The Hidden Risks of Exposed API Keys: How to Secure Your Cloud Systems [2025]
In a digital world driven by interconnected systems, API keys act like the keys to your kingdom. They're the secret tokens that allow applications to communicate with each other, granting access to data and services. But what happens when these keys are inadvertently exposed? A recent study scanned 10 million websites and found thousands of these keys publicly accessible, quietly granting access to cloud systems and critical infrastructure. Let's dive into the implications, real-world examples, and strategies for securing your API keys.
TL; DR
- Exposed API keys: Thousands found on public websites, posing serious security risks.
- JavaScript files: A primary source of credential exposure, often overlooked by developers.
- Impact: Unauthorized access can lead to data breaches, financial loss, and infrastructure damage.
- Best practices: Encrypt keys, use environment variables, and implement access controls.
- Future trends: Increased focus on API security with the rise of complex cloud environments.
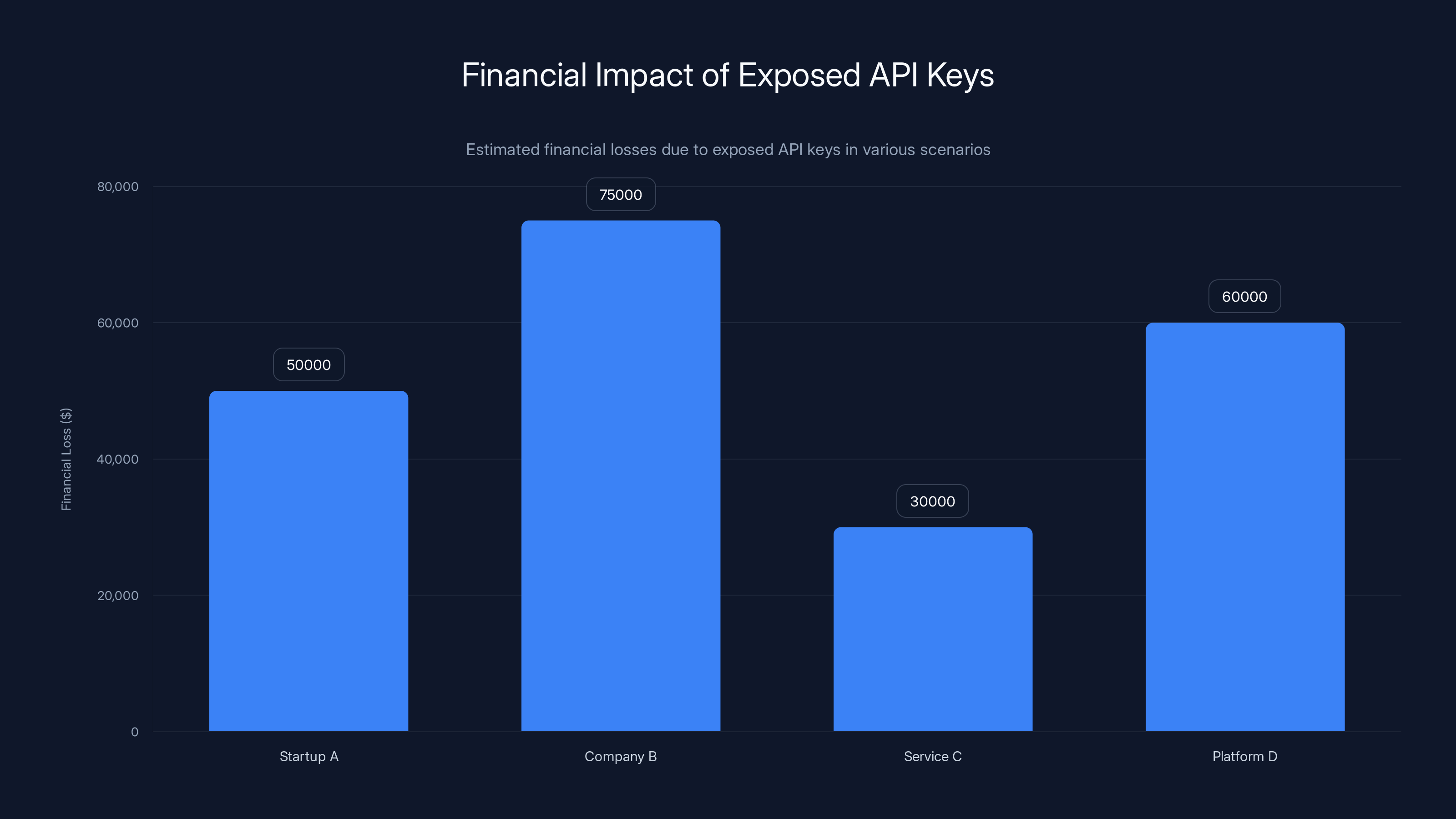
Exposed API keys can lead to significant financial losses, as illustrated by a startup facing a $50,000 bill. (Estimated data)
The Importance of API Keys
API keys are unique identifiers used to authenticate requests from applications accessing APIs. They are crucial for maintaining secure communication between systems, controlling access, and monitoring usage.
Example Use Case: Imagine a weather application fetching data from a service provider. The API key ensures that only authorized applications can access the data and prevents unauthorized use.
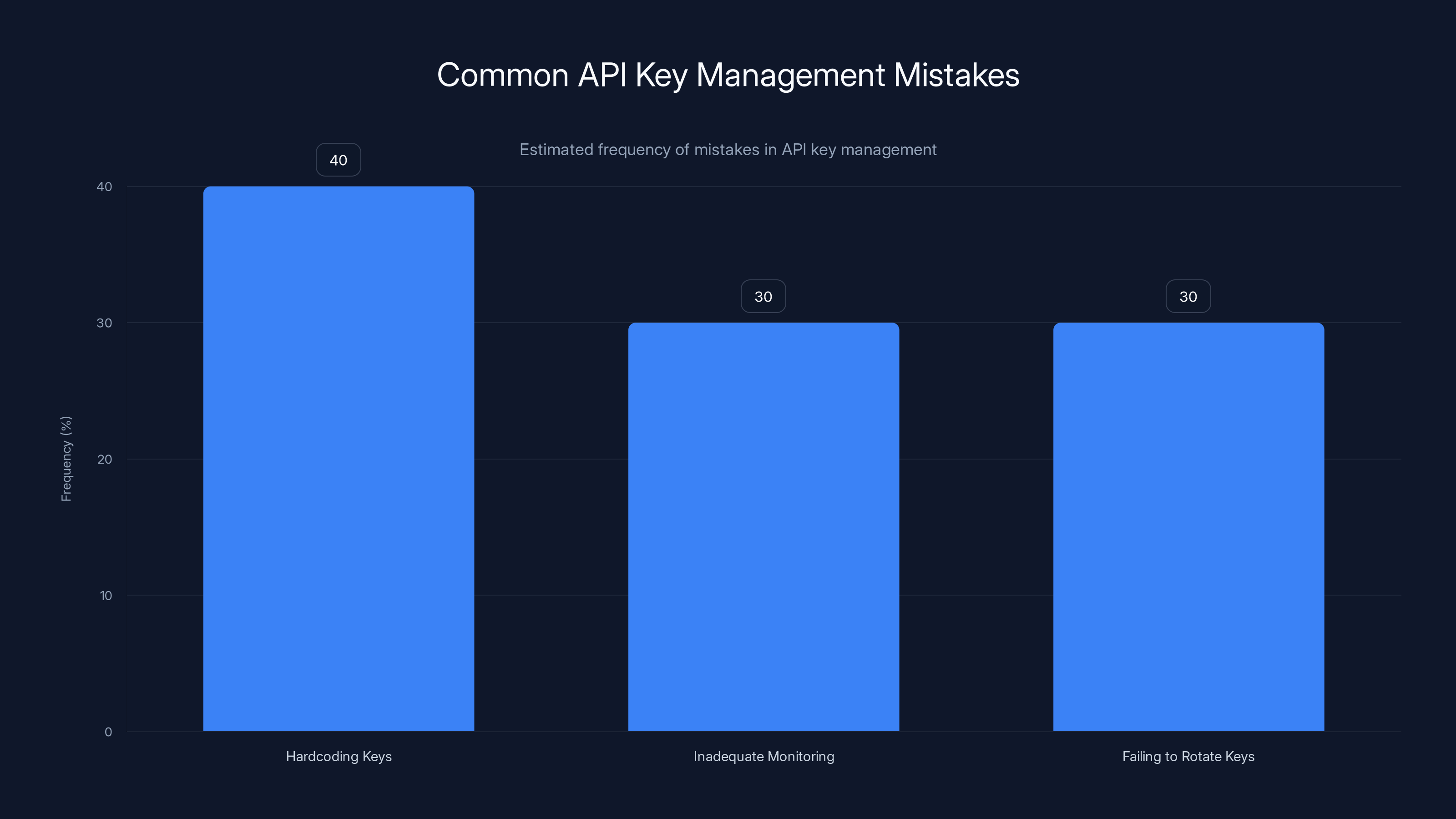
Hardcoding keys is the most common mistake in API key management, followed closely by inadequate monitoring and failing to rotate keys. Estimated data.
The Scope of Exposure
A recent investigation revealed that thousands of API keys are exposed across various platforms, from GitHub repositories to public websites. The most common culprits? JavaScript files. These files are often overlooked during security audits, leading to significant vulnerabilities.
Common Pitfalls:
- Hardcoding API keys in client-side code.
- Storing keys in public repositories.
- Failing to rotate keys regularly.
Real-World Impact of Exposed API Keys
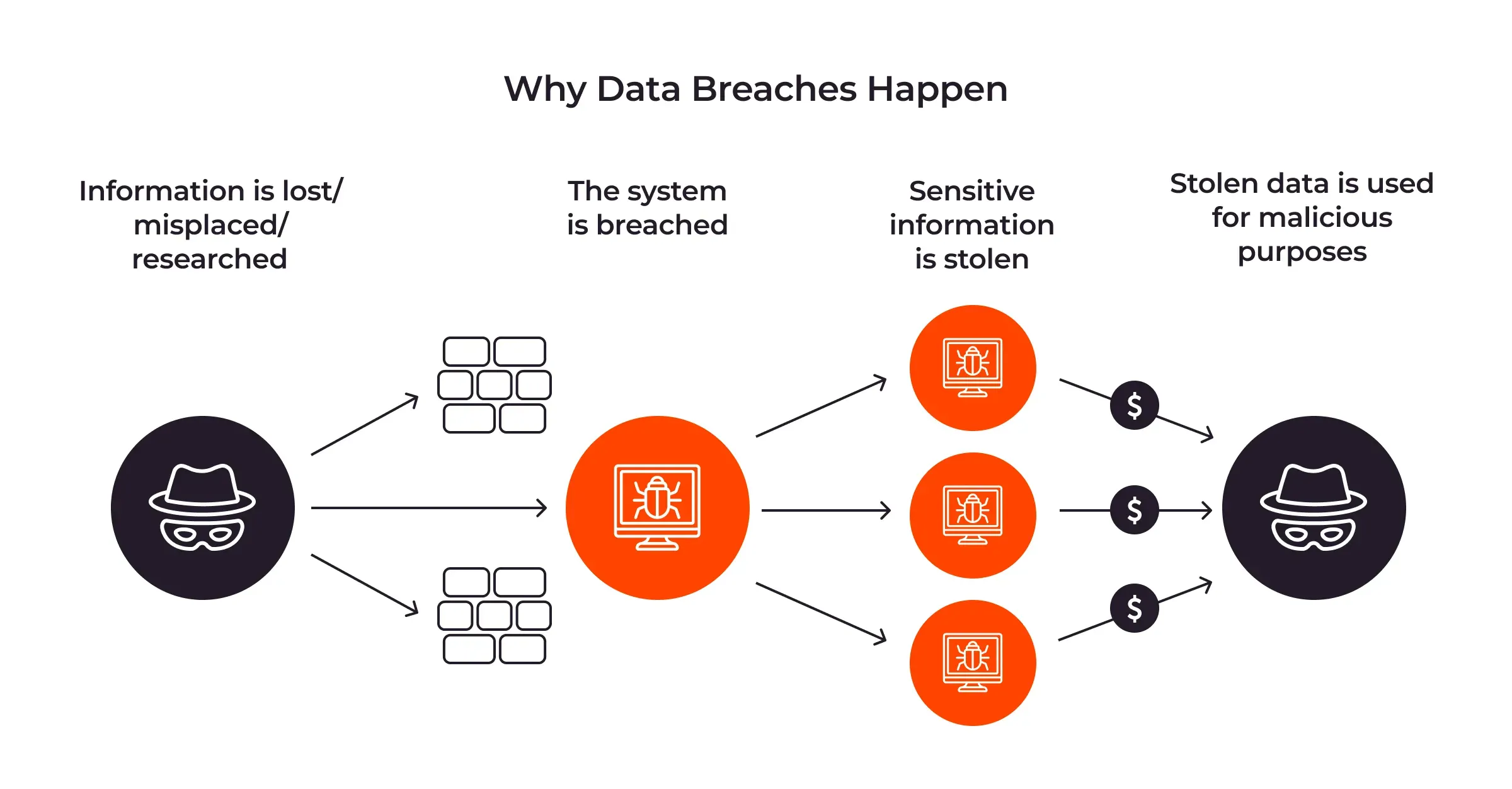
Data Breaches
Exposed API keys can lead to unauthorized data access, resulting in breaches. For instance, if a financial app's API key is compromised, cybercriminals could access sensitive user data, leading to identity theft or financial fraud.
Financial Losses
Unauthorized use of API keys can result in unexpected costs. Imagine an attacker using your API key to make thousands of requests to a paid service, racking up enormous bills.
Case Study: A startup faced a $50,000 bill after their cloud service API key was exposed, allowing malicious actors to exploit their resources.
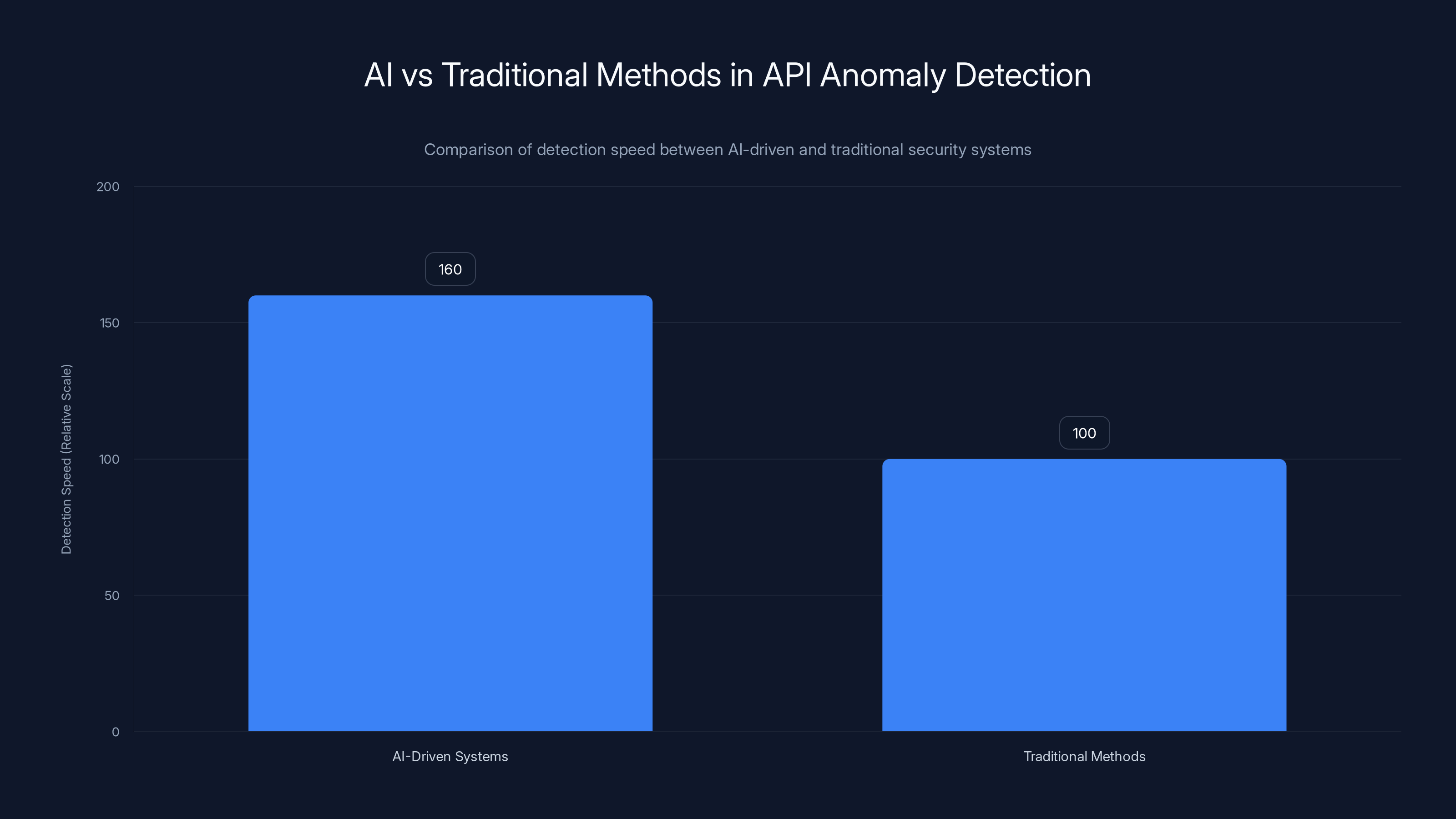
AI-driven security systems can detect anomalies in API usage patterns 60% faster than traditional methods, significantly enhancing security response times.
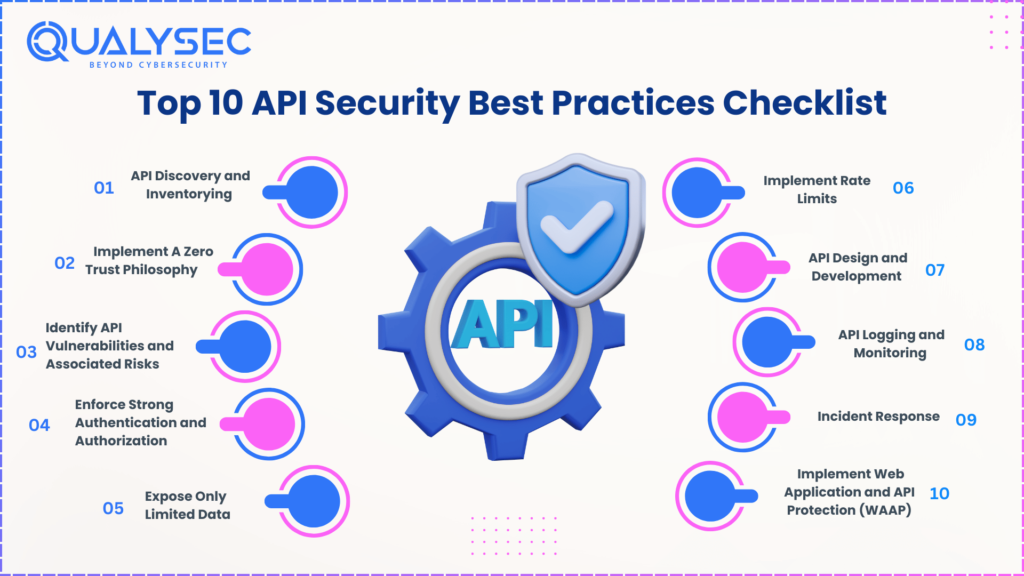
Best Practices for Securing API Keys
1. Encrypt API Keys
Never store API keys in plaintext. Use encryption to protect them, ensuring that even if they are exposed, they're useless without the decryption key.
Implementation Guide:
- Use a secure encryption algorithm like AES-256.
- Store encryption keys in a secure vault, separate from the API keys.
2. Use Environment Variables
Store API keys in environment variables rather than in your codebase. This separates your keys from your application's source code and adds an additional layer of security.
bash# Example of setting an environment variable for an API key
export WEATHER_API_KEY="your_api_key_here"
3. Implement Access Controls
API keys should be associated with specific permissions. Use role-based access control (RBAC) to ensure that keys can only access the resources they need.
Quick Tip: Regularly audit your API keys and permissions to ensure compliance with security policies.
Common Mistakes and How to Avoid Them
Mistake 1: Hardcoding Keys
Solution: Use configuration files or environment variables to manage keys. This reduces the risk of accidental exposure.
Mistake 2: Inadequate Monitoring
Solution: Implement logging and monitoring to track API key usage and detect anomalies.
json{
"api_key_usage": {
"total_requests": 1200,
"anomalous_activity": true
}
}
Mistake 3: Failing to Rotate Keys
Solution: Regularly rotate API keys to limit the impact of exposure. Automate the process where possible to ensure consistency.
Future Trends in API Security
Automation and AI
The use of AI to monitor API key usage and detect anomalies is on the rise. Machine learning algorithms can analyze patterns and flag suspicious activities, enhancing security.
Did You Know: AI-driven security systems can detect anomalies in API usage patterns 60% faster than traditional methods.
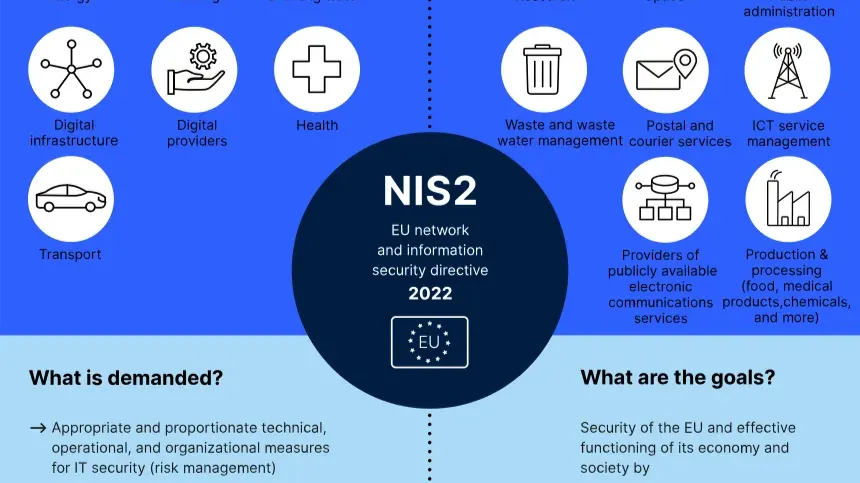
Zero Trust Architecture
As cloud environments become more complex, adopting a Zero Trust approach to API security is crucial. This means assuming that every API request is a potential threat and verifying everything.
Key Features:
- Continuous authentication and authorization.
- Strict access controls and network segmentation.

Recommendations for Developers
- Secure Storage: Use tools like AWS Secrets Manager or HashiCorp Vault to store API keys securely.
- Implement Rate Limiting: Protect your APIs from abuse by limiting the number of requests a key can make.
- Educate Your Team: Regular training on secure coding practices can prevent common mistakes.

Conclusion
Exposed API keys pose a significant threat to cloud systems and critical infrastructure. By understanding the risks and implementing best practices, you can protect your digital assets from unauthorized access. As technology evolves, staying informed about the latest security trends and tools is essential for maintaining robust API security.
FAQ
What are API keys?
API keys are unique identifiers used to authenticate requests between applications and APIs, ensuring secure communication and access control.
Why are API keys often exposed?
API keys are often exposed due to inadequate security practices, such as hardcoding keys in client-side code or storing them in public repositories.
How can I secure my API keys?
Secure your API keys by encrypting them, using environment variables, implementing access controls, and regularly rotating keys.
What is the impact of an exposed API key?
Exposed API keys can lead to unauthorized data access, financial losses, and damage to critical infrastructure.
What are some tools for managing API keys securely?
Tools like AWS Secrets Manager, HashiCorp Vault, and Azure Key Vault help manage API keys securely by providing encryption, access control, and audit logging.
How can AI help in API security?
AI can monitor API key usage, detect anomalies, and flag suspicious activities, enhancing security by providing real-time insights and alerts.
What is Zero Trust Architecture?
Zero Trust Architecture is a security model that assumes every API request is a potential threat, enforcing strict access controls and continuous authentication.
Key Takeaways
- Thousands of API keys exposed publicly, risking unauthorized access.
- JavaScript files frequently expose credentials, a common oversight.
- Encrypt API keys and use environment variables for secure storage.
- AI and machine learning enhance anomaly detection in API usage.
- Zero Trust Architecture is crucial for securing complex cloud environments.
Related Articles
- Safeguarding Older Apple Devices from DarkSword Attacks: A Comprehensive Guide [2025]
- Unveiling OpenClaw Security Risks You Must Know About [2025]
- Critical Flaw in OpenAI's Codex: Enterprise Security Risks and Solutions [2025]
- The Hidden Dangers of AI: What If Your AI Agent Is Working Against You? [2025]
- Inside the Anthropic Leak: Unpacking the Claude Code Source Code Exposure [2025]
- Tech Sovereignty: Why One Size Doesn’t Fit All [2025]
![The Hidden Risks of Exposed API Keys: How to Secure Your Cloud Systems [2025]](https://tryrunable.com/blog/the-hidden-risks-of-exposed-api-keys-how-to-secure-your-clou/image-1-1775075661075.jpg)



