Understanding the Complex Ties Between Ransomware Gangs and Government Infrastructures [2025]
Ransomware attacks have been a growing concern for years, and the recent conviction of Latvian hacker Deniss Zolotarjovs has brought to light the intricate connections between ransomware gangs and government infrastructures. This article delves deep into these connections, discusses the implications, and provides practical advice for organizations looking to bolster their cybersecurity measures.
TL; DR
- Ransomware gangs like Karakurt are linked with government entities, accessing classified databases to intimidate victims, as detailed in a TechCrunch report.
- Ransomware impact is significant, affecting critical services like 911 systems and exposing sensitive data, according to Government Technology.
- Cybersecurity measures should be enhanced to protect against sophisticated attacks, as emphasized by the Information Technology and Innovation Foundation.
- International collaboration is vital for combating ransomware threats, as highlighted by Europol's 2026 IOCTA report.
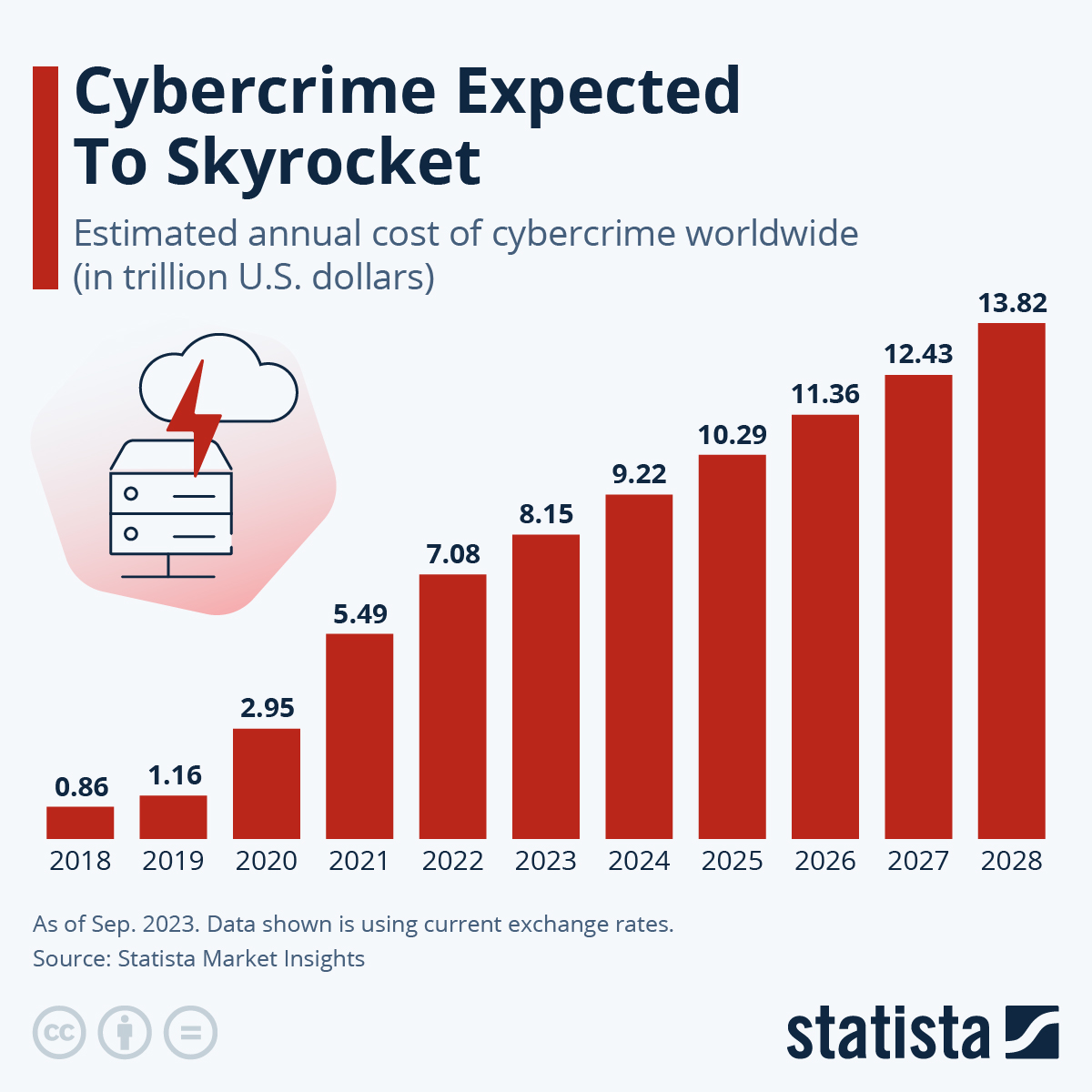
- Future trends indicate a rise in state-sponsored cybercrimes, as noted in the Cybersecurity Ventures report.
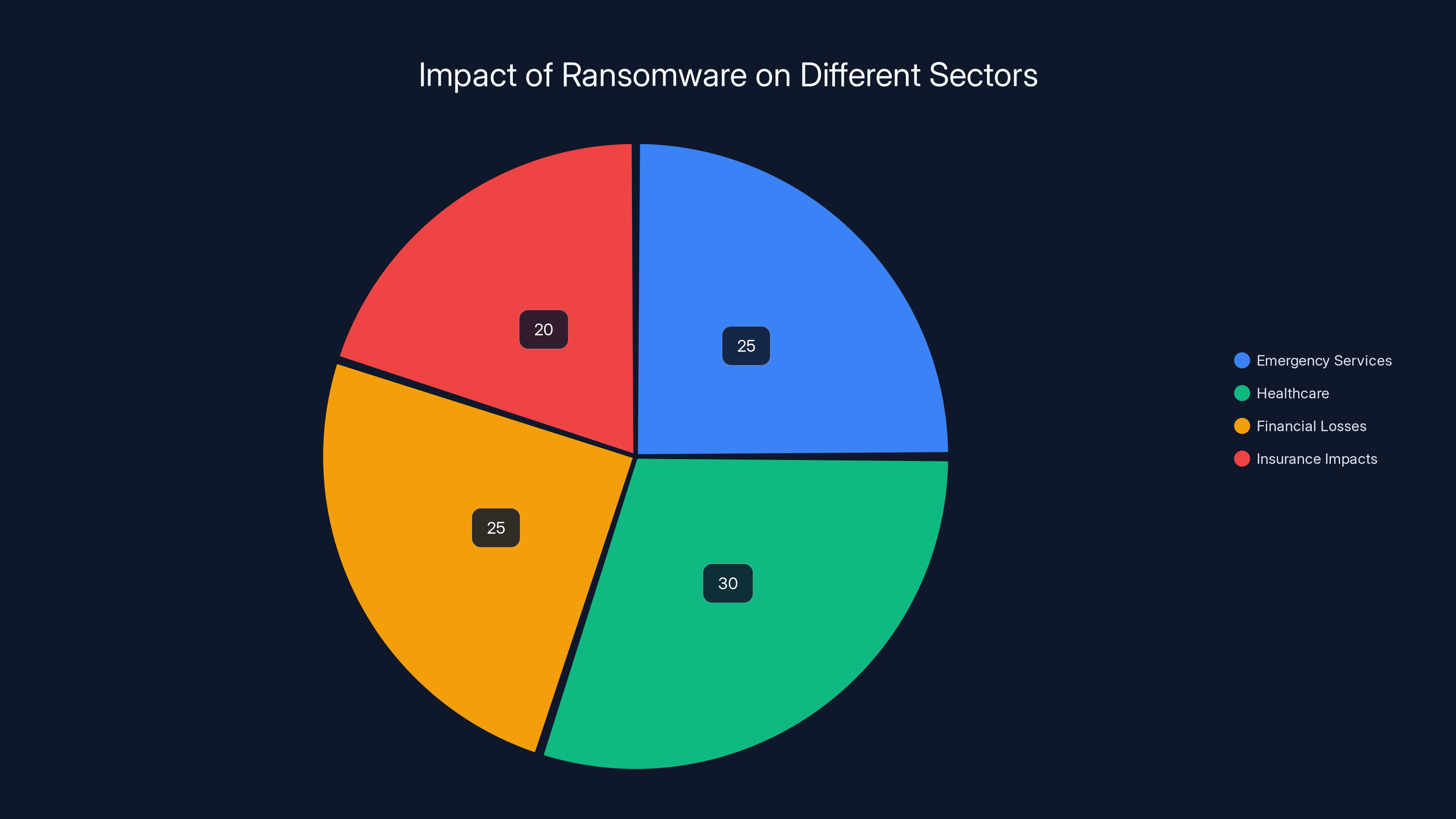
Estimated data shows that healthcare and emergency services are significantly impacted by ransomware, each accounting for around 25-30% of the total impact.
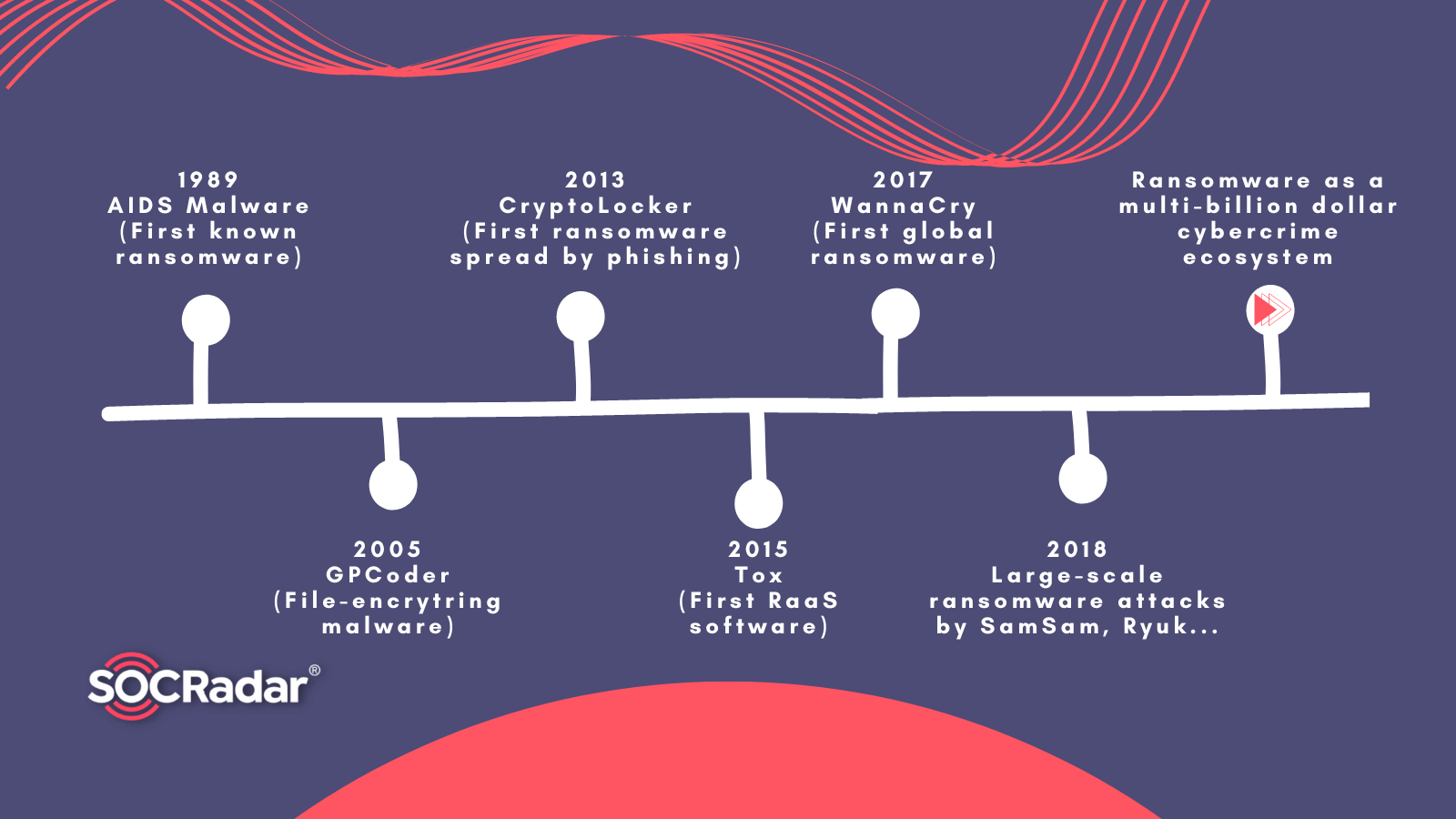
The Rise of Ransomware
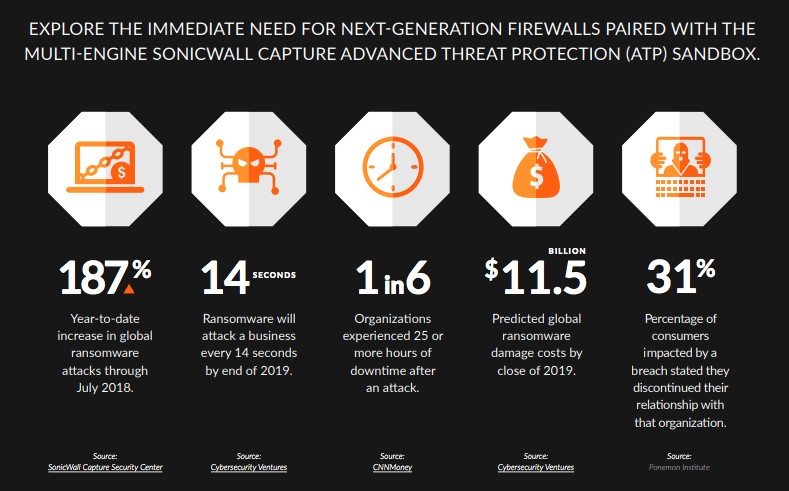
Ransomware attacks have evolved from simple encryption of data to complex operations involving extortion, data theft, and even partnerships with state actors. The sophistication of these attacks makes them a formidable threat to national security, as discussed in Industrial Cyber's report.
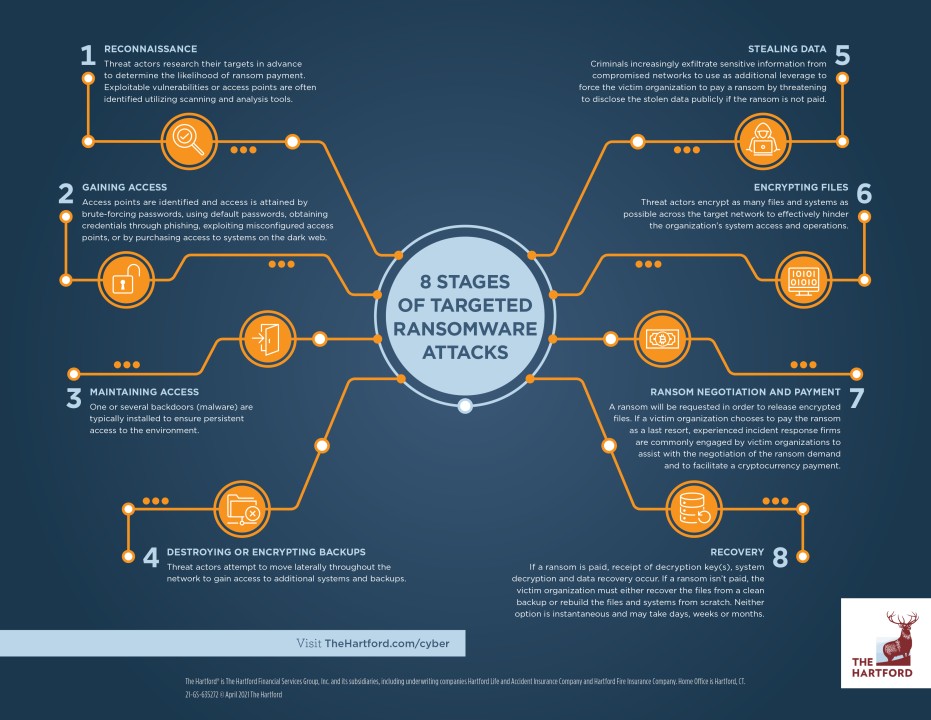
How Ransomware Works
At its core, ransomware encrypts the victim's data, rendering it inaccessible until a ransom is paid. However, modern ransomware gangs go beyond encryption.
- Data Theft: Before encrypting, attackers often exfiltrate sensitive data.
- Double Extortion: Threatening to release stolen data unless an additional ransom is paid.
- Targeted Attacks: Using spear-phishing and other methods to infiltrate specific organizations.

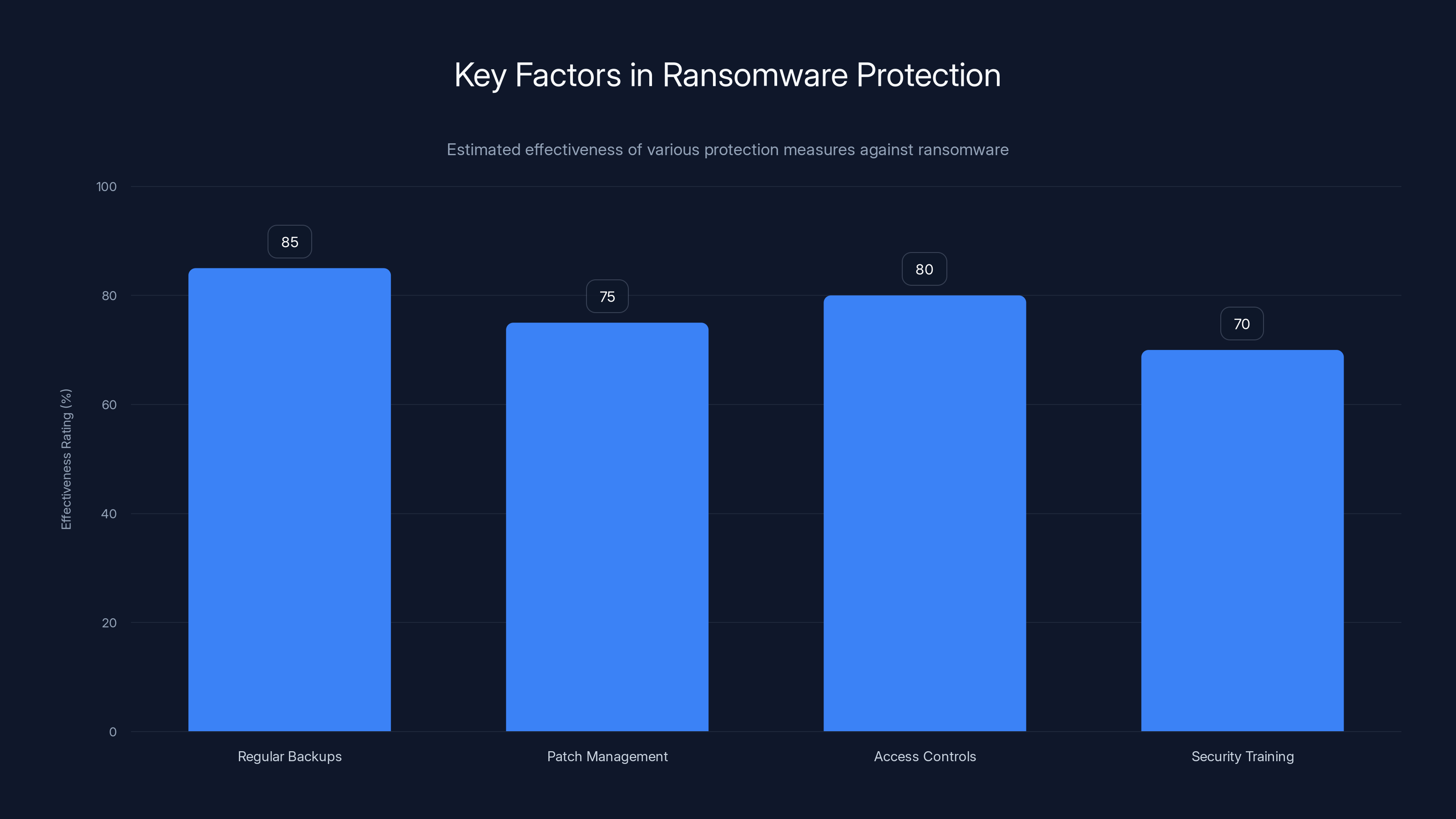
Regular backups are the most effective measure against ransomware, followed by access controls and patch management. Estimated data.
Case Study: Karakurt Ransomware Gang
The Karakurt gang, linked to Russian intelligence, showcases the sophisticated operations of modern ransomware groups, as reported by CyberScoop.
Tactics and Operations
Karakurt is known for its strategic approach:
- Government Connections: Allegedly accessing Russian government databases to apply pressure on victims, as detailed in TechCrunch.
- Targeting Critical Infrastructure: Attacks on emergency services and healthcare systems, as highlighted by HIPAA Journal.
- Psychological Warfare: Using information from government sources to intimidate victims.
The Role of Deniss Zolotarjovs
Deniss Zolotarjovs played a crucial role in the Karakurt gang, responsible for increasing pressure on victims.
- Escalation Techniques: Employing threats and leveraging stolen data to enforce compliance, as noted in Security Affairs.
- Coordination with Leaders: Collaborating with former leaders of the Akira and Conti gangs, as reported by SecurityWeek.

Technical Details of Ransomware Attacks
Understanding the technical aspects of ransomware can help organizations better prepare for potential threats.
Common Attack Vectors
- Phishing Emails: The most prevalent method for delivering ransomware payloads.
- Exploiting Vulnerabilities: Taking advantage of unpatched software and security gaps, as discussed in Microsoft's security blog.
- Remote Desktop Protocol (RDP) Attacks: Gaining unauthorized access to systems through RDP.
Best Practices for Prevention
To safeguard against ransomware attacks, organizations should implement the following measures:
- Regular Backups: Ensure data backups are frequent and stored securely.
- Patch Management: Keep all software and systems updated with the latest patches.
- Access Controls: Limit user access to essential systems and data.
- Security Awareness Training: Educate employees about phishing and other common threats.
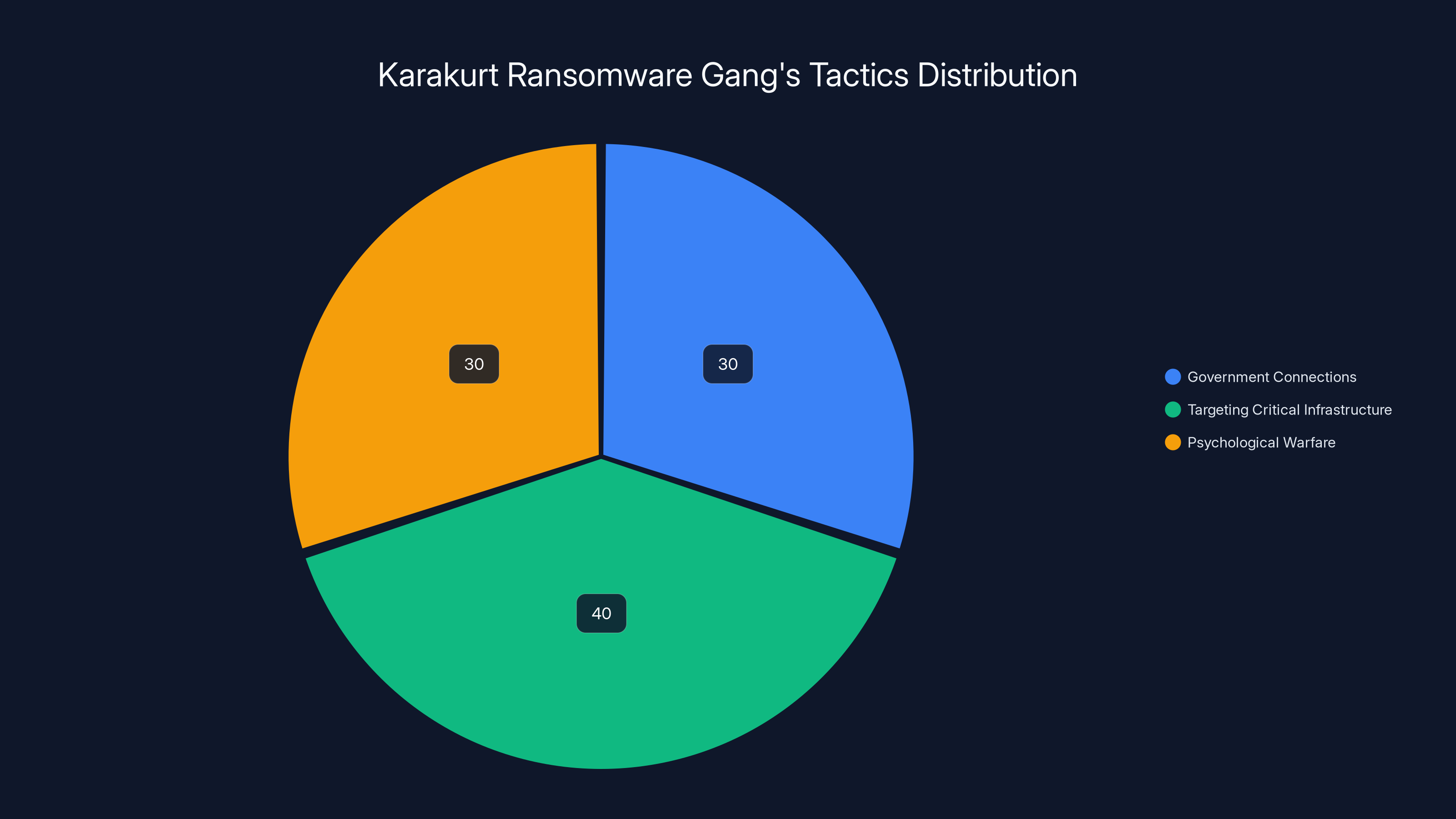
The Karakurt gang's operations are evenly split between government connections, targeting critical infrastructure, and psychological warfare. Estimated data.
The Impact of Ransomware on Society
Ransomware attacks have far-reaching implications, affecting not just the targeted organizations but society at large.
Disruption of Critical Services
- 911 Systems: Attacks can disrupt emergency services, putting lives at risk, as noted by Government Technology.
- Healthcare: Exposing patient data and disrupting medical services, as highlighted in the Cybersecurity Ventures report.
Economic Consequences
- Financial Losses: Organizations face significant costs in ransom payments, recovery, and reputational damage.
- Insurance Impacts: Increased premiums and coverage limitations for cyber insurance.
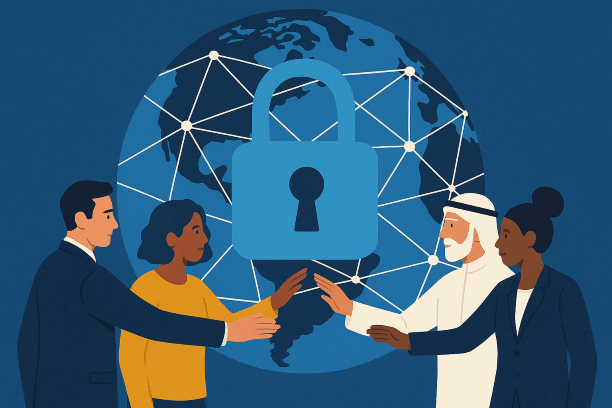
International Collaboration in Cybersecurity
Addressing the ransomware threat requires a coordinated international response.
Key Strategies
- Information Sharing: Cross-border collaboration to share threat intelligence, as emphasized by Europol.
- Joint Task Forces: Forming alliances to investigate and disrupt ransomware operations.
- Legal Frameworks: Establishing international laws and regulations to prosecute cybercriminals.
The Future of Cybercrime
As ransomware tactics evolve, the future landscape of cybercrime will likely see increased complexity and state involvement.
Predictions and Trends
- State-Sponsored Cyber Attacks: More nations may engage in cyber warfare, using ransomware as a tool, as predicted by Cybersecurity Ventures.
- AI-Driven Cybercrime: The use of AI to automate and enhance ransomware attacks.
- Ransomware as a Service (Raa S): Lowering entry barriers for cybercriminals.
Conclusion
The conviction of Deniss Zolotarjovs highlights the complex relationship between ransomware gangs and government infrastructures. As cyber threats continue to evolve, organizations must enhance their security measures and collaborate internationally to combat this growing menace.

FAQ
What is ransomware?
Ransomware is a type of malware that encrypts a victim's data, demanding payment for the decryption key.
How do ransomware gangs operate?
They use phishing, exploit vulnerabilities, and leverage stolen data to pressure victims into paying ransoms.
What are the consequences of ransomware attacks?
These attacks can disrupt critical services, expose sensitive data, and lead to significant financial losses.
How can organizations protect against ransomware?
Implement regular backups, patch management, access controls, and security awareness training.
What role do governments play in ransomware attacks?
Some ransomware gangs have ties to state actors, using government resources to enhance their operations.
What does the future hold for ransomware?
Increased state involvement, AI-driven attacks, and the rise of Ransomware as a Service (Raa S).
Why is international collaboration important?
It enables information sharing, joint investigations, and the establishment of legal frameworks to combat cybercrime.

Key Takeaways
- Ransomware gangs like Karakurt are linked with government entities.
- Ransomware impact is significant, affecting critical services.
- Cybersecurity measures should be enhanced to protect against sophisticated attacks.
- International collaboration is vital for combating ransomware threats.
- Future trends indicate a rise in state-sponsored cybercrimes.
Related Articles
- The Rise of AI in Cybercrime: Understanding the Impact and Challenges [2025]
- Google's $1.5 Million Bounty for Security Bugs in Android and Chrome [2025]
- Understanding the Vimeo Data Breach and Protecting Your Digital Footprint [2025]
- The Unseen Threat: AI Agent Backdoors in Open-Source Repositories [2025]
- Understanding Supply-Chain Attacks: The Daemon Tools Incident and Its Implications [2025]
- Robots on the Rails: How Automation is Shaping Public Transport [2025]
![Understanding the Complex Ties Between Ransomware Gangs and Government Infrastructures [2025]](https://tryrunable.com/blog/understanding-the-complex-ties-between-ransomware-gangs-and-/image-1-1778092436126.jpg)



