'The Attacker Completed in Under Five Minutes': Unpacking the North Korea-Linked Crypto Attack [2025]
The digital landscape is fraught with threats, and the recent North Korea-linked campaign is a startling reminder of how sophisticated these can be. In this article, we delve into the details of the campaign, its implications for cryptocurrency executives, and best practices for safeguarding against such attacks.
TL; DR
- Sophisticated Threat: Attackers used fake Zoom meetings to impersonate legitimate contacts, as detailed in BankInfoSecurity's report.
- Rapid Execution: The entire attack could be completed in under five minutes, according to Wired's analysis.
- High-Stakes Target: Cryptocurrency executives are prime targets due to the value of digital assets, as noted in TRM Labs' blog.
- Impersonation and Malware: Attackers use social engineering and malware to gain access, highlighted by SecurityWeek.
- Protection Strategies: Multi-layered security measures are essential to defend against such threats, as emphasized by Cyfirma's intelligence report.
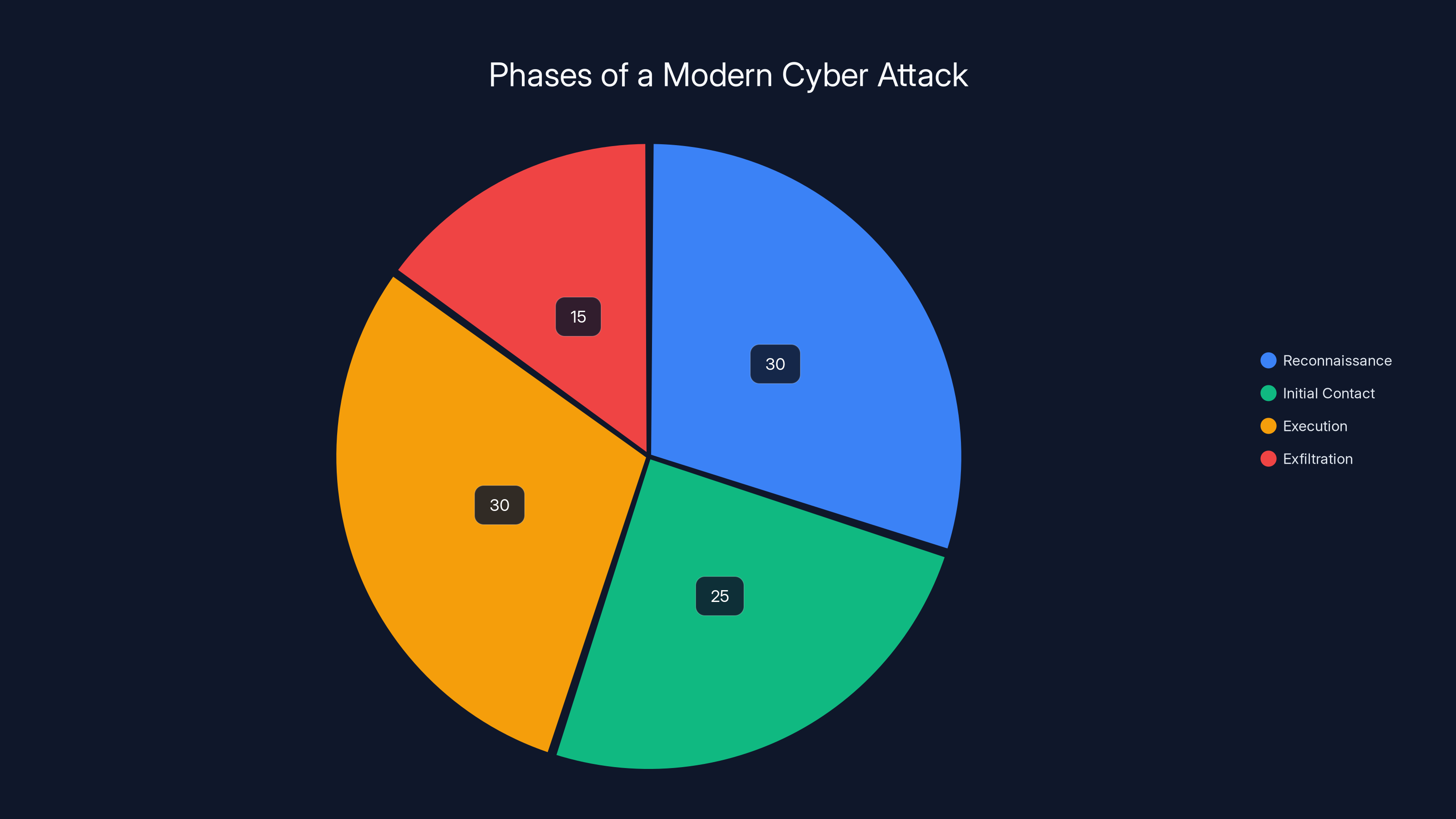
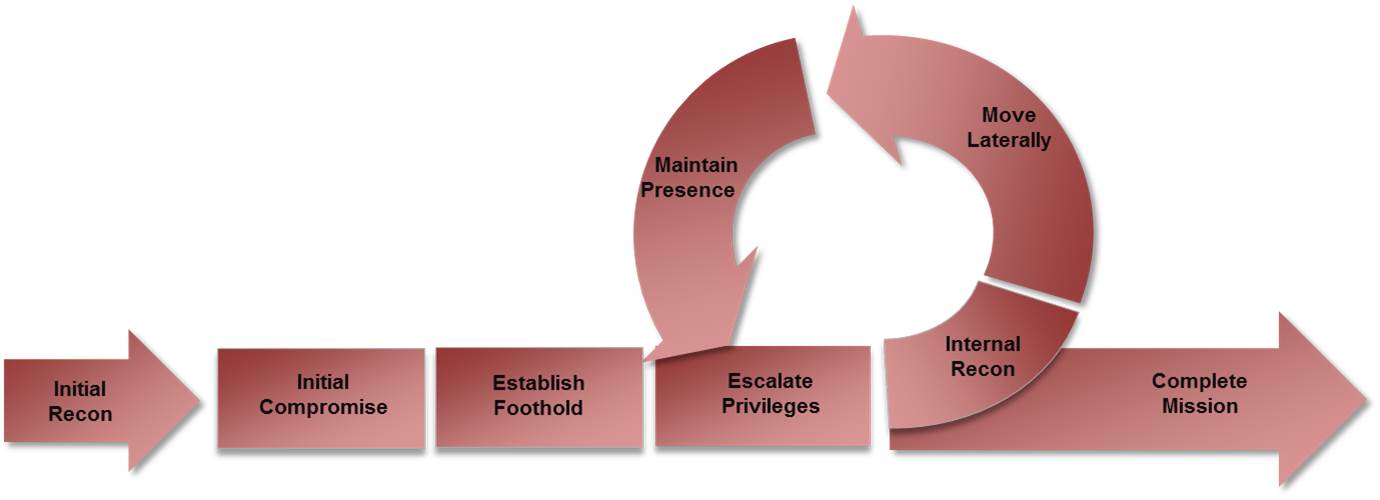
Estimated data shows that reconnaissance and execution phases consume the most time and effort in a modern cyber attack.
The Anatomy of a Modern Cyber Attack
Cyber attacks have evolved significantly, with state-sponsored groups deploying increasingly sophisticated techniques. In the case of the recent North Korea-linked campaign, the attackers crafted fake Zoom meetings to deceive their targets. Let's break down how such an attack is typically structured.
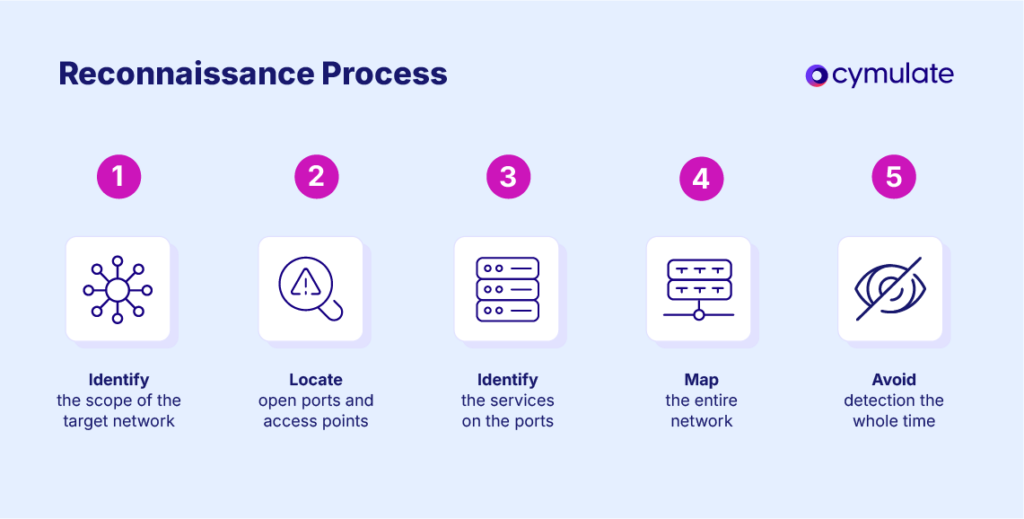
Phase 1: Reconnaissance
Before launching an attack, hackers conduct thorough reconnaissance. This involves gathering information about the target, such as email addresses, social media profiles, and professional networks. Using this data, attackers can create a convincing digital persona, as explained by MSU Denver's guide.
Phase 2: Initial Contact
The attackers initiate contact through seemingly legitimate emails inviting the target to a Zoom meeting. These emails mimic those from trusted colleagues or business partners, making them difficult to detect, as reported by TechCrunch.
Phase 3: Execution
Once the target joins the fake Zoom meeting, attackers deploy malware or engage in direct social engineering tactics. In some cases, they might request sensitive information, such as cryptocurrency wallet keys, under the guise of a legitimate business discussion, as noted by Yahoo Finance.
Phase 4: Exfiltration
After obtaining the desired information, attackers quickly exfiltrate data. The entire process can be completed in under five minutes, leaving little time for detection and response, as highlighted by Security.com.
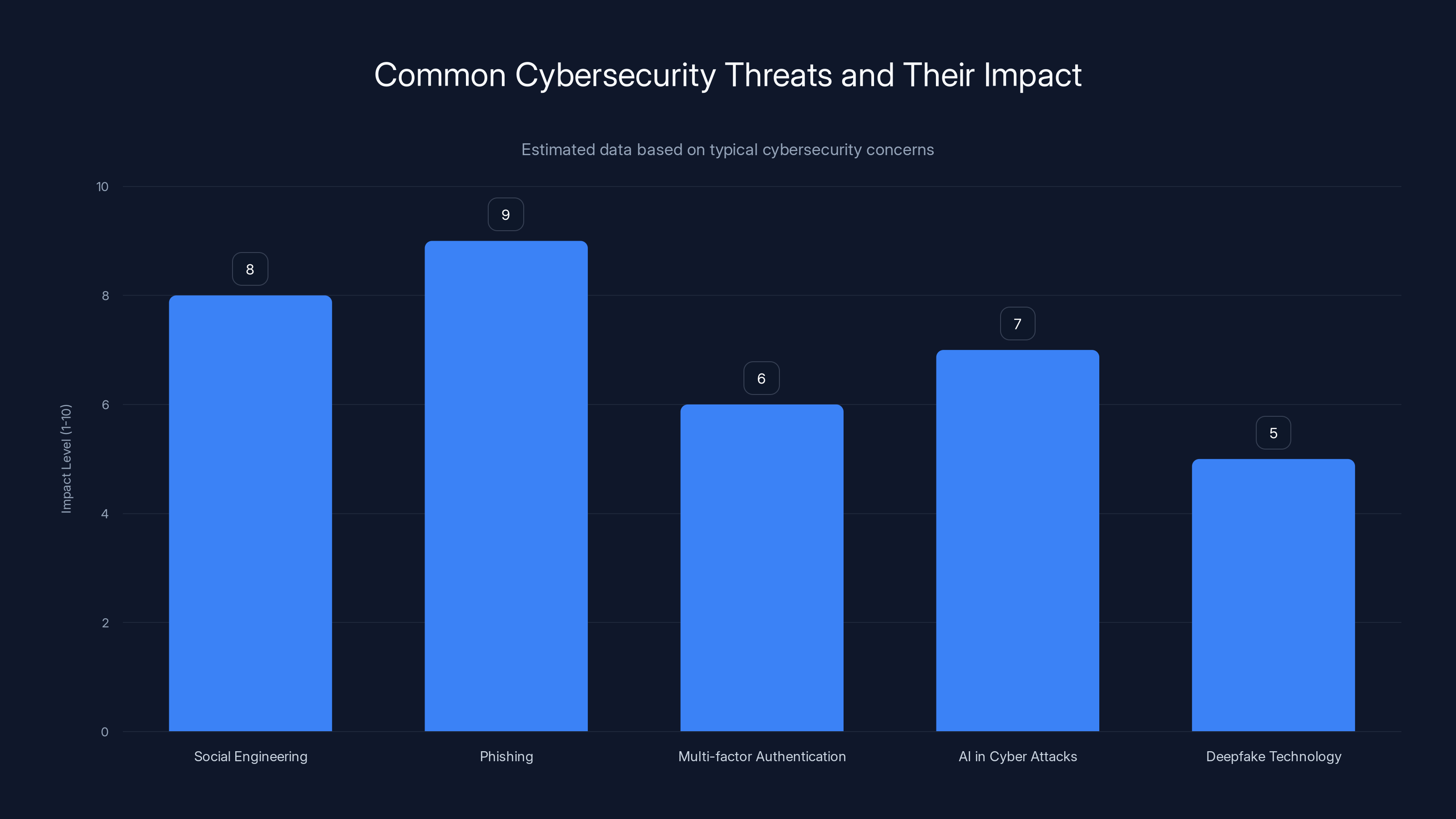
Phishing and social engineering attacks are estimated to have the highest impact levels, highlighting the need for robust security measures. Estimated data.
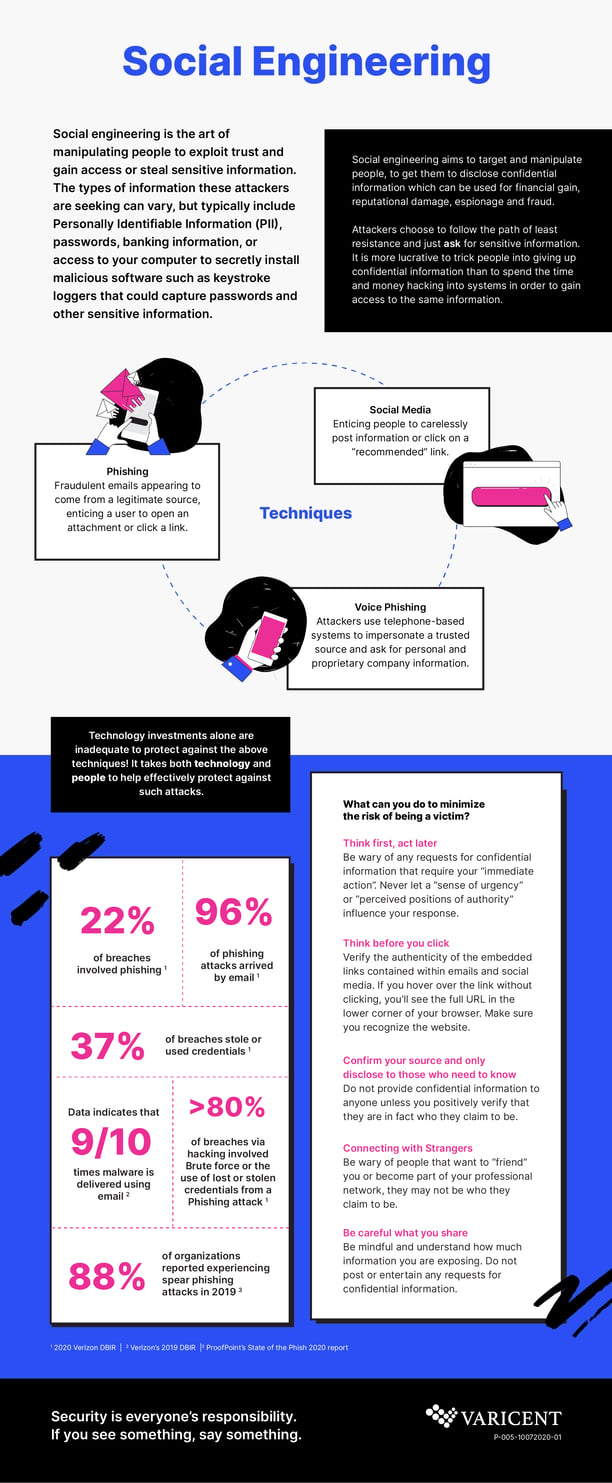
The Role of Social Engineering
Social engineering is at the heart of these attacks. By exploiting human psychology, attackers manipulate victims into divulging confidential information. Techniques include impersonation, urgency, and creating a false sense of trust.
Impersonation
Attackers often impersonate high-ranking executives or trusted colleagues. By leveraging details from social media and professional networks, they can make their impersonation highly convincing, as discussed in Princeton Perspectives.
Urgency and Pressure
Creating a sense of urgency is a common tactic. Attackers may claim that the requested information is needed immediately to prevent a business disaster, pushing the target to act without verifying the request's legitimacy, as outlined by Bain & Company's insights.
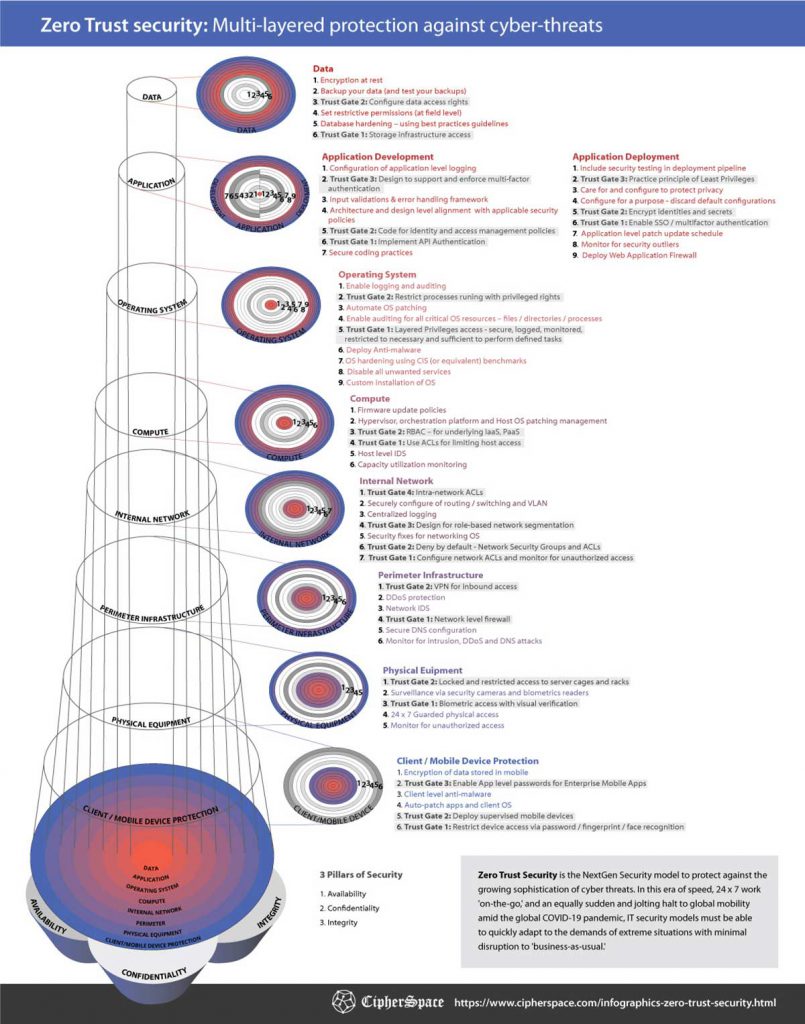
Implementing Robust Security Measures
Protecting against such sophisticated attacks requires a multi-layered security approach. Here are some best practices:
Education and Awareness
Training employees to recognize phishing attempts and social engineering tactics is crucial. Regularly updated training sessions can keep staff informed about the latest threats, as recommended by Microsoft's security blog.
Strong Authentication
Implementing two-factor authentication (2FA) can significantly reduce the risk of unauthorized access. Even if attackers obtain login credentials, 2FA provides an additional layer of security, as detailed in Palo Alto Networks' report.
Secure Communication Channels
Using encrypted communication tools can prevent unauthorized interception of sensitive information. Ensure that video conferencing platforms are configured securely, with password protection and waiting rooms enabled, as advised by Penn State News.
Regular Security Audits
Conducting regular security audits can help identify vulnerabilities before attackers exploit them. These audits should include penetration testing and a review of access controls, as suggested by WILX News.

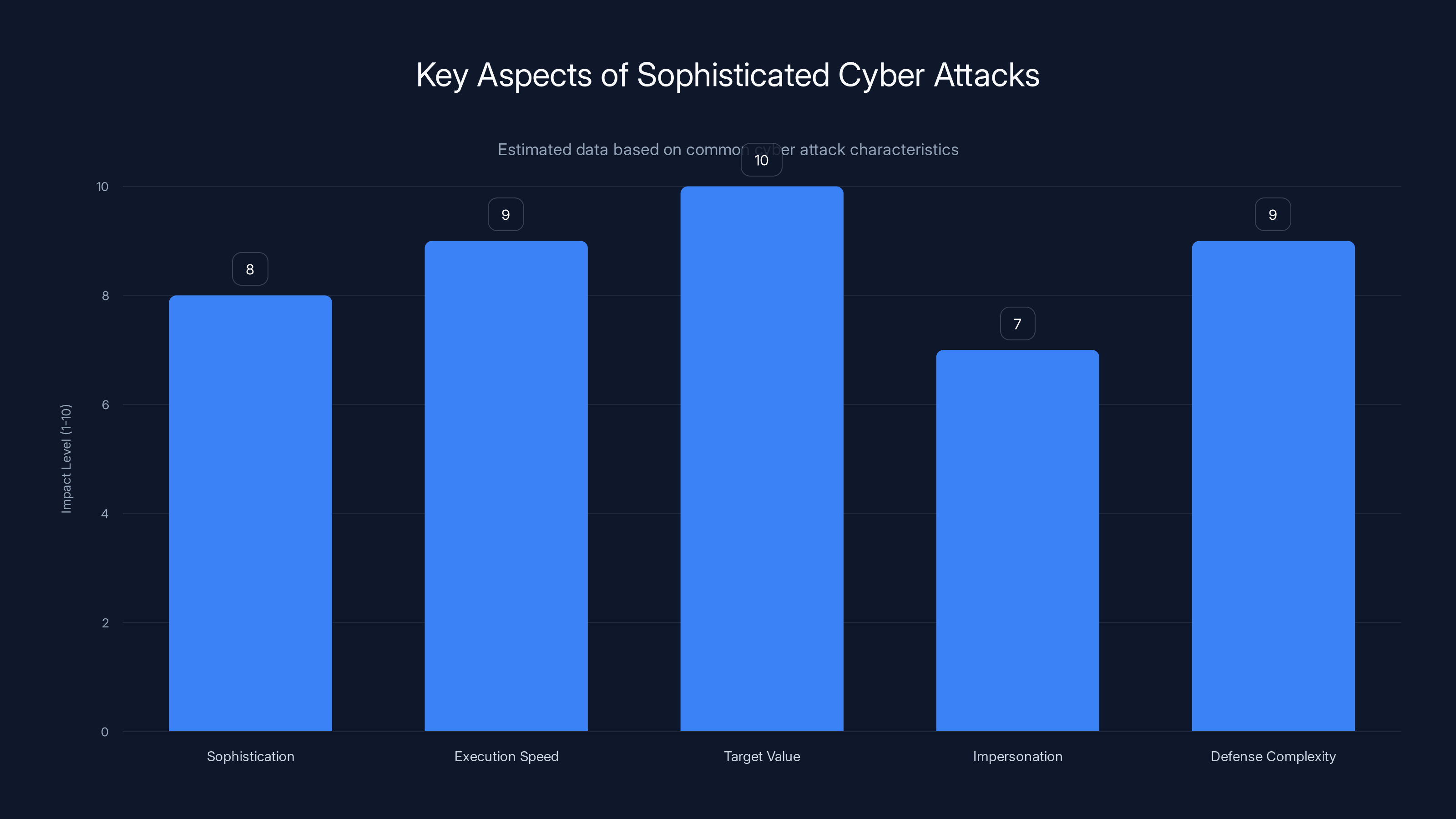
Estimated data shows that cryptocurrency executives face high-stakes threats with rapid execution and complex defense needs.
Real-World Implications for Cryptocurrency Firms
Cryptocurrency executives are particularly attractive targets due to the high value and volatility of digital assets. A successful attack can lead to significant financial losses and damage to reputation, as emphasized by TRM Labs.
Case Study: The 2025 Crypto Heist
In a recent incident, a prominent cryptocurrency exchange fell victim to a similar attack. The attackers used a fake Zoom meeting to gain access to the CEO's account credentials. Within minutes, they transferred millions in cryptocurrency to an untraceable wallet, as reported by BankInfoSecurity.
Lessons Learned
The exchange's failure to implement multi-factor authentication and inadequate employee training were key factors in the breach. Following the incident, the company overhauled its security protocols, emphasizing the importance of continuous education and robust authentication, as noted in Cyfirma's report.
Emerging Trends and Future Threats
As technology evolves, so do the tactics of cybercriminals. Here are some trends to watch:
Deepfake Technology
Deepfakes, which use AI to create realistic but fake videos, could be used to enhance impersonation attacks. This technology poses a significant threat as it becomes more accessible, as discussed in Wired.
AI-Driven Attacks
Cybercriminals are increasingly using AI to identify vulnerabilities and automate attacks. AI can analyze large data sets to find weaknesses faster than traditional methods, as highlighted by Palo Alto Networks.

Preparing for the Future
To stay ahead of these threats, organizations must adopt a proactive security stance. This involves:
Continuous Monitoring
Implementing real-time monitoring tools can help detect suspicious activity early. Anomaly detection systems can alert security teams to potential breaches before they occur, as advised by Bain & Company.
Collaboration and Information Sharing
Sharing threat intelligence with industry peers can provide valuable insights into emerging threats. Organizations should participate in threat intelligence sharing platforms to stay informed, as recommended by Security.com.
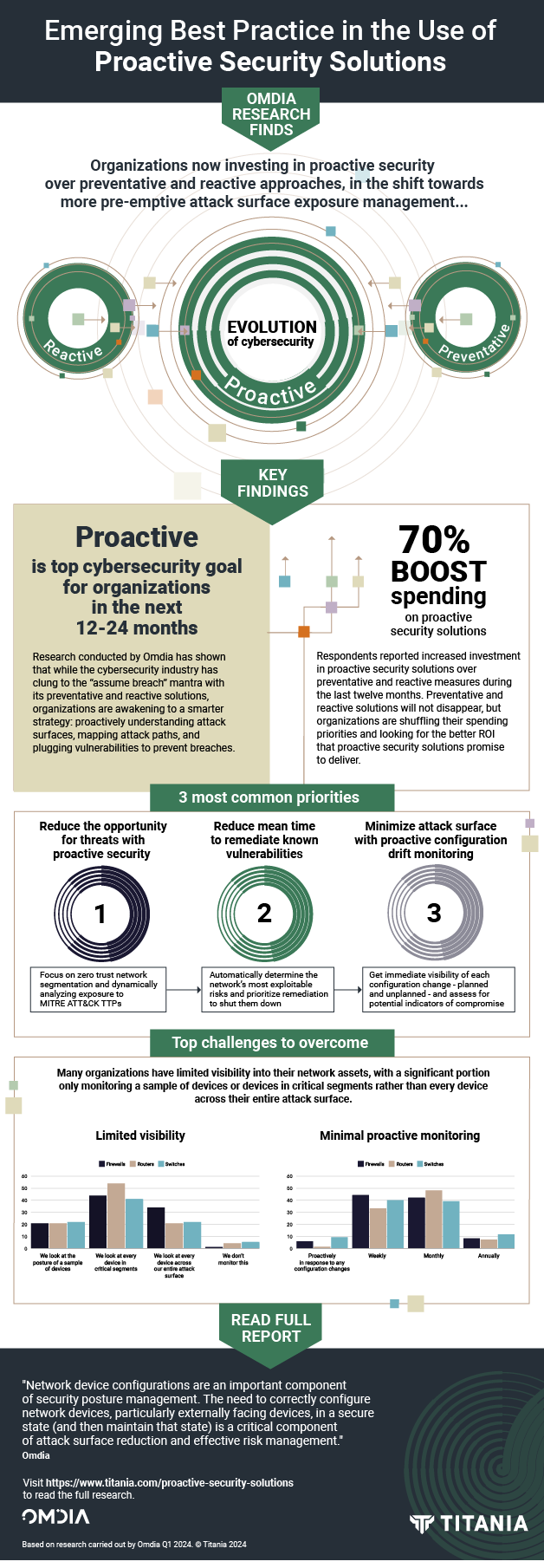
Conclusion: Strengthening Your Cyber Defense
The North Korea-linked campaign is a stark reminder of the need for robust cybersecurity measures. By understanding the anatomy of these attacks and implementing best practices, organizations can protect themselves against even the most sophisticated threats. Investing in employee education, strong authentication, and continuous monitoring are essential steps in building a resilient defense against cybercrime, as emphasized by Microsoft.
FAQ
What is a social engineering attack?
A social engineering attack involves manipulating individuals into divulging confidential information through psychological tricks. These attacks rely on human interaction rather than technical vulnerabilities, as explained by MSU Denver.
How can organizations protect against fake Zoom meeting attacks?
Organizations can protect themselves by verifying the authenticity of meeting invitations, implementing two-factor authentication, and training employees to recognize phishing attempts, as advised by TechCrunch.
What are the signs of a phishing email?
Phishing emails often contain urgent requests, unfamiliar sender addresses, or links to suspicious websites. They may also have spelling or grammar errors that can indicate their illegitimacy, as noted by Bain & Company.
How does multi-factor authentication enhance security?
Multi-factor authentication requires users to provide two or more verification factors to gain access, making it more difficult for attackers to gain unauthorized entry, as detailed by Palo Alto Networks.
What role does AI play in modern cyber attacks?
AI can be used by attackers to automate the identification of vulnerabilities and execute attacks. However, it can also be used defensively to detect and respond to threats more quickly, as highlighted by Wired.
How can organizations stay informed about emerging cyber threats?
Organizations can stay informed by participating in threat intelligence sharing platforms, attending industry conferences, and subscribing to cybersecurity news outlets, as recommended by Security.com.
What are the consequences of a successful cyber attack on a cryptocurrency firm?
A successful attack can result in significant financial losses, reputational damage, and loss of customer trust. It may also lead to regulatory scrutiny and legal consequences, as emphasized by TRM Labs.
How can deepfake technology be used in cyber attacks?
Deepfake technology can be used to create realistic but fake videos, enhancing impersonation attacks by making them more convincing and harder to detect, as discussed in Wired.

Key Takeaways
- Sophisticated cyber attacks can occur in under five minutes, highlighting the need for rapid detection and response, as noted by Security.com.
- Social engineering remains a potent tool for attackers, exploiting human psychology to gain access to sensitive information, as explained by MSU Denver.
- Cryptocurrency firms are high-value targets due to the potential for financial gain and the high stakes involved, as emphasized by TRM Labs.
- Deepfake technology poses a significant future threat, enhancing impersonation attacks with realistic fake videos, as discussed in Wired.
- Implementing multi-factor authentication and continuous monitoring are critical components of a robust cyber defense strategy, as detailed by Palo Alto Networks.
Related Articles
- Inside the New Cyber Scam: How Hackers Exploit Microsoft Teams to Steal Your Data [2025]
- Understanding and Mitigating Phishing Scams: Lessons from the Robinhood Incident [2025]
- Understanding Cybersecurity Threats in the Medical Sector: Lessons from Recent Breaches [2025]
- Keeping AI Agents in Check: Preventing Unauthorized Use of Your Credit Cards [2025]
- Understanding the Threat: Attack of the Killer Script Kiddies [2025]
- Understanding the Itron Cyberattack: Impacts and Lessons [2025]
!['The Attacker Completed in Under Five Minutes': Unpacking the North Korea-Linked Crypto Attack [2025]](https://tryrunable.com/blog/the-attacker-completed-in-under-five-minutes-unpacking-the-n/image-1-1777404866747.jpg)



