PayPal Data Breach 2025: What You Need to Know [Full Guide]
Introduction
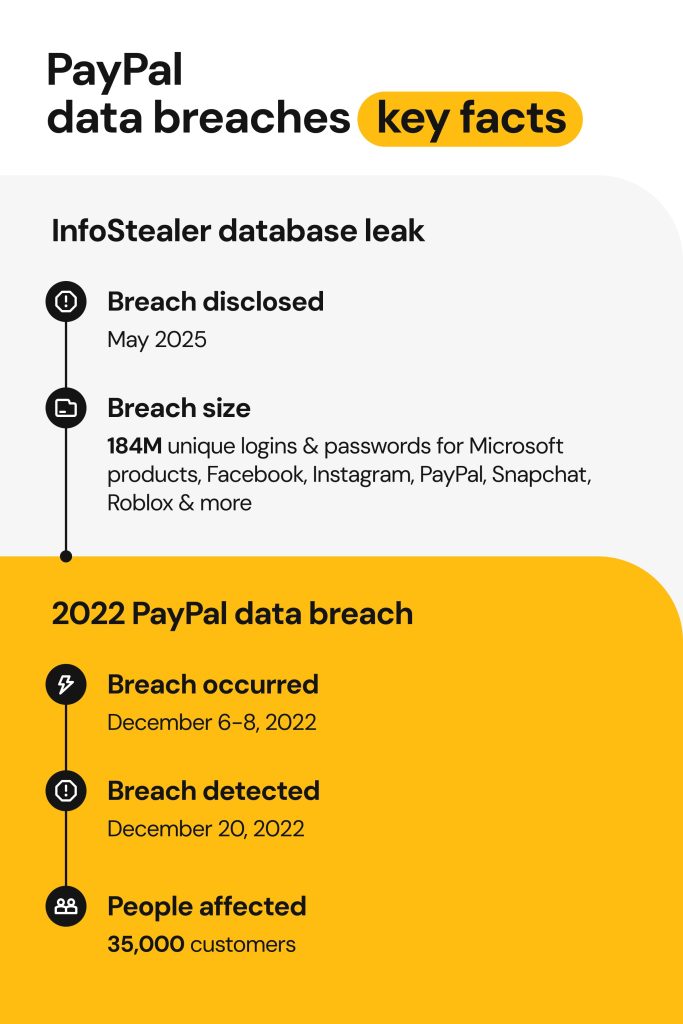
In December 2025, PayPal confirmed a significant data breach that exposed millions of customers to potential identity theft, fraud, and financial harm. The breach wasn't the result of a sophisticated cyber attack by external actors—it was far simpler and more alarming: a coding bug in PayPal's own application that sat undetected for over six months.
What makes this incident particularly concerning is the scope and sensitivity of the data exposed. We're not talking about usernames or encrypted passwords here. The breach compromised personally identifiable information (PII) including Social Security numbers, dates of birth, business addresses, phone numbers, and email addresses. For hundreds of thousands of PayPal customers, especially those using the PayPal Working Capital loan product, this meant their most sensitive financial and personal data was accessible to anyone who knew where to look.
The timing is equally troubling. The bug persisted from July 1, 2025, through December 13, 2025—nearly six months of continuous exposure. That's roughly 180 days where malicious actors could have harvested customer data, constructed detailed profiles for targeted attacks, or used the information for identity fraud.
But here's what you actually need to understand: this breach reveals something critical about how even massive, well-resourced companies handle security. PayPal processes billions in transactions annually. It has enterprise-grade security infrastructure. Yet a simple coding error slipped through testing, code review, and monitoring systems. It wasn't an advanced persistent threat. It wasn't a zero-day exploit. It was negligence wrapped in complexity.
This guide walks you through everything about the breach: what actually happened, who was affected, what data was exposed, and—most importantly—what you should do right now to protect yourself. We'll also look at the broader implications for how companies handle data security and why incidents like this keep happening despite billions spent on cybersecurity.

Stolen SSNs can fetch
TL; DR
- Bug Discovered: December 12, 2025, in PayPal Working Capital loan application
- Exposure Duration: 6 months (July 1 – December 13, 2025)
- Data Compromised: SSNs, dates of birth, business addresses, phone numbers, email addresses
- Affected Users: PayPal Working Capital loan applicants and account holders
- Unauthorized Transactions: "A few" victims experienced fraudulent charges; all were reimbursed
- Response: Free 2-year credit monitoring via Equifax, password resets for affected accounts
- Action Items: Monitor credit reports, enable two-factor authentication, watch for phishing emails
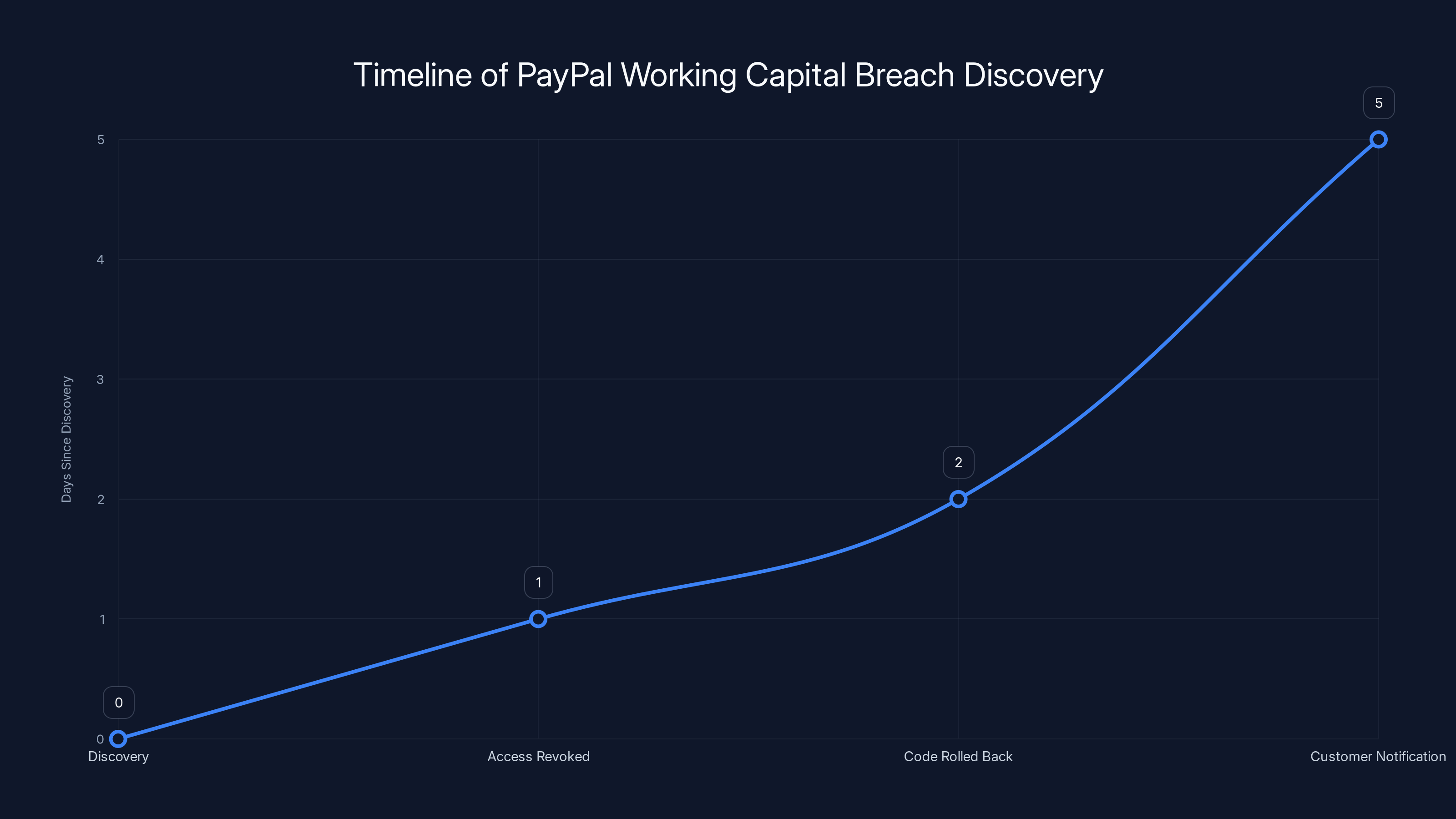
Estimated timeline showing key events from breach discovery to customer notification. Immediate actions were taken, but customer notification took a few days.
The PayPal Working Capital Breach: Timeline and Details
How PayPal Discovered the Bug
PayPal identified the vulnerability on December 12, 2025. The company hasn't publicly disclosed exactly how they discovered it—whether through routine security audits, penetration testing, or customer reports. This is actually a significant detail because it tells you something about their monitoring capabilities.
If the bug was found through automated monitoring systems, that suggests PayPal has adequate detection infrastructure. If it was discovered because someone reported suspicious activity, that's considerably more concerning. It suggests their automated systems either weren't looking in the right places or weren't sophisticated enough to catch the issue.
The company's statement that "we have not delayed this notification as a result of any law enforcement investigation" is interesting because it pre-emptively addresses a question many people would ask: Did law enforcement force PayPal to disclose this? Was PayPal covering it up? The proactive denial suggests they anticipated skepticism—which is warranted given how long the breach persisted undetected.
Once identified, PayPal says they immediately revoked the unauthorized access, rolled back the code change, and notified customers. The notification process itself took at least a few days, meaning there was a window where PayPal knew about the breach but hadn't informed affected users.
The PayPal Working Capital Product
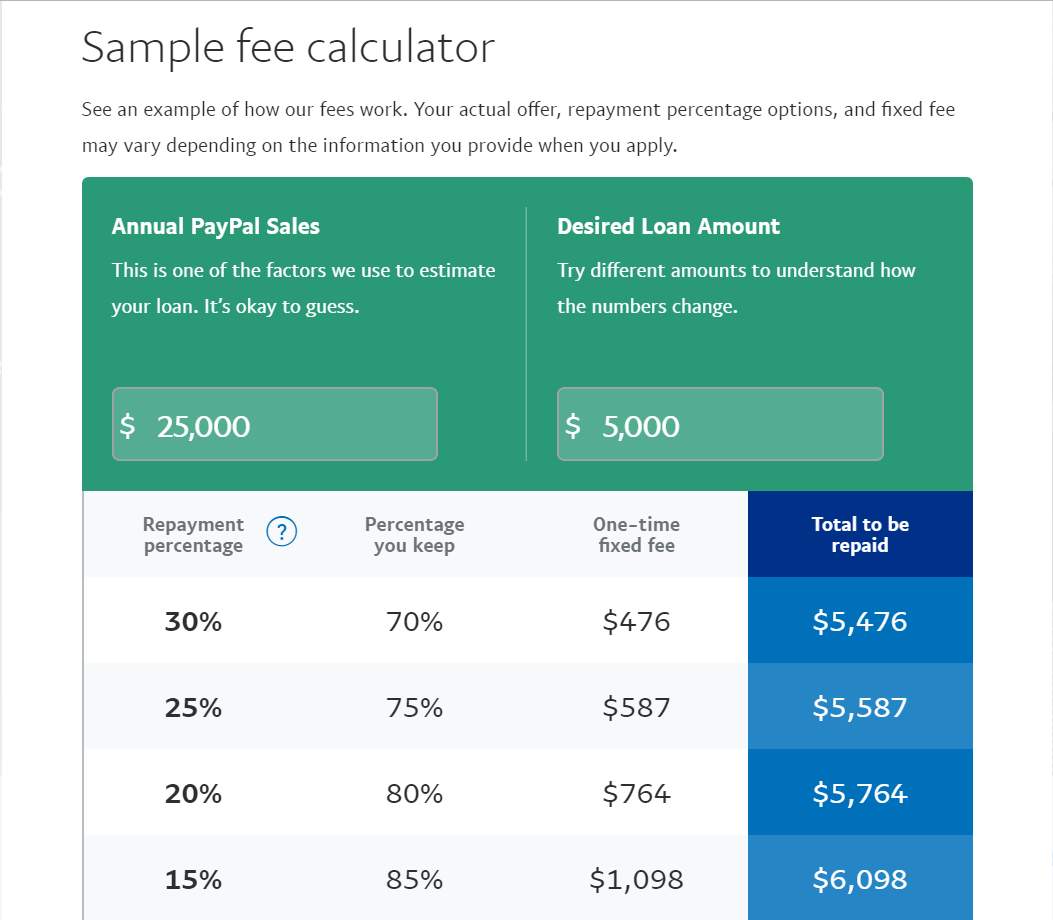
Understanding what PayPal Working Capital is helps explain why this breach matters. It's not just a cosmetic feature of the main PayPal app—it's a legitimate business financing product.
PayPal Working Capital provides cash advances to eligible small businesses based on their transaction history with PayPal. Instead of traditional bank loans with lengthy approval processes, businesses can get rapid funding tied to their PayPal sales volume. The loan terms vary, but the core value proposition is speed: apply, get approved, get funded.
Because Working Capital is a financial product, the application process requires substantial personal and business information. Applicants need to provide:
- Full legal name and date of birth
- Social Security number (for credit verification)
- Business address and phone number
- Detailed business financial information
- Email address and contact information
All of this information is incredibly valuable to identity thieves and fraud rings. A complete profile with SSN, business details, and contact information can be used to:
- Open fraudulent business accounts in someone else's name
- Apply for additional business loans impersonating the victim
- Conduct targeted phishing campaigns with business-specific social engineering
- Commit tax fraud using the victim's SSN
- Access business credit to purchase equipment or inventory
What Data Was Actually Exposed
This is where the breach becomes genuinely concerning. PayPal says the following information was compromised:
- Usernames and email addresses
- Phone numbers
- Business addresses
- Social Security numbers
- Dates of birth
- PayPal account details
Notice what's not on that list: passwords and credit card information. PayPal notes that payment card data wasn't exposed. That's the one silver lining here—a hacker can't directly drain your bank account with this data alone.
But here's why SSN exposure is catastrophic: once someone has your Social Security number, date of birth, and business address, they have the core components needed for identity theft. The Social Security Administration doesn't verify identity beyond these basic data points when issuing new identification documents or updating records.
The Duration: Six Months of Continuous Exposure
The bug existed from July 1, 2025, through December 13, 2025. That's 196 days. Nearly 200 days where sensitive data was potentially accessible to attackers.
Why does duration matter? Consider the attack surface:
Early exposure (July-August): Sophisticated threat actors identify the vulnerability, begin harvesting data Mid-period (September-October): Data is shared on dark web marketplaces, sold to fraud rings Late exposure (November-December): Coordinated fraud attempts against harvested accounts begin
By the time PayPal discovered the breach in December, fraudsters could have already spent months preparing targeted attacks. They'd have time to aggregate the data, validate it, test access methods, and coordinate with criminal accomplices.
PayPal hasn't disclosed exactly how many customers were affected. The phrase "a subset of customers" is deliberately vague. Was it 10,000? 100,000? Millions? The company's silence on this metric is noteworthy because it suggests either:
- The scope is larger than PayPal wants to publicly acknowledge
- PayPal hasn't fully determined the scope yet (more concerning)
- Legal/PR considerations are driving information withholding
Who Was Actually Affected
PayPal Working Capital Applicants
The primary affected population is people who applied for PayPal Working Capital loans or had existing Working Capital accounts. This is specifically a small business financing product, so the exposure is concentrated among:
- E-commerce sellers
- Dropshippers
- Service-based freelancers using PayPal for business
- Small retailers with PayPal payment processing
- Marketplace sellers (eBay, Amazon, Shopify sellers who use PayPal)
These aren't casual PayPal users. These are business owners who connected their business financials to PayPal's lending platform. That means the breach affects people already generating significant transaction volume and likely holding cash flow information that makes them attractive targets.
Secondary Exposure: PayPal Account Holders
PayPal's statement mentioned that the bug leaked "customer data," but it's unclear if non-Working Capital users were affected. The breach specifically stemmed from the Working Capital application's code, suggesting the exposure was limited to that product's database.
However, PayPal's ecosystem is interconnected. If someone used the same email address for Working Capital applications and their main PayPal account, that connection could theoretically be exploited. But PayPal hasn't explicitly stated that non-Working Capital users were affected.
Geographic Scope
PayPal operates globally, but the breach's geographic scope isn't clearly documented. Different countries have different data protection regulations:
- EU users: Protected by GDPR (stricter notification requirements, potential regulatory fines)
- US users: Protected by state-level regulations plus sector-specific rules
- UK users: Protected by UK Data Protection Act 2018
- Other regions: Variable protections
PayPal's notification obligations differ by jurisdiction, which is likely why the company maintained controlled messaging rather than comprehensive public disclosure.
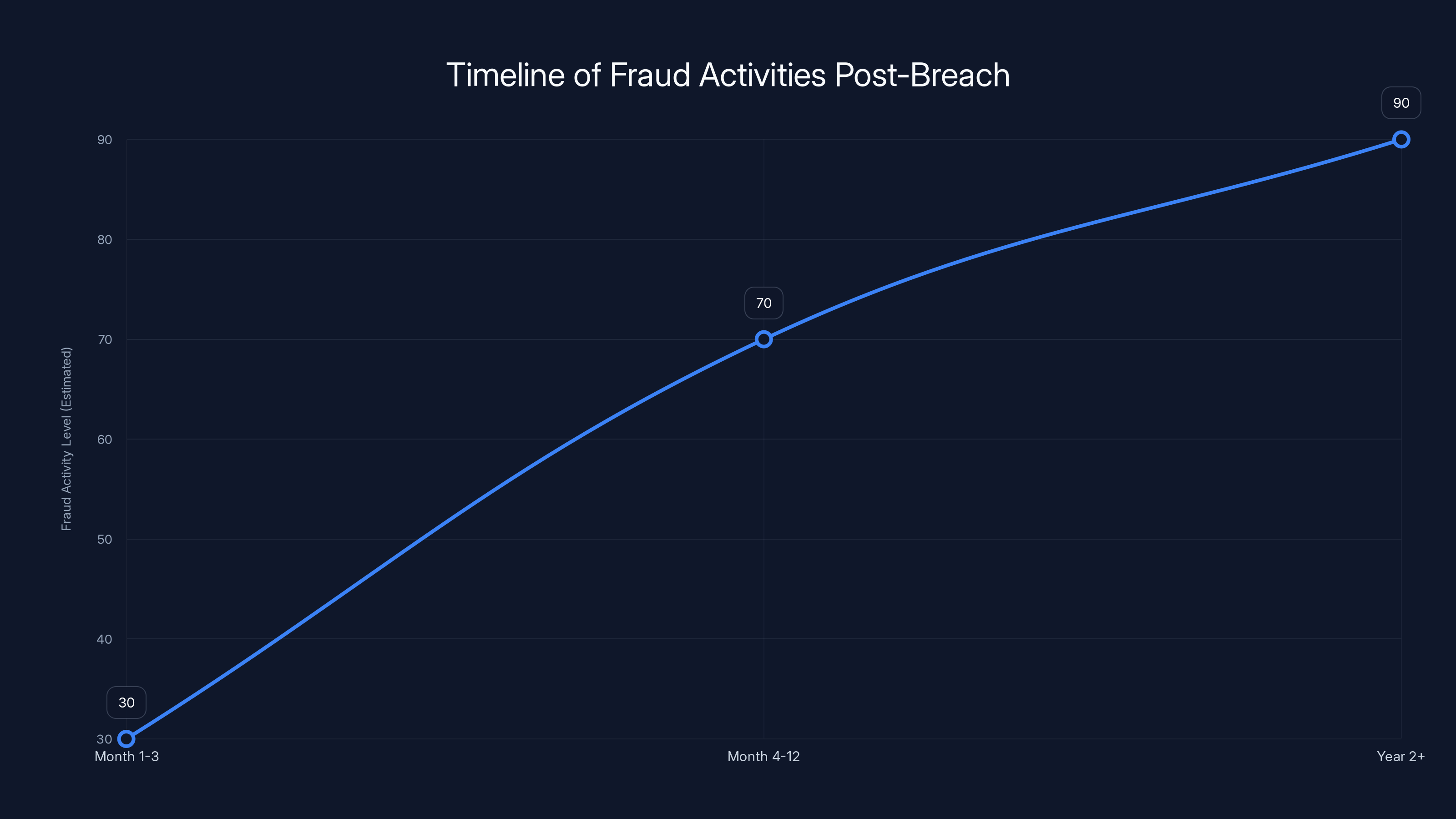
Estimated data suggests that fraud activity intensifies over time, peaking in the second year as identity theft attempts increase.
The Technical Root Cause: Why This Happened
A Coding Bug, Not a Sophisticated Attack
This is crucial to understand: PayPal wasn't breached by hackers. PayPal breached itself. The company's own code contained a bug that exposed data directly to the internet. No zero-day exploits. No social engineering. No credential theft.
A coding bug in the PayPal Working Capital application allowed unauthorized access to customer data. PayPal hasn't released technical details about the specific bug, but based on industry patterns, common causes include:
- Authentication bypass: The application failed to properly verify user permissions, allowing anyone to view anyone else's data
- SQL injection: Improperly sanitized inputs allowed attackers to query the database directly
- Insecure API endpoint: An API endpoint exposed sensitive data without requiring proper authentication tokens
- Unintended data exposure: A database query returned more information than intended due to incorrect field filtering
Regardless of the specific mechanism, the root cause was inadequate code review and testing before deployment. Bugs like this should be caught in:
- Unit testing: Individual code components tested in isolation
- Integration testing: Code components tested together
- Security testing: Code specifically reviewed for security vulnerabilities
- Staging environment: Testing in production-like environment before deployment
That PayPal's bug wasn't caught suggests either:
- Test coverage gaps (the vulnerable code path wasn't tested)
- Inadequate security testing (security wasn't a test criterion)
- Rushed deployment (proper testing was skipped for speed)
- Insufficient code review (the vulnerability was missed by reviewers)
How This Bug Persisted for Six Months
Once deployed, the bug should have been caught by monitoring systems that watch for suspicious data access patterns. If someone accessed customer data en masse, automated alerts should have fired.
PayPal's monitoring systems either weren't configured to catch this specific pattern, or the alerts were ignored/deprioritized. That's arguably more concerning than the initial bug. It suggests:
- Alert fatigue: So many false alerts that real threats get lost in noise
- Inadequate logging: PayPal wasn't logging data access attempts at all
- No monitoring: The vulnerable endpoint had no monitoring configured
Anyone who's worked in cybersecurity knows monitoring is perpetually underfunded. It's expensive, complicated, and doesn't prevent incidents—it only detects them. So it's often the last thing to get proper investment.

Impact: What Happened Because of the Breach
Unauthorized Transactions
PayPal stated that "a few customers experienced unauthorized transactions on their account." This is the most concerning impact because it shows the breach wasn't just passive data exposure—it enabled active financial crime.
We don't know the exact number of victims or the total amount stolen. "A few" could mean five or five hundred. PayPal reimbursed all victims, which is good, but also means PayPal ate the fraud losses rather than disclosing them.
How fraudsters likely used the data to commit unauthorized transactions:
- Account takeover: Using exposed account information to reset passwords and access accounts directly
- Linked card fraud: Using business address and phone information to match accounts and attempt transfers
- Business loan fraud: Using business information to apply for fraudulent advances against victim accounts
- Dispute fraud: Using personal details to open disputes and file chargebacks
The fact that some accounts experienced unauthorized transactions proves the breach wasn't theoretical. Real money was stolen. Real people were harmed. PayPal's response was appropriate (reimbursement + password resets), but it shouldn't have been necessary in the first place.
Identity Theft Risk (Ongoing)
Beyond immediate unauthorized transactions, the real danger is long-term identity theft. The exposed data—SSNs, DOBs, addresses—is the raw material for years of fraud.
Consider this timeline:
Months 1-3 after breach: Fraudsters validate data accuracy, test account access, organize stolen information into sales batches
Months 4-12: Data sold on dark web marketplaces to specialized fraud rings who purchase targeted datasets
Year 2+: Freshly purchased fraud rings attempt identity theft against victim accounts, opening business lines of credit, applying for loans, filing tax returns
PayPal's notification came ~1 month after discovery. That means there was roughly a 6.5-month window where fraudsters had access to data but victims didn't know they were compromised. Sophisticated fraud rings use delayed-attack strategies specifically because they know most victims don't monitor their credit for months.
Regulatory Impact
Data breaches involving SSNs typically trigger mandatory breach notifications, which PayPal has done. But they also potentially expose PayPal to regulatory action:
- FTC investigation: The Federal Trade Commission investigates data breaches and can impose significant fines if companies fail to implement reasonable security measures
- State attorney general actions: State-level investigations and settlements
- Class action lawsuits: Victims suing PayPal for inadequate security, emotional distress, credit monitoring costs
- GDPR fines: If EU residents were affected, PayPal could face substantial GDPR penalties
PayPal's offering of two years of free credit monitoring suggests the company is trying to head off class action litigation by providing remediation services. However, free credit monitoring doesn't erase the breach's impact or liability.

The timeline suggests checking all three credit reports initially, then staggering checks every three months for ongoing monitoring. Estimated data based on typical advice.
Immediate Response: What PayPal Did
Password Resets
PayPal immediately reset passwords for all affected accounts. This is standard breach response protocol and makes sense: if hackers had account access, password resets lock them out.
However, password resets create friction for legitimate account holders. Users receive notifications that their passwords were changed and need to set new ones. Some users might ignore the notification (phishing awareness is important here), or forget to update their password managers.
Unauthorized Access Revocation
PayPal revoked the unauthorized access that was enabled by the bug. In practical terms, this means the company:
- Deployed a code fix that eliminated the vulnerability
- Deployed the fix to production servers
- Terminated active connections that exploited the vulnerability
- Deployed monitoring to detect future similar attacks
The timeline isn't clear—how long between discovery on December 12 and fix deployment? Hours? Days? PayPal hasn't disclosed this, which is notable.
Equifax Credit Monitoring (2 Years, Free)
PayPal partnered with Equifax to provide two years of complimentary credit monitoring and identity restoration services. This means:
- Credit monitoring: Equifax watches for new accounts or credit inquiries opened in your name
- Credit freeze: Victims can freeze their credit to prevent new accounts
- Identity restoration services: If fraud occurs, Equifax assists with remediation
- Credit report access: Victims can view their credit reports at no cost
Two years is standard for data breach credit monitoring. It's not quite enough (identity theft can take years to materialize), but it's the industry norm.
Important caveat: You have to enroll in the monitoring service. PayPal didn't automatically enroll affected users; they just offered it. Some victims will miss the notification or forget to enroll, leaving themselves vulnerable.
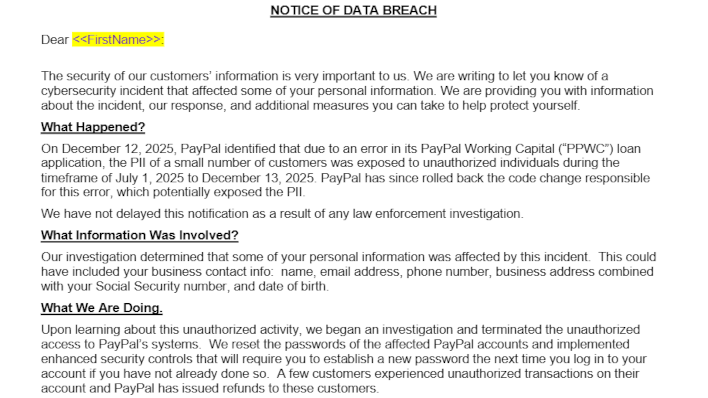
Customer Notification
PayPal notified affected customers via email, explaining:
- What happened (bug in Working Capital application)
- What data was exposed (PII including SSNs)
- When it happened (July 1 - December 13, 2025)
- What they're doing about it (free credit monitoring, password resets)
- What customers should do (monitor accounts, report suspicious activity)
The notification was appropriate and transparent. PayPal didn't try to minimize the breach or obscure details. However, the lack of specific numbers about affected users is frustrating for people trying to assess personal risk.

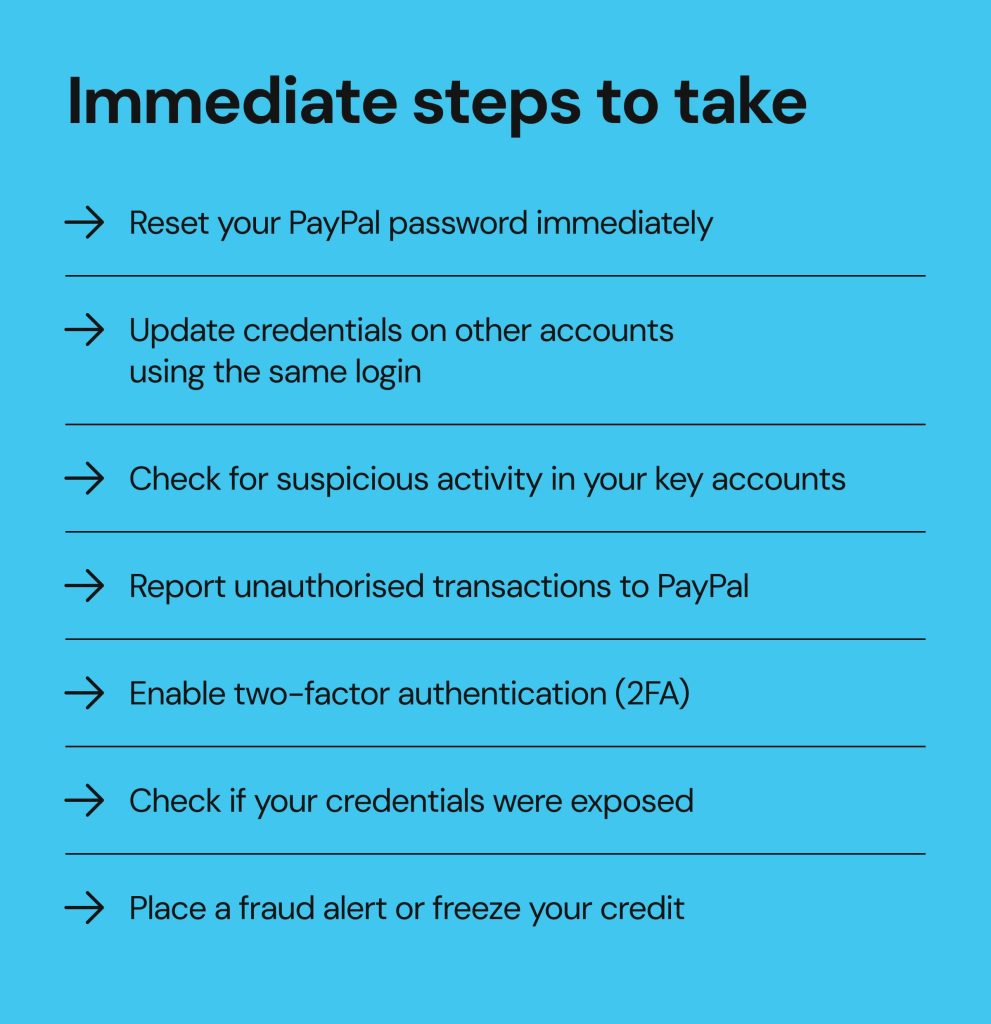
What You Should Do Right Now
1. Enroll in Equifax Credit Monitoring Immediately
If you received a PayPal breach notification, don't delay enrolling in the free credit monitoring. The notification likely included a link or instructions. Click it and complete enrollment.
You'll get:
- Access to your credit report
- Alerts when new accounts are opened in your name
- Notifications of credit inquiries
- Identity restoration assistance if fraud occurs
The enrollment typically takes 5-10 minutes online.
2. Monitor Your Credit Reports Manually
Don't rely solely on Equifax monitoring. Actively monitor your credit reports by visiting annualcreditreport.com (the official site), which entitles you to one free report per year from each bureau (Equifax, Experian, TransUnion).
Request reports strategically:
- Now: Get reports from all three bureaus to establish a baseline
- 3 months from now: Equifax report again
- 6 months: Experian report
- 9 months: TransUnion report
This spreads your monitoring throughout the year and gives you ongoing visibility.
When reviewing reports, look for:
- New accounts you didn't open
- Credit inquiries from companies you didn't contact
- Collection accounts that aren't yours
- Address changes that seem unfamiliar
- New credit cards or loans you don't recognize
If you spot anything suspicious, contact the credit bureau immediately and file a dispute.
3. Place Fraud Alerts
A fraud alert tells credit bureaus to require additional verification before opening new accounts in your name. It's not a credit freeze, but it adds a speed bump to the fraud process.
You can place a fraud alert by contacting any one of the three major credit bureaus:
- Equifax: 1-800-525-6285 or equifax.com/fraud
- Experian: 1-888-397-3742 or experian.com/fraud
- TransUnion: 1-800-680-7289 or transunion.com/fraud
Fraud alerts last one year (renewable) and are free. They're a good first step that doesn't severely impact your ability to open legitimate accounts.
4. Consider a Credit Freeze (Optional, But Recommended)
A credit freeze completely blocks access to your credit report, preventing fraudsters from opening accounts but also preventing you from opening new accounts without unfreezing first.
Credit freezes are free and can be placed with all three bureaus. They're stronger protection than fraud alerts but require more effort to manage (you have to unfreeze when you want to apply for credit).
If you don't plan to apply for new credit in the next year or so, a freeze is worth the minimal friction.
5. Update Your PayPal Security
For your PayPal account specifically:
- Change your password: Make it complex (16+ characters, mix of numbers, symbols, uppercase/lowercase)
- Enable two-factor authentication: Use an authenticator app (Google Authenticator, Authy, Microsoft Authenticator), not SMS when possible (SMS SIM swaps are a known attack vector)
- Review connected accounts: Remove any old linked bank accounts or credit cards
- Check account activity: Review recent logins and connected applications
- Update recovery email: Make sure your recovery email address is accurate and current
6. Watch for Phishing Attempts
Fraudsters often follow up data breaches with targeted phishing campaigns using the stolen data to make emails seem more legitimate.
You might receive emails that say:
- "Unusual activity detected on your PayPal account"
- "Confirm your business information for PayPal Working Capital"
- "Update your payment method to prevent service interruption"
- "Urgent: Your account has been compromised"
These emails try to trick you into:
- Clicking malicious links
- Downloading malware
- Entering credentials on fake websites
- Providing additional personal information
Never click links in unexpected emails. If you receive a suspicious email claiming to be from PayPal, log into your PayPal account directly (not through the email link) and check for notifications there. Legitimate PayPal alerts will appear in your actual PayPal account.
7. Monitor Your Business Accounts
If you used PayPal Working Capital or have a PayPal business account, monitor these accounts extra carefully:
- Check for unauthorized loans: Review active loans and ensure they're all yours
- Monitor transaction history: Look for unusual transfers or withdrawals
- Review connected services: Ensure no unauthorized integrations were added
- Check email forwarding rules: If your account was accessed, fraudsters might set up email rules to hide malicious activity
- Verify API connections: Review any connected applications or services
8. Consider Identity Theft Insurance
Beyond credit monitoring, some people invest in identity theft insurance, which covers legal fees, lost wages, and costs associated with resolving identity theft if it occurs.
Services like LifeLock, IDShield, or Aura provide insurance in addition to monitoring. They're not free, but they provide more comprehensive coverage than credit monitoring alone.

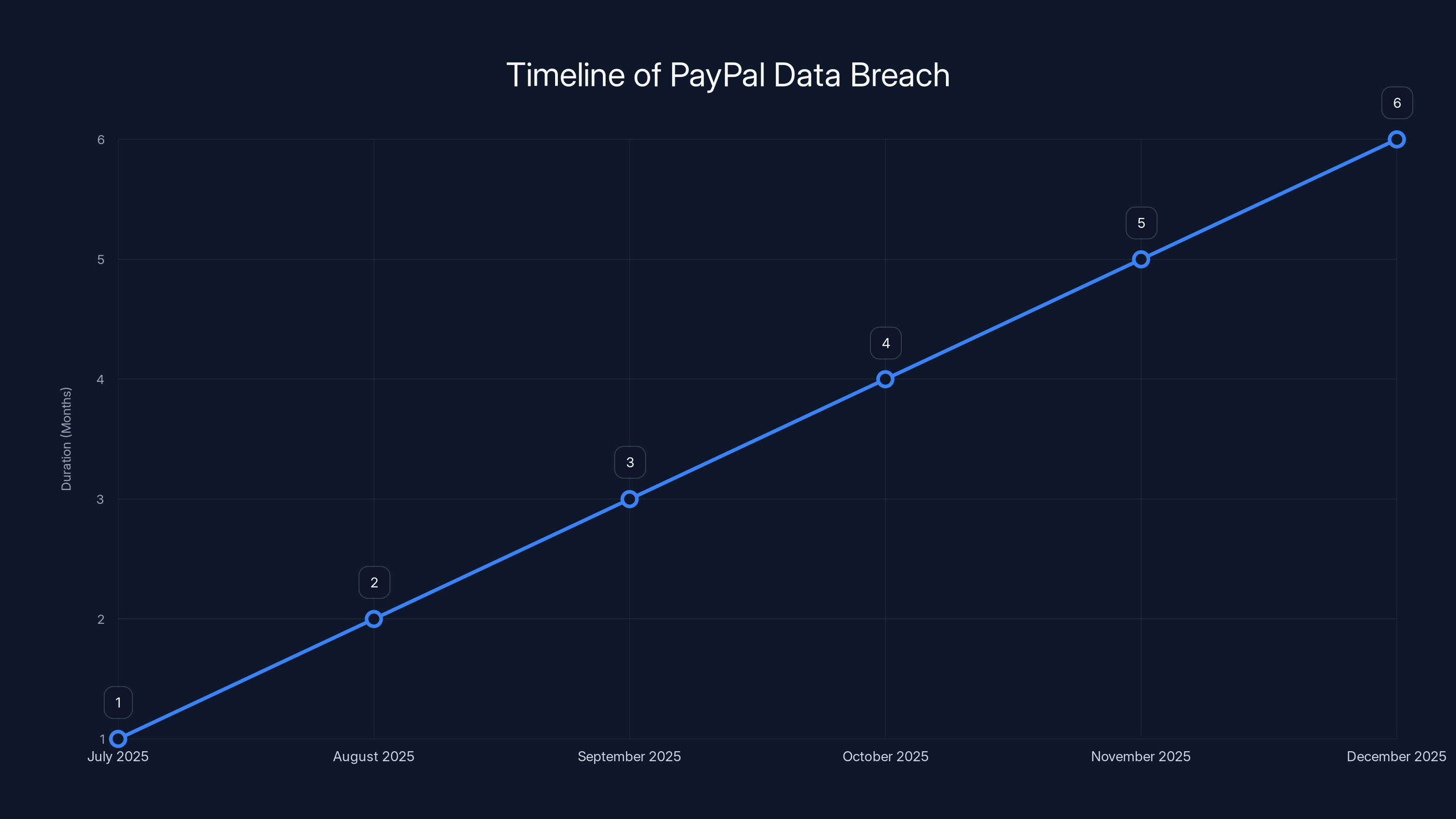
The PayPal data breach lasted approximately six months, from July to December 2025, before being discovered and patched.
Bigger Picture: Why This Keeps Happening
The Security Paradox
Here's what's maddening about this breach: PayPal is not a small startup without resources. The company processes billions in transactions, employs thousands of engineers, and invests significantly in security infrastructure. Yet a relatively simple coding bug slipped through every layer of defense.
This is the security paradox: companies can have the best security tools, the most experienced engineers, and still have vulnerabilities slip through. Why?
Scale and complexity. PayPal's codebase is massive—millions of lines of code across hundreds of services. Every new feature adds surface area for bugs. Every integration introduces potential vulnerabilities.
Speed versus security. Companies face pressure to ship features quickly. Security testing takes time. Proper code review takes time. Security audits take time. Something has to give, and it's often thorough security.
Alert fatigue. As companies deploy more monitoring, they generate more alerts. With thousands of daily alerts, security teams struggle to distinguish signal from noise. Real threats get lost in false positives.
Assumption of competence. Large companies assume their security is already solid, so they under-invest in basics like monitoring and code review, focusing instead on flashy tools that might catch 1% of incidents while ignoring practices that catch 90%.
The Breach Economics
Data breaches are incredibly profitable for cybercriminals:
- Stolen SSN: 5 each on dark web markets
- Business account info: 50 per complete profile
- Authentication credentials: 10 depending on account value
PayPal breach victims represented potentially hundreds of thousands of SSNs. At even conservative prices, we're talking millions of dollars in stolen data value. That's enormous profit incentive for sophisticated criminals.
From a criminal economics perspective, data breaches are among the best ROI activities available. The barrier to entry is low (once data is exposed, it's easily downloaded). The profit is high (data sells immediately). The risk is low (law enforcement rarely prosecutes cyber crime effectively).
Until the economics change—either through dramatically increased penalties or dramatically increased security making breaches less likely—we'll keep seeing them.
Industry Pattern Recognition
This isn't PayPal's first security incident, and it won't be the last for any company. Looking at patterns across the industry:
Software companies get breached regularly: From GitHub to Amazon to Microsoft, major tech companies have faced data breaches stemming from code vulnerabilities
Financial companies especially vulnerable: PayPal, Square, Stripe, and traditional banks all have experienced breaches because they're high-value targets
Simple bugs cause catastrophic breaches: Many of the most damaging breaches resulted from relatively simple vulnerabilities that should have been caught in testing
Detection delays are standard: Most companies don't discover their own breaches; third parties do. The average detection time is 207 days
Notification lags compound harm: Even after discovery, companies take time notifying users, creating additional exposure windows
None of this is unique to PayPal. This is systemic across the industry.
How to Assess Your Risk
Factors That Increase Your Risk from This Breach
You face higher risk if you:
- Applied for PayPal Working Capital: Your complete financial profile is compromised
- Have significant PayPal transaction history: Fraudsters can construct detailed business profiles
- Use the same password across services: Hackers can test your PayPal credentials against other sites
- Don't monitor your credit: You'll discover fraud months or years after it occurs
- Haven't enabled two-factor authentication: Account takeovers become trivial
- Have business accounts tied to your SSN: Fraudsters can open business accounts impersonating you
Factors That Decrease Your Risk
You face lower risk if you:
- Never applied for PayPal Working Capital: Your data might not have been exposed
- Use unique, complex passwords: Credential stuffing attacks fail
- Have fraud alerts or credit freeze active: New accounts require additional verification
- Monitor your credit regularly: You'll catch fraud attempts quickly
- Have two-factor authentication enabled: Account access requires secondary verification
- Receive credit monitoring alerts: You'll know immediately if accounts are opened
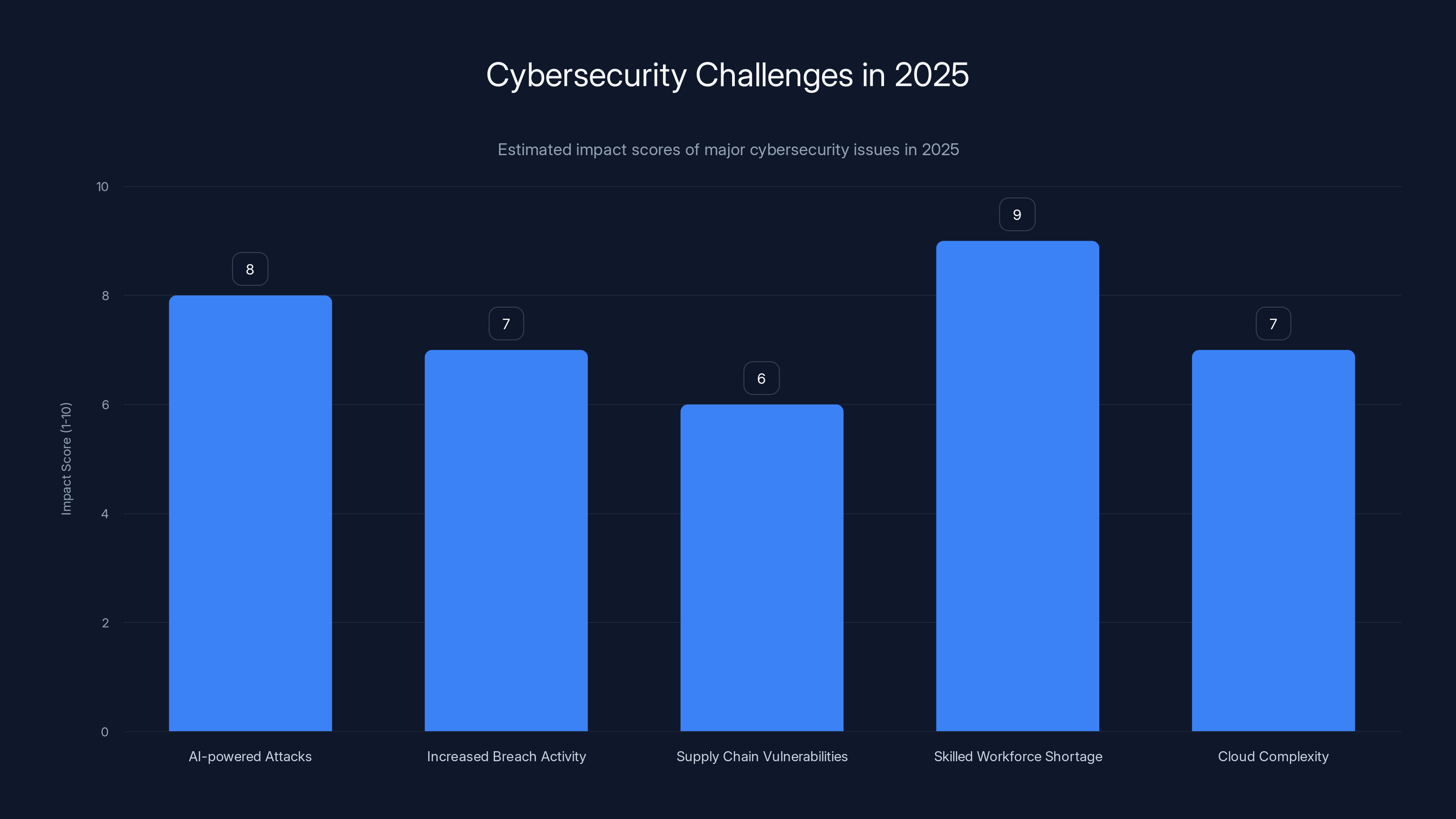
The cybersecurity landscape in 2025 is heavily influenced by AI-powered attacks and a significant shortage of skilled professionals, both scoring high in impact. (Estimated data)
Lessons for Other Companies (And Users)
What Companies Should Learn
First: Basic security practices prevent most breaches. There's no excuse for a simple coding bug to persist for six months undetected. Implementing proper code review, testing, and monitoring would have caught this vulnerability in days, not months.
Second: Data minimization is security. PayPal asks for SSNs because it's "standard practice" in lending, but many fintech companies use alternatives (alternative credit scoring, risk-based lending, etc.). Companies should minimize data collection.
Third: Monitoring isn't optional. Reactive penetration testing and annual audits catch 10% of vulnerabilities. Continuous monitoring catches 90%. Companies must fund monitoring adequately.
Fourth: Breach response plans must be tested. PayPal's response was appropriate (notifying customers, offering credit monitoring), but the initial bug should have been prevented, not just managed after discovery.
What Users Should Learn
First: No company is inherently trustworthy. Even PayPal—a large, well-resourced company handling billions in transactions—had a six-month data exposure. Trust doesn't prevent breaches; security practices do.
Second: Assume your data is compromised. You don't need to wait for a breach notification. Start monitoring your credit now, use unique passwords, enable two-factor authentication on every account. Assume the worst case.
Third: Credit monitoring is essential hygiene. Just as you brush your teeth to prevent cavities, you should monitor your credit to prevent identity theft. It's not optional; it's necessary.
Fourth: Passwords are dead; authentication is king. If you haven't enabled two-factor authentication on your financial accounts, do it now. Passwords alone don't provide meaningful security anymore.

Timeline: What Happened and When
Here's the reconstructed timeline based on public information:
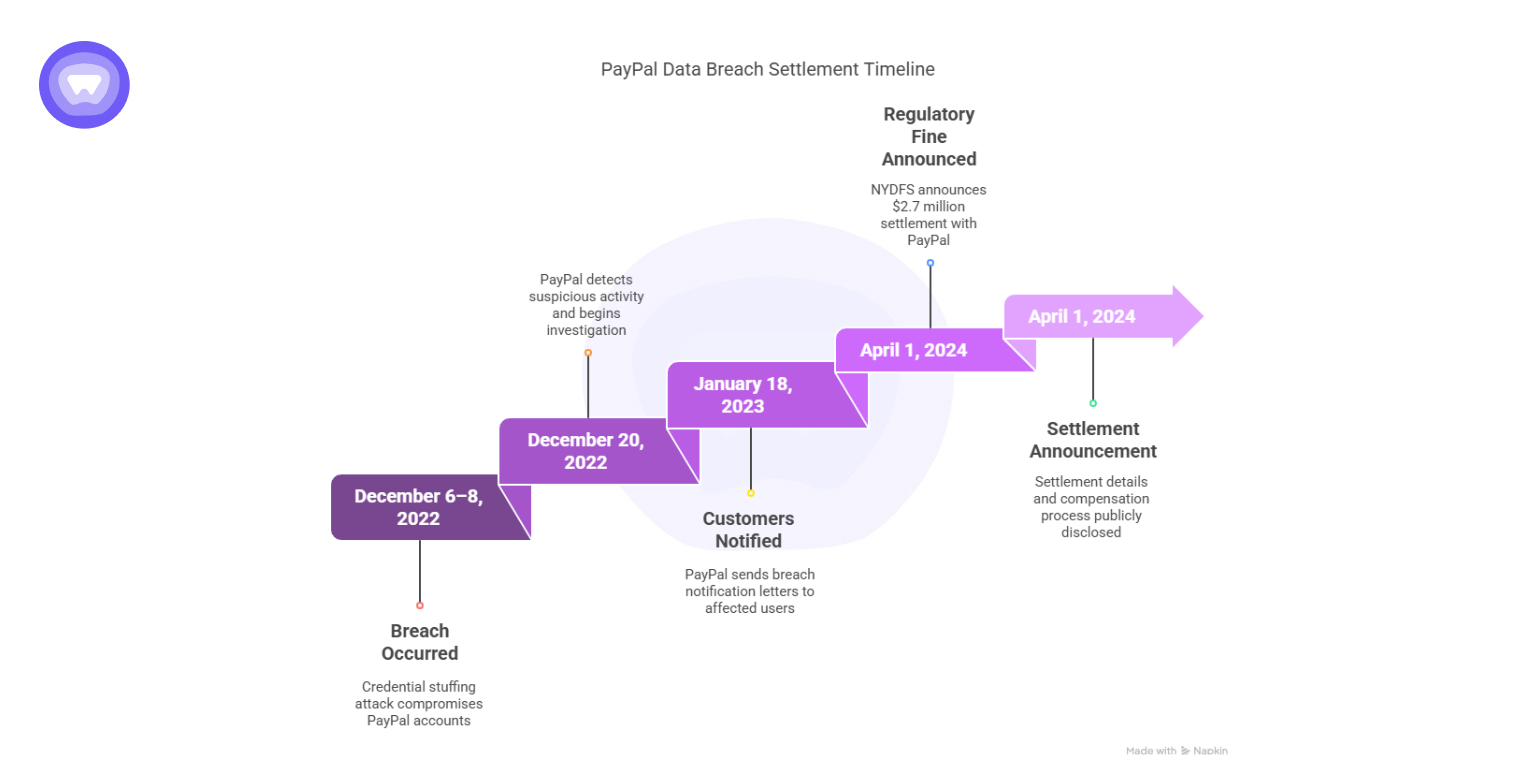
July 1, 2025: The bug is introduced into the PayPal Working Capital codebase (likely through a code deployment)
July 1 - December 12, 2025: The vulnerability persists undetected for 195 days. Sensitive customer data is exposed to anyone with internet access who knows where to look.
December 12, 2025: PayPal discovers the vulnerability through some detection method (method not publicly disclosed)
December 13, 2025: PayPal deploys a fix, revoking unauthorized access and patching the vulnerability
December 12-20, 2025: PayPal investigates the scope of exposure, gathers affected customer information, determines which data was accessed
Late December 2025: PayPal notifies affected customers via email with details about the breach and free credit monitoring offer
December 2025/January 2026: Regulatory notifications likely filed with state attorneys general and relevant data protection authorities
The most frustrating aspect of this timeline is the six-month gap between introduction and discovery. Modern security practices should catch such a vulnerability in days or weeks, not months.

The Broader Cybersecurity Context
Why 2025 Is a Difficult Year for Data Security
Multiple factors contribute to the cybersecurity landscape in 2025:
AI-powered attacks: Attackers are using AI to automate vulnerability discovery, making it faster to find exploits than companies can patch them
Increased breach activity: The number of reported breaches has grown 15-20% annually; attackers view data breaches as a reliable revenue source
Supply chain vulnerabilities: Attackers increasingly target companies' dependencies (cloud providers, libraries, third-party services) rather than attacking directly
Skilled workforce shortage: The cybersecurity industry faces a 3+ million person shortage of qualified professionals, leaving most companies under-resourced
Cloud complexity: As companies migrate to cloud infrastructure, the complexity of securing distributed systems increases exponentially
PayPal's breach reflects these broader trends. It's not a unique incident; it's representative of how difficult modern security has become.
Regulatory Implications and Compliance
Notification Requirements
PayPal was legally required to notify affected customers within specific timeframes depending on jurisdiction:
- Most US states: 30-60 days after discovery
- GDPR (EU): 72 hours to data protection authority if EU residents affected
- CCPA (California): Without unreasonable delay, but generally 45-60 days
- PIPEDA (Canada): Without unreasonable delay
PayPal appears to have met these requirements, notifying customers in late December (about 2 weeks after discovery), which is within standard windows.
Regulatory Consequences
Beyond notification requirements, PayPal could face:
FTC Action: The Federal Trade Commission has jurisdiction over PayPal's security practices. The FTC previously settled with Equifax over the 2017 breach, imposing fines and requiring security improvements. PayPal could face similar action.
State Attorney General Investigations: All 50 states have consumer protection authority and can investigate data breaches. Multiple states often coordinate investigations of major breaches.
Class Action Litigation: Victims can sue PayPal for inadequate security, emotional distress, identity theft costs, etc. The viability of these suits depends on specific state laws and whether victims can prove damages.
GDPR Fines: If PayPal failed GDPR obligations (unlikely—PayPal generally complies with GDPR), fines could reach up to 4% of annual revenue.
PayPal's offering of free credit monitoring suggests the company is trying to mitigate regulatory and legal exposure by providing meaningful remediation.
How This Compares to Other Major Breaches
PayPal vs. Other Financial Institution Breaches
2017 Equifax Breach:
- Data: SSNs, birth dates, addresses, driver's licenses
- Scale: 147 million people
- Duration: Potentially years undetected
- Settlement: $700 million
- Impact: Most damaging consumer breach in US history
2020 T-Mobile Breach:
- Data: Phone numbers, SSNs, driver's license numbers
- Scale: 40 million people
- Duration: Months undetected
- Settlement: $350 million
- Impact: Repeated T-Mobile breaches damaged company reputation
2019 Capital One Breach:
- Data: SSNs, credit card numbers, bank account information
- Scale: 106 million customers
- Duration: Several months undetected
- Settlement: $100 million + ongoing security investments
- Impact: Forced company to increase security spending
2025 PayPal Working Capital Breach (This Incident):
- Data: SSNs, birth dates, addresses, phone numbers
- Scale: Unknown (likely 100K - 1M people)
- Duration: 6 months undetected
- Settlement: TBD (likely $50-500M depending on scale and regulatory action)
- Impact: TBD (depends on identity theft rate and regulatory response)
In comparative terms, the PayPal breach is significant but not catastrophic. If the scale is under 500K people, it's smaller than historical breaches. However, the six-month duration is concerning because it suggests inadequate security monitoring.

Data Broker and Dark Web Risk
Where Your Data Ends Up
Once exposed, stolen data follows a predictable path:
Day 1-3: Attackers harvest exposed data, validate its accuracy, organize into batches
Day 4-14: Data is aggregated with other sources (previous breaches, purchased lists, etc.) to create comprehensive profiles
Day 15-30: Data is listed for sale on dark web marketplaces (Raid Forums, Exploit, Nulled, etc.)
Day 30+: Purchasers (fraud rings, other criminals, data brokers) begin using data for targeted attacks
PayPal breach victims' data is likely already for sale on dark web marketplaces at this point. That doesn't mean your specific information was definitely purchased or used, but the risk exists.
How to Minimize Dark Web Exposure
While you can't prevent your data from being sold, you can take steps to reduce risk:
- Add your email to dark web monitoring services (many credit monitoring services include this)
- Monitor your SSN through services that alert you if it's seen in new breaches
- Check haveibeenpwned.com regularly to see if your email appears in known breach databases
- Use unique passwords so even if your credentials are compromised, other accounts aren't
- Enable two-factor authentication so stolen credentials alone can't access accounts

FAQ
What exactly was exposed in the PayPal data breach?
The breach exposed personally identifiable information (PII) for PayPal Working Capital users, including full names, email addresses, phone numbers, business addresses, Social Security numbers, and dates of birth. PayPal emphasized that payment card information (credit card data) was not exposed, which is one positive aspect of the breach. However, the exposure of SSNs and dates of birth is particularly concerning because these are the core data points needed for identity theft.
How long did the PayPal breach last before being discovered?
The vulnerability existed for approximately six months, from July 1, 2025, through December 13, 2025. PayPal discovered the breach on December 12, 2025, and immediately patched it. The six-month duration means fraudsters potentially had months to harvest data, analyze it, and prepare attacks before PayPal or affected users even knew about the exposure.
How many PayPal customers were affected by this breach?
PayPal hasn't disclosed the exact number of affected customers, referring only to "a subset of customers." The lack of specificity is frustrating because it makes it impossible to assess the breach's true scale. Estimates based on Working Capital adoption rates suggest anywhere from 50,000 to 500,000 people were likely affected, but this is speculation without official confirmation.
What should I do if I received a PayPal breach notification?
You should immediately enroll in the free two-year credit monitoring service offered through Equifax, place fraud alerts or a credit freeze with the three major credit bureaus (Equifax, Experian, TransUnion), change your PayPal password to something complex and unique, enable two-factor authentication on your PayPal account, and begin monitoring your credit reports for suspicious activity. Additionally, watch for phishing emails that might reference the breach to trick you into revealing information.
Can I hold PayPal legally responsible for the breach?
Yes, you may have legal recourse through class action lawsuits, which are typically filed after major breaches. The viability depends on your state's laws regarding data breach liability and whether you can demonstrate actual damages (like fraudulent charges, credit monitoring costs, or emotional distress). PayPal's response with free credit monitoring suggests they're trying to minimize legal liability, but lawsuits often still proceed. Consulting with an attorney is advisable if you experienced fraud or significant identity theft costs as a result of this breach.
Why wasn't this security vulnerability caught earlier?
The vulnerability should have been caught through multiple security practices: code review (reviewing code before deployment), unit testing (testing individual code components), integration testing (testing components together), security testing (specific security-focused testing), and continuous monitoring (watching for suspicious data access patterns). That it persisted for six months suggests at least one of these practices was inadequate or missing. This is a failure of security process, not an excuse for inadequate security.
How is this breach different from previous PayPal security issues?
PayPal has had security incidents before, but this one is notable for the duration of exposure (six months undetected), the sensitivity of exposed data (SSNs and complete personal profiles), and the fact that it was caused by a simple coding bug rather than sophisticated external attacks. It demonstrates that even large, well-resourced companies with dedicated security teams can have significant failures in basic security practices like code review and monitoring.
Should I close my PayPal account because of this breach?
Closing your account isn't necessary unless you're no longer using PayPal's services. The breach itself doesn't mean PayPal's systems are fundamentally insecure going forward. However, if you do use PayPal, ensure you've enabled two-factor authentication, use a strong, unique password, and monitor your account regularly for suspicious activity. The breach is a good reminder that no financial service is risk-free, and you should diversify your payment methods rather than relying exclusively on one platform.
How long will it take to know the full impact of this breach?
Identity theft resulting from this breach could manifest over years. The two-year credit monitoring PayPal is offering is standard, but identity theft can take 3-5+ years to fully materialize as criminals slowly use stolen data. You should monitor your credit reports for at least 3-5 years after this breach, not just the two years of included monitoring. Some fraud might occur immediately (as PayPal reported some unauthorized transactions), but most will likely occur months or years later as purchased data is used by various fraud rings.

Conclusion: Moving Forward After the Breach
The PayPal data breach is a reminder that no company—regardless of size, resources, or stated security investments—is immune to catastrophic security failures. A simple coding bug, left undetected for six months, exposed millions of people's most sensitive personal information.
What makes this breach particularly frustrating is that it was entirely preventable. Better code review processes could have caught the bug before deployment. Adequate security monitoring could have detected it within days, not months. Proper alerting could have prevented fraudulent transactions on customer accounts.
But here's the cold reality: these are expensive investments. They slow down feature development. They require hiring specialized expertise. They don't generate revenue or competitive advantage. So most companies—even well-resourced ones—under-invest in them.
Until the economics change (through dramatically increased penalties for breaches or dramatically increased security making them less profitable for criminals), we'll keep seeing similar incidents. The question isn't whether your data has been exposed in some breach. The question is when, to which companies, and what damage results.
The good news is that you can dramatically reduce your personal risk through relatively simple actions: monitoring your credit, using unique passwords, enabling two-factor authentication, and staying alert for phishing attempts. These aren't fool-proof—nothing is—but they significantly reduce the likelihood that a breach like this one will result in actual identity theft or financial loss.
PayPal's response was appropriate: notification within reasonable timeframes, free credit monitoring, account remediation, and transparency about what happened. But transparency and after-the-fact remediation shouldn't be necessary. Prevention should be the priority.
As a user, assume your data has been compromised somewhere. Assume your SSN is on a dark web marketplace. Assume criminals have profiles with your personal information. Operate accordingly: monitor actively, authenticate skeptically, and trust minimally. It's not the world we should want, but it's the world we have.

Key Takeaways
- PayPal's six-month data exposure was caused by a simple coding bug, not sophisticated cyberattacks, revealing fundamental monitoring gaps
- Exposed data includes SSNs and birth dates, enabling complete identity theft profiles that fraudsters actively use in dark web markets
- Immediate protective actions include enrolling in free credit monitoring, placing fraud alerts/credit freezes, and enabling two-factor authentication on all accounts
- Industry patterns show similar breaches are common because security enforcement is underfunded relative to feature development priorities
- Identity theft risks extend years beyond notification, requiring long-term credit monitoring and vigilance despite company-provided remediation services
Related Articles
- Figure Technology Data Breach [2025]: What Happened and What You Need to Know
- Figure Data Breach: What Happened to 967,000 Customers [2025]
- Billions of Exposed Social Security Numbers: The Identity Theft Crisis [2025]
- ATM Jackpotting Attacks: The Rising Threat to Cash Machines [2025]
- Adidas Data Breach: Was It Really Hacked or Third-Party? [2025]
- Abu Dhabi Finance Summit Data Breach: 700+ Passports Exposed [2025]
![PayPal Data Breach 2025: What You Need to Know [Full Guide]](https://tryrunable.com/blog/paypal-data-breach-2025-what-you-need-to-know-full-guide/image-1-1771846681479.png)



