Inside Southeast Asian Scam Compounds: The Crypto Fraud Crisis [2025]
It started with an email from someone calling themselves Red Bull. The message came through an encrypted service at midnight, and what it contained would pull me into a months-long investigation into one of the largest and most brutal crime networks operating today.
Let me set the scene: a legitimate journalist receives an email from someone claiming to be trapped inside a major cryptocurrency romance scam operation in the Golden Triangle region of Southeast Asia. They say they're a computer engineer, forced to work there, passport confiscated. They have documents. They want out. And they're willing to expose everything.
Here's the problem. This scenario sounds almost too perfectly dramatic to be real. Yet it is. And what makes it genuinely disturbing isn't just the individual story of one whistleblower—it's the industrial machine he's trying to expose.
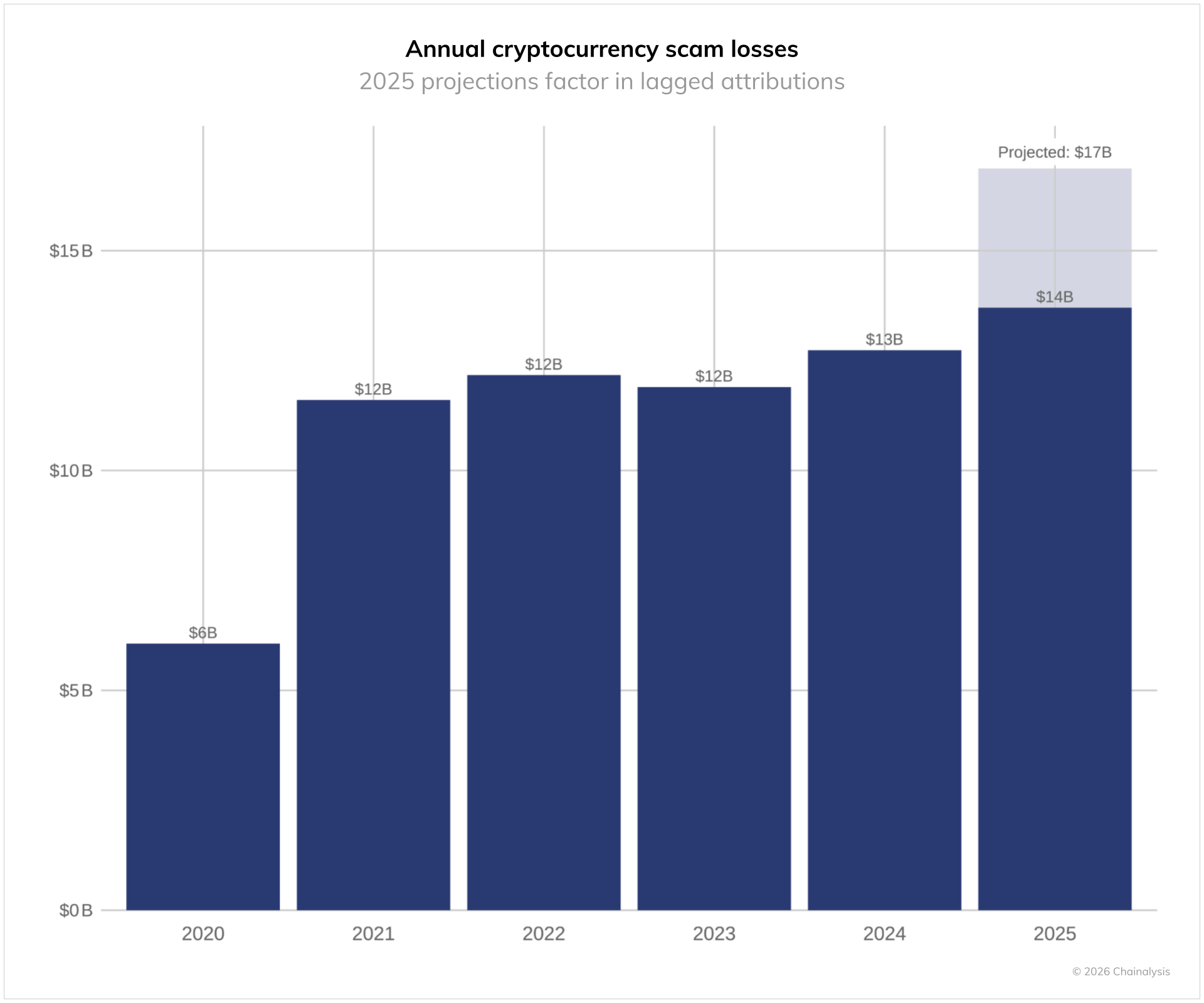
The pig butchering scam industry (that's the actual term used by law enforcement and cybercriminals) has become the single most profitable form of cybercrime in existence. We're talking tens of billions of dollars annually being extracted from victims, primarily across the United States and India. The victims lose their life savings. The perpetrators? They're mostly forced laborers in compounds across Myanmar, Cambodia, and Laos, trafficked from the poorest regions of Asia and Africa, working under conditions that constitute modern slavery.
But here's what's different about this story: it's not coming from a survivor who escaped. It's coming from someone still inside. Someone willing to document the entire operation while he figures out how to get out alive.
TL; DR
- Romance scams cost victims $1.3 billion annually in the US alone, with global totals in the tens of billions
- Hundreds of thousands of forced laborers are trafficked to Southeast Asian compounds to carry out these scams
- Whistleblowers from inside compounds are extremely rare, making this investigation unprecedented
- The scam industry operates with sophisticated infrastructure including fake profiles, AI deepfakes, and fake investment platforms
- Escape from these compounds is dangerous, requiring coordination with law enforcement and journalists

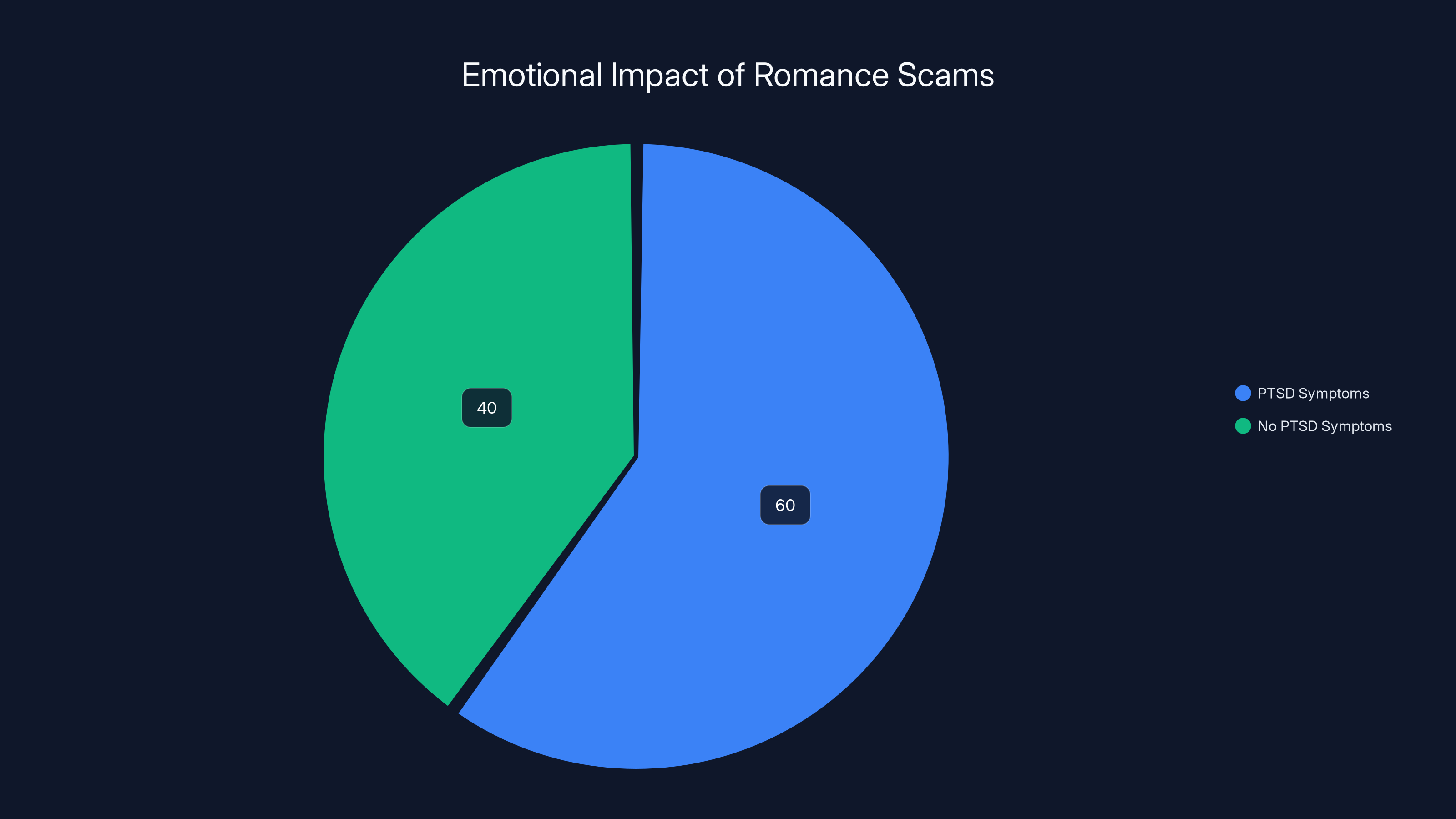
Approximately 60% of romance scam victims who lose significant amounts experience long-term PTSD symptoms, highlighting the severe emotional impact beyond financial loss.
Understanding Pig Butchering: The Deadliest Scam You've Never Heard Of
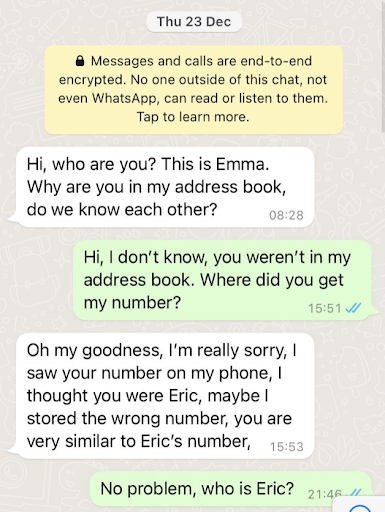
If you've been on dating apps in the last five years, you've probably encountered someone who seemed too perfect. Too attractive. Too interested. Too willing to shift to messaging apps and talk about investments.
That's pig butchering. And it's called that for a reason.
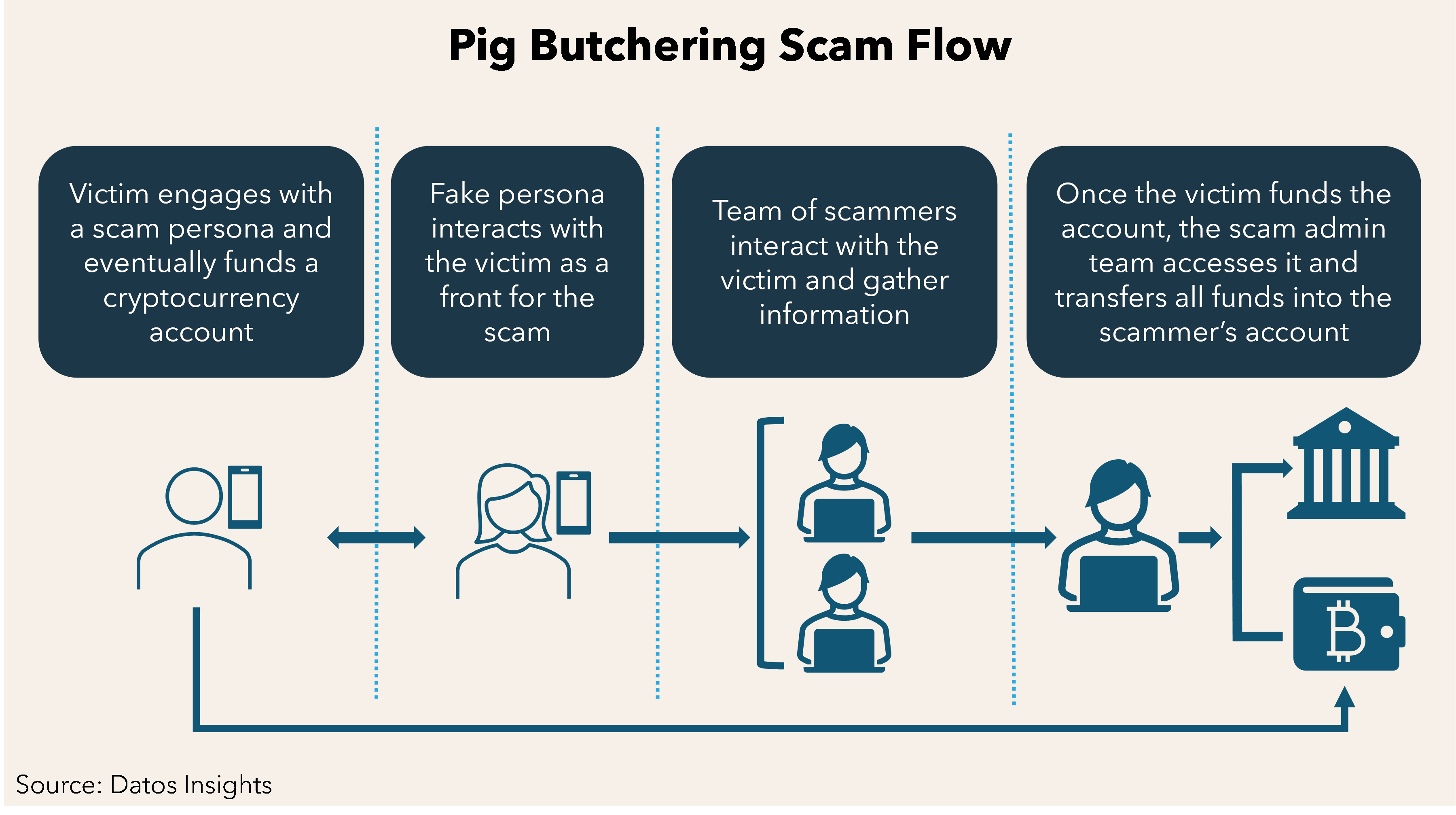
The term comes from an actual farming practice: you want to fatten the pig before you slaughter it. In the context of these scams, victims are the pigs. They're groomed (fattened) over weeks or months with romantic attention, emotional investment, and gradually escalating "investment opportunities." Then the scammers harvest (slaughter) everything the victim will give them.
The mechanics are straightforward but devastatingly effective. A victim matches with an attractive person online. Over weeks, they develop a relationship. The scammer builds trust. Then they share an "exclusive investment opportunity"—a fake cryptocurrency trading platform, a fraudulent business venture, or a bogus lending scheme. The victim invests. They're shown fake returns at first. This hooks them deeper. They invest more. And more. Until one day, the account is frozen. The contact disappears. The money's gone.
What makes this particularly vicious is the psychological component. Victims don't just lose money. They lose trust in their ability to judge people and situations. Many experience severe depression and suicidal ideation. Some do attempt suicide. The emotional damage often exceeds the financial damage.
The Scale of the Problem
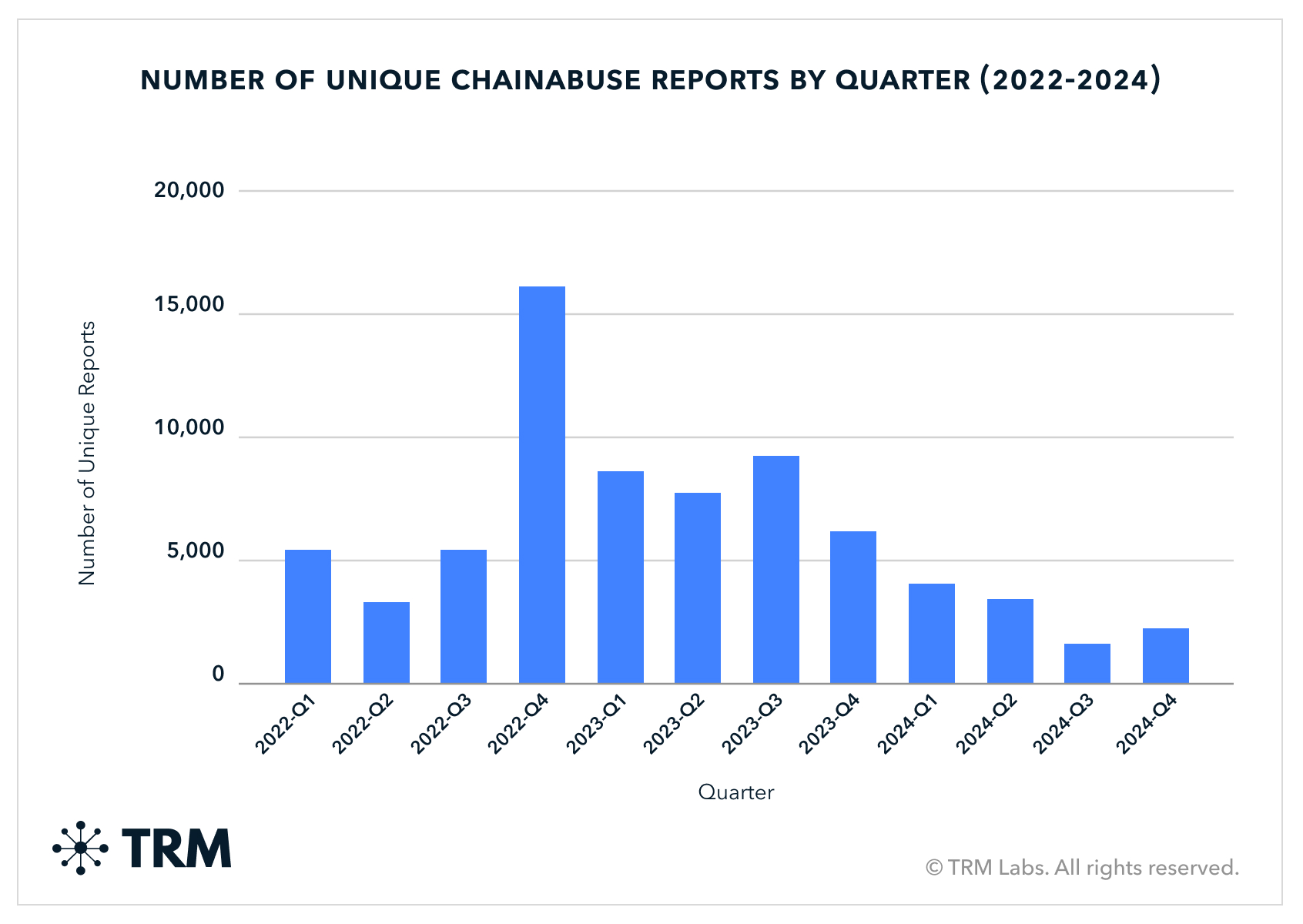
Let's talk numbers, because the numbers are what make this a crisis rather than just a recurring problem.
In the United States, the Federal Trade Commission reported that romance scams alone extracted
But here's what's actually terrifying: we don't have reliable global numbers because most victims never report being scammed. They're embarrassed. They feel stupid. They're ashamed they fell for a romantic con. So these figures are almost certainly undercounting the actual scale by a factor of 2-5x.
That means the real global take from this industry could be $30-50 billion annually. To put that in perspective, that's comparable to the annual revenue of Netflix. This isn't a marginal problem. This is a major organized crime industry operating at scale.
Why It's So Hard to Stop
Why hasn't law enforcement shut this down? Why do these compounds keep operating?
The answer involves jurisdiction, corruption, forced labor, and the nature of cryptocurrency itself.
First, jurisdiction. These compounds operate primarily in the Golden Triangle region of Southeast Asia—specifically in areas of Myanmar, Cambodia, and Laos that have limited governmental control. The Laotian "special economic zones" involved are largely controlled by Chinese business interests with their own security forces. If you're the Thai government, what's your incentive to crack down on criminal operations in Laos? If you're the Laotian government in an economically depressed region, and Chinese criminal syndicates are paying local officials to look the other way, what's your incentive to shut them down?
Second, the actual perpetrators. The people making decisions, running the compounds, and coordinating the money flows? They're almost entirely in China, or connected to Chinese organized crime networks. The laborers doing the actual scamming? They're young, desperate, often from India, Pakistan, or Ethiopia. They're not the kingpins. Arresting them accomplishes nothing except creating a PR win while the actual criminal network remains intact.
Third, cryptocurrency. Cryptocurrency doesn't exist in any bank. It doesn't flow through SWIFT networks that regulators monitor. It flows through decentralized exchanges, mixing services, and peer-to-peer networks. By the time law enforcement figures out where the money went, it's been converted, tumbled, and moved across a dozen blockchain networks.
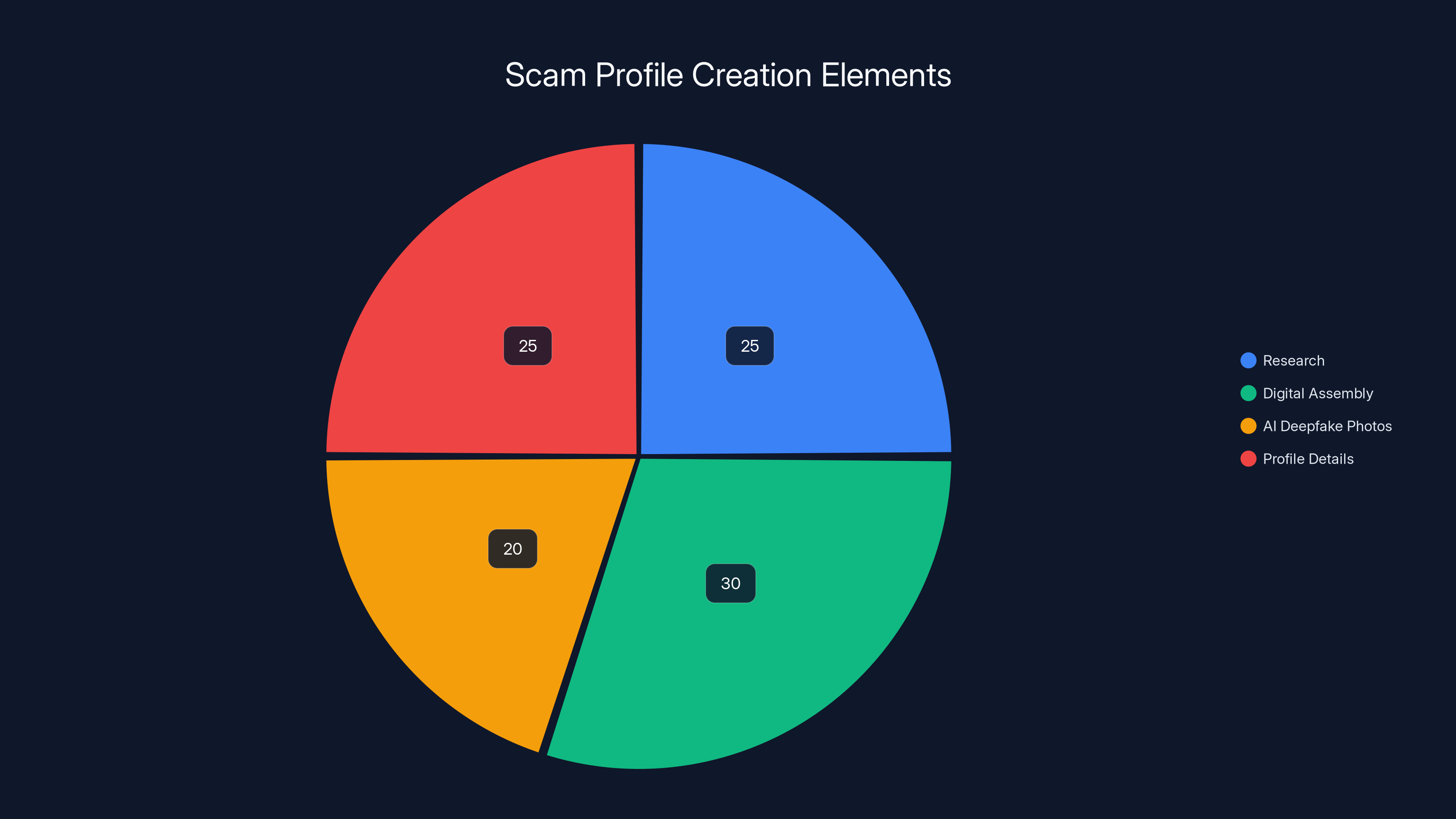
Estimated data shows that digital assembly and profile details each take about 25-30% of the effort in creating a fake profile, highlighting the importance of specificity in scams.
The Golden Triangle: A Lawless Zone for Cybercrime
The Golden Triangle sounds like something from an adventure novel. In reality, it's one of the most dangerous and lawless regions on Earth.
Historically, the Golden Triangle was known for opium and heroin production. But the drug trade has evolved, and so has the criminal activity in the region. Today, the term refers primarily to a cluster of "special economic zones" in the border region between Myanmar, Thailand, and Laos.
These zones operate under different rules than the rest of their host countries. They have their own security forces. They answer to different economic authorities. And crucially, they've become havens for every kind of cross-border crime you can imagine: human trafficking, drug manufacturing, wildlife trafficking, and—most profitably—cryptocurrency fraud.
The Chinese government's Belt and Road Initiative has poured hundreds of millions into infrastructure development in these zones, ostensibly to create legitimate trade corridors. But the reality on the ground is that these zones have become essentially autonomous criminal territories. Local officials are paid off. Escape routes are controlled. Anyone trying to leave without permission faces violence.
Why Compounds Exist Here
You might wonder why scammers need physical compounds at all. If this is cybercrime, couldn't they operate from anywhere?
They could, theoretically. But compounds serve several functions that justify their existence.
First, labor control. You can't monitor a remote worker's productivity effectively. You can't stop them from leaking information. You can't stop them from taking the money and running. A compound where workers sleep in shared dormitories, work 15-hour shifts on a nocturnal schedule, eat meals provided by the compound, and have their phones monitored and checked? That's how you maintain control over a workforce that would otherwise have no incentive to stay.
Second, efficiency optimization. Scammers working in compounds are arranged by ethnicity and language group to match with victims. An Indian scammer targeting Indian Americans. A Pakistani targeting Pakistani Americans. This dramatically increases conversion rates because the rapport-building works better. And conversion rates directly equal money extracted.
Third, operational security. All the infrastructure is in one place. The servers running the fake trading platforms. The AI tools generating deepfakes and creating realistic social media profiles. The phone banks where scammers work. The money conversion systems. If something goes wrong, everyone's right there to fix it.
Fourth, force and coercion. Let's be honest: you can't coerce a remote worker. You can coerce someone living in a compound surrounded by security guards, in a country where they don't speak the language, without a passport or money to leave.
How the Scam Actually Works: The Step-by-Step Machine
When Red Bull sent his initial documents, they contained flowcharts and written guides describing the exact process. Let me walk you through it, because understanding the mechanics is crucial to understanding why these scams work so well.
Stage One: Profile Creation
Every scam starts with a fake person. Not a real person using a fake account—an entirely fictional person created from the ground up.
The process begins with research. Scammers identify what their target demographic finds attractive. Are they targeting wealthy divorced women in their 50s? Young professional women in their 30s? Men interested in cryptocurrency? The targeting is specific because different personas appeal to different victim profiles.
Next comes the digital assembly. A team member creates a Facebook profile using stolen photos, often of attractive younger people. They use AI tools to generate additional photos that don't exist—pictures of the fake person traveling, at the beach, at work, doing activities that seem spontaneous and real.
The AI deepfake technology is crucial here. It's not sophisticated enough to fool someone meeting in person, but it's absolutely good enough to fool someone scrolling through profile pictures on a dating app or social media. A photo of a "person" at a beach doesn't need to be perfect. It just needs to look plausibly real enough to not trigger immediate skepticism.
They fill in the profile with specific details. Birth date. Hometown. Workplace. Education. Interests. The more specific the details, the more real the person feels. Someone with vague interests ("likes travel and pizza") feels fake. Someone who says "I'm an engineer at [specific company] and spend weekends hiking in the Cascades, currently reading The Three-Body Problem" feels like a real human you might know.
Stage Two: The Rapport-Building Grind
Once the fake profile is live, the scammer—a real person in the compound, assigned to this particular victim—starts messaging. This phase can last weeks or even months.
The scammer's job is straightforward: make the victim fall in love with the persona. This sounds callous when stated directly, but that's exactly what's happening. The scammer knows psychological tricks for building attachment. They respond quickly to messages. They ask questions that make the victim feel seen and understood. They share "vulnerable" moments that create reciprocal emotional investment.
The conversations are customized. Different scammers are trained on different strategies depending on the target demographic. For women, many scammers pose as successful men with interesting careers but emotionally unavailable fathers or exes—they play into narratives of potential transformation. For men, they often pose as younger women and play into desires and flattery.
Something crucial happens during this phase: the victim becomes invested in the relationship. Their friends might be skeptical. They might have rational doubts. But the emotional connection is real—the victim is experiencing genuine chemical bonding from regular contact with someone who seems to understand them.
The scammer is, simultaneously, working this account for 3-5 other victims. One has fallen in love with a businessman. Another with a military man. Another with an oil rig worker. The actual scammer behind these profiles is a 22-year-old from Bangalore working a 15-hour shift in a Laotian compound.
Stage Three: The Pivot to Investment
After the victim is emotionally invested, the scammer introduces money into the conversation. This is critical and must be done carefully.
The scammer doesn't immediately ask for money. Instead, they share an "opportunity." A friend has a business. A relative is running an investment fund. They heard about this cryptocurrency exchange through work. The setup is always something that sounds like a casual conversation, not a pitch.
The victim often isn't interested at first. They don't know about crypto. They don't have money to invest anyway. The scammer backs off. But the seed is planted.
Over the next week or two, the scammer keeps mentioning these returns casually. "Oh, I just made $2,000 this week with that investment I mentioned." Or "My friend tripled her money last month." The casual mentions accumulate. The victim starts to think, "Maybe I should ask more about this."
Eventually, the victim asks. And the scammer "reluctantly" provides a link to a fake cryptocurrency trading platform or investment app.
Stage Four: The Fake Platform
This is where the technical infrastructure matters. The fake platform looks professional. It has a proper website. It has an app. It shows real market charts and data (usually copied from legitimate exchanges). It has a customer service email address that actually responds.
When the victim creates an account and makes an initial investment—let's say
Over the next week, the account shows more gains.
What's actually happening is simple: the platform isn't real. The gains aren't real. The victim isn't actually buying cryptocurrency. They're just watching numbers go up on a website that exists only to show them false data.
At some point—usually after a few weeks—the victim gets an email from "customer service." There's a problem with their account. A regulatory fee. A deposit requirement to unlock larger trades. Something that requires sending more money.
But here's the psychological hook: the victim has made money. Real gains, or so they believe. To keep making money, to unlock the larger account, to access the premium features, they need to send more.
So they do. They send
Stage Five: The Harvest
Eventually, the scammers decide they've extracted enough from this particular victim. The account gets frozen. Suddenly they can't log in. Messages to customer service go unanswered. The romantic interest stops responding. By the next day, the account is gone, the website is inaccessible, and the scammer has moved on.
The victim checks their bank account. The $100,000 they've sent is gone. The gains they've made? They were never real. They were just numbers on a fake website.
Some victims realize immediately they've been scammed. Others take weeks to fully accept what's happened. Many deny it for months, hoping the account will come back online, that there's been some mistake.


Scam operations in Southeast Asia are primarily due to limited oversight and corruption protection, with each factor contributing significantly to the choice of location. Estimated data.
Inside the Compound: What Red Bull Revealed
Red Bull's documents painted a picture of a twisted corporate environment. The compound operated like a sales floor crossed with a prison.
Workers were arranged by ethnicity and language. Indians scamming Indians. Pakistanis scamming Pakistanis. Ethiopians scamming Americans. This was deliberate—using people from the same ethnic background made the scams more convincing.
Everyone worked the same nocturnal schedule: midnight to 3 PM. This was designed to sync with daytime in the United States and India, when their targets would be awake and active on social media and dating apps.
Payment worked through a commission system designed to create perpetual debt. Workers were told they could earn money based on what they extracted from victims. A successful scam might earn them a commission. But the compound charged fees for everything. Housing. Food. The laptop they used. Phone service. Internet access. By the time commissions and fees were calculated, most workers found themselves deeper in debt than when they started.
It was, Red Bull explained, a grotesque parody of a tech startup sales floor. The motivational posters existed. The "team celebrations" happened when someone pulled off a successful scam—a gong would be struck in the office. There were even rankings posted showing which scammer had extracted the most money that month.
But everyone was effectively enslaved. Passports confiscated. Unable to leave. Working in a country where they didn't speak the language, surrounded by security guards. The entrepreneurial language of commission and bonus was pure theater. The actual system was debt bondage.
Red Bull himself had fallen for a fake job listing. A company recruiting for IT managers in Laos. The position paid well. It seemed legitimate. When he arrived, he discovered he was working inside a scam compound. His passport was taken. He was assigned to manage the technical infrastructure for the scamming operation.
Because he had technical skills, his situation was slightly better than workers just doing the manual scamming. He had more access. More freedom of movement. More information. But he was still trapped. Still monitored. Still coerced.
The Whistleblower's Dilemma: Why Red Bull Decided to Expose Everything
Why would someone in Red Bull's situation risk exposure? What made him decide to contact a journalist and potentially blow up his entire situation?
The answer is complicated. Red Bull had family in India. He'd been inside the compound long enough to understand the scale of the operation and the number of people being harmed. He'd seen workers being abused. He'd seen people try to escape and get caught. He'd seen the psychological breakdown that came from months or years of forced labor.
And he'd come to a decision: staying quiet made him complicit. Getting out quietly, even if he could, wouldn't stop the operation. Someone needed to expose this from the inside.
This was extraordinarily dangerous. If the compound discovered he was communicating with a journalist, the consequences would be severe. Not metaphorically severe. Actually, physically severe. Violence. Possible death. Definitely confiscation of money he'd hidden and complete isolation.
So Red Bull developed a strategy. He would document everything. He would communicate using encrypted channels, with disappearing messages. He would be methodical. And he would do it all while still working, still playing his role, so that suspicion wouldn't arise.

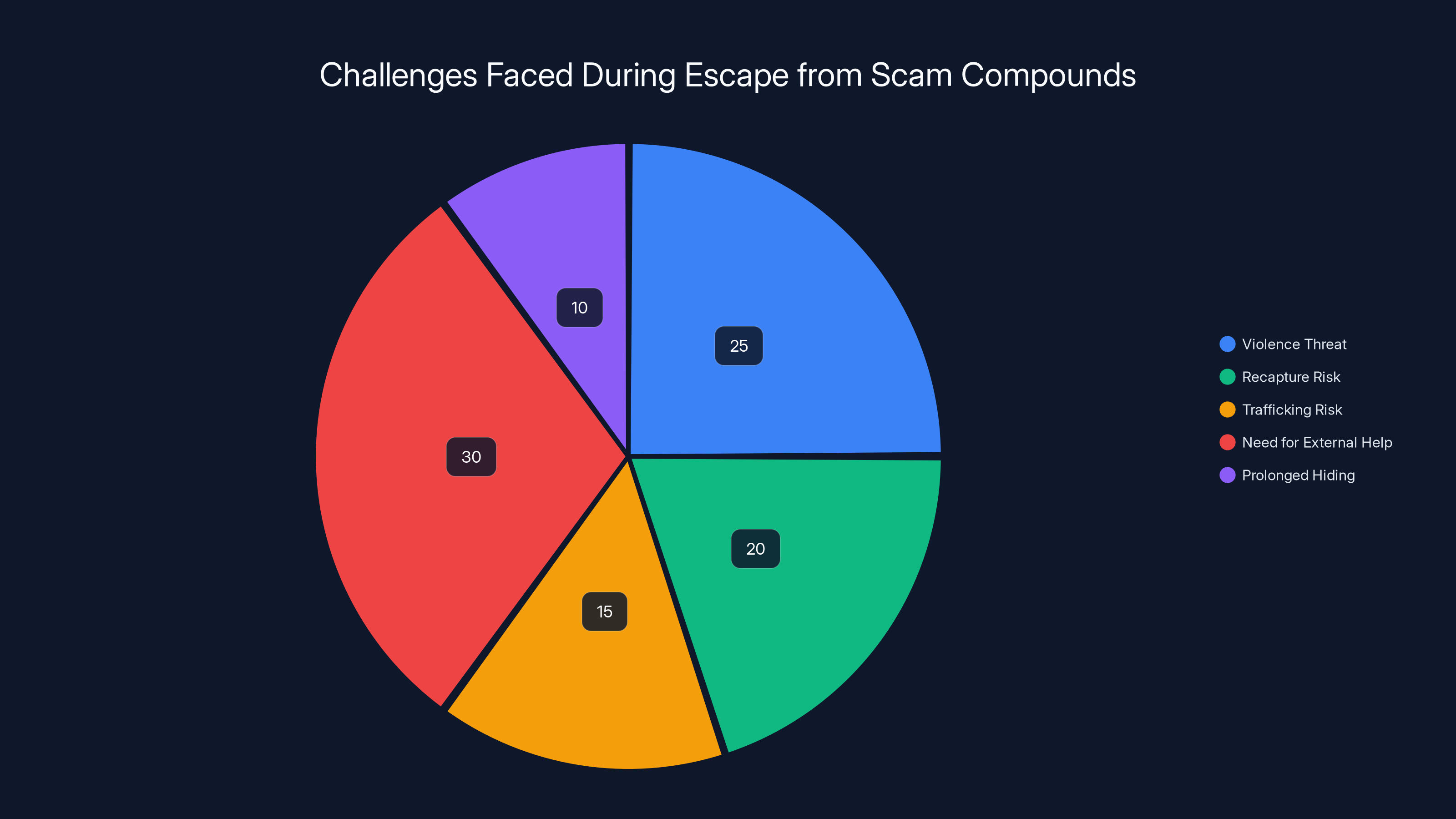
Escaping scam compounds involves significant risks, with external help being crucial for success. Estimated data based on typical escape narratives.
The Technical Infrastructure: How Fake Platforms Are Built
One thing Red Bull emphasized was the sophistication of the technical infrastructure. This wasn't hobbyists running a scam out of an apartment. This was an organized operation with real engineers, real servers, and real infrastructure.
The fake trading platforms, for instance, required constant maintenance. They had to look like legitimate exchanges. They had to show real market data (actually sourced from legitimate exchanges and displayed with fake account balances overlaid). They had to process transaction requests. They had to send notifications and emails.
The AI deepfake technology was similarly sophisticated. Not in the sense of producing perfect images, but in producing images good enough to pass a dating app's minimum standards. The tools could generate variations of a few base photos, creating the illusion that a fake person had diverse experience and an actual life.
The social media accounts managing all the fake profiles required infrastructure to manage. Each profile needed unique browsing histories, account histories, activity patterns. If someone investigated a profile and found that it was created yesterday, that would raise red flags. So the infrastructure included systems for aging profiles, for creating historical activity, for making them look like real people with years of history.
All of this required specialized engineering. Which is why the compound employed actual engineers like Red Bull. They weren't just scammers. They were building an industrial-scale fraud machine.

The Human Cost: Victims on Both Sides
What's crucial to understand is that there are victims on both sides of this crime.
On one side are the targets of the scams. People who've lost their life savings. People who've experienced emotional trauma. People who've attempted suicide. The scale of human suffering on this end is difficult to quantify but easy to understand.
On the other side are the forced laborers. People like Red Bull. Young people from poor families in India, Pakistan, and Ethiopia who responded to a job posting and found themselves enslaved. People forced to work 15-hour days committing fraud. People who can't leave. People whose only escape route is either waiting until they've somehow paid off their manufactured debt (which is impossible) or risking violence by trying to escape.
Both groups are victims of the same criminal enterprise. Both have had their futures stolen. Both carry psychological scars.
The difference is that scam victims have advocacy organizations, media attention, and police resources devoted to their cases. Victims of forced labor in these compounds are often overlooked. They're perpetrators from one perspective (they're the ones committing fraud) and victims from another (they're forced to do it). This legal and moral ambiguity means they often don't get protection or resources they need.

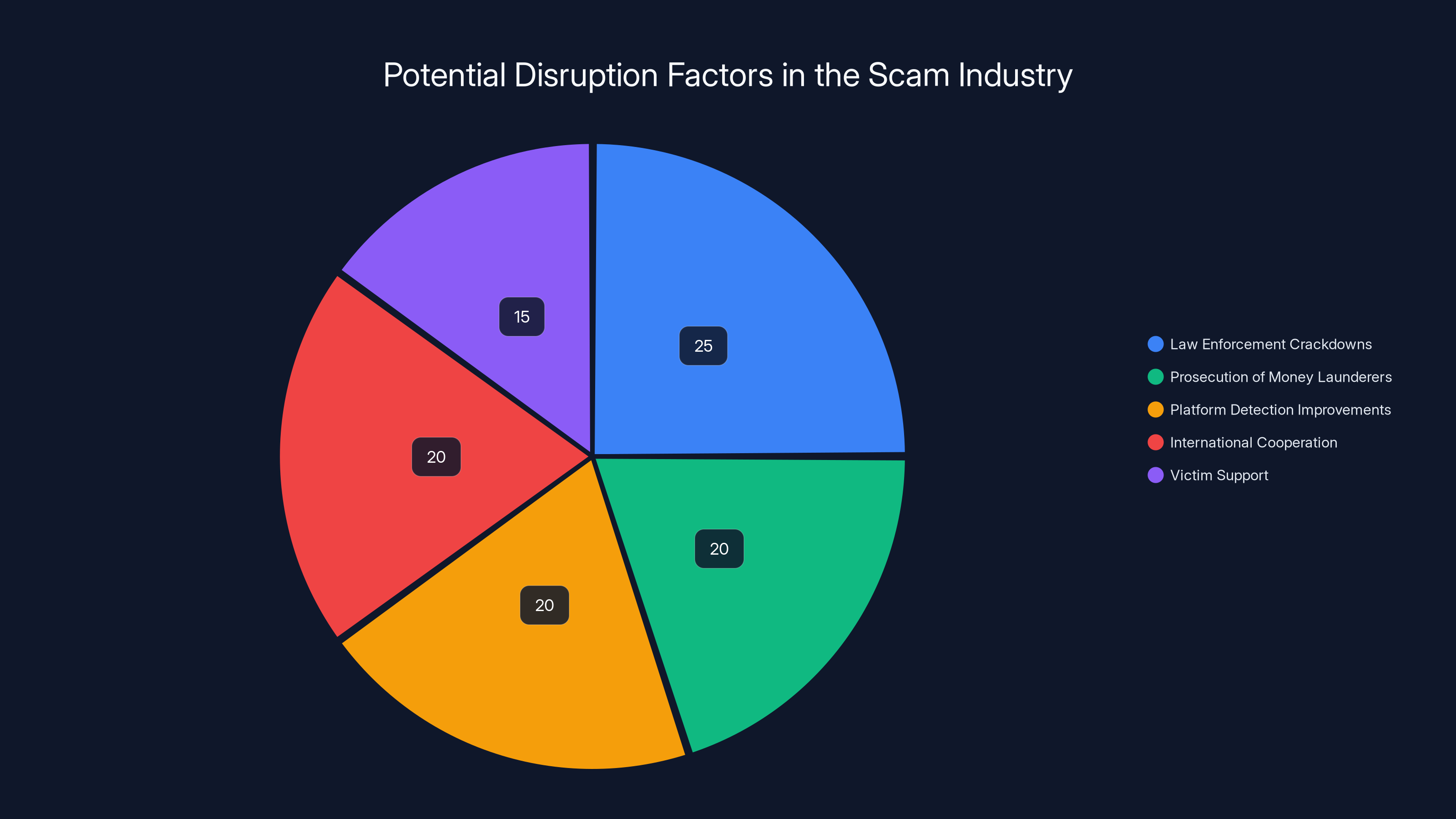
Simultaneous action across multiple fronts could significantly disrupt the scam industry. Estimated data suggests law enforcement crackdowns and platform improvements are key factors.
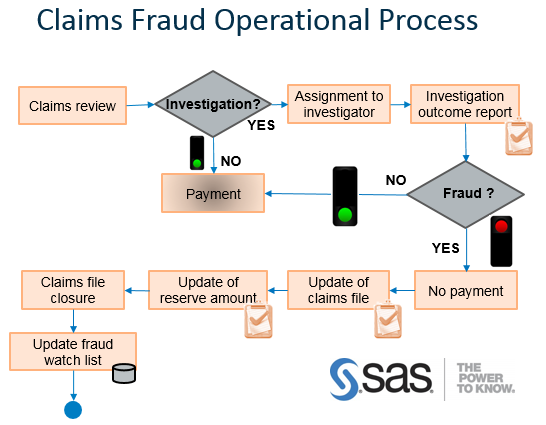
Law Enforcement Response: Why It's So Limited
If this problem is as large as described, you'd expect massive law enforcement operations dedicated to stopping it. You'd expect international task forces. You'd expect major arrests and prosecutions.
Instead, what you get is fragmented, underfunded efforts with limited success.
The reasons are structural and depressing. First, the cryptocurrency angle means that traditional financial crimes units are often out of their depth. Most law enforcement was trained to follow bank transfers and wire records. Following a money trail through blockchain is entirely different and requires specialized expertise.
Second, the international nature creates jurisdictional nightmares. A victim in New York. A scammer in Laos. Money flowing through decentralized exchanges and blockchain. Which agency takes the lead? The FBI? The Secret Service? Local police? Interpol? Each agency has jurisdiction questions.
Third, the victims themselves are often reluctant to cooperate with law enforcement. They're embarrassed. They don't want to admit they fell for a romance scam. They might not even realize they've been scammed until the emotional investment makes acknowledging it impossible.
Fourth, many law enforcement agencies don't even collect systematic data on cryptocurrency romance scams. They might have a case here or there, but they don't share intelligence with other departments or other countries. Without good data, it's hard to mobilize resources.
Fifth, even when law enforcement does identify a compound and wants to take action, they have to coordinate with foreign governments that may not prioritize the issue. A compound in Laos generating billions for Chinese crime syndicates has local political protection. Why would the Laotian government shut it down?

The Escape: Getting Out of a Scam Compound
Red Bull's situation came to a critical point after several months of communication with journalists and law enforcement. The operation was becoming riskier. The window for escape was closing.
Getting out of a compound like this isn't like walking out the front door. It requires coordination with people outside—law enforcement, journalists, humanitarian organizations. It requires money. It requires a plan that accounts for the fact that the compound will try to stop anyone from leaving.
The escape plan that eventually came together was complex and dangerous. It involved coordination with Thai police, travel documents, financial support, and a route that avoided the compound's security apparatus.
What's notable is that escaping from one of these compounds is dangerous enough that it requires outside help. Escapees face violence. They face being recaptured. They face being trafficked elsewhere. Many who escape successfully end up hiding for months while they try to stabilize their situation.
Some don't make it.
There are stories of people trying to escape compounds and being recaptured or worse. These stories rarely make international news. They exist in the reports of NGOs and humanitarian organizations but don't penetrate mainstream awareness.
When Red Bull finally escaped, he'd provided detailed documentation of the compound's operations, the people running it, and the infrastructure involved. Enough to interest law enforcement in Thailand and potentially India. But prosecutions are slow. International cooperation is difficult. And in the meantime, the compound continues operating.
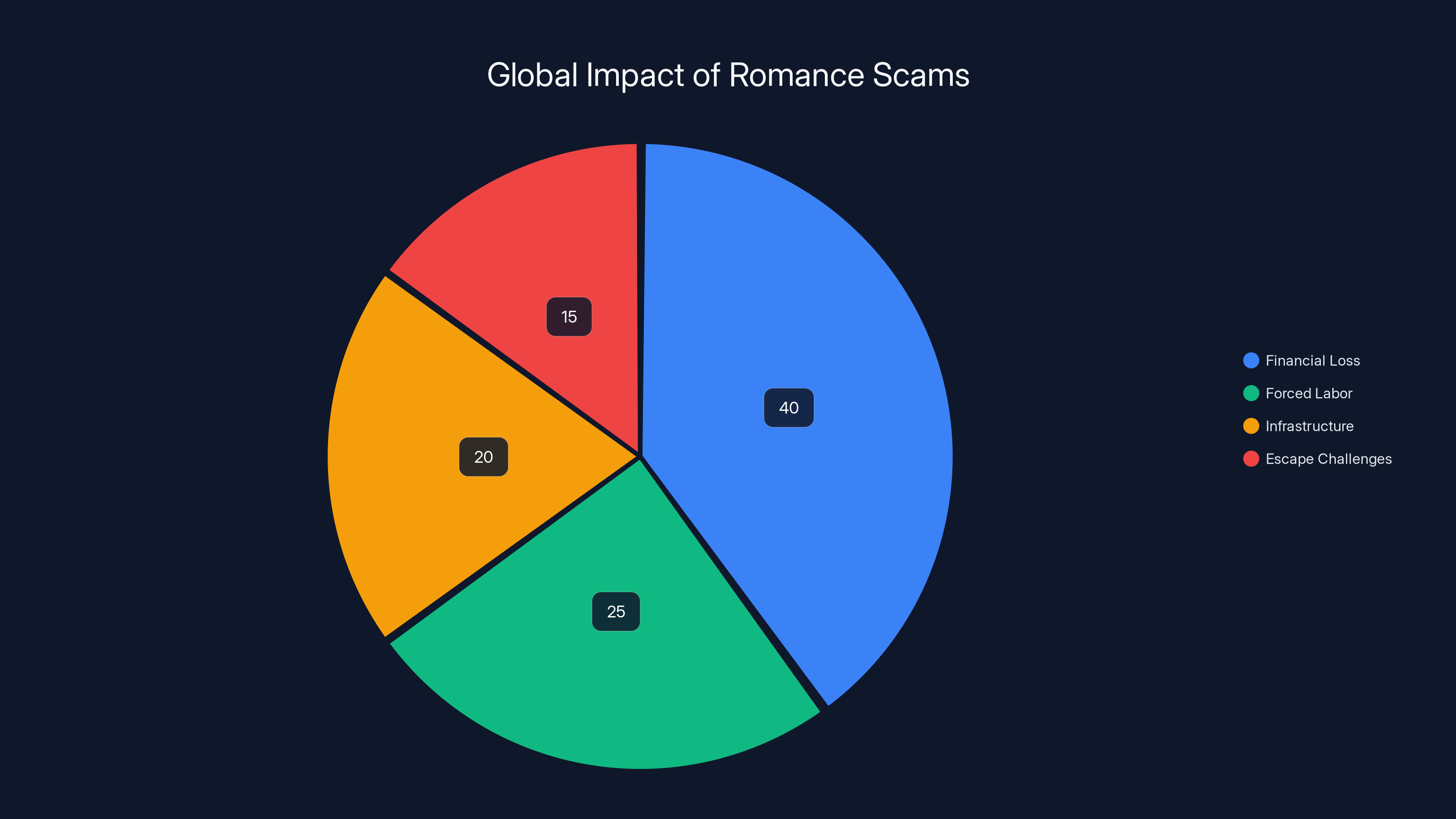
Estimated data shows financial loss as the largest impact of romance scams, followed by forced labor and sophisticated infrastructure. Escape challenges also significantly affect victims.
The Broader Network: How These Operations Connect
One thing Red Bull's exposure clarified was that these aren't isolated compounds. They're part of a larger network.
There are dozens of major compounds across the Golden Triangle region. Some focus on cryptocurrency romance scams. Others handle illegal online gambling operations. Some handle market manipulation schemes. But they all serve the same criminal organizations—primarily Chinese syndicates—and they all operate on similar principles.
Workers are trafficked between compounds. Infrastructure is shared. Money is pooled and moved through similar channels. Take down one compound and the network adapts. Move to Thailand and the operations shift to Cambodia or Laos.
This distributed, adaptive network is one reason why law enforcement has struggled to seriously disrupt the operations. You can't shut it down by taking down one compound. You have to take down the entire network simultaneously, which requires international cooperation at a level that doesn't currently exist.
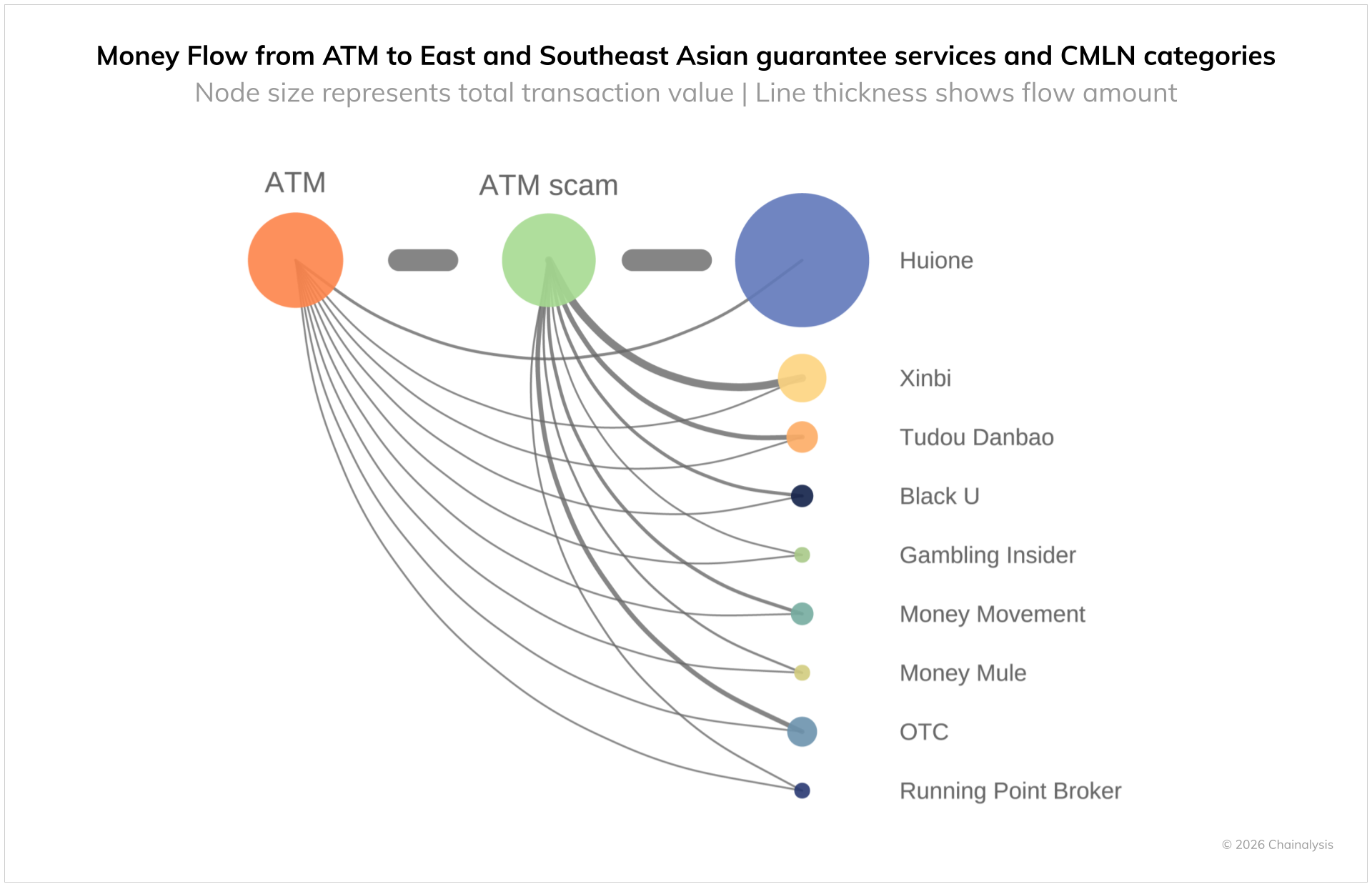
The Money Trail: How Scam Proceeds Are Laundered
Here's a question that might seem obvious but is actually complicated: where does all the money go?
Victims send money to fake cryptocurrency exchanges. But someone has to convert that cryptocurrency into actual fiat currency that can be spent. That process—the conversion from digital to physical money—is where law enforcement might theoretically intercept.
Except the scam operations have sophisticated money laundering operations in place. Cryptocurrency is converted through mixing services that obscure the money trail. It's split into smaller transactions to avoid triggering regulatory alerts. It's moved through peer-to-peer networks and decentralized exchanges.
By the time the money is converted to fiat currency, it's moving through networks of small businesses, money exchange services, and cryptocurrency brokers in Southeast Asia, each taking a cut, all making it harder to trace.
Some of the money stays in Southeast Asia, funding the compounds and paying local officials. Some is moved through official channels—purchase of property, transfer through banks, investment in legitimate businesses. Some ends up in China through various mechanisms.
The result is a money laundering system sophisticated enough that even when law enforcement identifies money flows, actually capturing it and proving criminality requires cooperation between agencies that often don't cooperate well.
Prevention: What Victims and Platforms Need to Know
Given the scale and sophistication of these operations, prevention is genuinely difficult. But there are strategies that reduce risk.
For individuals: Be suspicious of rapid escalation to off-platform communication. Be skeptical of investment opportunities shared by new romantic connections. Be aware that the profiles you're seeing might be AI-generated. Use reverse image searches to check if profile photos have been used elsewhere. Video call before developing emotional attachment (scammers often avoid video). And most importantly: legitimate investments don't require romantic relationships to succeed.
For dating platforms: The platforms themselves have been reluctant to take serious action, partly because romance scams happen on every platform and fully preventing them would require changes that hurt legitimate user experience. But progress could be made: better detection of coordinated fake profiles, faster removal of scam accounts, better education for users, and cooperation with law enforcement.
For law enforcement: International cooperation is essential. A scam that starts in Laos, targets Americans, and moves money through cryptocurrency exchanges requires coordination across multiple countries. That coordination doesn't currently exist at necessary levels.
The Aftermath: What Happens to Rescued Victims
When people successfully escape from these compounds, their troubles don't end. They often face trauma, legal ambiguity, and difficulty reintegrating.
Many escapees have been threatened with violence if they speak out. Many have family still at risk or family who were threatened. Many face legal questions about their own role in the scamming operations. Some face deportation.
Humanitarian organizations have stepped in to fill gaps, providing shelter and psychological support for escapees. But resources are limited. And the psychological trauma of months or years in forced labor is profound.
Red Bull's situation, after escape, involved becoming more involved with law enforcement investigations. That comes with its own risks and complications. He became a key witness. Key witnesses can be targeted by criminal organizations.
The scam industry has shown it's willing to use violence against threats. Escapees. Whistleblowers. Even journalists investigating the operations. This isn't a victimless crime with just financial consequences. Real physical danger is involved.

The Chinese Connection: Why This Matters Geopolitically
Here's something important that often gets lost in the individual stories: these operations are connected to organized crime groups that have the backing—directly or indirectly—of Chinese government interests.
The compounds operate in zones that exist because of Chinese economic policy and investment. The operational scale that makes billions annually profitable requires institutional support. The money flows through systems connected to Chinese banking and financial infrastructure.
This isn't to say the Chinese government is running these scams. But the criminal organizations running them have been remarkably insulated from crackdowns, suggesting political protection at various levels.
This matters because it makes the problem harder to solve. A criminal organization can be prosecuted if it's operating in a neutral country. A criminal organization that has backing from a major power is effectively insulated from traditional law enforcement pressure.
Geopolitically, this is part of a broader pattern of Chinese criminal organizations operating across Southeast Asia with minimal interference. It's connected to questions about Chinese influence, regional instability, and law enforcement capacity.

The Parallel to Other Forced Labor Operations
While pig butchering scam compounds are unique in some ways, they're not the only examples of industrial-scale forced labor operations in the same geographic region.
Mines, manufacturing facilities, agricultural operations, and fishing vessels all employ similar forced labor systems. Young people, often from poor countries, are recruited with fake job offers, trapped by debt, and worked until they break or until the operation shifts.
The mechanisms are similar enough that expertise from organizations focused on human trafficking and modern slavery could theoretically transfer to combating scam compounds. But the actual cooperation between these advocacy areas is minimal.
There's something particularly insidious about scam compounds, though. Unlike a mine or factory where the forced labor is producing something (minerals, goods, agricultural products), scam compounds are specifically designed to psychologically manipulate both the workers and the targets. Every interaction is a negotiation of manipulation and coercion.

What Happens to the Scam Industry Going Forward
In the short term, nothing changes. The compounds continue operating. The scams continue. Victims continue losing money and suffering psychological trauma. Forced laborers continue being exploited.
Law enforcement might eventually coordinate more effectively. International pressure on the countries hosting these operations might increase. Technology might improve, making it harder for scammers to create convincing fake profiles. Platforms might finally take serious action.
But each of these changes faces structural obstacles. International cooperation is difficult. The countries involved have limited motivation. Technology keeps evolving on both sides. And the profits are large enough that even if crackdowns eliminate 50% of the operations, the remaining 50% is still worth billions.
What would actually disrupt the industry would be simultaneous action on multiple fronts: law enforcement crackdowns in the countries hosting compounds, serious prosecution of money launderers, improvements in platform detection and prevention, international cooperation, and victim support and recovery.
None of that seems imminent.

The Role of Journalism: Why Whistleblowers Matter
Why did Red Bull choose to reach out to journalists specifically?
Because journalists can tell the story in ways that law enforcement can't. A law enforcement investigation results in court documents. A journalistic investigation results in a story that reaches millions of people. That story creates pressure. It creates awareness. It creates political incentive for action.
When major news outlets cover these issues, they affect public perception and policy priorities. They give victims a framework for understanding what happened to them. They document the scale and nature of the problem.
But journalism also faces challenges on this topic. It's hard to verify claims from someone in a dangerous situation. It raises ethical questions about operational security. It requires patience—developing a whistleblower relationship that produces usable information takes months or years.
And there's real danger. Journalists investigating these operations have been threatened. Whistleblowers have been targeted.
But the alternative—letting the operations continue in darkness—is worse. Exposure, even imperfect exposure, at least creates pressure for change.
Conclusion: Understanding the Scale of the Crisis
Red Bull's story is remarkable because it's rare. Most people inside these compounds don't successfully escape. Most whistleblowers don't make contact with journalists. Most investigations don't produce detailed documentations of the operations.
But that rarity makes it more important, not less. When someone manages to provide an inside view of how these operations work, it's a genuine opportunity to understand the problem at scale.
What Red Bull revealed was an industrial-scale fraud and forced labor operation. Hundreds of thousands of people trapped in compounds across Southeast Asia. Tens of billions of dollars extracted from victims globally. Sophisticated technical infrastructure. Effective psychological manipulation. Organized crime networks with resources and protection.
This isn't a small problem. This isn't a niche issue. This is one of the largest ongoing crimes affecting people in wealthy countries like the United States and Canada, and one of the largest trafficking and forced labor operations in the world.
Solving it requires understanding it first. And understanding it requires listening to people like Red Bull, who risked everything to expose what was happening inside the machines built to hurt people.
The broader question is whether we're willing to make the necessary changes to disrupt these operations. Better platform safety. International law enforcement cooperation. Victim support systems. Prosecution of money launderers. Political pressure on countries hosting the compounds.
These are all possible. They just haven't been prioritized. Until they are, the industry continues. The compounds operate. Victims lose money and trust. Forced laborers remain trapped.
Red Bull's story shows that change is possible—that someone inside the machine can recognize the harm and choose to expose it. What remains is whether the rest of us will respond with the seriousness the problem demands.

FAQ
What is a pig butchering scam?
A pig butchering scam is a form of romance fraud where someone establishes an emotional relationship with a target through online dating or social media, then convinces them to invest money in fake cryptocurrency platforms or other fraudulent schemes. The victim believes they're making real investments with real returns, when in fact they're sending money to criminals who disappear after extracting a target amount. The name comes from the farming practice of fattening a pig before slaughter—victims are "fattened" with emotional attention before being "harvested" for money.
How do scammers create fake profiles that seem real?
Modern scam operations use multiple techniques to create convincing fake profiles. They steal photos from social media and use AI tools to generate additional images of fictional people that don't exist. They create detailed profiles with specific birth dates, job titles, locations, and interests that make the persona feel like a real person. They maintain these profiles over weeks, gradually building activity histories and social connections to make them look established and legitimate. When victims interact with the profiles, they're communicating with real scammers in compounds working shifts, not with the fictional person in the photos.
Why are Southeast Asian compounds used for these operations?
Scam compounds exist in Southeast Asia for several reasons: they operate in lawless zones with limited government oversight, they allow physical control over a forced labor workforce, they enable efficient organization of scammers by ethnicity and language for better targeting, they provide centralized infrastructure for the fake platforms and technical operations, and they exist in regions with local government corruption that allows them to operate with relative protection. The geographic location also provides a distance from the victims being targeted, making law enforcement investigation more difficult.
How much money do victims typically lose in pig butchering scams?
Victims lose widely varying amounts depending on their financial resources and how long the scam operates. The average loss ranges from
What should I do if I think I'm being scammed?
If you suspect you're being scammed: stop all financial transactions immediately, save all evidence of communications, block the person on all platforms, and report the account to the dating app or social media platform. Then report the scam to the FTC at reportfraud.ftc.gov, and if cryptocurrency was involved, to your local law enforcement. Don't be embarrassed—these scams are extraordinarily sophisticated, well-funded, and executed by professional criminals. Thousands of victims report these scams monthly, and you're not alone. The sooner you stop interaction, the easier recovery becomes.
How do scammers convert cryptocurrency to real money?
Scammers use sophisticated money laundering techniques to convert cryptocurrency proceeds into usable currency. They use mixing services that obscure the original source of funds, split large amounts into smaller transactions to avoid regulatory detection, route money through peer-to-peer cryptocurrency exchanges, and eventually convert to fiat currency through networks of small businesses and money exchange services in Southeast Asia. Some money stays in the region to fund compound operations and pay local officials. Some is moved through legitimate business investments and banking channels. By the time law enforcement tries to trace the money, it has passed through multiple systems and jurisdictions, making recovery nearly impossible.
Why don't dating apps prevent these scams more effectively?
Dating platforms face challenges in preventing romance scams at scale. Completely eliminating fake profiles would require verification systems that compromise user privacy and reduce overall platform usability. Scammers adapt quickly to new detection methods. Users are often reluctant to admit they're being scammed, reducing reporting rates. The platforms themselves have faced criticism for prioritizing growth over safety, and romance scams, while devastating to individuals, represent a relatively small percentage of platform activity. However, platforms could do significantly more through better AI detection of coordinated fake profiles, faster account removal, better user education, and actual cooperation with law enforcement investigations.
What happens to people rescued from scam compounds?
People who escape or are rescued from scam compounds face significant challenges. They often experience psychological trauma from the forced labor, threats of violence, and complex moral feelings about their role in scamming others. They may face legal complications and deportation risk in the countries where they escaped. They often fear retaliation against family members who might still be in the country where they were trafficked from. Humanitarian organizations provide shelter and support, but resources are limited. Many escapees spend months hiding and trying to stabilize their lives before they can safely provide cooperation to law enforcement or journalists investigating the operations.
Key Takeaways
- Pig butchering romance scams extract tens of billions annually through fake profiles, emotional manipulation, and fake investment platforms
- Hundreds of thousands of forced laborers are trafficked to Southeast Asian compounds where they work as scammers under modern slavery conditions
- Cryptocurrency's decentralized nature and sophisticated money laundering make it virtually impossible for law enforcement to recover stolen funds
- Whistleblowers from inside compounds are extremely rare, making firsthand documentation of operations crucial for understanding the scale
- Escaping scam compounds requires outside coordination and carries serious risk of violence, making long-term institutional solutions essential
Related Articles
- 149 Million Credentials Exposed: The Massive Data Leak Explained [2025]
- Under Armour 72M Record Data Breach: What Happened [2025]
- SMS Sign-In Links: A Critical Security Vulnerability Affecting Millions [2025]
- Most Spoofed Brands in Phishing Scams [2025]
- Supreme Court Hacker Posted Stolen Data on Instagram [2025]
- 45 Million French Records Leaked: What Happened & How to Protect Yourself [2025]
![Inside Southeast Asian Scam Compounds: The Crypto Fraud Crisis [2025]](https://tryrunable.com/blog/inside-southeast-asian-scam-compounds-the-crypto-fraud-crisi/image-1-1769514071255.jpg)



