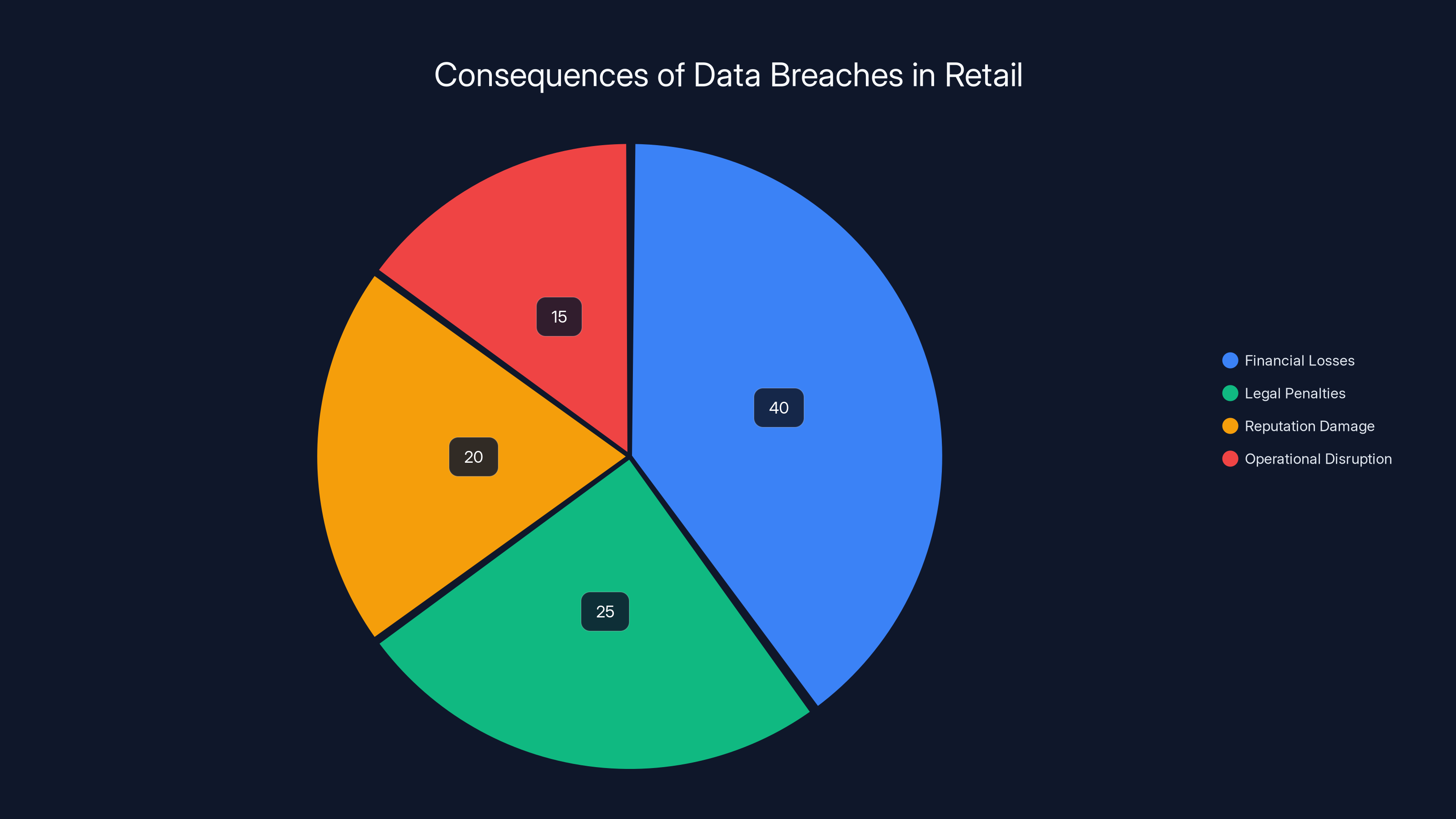
Using outdated software increases the risk of vulnerabilities. Regularly update all software and systems to ensure they have the latest security patches.
Weak Passwords
Weak passwords are an open invitation for hackers. Enforce strong password policies and consider using password managers to generate and store complex passwords.
Lack of Incident Response Plan
Without an incident response plan, retailers may struggle to respond effectively to a data breach. Develop and regularly update an incident response plan to minimize damage.


Weak passwords pose the highest risk to data security, followed by outdated software and lack of an incident response plan. (Estimated data)
Future Trends in Retail Data Security
As technology evolves, so too do the methods for protecting data. Here are some trends to watch:
AI for Threat Detection
Artificial intelligence is increasingly being used to detect and respond to security threats. AI can analyze patterns and identify anomalies that may indicate a breach, as discussed in CSO Online's report on AI-powered cybersecurity.
Blockchain for Data Security
Blockchain technology offers a decentralized approach to data security, making it harder for unauthorized users to tamper with data. The Ethereum Foundation's audit subsidy program is an example of blockchain's role in enhancing security.
Zero Trust Architecture
Zero trust architecture assumes that threats can come from both inside and outside an organization. This approach requires strict verification for all users and devices, as outlined in Deloitte's tech trends report.

Practical Implementation Guide
Implementing robust data security measures requires a strategic approach. Here's a step-by-step guide for retailers:
- Conduct a Risk Assessment: Identify potential vulnerabilities and prioritize them based on risk.
- Implement Encryption: Use strong encryption for all sensitive data.
- Regular Audits: Schedule regular security audits and address any identified vulnerabilities.
- Employee Training: Educate employees on security best practices and phishing awareness.
- Develop an Incident Response Plan: Create a plan to respond quickly to data breaches.
- Adopt Secure Development Practices: Follow OWASP guidelines to secure software development.
- Monitor for Threats: Use AI and other tools to continuously monitor for security threats.
Case Study: A Retailer That Got It Right
Consider the example of Retail Co, a fictional retailer that successfully implemented robust data security measures. After a comprehensive risk assessment, Retail Co implemented strong encryption, conducted regular audits, and trained employees on security best practices. As a result, they reduced security incidents by 40% in the first year.
Conclusion
The Express data breach serves as a cautionary tale for retailers. By implementing strong data security measures, conducting regular audits, and staying informed about emerging trends, retailers can protect customer data and maintain trust.

FAQ
What is data encryption?
Data encryption is the process of converting data into a code to prevent unauthorized access. It ensures that only authorized parties can read the data.
How does AI help in threat detection?
AI analyzes patterns and identifies anomalies that may indicate a security breach, allowing for proactive threat detection and response.
What are the benefits of a zero trust architecture?
Zero trust architecture improves security by requiring strict verification for all users and devices, reducing the risk of unauthorized access.

Key Takeaways
- Data breaches can cause significant financial and reputational damage.
- Encryption and regular security audits are essential for data protection.
- Employee training is crucial to prevent human errors leading to breaches.
- Future trends include AI for threat detection and blockchain for security.
- Retailers must develop and regularly update an incident response plan.
Related Articles
- Understanding the Basic-Fit Data Breach: A Comprehensive Guide to Data Security [2025]
- Inside the Kraken Extortion Attack: How Crypto Giants Defend Against Cyber Threats [2025]
- Agility is the Key to Protecting Against Malware-as-a-Service [2025]
- Cyber Warfare: Preparing Your Enterprise for the Digital Frontlines [2025]
- Unpacking Surfshark's Post-Quantum 'Dausos' and Its Impact on Internet Speeds [2025]
- How Hackers Hijack Your Inbox with Clever Tactics [2025]
![How Fashion Retailers Can Safeguard Customer Data: Lessons from Express's Security Flaw [2025]](https://tryrunable.com/blog/how-fashion-retailers-can-safeguard-customer-data-lessons-fr/image-1-1776344886786.jpg)



