N8N Critical Security Vulnerabilities: Complete Guide to CVE-2025-68613 and CVE-2026-25049
If you're running n8n in production, you need to read this. Right now.
In late December 2025, the automation community discovered something that should've kept n8n's security team up at night. A patch designed to fix a critical remote code execution vulnerability actually left the door wide open. We're talking about a security flaw so severe that an attacker with the ability to create or edit a single workflow can take complete control of your underlying server. Not just access data. Not just read secrets. Complete, unrestricted command execution.
This isn't theoretical. Proof-of-concept code is already public. The vulnerability impacts thousands of n8n instances across enterprises, startups, and development teams. Organizations sharing multi-tenant n8n deployments are particularly exposed because an attacker can pivot between tenants, stealing data from multiple companies simultaneously.
Here's what you need to know: how these vulnerabilities work, what's actually at risk, which versions are impacted, and exactly what to do right now to protect your workflows and infrastructure.
The Timeline: How a Patch Created a Bigger Problem
The story starts in December 2025 when n8n released a patch for CVE-2025-68613, a critical vulnerability in the workflow expression evaluation system. The patch seemed solid on the surface. The developers identified the issue, pushed a fix to version 2.4.0, and moved on.
But security researchers at Endor Labs and the team at Pillar Security kept digging. What they found was alarming: the patch was incomplete. The vulnerability wasn't actually closed. It was transformed into something arguably worse because it gave a false sense of security while attackers could still exploit it through a different vector.
By December 30, 2025, researchers had already weaponized the flaw. A public proof-of-concept appeared online, making it trivial for anyone to test if a target n8n instance was vulnerable. Within weeks, n8n developers released version 2.5.2 to address the follow-up vulnerability, tracked as CVE-2026-25049. But the damage was already done—awareness was low, many instances remained unpatched, and the attack surface was clear.
Understanding CVE-2025-68613: The Original RCE Flaw
What Went Wrong in the Expression Evaluator
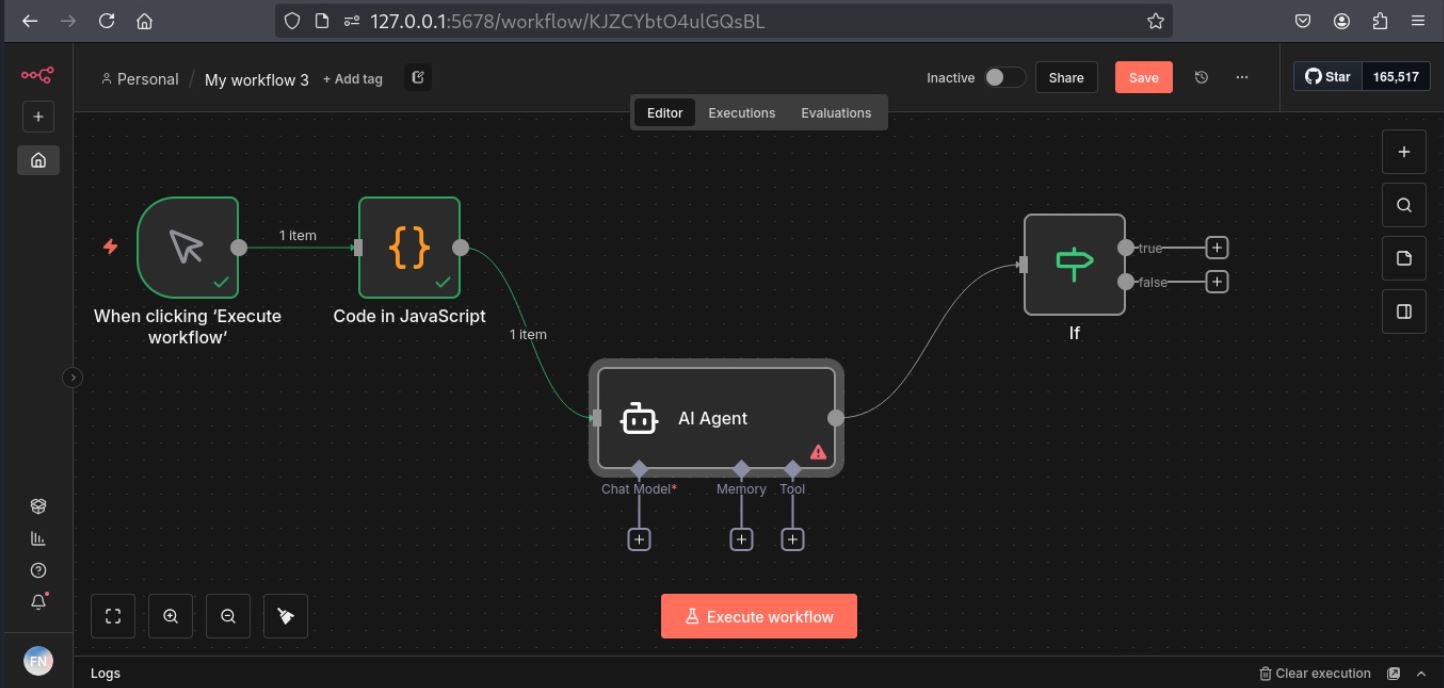
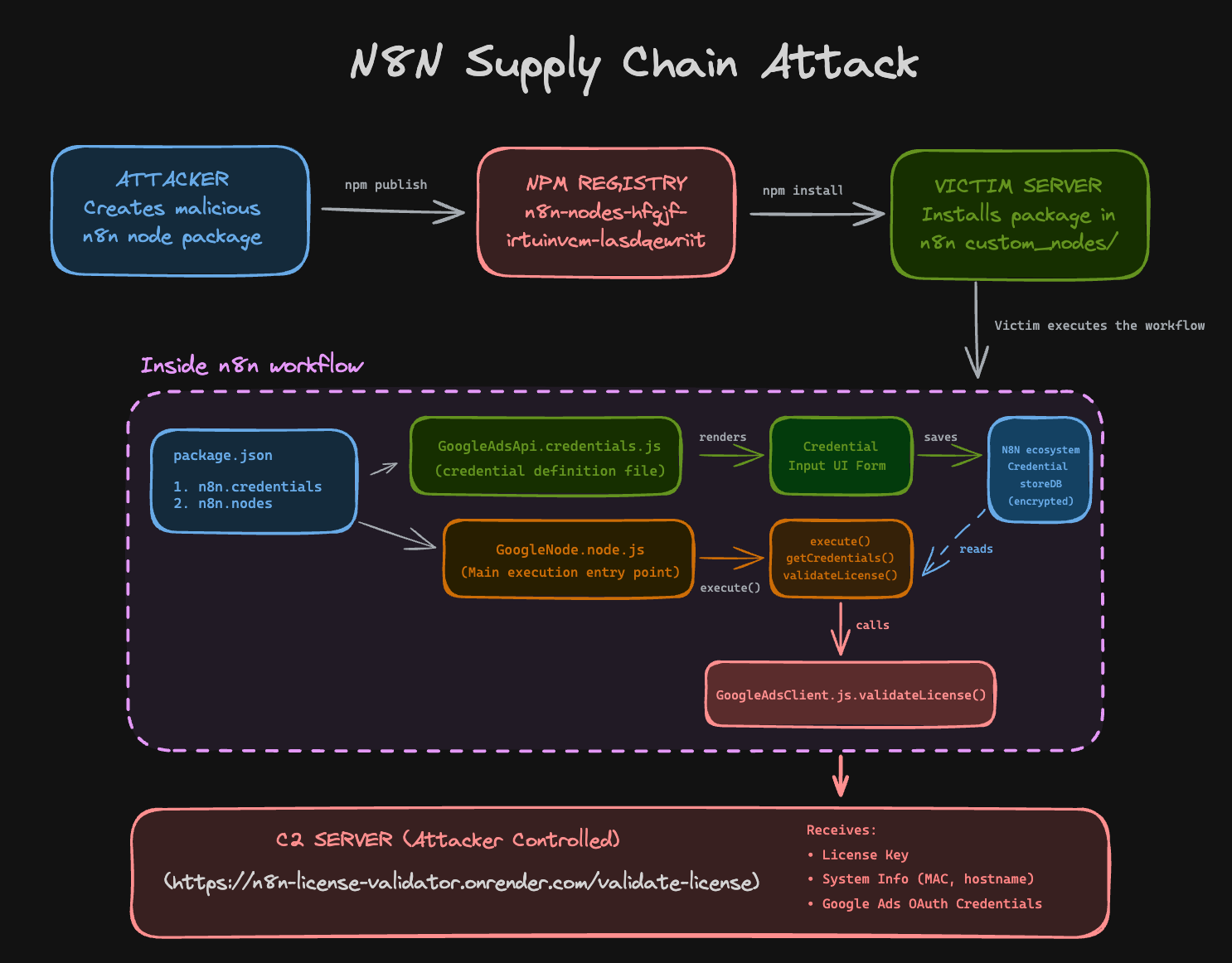
N8N's power comes from its expression system. Users write JavaScript-like code in workflow nodes to manipulate data, make conditional logic, and orchestrate complex automation. This expression evaluator is the heart of n8n's flexibility—it's also where this vulnerability lives.
The original vulnerability (CVE-2025-68613) existed in how n8n handled the evaluation of these expressions. Specifically, the issue was in the sanitization function that's supposed to prevent malicious code from breaking out of the sandbox environment.
Think of it like a prison. The expression evaluator is the prison, and the sandbox is supposed to be the walls. The guards (sanitization functions) are responsible for making sure nobody tunnels out. But the guards had a shift change, and some of them weren't properly trained. Attackers could social-engineer specific scenarios where the guards would let them through.
The vulnerability allowed attackers to craft specially formed expressions that would bypass the sandbox entirely. Once outside the sandbox, they could execute arbitrary system commands with the same privileges as the n8n process. If n8n is running as root (a common configuration in containerized environments), the attacker gains root access. If it's running as a service user, they still get full control over the server.
The Attack Surface
Here's what makes this particularly dangerous: you don't need special privileges to exploit it. You don't need to be a registered user. You don't need to guess credentials. If your n8n instance allows unauthenticated users to create or edit workflows—which many do for demo purposes, API endpoints, or team collaboration—the vulnerability is trivially exploitable.
Imagine you're a small startup using n8n's cloud offering or self-hosted version. You invite your team members to collaborate on workflows. An attacker gets hired as a contractor, or a disgruntled employee creates an attack, or a compromised third-party integration provides access. They click "create workflow," write a malicious expression, and suddenly they're running system commands on your infrastructure.
The attack doesn't require knowledge of n8n internals. Endor Labs published a working PoC that a junior developer could execute. Bleeping Computer reported that any attacker needing to exploit this would find detailed exploitation guides in security forums and exploit databases.
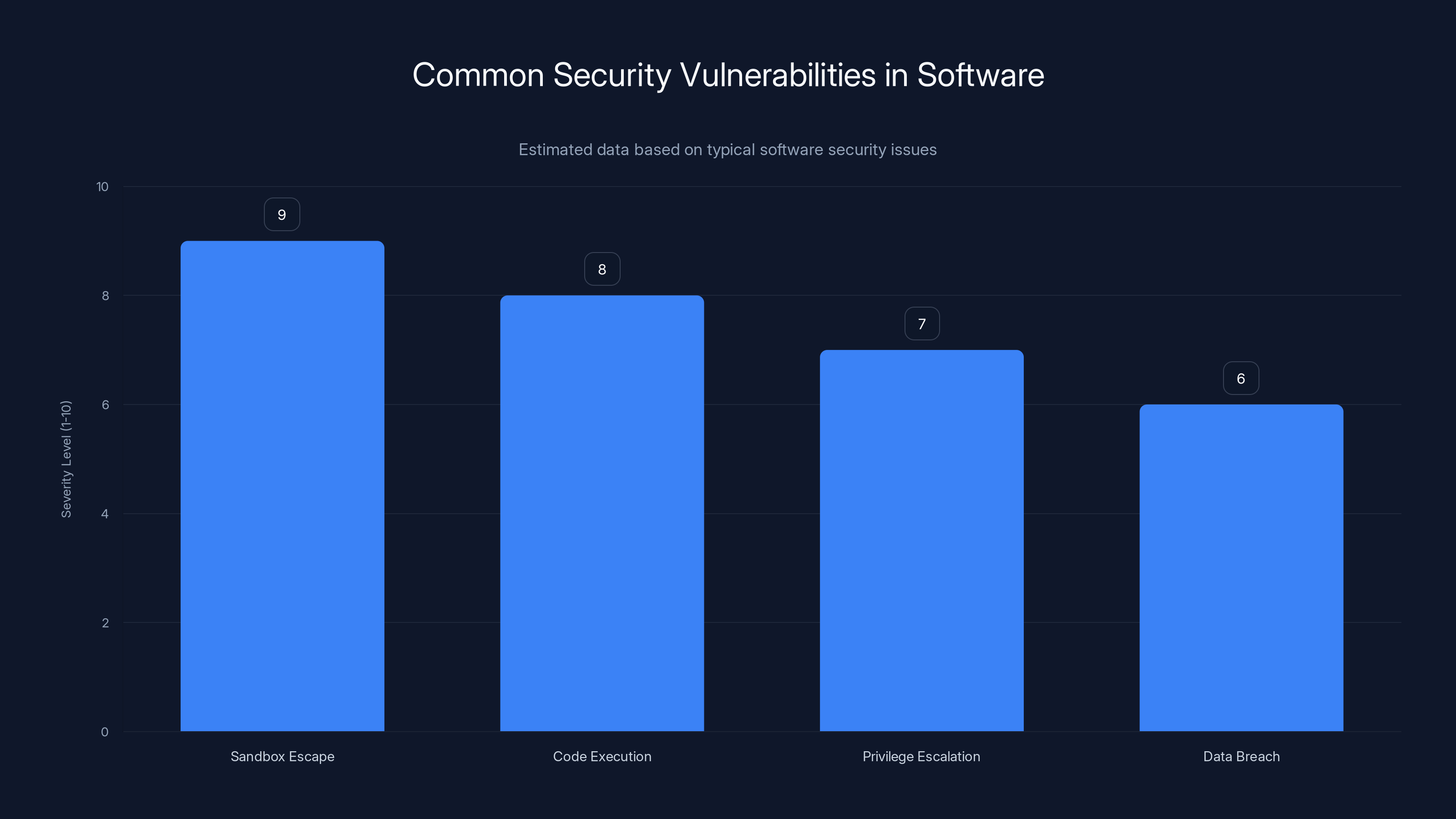
Sandbox escape is one of the most severe vulnerabilities, often rated at a 9 out of 10 in severity due to its potential to allow full system access. Estimated data.
CVE-2026-25049: The Incomplete Fix That Became a Second Vulnerability
Why The Original Patch Failed
After releasing version 2.4.0, n8n's developers thought they'd solved the problem. The patch modified the sanitization function to add additional checks. They tested it. It passed security reviews. They announced it as fixed.
But researchers noticed something: the patch only addressed one specific method of bypassing the sandbox. It fixed the front door while leaving the side door open.
According to Endor Labs' analysis, the issue was in how the sanitization function handled property access keys in attacker-controlled code. The function assumed these keys would always be strings when accessed by normal code. But attackers realized they could craft expressions where keys aren't strings—they could be objects, numbers, or complex data structures that the sanitization logic didn't account for.
It's like a bank fixing one type of lock on their vault door but forgetting that the same lock type protects multiple other entry points. An attacker sees that one entry point is harder now, looks for alternatives, and finds another identical lock controlling access to the same vault.
The Root Cause Analysis
The fundamental problem wasn't a missing patch. It was a flawed approach to sandboxing. N8N was trying to prevent code execution by filtering what users could write. But filtering is fragile. For every filter you write, there are dozens of ways to bypass it:
- Using alternative JavaScript methods to achieve the same result
- Chaining operations to obfuscate intent
- Leveraging built-in functions that weren't explicitly blocked
- Exploiting prototype pollution
- Using object notation tricks
A proper sandbox doesn't rely on filtering what you can do. It relies on being able to do nothing dangerous at all, regardless of how creative the attacker gets.
N8N's architecture was fundamentally designed around a filtering approach rather than a true isolation approach. This is a common problem in automation platforms where you need to offer users powerful scripting capabilities while preventing them from breaking out.
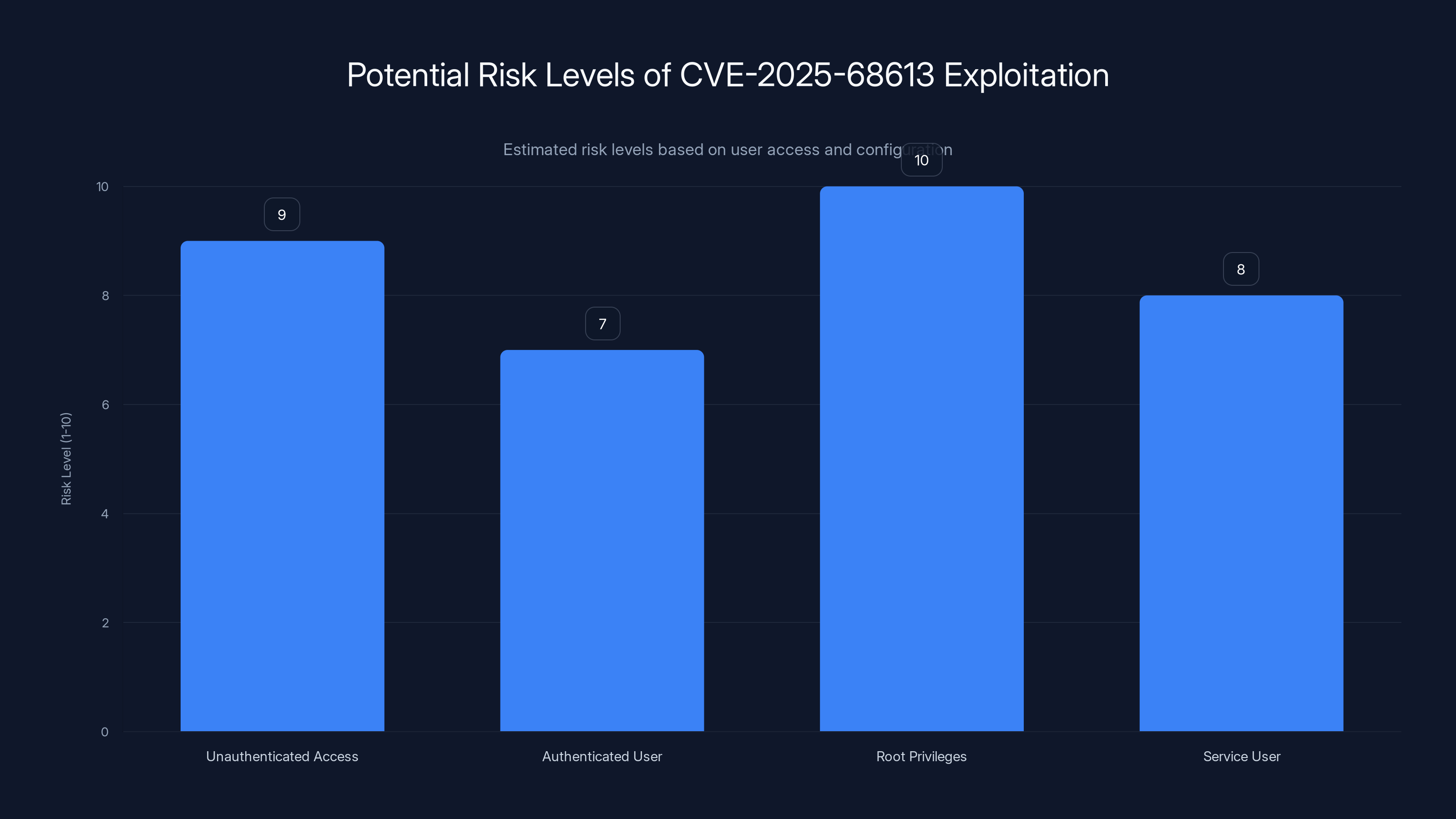
The CVE-2025-68613 vulnerability poses the highest risk when n8n is configured with root privileges, but remains significantly risky even with service user access. (Estimated data)
What's Actually at Risk: The Real Impact
Secrets and API Keys
Every n8n installation stores secrets. API keys for third-party integrations like Slack, GitHub, Stripe, AWS. OAuth tokens for connected services. Database credentials. SSH keys. All of this sensitive data is stored in n8n's database and loaded into memory when workflows run.
An attacker executing arbitrary code on the n8n server can:
- Read environment variables where secrets might be stored
- Access the database files directly
- Dump memory to find tokens
- Read configuration files containing credentials
- Query the n8n API as an authenticated service
One company running n8n might have 50+ API keys connected to their ecosystem. An attacker gains all of them in seconds.
Cross-Tenant Data Exposure
For organizations using n8n's SaaS offering or running multi-tenant self-hosted instances, the risk extends beyond a single tenant.
Multi-tenant n8n installations run multiple customers' workflows in the same environment. If an attacker gains code execution on the server, they can potentially:
- Access workflows from other customers
- Read data stored by other tenants
- Access secrets configured by competitors or other companies
- Modify other customers' workflows to steal their data or inject malicious code
- Create persistent backdoors affecting all tenants
This is a nightmare scenario for n8n's managed service customers. A single vulnerability in one company's workflow could compromise hundreds of other organizations using the same deployment.
Business Continuity
Beyond data theft, an attacker with code execution can:
- Delete or corrupt workflows, stopping critical automation
- Modify data in downstream systems (delete Slack channels, modify database records, trigger false alerts)
- Consume cloud resources, spiking your AWS/Azure bill
- Launch attacks against your infrastructure or customers
- Plant malware for long-term persistence
N8N often runs critical automation: customer onboarding, payment processing, data synchronization, alert routing. When it goes down or gets compromised, businesses suffer immediate operational impact.
Which Versions Are Affected?
The Version Timeline
Not all versions of n8n have this vulnerability. If you're running an old version, you might be affected by the original CVE-2025-68613. If you updated to 2.4.0, you might think you're safe but you're actually affected by CVE-2026-25049. Only the very latest versions are truly safe.
Here's the vulnerable version breakdown:
CVE-2025-68613 (Original RCE):
- All versions prior to the 2.4.0 release in December 2025
- Affects self-hosted and cloud instances
- Publicly known for weeks before patch release
CVE-2026-25049 (Incomplete Patch):
- Version 2.4.0 (the patch that was supposed to fix it)
- All versions between 2.4.0 and 2.5.2
- All 1.x versions prior to 1.123.17
Patched Versions:
- n8n 2.5.2 and later
- n8n 1.123.17 and later
If you're running n8n 2.0-2.5.1 or 1.x before 1.123.17, you're exposed. No exceptions. No workarounds. The vulnerability is trivially exploitable.
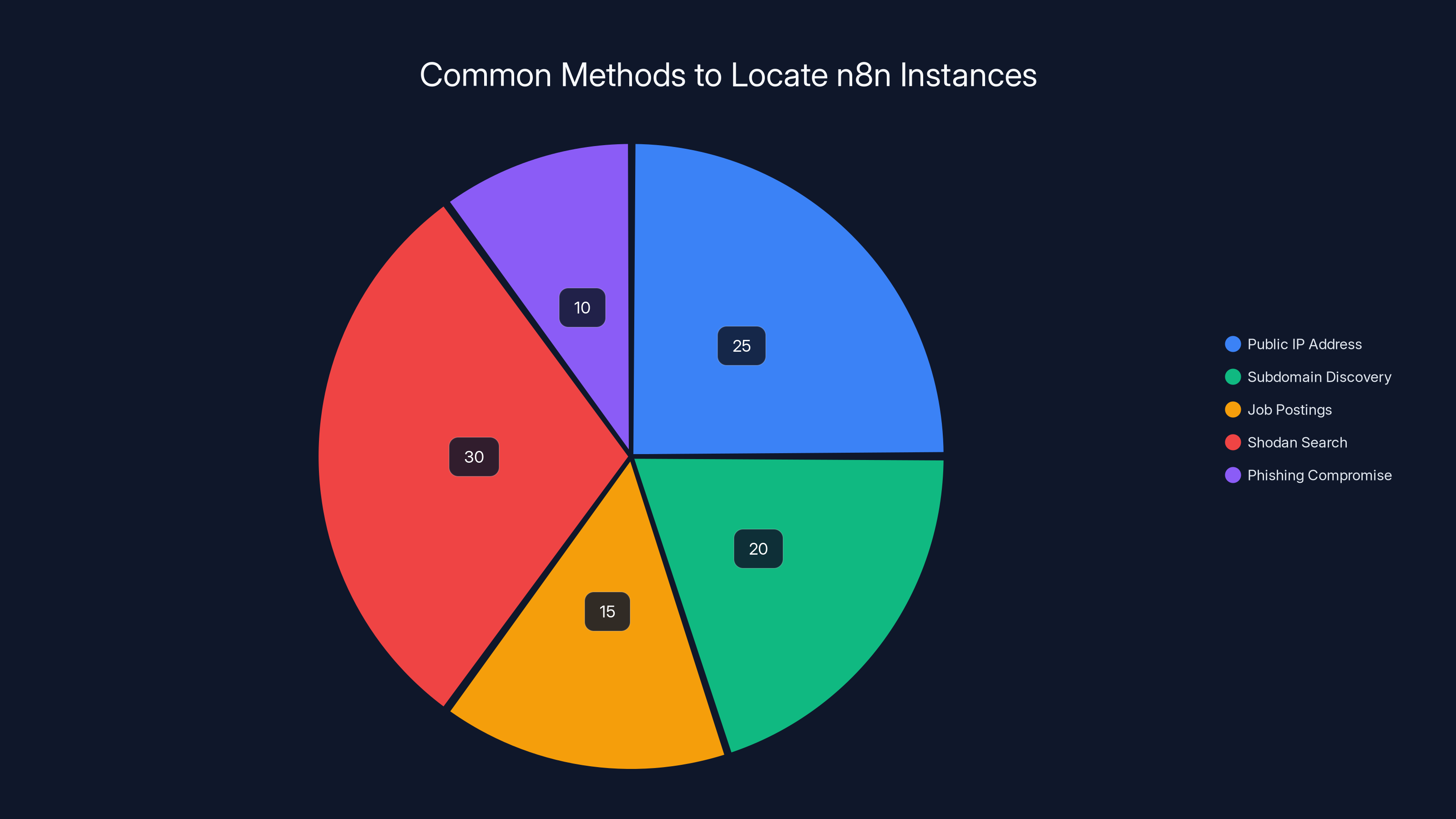
Estimated data showing the distribution of methods attackers might use to locate n8n instances, with Shodan searches being the most common.
Step-by-Step: How An Attack Would Actually Work
Step 1: Reconnaissance
An attacker starts by identifying an n8n instance. They might find it through:
- A public IP address disclosed in a GitHub commit
- A subdomain like
automation.company.comorn8n.company.com - A company mentioning n8n in job postings or documentation
- Checking Shodan or similar services for n8n instances
- Gaining access through a phishing compromise that includes VPN access
Once they've located an instance, they check if it allows unauthenticated workflow creation. For many n8n deployments, this is the default.
Step 2: Gaining Access or Exploiting Anonymous Creation
The attacker needs to either:
- Create a new workflow (if anonymous creation is allowed)
- Get hired as a contractor or integrate as a third party
- Phish credentials from an existing user
- Discover a compromised integration
For the purposes of this demonstration, let's assume anonymous workflow creation is enabled. They go to the "Create Workflow" button and start writing their attack.
Step 3: Crafting The Malicious Expression
Instead of a normal expression that processes data, they write code that breaks out of the sandbox. The exact payload varies depending on the n8n version and JavaScript engine, but the basic idea is the same:
this.constructor.constructor("return process.mainModule.require('child_process').execSync('whoami')")().toString()
Or using alternative methods that work around the sanitization:
Object.getOwnPropertyDescriptor(this.constructor.prototype, 'constructor').value.constructor("return require('child_process').execSync('cat /etc/passwd')").call()
The key insight is that the sanitization function was designed to block certain patterns. But JavaScript offers dozens of ways to achieve the same result. By chaining function calls or using property access tricks, attackers can execute code the filter didn't anticipate.
Step 4: Execution and Persistence
Once the initial command executes, the attacker:
- Establishes persistence (adds a cron job, creates a new user, plants a backdoor)
- Exfiltrates sensitive data (API keys, database credentials, customer data)
- Moves laterally (accesses connected services, explores the internal network)
- Covers tracks (clears logs, removes evidence)
The whole attack might take 10 minutes from initial discovery to complete compromise.
Checking If You're Vulnerable: A Practical Assessment
Method 1: Version Check
The fastest way to determine if you're vulnerable is simply checking your version:
- Log into your n8n instance
- Click Settings (gear icon) in the bottom left
- Click "About"
- Compare your version against the vulnerable list above
If you're on 2.5.2 or 1.123.17 or later, you're patched. Anything else needs immediate attention.
Method 2: Check Deployment Configuration
For self-hosted deployments, verify your version in your configuration:
Docker:
bashdocker inspect <container-id> | grep n8n
Kubernetes:
bashkubectl describe pod <n8n-pod> | grep image
Direct Installation:
bashcd /path/to/n8n && npm list n8n
Method 3: API Endpoint Check
You can query the n8n API directly to get version information:
bashcurl https://your-n8n-instance/api/version
This returns JSON with the current version number.
Method 4: Assess Your Attack Surface
Beyond just checking the version, evaluate your actual risk:
- Who can create workflows? If it's public or contractor-accessible, risk is high
- What secrets are stored? Count how many API keys and credentials are configured
- Is it multi-tenant? If yes, the impact of compromise extends to all customers
- What's your backup strategy? Can you recover if the instance is compromised?
- Is network access restricted? Can only trusted sources reach the n8n server?
Answer these questions honestly. Your risk level depends on multiple factors, not just the version number.
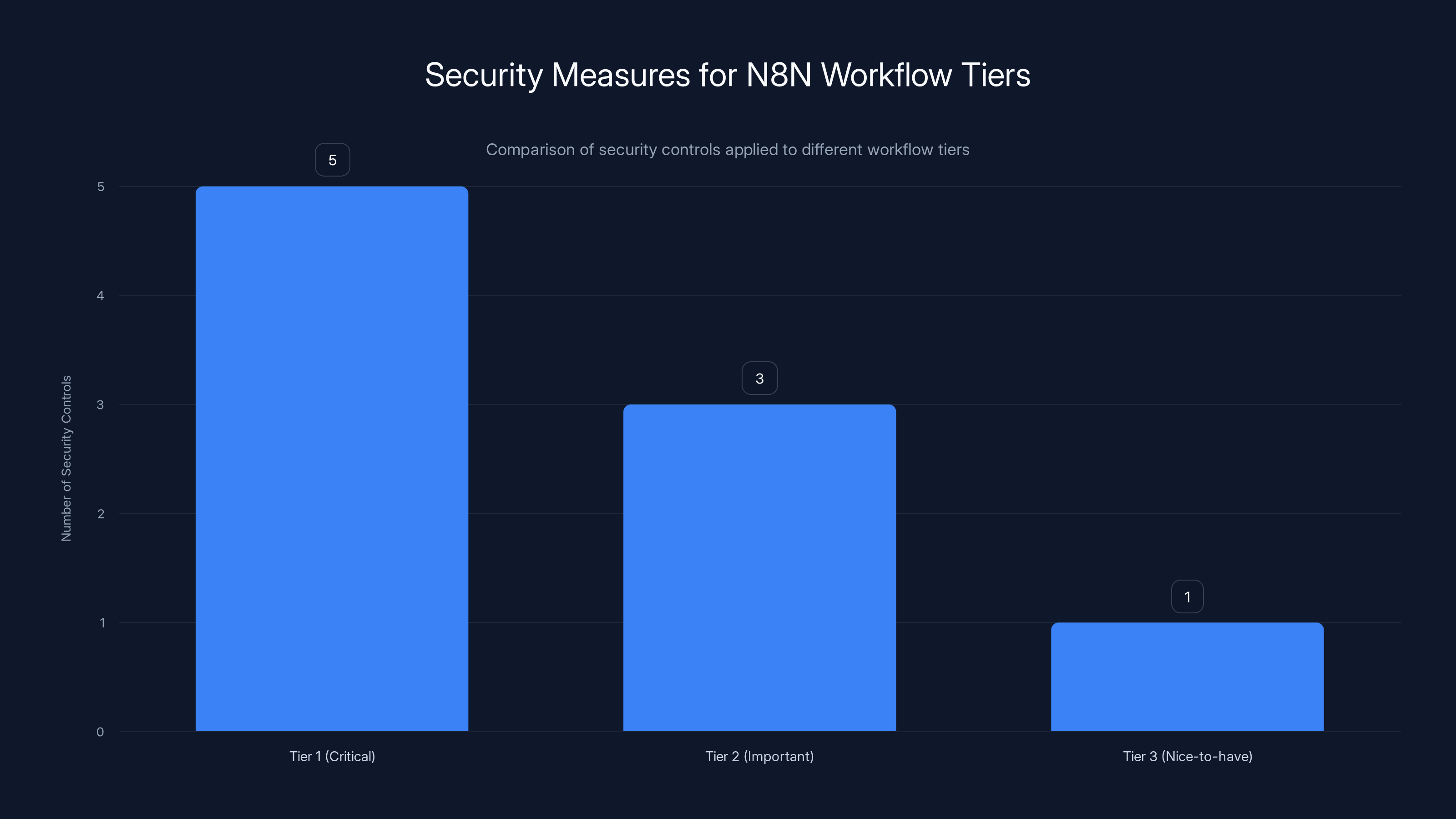
Tier 1 workflows, such as payment processing, have the most security controls, while Tier 3 workflows, like Slack reminders, have the least. Estimated data based on typical security practices.
Immediate Actions: What To Do Right Now
Priority 1: Update Immediately (Target: Today)
If you're running vulnerable versions, this is your top priority.
For Self-Hosted Deployments:
- Backup everything. Before touching anything, create a complete backup of your n8n instance and database:
bash# If using Docker
docker exec <n8n-container> n8n export --backup --output=/tmp/n8n-backup.json
# If using direct installation
n8n export --backup --output=/tmp/n8n-backup.json
-
Schedule maintenance window. Don't update during business hours unless your automation isn't critical. N8N will need to restart.
-
Update to the patched version:
bash# Docker
docker pull n8nio/n8n:2.5.2 # or latest
docker stop <container-id>
docker rm <container-id>
docker run --name n8n -d n8nio/n8n:2.5.2
# Direct installation
cd /path/to/n8n
npm update n8n
pm2 restart n8n # or your process manager
- Verify the update:
bashcurl https://your-n8n-instance/api/version
- Test critical workflows. Don't assume everything works after the update. Test your most important automations.
For N8N Cloud (Managed):
If you're using n8n's official cloud offering, the company claims automatic updates are applied. You should verify this by:
- Checking your account settings for any security notices
- Confirming your version is 2.5.2 or later
- Contacting n8n support to confirm your account has been patched
Don't trust that it happened automatically—verify it.
Priority 2: Temporary Workarounds (While Updating)
If you can't update immediately, implement these mitigations:
Restrict Workflow Permissions:
- Go to Settings > Users
- Create a specific user role that can only execute workflows, not create them
- Assign all non-admin users to this restricted role
- Document who has creation privileges
Limit Network Access:
- Move your n8n instance behind a VPN or corporate network
- Restrict access to specific IP addresses only
- Disable public internet access if possible
- Use a web application firewall to block suspicious patterns
Harden the N8N Process:
- Run n8n as a service user, not root:
bashchown -R n8n:n8n /path/to/n8n
su - n8n -s /bin/bash
- Disable unnecessary Node.js permissions:
bashnode --expose-gc --max-old-space-size=2048 /path/to/n8n
- Use AppArmor or SELinux to restrict what the n8n process can do
Monitor for Attacks:
- Enable access logs and review them daily
- Monitor system resource usage for unexpected spikes
- Set alerts on failed login attempts
- Watch for new workflow creation by unexpected users
These mitigations reduce (but don't eliminate) your risk while you're working on the actual patch.
Long-Term Security: Building a Resilient N8N Infrastructure
Architecture Best Practices
Network Segmentation:
Don't expose n8n directly to the internet. Put it behind a reverse proxy (nginx, Cloudflare) that requires authentication before anything reaches n8n:
Internet → Reverse Proxy (Auth Required) → N8N Instance → Internal Services
This ensures only authenticated requests reach n8n, even if a vulnerability exists.
Run As Non-Root:
Always run n8n as a dedicated service user with minimal privileges. If compromised, the attacker inherits only that user's permissions, not root:
bashuseradd -m -s /bin/false n8n
chown -R n8n:n8n /opt/n8n
su - n8n -s /bin/bash # Run as n8n user
Secrets Management:
Don't store API keys directly in n8n. Use a dedicated secrets manager:
- AWS Secrets Manager for cloud deployments
- HashiCorp Vault for on-premise
- Sealed Secrets for Kubernetes
Configure n8n to fetch secrets from these systems instead of storing them locally.
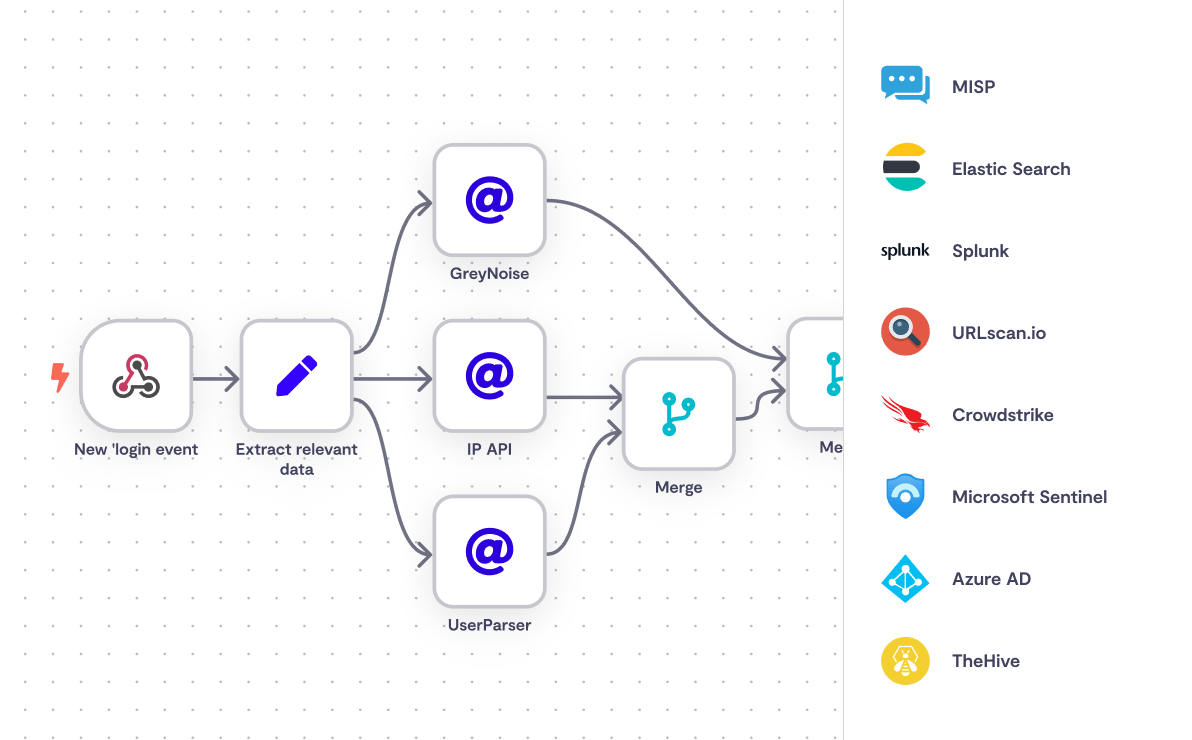
Monitoring and Detection
Log Aggregation:
Collect all n8n logs centrally using:
- Splunk
- ELK Stack (Elasticsearch, Logstash, Kibana)
- Datadog
- CloudWatch
Alerts should fire on:
- Unexpected workflow creation
- Failed authentication attempts
- Process execution outside normal parameters
- New user registration
Anomaly Detection:
Set up alerts for unusual patterns:
IF workflow_creation_rate > 5_per_hour THEN alert
IF failed_login_attempts > 10_per_hour THEN alert
IF new_user_registration AND after_hours THEN alert
IF process_spawned_from_n8n THEN alert
Regular Audits:
- Review who has workflow creation permissions monthly
- Audit what secrets are configured quarterly
- Check access logs for suspicious activity weekly
- Penetration test your n8n deployment annually
Backup and Recovery Strategy
Automated Backups:
bash#!/bin/bash
# Daily backup script
DATE=$(date +%Y%m%d)
n8n export --backup --output=/backups/n8n-backup-${DATE}.json
# Keep only 30 days of backups
find /backups -name "n8n-backup-*.json" -mtime +30 -delete
Recovery Testing:
Don't wait for a disaster to test your recovery process. Monthly:
- Restore from a backup to a test instance
- Verify all workflows function correctly
- Document the recovery time
- Update runbooks with any issues discovered
Multi-Region Redundancy (For Critical Deployments):
For enterprise n8n deployments handling critical workflows:
- Run replicas in multiple regions
- Use load balancers to distribute traffic
- Sync database changes across regions
- Test failover monthly

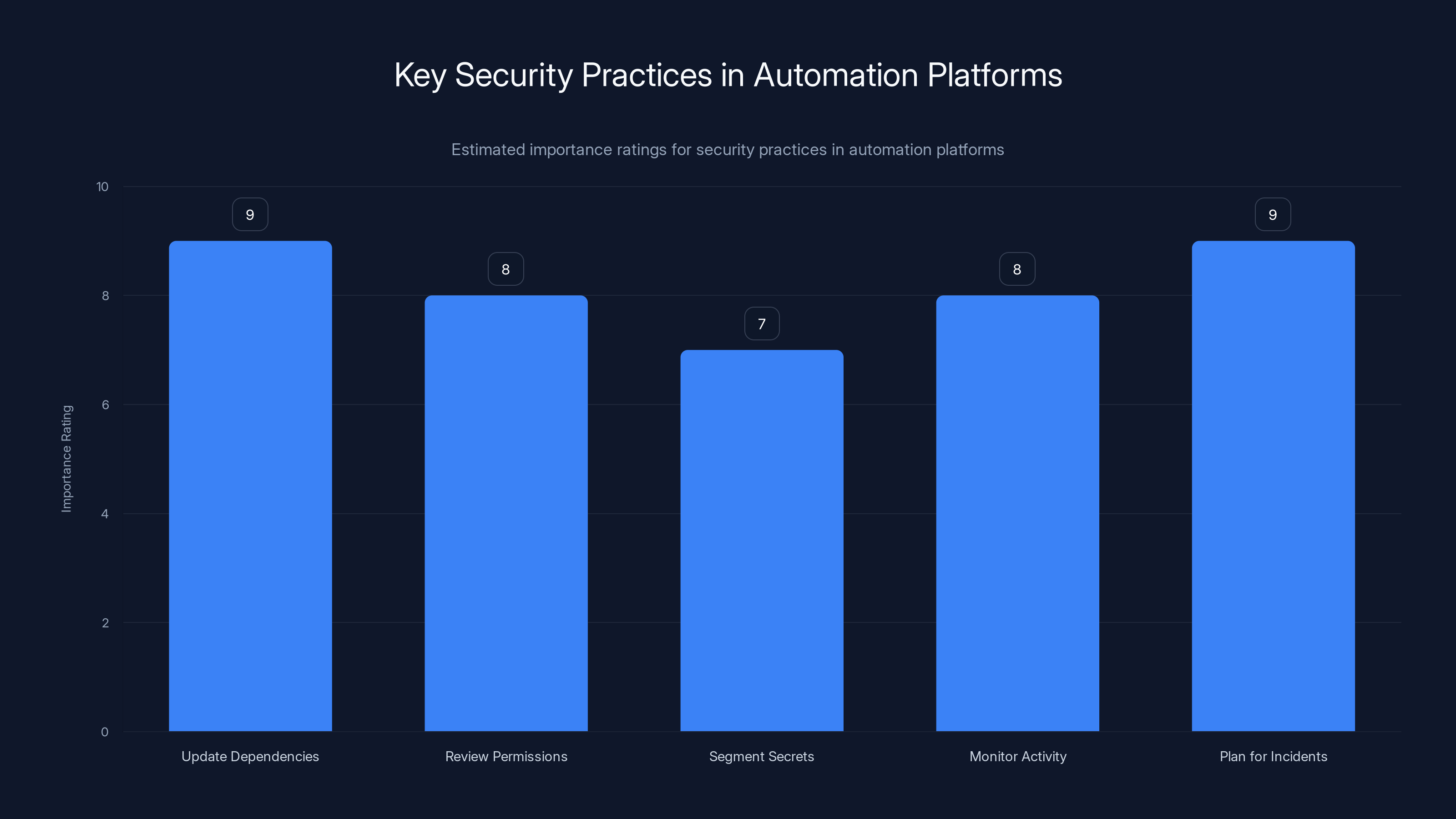
Updating dependencies and planning for incidents are rated as the most critical security practices in automation platforms. Estimated data.
Workflow Hardening: Writing Safer N8N Code
Expression Security
Even after patching, be cautious about what expressions you write:
Avoid:
javascript// Don't use eval-like patterns
Function(userInput)();
// Don't chain complex object access without validation
data[key1][key2][key3];
// Don't dynamically execute code paths
if (condition) { eval(code); }
Prefer:
javascript// Use specific, known functions
data.map(item => item.value);
// Validate before accessing nested properties
if (data?.user?.profile?.email) { ... }
// Use explicit logic instead of dynamic execution
if (condition === 'type1') { ... } else { ... }
Integration Security
When connecting external services:
-
Use API tokens with minimal permissions - If Slack integration only needs to send messages, don't grant admin permissions
-
Rotate credentials regularly - Update API keys and OAuth tokens every 90 days
-
Monitor API usage - Alert if a workflow makes unexpected API calls to integrated services
-
Version integrations - Pin to specific versions instead of always pulling latest
Workflow Isolation
Sensitive Workflows → Restricted Permissions → Logging & Monitoring → Alerts
Public Workflows → Open Permissions → Basic Logging → No Alerts
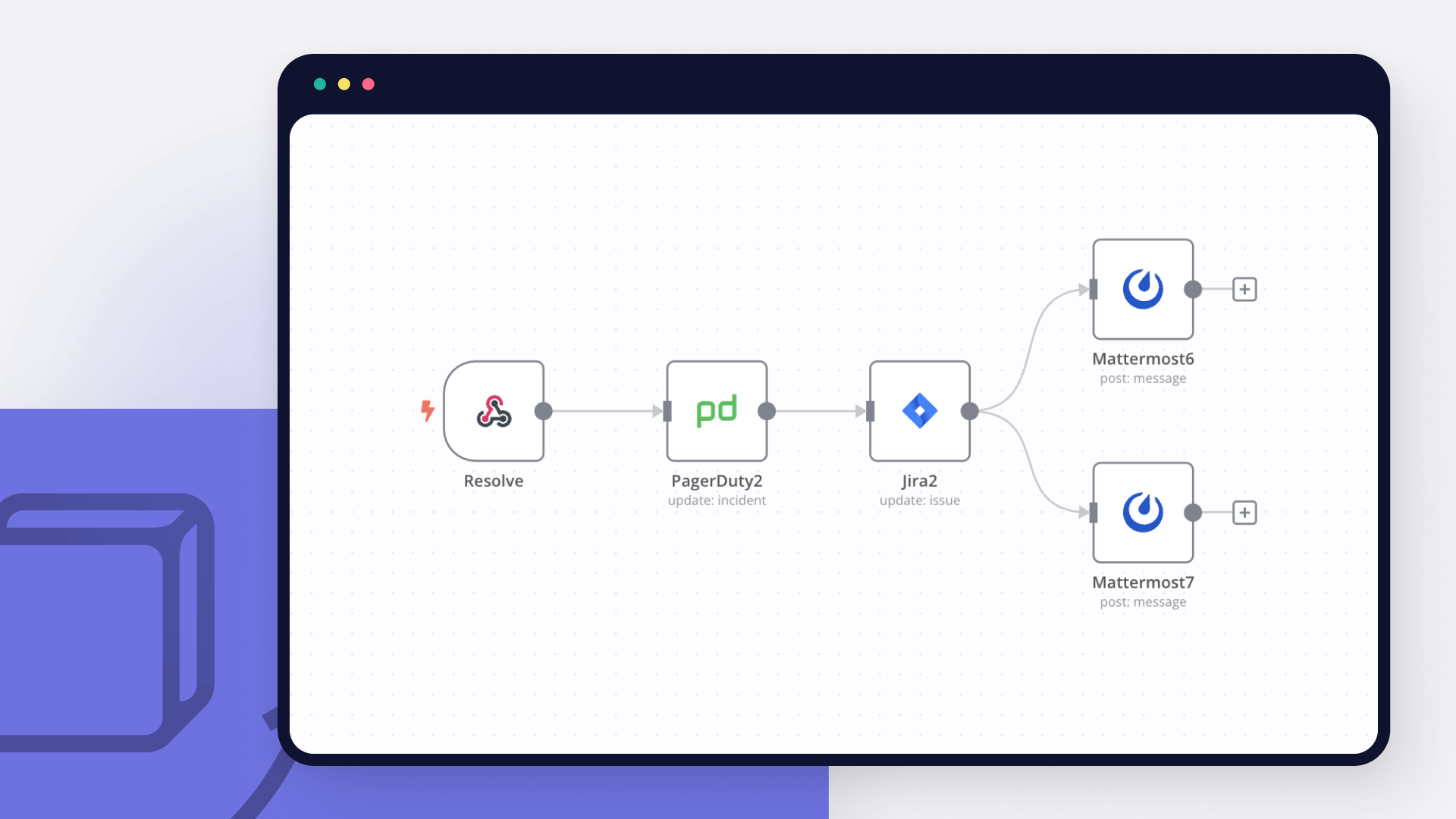
Not all workflows are equally important. Categorize them:
- Tier 1 (Critical): Payment processing, user data handling, financial transactions
- Tier 2 (Important): Customer notifications, reporting, internal data sync
- Tier 3 (Nice-to-have): Slack reminders, email forwarding, social media posts
Apply different security controls to each tier.
Understanding N8N's Response and Lessons Learned
What N8N Did Right
- Acknowledged the issue publicly - N8N didn't try to hide the vulnerability
- Released patches promptly - 2.5.2 came out within weeks of disclosure
- Provided workarounds - Gave customers mitigation options while patching
- Communicated clearly - Security advisories were detailed and actionable
What N8N Did Wrong
- First patch was incomplete - Version 2.4.0 gave false confidence while remaining vulnerable
- Sandboxing architecture is fundamentally flawed - Filtering-based sandbox can never be truly secure
- Allowed unauthenticated workflow creation by default - High-risk configuration shipped by default
- Slow to recognize the incomplete patch - Took external researchers to identify the gap
Industry Implications
This vulnerability highlights a critical problem in automation platforms: they try to offer powerful scripting capabilities while preventing code execution. This is fundamentally contradictory.
Players like Zapier sidestep this by only offering pre-built connectors. N8N offers JavaScript, which is far more powerful but far riskier.
The solution isn't more filters. It's proper isolation:
- Run workflow code in completely isolated containers
- Use WebAssembly for sandboxing instead of V8 filters
- Implement capability-based security instead of role-based
- Require explicit permission grants for each system resource
For now, n8n's approach is functional with proper patching and hardening. But long-term, expect more vulnerabilities until they fundamentally rearchitect how workflows execute.

Comparing N8N Against Alternatives
Why Automation Platforms Face These Risks
N8N isn't alone in facing code execution vulnerabilities. Any platform offering workflow scripting faces this challenge:
Zapier - Avoids the issue entirely by not offering general-purpose code execution. Their integrations are pre-built, reducing attack surface but limiting flexibility.
Make.com - Offers custom code modules but in isolated environments. Better than n8n's approach but more limited.
AWS Step Functions - Runs in AWS's managed environment with tight IAM controls. Secure but vendor-locked and expensive.
Apache Airflow - Runs Python workflows but requires deployment in your own infrastructure. Security depends entirely on how you configure it.
For automation platforms offering user-written code, the fundamental security question is: How do you let users write powerful code without letting them break out of the sandbox?
N8N's answer was filters. It didn't work. A better answer involves true isolation.
The Broader Automation Security Landscape
Why This Matters Beyond N8N
If you're using any automation platform—n8n, Make, Zapier, Airflow—this vulnerability should prompt a security review of your entire automation infrastructure:
- Update your dependencies - Keep all automation platforms at latest versions
- Review your permissions model - Who can create/edit workflows? Can this be more restrictive?
- Segment your secrets - Don't grant all API keys to all workflows
- Monitor for suspicious activity - Set up alerts for unusual workflow behavior
- Plan for incidents - If your automation platform is compromised, what's your recovery plan?
The same concerns apply to other integrations and platforms you rely on.
Contributing to Open Source Security
If you're running n8n (which is open source), consider contributing security improvements:
- Review code changes before merging
- Run security scanning tools (SAST) on pull requests
- Contribute hardened sandbox implementations
- Report vulnerabilities responsibly through their security program
- Test security patches thoroughly before release
Open source security is everyone's responsibility. A few contributions from users can prevent future vulnerabilities.
FAQ
What exactly is a sandbox escape and why is it so dangerous?
A sandbox is a restricted environment where code is supposed to run with limited permissions. A sandbox escape occurs when an attacker breaks out of these restrictions and gains access to the full system. In the case of n8n, the vulnerability allows code written by an attacker to escape the expression evaluator sandbox and execute arbitrary system commands with full permissions. This is dangerous because the attacker can read sensitive files, access API keys, modify data, delete information, or take complete control of the server.
I'm running n8n on a Docker container with restricted resources—am I still vulnerable?
Yes, absolutely. Restricting Docker resources (CPU, memory) provides no protection against code execution vulnerabilities. An attacker can still execute arbitrary commands within the container, read all data accessible to the container, and pivot to attack other systems. The only protection is the network restrictions around the container (limiting who can reach it) and the privileges of the user running the process. If you're running n8n as root inside a Docker container, a code execution vulnerability gives the attacker root access to the container and potentially the host.
Can I safely keep running n8n 2.4.0 if I disable workflow creation for all users except me?
No. While restricting workflow creation does reduce your attack surface significantly, it's not a complete solution. A disgruntled employee, contractor, or anyone with legitimate access could still exploit the vulnerability. Additionally, you might have misconfigured permissions somewhere—users might have access you forgot about. The risk is too high. Update to 2.5.2 or later as soon as possible. Workarounds are temporary measures while you prepare to patch, not long-term solutions.
How do I know if my n8n instance was already compromised before I patched it?
This is the difficult question. An attacker with code execution could have covered their tracks by deleting logs, removing evidence, or using sophisticated persistence mechanisms. However, you can investigate by checking:
- Access logs - Look for unusual login attempts or workflow creation by unexpected users
- System logs - Check for unexpected processes, connections, or resource usage
- Database integrity - Compare your database against backups to spot modifications
- Network traffic - Check for outbound connections to suspicious IPs
- Filesystem changes - Look for new files, modified binaries, or added cron jobs
If you find evidence of compromise, you'll need to follow incident response procedures: isolate the system, preserve evidence, notify affected parties, and perform a full forensic investigation.
What if my n8n instance is behind a firewall and only accessible internally—do I still need to patch?
Yes, you still need to patch. While a firewall provides an additional layer of defense, internal threats are real: disgruntled employees, contractors, phishing attacks, lateral movement from compromised systems. Defense in depth means you protect against multiple attack vectors. Even if external access is blocked, an attacker with internal network access can exploit this vulnerability. Additionally, you might have accidentally exposed n8n to the internet through misconfigured firewalls, VPN leaks, or other configuration errors.
Should I migrate away from n8n because of this vulnerability?
Not necessarily. Vulnerabilities happen in all software. What matters is how quickly they're patched, how transparent the vendor is, and whether you trust them to fix issues when discovered. N8N released patches within weeks and was transparent about the vulnerability. That's good. However, if you're concerned about their security practices long-term, you could:
- Implement stricter network controls regardless of platform
- Consider splitting critical workflows across multiple platforms to reduce single-point-of-failure risk
- Invest in workflow code review processes before deployment
- Run security audits on your automation infrastructure regularly
But migrating entirely away is probably overkill unless you have other concerns about n8n beyond this particular vulnerability.
Are SaaS n8n deployments automatically patched?
N8N claims that cloud instances are automatically patched, but don't assume this happened without verification. Security incidents often occur because administrators assume patches were applied automatically. You should:
- Contact n8n support to confirm your account is running 2.5.2 or later
- Log into your account and verify the version matches
- Check your account security logs for any suspicious activity
- Document the patch date in your own records
Don't trust implicit assumptions about security patches—verify explicitly.
What's the long-term fix for sandbox vulnerabilities like this?
The long-term fix requires a fundamental architectural change. Instead of trying to filter dangerous code, n8n should:
- Use WebAssembly - Compile workflow code to WebAssembly instead of running raw JavaScript, providing better isolation
- Capability-based security - Each workflow only gets the specific permissions it needs, not blanket access
- Process isolation - Each workflow runs in its own isolated process or container, not the same process as other workflows
- Formal verification - Mathematically prove that code can't escape the sandbox, rather than relying on filters
These approaches are more complex and slower, but they're secure. Until n8n (or any automation platform) adopts them, expect more sandbox escape vulnerabilities in the future.
Conclusion: Building a Secure Automation Future
The n8n vulnerabilities (CVE-2025-68613 and CVE-2026-25049) represent a critical but solvable security problem. Thousands of organizations running n8n need to act immediately, but the path forward is clear:
Today: Update to n8n 2.5.2 or later if you haven't already.
This week: Audit who has access to create and edit workflows. Restrict permissions to trusted users only.
This month: Implement proper secrets management, logging, and monitoring around your n8n deployment.
This quarter: Review your entire automation infrastructure—n8n, Zapier, Make, or anything else—and apply the same security principles.
Long-term: Expect automation platforms to improve their sandboxing mechanisms. For now, defense in depth is your best strategy: restrict access, monitor activity, segment networks, manage secrets separately, and keep everything patched.
Automation platforms like n8n solve real problems—they let non-engineers build powerful integrations without writing complex code. But with that power comes responsibility. Use these tools wisely, secure them properly, and monitor them carefully.
The alternative—doing everything manually or investing in custom integration development—costs far more time and money than the security practices outlined in this guide.
Your automation infrastructure is as critical as your production database or customer-facing applications. Treat it with the same security rigor, and these vulnerabilities become manageable rather than catastrophic.
Key Takeaways
- CVE-2025-68613 and CVE-2026-25049 allow unauthenticated attackers to execute arbitrary code on n8n servers and steal API keys, secrets, and customer data
- N8N versions prior to 2.5.2 (or 1.123.17) are vulnerable; updating is the only complete fix, not workarounds
- Restrict workflow creation permissions to trusted users, implement secrets management, and run n8n as non-root for defense in depth
- An attacker with workflow creation access needs only 10 minutes to compromise the server completely and exfiltrate all credentials
- Multi-tenant n8n deployments create additional risk: one compromised workflow can expose all other tenants' data and secrets
Related Articles
- NGINX Server Hijacking: Global Traffic Redirect Campaign [2025]
- Microsoft Office Vulnerability: How Russian State Hackers Exploited It in 48 Hours [2025]
- Office 365 Zero-Day Exploit: What You Need to Know [2025]
- Minecraft Server Security Guide: Keep Your Server Safe [2025]
- Agentic AI Security Risk: What Enterprise Teams Must Know [2025]
- AI Toy Security Breaches Expose Children's Private Chats [2025]
![N8N Critical Vulnerabilities Explained: CVE-2025-68613 & CVE-2026-25049 [2025]](https://tryrunable.com/blog/n8n-critical-vulnerabilities-explained-cve-2025-68613-cve-20/image-1-1770309576612.png)



