Honeywell CCTV Camera Vulnerability: Complete Security Guide [2025]
You installed those Honeywell CCTV cameras thinking you had surveillance locked down. But here's what keeps security teams up at night: a single missing line of code can unravel the whole thing.
That's exactly what happened with CVE-2026-1670, a critical vulnerability affecting multiple Honeywell CCTV camera models. An unauthenticated attacker doesn't need your password. They don't need to crack anything. They just need network access to your camera and boom—they're in, watching your feeds, changing your recovery email, and owning your account completely.
Let's be real. This isn't some theoretical researcher finding a flaw in a lab. The US Cybersecurity and Infrastructure Security Agency (CISA) is actively warning organizations to patch immediately. If you're running industrial operations, managing warehouses, or securing critical infrastructure, this matters to you today.
We're going to walk through exactly what this vulnerability is, why it's so dangerous, which cameras are affected, how to fix it, and what you need to do right now to protect your network. By the end, you'll understand the real risk and have a concrete action plan.
TL; DR
- CVE-2026-1670 affects Honeywell CCTV cameras with a critical 9.8/10 severity score due to missing authentication on critical functions
- Unauthenticated attackers can access camera feeds and take over accounts without knowing passwords
- Multiple models are vulnerable including I-HIB2PI-UL, MVO-3, and WDR_2MP variants commonly used in business and industrial settings
- Patches are available now and CISA urges immediate deployment before attackers actively scan for vulnerable systems
- Network isolation is critical until patched, including firewalls, VPNs, and minimizing direct internet exposure
- Bottom Line: Treat this as urgent. Not optional.

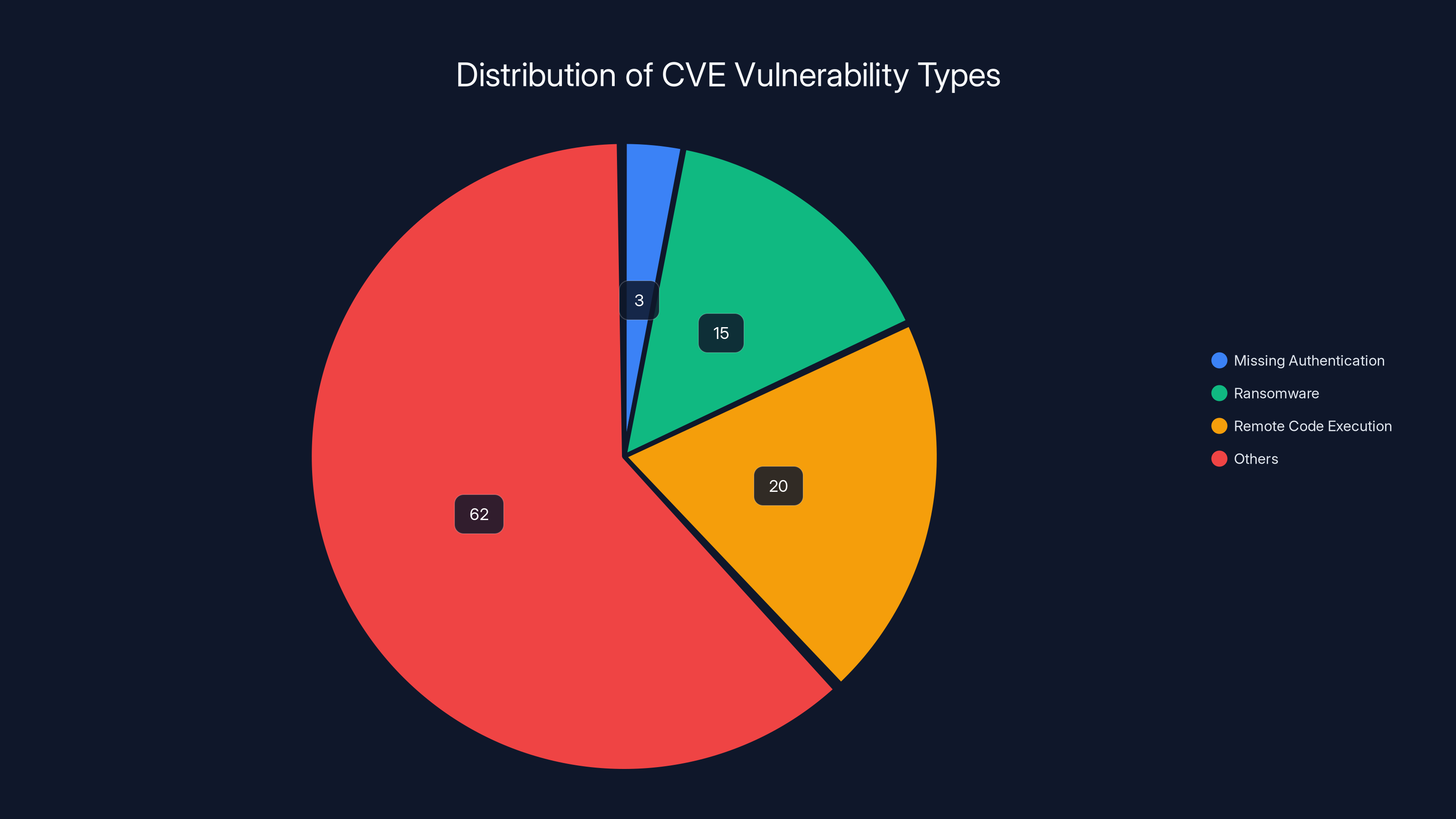
Missing authentication vulnerabilities account for approximately 2-3% of all CVEs, but are among the top 10 most dangerous due to ease of exploitation. Estimated data.
What Is CVE-2026-1670 and Why Should You Care?
The vulnerability itself is deceptively simple. Honeywell's CCTV camera firmware is missing authentication checks on certain critical functions. That means when an attacker sends a request to change settings, access video feeds, or modify account credentials, the camera doesn't verify that the person making the request is actually authorized to do so.
Authentication is supposed to be the bouncer at the club. It checks your ID, verifies you're on the list, and then lets you in. Without it, anyone can walk in the front door.
What makes CVE-2026-1670 especially nasty is the scope of damage. We're not talking about aesthetic issues like disabling notifications. An attacker can change the recovery email address associated with your camera account. This is a keystroke away from full account takeover. Once they control the recovery email, they can reset the actual password and lock you out of your own surveillance system.
The severity score is 9.8 out of 10. That's critical. CISA doesn't throw around critical ratings casually. This sits in the same category as ransomware vulnerabilities and remote code execution flaws.
Here's what makes this particular flaw dangerous in a real-world context. Honeywell's customer base includes industrial operators, critical infrastructure providers, government agencies (they offer NDAA-compliant models), warehouses, and medium-sized businesses. These organizations often deploy cameras as part of larger security ecosystems. If an attacker compromises the camera system, they gain reconnaissance intel on physical security, staffing patterns, entry/exit points, and security protocols.
In industrial facilities, this is surveillance gold. An attacker can monitor guard rotations, identify when facilities are understaffed, watch for pattern breaks in operations, and plan physical security breaches.
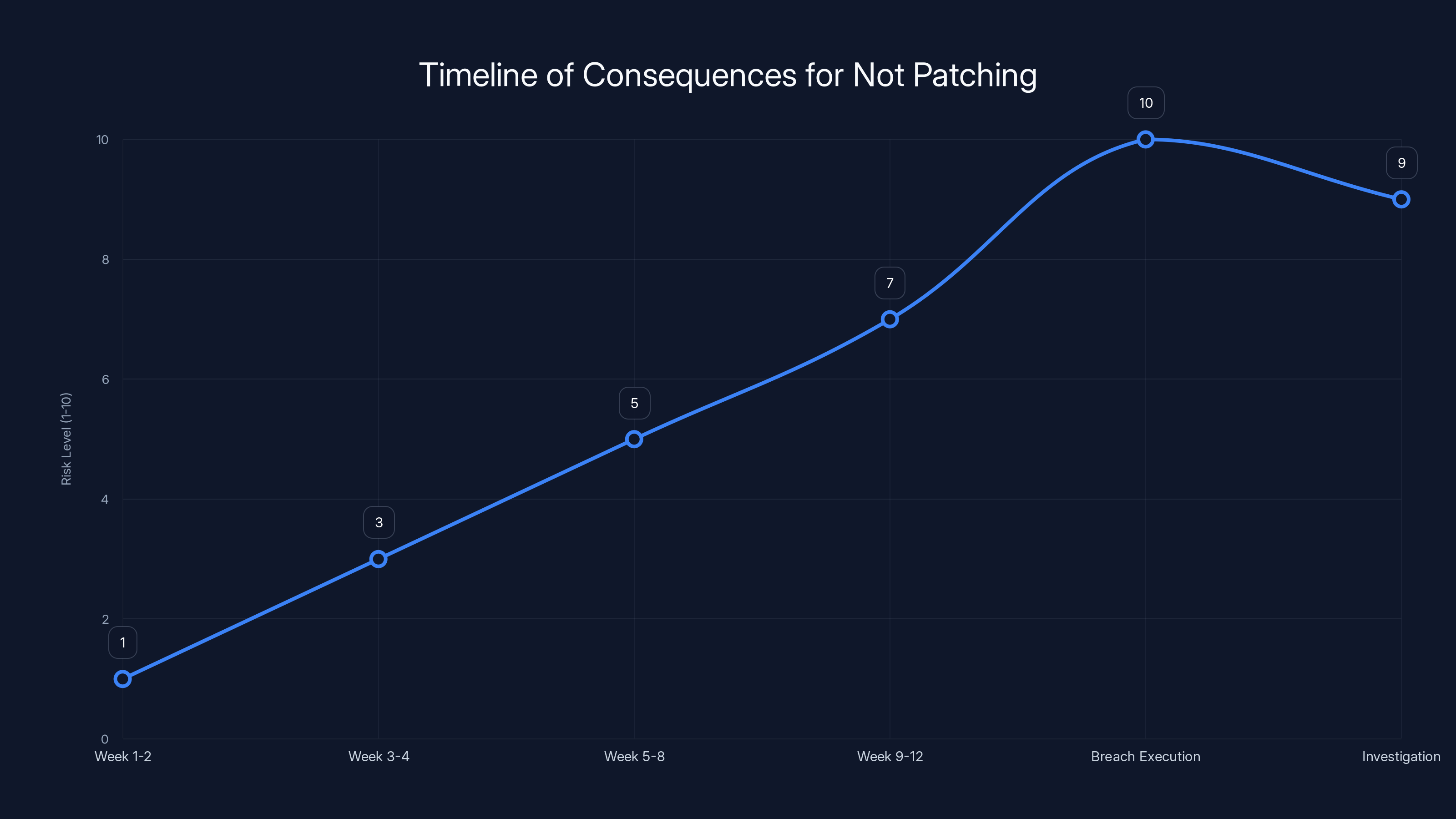
The risk level increases significantly over time if vulnerabilities are not patched, culminating in a breach. Estimated data based on typical progression.
The Vulnerability Timeline: When Did This Start?
There's no public disclosure of exactly when this vulnerability was introduced into Honeywell's firmware. What we know is that it existed long enough to be affecting production systems worldwide before CISA identified it.
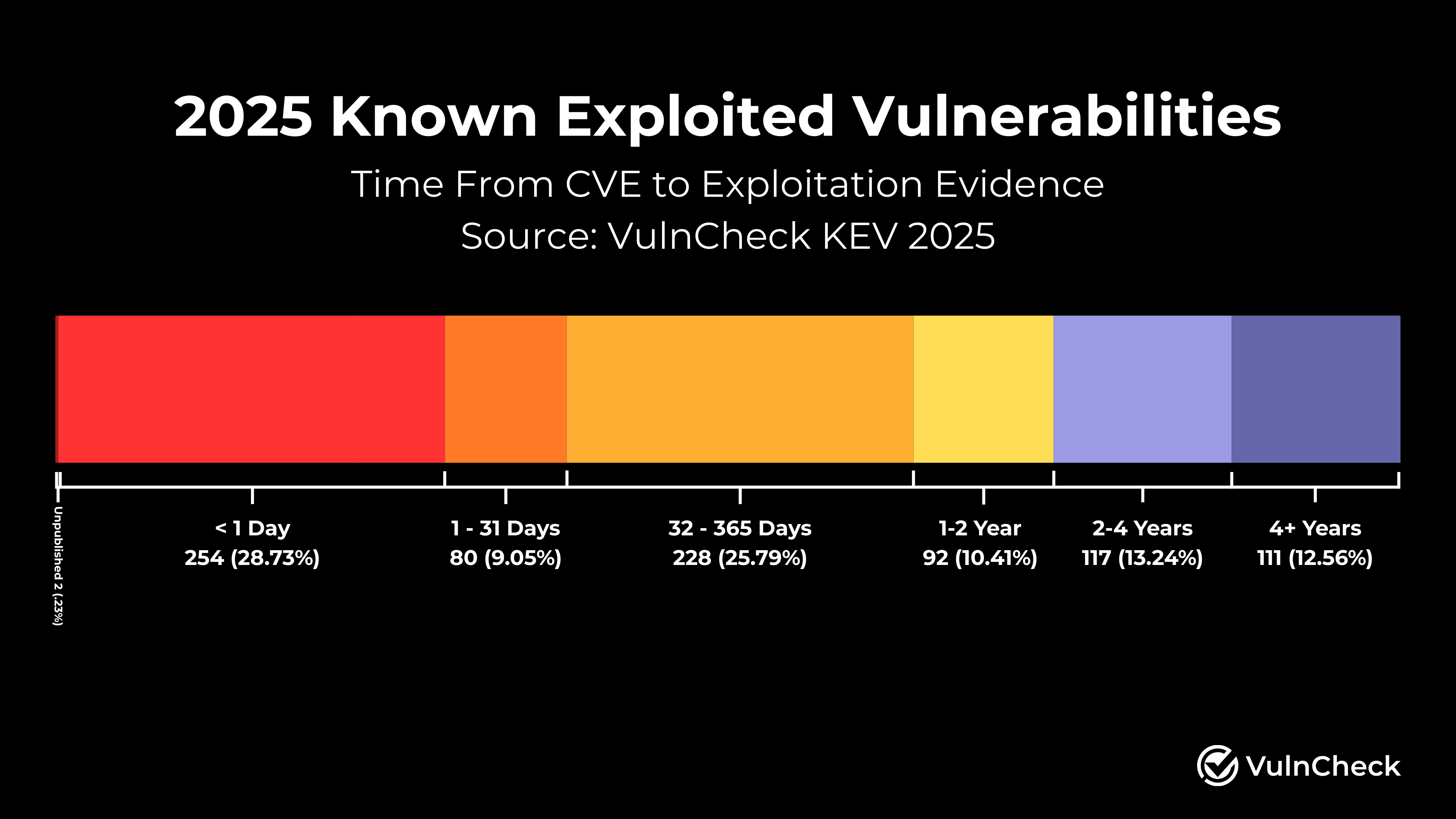
At the time of disclosure, the vulnerability had not yet appeared in CISA's Known Exploited Vulnerabilities (KEV) catalog. That's both good news and bad news. The good news: no documented active exploitation in the wild yet. The bad news: the moment a detailed advisory goes public, the clock starts ticking.
Cybercriminals operate on a simple timeline. They wait for patches to be announced, reverse-engineer the fixes to understand the vulnerability, then immediately start scanning networks for unpatched systems. Researchers call this "patch spraying." You announce a vulnerability on Monday, and by Wednesday, you'll see automated scanners probing for vulnerable systems.
Given Honeywell's market position and the nature of their customers, it's safe to assume that sophisticated threat actors are now actively scanning for I-HIB2PI-UL, MVO-3, and other affected models.
Which Honeywell Camera Models Are Actually Vulnerable?
Honeywell makes a lot of CCTV cameras. They have enterprise solutions, mid-market offerings, and budget-friendly models. Not all of them are affected by CVE-2026-1670.
Here are the confirmed vulnerable models:
I-HIB2PI-UL 2MP IP 6.1.22.1216: This is a 2-megapixel IP camera commonly deployed in smaller commercial environments. The firmware version 6.1.22.1216 contains the vulnerability.
SMB NDAA MVO-3: The MVO-3 is Honeywell's mid-range PTZ (pan-tilt-zoom) camera. It's designed for small and medium business deployments and offers NDAA compliance for federal deployment eligibility. The SMB variant affects multiple firmware versions.
WDR_2MP_32M_PTZ_v 2.0 variants: This line includes several sub-models, all using the WDR (Wide Dynamic Range) 2MP sensor with 32x zoom optical capability. The vulnerabilities span across different deployment configurations.
What's important to understand is that these are mid-level cameras. They're the workhorse equipment. Not the premium enterprise solutions, not the budget cameras. The ones most organizations actually deploy at scale.
Honeywell offers NDAA-compliant models specifically engineered for government and critical infrastructure use. This isn't a theoretical problem affecting some niche product line. This affects systems protecting actual facilities.

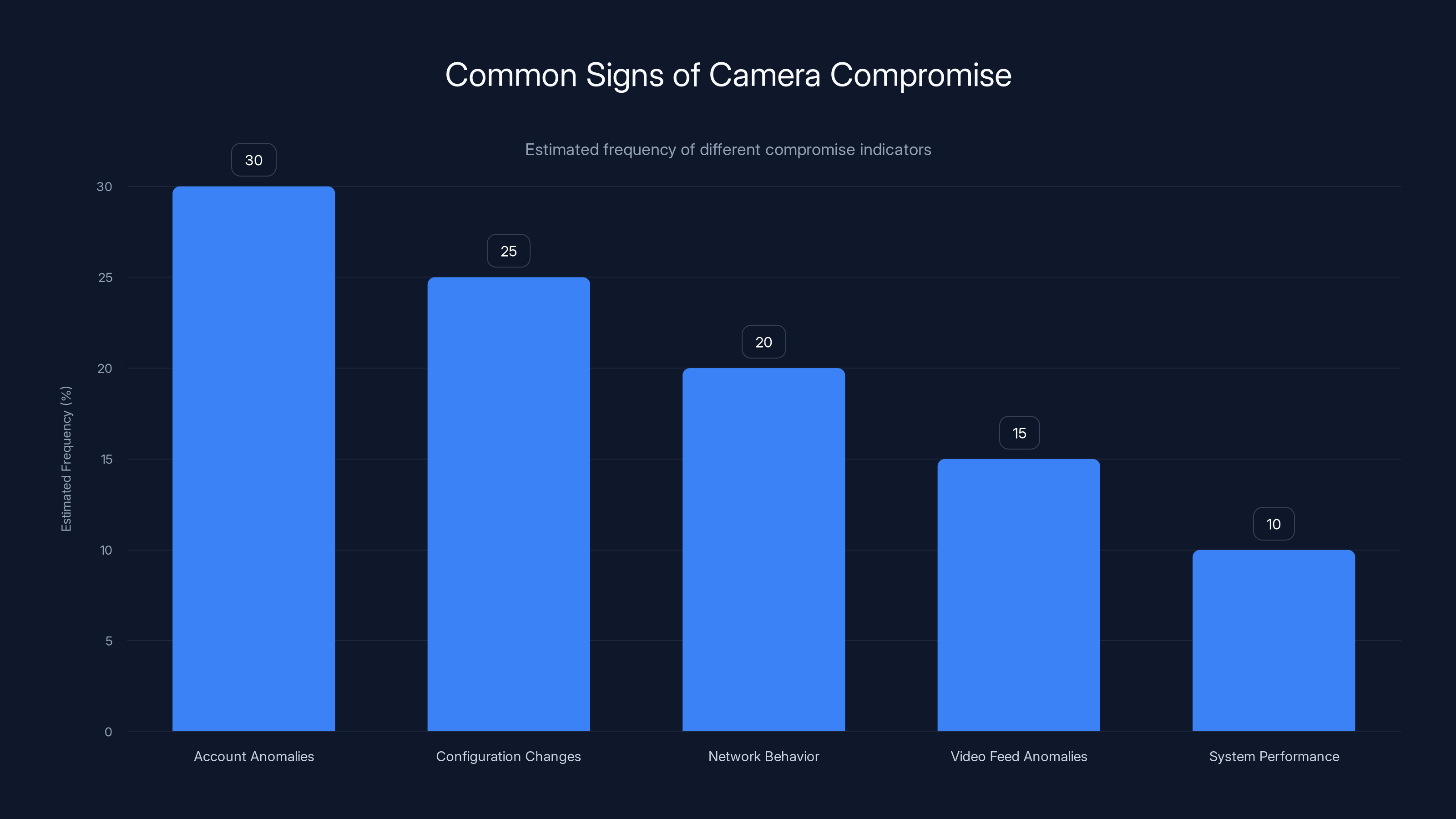
Account anomalies are the most common sign of camera compromise, followed by configuration changes. Estimated data based on typical security reports.
How Does the Attack Actually Work? Step by Step
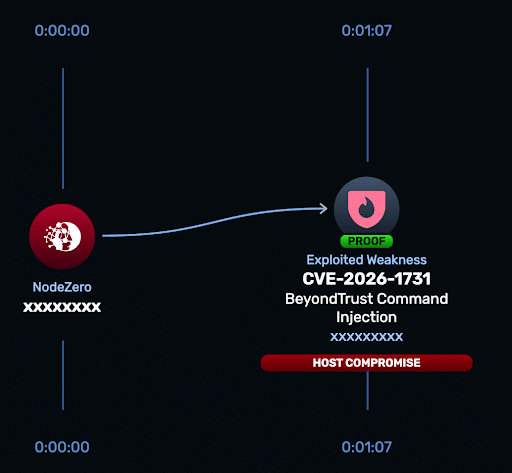
Let's walk through how an attacker exploits this vulnerability in a realistic scenario. Understanding the attack chain helps you understand why patches are urgent.
Step 1: Reconnaissance and Discovery
An attacker starts with network scanning. They're looking for Honeywell cameras that are internet-facing or accessible from compromised network segments. Tools like Shodan, Censys, or basic port scanning identify cameras by their HTTP headers and response signatures.
They're looking for the characteristic response from a Honeywell camera API. Maybe the camera is on the public internet. Maybe it's inside a compromised business network. Either way, if the camera can be reached, the attacker has the first piece of the puzzle.
Step 2: Unauthenticated API Access
Normally, when you access a camera's settings, you'd need to authenticate first. The camera server checks your credentials, verifies you're authorized, and then grants access to sensitive functions.
With CVE-2026-1670, that authentication check is missing on critical functions. The API endpoint that manages account recovery email, for instance, doesn't verify who's calling it. An attacker can send a request directly to this endpoint without providing any credentials.
Step 3: Account Recovery Email Modification
The attacker sends an API call that changes the recovery email address associated with the camera account. Maybe the original email was security-team@company.com. The attacker changes it to attacker@gmail.com.
This happens silently. No notification to the original owner. No confirmation request. Just gone.
Step 4: Password Reset and Account Takeover
With the recovery email changed, the attacker clicks the "Forgot Password" function. Honeywell sends the password reset link to the new recovery email address—the one the attacker controls. The original owner never sees it.
The attacker resets the password, creates a new one, and now has full account access. They're in.
Step 5: Lateral Movement and Reconnaissance
Now the attacker has legitimate access to the camera system. They can:
- View live camera feeds to understand physical security
- Access recorded footage to identify patterns and vulnerabilities
- Potentially reach other systems connected to the camera network
- Use the camera system as a foothold for deeper network penetration
This is where the real damage happens. The camera wasn't the final target—it was the door to get inside.
The Root Cause: Missing Authentication Logic
From a code perspective, this boils down to one thing: Honeywell's developers implemented critical functions—changing recovery emails, accessing camera feeds, modifying settings—without verifying that the request came from an authenticated user.
Probably, the code looks something like this in pseudocode:
function change Recovery Email(new Email) {
// Missing: Check if user is authenticated
// Missing: Verify user has permission to change this field
database.update Recovery Email(new Email);
return {status: "success"};
}
Instead of what it should be:
function change Recovery Email(new Email, auth Token) {
// Verify authentication token is valid
if (!verify Auth Token(auth Token)) {
return {status: "error", message: "Unauthorized"};
}
// Verify user has permission
if (!has Permission(auth Token, "modify_account")) {
return {status: "error", message: "Insufficient permissions"};
}
database.update Recovery Email(new Email);
return {status: "success"};
}
It's a straightforward security oversight. Missing authentication checks are consistently in the top 5 most dangerous vulnerability types because they're simple to exploit and devastating in impact.
Honeywell's firmware didn't include the necessary checks on critical account management functions. This vulnerability likely affects multiple firmware branches and deployment versions, which is why the affected models list includes several variants.
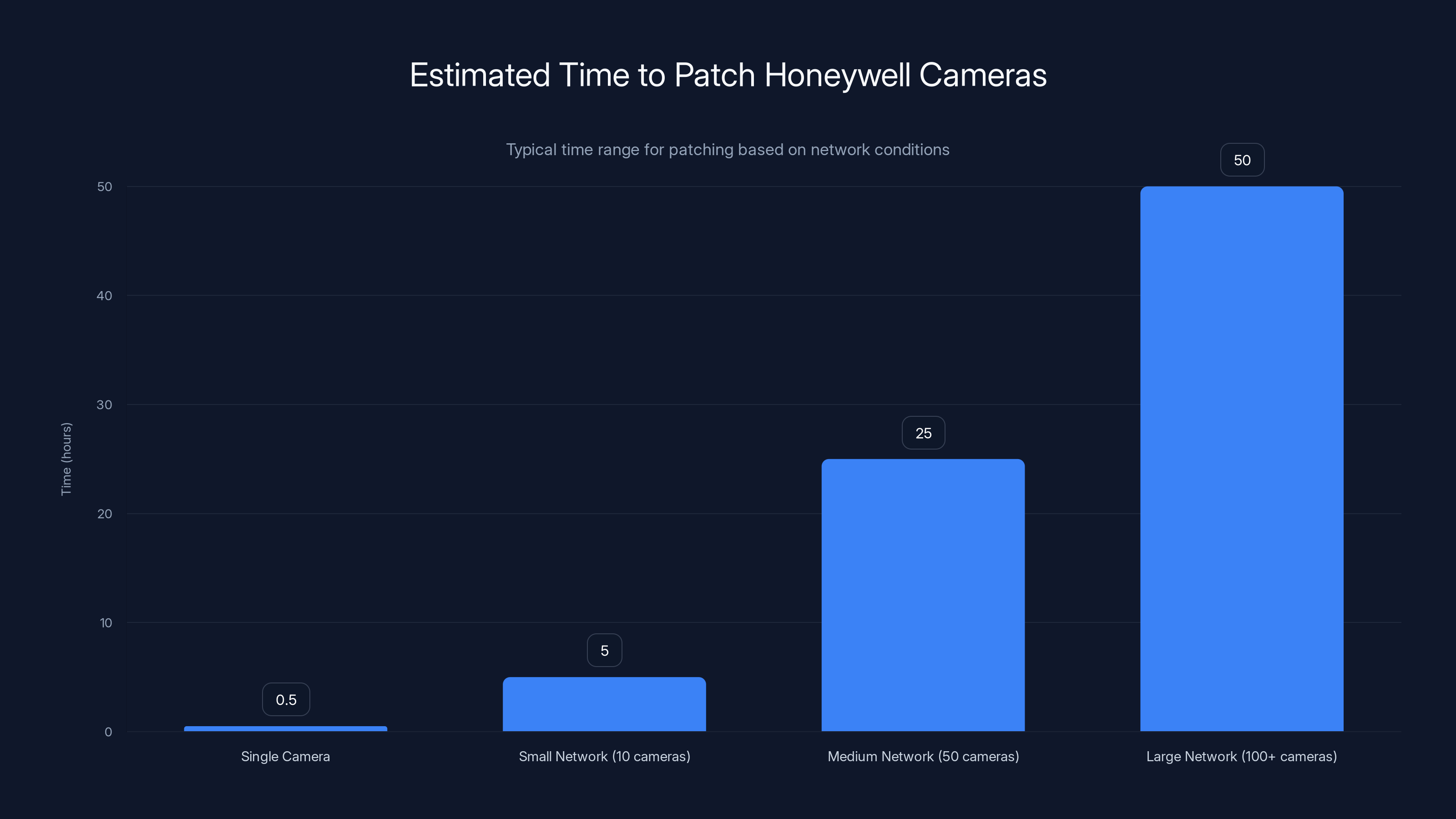
Patching a single Honeywell camera takes 30-60 minutes. Larger networks require staged updates, potentially spanning several weeks. Estimated data.
Which Organizations Are Most at Risk?
Not all organizations face equal risk. The impact depends on your network architecture, camera deployment, and operational context.
High-Risk Scenarios:
You're at significant risk if your Honeywell cameras are internet-facing or accessible from compromised segments. Cloud-connected cameras that allow remote access amplify the risk because the attack surface extends beyond your physical network.
Critical infrastructure operators, government agencies, and organizations with sensitive physical security requirements face elevated risk. Attacker interest correlates strongly with target value. A camera compromise at a data center, government facility, or high-security warehouse attracts serious threat actors.
If your network doesn't segment cameras from operational systems, the risk escalates dramatically. A compromised camera that can pivot to your internal network becomes a beachhead for lateral movement.
Medium-Risk Scenarios:
Warehouses, manufacturing facilities, and medium-sized businesses running these cameras are at moderate risk. The camera system is valuable for reconnaissance, but it's not necessarily the primary target.
If your cameras are isolated on a separate network segment with restricted access to production systems, risk is mitigated but not eliminated. Attackers still gain visual reconnaissance.
Lower-Risk Scenarios:
Small businesses with cameras isolated on internal networks only, no internet connectivity, and minimal sensitive operations visible in footage face lower risk. But "lower risk" doesn't mean "no risk." A disgruntled insider or compromised employee account could still access the camera network.
CISA's Official Recommendation: What You Must Do
The Cybersecurity and Infrastructure Security Agency doesn't make casual recommendations. When CISA issues an advisory, they've already assessed the real-world risk and determined action is necessary.
For CVE-2026-1670, CISA's official guidance includes immediate patching, network isolation, and architectural changes to limit exposure. Let's break down each recommendation and explain why it matters.
Immediate Priority: Apply Security Patches
Honeywell has released patched firmware addressing this vulnerability. The exact version numbers and availability depend on your specific model, but patches are available now.
The process typically involves:
- Logging into your camera's admin interface
- Navigating to System Settings or Device Management
- Checking for firmware updates
- Downloading and installing the latest patched version
- Verifying the camera reboots and reconnects properly
But here's the catch: you need to do this carefully. Firmware updates on surveillance systems require planning. You can't just update all cameras simultaneously during business hours. You'll lose surveillance coverage. Coordinate with your security team to schedule updates during low-risk windows.
For organizations with hundreds of cameras, this is a logistical challenge. But it's non-negotiable. Unpatched cameras are currently vulnerable.
Secondary Priority: Network Isolation
Even if you can't patch immediately, you can reduce risk by isolating cameras from the broader network.
Implement these controls:
Firewall Rules: Configure firewalls to allow camera traffic only to and from authorized management systems. Block all inbound access from the internet. Restrict outbound access to only necessary services (NTP for time sync, maybe a cloud service if you use one).
Network Segmentation: Isolate cameras on a dedicated VLAN or subnet separate from production systems. If a camera is compromised, it shouldn't have direct access to your database servers, application servers, or critical infrastructure.
VPN for Remote Access: If you need remote access to cameras, route it through a VPN. Don't expose the camera interface directly to the internet. VPNs add an authentication layer before attackers can even reach the vulnerable camera API.
CISA specifically noted that "not all VPNs are equal." You need properly configured VPNs with strong authentication, ideally with multi-factor authentication for administrative access.
Monitoring and Alerting:
Set up network monitoring to detect unusual camera behavior. Alert on:
- Failed authentication attempts to the camera interface
- Unusual API calls or function access
- Configuration changes (especially email address modifications)
- Unexpected network connections initiated by the camera
- Firmware or software modifications
Intrusion detection systems should flag suspicious patterns associated with this vulnerability class.


Organizations with internet-facing or poorly segmented networks face the highest risk. Estimated data based on typical scenarios.
How to Patch: The Complete Technical Process
Patching sounds simple until you have 50 cameras spread across multiple locations. Here's a realistic, step-by-step approach.
Phase 1: Inventory and Assessment (Day 1-2)
First, you need to know what you actually have. Create a comprehensive inventory:
- Identify every Honeywell CCTV camera in your environment
- Document the model number (check camera body or admin interface)
- Record the current firmware version
- Note the network location (which subnet, which building, etc.)
- Determine dependencies (systems that rely on this camera, monitoring solutions, etc.)
Check your admin interface. Most Honeywell cameras show firmware version under "About" or "System Information." Compare your versions against the vulnerable list.
Phase 2: Patch Sourcing (Day 2-3)
Visit Honeywell's support portal or contact their technical support directly. Provide your model numbers. Request the latest patched firmware.
Download patches from official Honeywell sources only. Don't use third-party firmware downloads or unofficial updates. Firmware is a critical security component. Integrity matters.
Verify firmware checksums if available. Honeywell often provides MD5 or SHA-256 checksums to verify download integrity.
Phase 3: Testing and Planning (Day 3-5)
If you have a test environment, update one camera first. Verify:
- Firmware installs without corruption
- Camera boots up successfully
- Network connectivity is restored
- Admin interface is accessible and functions properly
- Integration with your monitoring system works (if applicable)
For production updates, create a timeline. You'll lose surveillance coverage during updates. Communicate with security teams about acceptable downtime windows.
Prioritize cameras by risk. Update internet-facing or high-security area cameras first.
Phase 4: Staged Rollout (Day 5-14)
Update cameras in batches, not all at once. A reasonable approach:
- Day 5-6: Update 10-15 cameras in low-security areas
- Day 7-9: Update 15-20 cameras in medium-priority areas
- Day 10-12: Update critical facility cameras
- Day 12-14: Finish remaining cameras
After each batch, verify cameras are functioning and reconnected to the network.
Phase 5: Verification and Documentation (Day 14-15)
After all cameras are patched, verify:
- Spot-check firmware versions on random cameras
- Verify network functionality
- Test camera access from authorized locations
- Confirm monitoring systems are receiving feeds
- Document patch dates and versions in your asset management system
Keep records of this for compliance and future reference.

Network Architecture Changes: Beyond Patching
Patching is necessary but not sufficient. You should also redesign how these cameras integrate with your network to prevent similar attacks in the future.
Implement Zero Trust for Camera Systems
Zero trust doesn't mean trusting nothing. It means verifying everything, regardless of network location.
For cameras, this translates to:
- Every access request must authenticate, even from internal networks
- Cameras should not have implicit trust just because they're on the corporate network
- Least privilege access: cameras can only reach systems they genuinely need to reach
- Microsegmentation: isolate cameras on their own network segment with strict ingress/egress rules
This prevents a compromised camera from accessing your database servers, email systems, or sensitive corporate data.
Implement API Gateway Controls
If cameras communicate with cloud services or management systems, route this traffic through an API gateway with authentication, rate limiting, and request validation.
An API gateway sits between the camera and the backend system, checking every request for legitimacy before allowing it through.
Enable Comprehensive Logging
Log all camera access, configuration changes, and network activity. Store logs centrally in a SIEM (Security Information and Event Management) system where they can't be tampered with locally.
This gives you the evidence trail to detect when something went wrong and understand the scope of compromise if an incident occurs.

Identifying Compromise: Signs Your Cameras Have Been Attacked
If your cameras were vulnerable before patching, how would you know if an attacker had already compromised them?
Look for these indicators:
Account Anomalies:
The most obvious sign is if someone changes your recovery email or password without authorization. Check your camera account settings. If the recovery email isn't what you set it to, you've been compromised.
Review account access logs if available. Most Honeywell cameras can log login attempts. Look for failed authentication attempts followed by successful logins from unexpected IP addresses.
Configuration Changes:
Attackers might disable motion detection, reduce video quality, or modify recording settings to cover their tracks. Someone should have documented your camera settings. If they've changed without authorization, that's suspicious.
Some attackers modify the camera's time settings to corrupt timestamp evidence in video footage.
Network Behavior:
Monitor outbound network connections from your cameras. They should only reach authorized management servers or cloud services. Unexpected outbound connections to unfamiliar IP addresses suggest compromise.
Use netstat, network monitoring tools, or firewall logs to audit camera network activity.
Video Feed Anomalies:
If recordings are missing or discontinuous during periods when nothing should have changed, that's suspicious. Attackers might delete footage covering their reconnaissance activity.
Look for gaps in recordings or unusual recording patterns.
System Performance:
Compromised cameras might show degraded performance—slower response times, higher CPU usage, or unexpected network bandwidth consumption. The camera might be running additional malicious processes.
If You Suspect Compromise:
- Isolate the camera immediately by disconnecting it from the network
- Preserve logs from the past 30-90 days for forensic analysis
- Factory reset the camera and reload firmware from official sources
- Review network logs to understand what the compromised camera accessed
- Check connected systems for signs of lateral movement
- Notify your security incident response team
Doesn't require panicking, but it does require systematic investigation.

The Broader Context: Why Camera Vulnerabilities Matter So Much
You might be thinking: "It's just a camera. What's the big deal?"
But surveillance systems have become integral to infrastructure security. They're the visual layer of your defense. And they're increasingly networked, internet-connected, and integrated with other systems.
Here's why a camera vulnerability is actually a serious problem:
Physical Security Reconnaissance: Compromised cameras give attackers detailed visual intelligence about your facility. They can identify security patterns, guard rotations, entry/exit procedures, and vulnerabilities before they plan a physical breach.
Network Foothold: A camera with network access can become a pivot point for lateral movement. From the camera system, an attacker might reach backup systems, management networks, or storage devices.
Supply Chain Risk: If Honeywell cameras are part of your critical infrastructure, compromised cameras affect not just your organization but potentially downstream customers who rely on your services.
Compliance Violations: Depending on your industry, you might have specific security requirements for surveillance systems. Failing to patch known vulnerabilities can violate compliance frameworks like HIPAA, PCI-DSS, or SOC 2.
Insider Threat Enablement: An employee with compromised camera credentials can monitor colleagues, disable recordings, or gather intel for theft or espionage.
This is why CISA treats camera vulnerabilities seriously. It's not just about the camera—it's about what the camera enables attackers to do next.

Proactive Vulnerability Management: Beyond This Specific Flaw
CVE-2026-1670 is today's problem. But what about tomorrow's vulnerabilities?
Build a sustainable vulnerability management process:
1. Continuous Monitoring
Subscribe to security advisories from your equipment vendors. Honeywell publishes security bulletins. CISA maintains a database of vulnerabilities. Subscribe to these feeds.
Set up automated scanning that identifies Honeywell cameras and their firmware versions on your network regularly. When new vulnerabilities are announced, you'll already know which cameras are affected.
2. Regular Patching Cadence
Don't wait until a critical vulnerability forces your hand. Establish a regular patching schedule—monthly or quarterly—where you review available updates and apply them systematically.
Small, regular patches are less disruptive than emergency patches.
3. Firmware Integrity Verification
When you update camera firmware, verify the download against official checksums. Firmware tampering is a real attack vector. Before deploying firmware, confirm it comes from official sources and hasn't been modified.
4. Configuration Hardening
Beyond patching, harden camera configurations:
- Disable unnecessary services and protocols
- Change default credentials immediately (camera-admin credentials are often trivial)
- Enable all available logging
- Restrict remote access features if you don't use them
- Disable cloud connectivity if it's not required
5. Threat Intelligence Integration
Monitor threat intelligence feeds for reports of CVE-2026-1670 exploitation. If researchers publish exploit code or attackers begin active exploitation, you'll want to know immediately so you can prioritize patching.

The Cost of Inaction: What Happens If You Don't Patch
Let's be concrete about consequences. What actually happens if your organization ignores this vulnerability?
Week 1-2 Post-Disclosure:
Your camera remains vulnerable but uncompromised. No immediate operational impact.
Week 3-4:
Automated scanning networks start detecting unpatched Honeywell cameras. Attackers identify your organization as having vulnerable systems.
Week 5-8:
Sophisticated threat actors begin targeting your facility. They gain access to camera accounts and begin reconnaissance. You don't know this is happening.
Week 9-12:
Based on reconnaissance, attackers plan a physical breach. Maybe they're after inventory, intellectual property, or just gathering intel for a larger attack.
Breach Execution:
Using knowledge from camera reconnaissance—security guard schedules, entry points, alarm configurations—attackers compromise your facility. Physical security is bypassed.
Investigation and Response:
You discover the breach. Investigation reveals attackers used compromised cameras for reconnaissance. Incident response costs escalate. Your organization faces compliance violations, potential notification requirements, and reputational damage.
This isn't hypothetical. Camera-based reconnaissance precedes actual physical breaches in documented incidents.
The Math:
Patching a camera takes 30-60 minutes. Investigating a breach potentially costs

FAQ
What does CVE-2026-1670 actually allow attackers to do?
CVE-2026-1670 allows unauthenticated attackers to access Honeywell CCTV camera feeds and take over camera accounts by changing the recovery email address associated with the account. Once the recovery email is changed, attackers can reset the password and lock out legitimate users while gaining full administrative access to the camera system.
How do I know if my Honeywell cameras are vulnerable?
Check your camera's firmware version by accessing the admin interface (usually available at http://camera-ip-address). Go to System Settings or Device Information and note the firmware version. Compare it against the affected versions list (I-HIB2PI-UL 2MP IP 6.1.22.1216, SMB NDAA MVO-3, and WDR_2MP variants). If your firmware version matches or predates the vulnerable versions, your camera is affected until patched.
How long does it take to patch a Honeywell camera?
Patching a single camera typically takes 30-60 minutes depending on firmware size and network speed. The process involves logging into the admin interface, downloading the patched firmware, initiating the update, and allowing the camera to reboot and reconnect. For organizations with multiple cameras, you should plan staged updates across several weeks to maintain surveillance coverage during maintenance windows.
Can I patch cameras without losing surveillance?
Yes, you should schedule patches during low-risk periods when loss of surveillance is acceptable. Batch updates by location or time zone so not all cameras are down simultaneously. Coordinate with your security team to identify maintenance windows. For 24/7 critical facilities, you might patch just a few cameras at a time while maintaining coverage from others.
What should I do if I can't patch immediately?
If you can't patch right away, implement network isolation immediately. Configure firewalls to block inbound access to cameras from the internet. Place cameras on a separate network segment isolated from production systems. Enable VPN access for remote administration instead of direct internet exposure. Monitor network traffic for unusual camera activity. These controls significantly reduce risk while you plan your patching timeline.
How do I detect if my cameras have already been compromised by this vulnerability?
Check your camera account's recovery email address in the admin settings. If it's not what you set it to, you've likely been compromised. Review access logs for failed login attempts or logins from unexpected IP addresses. Monitor outbound network connections from cameras using network monitoring tools or firewall logs. Look for missing video segments or unusual recording gaps. If you suspect compromise, isolate the camera immediately and preserve logs for forensic investigation.
Will my vulnerability scanner detect CVE-2026-1670?
Most modern vulnerability scanners can identify CCTV cameras and their firmware versions on your network. They'll flag them as vulnerable once signatures for CVE-2026-1670 are added to their databases. Additionally, tools like Shodan and Censys can find internet-facing Honeywell cameras. However, your organization should also manually scan your network to build a complete inventory of cameras for vulnerability assessment.
What's the difference between this vulnerability and typical password attacks?
Traditional attacks require the attacker to crack your password or obtain credentials through phishing or social engineering. CVE-2026-1670 requires neither. An attacker doesn't need your password or any credentials. They simply send a request to the camera's API without authenticating, and the camera processes their request as if they were authorized. This is why it's so dangerous—it bypasses traditional authentication entirely.
How do I know if my network is being scanned for vulnerable cameras?
Enable logging on your firewall and camera systems. Look for repeated connection attempts to your camera IP addresses from external sources. Monitor for unusual API requests or HTTP requests to the admin interface from unknown IP addresses. Set up intrusion detection systems to alert on reconnaissance activity. If you see patterns of scanning attempts, it suggests attackers are actively looking for vulnerable cameras in your network range.
Should I disconnect my cameras from the internet completely?
If you don't need remote access, air-gapping cameras (keeping them on internal networks only, not internet-connected) significantly reduces risk. However, if you require remote monitoring, use secure methods like VPNs with strong authentication rather than direct internet exposure. Even after patching, limiting internet connectivity for cameras is a good security practice.
What happens if I factory reset a compromised camera?
Factory resetting will clear the malicious configuration changes (like the modified recovery email address) and restore the camera to default settings. However, you must reload with patched firmware, not the original vulnerable firmware, otherwise you'll be re-vulnerating the camera. Factory reset should be part of your recovery process if you discover compromise: isolate the camera, factory reset it, load patched firmware from official sources, change all default credentials, and reintegrate it into your network.

Key Takeaways
CVE-2026-1670 is a critical vulnerability affecting Honeywell CCTV cameras, but it's manageable with immediate action. Patch now if your camera firmware matches the vulnerable versions. If you can't patch immediately, isolate cameras behind firewalls and VPNs. Monitor for signs of compromise like unauthorized recovery email changes. Beyond this vulnerability, establish ongoing patch management and network segmentation for all camera systems. The cost of patching is negligible compared to the cost of a breach enabled by camera reconnaissance.
Don't delay. Start your patch assessment today.

Related Articles
- Japanese Hotel Chain Hit by Ransomware: What You Need to Know [2025]
- Dell Zero-Day Vulnerability: Hardcoded Credentials Exploited for 2 Years [2025]
- Texas Sues TP-Link Over China Links and Security Vulnerabilities [2025]
- AI Governance & Data Privacy: Why Operational Discipline Matters [2025]
- Ransomware Targeting Firewalls: The Critical 2025 Security Crisis [2025]
- Abu Dhabi Finance Summit Data Breach: 700+ Passports Exposed [2025]
![Honeywell CCTV Camera Vulnerability: Complete Security Guide [2025]](https://tryrunable.com/blog/honeywell-cctv-camera-vulnerability-complete-security-guide-/image-1-1771538734532.jpg)



