Introduction
In the ever-evolving landscape of cybersecurity, hackers continuously adapt, searching for new vulnerabilities and methods to exploit. One of the latest tactics involves the exploitation of .arpa domains. Traditionally, these domains are part of the internet's core infrastructure, used for reverse DNS lookups to map IP addresses to domain names. However, recent developments have shown that cybercriminals are hijacking these domains to host phishing pages, cleverly disguising their malicious intents. Let's delve into how this attack vector operates, the risks involved, and how you can protect yourself.
TL; DR
- Hackers exploit .arpa domains: Using these domains to host phishing attacks, making detection difficult. According to a recent report, these domains are increasingly being used for malicious purposes.
- IPv6 addresses are key: Attackers use the vastness of IPv6 to control malicious subdomains. This is supported by findings in the Cybersecurity News.
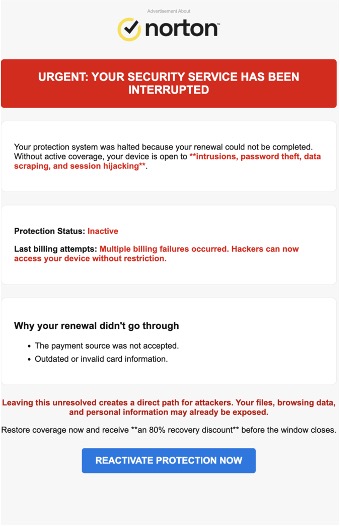
- Phishing tactics evolve: Emails mimic trusted brands to extract user credentials, as detailed in the Simplilearn's cybersecurity trends article.
- Preventive measures: Using DNS security extensions and keeping software updated can mitigate risks.
- Future outlook: As IPv6 adoption grows, new security challenges will emerge, as discussed in the CircleID article.
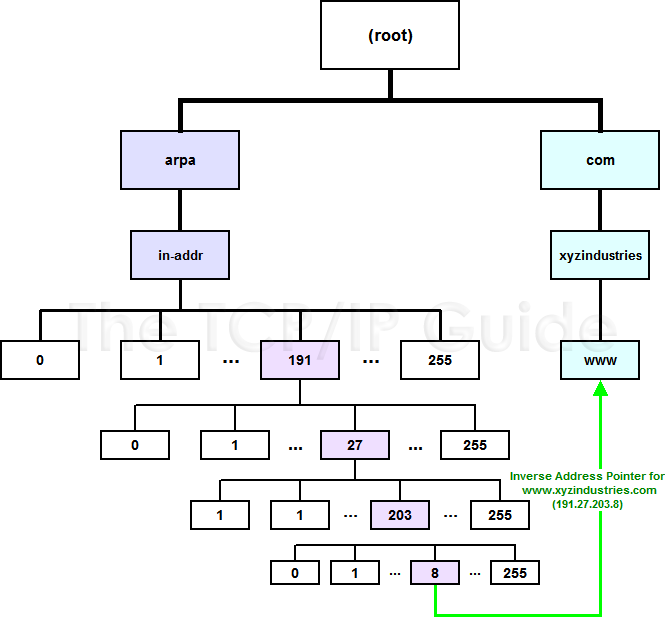
Understanding .arpa Domains
Before diving into the specifics of the attack, it's crucial to understand the role of .arpa domains. The Address and Routing Parameter Area (.arpa) is a top-level domain primarily reserved for internet infrastructure tasks. Its most significant function is facilitating reverse DNS lookups, which help resolve IP addresses to hostnames.
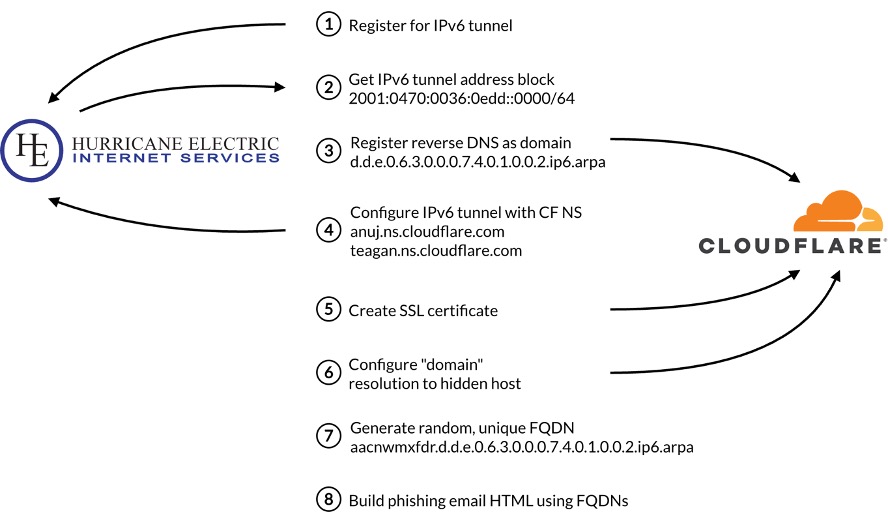
How Hackers Exploit .arpa
By leveraging the .arpa domain, attackers can create subdomains that are not typically subjected to the same scrutiny as commercial domains like .com or .net. This lack of scrutiny, combined with the technical nature of .arpa, makes it an ideal candidate for hosting phishing pages.
Key Exploitation Techniques:
- Subdomain Creation: Attackers generate numerous subdomains under .arpa, masking their malicious content.
- Phishing Page Hosting: These subdomains host pages that mimic legitimate brands, tricking users into entering sensitive information.
- URL Obfuscation: By embedding these domains in emails and hyperlinks, attackers craft URLs that appear legitimate.
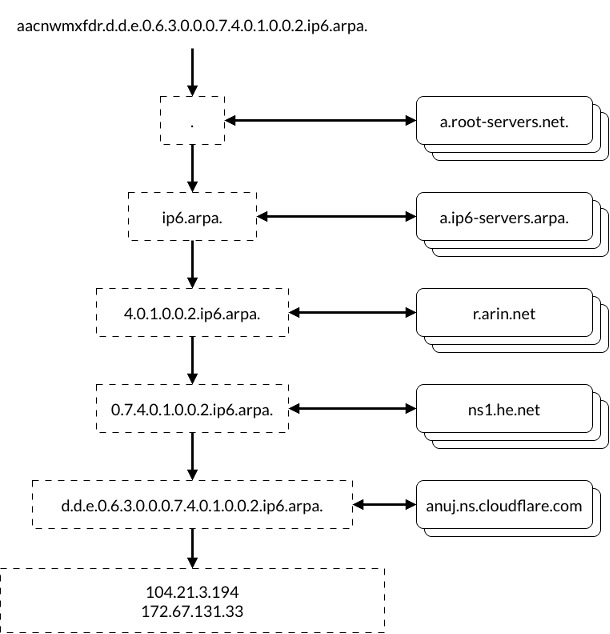
The Role of IPv6 in Phishing Attacks
IPv6, the latest version of the Internet Protocol, offers a significantly larger address space than its predecessor, IPv4. While this expansion facilitates the growth of the internet, it also introduces new security challenges.
How IPv6 Facilitates Phishing
The vast address space of IPv6 allows for the generation of a massive number of unique IP addresses. Hackers exploit this by creating a multitude of IPv6 addresses linked to phishing domains. This strategy not only enhances the scale of their operations but also complicates detection efforts.
Advantages for Attackers:
- Increased Anonymity: The sheer number of IP addresses available makes it easier to hide malicious activity.
- Difficult Blacklisting: Blacklisting individual IPv6 addresses is impractical due to the volume and variability.
- Enhanced Persistence: Attackers can continually rotate addresses, maintaining a persistent presence.
Anatomy of a Phishing Attack
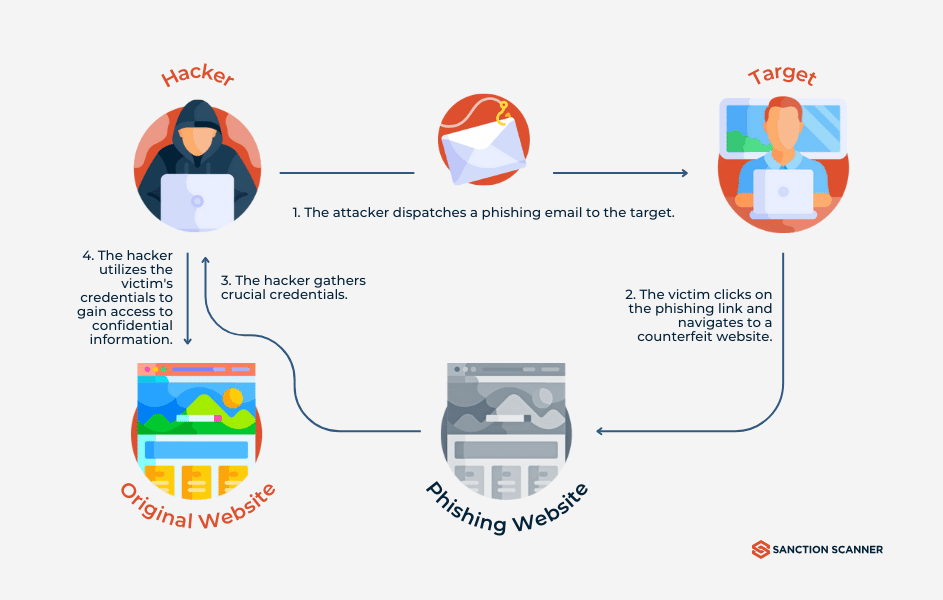
Phishing attacks via .arpa domains typically follow a structured approach, designed to maximize effectiveness while minimizing the risk of detection.
Step-by-Step Breakdown
- Domain Setup: Hackers set up a subdomain within the .arpa namespace.
- Phishing Page Creation: They create a phishing page that mimics a trusted brand's login page.
- Email Campaign: Phishing emails are sent, containing links to the malicious .arpa domain.
- Credential Harvesting: Unsuspecting users enter their credentials, which are then captured by the attackers.
- Data Exploitation: Stolen data is used for financial gain, identity theft, or further attacks.

Protecting Against .arpa Domain Phishing
While the threat is significant, several strategies can help mitigate the risks associated with .arpa domain phishing.
DNS Security Extensions (DNSSEC)
DNSSEC adds an additional layer of security to the Domain Name System by enabling DNS responses to be verified for authenticity. This can prevent attackers from redirecting users to malicious sites.
Network Monitoring and Filtering
Implementing robust network monitoring tools can help identify unusual traffic patterns indicative of phishing activity. Additionally, filtering out known malicious IP addresses can further protect your network.
Best Practices:
- Regularly Update Filters: Keep your IP and domain blacklists current.
- Employee Training: Educate users on recognizing phishing attempts.
- Incident Response Plan: Have a plan in place to respond to phishing incidents swiftly.
Case Study: A Real-World Example
Consider the case of a financial institution that fell victim to a .arpa domain phishing attack. The attackers set up a subdomain that closely mimicked the bank's online portal. Despite advanced security measures, several employees were tricked into entering their credentials, leading to a data breach.
Analysis and Lessons Learned
- Weak Points: The attack exploited human error—employees clicked on phishing links.
- Remedies Implemented: The institution enhanced its email filtering systems and provided additional training to staff.
- Outcomes: Post-incident analysis led to improved security protocols and reduced vulnerability to similar attacks.
Future Trends in Phishing and Cybersecurity
As technology evolves, so do the tactics employed by cybercriminals. Understanding future trends can help organizations prepare and adapt their defenses.
Increasing Sophistication
Phishing attacks are becoming increasingly sophisticated, leveraging AI and machine learning to craft more convincing scams. These technologies enable attackers to personalize phishing emails, increasing the likelihood of success.
Emerging Threats:
- Deepfake Technology: Used to create convincing audio and video phishing content.
- AI-Powered Social Engineering: AI analyzes social media profiles to craft personalized phishing messages.
Recommendations for the Future
- Continuous Education: Regularly update employee training programs to address new phishing techniques.
- Advanced Threat Detection: Invest in AI-driven threat detection systems to identify anomalies.
- Collaboration and Sharing: Engage in information sharing with industry peers to stay informed about new threats.
Conclusion
The hijacking of .arpa domains for phishing represents a significant threat in the cybersecurity landscape. By understanding the mechanisms behind these attacks and implementing robust defenses, organizations can better protect themselves and their users. As IPv6 adoption continues to grow, staying informed and prepared will be crucial in mitigating the risks of such sophisticated phishing schemes.
FAQ
What is a .arpa domain?
.arpa is a top-level domain used for technical and infrastructure purposes, specifically for reverse DNS lookups. It's not typically used for hosting websites but has been exploited by hackers for phishing.
How do hackers use .arpa domains for phishing?
Hackers create subdomains within the .arpa namespace to host phishing pages. These domains are less scrutinized, making it easier for attackers to operate undetected.
What role does IPv6 play in phishing attacks?
IPv6 provides a vast address space, allowing attackers to generate numerous IP addresses linked to phishing domains, complicating detection and blacklisting efforts.
How can I protect my organization from .arpa domain phishing attacks?
Implement DNSSEC, ensure robust network monitoring and filtering, and conduct regular employee training to recognize phishing attempts.
What are future trends in phishing?
Phishing attacks are becoming more sophisticated, leveraging AI and machine learning to create personalized and convincing scams.
What should I do if my organization falls victim to a phishing attack?
Immediately implement your incident response plan, inform affected users, and conduct a thorough investigation to prevent future attacks.

Key Takeaways
- Hackers use .arpa domains to host undetectable phishing pages.
- IPv6 addresses provide anonymity and persistence for attackers.
- DNSSEC can prevent unauthorized domain redirections.
- AI and machine learning are making phishing attacks more sophisticated.
- Continuous education and advanced threat detection are key defenses.
Related Articles
- Beware of Google Tasks Scams: Protect Your Workplace from Phishing Attacks [2025]
- Australia's Bold Move on AI Services: Age Verification and App Store Compliance [2025]
- Accidental Hacks: Lessons from the 6,700 Robot Vacuum Incident [2025]
- How to Secure Cryptocurrency Holdings: Lessons from the South Korean Crypto Incident [2025]
- Oh Great, Here Comes 6G: What You Need to Know [2025]
- When AI Lies: Navigating the Complexities of Alignment Faking in Autonomous Systems [2025]
![The Silent Threat: How Hackers Exploit .arpa Domains for Phishing Schemes [2025]](https://tryrunable.com/blog/the-silent-threat-how-hackers-exploit-arpa-domains-for-phish/image-1-1772496291445.jpg)



