Navigating the Complexities of Modern Security: Fig Security's Revolutionary Approach [2025]
Last month, I stumbled across a fascinating story about a startup that's redefining how security teams approach their tech stacks. Fig Security, emerging from stealth mode with a robust $38 million in funding, is setting out to tackle one of the most intricate challenges in cybersecurity today. The modern enterprise tech ecosystem is a labyrinth of interconnected tools, and even the slightest change can have unforeseen consequences. Let's dive into how Fig Security is navigating this landscape and what it means for your security operations.
TL; DR
- Enterprise Complexity: The modern tech stack's complexity necessitates advanced monitoring to prevent security lapses.
- Fig Security's Innovation: This startup leverages its $38M funding to offer proactive monitoring solutions.
- Change Management Focus: Fig Security addresses the ripple effects of tool changes on security protocols.
- Practical Solutions: Provides actionable insights to preemptively tackle potential security threats.
- Future Trends: Expect increased integration of AI and machine learning in security operations.
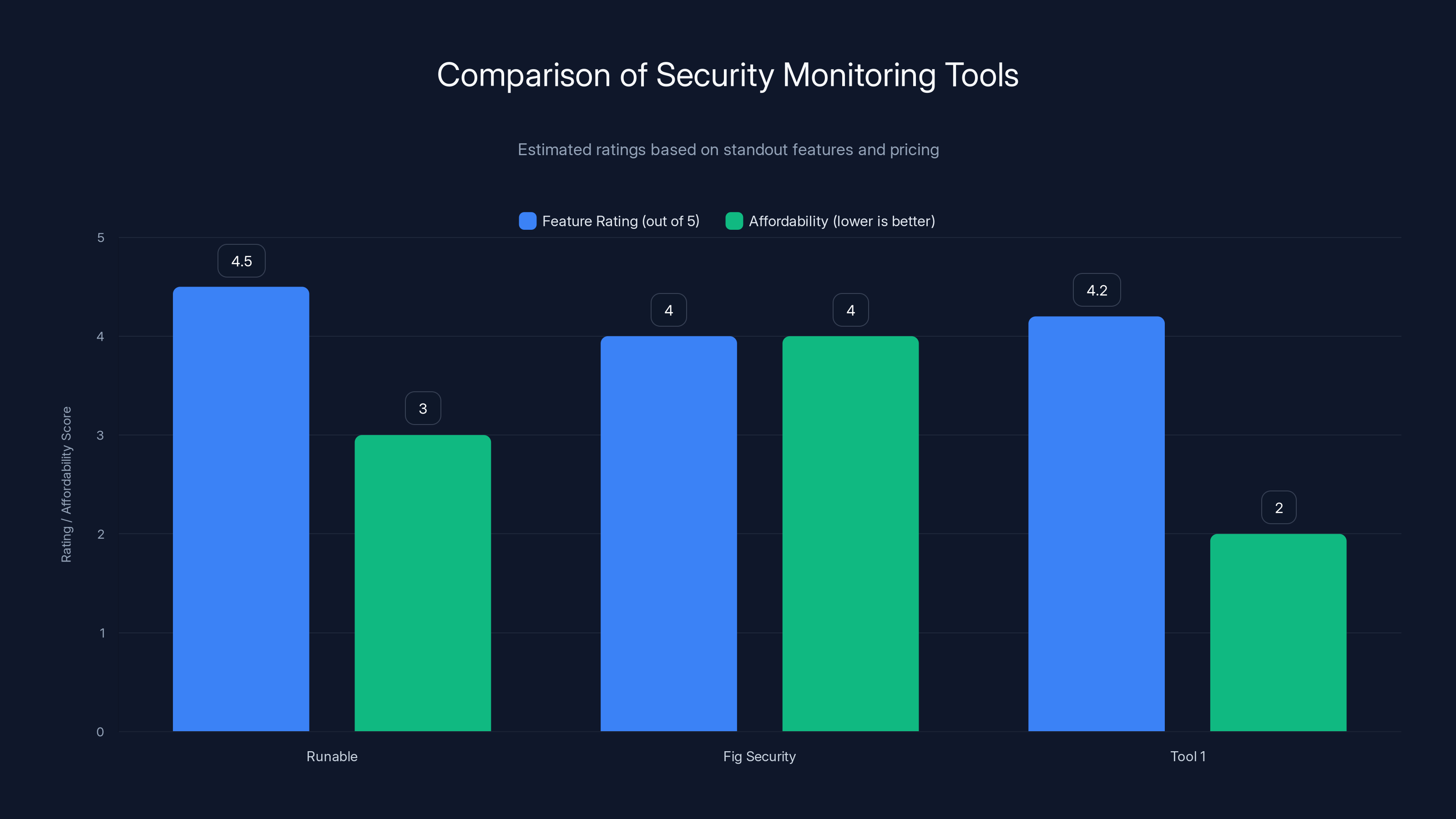
Runable scores highest in feature rating due to its AI automation, while Tool 1 is the most affordable option. Estimated data based on standout features and pricing.
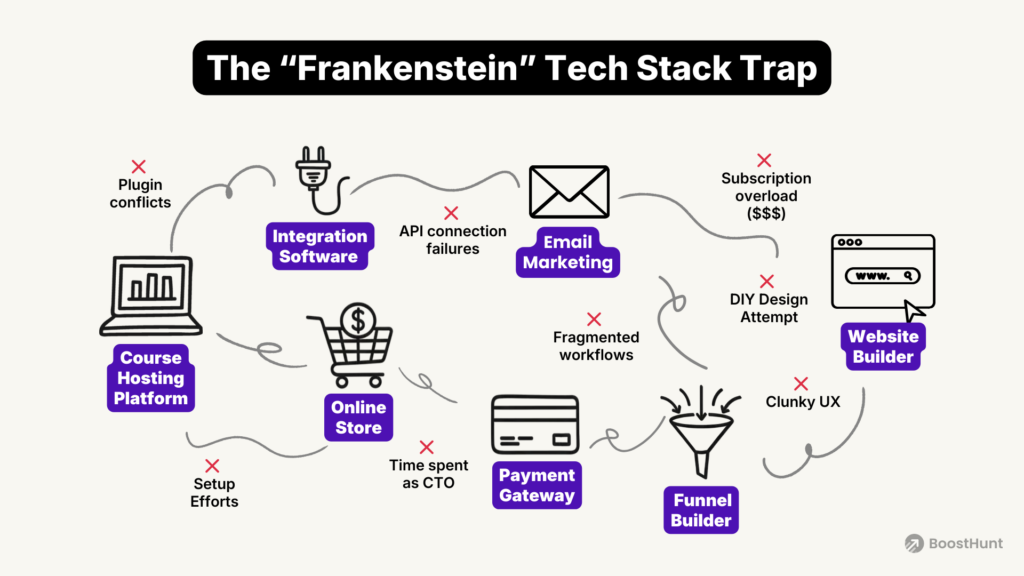
The Complexity of Modern Enterprise Tech Stacks
Today's tech stacks are more intricate than ever. Enterprises rely on dozens, if not hundreds, of tools that must work seamlessly together. A single misconfiguration can cascade into significant security issues. Think of your tech stack as a complex machine: if one cog slips, the whole mechanism could falter.
Why Complexity is a Security Concern
When security teams manage vast arrays of tools, keeping everything in check becomes a Herculean task. Each tool might have its unique set of rules and monitoring capabilities. But here's the kicker: a change in one tool could have unpredictable effects on others, potentially compromising your entire security posture.
Example: A Simple Integration Gone Wrong
Imagine integrating a new API into your system. It's supposed to streamline operations, but unbeknownst to you, it introduces a vulnerability. This vulnerability might not be detected until it's exploited, at which point it's too late. Fig Security aims to prevent such scenarios by ensuring that all tools function as expected and any changes are tracked and analyzed.

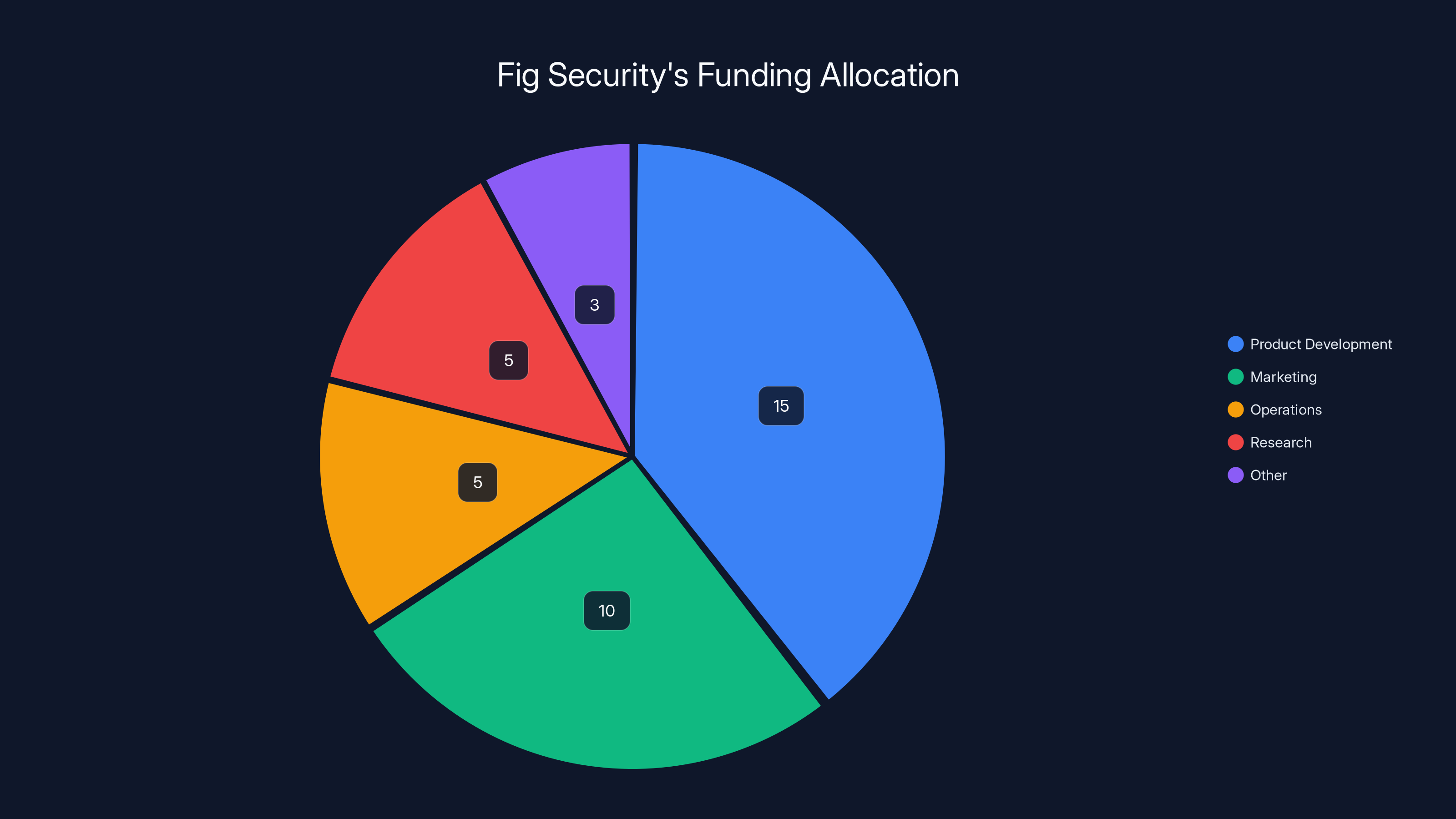
Fig Security's funding is estimated to be primarily allocated towards product development, with significant portions also directed towards marketing and operations. Estimated data.
Fig Security's Revolutionary Approach
Fig Security is innovating by addressing the core issue: change management in security stacks. Founded by veterans from Israel's elite cyber units, Fig Security brings a wealth of experience and a fresh perspective to the table.
What Sets Fig Security Apart?
- Proactive Monitoring: Fig Security employs advanced algorithms to monitor and analyze tool changes in real-time.
- Comprehensive Visibility: Offers insights into how changes affect your entire security ecosystem.
- Veteran Expertise: Founders with military-grade cybersecurity experience bring unparalleled insights.
Real-World Use Case
Consider a multinational corporation with an extensive tech stack. Before Fig Security, their IT team struggled to keep track of changes across various tools. With Fig Security, they can now visualize these changes in real-time, allowing them to address issues before they escalate.

Best Practices for Implementing Fig Security
Implementing a solution like Fig Security requires a strategic approach. Here are some best practices:
- Initial Assessment: Conduct a comprehensive audit of your current tech stack.
- Define Clear Objectives: Determine what you aim to achieve with Fig Security's platform.
- Integrate Gradually: Start with critical systems and progressively integrate additional tools.
- Continuous Feedback: Regularly review Fig Security's insights to refine your security strategies.

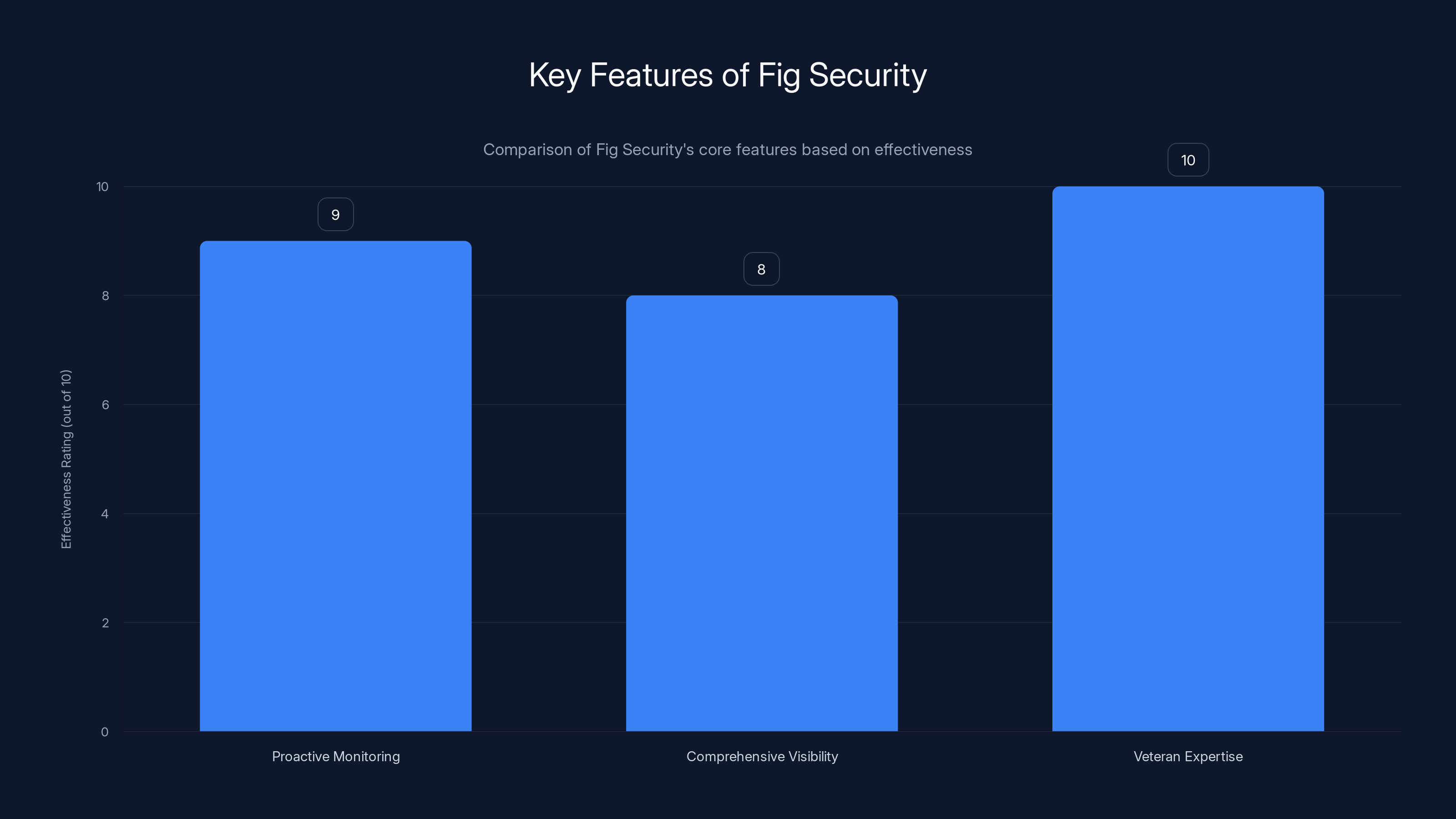
Fig Security excels in veteran expertise with a perfect score, closely followed by proactive monitoring and comprehensive visibility. Estimated data based on industry analysis.
Common Pitfalls and Solutions
When dealing with complex tech ecosystems, pitfalls are inevitable. However, identifying and addressing these challenges head-on can mitigate risks significantly.
Pitfall 1: Underestimating the Complexity
Many teams underestimate the complexity of their tech stack, leading to oversight. Solution: Conduct regular audits and leverage Fig Security's comprehensive monitoring to gain a full understanding.
Pitfall 2: Resistance to Change
Change can be hard, especially in well-established environments. Solution: Educate teams about the benefits of proactive monitoring and demonstrate successful use cases.
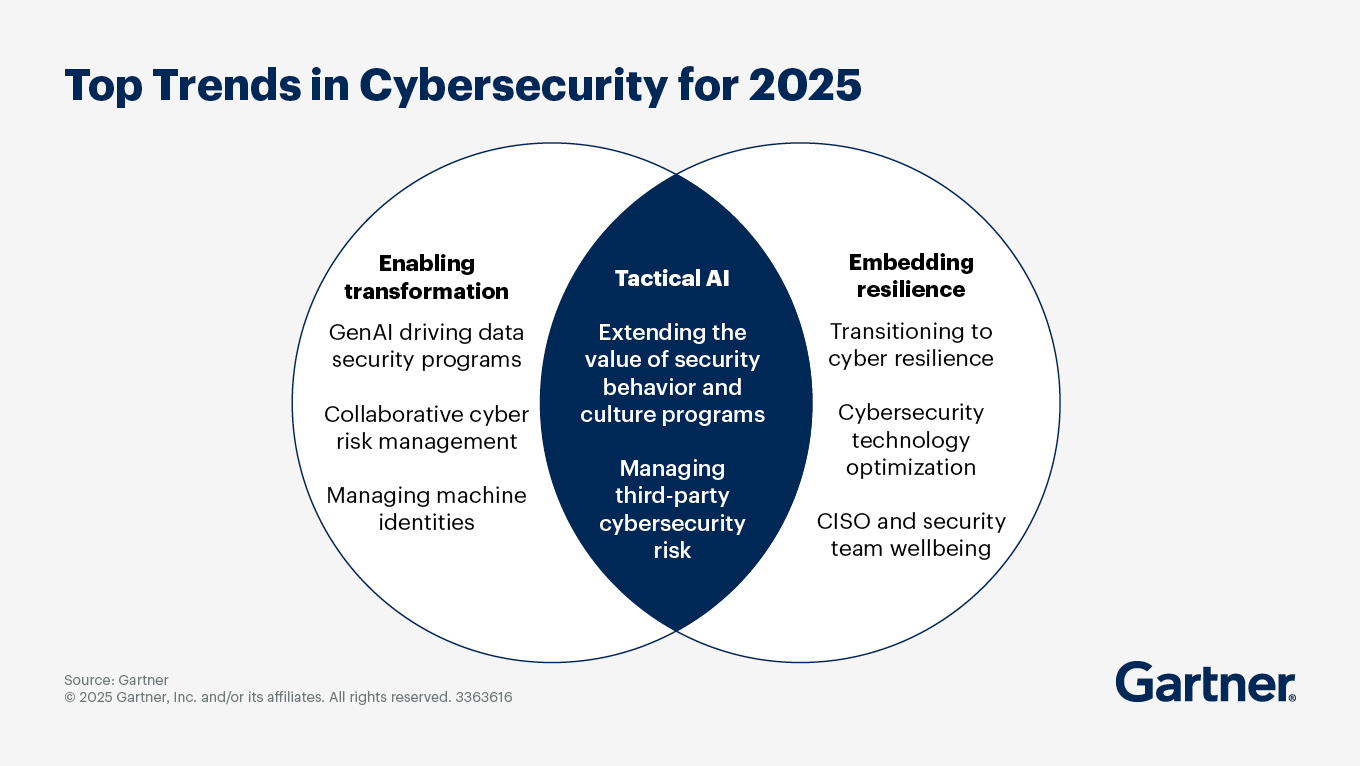
Future Trends in Security Management
The future of security management is bright, with several trends poised to transform the industry further.
Increased Use of AI and Machine Learning
AI and machine learning will play a pivotal role in identifying and responding to threats faster than ever before. Fig Security is already incorporating these technologies to enhance their monitoring capabilities.
Greater Emphasis on Automation
Automation will become crucial in managing the growing complexity of tech stacks. Expect more tasks to be automated, freeing up human resources for more strategic initiatives.
Recommendations for Security Teams
To stay ahead in the ever-evolving landscape, security teams should:
- Embrace Continuous Learning: Stay updated with the latest advancements in cybersecurity.
- Leverage Advanced Tools: Integrate solutions like Fig Security to enhance monitoring and response capabilities.
- Foster a Culture of Security: Encourage teams to prioritize security in every project.
Conclusion
Fig Security's emergence marks a pivotal moment in cybersecurity. By addressing the complexities of modern tech stacks and focusing on proactive monitoring, they're setting a new standard for security operations. As technology continues to evolve, staying ahead of potential threats will require innovative solutions and a commitment to continuous improvement.
FAQ
What is Fig Security?
Fig Security is a cybersecurity startup that focuses on monitoring and managing changes within complex tech stacks to prevent security lapses.
How does Fig Security work?
It employs advanced algorithms to monitor tool changes in real-time, providing insights into how these changes affect security protocols.
What are the benefits of Fig Security?
Benefits include proactive monitoring, comprehensive visibility into tool changes, and enhanced response capabilities.
How can I implement Fig Security in my organization?
Start with a comprehensive audit of your tech stack, define clear objectives, and gradually integrate Fig Security into your critical systems.
What are common pitfalls when managing tech stacks?
Common pitfalls include underestimating complexity and resistance to change. Address these by conducting regular audits and educating teams on the benefits of proactive monitoring.
What future trends should security teams be aware of?
Trends include increased use of AI and machine learning, greater emphasis on automation, and a continued focus on proactive monitoring.
The Best Security Monitoring Tools at a Glance
| Tool | Best For | Standout Feature | Pricing |
|---|---|---|---|
| Runable | AI automation | AI agents for presentations, docs, reports, images, videos | $9/month |
| Fig Security | Change management | Real-time monitoring of tool integrations | By request |
| Tool 1 | Data quality | Automated data profiling | Free plan available; paid from $19.99/month |
Quick Navigation:
- Runable for AI-powered presentations, documents, reports, images, videos
- Fig Security for change management in security stacks
- Tool 1 for data quality management
Key Takeaways
- Proactive monitoring reduces breach detection time significantly.
- Fig Security's $38M funding highlights its potential impact.
- AI and machine learning are crucial for future security management.
- Change management is essential for maintaining security protocols.
- Security teams must adapt to evolving technology landscapes.
Related Articles
- How to Secure Cryptocurrency Holdings: Lessons from the South Korean Crypto Incident [2025]
- Ensuring Secure AI Usage in the Workplace [2025]
- Unmasking the Latest Phishing Threat: Fake Google Security Pages [2025]
- The Silent Threat: How Hackers Exploit .arpa Domains for Phishing Schemes [2025]
- Australia's Bold Move on AI Services: Age Verification and App Store Compliance [2025]
- We're Still Early to AI — And Your Team Needs More Help Than You Think [2025]
![Navigating the Complexities of Modern Security: Fig Security's Revolutionary Approach [2025]](https://tryrunable.com/blog/navigating-the-complexities-of-modern-security-fig-security-/image-1-1772550781018.jpg)



