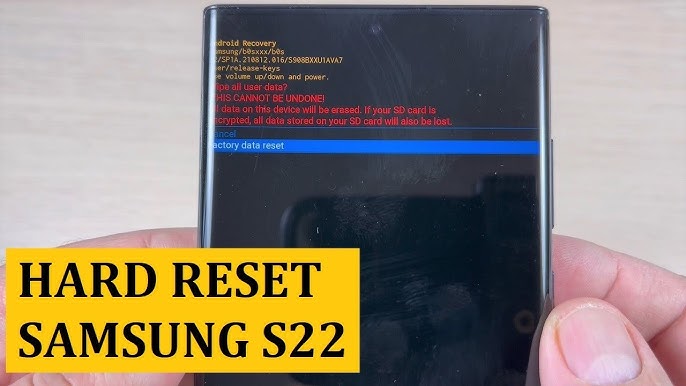
Samsung Galaxy S22 Ultra Factory Reset Hijack: Understanding the Issue and Solutions [2025]
In the digital age, smartphones are more than just communication devices; they are powerful tools that hold a significant portion of our lives. When something goes wrong, especially with high-end models like the Samsung Galaxy S22 Ultra, users are understandably concerned. Recently, reports have emerged about these devices being hijacked after a factory reset, leaving many users puzzled and vulnerable.
TL; DR
- Post-Factory Reset Hijacking: Some Samsung Galaxy S22 Ultra devices are being compromised after a factory reset.
- Security Risks: Hijacks can lead to data theft and unauthorized access.
- No Clear Fix: Samsung has yet to provide a definitive solution.
- Preventive Measures: Users should employ security best practices to minimize risks.
- Future Trends: Enhanced security measures and software updates are anticipated.

Estimated data suggests that biometric authentication will see the highest adoption rate, with 85% of new models expected to incorporate this feature by 2024.
Understanding the Issue
What is Factory Reset Hijacking?
A factory reset is supposed to return a device to its original state, deleting all personal data and settings. However, some users of the Samsung Galaxy S22 Ultra have reported that their devices are being hijacked even after this reset. This means unauthorized users are gaining access to the device, leading to potential data breaches and unauthorized use.
How Does It Happen?
The exact mechanism behind these hijacks is still a mystery. However, experts suggest several possible vulnerabilities:
- Residual Data: Incomplete deletion of data during the reset.
- Malware: Pre-installed or persistent malware that survives the reset.
- Network Exploits: Vulnerabilities in network settings that are not fully reset.

Factory Reset Hijack accounts for an estimated 25% of smartphone security issues in 2025, highlighting the need for improved security measures. (Estimated data)
Technical Insights
Residual Data and Incomplete Reset
Despite a factory reset's intention to wipe data, some information might remain. This happens due to the way data is overwritten. Modern storage technology, like SSDs used in smartphones, might not completely erase data, leaving remnants that could be exploited.
Malware Resilience
Certain malware types are designed to survive resets. These are often embedded deep within the system files or disguised as legitimate applications. They can re-establish themselves once the device restarts, posing significant security risks.
Network Vulnerabilities
Even after a reset, network settings might not fully revert to default. This includes saved Wi-Fi passwords and network configurations, which can be exploited by hackers.
Common Pitfalls and Solutions
Pitfalls
- Assuming Complete Data Wipe: Believing a factory reset thoroughly deletes all data can lead to complacency.
- Ignoring Software Updates: Outdated software is more susceptible to vulnerabilities.
- Neglecting Network Security: Overlooking network settings can lead to easy exploits.
Solutions
- Secure Data Wipe Tools: Use third-party apps to ensure complete data erasure.
- Regular Software Updates: Always keep your device's firmware up-to-date.
- Network Security Practices: Change network passwords and review settings post-reset.

Estimated data suggests that residual data and malware are the primary causes of factory reset hijacking, followed by network exploits.
Best Practices for Users
Data Protection
- Encrypt Your Device: Encryption adds an extra layer of security, making data inaccessible without proper credentials.
- Backup Regularly: Keep backups of important data to prevent loss during resets or hijacks.
Firmware Vigilance
- Enable Automatic Updates: This ensures your device always runs the latest security patches.
- Check for Unofficial Software: Avoid installing apps from unverified sources that could harbor malware.
Network Security
- Use VPNs: Virtual Private Networks can protect your data from network-based attacks.
- Secure Wi-Fi: Regularly update your Wi-Fi passwords and use strong encryption methods.

Future Trends and Recommendations
Enhanced Security Features
The industry is moving towards integrating more robust security features in upcoming models. These include:
- Advanced Biometric Authentication: Enhanced fingerprint and facial recognition technologies.
- AI-Powered Security: Using AI to detect and neutralize threats in real-time.
Recommendations for Manufacturers
- Thorough Reset Protocols: Ensure factory resets genuinely wipe all data, including system caches.
- Regular Security Audits: Conduct frequent audits to identify and patch vulnerabilities.
- User Education Initiatives: Provide guides and resources to help users secure their devices effectively.

Conclusion
The ongoing issues with the Samsung Galaxy S22 Ultra highlight the importance of robust security practices. While no device is immune to threats, understanding potential vulnerabilities and implementing best practices can significantly mitigate risks. As technology evolves, staying informed and proactive about security is more important than ever.
FAQ
What is a factory reset hijack?
A factory reset hijack occurs when unauthorized users gain access to a device even after it has been reset to its original factory settings, potentially leading to data breaches.
How can I protect my Samsung Galaxy S22 Ultra from hijacks?
You can protect your device by regularly updating its software, using encryption, employing secure data wipe tools, and maintaining strong network security.
Are there any tools to ensure complete data erasure?
Yes, several certified data erasure tools are available that can completely wipe data from your device, ensuring no residual data remains post-reset.
Why is my device vulnerable even after a reset?
Vulnerabilities can arise from leftover data, resilient malware, or incomplete network setting resets, which can be exploited by hackers.
What future security trends should I be aware of?
Future trends include enhanced biometric authentication, AI-powered security measures, and more rigorous reset protocols to ensure complete data erasure.
How often should I update my device's firmware?
It's recommended to enable automatic updates to ensure your device always runs the latest security patches, protecting it from known vulnerabilities.
Can using a VPN enhance my device's security?
Yes, using a VPN can protect your data from network-based attacks by encrypting your internet connection, making it difficult for hackers to intercept.
What role does AI play in smartphone security?
AI can enhance smartphone security by identifying and neutralizing threats in real-time, adapting to new attack vectors more efficiently than traditional methods.
Key Takeaways
- Some Samsung Galaxy S22 Ultra devices are being hijacked post-factory reset.
- Incomplete data wipes and malware resilience are likely causes of hijacks.
- Regular software updates and data protection practices can mitigate risks.
- Future trends include enhanced biometric authentication and AI-powered security.
- Manufacturers should ensure complete data erasure and conduct regular security audits.
Related Articles
- The Dark Side of Cybersecurity: NHS Scotland Domains and the Hidden Threats [2025]
- How Digital Devices Endanger Our Privacy Rights [2025]
- Understanding the LAPD Data Breach: Lessons in Cybersecurity [2025]
- Navigating Encryption Challenges: VeraCrypt's Developer Faces Microsoft Account Lock [2025]
- Stolen Session Cookies: The Hidden Threat to Account Security [2025]
- Unmasking SVG Steganography: How Hackers Use Tiny Images to Hide Credit Card Skimmers [2025]
![Samsung Galaxy S22 Ultra Factory Reset Hijack: Understanding the Issue and Solutions [2025]](https://tryrunable.com/blog/samsung-galaxy-s22-ultra-factory-reset-hijack-understanding-/image-1-1775817354018.jpg)



