Microsoft Notepad Markdown Security Vulnerability: The Complete Guide to CVE-2026-20841
Last month, Microsoft disclosed a security vulnerability in Notepad that most users didn't even know existed. The flaw affects how Notepad handles Markdown files, and it's the kind of issue that makes security researchers shake their heads because it's so deceptively simple yet dangerously effective.
Here's what happened. A bad actor could trick you into clicking a single link inside a Markdown file opened in Notepad. That's it. One click. And from there, malicious code could execute on your computer, giving attackers access to whatever they want. Microsoft patched this in its February 2025 security update, but the vulnerability (tracked as CVE-2026-20841) highlights a bigger problem with how modern operating systems are adding features without always thinking through the security implications.
We're going to walk through exactly what this vulnerability is, how it works, why it matters, and most importantly, what you should actually do about it. This isn't just technical jargon. This is about understanding a real threat that could affect millions of Windows users.
TL; DR
- CVE-2026-20841 is a remote code execution vulnerability in Windows Notepad affecting Markdown file handling
- Attackers can trick users into clicking malicious links inside Markdown files, launching unverified protocols
- Microsoft patched the flaw in its February 2025 security update with no known active exploitation
- The vulnerability works because Notepad's Markdown preview renders clickable links without proper validation
- Users should update Windows immediately and remain cautious with Markdown files from untrusted sources
- This exploit highlights the broader risk of adding complex features to simple applications

CVE-2026-20841 is a critical vulnerability with a CVSS score of 9.0. It requires user interaction but has no active exploitation reported. A patch is available.
Understanding the Notepad Markdown Vulnerability Basics
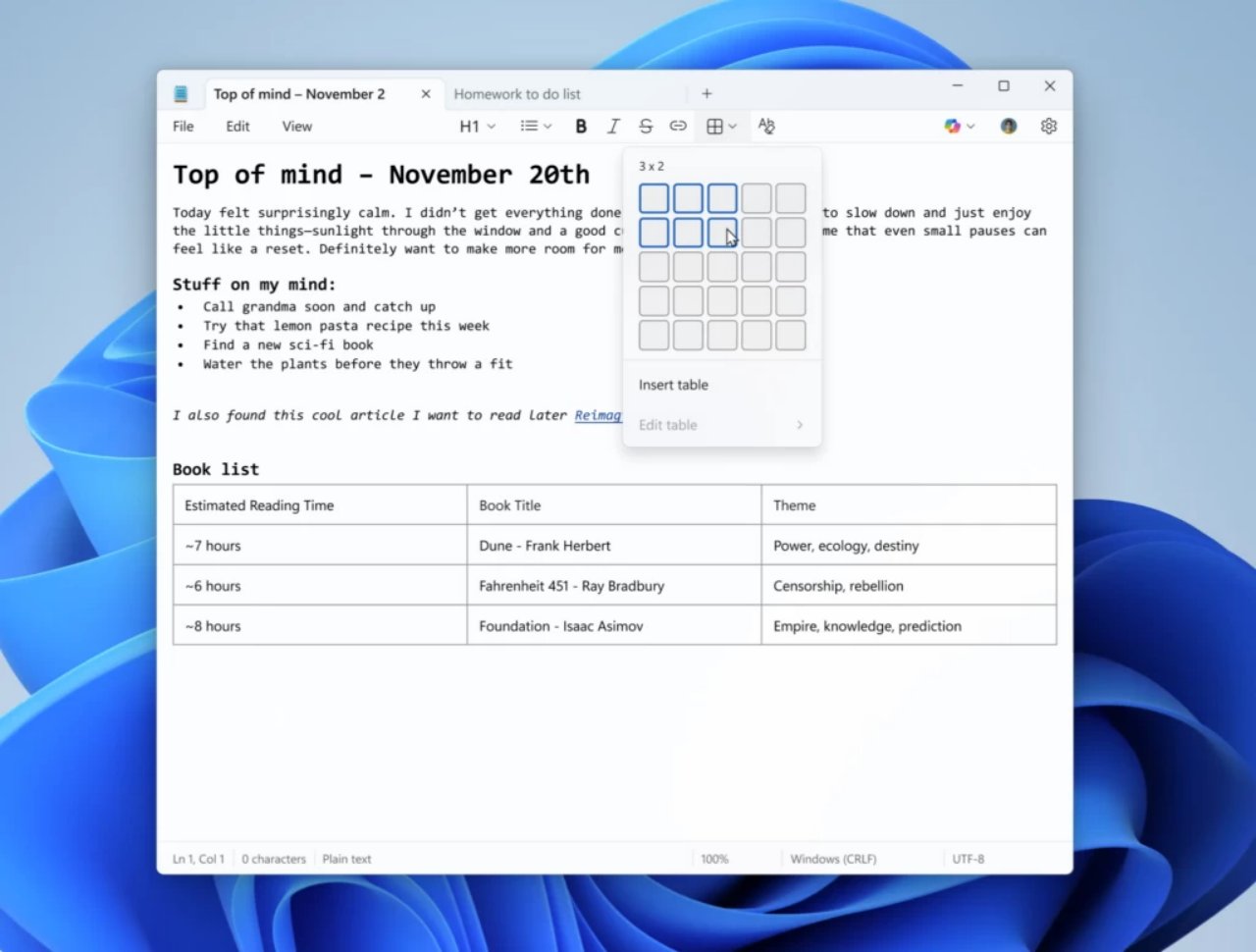
Microsoft introduced Markdown support to Notepad on Windows 11 back in May 2024. The feature seems simple enough on the surface: open a .md file, and Notepad displays a preview pane on the right showing how the formatted text will look. Headings are larger, bold text is bold, and links are clickable.
That last part is where the problem lives.
When Notepad renders Markdown, it converts link syntax into clickable elements in the preview pane. In standard Markdown, you write links like this: [click here](https://example.com). Notepad helpfully turns that into an actual clickable link. But here's the critical flaw: Notepad doesn't properly validate what's inside those parentheses.
Instead of only allowing safe web URLs (like https://), Notepad will process other types of protocols. This includes protocols that Windows uses for system operations. An attacker can craft a Markdown link using something like [click here](cmd://command) or similar protocol handlers, and when you click that link in the preview, Windows will execute whatever command follows.
The vulnerability is CVE-2026-20841, and Microsoft assigned it a CVSS severity score indicating critical risk. No public exploit code has been released, and Microsoft confirmed there's no evidence of attackers actively exploiting it in the wild. But that doesn't mean it's not dangerous—it just means the window of vulnerability was relatively small before the patch was released.
How the Exploit Actually Works: A Step-by-Step Breakdown
Let's walk through exactly how this attack would theoretically play out, because understanding the mechanics helps you understand why it's such a serious issue.
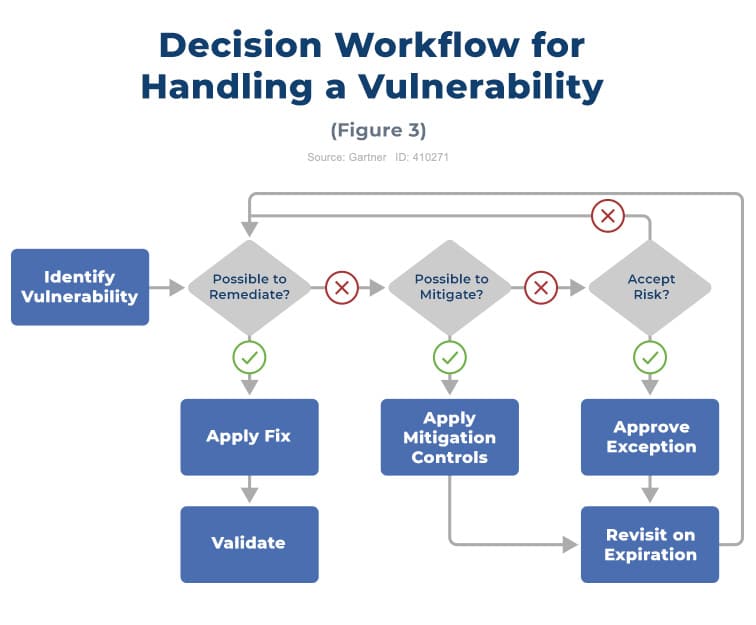
Step 1: Crafting the Malicious Markdown File
An attacker creates a normal-looking Markdown file. It might contain useful-seeming content: maybe it's a README for a software project, or technical documentation. But embedded in that file is a malicious link. Instead of pointing to a web URL, it uses an unverified protocol handler. On Windows, these handlers can include things like ms-settings:, shell:, or custom protocols that trigger system actions.
The attacker might use something like [Download Update](ms-settings: windowsupdate) or more dangerously, point to a URL that downloads an executable: [Click for more info](file:///C:/malicious.exe).
Step 2: Social Engineering
The attacker distributes this Markdown file through normal channels. It might come as an email attachment labeled "Project Documentation.md", or posted on a forum as part of a helpful-looking code snippet, or shared via file transfer. The user has no reason to suspect it's dangerous because Markdown files are plain text and seem harmless.
Step 3: Opening in Notepad
The user downloads or receives the file and opens it in Notepad. Windows 11 will often open .md files in Notepad by default. Now the Notepad preview pane is rendering that Markdown, and it's showing a clickable link that looks legitimate.
Step 4: The Click
The user clicks the link, thinking it will take them to a website or provide more information. But because Notepad doesn't validate the protocol, Windows instead executes whatever the attacker put in that link. This could launch a download, execute a command, or trigger a system action without any warning dialog.
Step 5: Code Execution
Once the malicious payload executes, an attacker could:
- Download and run ransomware
- Install a backdoor for persistent access
- Steal credentials from your system
- Modify system files
- Install spyware or keyloggers
- Any other action that malware typically does
All of this happens because of a single click on what looked like a legitimate link in a text editor.
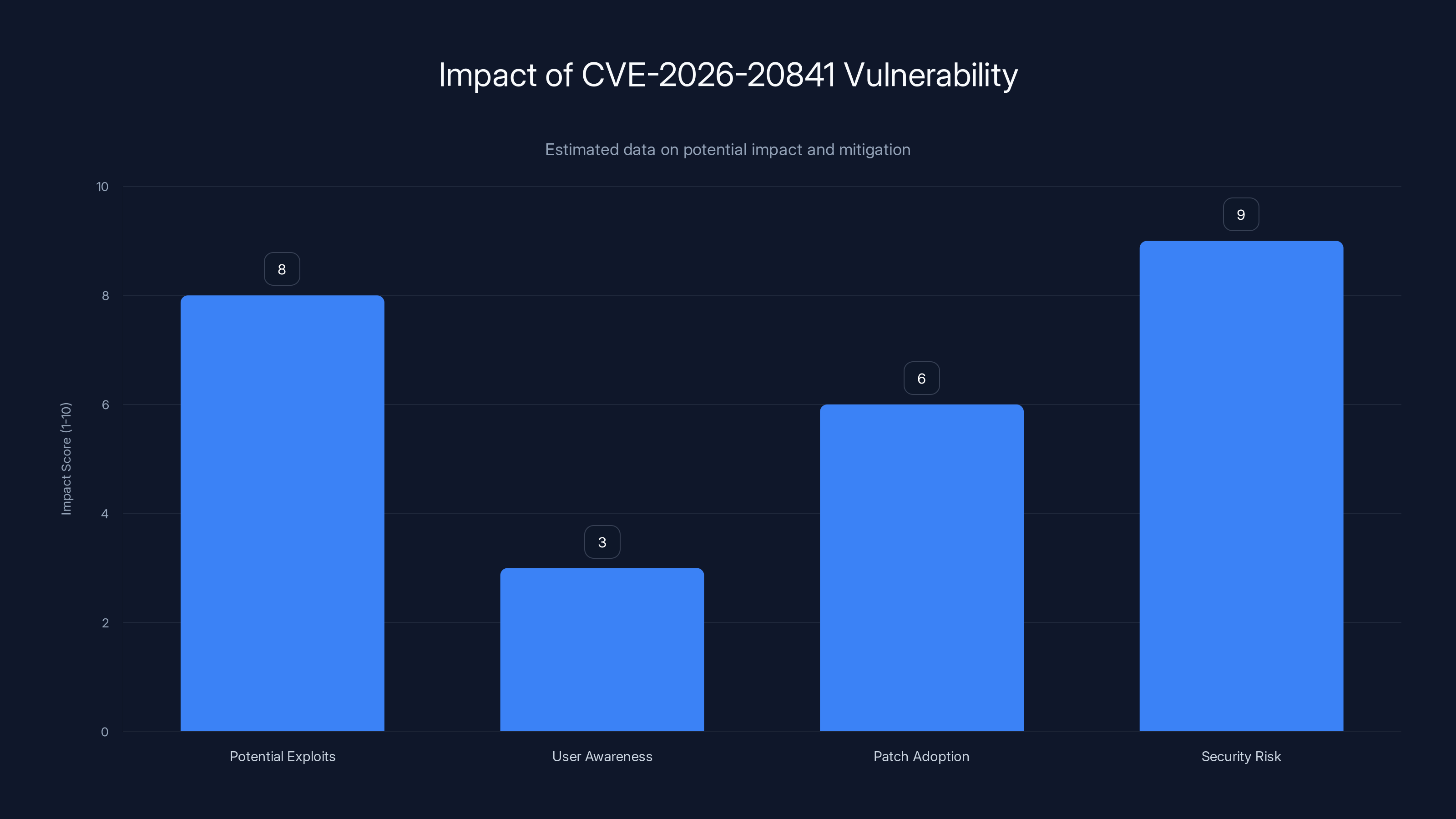
The CVE-2026-20841 vulnerability in Microsoft Notepad poses a high security risk (score: 9) due to its simplicity and potential for exploitation. User awareness is relatively low (score: 3), but patch adoption is moderate (score: 6). Estimated data.
The Technical Details: Protocol Handlers and Windows Security
To understand why this is such a problem, you need to know how Windows handles protocols. Every URL you click starts with a protocol identifier: http://, https://, ftp://, and so on. Windows has a registry system that maps these protocols to specific applications. When you click a mailto: link, Windows opens your email client. When you click an http:// link, your browser opens.
But Windows also has system protocols. ms-settings: opens the Settings app. file:/// accesses local files. shell: can trigger shell operations. Some of these protocols have security restrictions, but not all of them.
The vulnerability in Notepad occurs because the Markdown preview pane treats all protocols equally. It doesn't distinguish between safe web protocols and potentially dangerous system protocols. More importantly, it doesn't require user confirmation before launching a protocol action.
Most modern browsers have security protections against this. If you try to click a ms-settings: link on a website, your browser will block it and show a warning. But Notepad's Markdown preview didn't have these protections.
This is the key insight: applications that render user-controlled content (like Markdown) need to be extremely careful about what actions that content can trigger. Browsers learned this lesson through years of security vulnerabilities. Notepad apparently didn't have the same protections in place when Markdown support was added.
Why This Vulnerability Matters: The Bigger Picture
On the surface, this might seem like a minor issue. After all, you have to actively click a link. Compared to vulnerabilities where just opening a file causes code to execute, this seems less severe. But that's underestimating how effective social engineering is.
First, Markdown files are increasingly common. They're the default format for documentation in software development, used extensively in GitHub, GitLab, and countless other platforms. Developers regularly share Markdown files with each other, often without much scrutiny about their source. A developer receives a Markdown file from what looks like a legitimate source—perhaps a GitHub raw link, or a file from a colleague—and opens it without thinking twice.
Second, the click is deliberate but not necessarily informed. The attacker can craft the link text to seem harmless or even helpful: "[Click here to see more details]", "[Download documentation]", "[View the full spec]." Users click these kinds of links all the time. The difference between a link that opens a website and one that executes code is completely invisible to the user.
Third, this vulnerability highlights a pattern that's been concerning security researchers: Microsoft keeps adding features to Notepad that significantly increase its surface area. Markdown support, AI integration attempts, syntax highlighting—all of these add complexity to what was once one of the simplest applications on Windows. And with additional complexity comes additional security risk.
When Notepad was just a plain text editor, it was nearly impossible to exploit. You could open any file without worrying about malicious code execution. That's no longer true. And most users don't realize that opening a .md file in Notepad now means trusting the contents of that file in ways they previously didn't have to.
CVE-2026-20841: The Official Details
Microsoft officially disclosed CVE-2026-20841 in its regular Patch Tuesday update on February 11, 2025. Here are the technical details:
Vulnerability Type: Elevation of Privilege / Remote Code Execution
Affected Component: Microsoft Windows Notepad (specifically the Markdown rendering component)
Affected Versions: Windows 11 with Notepad versions that include Markdown preview support
CVSS Score: Indicating critical severity
Attack Vector: Network / Local (attackers could distribute malicious Markdown files)
User Interaction Required: Yes (user must click the malicious link)
Impact: Remote code execution with the privileges of the logged-in user
Patch Status: Available in the February 2025 Windows security update
Active Exploitation: No confirmed active exploitation in the wild at the time of disclosure
The important detail here is that Microsoft disclosed this vulnerability before it was actively exploited. This is the ideal security scenario. It gives users time to patch before attackers have a chance to weaponize the flaw. However, it also means that the vulnerability was discovered internally at Microsoft (or reported by a security researcher) and fixed before the broader security community knew about it.
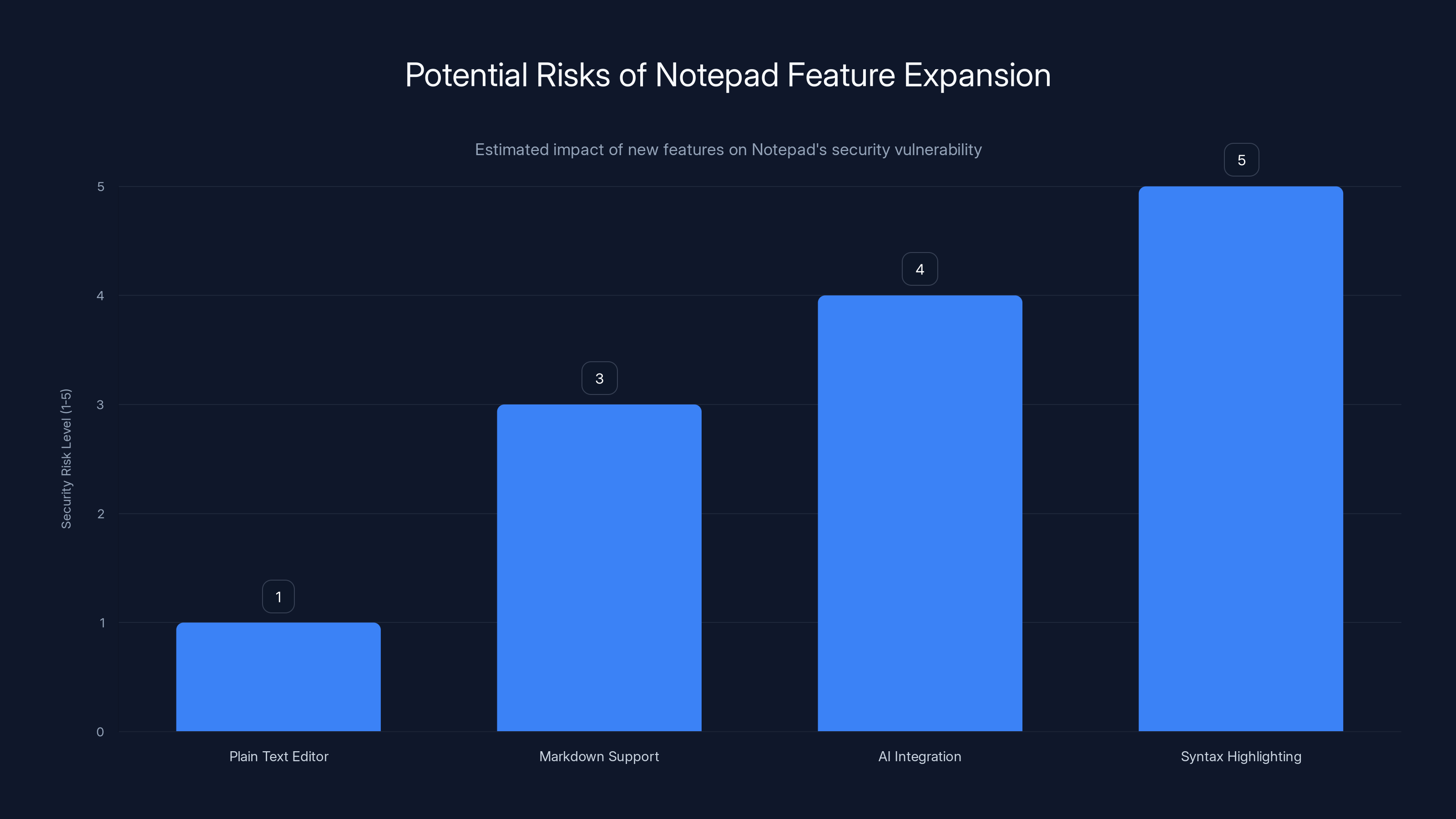
As Notepad evolves with new features like Markdown support and AI integration, its security risk level increases. Estimated data based on feature complexity.
Attack Scenarios: When This Could Actually Happen
Let's think about realistic scenarios where someone might encounter this vulnerability.
Scenario 1: Supply Chain Attack
An attacker compromises a GitHub repository that's used by thousands of developers. They modify the README.md file to include a malicious link disguised as something helpful: "View the installation guide". Developers update their local copy of the repository, open the README in Notepad to read the new instructions, click the link, and get compromised. This could affect hundreds or thousands of developers at once.
Scenario 2: Email Distribution
An attacker sends targeted emails to developers at a specific company, claiming to be from a vendor or partner. The email contains a Markdown file attachment labeled something like "Important_Security_Update.md". When the developer opens it in Notepad to read it, they see what appears to be a legitimate update notice with a link asking them to "Click here to confirm your access". The link executes malicious code.
Scenario 3: Trojanized Documentation
An attacker creates fake documentation for a popular open-source library and hosts it on a site that looks almost identical to the real documentation. They distribute links to this fake documentation through forums, Stack Overflow answers, and social media. When developers find this documentation and download the included Markdown files, opening them in Notepad triggers the exploit.
Scenario 4: Internal Threat
A disgruntled employee or contractor creates a Markdown file (like a README for a project) and shares it with colleagues. The file contains a malicious link. When colleagues open it, they get compromised. From there, the attacker has a foothold in the company's internal network.
All of these scenarios require deception and social engineering, but that's nothing new. Users fall for these tricks all the time. The difference is that in this case, users aren't opening a suspicious executable file—they're opening what appears to be harmless documentation.
The History of Markdown in Notepad: Why This Happened
To understand how this vulnerability made it into production, we need to look at why Microsoft added Markdown support to Notepad in the first place.
In May 2024, Microsoft announced that Notepad would get Markdown preview support. On the surface, this seems like a reasonable feature request. Markdown is everywhere. It's the default format for documentation, blog posts, README files, and countless other documents. Making Notepad into a Markdown preview tool seemed like a natural evolution.
But the timing and context matter. This came during a period when Microsoft was being criticized for turning Notepad into a bloated application. The company had already added features that many users didn't ask for, like AI integration and automatic syntax highlighting. Adding Markdown preview was part of a larger push to make Notepad do more.
The irony is that there are already excellent Markdown editors available: VS Code, Sublime Text, Typora, Obsidian, and many others. Notepad doesn't need to be a Markdown preview tool. But Microsoft seems committed to making every component of Windows more feature-rich, even when that increases complexity and risk.
When Markdown preview support was implemented, the developers likely didn't think through all the security implications of rendering user-controlled Markdown. They may have assumed that since it's a preview pane and not a full web browser, it wouldn't need the same security controls. That was a mistake.

Comparing This to Other Text Editor Vulnerabilities
Notepad isn't the only text editor that has faced security issues. Just around the same time this Notepad vulnerability was disclosed, another serious issue emerged with a different text editor.
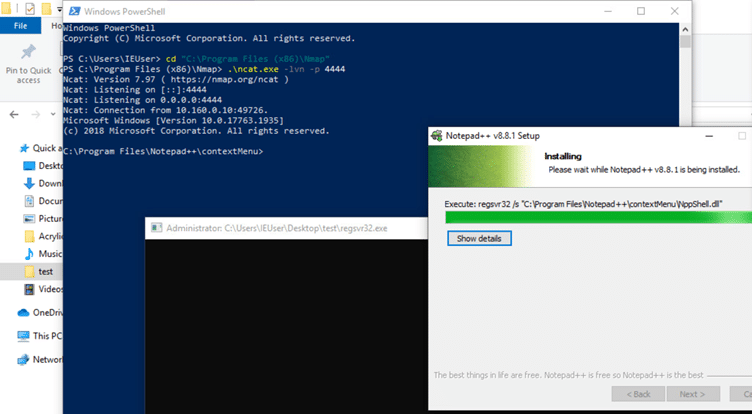
Notepad++ Security Issue
Notepad++, a popular third-party text editor for Windows, disclosed that some users had downloaded a malicious version of the application. The update had been trojanized by attackers, likely with the involvement of Chinese state-sponsored groups. Instead of the legitimate Notepad++ update, users received a version that included malware.
This is a different type of vulnerability from the Notepad Markdown issue, but it highlights a similar problem: even tools used by millions of developers can be compromised or made insecure. The difference is that the Notepad++ issue was about the distribution mechanism (the update download), while the Notepad issue is about the application's core functionality (how it renders content).
Historically, text editors have had relatively few vulnerabilities because they do one thing: display and edit text. But as editors become more complex—adding preview modes, rendering capabilities, language servers, and embedded interpreters—the attack surface grows. Each new feature is a potential security risk.


VS Code offers superior security features for handling Markdown files compared to Windows Notepad, making it a safer choice for users concerned about security. Estimated data.
How Microsoft Fixed the Vulnerability
Microsoft's fix for CVE-2026-20841 was to add proper protocol validation to Notepad's Markdown rendering. Here's what changed:
Before the patch: Notepad would render any URL in a Markdown link, including system protocol handlers, without validation or restrictions.
After the patch: Notepad now validates that links only use safe, web-based protocols (primarily http:// and https://). System protocols and unverified protocol handlers are either blocked or require explicit user confirmation.
Additionally, Microsoft likely added a warning or confirmation dialog before opening any external link from a Markdown preview. This matches best practices in modern browsers, which ask for confirmation before navigating to external sites.
The fix is straightforward: restrict what the preview pane can do. This is a common pattern in security—when you're rendering untrusted content, you need to sandbox it and limit its capabilities. Notepad was missing that sandbox.
The good news is that once you install the February 2025 Windows update, this vulnerability is no longer an issue. Microsoft has been consistent about releasing critical security patches through its regular Patch Tuesday cycle.
Who Should Be Concerned: Risk Assessment
Not everyone faces the same level of risk from this vulnerability. Let's break down the threat landscape.
High Risk:
- Developers and technical professionals who regularly work with Markdown files from various sources
- Users who download files frequently from the internet
- People who use Markdown in collaborative environments or open-source projects
- Organizations that share Markdown documentation internally
- Anyone who uses Notepad as their primary text editor for all file types
Medium Risk:
- Regular Windows users who occasionally open Markdown files
- Office workers who might receive Markdown files via email from vendors or partners
- Students and educators who work with Markdown documentation
- Users who browse GitHub and might clone repositories containing README files
Low Risk:
- Users who never open Markdown files
- People who use other text editors instead of Notepad
- Isolated systems without internet access
- Users on older Windows versions that don't have Markdown preview support
The key factor is how often you interact with Markdown files from sources you don't completely trust. If you're someone who downloads code from GitHub, reads documentation from various sources, or receives files via email, you should prioritize patching.
The Larger Security Concern: Feature Creep in System Applications
This vulnerability highlights a broader issue in software development: feature creep in system-critical applications. Windows Notepad has historically been one of the simplest, most reliable components of the operating system. It does one thing: edit and display plain text.
But over the last few years, Microsoft has been adding increasingly complex features to Notepad. Markdown preview is just the latest. Before that came syntax highlighting. There were also attempts to add AI-powered features and suggestions.
Each of these features adds complexity. And complexity is the enemy of security. When an application does one thing well, it's easier to audit, test, and secure. When an application tries to do many things, security issues start appearing.
This creates a tension in software design: users want features, but features introduce risk. Microsoft chose to add features, which led to this vulnerability. A different choice—keeping Notepad simple—would have avoided this particular security issue.
However, this is unlikely to change. Software vendors are driven by the desire to add features and compete with other applications. So we'll likely see more complex Notepad features in the future, and potentially more vulnerabilities as a result. The answer isn't to avoid using Notepad—it's to be aware of the risks and patch promptly.
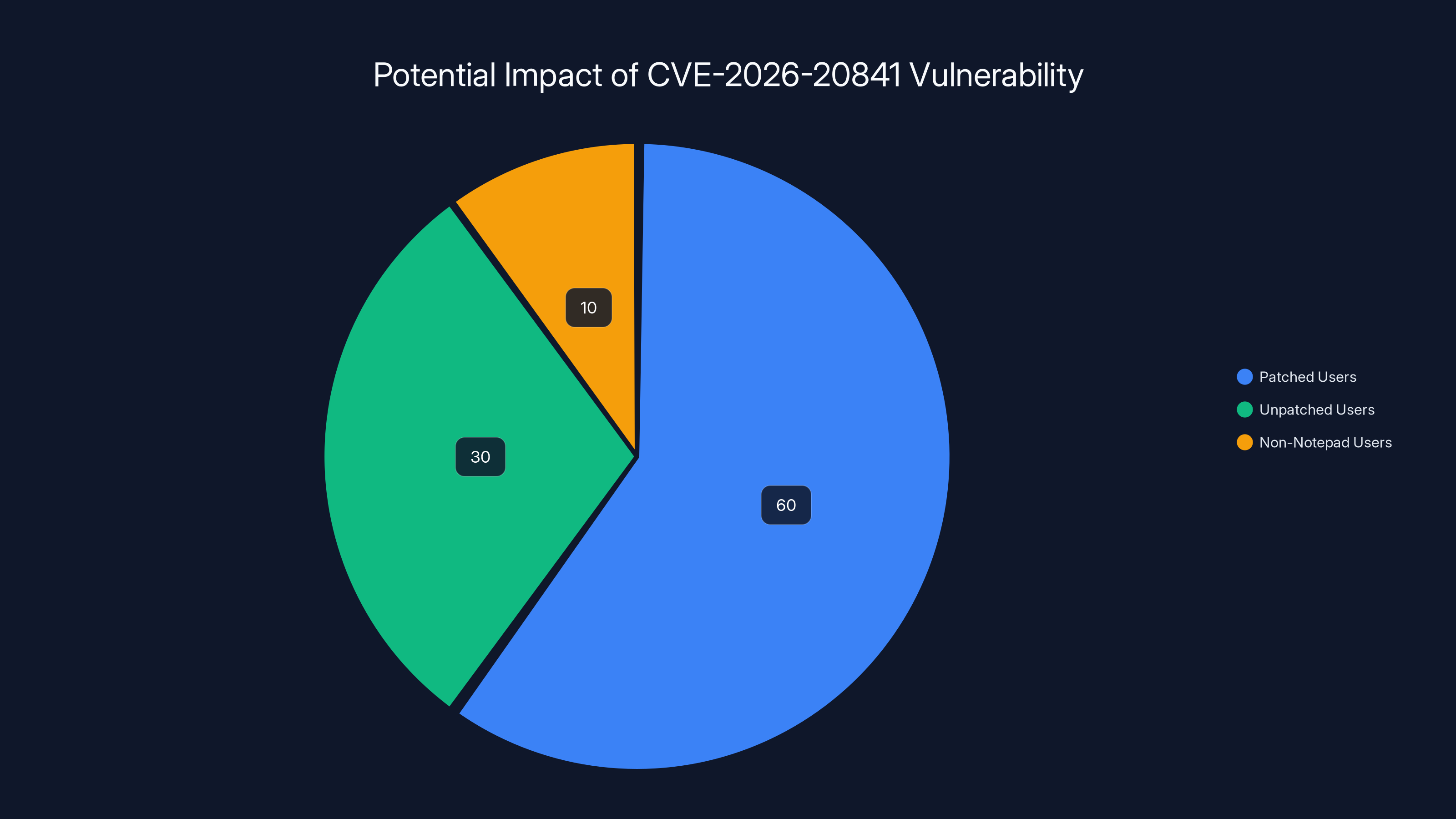
Estimated data shows that 30% of users might be vulnerable due to not applying the February 2025 update, while 60% are protected, and 10% use alternative editors.
Protecting Yourself: Practical Security Steps
If you use Windows Notepad with Markdown files, here's what you should do to protect yourself.
Immediate Actions:
First, update your Windows system immediately. Go to Settings > Update & Security > Windows Update and check for updates. Make sure you have the February 2025 patch installed. This patches CVE-2026-20841 and closes the vulnerability completely.
Second, be cautious with Markdown files from untrusted sources. If you receive a .md file via email or download it from an unfamiliar website, treat it with the same caution you'd apply to any executable file. Don't click on links in Markdown files unless you're absolutely sure they're legitimate.
Third, consider using a different editor for Markdown files if you're concerned about security. VS Code, for example, has better security controls around Markdown rendering and is actively maintained by Microsoft with security as a priority.
Ongoing Practices:
Keep your Windows system fully patched. Enable automatic updates if you haven't already. This ensures you'll get security patches as soon as they're released, not months later.
Use a reputable antivirus or security suite. These tools can often catch malware before it executes, providing an additional layer of defense beyond patching.
Be skeptical of files from untrusted sources. This is the oldest security advice, but it remains the most important. If you don't know and trust the source of a file, don't open it.
Use separate user accounts for different activities. If you use an administrator account for everyday tasks, malware running under that account has full access to your system. Using a standard user account for browsing and email reduces the impact if you do get compromised.
Alternative Text Editors for Markdown
If you've decided that you'd rather not use Notepad for Markdown files, or if you want a more feature-rich Markdown editing experience, there are several excellent alternatives.
Visual Studio Code (Free)
VS Code is Microsoft's own code editor, and it has excellent Markdown support. It includes preview panes, syntax highlighting, and extensions for Markdown-specific features. It's more complex than Notepad but significantly more powerful.
Markdown Specific Editors
- Typora: A clean, distraction-free Markdown editor with live preview
- Obsidian: A knowledge management system built around Markdown files
- Notion: A web-based alternative with collaborative Markdown editing
- Ghostwriter (Linux): A minimalist Markdown editor
- iA Writer: A premium option focused on distraction-free writing
Lightweight Alternatives
If you want something simpler than VS Code but better than Notepad, try:
- Sublime Text: A code editor with excellent Markdown support
- Geany: A lightweight code editor available on Windows
- Notepad2 or Notepad3: Lightweight Notepad replacements with additional features
The key advantage of these alternatives is that they either have better security controls (in the case of VS Code) or don't have Markdown preview features at all (keeping the attack surface smaller).

Windows Update and Patch Management: Getting Protected
Getting the patch for CVE-2026-20841 is straightforward, but it requires you to install Windows updates. Here's the process.
For Windows 11:
Go to Settings > System > About, then scroll down and click "Check for updates". Your system will check for available updates. If you're not fully patched, you'll see the February 2025 updates available. Click "Download and install".
Alternatively, go to Settings > Update & Security > Windows Update and click "Check for updates".
Your system will download the updates, and you'll be prompted to restart. Make sure you have time for this—it's important to complete the restart process to actually install the patches.
For Windows 10:
Windows 10 reached end of support in October 2025, but if you're still using it, updates are available through the same process: Settings > Update & Security > Windows Update. However, you should plan to upgrade to Windows 11, as Windows 10 will no longer receive security patches.
Enterprise Environments:
If you're in an organization with managed computers, your IT department likely has Windows Update configured to install patches automatically. You may not need to do anything—the patch might already be installed. You can check by going to Settings > About and looking at your OS build number.
The patch for this vulnerability is important enough that most organizations should prioritize installing it quickly. If your organization isn't patching Windows systems within days of patch release, that's a red flag for your security posture.

Future Implications: What This Means for Notepad
This vulnerability raises questions about the future direction of Notepad. Will Microsoft continue adding features? Or will this incident cause them to reconsider?
Based on Microsoft's recent behavior, they'll likely continue adding features but with more security scrutiny. This vulnerability will probably cause the company to implement security reviews for any new Notepad features going forward.
We might see:
- More restricted feature sets in Notepad (less complex interactions with content)
- Stronger security controls around rendering user-controlled content
- More prominent security warnings when opening files from untrusted sources
- Possible deprecation of Markdown preview in favor of recommending other tools
Long-term, this might lead to a bifurcation of the product: a minimal, simple Notepad for basic text editing, and VS Code or another tool for more complex scenarios like Markdown editing. But that's speculation.
What's certain is that this incident will influence how Microsoft (and other software vendors) think about adding features to existing applications. Security considerations should come earlier in the design process, not as an afterthought.
FAQs: Answering Your Questions About This Vulnerability
What exactly is CVE-2026-20841?
CVE-2026-20841 is a remote code execution vulnerability in Windows Notepad that affects how the application handles Markdown files. Attackers could craft malicious Markdown links that, when clicked, execute arbitrary code on the victim's computer instead of opening a web page.
How do I know if I'm vulnerable?
If you're using Windows 11 with Notepad and you haven't installed the February 2025 security update, you're potentially vulnerable. Check your Windows Update settings to see your current build number. If you're fully patched with the latest updates, you're protected.
Can this vulnerability affect me if I just view Markdown files and never click links?
No, you have to actually click a link in a Markdown file for the vulnerability to be exploited. Simply opening or viewing a Markdown file won't trigger the exploit. However, this is why the vulnerability is concerning—users click links all the time without thinking about the consequences.
Is there any evidence that attackers have used this vulnerability?
Microsoft confirmed that there's no evidence of active exploitation of CVE-2026-20841 in the wild at the time of disclosure. However, that doesn't mean attackers won't use it in the future, which is why patching is important.
Do other Markdown editors have the same vulnerability?
It's unlikely that other Markdown editors have the exact same vulnerability, as they implement their rendering differently. However, any application that renders untrusted Markdown content could potentially have similar security issues if not designed carefully. This is why it's important to use well-maintained, security-conscious tools.
Should I stop using Notepad for Markdown files?
You don't need to avoid Notepad entirely, but after patching, you should be cautious about opening Markdown files from untrusted sources. If you work with Markdown files regularly from multiple sources, switching to a dedicated Markdown editor like VS Code or Typora is a good idea for both security and functionality.
How long did it take Microsoft to fix this vulnerability?
The timeline isn't entirely clear from public information, but Microsoft disclosed this vulnerability in February 2025, which suggests it was discovered and patched relatively quickly before public disclosure. This is the preferred disclosure model—fixing the vulnerability before making it public.
Can I disable Markdown preview in Notepad?
Currently, there's no built-in setting to disable Markdown preview in Notepad. Your options are to use a different text editor, upgrade to the patched version, or simply avoid clicking links in Markdown files.
What if I'm using an older version of Notepad?
Older versions of Notepad (before Markdown support was added in May 2024) don't have this vulnerability. The feature was only added to relatively recent versions of Windows 11. If you're on Windows 10 or an earlier version of Windows 11, you don't need to worry about this specific issue.
Are there any known exploits publicly available for this vulnerability?
As of the publication date, there are no publicly available exploits for CVE-2026-20841. Microsoft patched the vulnerability before detailed exploitation techniques were published. This protects users who patch promptly.
Conclusion: Security in the Age of Feature-Rich Applications
CVE-2026-20841 is a reminder that security vulnerabilities can hide in the most unexpected places. A simple text editor, a common file format, and a basic user action (clicking a link) combine to create a serious security risk. This vulnerability isn't unique in that regard—it's just the latest example of how feature complexity and security are often at odds.
The good news is that Microsoft responded quickly. The vulnerability was patched in the February 2025 Windows update, and there's no evidence of active exploitation. Users who keep their systems updated don't need to worry.
But the broader lesson is more important: be thoughtful about the tools you use, especially when those tools interact with content from untrusted sources. Don't assume that a simple-looking application like Notepad is incapable of causing harm. And always, always keep your systems patched.
For developers and technical professionals, this is a good reminder to be cautious with files you download from the internet. For everyone else, it's a useful lesson in why security updates matter and why you shouldn't ignore those Windows Update notifications.
The fact that this vulnerability has already been patched means it's a non-issue for informed users. But for those who remain unpatched, it's a significant security risk. If you're one of them, stop reading this article and go install the latest Windows updates. Your security depends on it.
The battle between features and security is ongoing in software development. Vendors want to add features that users request. But each feature increases complexity, and complexity breeds vulnerabilities. The answer isn't to avoid using modern software—it's to stay informed, stay patched, and stay skeptical of content from untrusted sources. In a world of increasing digital threats, that's the security posture that will keep you protected.
Key Takeaways
- CVE-2026-20841 is a critical remote code execution vulnerability in Windows Notepad affecting Markdown file handling, patched in February 2025
- Attackers can exploit the flaw by tricking users into clicking malicious links in Markdown files, which launch unverified system protocols instead of web pages
- The vulnerability exists because Notepad doesn't properly validate protocols in Markdown preview panes, unlike modern web browsers with protocol security controls
- Users should immediately install the February 2025 Windows security update and remain cautious with Markdown files from untrusted sources
- This incident highlights the broader challenge of feature complexity versus security in system applications, as Notepad's new Markdown support introduced an unexpected attack surface
Related Articles
- BeyondTrust RCE Vulnerability CVE-2026-1731: What You Need to Know [2025]
- N8N Critical Vulnerabilities Explained: CVE-2025-68613 & CVE-2026-25049 [2025]
- 800,000 Telnet Servers Exposed: Complete Security Guide [2025]
- AI-Powered Phishing: How LLMs Enable Next-Gen Attacks [2025]
- AI Cybercrime: Deepfakes, Phishing & Dark LLMs [2025]
- Hyatt Ransomware Attack: NightSpire's 50GB Data Breach Explained [2025]
![Microsoft Notepad Markdown Security Flaw: What You Need to Know [2025]](https://tryrunable.com/blog/microsoft-notepad-markdown-security-flaw-what-you-need-to-kn/image-1-1770835040253.jpg)



