Inside Europol's Operation Power OFF: A Game-Changer in Combating DDoS-for-Hire Services [2025]
Last year, Europol launched Operation Power OFF, a groundbreaking initiative aimed at dismantling the growing menace of DDoS-for-hire services. This comprehensive operation spanned 21 countries, resulting in the arrest of four individuals, the seizure of 53 domains, and the execution of 25 search warrants. Remarkably, authorities discovered 3 million criminal accounts associated with these services, issuing warnings to 75,000 users.
TL; DR
- DDoS-for-hire services: Europol dismantled 53 domains and warned 75,000 users.
- Global Impact: The operation spanned 21 countries, showcasing international cooperation.
- Arrests and Seizures: Four people were arrested, and multiple assets seized, disrupting the DDoS ecosystem.
- Future Trends: Enhanced AI-based detection and international collaboration are pivotal.
- Bottom Line: Operation Power OFF marks a significant milestone in curbing cybercrime.

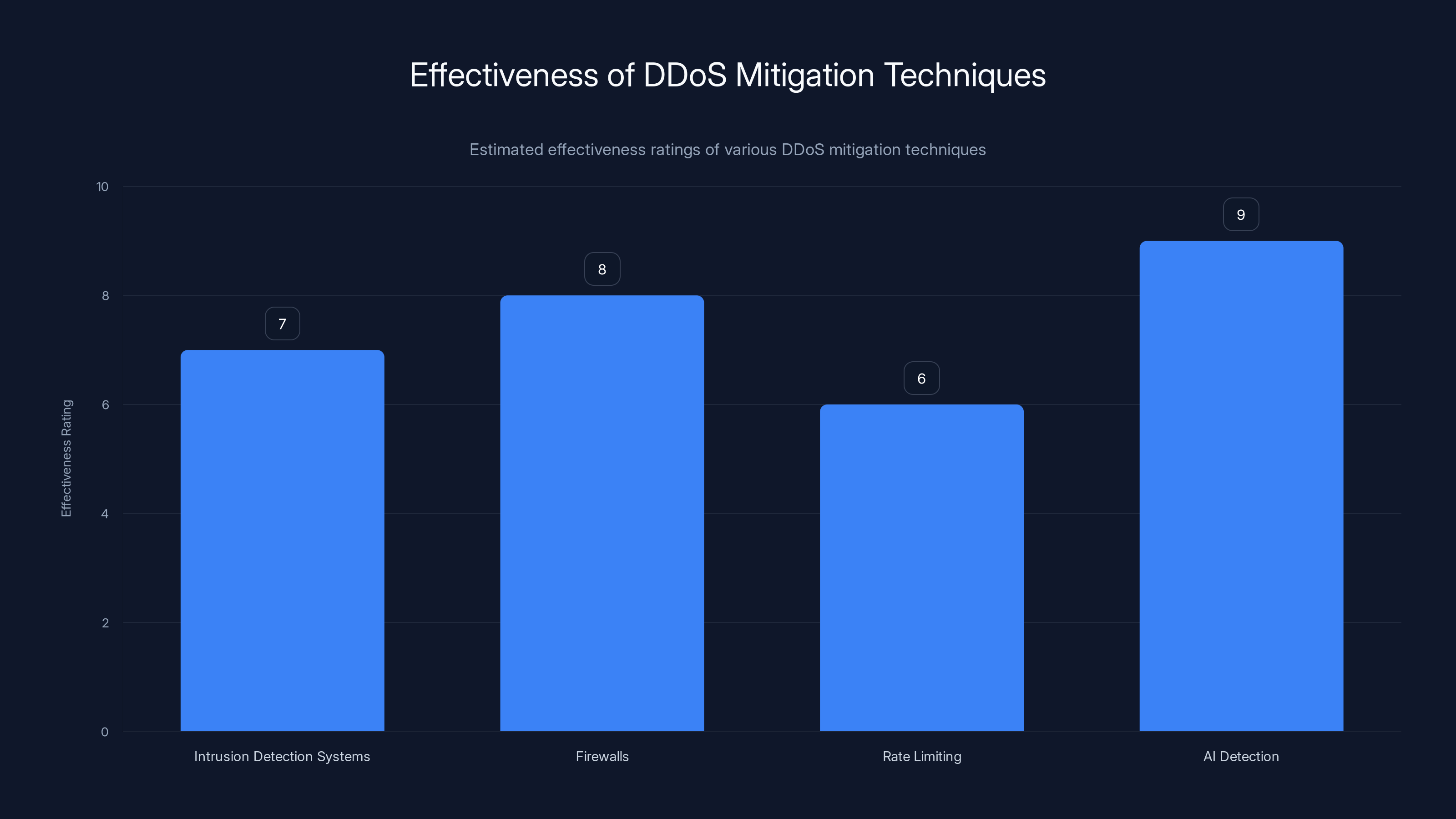
AI Detection is estimated to be the most effective technique with a rating of 9/10, highlighting its potential in real-time DDoS mitigation. (Estimated data)
The Rise of DDoS-for-Hire Services
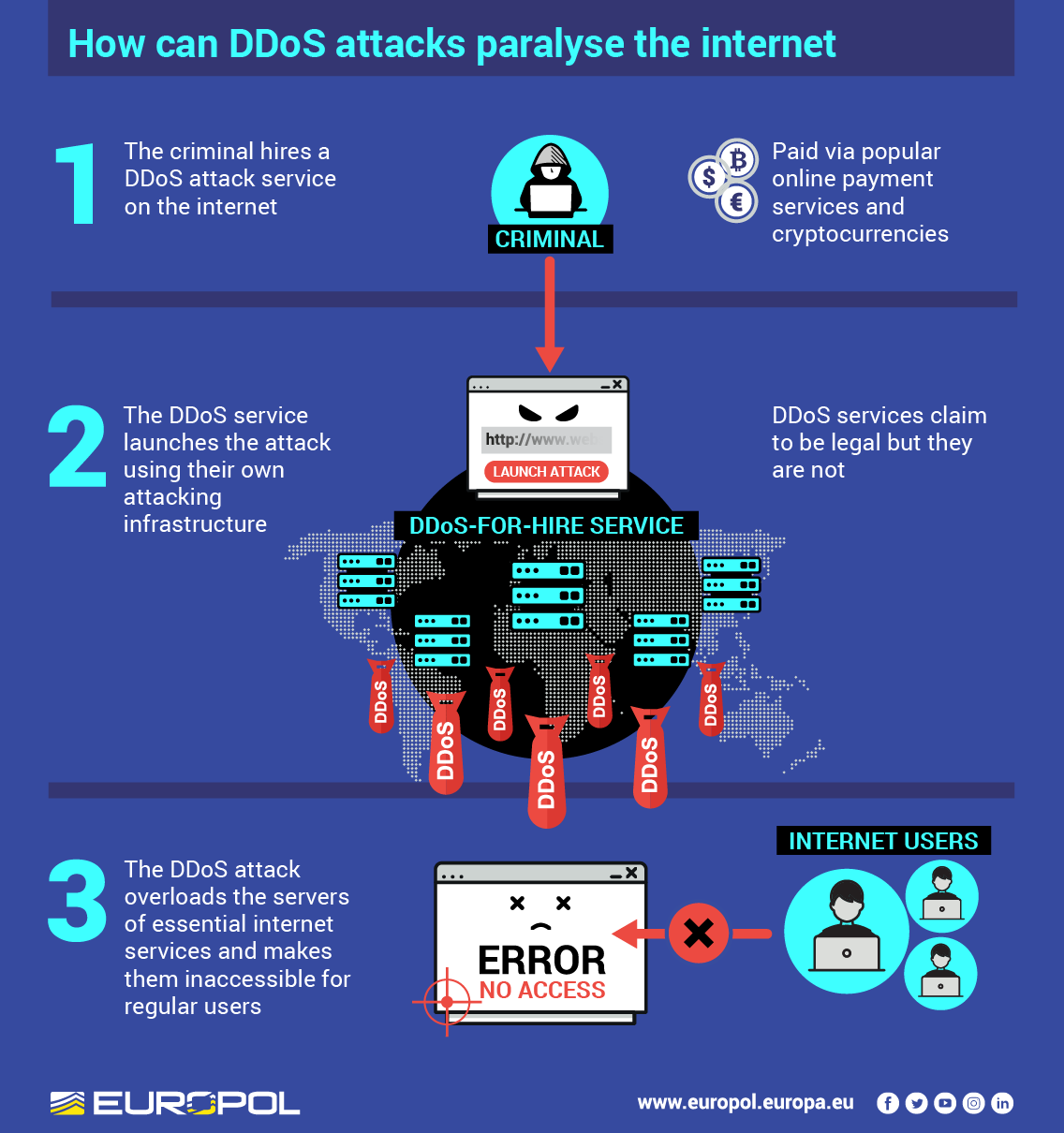
DDoS-for-hire services, often referred to as booters or stressers, provide malicious actors with the tools to launch Distributed Denial of Service (DDoS) attacks without needing technical expertise. For as little as $10 a month, anyone can purchase these services to flood a target's network with traffic, rendering it inaccessible.
Understanding DDoS Attacks
A DDoS attack involves overwhelming a server, service, or network with a flood of internet traffic. These attacks exploit multiple compromised computer systems to target a single system, causing a denial of service for users.
How DDoS-for-Hire Works
These services typically operate through a web-based interface where users can select their target, choose the attack duration, and execute the attack with just a few clicks. Payment is often made using cryptocurrencies to maintain anonymity.

Operation PowerOFF significantly disrupted DDoS-for-hire services by seizing 53 domains, warning 75,000 users, and arresting 4 key individuals.
Operation Power OFF: A Coordinated Global Effort
Europol's Operation Power OFF was no ordinary crackdown. It was a meticulously planned operation involving law enforcement agencies from 21 countries. This international collaboration was crucial for targeting and dismantling the infrastructure supporting DDoS-for-hire services.
Key Achievements of Operation Power OFF
- 53 domains seized: These domains were central to the operation of DDoS-for-hire services, and their seizure has significantly disrupted the market.
- 75,000 users warned: Authorities issued warnings to users of these services, highlighting the legal consequences of their actions.
- Four arrests made: The operation led to the arrest of key individuals behind these services, dealing a significant blow to the DDoS ecosystem.
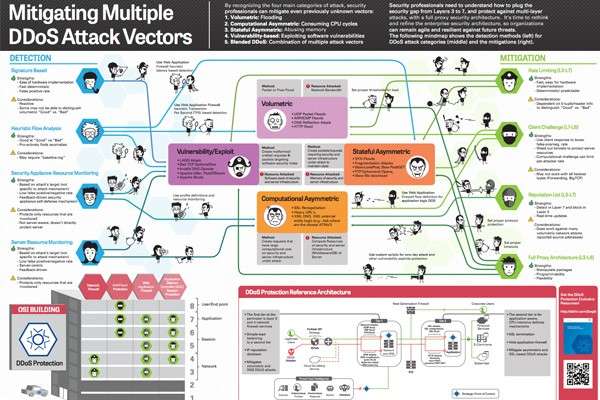
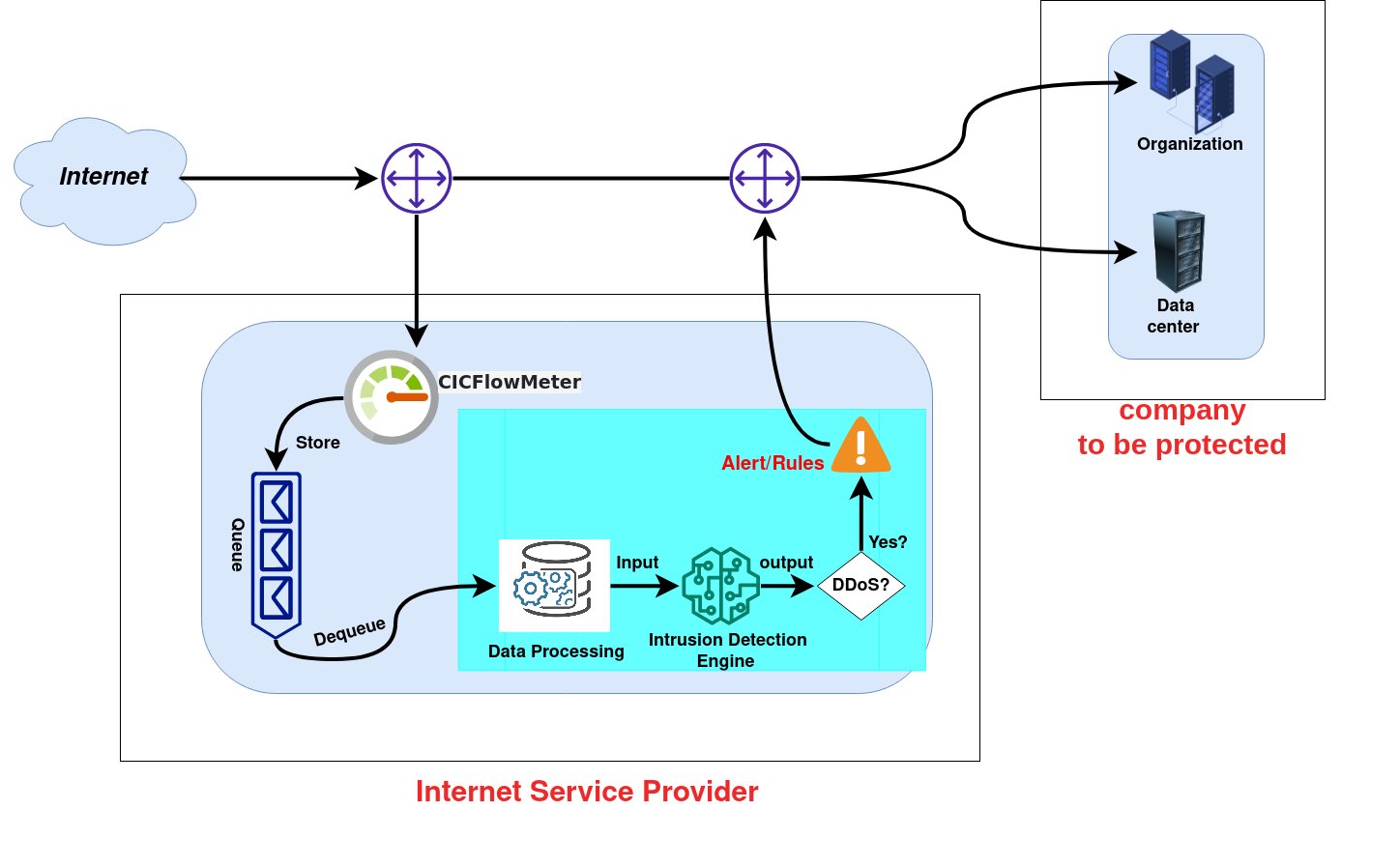
Technical Insights into DDoS Mitigation
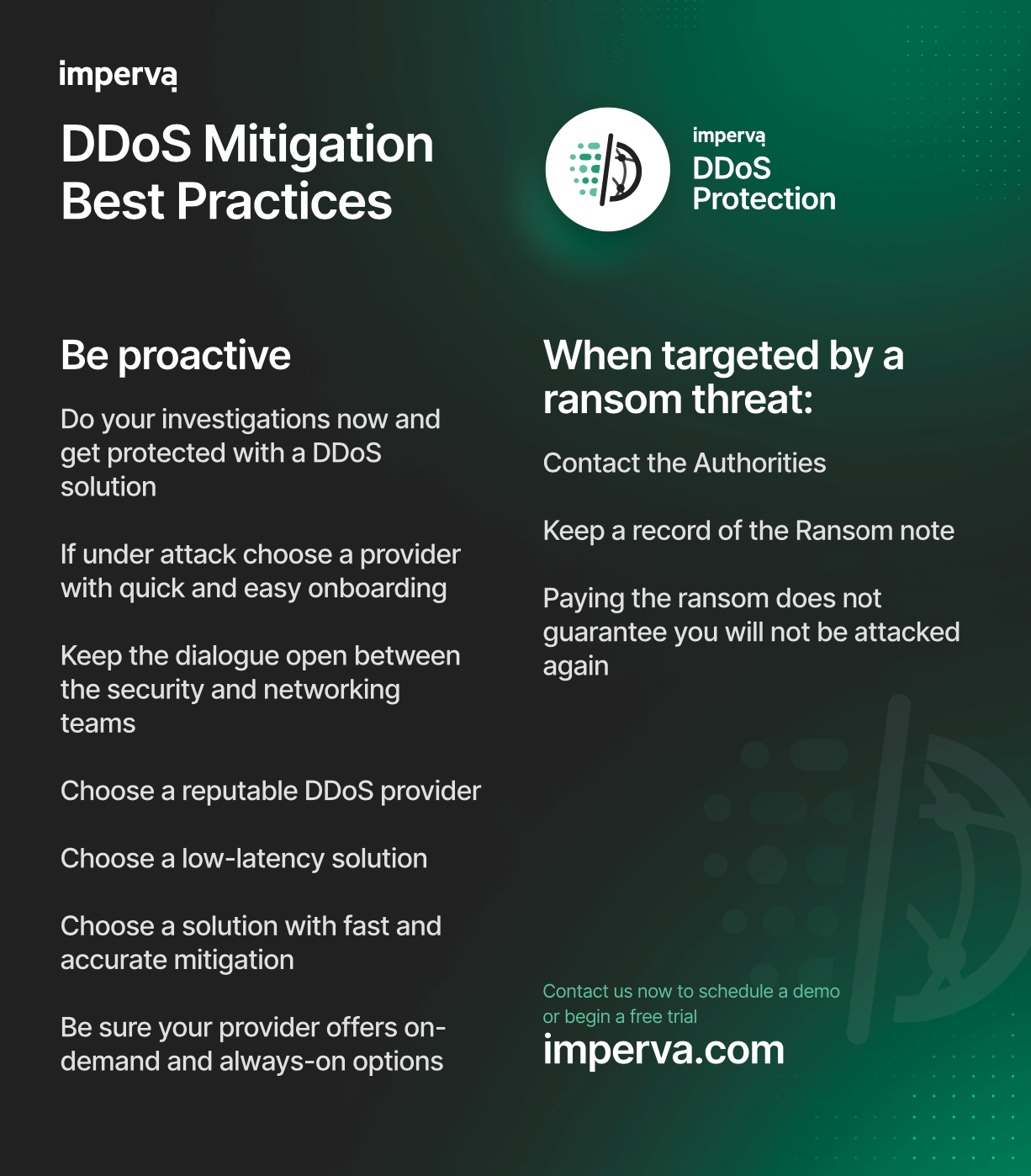
Tackling DDoS attacks requires a multi-faceted approach that combines technology, strategy, and collaboration.
Implementing Robust Network Security
- Intrusion Detection Systems (IDS): Deploy IDS to monitor network traffic for suspicious activity and potential threats.
- Firewalls: Use advanced firewalls configured to filter and block malicious traffic.
- Rate Limiting: Implement rate limiting to control the amount of incoming traffic.
Leveraging AI for DDoS Detection
AI and machine learning algorithms can analyze vast amounts of network data to identify patterns indicative of a DDoS attack. By training models on historical data, AI can accurately predict and mitigate attacks in real-time.
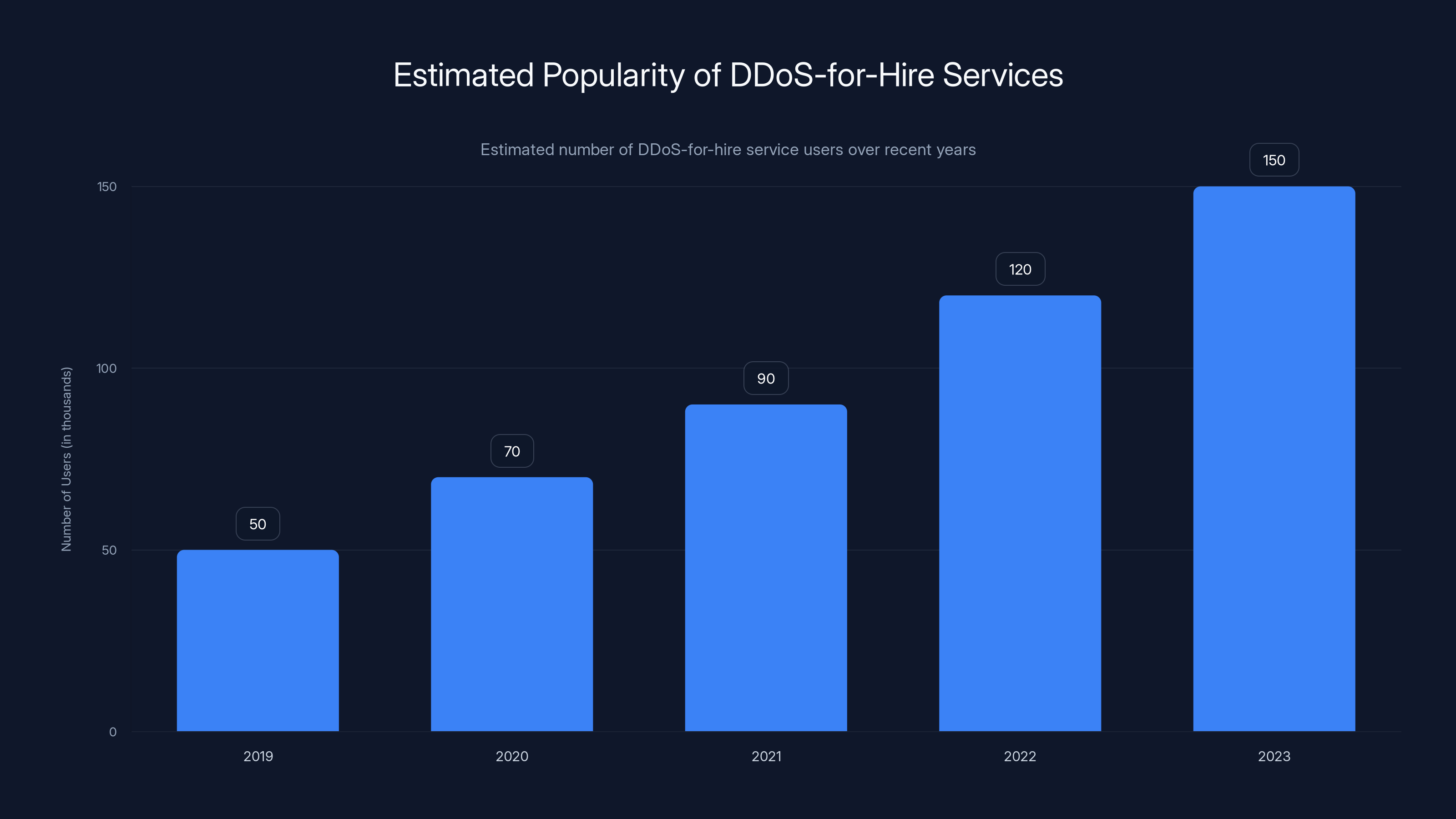
The popularity of DDoS-for-hire services has seen a significant rise, with an estimated 150,000 users in 2023. Estimated data.
Real-World Examples and Case Studies
The Attack on Dyn
In October 2016, a massive DDoS attack targeted Dyn, a company that manages domain name services. This attack disrupted major websites including Amazon, Twitter, and Netflix. It highlighted the vulnerability of centralized services and the far-reaching impact of DDoS attacks.
Lessons from the Mirai Botnet
The Mirai botnet exploited IoT devices to launch one of the largest DDoS attacks in history. This event underscored the importance of securing IoT devices and updating firmware to prevent exploitation.
Common Pitfalls and Solutions in DDoS Defense
Over-Reliance on Single Solutions
Relying solely on firewalls or IDS can create a false sense of security. A layered defense strategy that includes multiple security measures is more effective.
Neglecting Employee Training
Human error remains a significant vulnerability. Regularly train employees on identifying phishing attempts and other security threats.
Future Trends in DDoS Mitigation
Enhanced AI and Machine Learning
AI will continue to evolve, offering more sophisticated methods for detecting and mitigating DDoS attacks. Expect AI algorithms that can adapt to new attack vectors in real-time.
Increased Government Collaboration
Operation Power OFF demonstrated the power of international cooperation. Future efforts will likely involve more joint operations and information-sharing agreements between countries.
The Role of Cloud-Based Solutions
Cloud-based DDoS protection services offer scalability and flexibility, allowing businesses to defend against attacks without investing in expensive hardware.

Recommendations for Businesses
Conduct Regular Security Audits
Regular audits can help identify vulnerabilities in your network infrastructure. Ensure that all systems are patched and up-to-date.
Develop a Response Plan
Having a detailed response plan in place can minimize downtime and damage during a DDoS attack. This plan should include communication strategies, technical response procedures, and roles and responsibilities.
Engage with Professional Security Services
Consider partnering with managed security service providers (MSSPs) who specialize in DDoS mitigation.
Conclusion: The Impact of Operation Power OFF
Operation Power OFF is a landmark achievement in the fight against cybercrime. By dismantling the infrastructure of DDoS-for-hire services, Europol has dealt a significant blow to cybercriminals, setting a precedent for future operations.
As businesses and individuals become more aware of the risks associated with DDoS attacks, the demand for advanced security solutions will continue to grow. Increased collaboration between governments, law enforcement, and the private sector will be essential in creating a safer digital environment.
FAQ
What is a DDoS attack?
A DDoS attack is an attempt to make an online service unavailable by overwhelming it with traffic from multiple sources.
How can I protect my business from DDoS attacks?
Implement network security measures such as firewalls and IDS, conduct regular security audits, and develop a response plan.
What was Operation Power OFF?
Operation Power OFF was an international effort led by Europol to dismantle DDoS-for-hire services, resulting in arrests and domain seizures.
Why are DDoS-for-hire services popular?
They offer an easy and affordable way for non-technical users to launch DDoS attacks, often with anonymity via cryptocurrency payments.
What are the legal consequences of using DDoS-for-hire services?
Using these services is illegal and can result in criminal charges, fines, and imprisonment.
What future trends are expected in DDoS mitigation?
Expect advancements in AI-driven detection, increased international collaboration, and the rise of cloud-based defense solutions.
Key Takeaways
- Europol's Operation PowerOFF dismantled 53 DDoS-for-hire domains.
- 75,000 users were warned, highlighting the scale of the threat.
- AI and machine learning are crucial for future DDoS detection.
- International collaboration is key in combating cybercrime.
- Businesses should implement multi-layered defense strategies.
- Cloud-based DDoS protection offers scalable defense solutions.
Related Articles
- Cyber Warfare: Preparing Your Enterprise for the Digital Frontlines [2025]
- Stay Safe from iCloud Phishing Scams: What Every Apple User Needs to Know [2025]
- 'Trusted Access for the Next Era of Cyber Defense': OpenAI's Cybersecurity Revolution [2025]
- How FIFA World Cup Partners Could Be Exposing Fans to Email Attacks: An In-Depth Analysis [2025]
- Anthropic's Security Flaws: A Deep Dive into MCP Vulnerabilities [2025]
- Understanding the Complexities of Prompt Injection Vulnerabilities in AI Systems [2025]
![Inside Europol's Operation PowerOFF: A Game-Changer in Combating DDoS-for-Hire Services [2025]](https://tryrunable.com/blog/inside-europol-s-operation-poweroff-a-game-changer-in-combat/image-1-1776418491995.jpg)



