Quantum Computing's Growing Threat to Elliptic Curve Cryptography [2025]
The digital age is built on the bedrock of cryptography. It's the invisible force protecting your online banking transactions, securing your emails, and keeping your personal data away from prying eyes. At the heart of this fortress lies elliptic curve cryptography (ECC), a system that has, until now, provided robust security through complex mathematical problems. However, the rapid advancements in quantum computing threaten to upend this security paradigm.
TL; DR
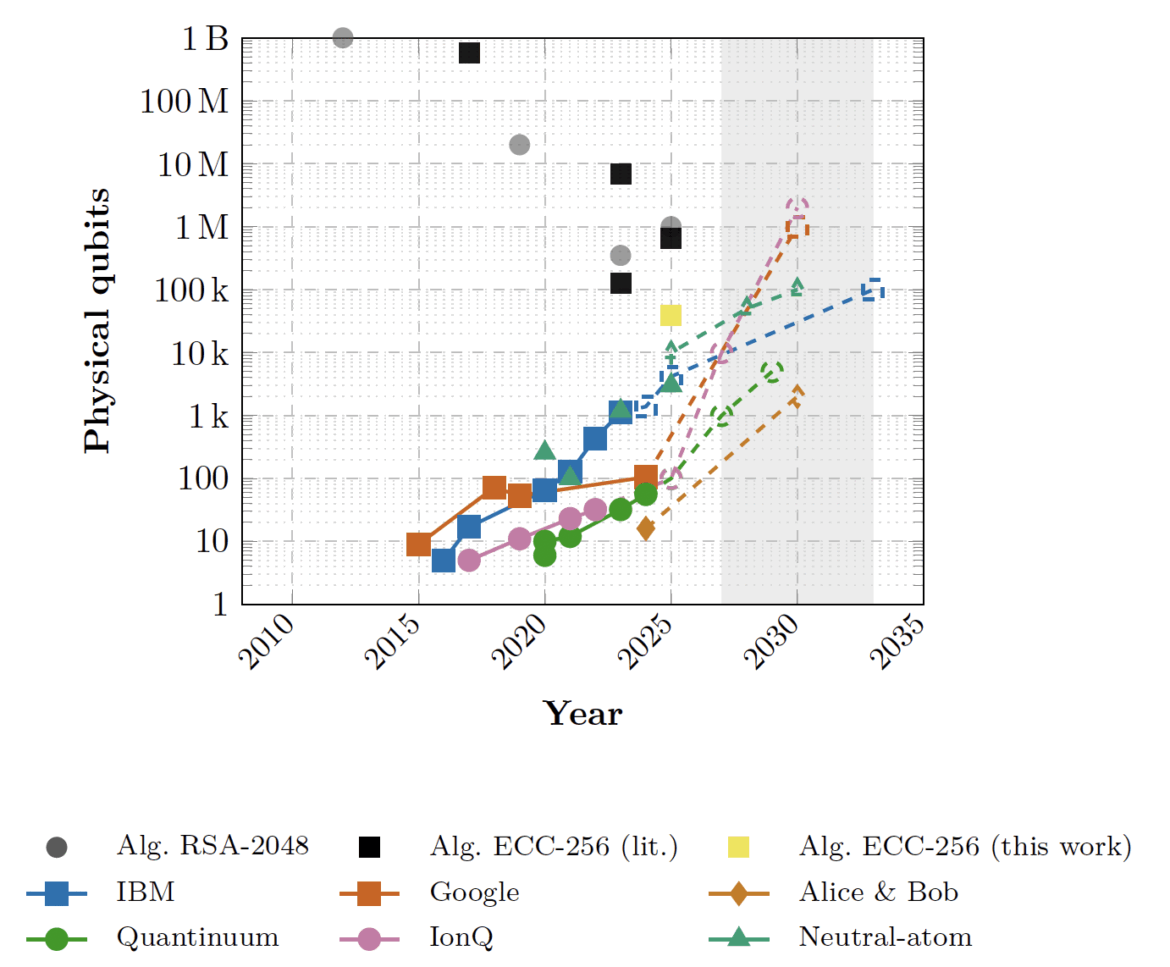
- Quantum Threat Realization: Recent advances in quantum computing have reduced the resources needed to break ECC significantly, as noted by SecurityWeek.
- Neutral Atom Qubits: Innovative use of neutral atoms as qubits can potentially crack 256-bit ECC within 10 days, according to CoinDesk.
- Cryptocurrency Vulnerability: Google researchers have demonstrated the capability to breach ECC-secured blockchains in under 9 minutes, as reported by CoinCentral.
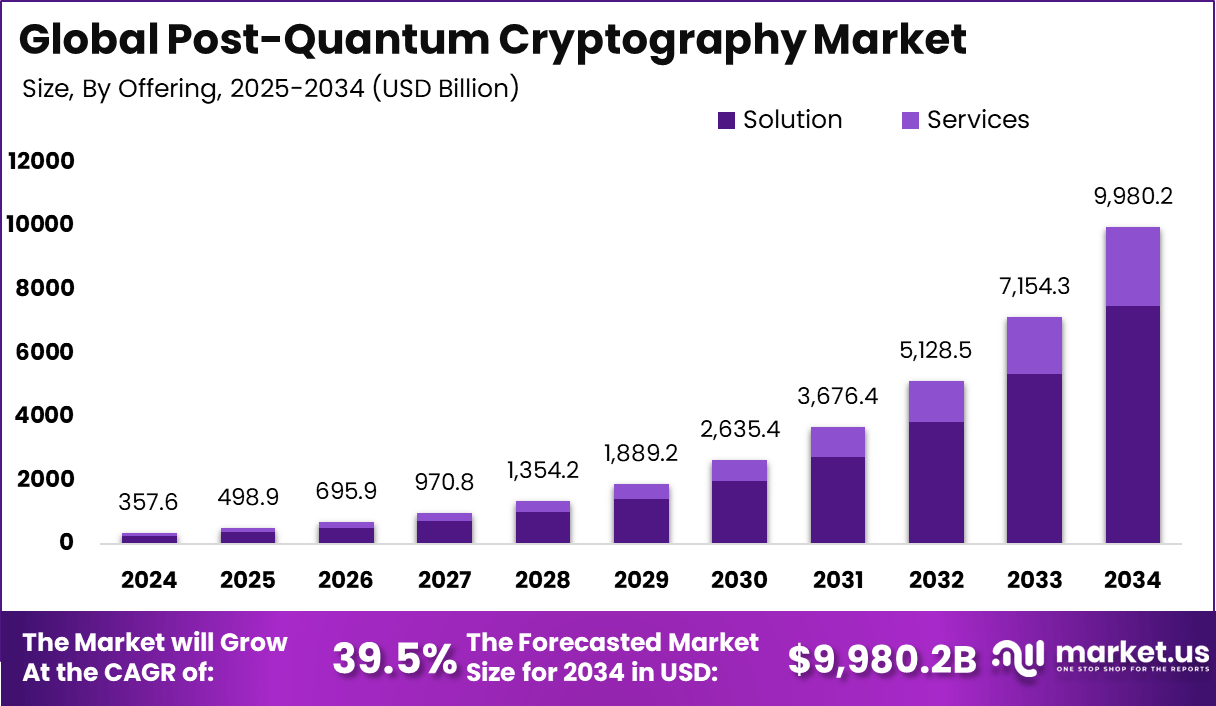
- Practical Implications: The shift to post-quantum cryptography is urgent to safeguard digital communications.
- Future Outlook: The race to develop quantum-resistant cryptography is a critical frontier in cybersecurity.
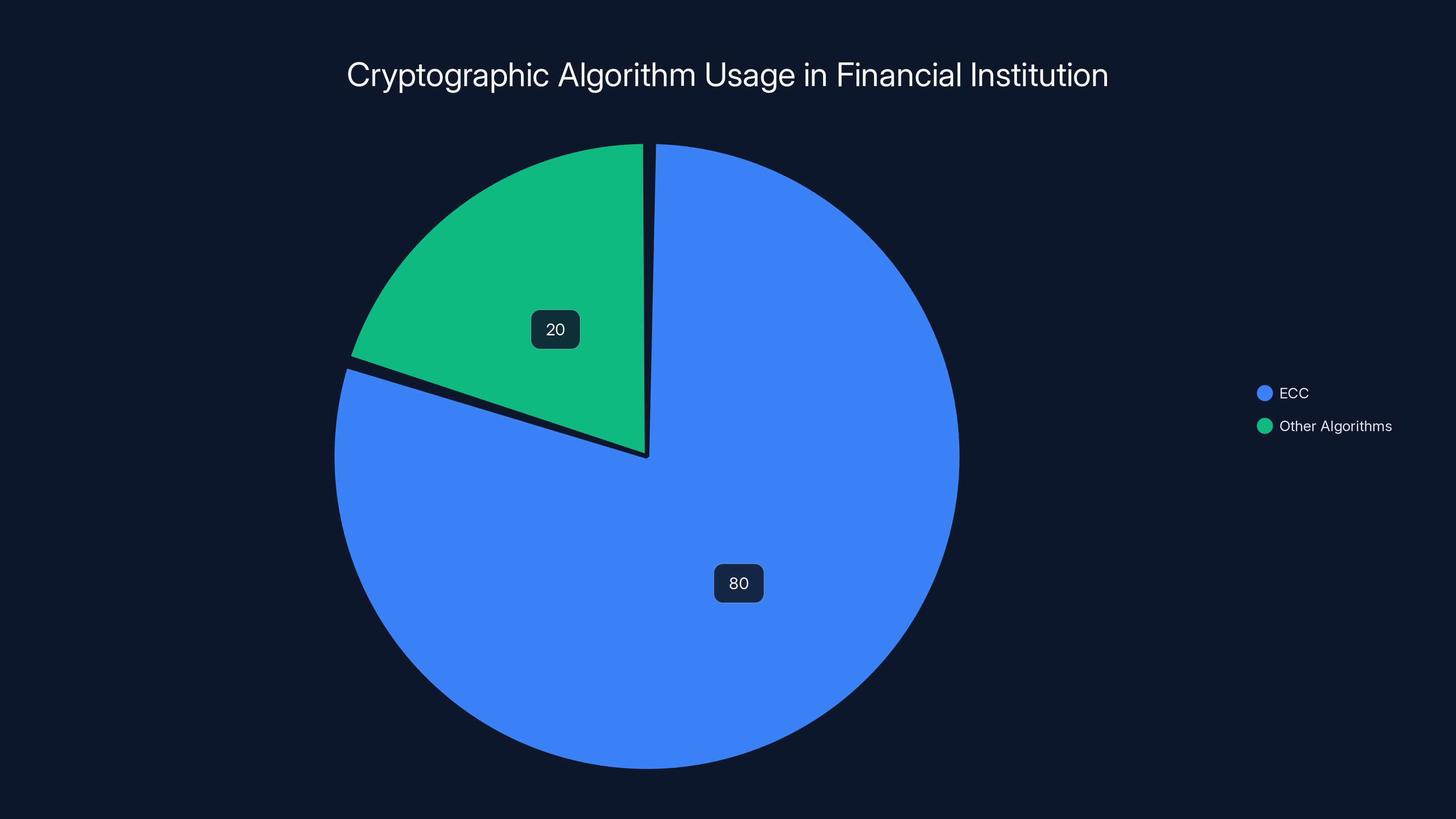
The financial institution found that 80% of its systems relied on ECC, prompting a shift to a hybrid cryptography approach to bolster security against quantum threats.
Introduction
In the world of cryptography, the term "Q Day" looms large. This is the day when quantum computers become powerful enough to break widely used cryptographic systems like ECC, posing a significant risk to global data security. While it might sound like science fiction, recent findings suggest that Q Day may arrive sooner than expected, as discussed in The Jerusalem Post.
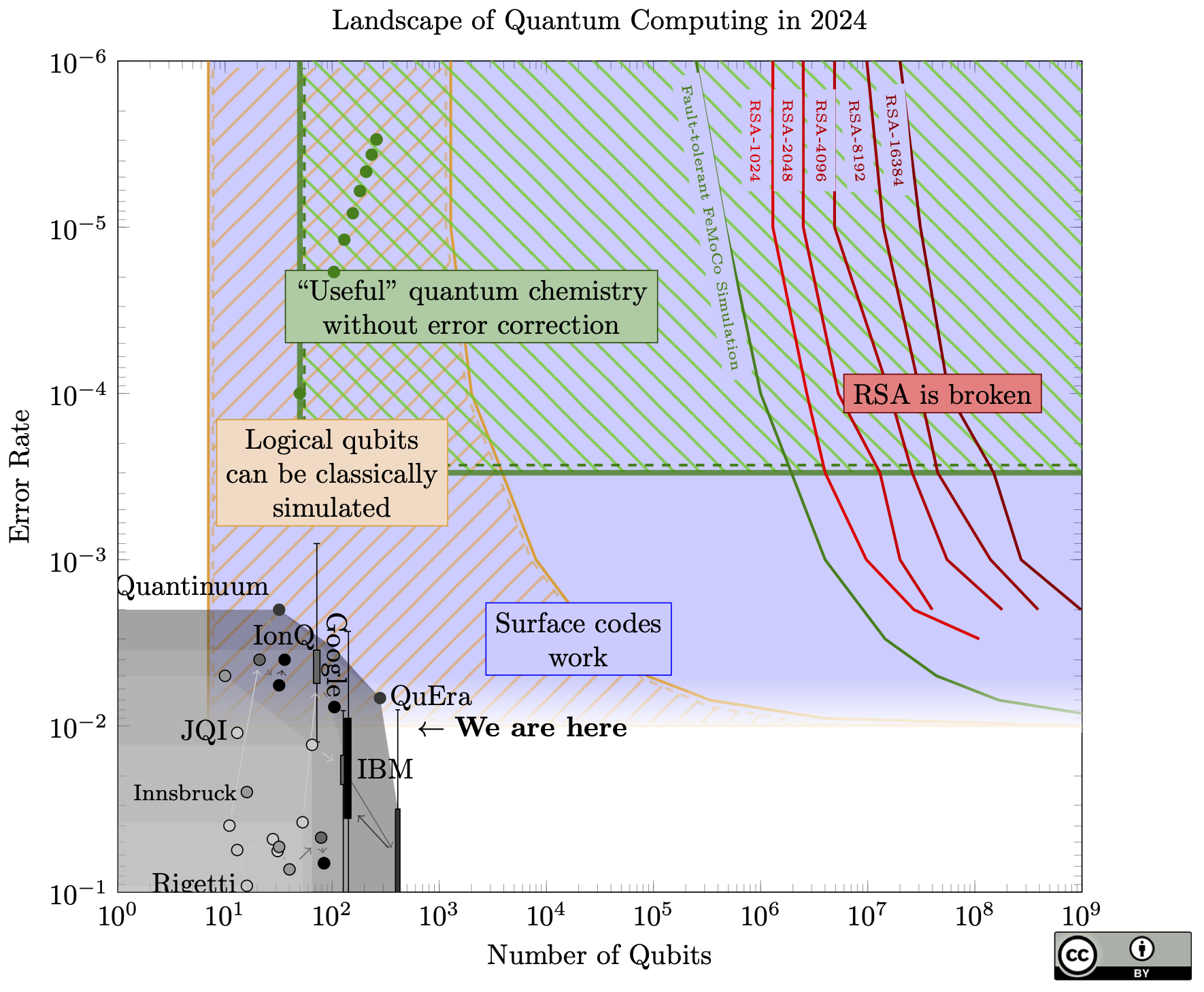
Quantum computing leverages the principles of quantum mechanics to process information in fundamentally new ways. Unlike classical computers, which use bits as the smallest unit of data, quantum computers use qubits, which can exist in multiple states simultaneously. This property, known as superposition, allows quantum computers to solve certain problems much faster than classical computers.

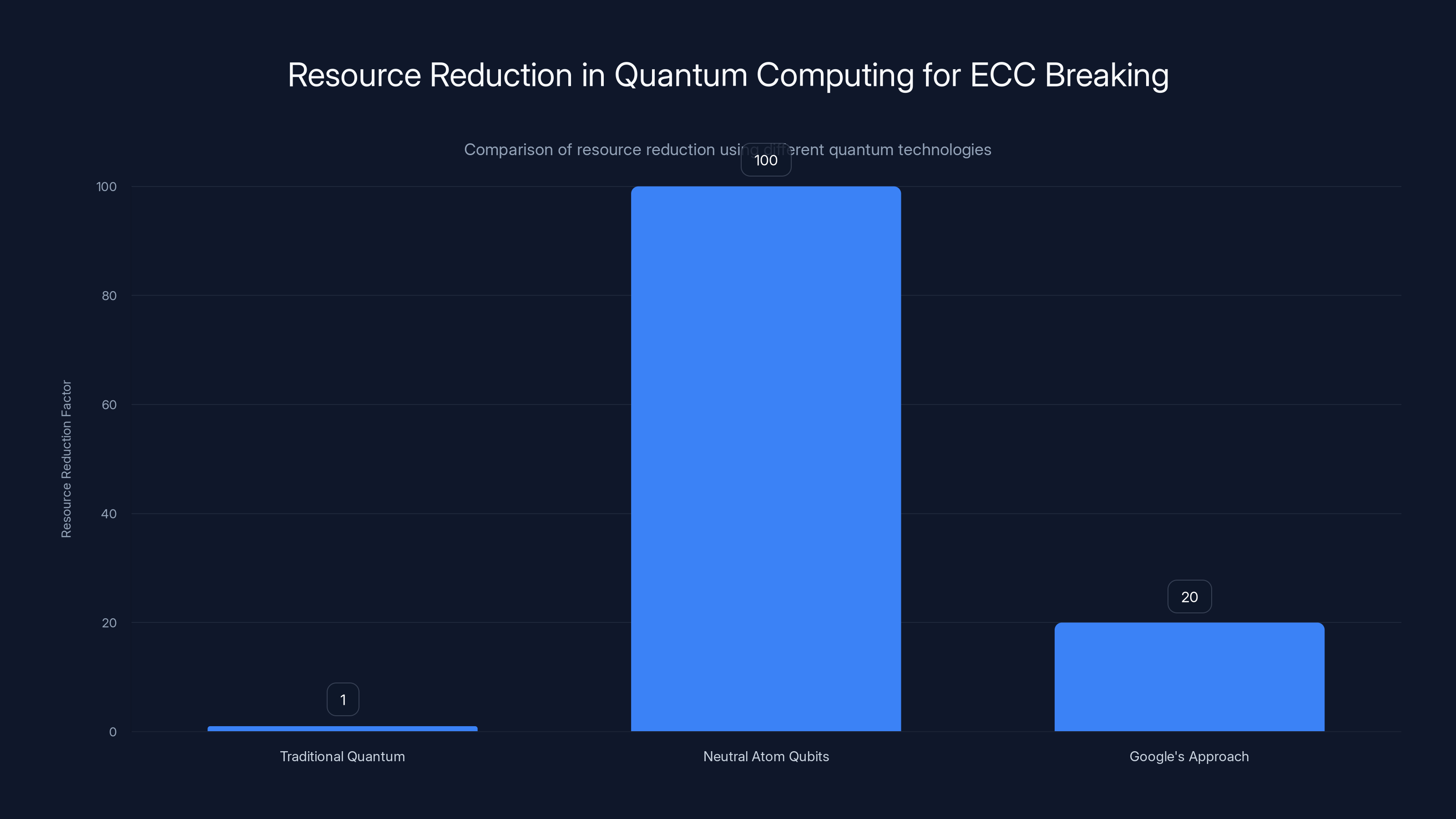
Neutral atom qubits offer a 100-fold resource reduction, significantly outperforming Google's 20-fold reduction in breaking ECC. Estimated data based on recent studies.
The Threat to Elliptic Curve Cryptosystems
Elliptic curve cryptography is favored for its efficiency and smaller key sizes compared to other systems like RSA. It relies on the difficulty of the elliptic curve discrete logarithm problem, which classical computers find hard to solve. However, quantum computers, equipped with Shor's algorithm, can potentially solve these problems in polynomial time, rendering ECC vulnerable, as highlighted by HackerNoon.
What Makes Quantum Computing So Powerful?
Quantum computers exploit two key principles of quantum mechanics:
- Superposition: Qubits can be in multiple states simultaneously, providing massive parallelism.
- Entanglement: Qubits can be entangled, meaning the state of one qubit can depend on the state of another, even at a distance.
These principles enable quantum computers to perform complex calculations much faster than classical computers.
Recent Advances in Quantum Computing
Recent independent studies have shown that the resources required to break ECC are far less than previously estimated. One study demonstrated the use of neutral atoms as reconfigurable qubits, allowing a quantum computer to break 256-bit ECC in just 10 days with 100 times less overhead, as detailed by CoinDesk. Another study by Google highlighted the possibility of breaking ECC-secured blockchains in under 9 minutes with a 20-fold resource reduction, as reported by SecurityWeek.
Neutral Atom Qubits
Neutral atoms are emerging as a promising qubit technology. They offer several advantages:
- Scalability: Neutral atoms can be easily scaled to thousands of qubits.
- Long Coherence Times: They maintain their quantum state longer, which is crucial for complex calculations.
- Reconfigurability: They can be rearranged easily, allowing more efficient quantum operations.
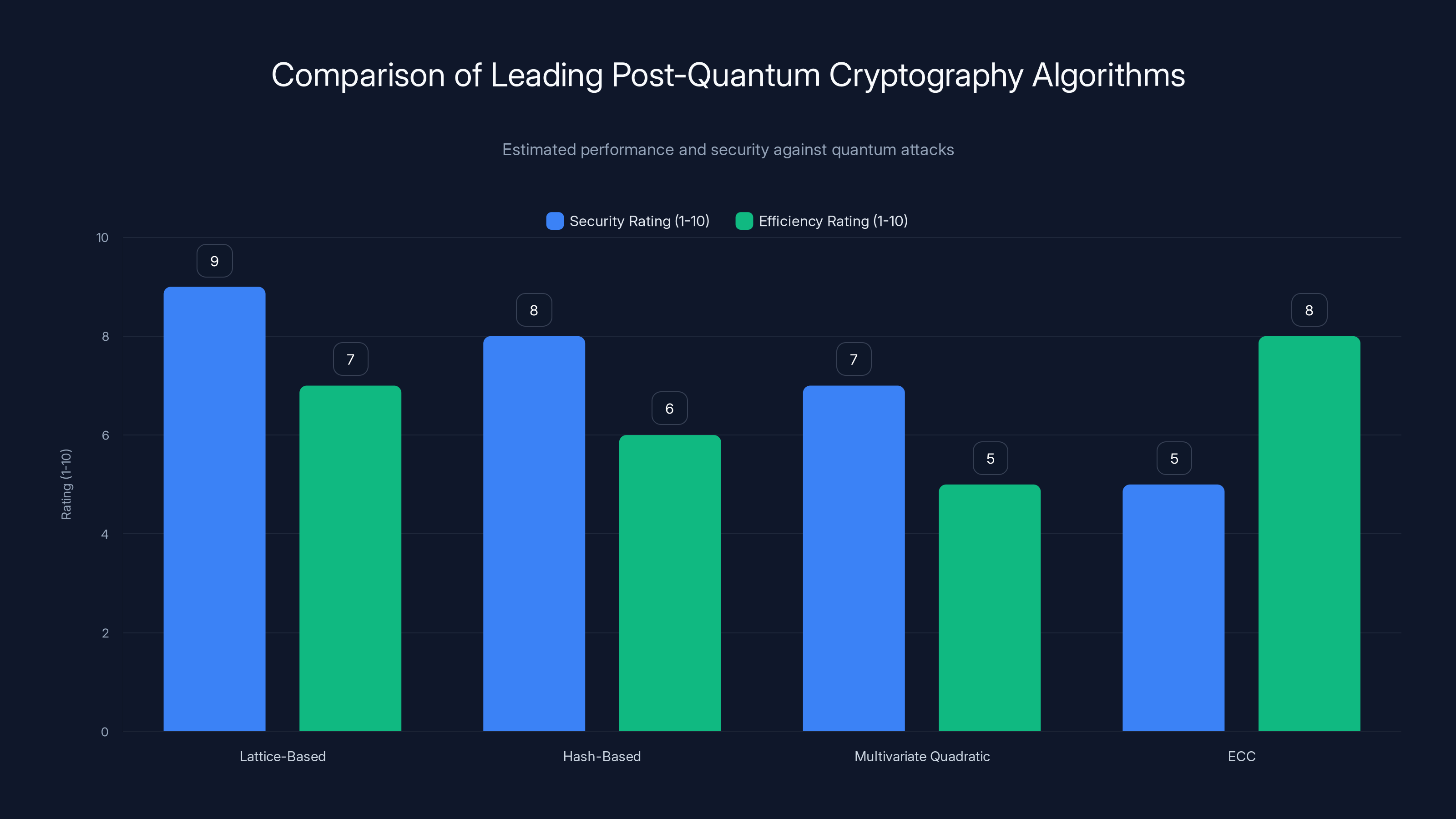
Lattice-Based Cryptography leads in security against quantum attacks, while ECC remains efficient but less secure. Estimated data.
Cryptographic Implications and Urgency
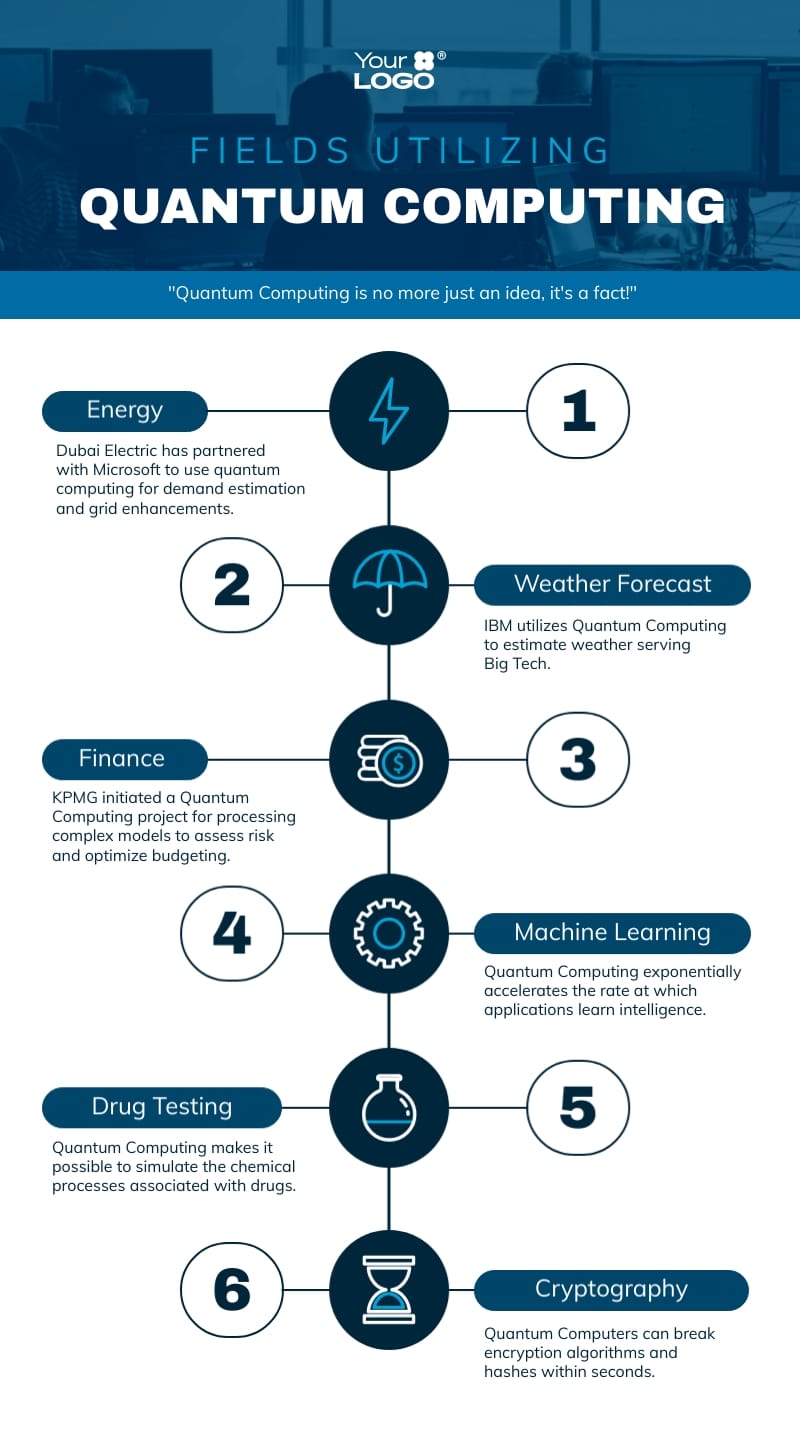
The implications of these advancements are profound. If quantum computers can break ECC, all data secured by this system becomes vulnerable. This includes:
- Cryptocurrencies: ECC secures most blockchains, including Bitcoin. A breach could lead to unauthorized transactions, double-spending, and loss of trust, as noted by CoinCentral.
- Financial Systems: Banks and financial institutions rely heavily on ECC for secure transactions.
- Government Communications: Classified government data could be exposed, leading to national security risks.
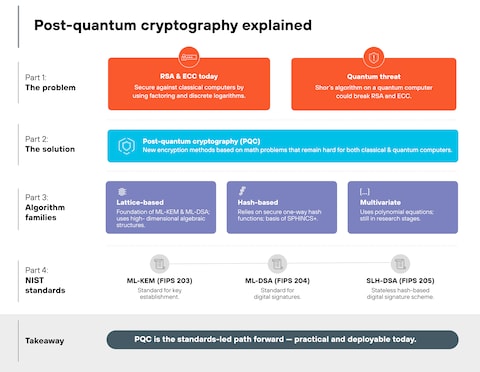
Transition to Post-Quantum Cryptography
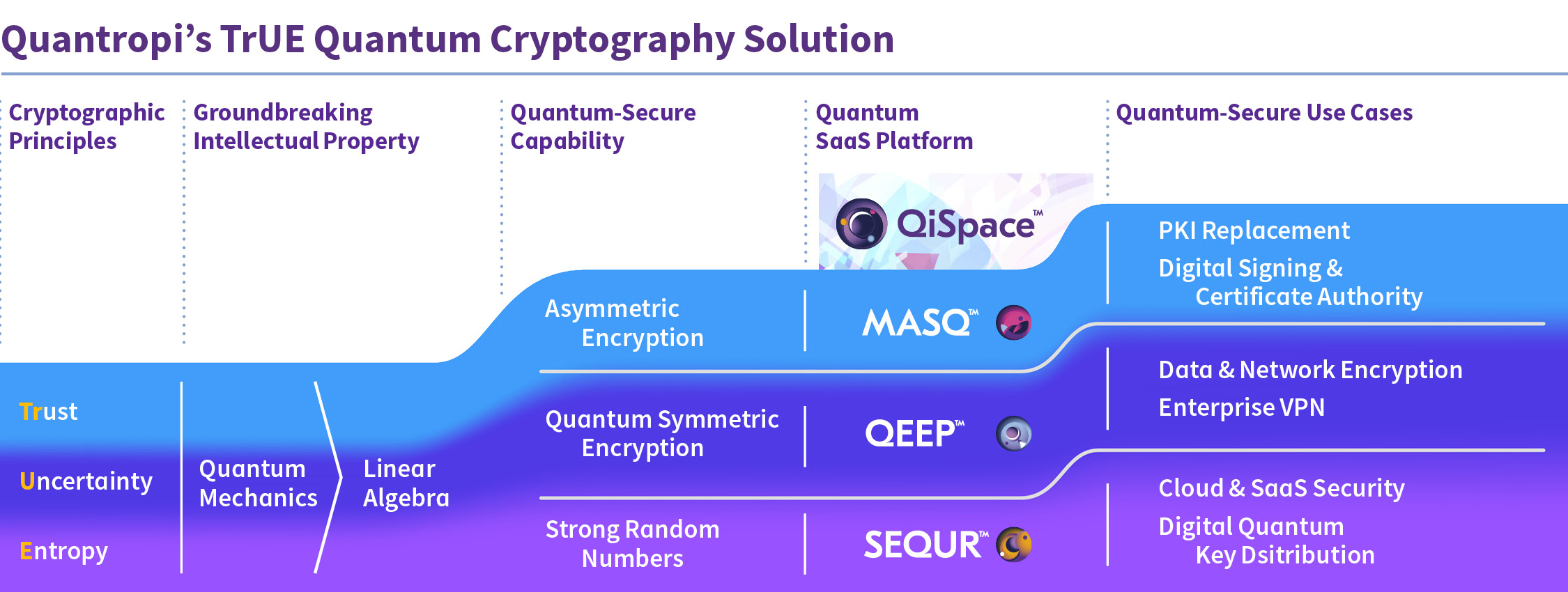
The quantum threat has accelerated efforts to develop quantum-resistant cryptographic algorithms, known as post-quantum cryptography (PQC). These algorithms aim to provide security against both classical and quantum attacks.
NIST's PQC Standardization
The National Institute of Standards and Technology (NIST) is spearheading the effort to standardize PQC algorithms. The selection process involves rigorous testing to ensure these algorithms can withstand quantum attacks while maintaining efficiency, as discussed in Google's blog.
Leading PQC Candidates
Some of the leading candidates in the PQC race include:
- Lattice-Based Cryptography: Uses complex mathematical structures called lattices, believed to be resistant to quantum attacks.
- Hash-Based Cryptography: Relies on hash functions, which are currently seen as safe against quantum computers.
- Multivariate Quadratic Equations: Involves solving systems of equations, a problem thought to be hard for quantum computers.
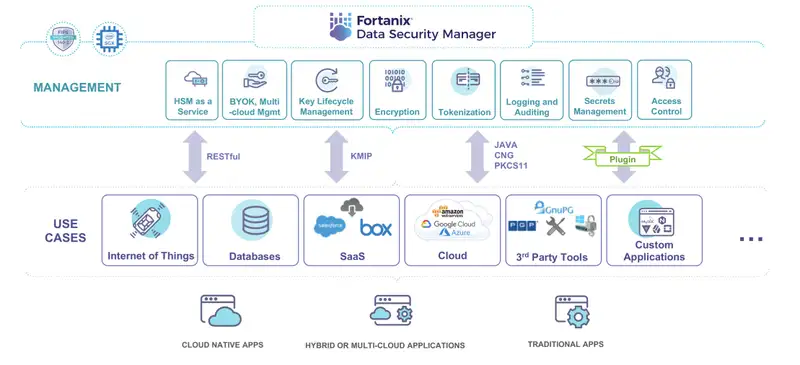
Practical Steps for Organizations
Organizations need to start preparing for the post-quantum era by:
- Conducting a Cryptographic Inventory: Identify all systems and applications using vulnerable cryptographic algorithms.
- Implementing Quantum-Safe Solutions: Gradually transition to PQC algorithms, starting with critical systems.
- Monitoring Developments: Stay informed about advancements in quantum computing and PQC standards.
- Educating Stakeholders: Ensure that leadership and technical teams understand the implications of quantum threats.
Real-World Case Study: Financial Institution
A leading financial institution conducted a cryptographic audit and discovered that over 80% of its systems relied on ECC. By transitioning to a hybrid approach using both ECC and lattice-based cryptography, they enhanced their security posture against future quantum threats, as highlighted in Polytechnique Insights.
Common Pitfalls and Solutions
As organizations transition to PQC, they may encounter several challenges:
- Compatibility Issues: Existing systems may not support new cryptographic algorithms. Solution: Use hybrid encryption techniques to maintain compatibility.
- Performance Overheads: PQC algorithms may introduce latency. Solution: Optimize algorithms and hardware to minimize performance impacts.
- Resource Constraints: Underestimating the resources needed for transition. Solution: Allocate dedicated teams and budgets for PQC implementation.

Future Trends and Recommendations
Quantum Hardware Advancements
Expect rapid developments in quantum hardware, particularly in qubit stability and error correction, which will make quantum computers more practical and accessible, as discussed in Chemical & Engineering News.
Increased Collaboration
Collaboration between academia, industry, and government will be crucial in developing and standardizing PQC solutions.
Continuous Monitoring of Quantum Threats
Organizations must establish frameworks to continuously evaluate their security posture in light of evolving quantum threats.
Conclusion
The quantum threat to elliptic curve cryptosystems is real and growing. While the sky isn't falling yet, the time to act is now. By transitioning to post-quantum cryptography and staying informed about advancements in quantum computing, organizations can safeguard their data and maintain trust in the digital ecosystem.
Use Case: Automate your cryptographic inventory with AI-powered solutions from Runable.
Try Runable For Free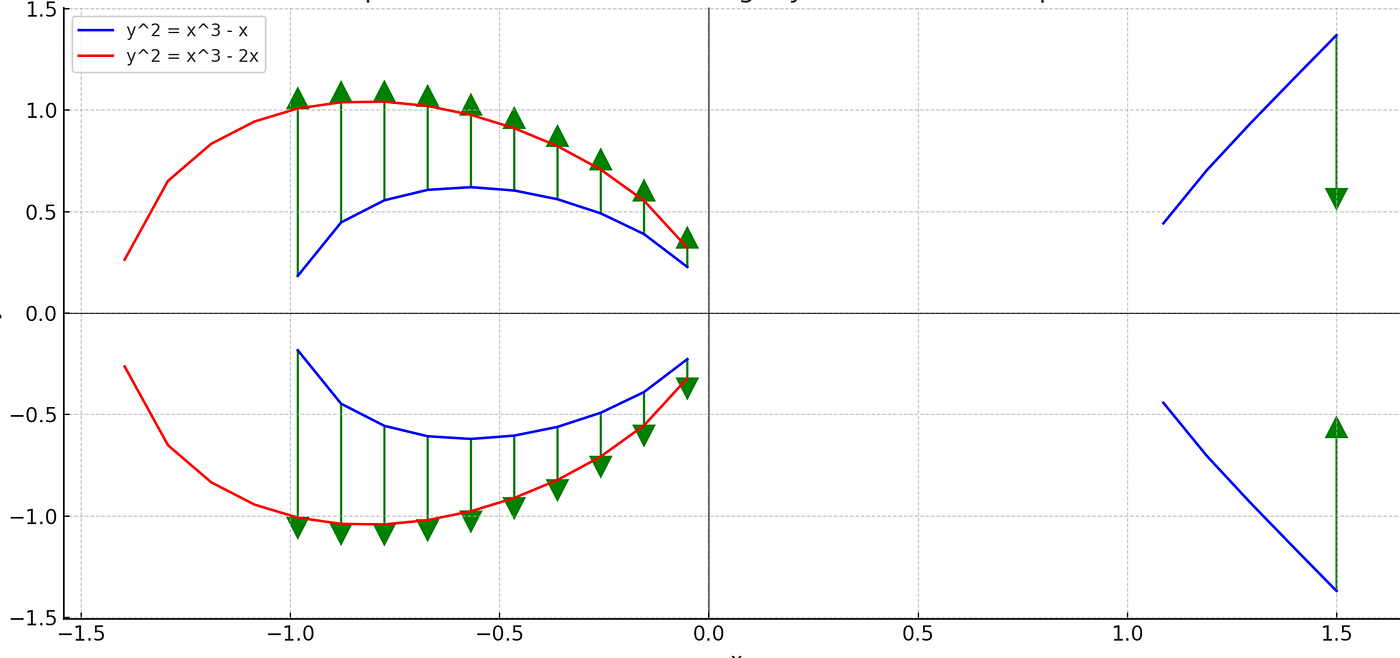
FAQ
What is elliptic curve cryptography?
Elliptic curve cryptography (ECC) is a cryptographic system that uses the mathematics of elliptic curves to secure digital communications.
How do quantum computers threaten ECC?
Quantum computers can potentially solve the mathematical problems that underpin ECC, making it vulnerable to attacks, as explained by The Quantum Insider.
What is post-quantum cryptography?
Post-quantum cryptography (PQC) refers to cryptographic algorithms designed to be secure against both classical and quantum attacks.
Why is post-quantum cryptography important?
PQC is crucial for ensuring data security in the face of advancing quantum computing capabilities.
How can organizations prepare for the quantum threat?
Organizations should conduct cryptographic audits, transition to PQC, and stay informed about quantum computing developments, as recommended by Help Net Security.
What are neutral atom qubits?
Neutral atom qubits are a type of qubit used in quantum computing that offer scalability and long coherence times, as introduced in Towards Data Science.
Key Takeaways
- Quantum computing advancements significantly reduce resources needed to break ECC.
- Neutral atom qubits can potentially crack 256-bit ECC within 10 days.
- Google researchers demonstrated ECC blockchain breaches in under 9 minutes.
- Transition to post-quantum cryptography is urgent to secure digital communications.
- NIST is leading efforts to standardize PQC algorithms.
- Organizations must conduct cryptographic audits and transition to PQC.
Related Articles
- AI Security: Understanding and Mitigating Risks in the AI Era [2025]
- World Backup Day 2026: Ultimate Guide to UGreen's 2-Bay NAS and Best Practices
- ExpressVPN's ExpressAI: A New Era in Privacy-Focused AI Chatbots [2025]
- Critical Flaw in OpenAI's Codex: Enterprise Security Risks and Solutions [2025]
- Citrix NetScaler Flaw: CISA's Patch Warning and What It Means [2025]
- Why Silence is No Longer a Security Strategy [2025]
![Quantum Computing's Growing Threat to Elliptic Curve Cryptography [2025]](https://tryrunable.com/blog/quantum-computing-s-growing-threat-to-elliptic-curve-cryptog/image-1-1774982059163.jpg)



