Chrome Extensions Hijacking 500K VKontakte Accounts: A Deep Dive Into the Attack [2025]
Let me start with something that should scare you a little: five Chrome extensions that looked completely harmless hijacked over half a million social media accounts. Nobody got a warning. Nobody saw it coming. The extensions just sat there on the Chrome Web Store, waiting to be installed, doing their damage in the background while users had no idea what was happening.
This isn't some theoretical attack. This happened in 2025. Real people, real accounts, real money stolen.
VKontakte—basically the Russian version of Facebook—is one of the largest social networks in the world. With around 650 million users, it's a goldmine for attackers. And someone realized that if you could hijack even a fraction of those accounts, you'd have access to payment information, private messages, personal data, and a massive botnet ready to do whatever you want.
What makes this attack genuinely interesting isn't just the scale. It's the sophistication. These weren't your typical cryptominers that make your laptop sound like a jet engine. These extensions were surgical. They modified CSRF tokens to bypass security. They reset account settings every 30 days to override anything users tried to change. They tracked "donations" to extract payment information. They subscribed victims to massive VK groups with 1.4 million members. And they did all of this while staying relatively quiet.
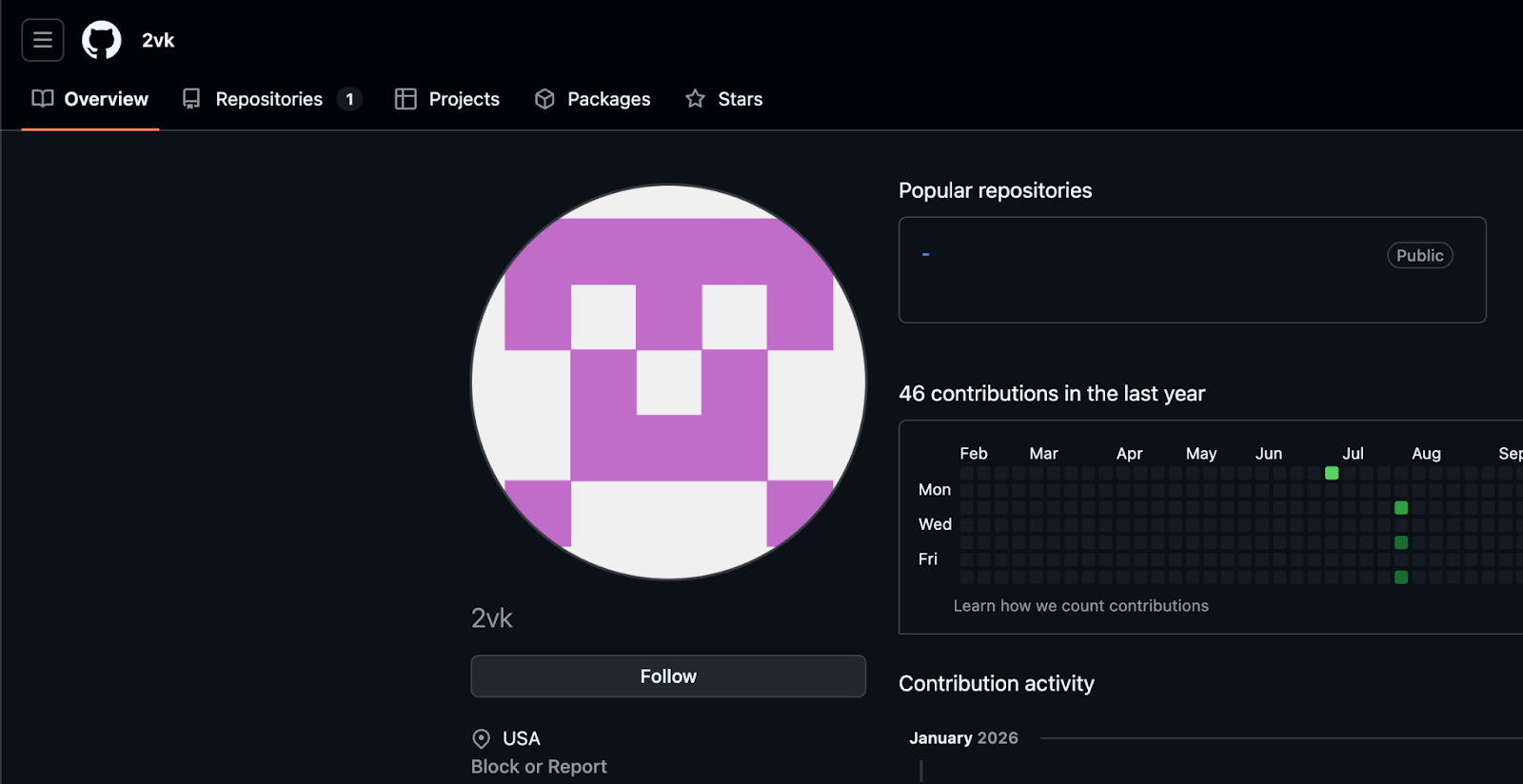
The campaign was discovered by researchers at Koi Security, who found that all five extensions shared a common thread: they were maintained by a single threat actor using the GitHub alias "2vk." They'd been running since mid-2025, and they were primarily targeting Russian-speaking users, though victims showed up in Eastern Europe, Central Asia, and beyond.
Here's what you need to know about this attack, why it matters, and what you can do to protect yourself from the next one.
TL; DR
- Half a million accounts compromised: Five malicious Chrome extensions hijacked over 500,000 VKontakte accounts through the official Chrome Web Store
- Multi-layered attack: Extensions auto-subscribed users to attacker groups, manipulated CSRF tokens, injected ads, and stole payment data
- Persistent threat: Campaign maintained by threat actor "2vk" since mid-2025, primarily targeting Russian-speaking users across multiple regions
- Payment theft confirmed: Attackers tracked donation status to extract credit card information and monetize victims directly
- Browser extension supply chain weakness: Demonstrates critical vulnerability in how browser extension stores validate and monitor plugins
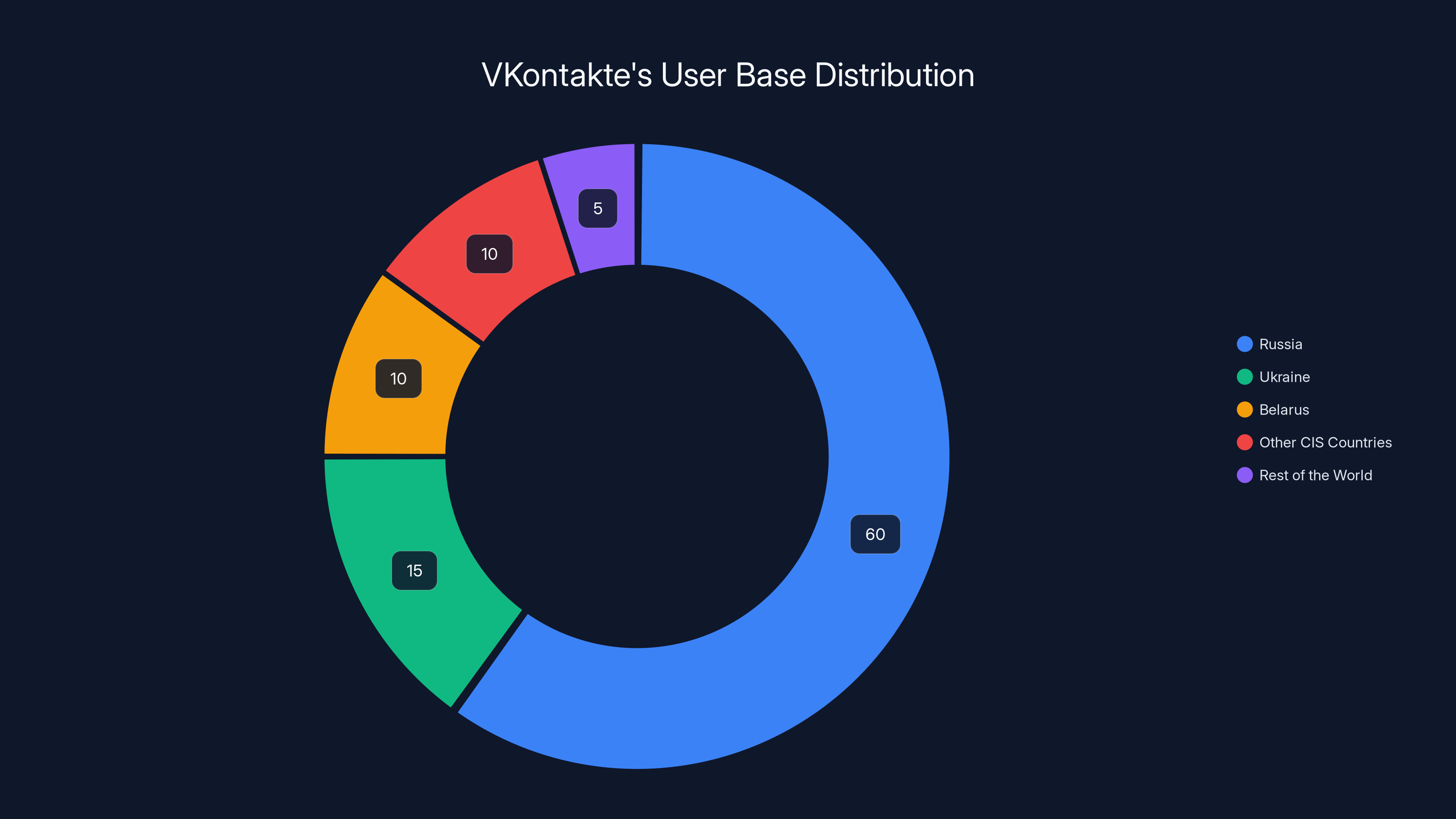
VKontakte's user base is predominantly in Russia, with significant portions in Ukraine and Belarus, making it a prime target for attackers due to regional cybercrime dynamics. (Estimated data)
The Attack Anatomy: How Five Extensions Compromised Half a Million Accounts
Understanding this attack requires breaking it down into its components. On the surface, these extensions did exactly what they claimed: they enhanced VKontakte's user interface. They promised theme changes, better visual experiences, quality-of-life improvements. The kind of thing that sounds useful enough to install if you're a regular VKontakte user.
But underneath that innocent facade was something far more sinister.
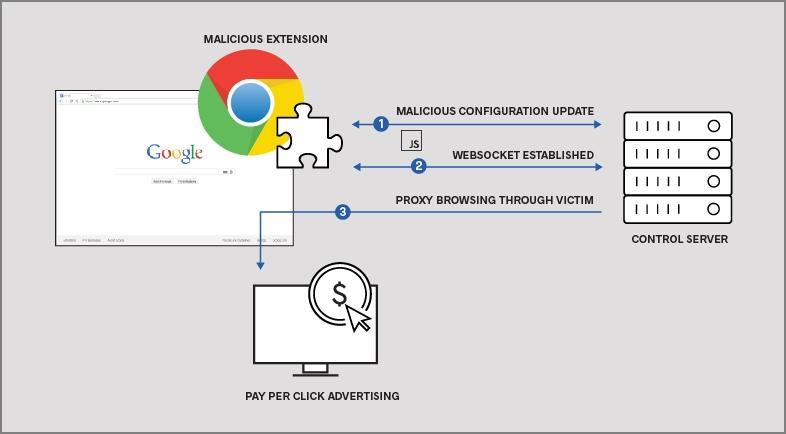
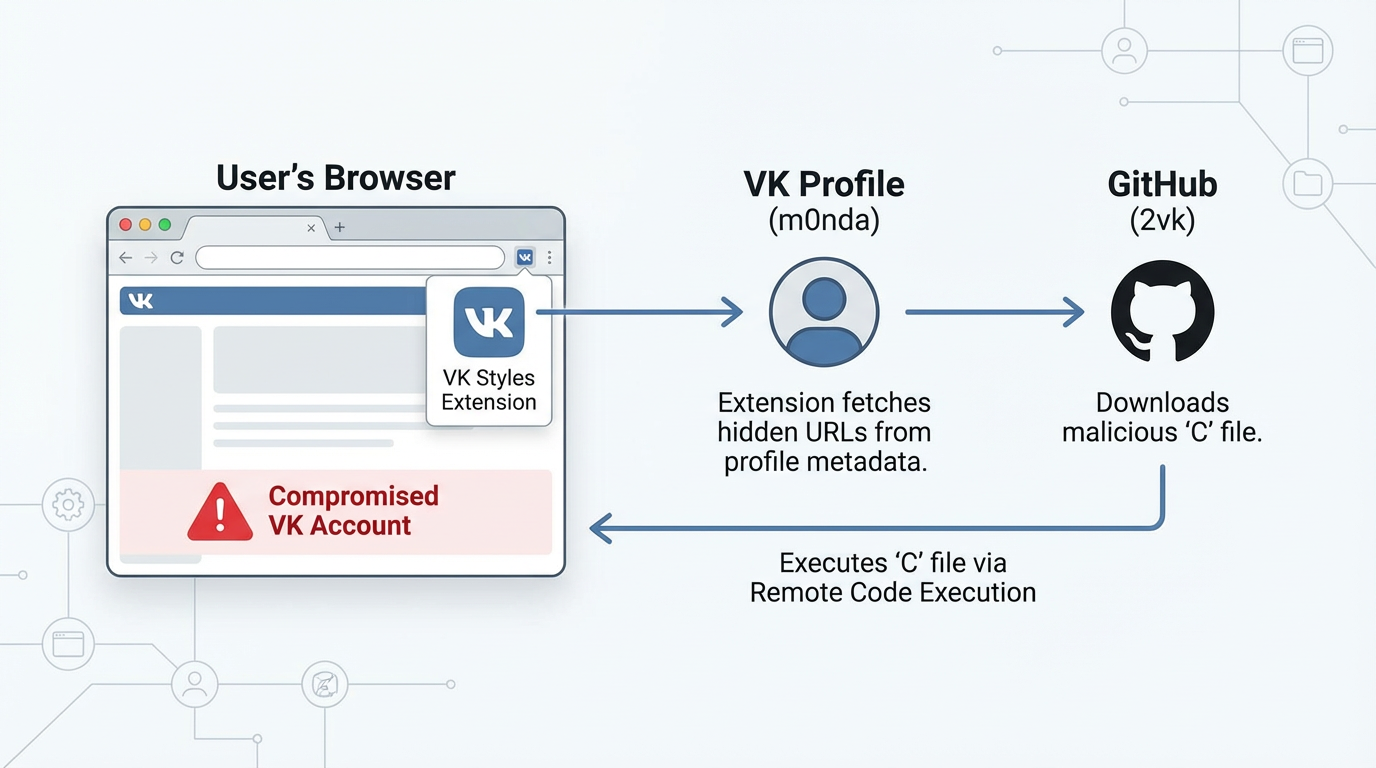
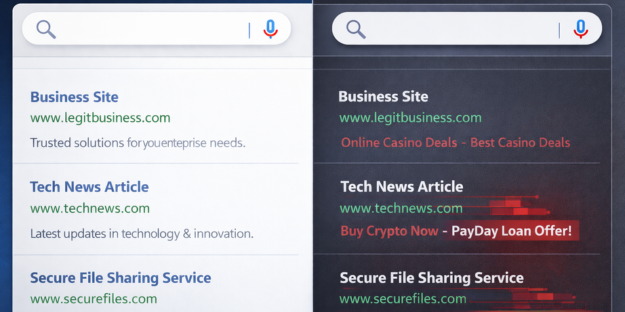
The extensions operated through what security researchers call a "multi-stage injection" system. When you installed one of these extensions, it didn't immediately start stealing everything. Instead, it injected code into every page you visited. This code was constantly being updated from attacker-controlled servers, which meant the attackers could change what the malware did at any time without requiring users to update.
This is genuinely clever from an attacker's perspective. If the malware is hardcoded into the extension, every change requires users to update. But if the malicious behavior is injected dynamically, you can pivot your attack based on what's working. If ad injection is profitable, do more of that. If payment information is valuable, focus there. If you need to expand your botnet, change tactics again.
The first victim that most users would experience was auto-subscription. The moment you installed one of these extensions, your VKontakte account was automatically subscribed to the attacker's groups. Eventually, these groups ballooned to 1.4 million members. For the attacker, this serves multiple purposes. It looks legitimate (hey, if a million people are in the group, it must be real). It creates a captive audience for serving ads and additional malware. And it gives the attacker a communication channel to potentially distribute more malicious content.
But auto-subscription is just the beginning. The extensions had access to your CSRF tokens, which are basically security credentials that tell VKontakte "yes, this request actually came from this user." With these tokens, attackers could perform actions as if they were you, without needing your password. Send messages pretending to be you. Access private conversations. Change your recovery email address. Access payment information stored on the account. It's the kind of access that makes compromised accounts genuinely valuable.
The extensions also implemented what researchers called a "reset mechanism." Every 30 days, they would reset your account settings. Why? Because security-conscious users would change their passwords, enable two-factor authentication, or revoke app permissions. By resetting everything back to default settings every month, the attackers maintained persistent access even as users tried to clean up their compromised accounts.
The financial angle was equally sophisticated. The extensions tracked when users tried to upgrade to "premium features" or make donations. When that happened, they captured the payment information. Credit card numbers, expiration dates, CVV codes. Everything needed to commit fraud. Victims thought they were paying for legitimate premium features. They were actually handing their financial information directly to attackers.
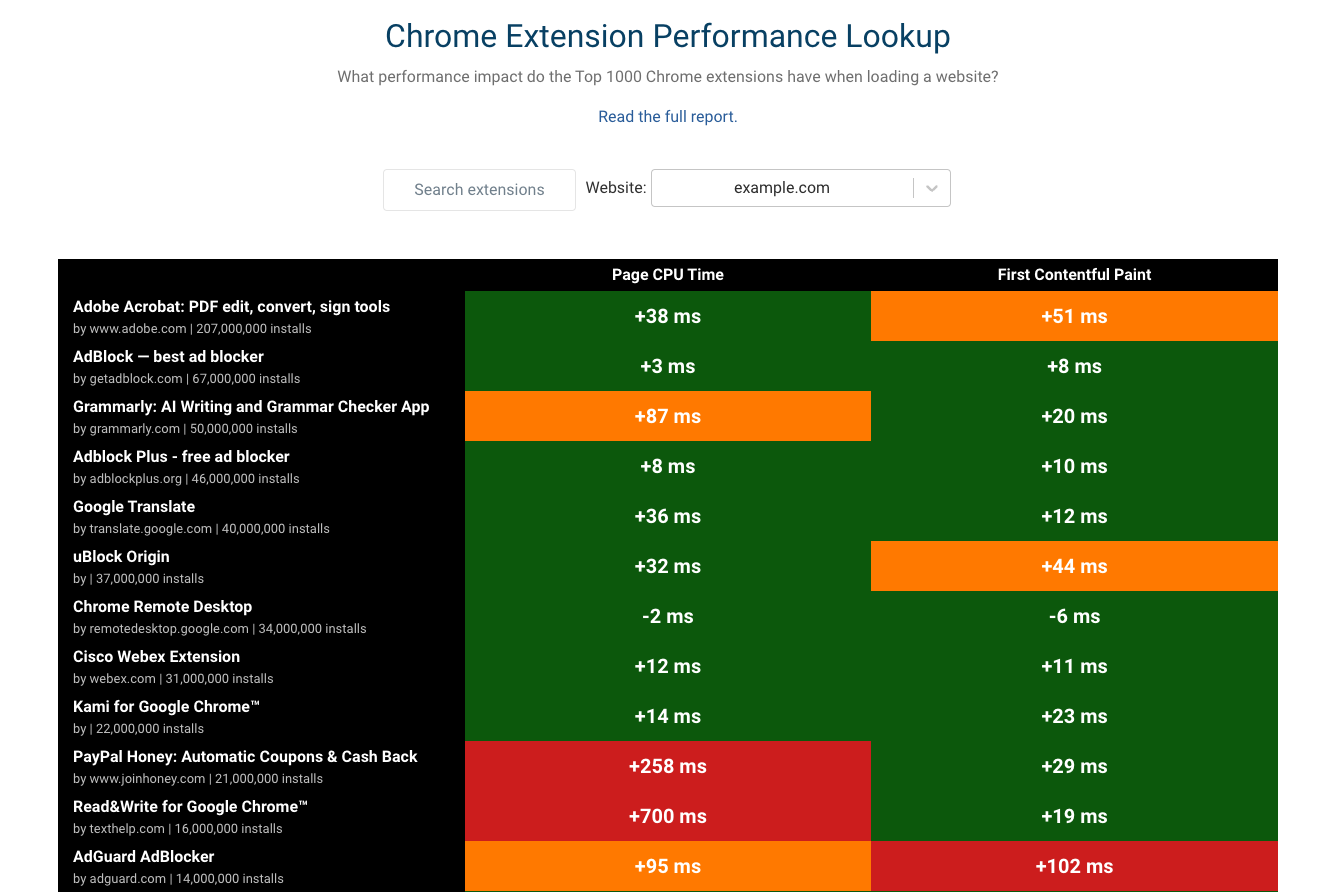
One extension specifically injected Yandex advertising scripts into every page users visited. This directly benefited the attackers financially. Every ad impression, every click, potentially generated revenue. It's basic ad fraud, but at scale across 500,000 accounts, the numbers add up quickly.
What makes this particularly insidious is that users had almost no way to detect what was happening. The extensions didn't make your computer run slowly. They didn't show obvious pop-ups or warning signs. The malicious behavior happened in the background, against your account, not your device. Your computer ran fine. Your browser felt normal. Meanwhile, your social media account was being harvested for every drop of value an attacker could extract.
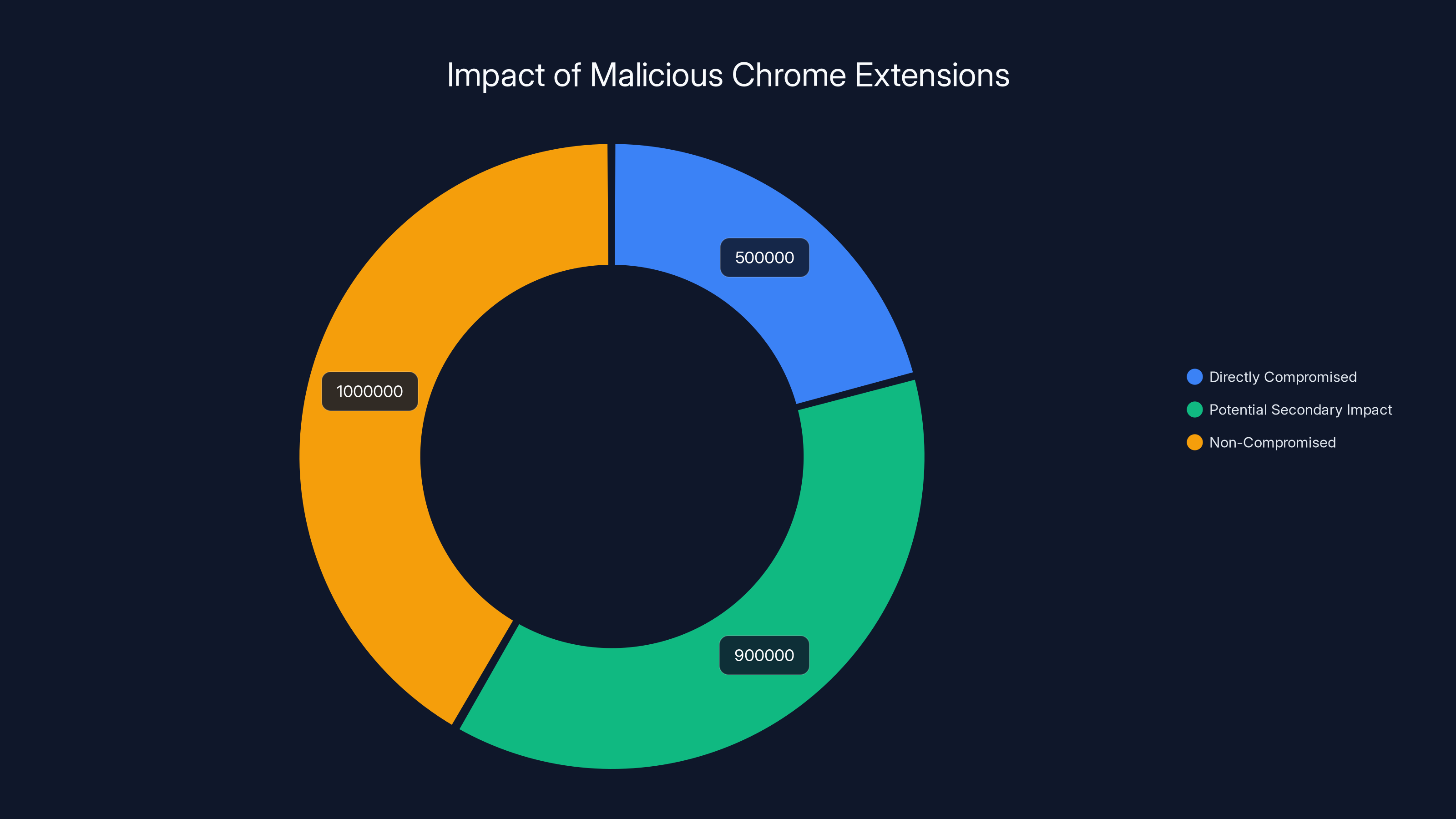
Estimated data shows 500,000 accounts were directly compromised, with potential secondary impacts reaching up to 900,000 more due to account sales.
Why VKontakte Was the Perfect Target
VKontakte isn't just a social network in Russia. It's the social network. If you want to understand why attackers chose this platform specifically, you need to understand its user base and financial ecosystem.
With approximately 650 million users, VKontakte represents one of the largest concentrations of Russian-speaking internet users in the world. In Russia, Belarus, Ukraine, and neighboring countries, VKontakte is what Facebook is to American users. It's where people maintain friendships, join interest groups, organize events, share photos, and yes, make payments.
But there's another layer to this. VKontakte's user base is heavily concentrated in countries where credit card fraud is more profitable and less likely to result in criminal prosecution. A stolen credit card from a Russian user is worth more to an attacker than the associated risk, from their perspective. The infrastructure for reporting financial crimes exists, but enforcement is inconsistent. Victims often can't effectively challenge fraudulent charges. For attackers operating in jurisdictions with weak cybercrime enforcement, this is ideal.
VKontakte also has a robust payment ecosystem built into the platform itself. Users can buy gifts, send donations, upgrade to premium features, all from within VKontakte. This means that to monetize a hijacked account, you don't even need to take the user off-platform. You can generate revenue directly through VKontakte's payment system. The platform becomes both your target and your cash register.
The platform's cultural context matters too. VKontakte has a different user culture than Facebook. Users are more likely to have their real name and address on their profile. They're more likely to maintain friend lists with people they actually know. They're more likely to have complete personal information available. For attackers looking to conduct identity theft or targeted fraud, this is valuable.
Finally, VKontakte's security posture, while respectable, was potentially seen as less well-defended than American platforms. Platforms like Facebook have teams of thousands dedicated to security. VKontakte, while reasonably secure, has fewer resources. This doesn't mean VKontakte was negligent. It means that attackers calculated the risk-reward differently.
The Chrome Web Store Problem: How Malware Got Past Google's Review
This is the part that should make you question how you install browser extensions at all.
Google's Chrome Web Store is supposed to be curated. Extensions are supposed to be reviewed before they're allowed to be published. Google employs security researchers, uses automated scanning, and has policies against malicious behavior. In theory, five extensions maintained by the same threat actor and performing coordinated attacks should have been caught immediately.
They weren't.
The extensions made it past Google's review process and remained on the official Chrome Web Store for months. Over 500,000 people installed them thinking they were legitimate. This wasn't because Google's security team is incompetent. It's because the threat actors were sophisticated enough to defeat the review process.
How did they do it? Researchers didn't reveal the exact evasion techniques, but the patterns are fairly consistent across malware that defeats store reviews. The malware likely didn't exhibit malicious behavior during the review process. Instead, it was activated after publication. The code injection happened dynamically, meaning the malicious payloads weren't visible in the extension's static code. The malware fingerprinted the Chrome review environment and behaved differently when detected.
This is an increasingly common pattern. Malware authors have become extremely sophisticated at defeating automated review systems. They know what automated scanners look for. They design their attacks to pass static analysis. They hide their malicious payloads behind encryption and lazy loading. By the time the extension is live and being used by real users, the malware activates.
Google has since improved its review process in response to incidents like this. But here's the uncomfortable truth: browser extension security will always be a cat-and-mouse game. The sheer number of extensions being submitted to the Chrome Web Store (thousands per day) makes comprehensive human review impossible. Automated review can be defeated. The system is inherently reactive rather than proactive.
The other problem is the information asymmetry. Google knows when an extension violates policy. But users don't. When one of these extensions was finally removed, Google didn't send notifications to everyone who'd installed it. Users didn't receive warnings. They didn't learn about the hijacking until they read security blogs weeks later.
This creates a perverse incentive structure. If attackers know they have weeks or months of operation before being caught, the ROI on sophisticated attack development becomes positive. Even if they're eventually caught and removed, the damage has already been done. Hundreds of thousands of accounts compromised, millions in credit card fraud, and the attacker simply moves on to the next target.

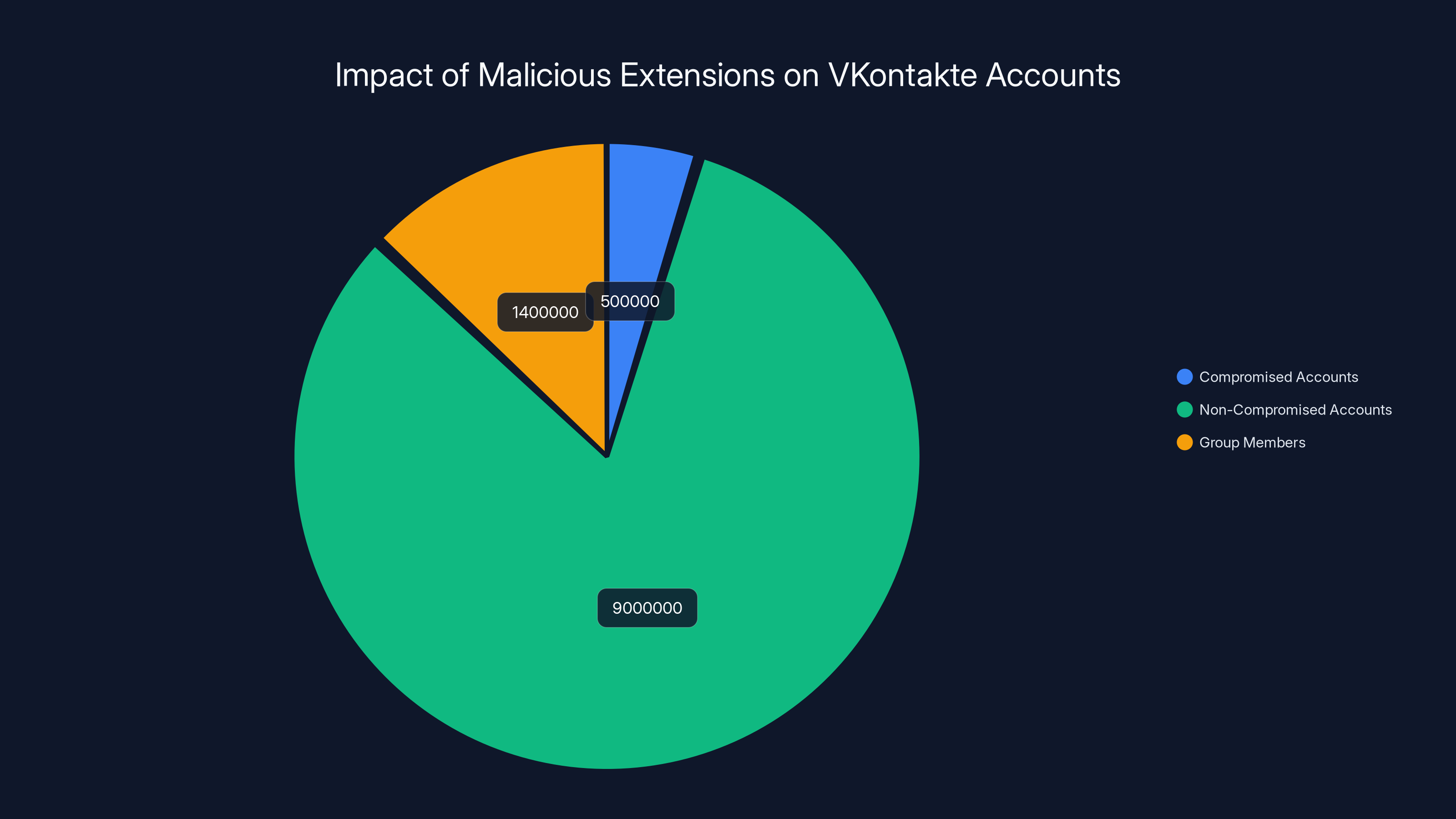
Estimated data shows that 500,000 accounts were compromised, and 1.4 million users were auto-subscribed to attacker groups, highlighting the widespread impact of the extensions.
The Technical Deep Dive: CSRF Manipulation and Token Theft
Let's talk about the mechanics of how these extensions actually stole access.
CSRF, or Cross-Site Request Forgery, is a fundamental web security concept. Imagine you're logged into your bank's website. Your browser has a session cookie that proves you're authenticated. Now imagine you visit a malicious website in another tab. That malicious site can't access your bank's website directly (browsers prevent that), but it can ask your browser to make requests to your bank on your behalf. Your browser will automatically include your session cookies with those requests, making them look legitimate.
To prevent this, modern websites use CSRF tokens. These are random, unique tokens that are embedded in forms and verified server-side. When you submit a form, the website checks that the token is correct and matches your session. If a malicious site tries to forge a request, it won't have the correct token, so the request fails.
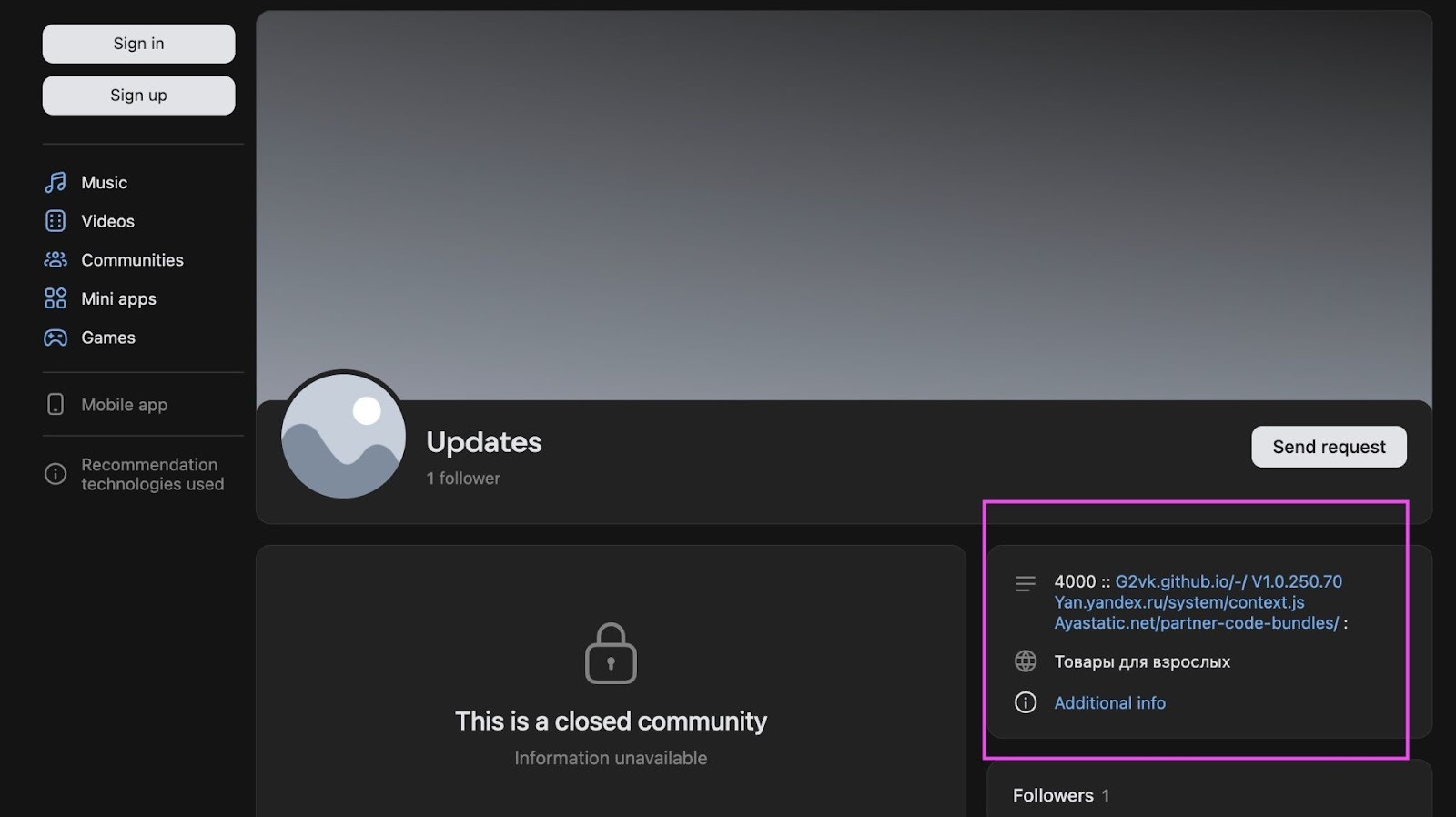
VKontakte uses CSRF tokens. But the malicious extensions had a massive advantage: they ran with the same privileges as your legitimate browsing. When you visited VKontakte while an extension was installed, the extension could intercept every response from VKontakte's servers, extract the CSRF tokens, and send them to the attacker's servers.
Once the attacker has a valid CSRF token, they can essentially impersonate you to VKontakte. They can make changes to your account, perform transactions, access private information. The token proves you're authenticated. The attacker has the token. The system has no way to distinguish between legitimate requests from you and fraudulent requests from the attacker.
The extensions made this even more dangerous by also extracting session cookies. These are the underlying authentication credentials that let you stay logged into a website. With both the session cookie and the CSRF token, an attacker has everything needed for complete account access.
But here's where it gets scarier: the extensions would reset account settings every 30 days. This is almost certainly an automated process running on the attacker's servers. The attacker sends requests to VKontakte (using the stolen credentials), requests your account settings, modifies anything the user might have changed (like two-factor authentication settings or account recovery options), and resets it back to what the attacker wants. The user's security improvements are automatically undone.
From a security perspective, this is brilliant and terrible. Brilliant because the attacker has figured out how to maintain persistent access even as the victim tries to secure their account. Terrible because the victim has no way to stop it. Changing your password? The attacker's credentials still work. Enabling two-factor authentication? The attacker resets it. Revoking application permissions? They get re-enabled automatically.
The only real solution is to completely remove the malicious extension and hope you've caught it before attackers have extracted too much value. But most users never realize their account is compromised. They don't know to check for malicious extensions. And by the time they do, the damage might already be done.

Payment Data Theft: From Subscriptions to Credit Card Fraud
Let's talk about what happened to people's money.
VKontakte offers various paid features. Users can buy gifts for other users (which can be monetized as a revenue stream for content creators). They can subscribe to premium features. They can donate to streamers. They can purchase in-game items. Every one of these transactions requires a payment method, typically a credit card.
The malicious extensions tracked when users engaged with these payment features. More specifically, the code would monitor for payment-related API calls and HTTP requests. When a user initiated a transaction, the extension would intercept that transaction and extract the payment data.
This is almost certainly not credit cards being stored directly. VKontakte uses payment processors, and the actual credit card data is sent through PCI-DSS compliant channels. But payment authorization flows often involve tokens, temporary identifiers, and sometimes last-four digits of credit cards. These can be valuable for fraud or for linking compromised accounts to real financial information.
The extension also implemented something researchers called a "donation tracker." The attacker's code would check if a user had recently made a payment or upgraded to premium features. If so, the extension could trigger additional malicious behavior. Maybe it would attempt to make additional unauthorized purchases. Maybe it would collect more detailed financial information. Maybe it would sell the account to another attacker because it's "proven to have money."
From the attacker's perspective, accounts that have successfully made payments are more valuable than accounts that haven't. They prove the user has a working payment method. They indicate the user is willing to spend money on the platform. They might even indicate the user has money available in their account.
The credit card theft combined with the account hijacking creates a perfect storm. The attacker has your account access (through the stolen credentials), your payment method information (through the payment data theft), and your personal information (available on your VKontakte profile). With all three, they can attempt fraud both on and off VKontakte.
One particularly insidious aspect of this attack is that victims might not notice the fraud immediately. VKontakte charges appear on credit card statements. If the attacker makes small fraudulent charges, users might not notice them among legitimate transactions. By the time they do, weeks or months might have passed. The attacker has already moved the money or hidden their tracks.
Users who did notice might assume their credit card information was stolen through a data breach or skimming attack. They probably wouldn't connect it to a browser extension they installed months ago. They'd cancel their card, but the damage would already be done.

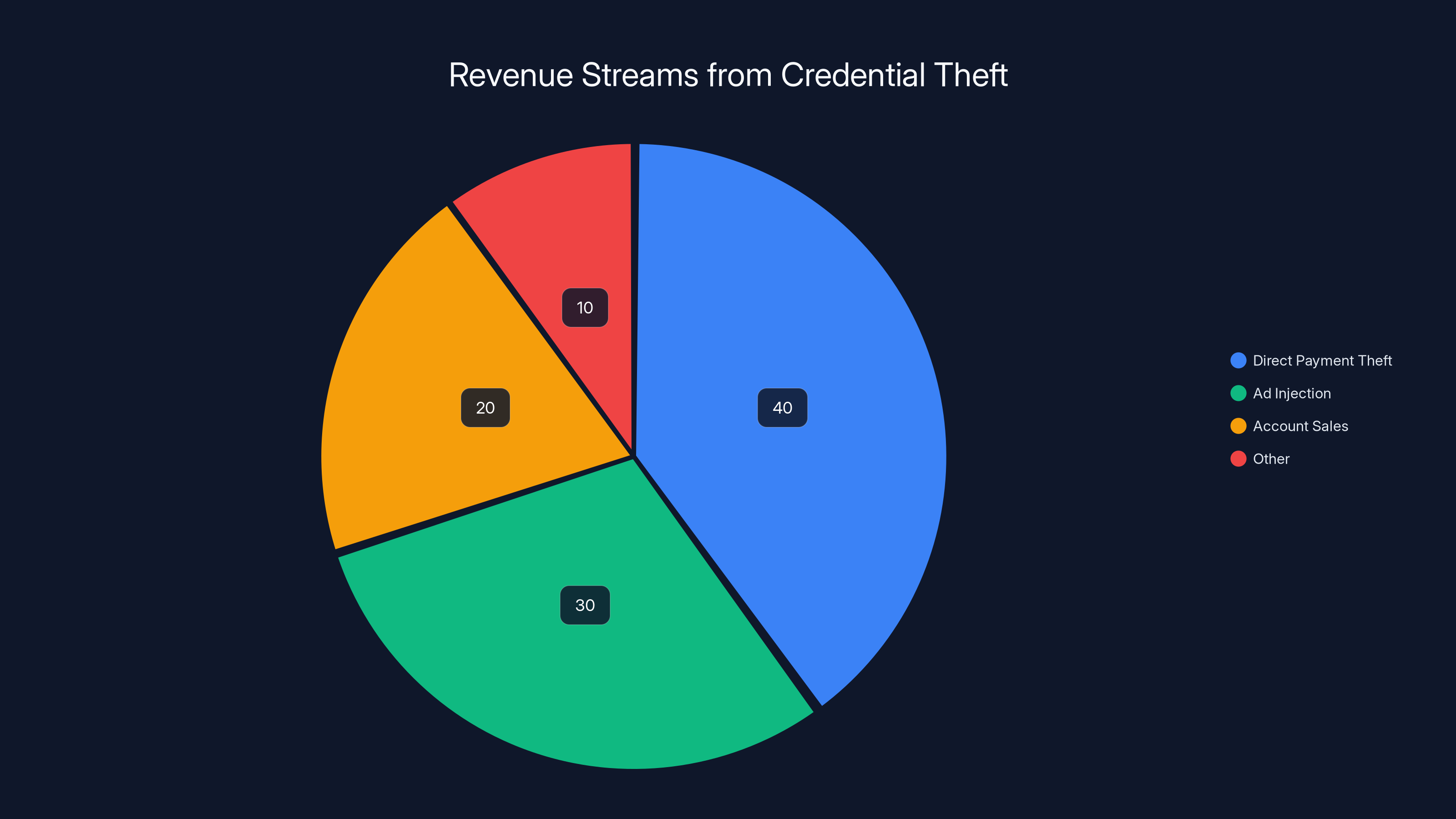
Estimated data shows that direct payment theft accounts for the largest share of revenue (40%), followed by ad injection (30%) and account sales (20%).
Geographic Targeting and Threat Actor Attribution
The campaign wasn't random. It was specifically designed for a particular audience.
Researchers found that victims were concentrated in Russian-speaking regions: Russia itself, Belarus, Ukraine, Kazakhstan, and other countries in the former Soviet Union. The extensions were served through the Russian version of the Chrome Web Store. The attacker's communications and code comments were in Russian. Everything about this campaign was tailored for Russian-speaking users.
Why? Partly because that's a massive market (over 260 million Russian speakers online). Partly because those regions represent lower cybercrime enforcement risk for the attacker. Partly because credit card fraud in those regions might be more profitable or easier to monetize.
The threat actor's GitHub alias was "2vk," which stands for "second VKontakte" (literally "second vk"). This suggests the attacker has history with VKontakte, whether as a legitimate user, security researcher, or previous attacker. The specific targeting of VKontakte combined with this alias suggests this isn't a generic malware author. This is someone who specifically wants to attack VKontakte and has chosen this platform as their primary target.
The campaign began in mid-2025 and was ongoing at the time of discovery. That's important because it means the threat was active for months. During those months, every new installation meant another compromised account. Every reset of account settings meant another victim losing control of their security measures. Every captured payment transaction meant another piece of financial data in the attacker's possession.
The fact that all five extensions were maintained by the same actor suggests this isn't opportunistic malware. This is a dedicated, focused campaign by someone with enough expertise to defeat Chrome's review process and sophisticated enough to implement multi-stage code injection and credential theft.
From a threat intelligence perspective, this tells us something important: when you see attackers targeting a specific platform, a specific region, and using specific aliases, you're looking at someone who has made this their business. This isn't a criminal-of-opportunity. This is an organized, focused threat actor who has decided that compromising VKontakte accounts is their primary revenue stream.
The Extension as an Entry Point: Browser Security Vulnerabilities
Why were browser extensions chosen as the attack vector?
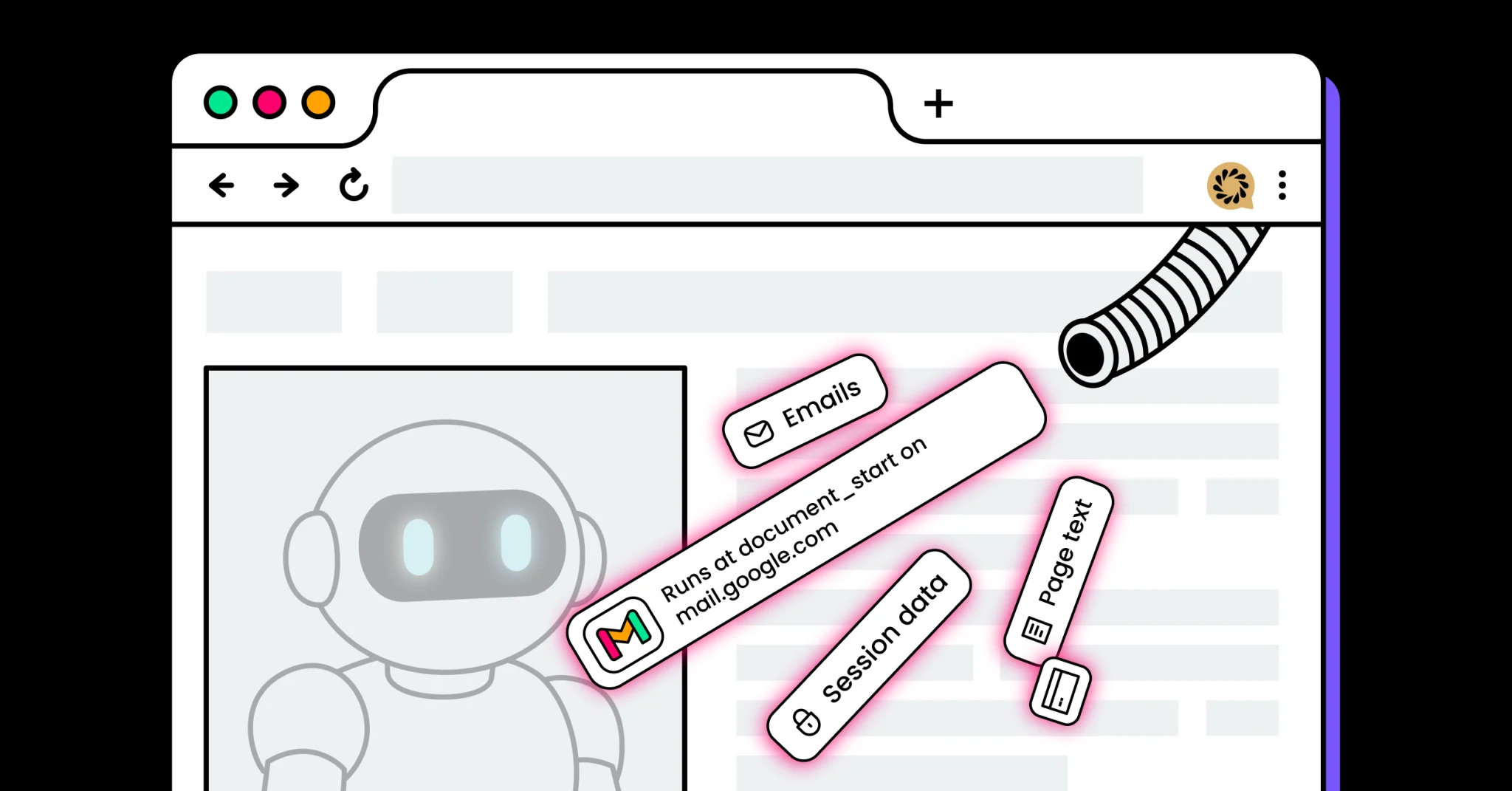
Browser extensions have a unique position in your security model. They're not sandboxed like regular websites. They have direct access to the pages you visit. They can intercept network requests and responses. They can read and modify your browsing data. They can access sensitive information like authentication tokens. In return, users grant them these permissions because, for legitimate extensions, these capabilities are necessary for the extension to function.
This permission model creates a trust boundary. Users assume that if an extension is on the official Chrome Web Store, it's safe. Users assume that Google has vetted it. Users assume it won't abuse its permissions. Those assumptions are reasonable for most extensions, but they're not guaranteed.
From an attacker's perspective, extensions are ideal because they solve several problems simultaneously. They have legitimate access to the data you care about. They're installed directly on your device, so they persist across browser sessions. They're updated from the attacker's servers, so the malicious behavior can change without user action. They're trusted by default, so users are less likely to scrutinize them.
A browser extension can do almost anything a sophisticated attacker wants, short of physical damage to your hardware. It can steal credentials, inject ads, redirect traffic, modify content, intercept communications, extract payment data. It can do all of this while maintaining the user's trust because it came from the official store.
Chrome has attempted to address this through various security improvements. The introduction of Manifest V3 was supposed to reduce the capability of extensions (particularly their ability to modify web content). But the rollout has been controversial and incomplete. Many users still use Manifest V2 extensions. Even Manifest V3 extensions, while more restricted, still have significant capabilities.
The fundamental problem is that there's a necessary tension between functionality and security. An extension that truly wanted to enhance VKontakte would need access to VKontakte's content. But that same access enables malicious behavior. You can't give an extension the permission to modify web content without also giving it the ability to modify web content in malicious ways.
Browser developers have recognized this and attempted to add additional controls: permission prompts, extension management dashboards, security warnings. But these are largely ineffective because most users don't understand what the permissions mean. When asked if an extension can "read and change all your data on the websites you visit," most people don't connect that to "this could steal your authentication tokens." They just see "yes" if they think the extension looks legitimate.

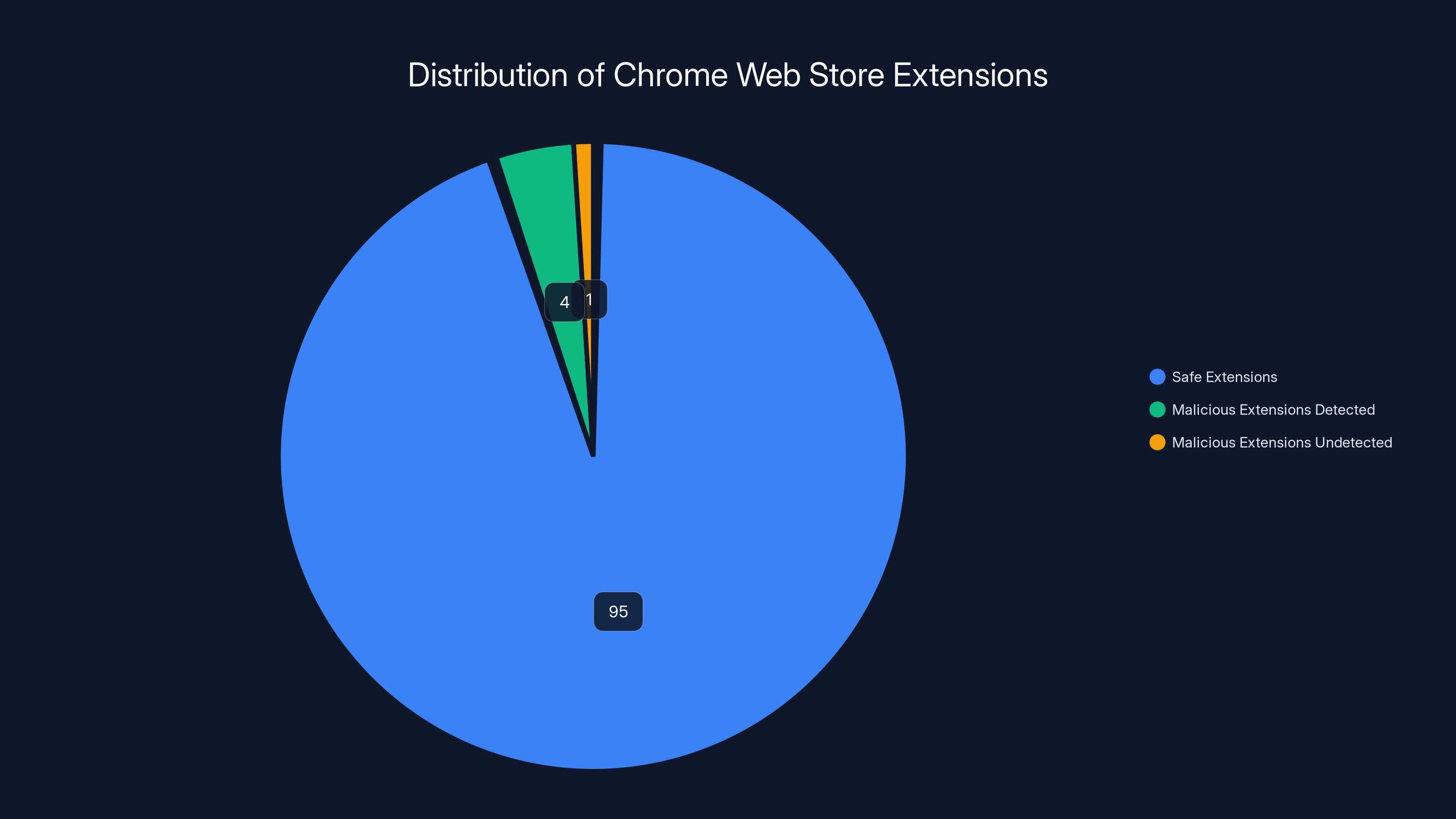
Estimated data suggests that while the majority of extensions are safe, a small percentage are malicious, with some evading detection. Estimated data.
Detection Challenges: Why This Attack Went Unnoticed for Months
The research team at Koi Security found these extensions while searching for Yandex advertising code. They happened to stumble upon them. This raises a critical question: why hadn't anyone else found them?
The answer involves several factors that made detection genuinely difficult.
First, the extensions had low profile. They didn't make your computer run slowly. They didn't consume massive amounts of bandwidth. They didn't make noticeable changes to the user interface (beyond their advertised theme changes). An average user's computer would run fine. Their browser would function normally. The malicious activity happened entirely against their account, not their device.
Second, most users don't check their account security logs. VKontakte, like most social networks, keeps logs of where your account has been accessed from and what actions have been taken. If you logged into your account from Moscow and Lagos on the same day, that's suspicious. But most users never check this. They don't know this information is available. They don't think to look for suspicious activity.
Third, the malicious behavior was distributed. The extensions didn't do everything themselves. Some handled credential theft. Some handled the ad injection. Some handled the auto-subscription. To detect the full scope of the attack, you'd need to connect these dots across five different extensions. That's exactly the kind of pattern detection that requires specialized security research.
Fourth, the attackers likely did some obfuscation. While the technical details weren't revealed, experienced threat actors know how to make their code harder to read. Variable names can be meaningless. The logic can be spread across multiple functions. The malicious payload can be encrypted and only decrypted at runtime. An extension review process that scans static code will miss this.
Finally, there's the sheer volume problem. Thousands of extensions are uploaded to the Chrome Web Store every day. Even with automated scanning, even with security researchers reviewing suspicious submissions, there's no way to manually verify every extension. Attackers know this. They know that if they can slip past the initial review, they have weeks or months of operation before they're likely caught. By then, the damage is done.
This is why Koi Security's discovery was significant. It took a dedicated security research team deliberately searching for suspicious patterns to find these extensions. Most companies aren't running that kind of analysis. Most users have no way to detect this level of compromise.
Security Implications: What This Means for Browser Extension Safety
This attack raises some uncomfortable questions about browser extension security broadly.
If five extensions could compromise half a million accounts, how many others are doing similar things right now? How many extensions on the Chrome Web Store are collecting data they shouldn't? How many have permissions they're not using for their stated purpose? How many are stealing credentials or payment information without detection?
We don't know. And that's the problem.
Secure browsing requires trusting your browser and the software it runs. But that trust is being betrayed repeatedly. In the past years, we've seen malicious extensions selling user data, injecting ads, hijacking search results, stealing credentials, and installing secondary malware. This isn't a new problem. It's a recurring problem that never seems to get solved.
Part of the issue is that extension security is fundamentally different from app security. When you download an app from the Apple App Store or Google Play Store, you're getting that app directly from the developer or through a trusted distributor. The app has a clear identity and a clear responsibility. If an app steals your data, you can identify the developer and take action.
Browser extensions are more anonymous. The same extension code could be uploaded by different people. Code could be modified after upload. Extensions could be sold from one developer to another. The provenance of extensions is murky in a way that apps aren't.
Another issue is permission creep. Extensions request broad permissions ("access all data on all websites") because narrower permissions are often insufficient for their stated purpose. But those broad permissions also enable malicious behavior. This creates a situation where almost any permission request seems reasonable in context.
The final issue is user awareness. Most users don't understand what extensions do or why they need particular permissions. They install extensions because they seem useful, without thinking about the security implications. Even if browsers displayed warnings, most users would click "Allow" anyway.
Solving this would require fundamental changes to how browser extensions work. More granular permissions. Better review processes. More transparency about what extensions are doing. Real-time monitoring of extension behavior. But all of these come with costs. More granular permissions make extensions harder to develop and use. Better review processes require resources. Transparency requires clear communication that many users won't read. Real-time monitoring has performance costs.
Until these changes happen, browser extension security will remain a weak point in the security model. And attackers will keep exploiting it.

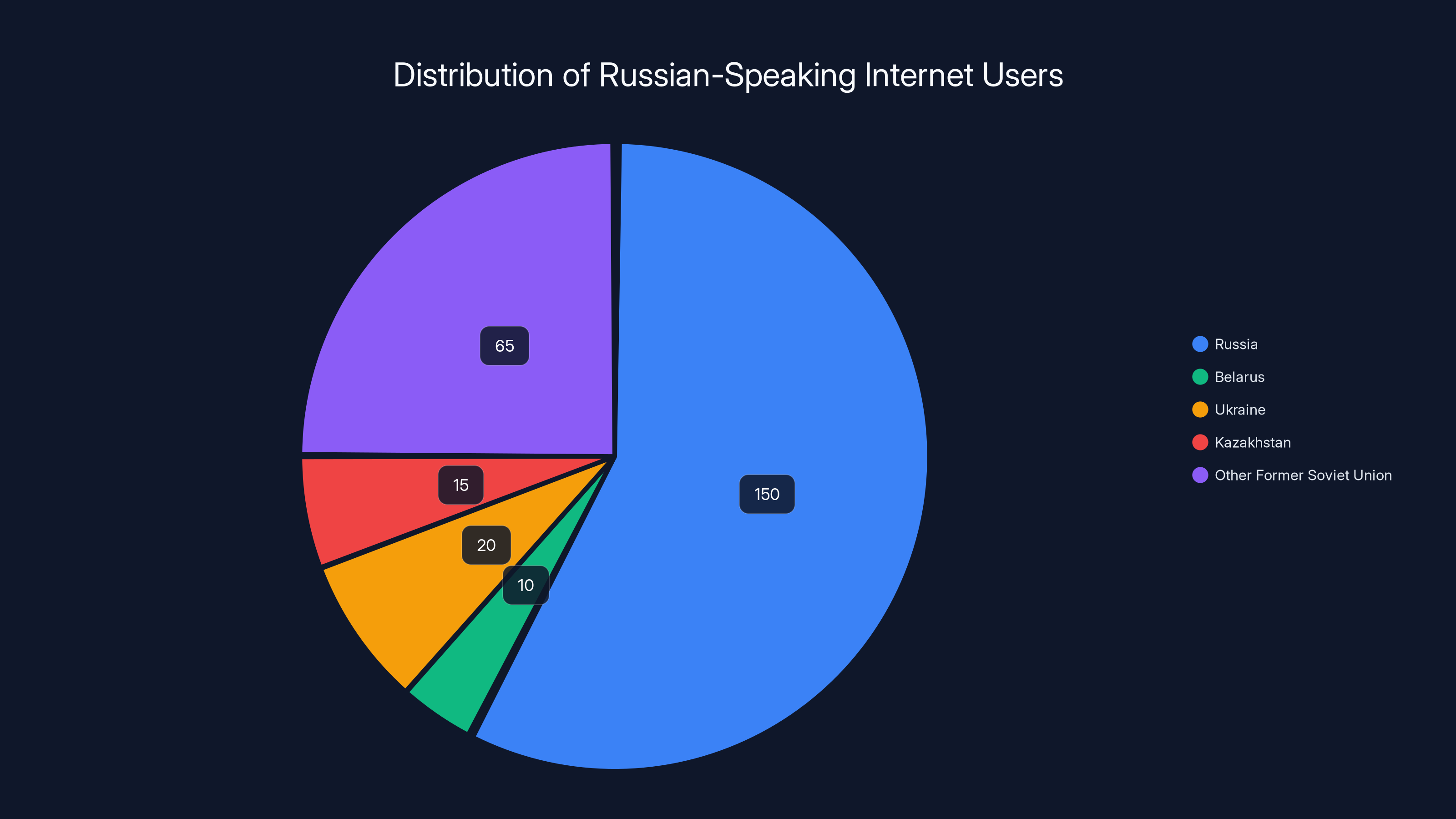
Estimated data shows Russia as the largest segment of Russian-speaking internet users, highlighting the strategic focus of the campaign on these regions.
The Credential Theft Infrastructure: How Stolen Access Is Monetized
Once an attacker has compromised an account, they need to actually extract value from it. That's where the monetization infrastructure comes in.
In this case, the attackers operated on multiple revenue streams simultaneously. The most obvious was direct payment theft. Intercept payment transactions, extract the credit card information, use it for fraud. This is straightforward criminal activity, but effective at scale.
The auto-subscription to the attacker's 1.4 million member group served multiple purposes. It created the perception of legitimacy (the attacker's group looked real and active because it had a million members). It created a captive audience for serving ads or distributing additional malware. It potentially gave the attacker a way to contact compromised users if they wanted to distribute something else.
The ad injection provided a more sustainable revenue stream. Every ad impression, every click, could generate a small amount of revenue. At 500,000 compromised accounts, serving ads 24/7, the numbers add up. If each compromised account sees even five cents worth of ads per day, that's
The CSRF token theft and password reset mechanism created a secondary market. Compromised accounts are valuable. Other cybercriminals might want to buy accounts with established payment methods. An attacker could sell accounts to credential harvesters, to account takeover specialists, or to other criminal operations.
The tracking of "donations" and payment status created targeting opportunities. Accounts with successful payment methods are more valuable. The attacker could prioritize those for additional attack. They could attempt larger fraudulent charges knowing the account was linked to a valid credit card. They could sell those accounts for more money.
What's important to understand is that this wasn't a smash-and-grab operation. This was a long-term revenue generation system. The attacker had built infrastructure to maintain persistent access, extract multiple revenue streams, and systematically exploit compromised accounts. This suggests they were planning to run this attack for months or years.
Remediation: What Victims Should Do
If you installed one of these extensions, what should you do?
First, remove the extension immediately. Go to chrome://extensions/, find any extension matching those names (the specific names weren't widely publicized for obvious reasons), and click "Remove."
Second, change your VKontakte password. From a secure device, log into VKontakte and change your password. Don't reuse the password you've changed it to elsewhere.
Third, review your account activity. Check VKontakte's security log (if available) to see where your account has been accessed from. Look for logins from cities or countries you've never visited. This is where the compromised credentials might have been used.
Fourth, check your linked accounts. If you've used VKontakte to sign into other services, you might need to unlink them or reset those accounts as well. Account takeover doesn't stop at VKontakte.
Fifth, review your payment methods. Check if any unauthorized charges have been made to your credit card. If you see anything suspicious, contact your bank immediately. In many cases, banks will refund fraudulent charges, but you need to report them quickly.
Sixth, enable two-factor authentication (if VKontakte offers it). This makes it much harder for someone to maintain access even if they have your password.
Seventh, consider credit monitoring. If your credit card information was stolen, fraudsters might attempt to open credit accounts in your name. Credit monitoring services can alert you if someone tries to take out new credit in your name.
The uncomfortable truth is that if your account was compromised for weeks or months, the damage might already be done. The attacker might have your credit card information, your personal data, and access to all your private messages. There's no way to undo that. You can only prevent future compromise and monitor for ongoing fraud.
Browser Security Best Practices: Reducing Your Risk
This attack highlights several security practices that actually matter.
Minimize extensions. Every extension you install increases your attack surface. Each extension is a potential entry point for malware. The best practice is to use as few extensions as possible. If your browser's built-in features can do the job, use those instead.
Review permissions carefully. When installing an extension, pay attention to what permissions it's requesting. If an extension that's supposedly a theme changer is asking for permission to "read and change all your data," that's suspicious. If the permissions don't match the extension's stated purpose, don't install it.
Use extension management tools. Some browser extensions exist specifically to monitor other extensions for suspicious behavior. While not perfect, they can catch obvious malware. Consider using one if you're going to install multiple extensions.
Keep your browser updated. Browser vendors release security patches regularly. Keeping your browser updated ensures you have the latest security improvements. This applies to Chrome, Firefox, Edge, Safari, and any other browser you use.
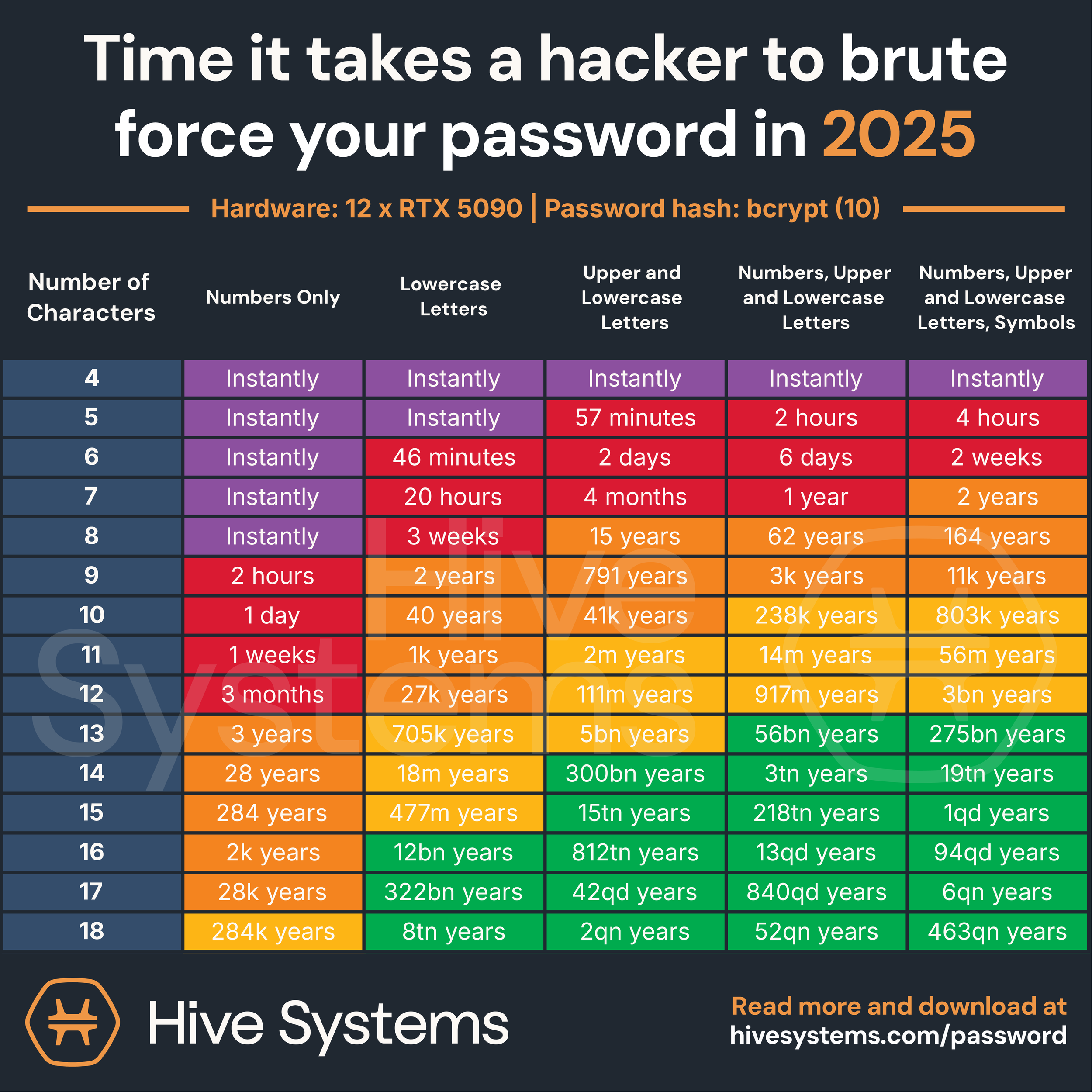
Use strong, unique passwords. If your password is compromised, a strong unique password limits the damage to that one account. If you reuse the same password across sites, one compromise becomes many.
Enable two-factor authentication. This makes account takeover much harder. Even if your password and authentication tokens are stolen, two-factor authentication creates an additional barrier.
Monitor your accounts. Periodically check your account security logs. Look for suspicious logins or unauthorized changes. The faster you detect a compromise, the faster you can respond.
Be skeptical of extensions. If an extension seems too good to be true, it probably is. Legitimate extensions are developed by teams with reputations to protect. Unknown extensions from unverified developers are higher risk.
These aren't foolproof protections. Sophisticated attackers can bypass all of them. But they raise the bar significantly, making you a less attractive target.
The Broader Threat Landscape: Related Attacks and Trends
This VKontakte hijacking isn't isolated. It's part of a larger trend of malicious browser extensions being used as attack vectors.
In recent years, security researchers have documented multiple campaigns using similar techniques. Malicious extensions stealing cryptocurrency wallet credentials. Extensions hijacking search traffic and injecting ads. Extensions capturing banking credentials. Extensions serving as entry points for ransomware distribution. The pattern is consistent: attackers develop convincing-looking extensions, get them into official app stores, and exploit the users who install them.
What's changing is the sophistication level. Older malware extensions were often crude and obvious. They'd crash your browser or consume massive resources. Newer malware extensions are deliberately designed to avoid detection. They implement proper error handling. They throttle their resource consumption to avoid suspicion. They obfuscate their code and hide their malicious behavior behind legitimate-looking features.
The VKontakte campaign represents a maturation of this attack type. The attackers didn't just steal credentials. They implemented multiple revenue streams. They designed resilient infrastructure to maintain access even as users tried to secure their accounts. They targeted a specific platform and region where enforcement was likely to be weak.
This level of sophistication suggests that browser extension attacks are becoming a professional operation. This isn't someone experimenting with malware. This is organized crime treating VKontakte hijacking as a business.
We're also seeing convergence between different attack types. Malicious extensions can be used to spread ransomware. They can be used to steal credentials for corporate accounts, leading to broader breaches. They can be used as part of sophisticated supply chain attacks. The extension becomes the entry point, and from there, attackers can escalate to more valuable targets.
Security vendors have responded by improving their detection and monitoring of suspicious extensions. But they're playing catch-up. The number of extensions being uploaded to app stores continues to grow faster than the ability to review them.
The Role of Security Research: How Koi Security Found This
You might be wondering how Koi Security discovered this campaign. What made them stumble upon these five extensions among the thousands in the Chrome Web Store?
They were searching for Yandex advertising code. This suggests they were tracking ad injection campaigns or researching how malicious actors were monetizing compromised accounts. While searching for suspicious advertising scripts, they found several extensions that were injecting Yandex ads into pages where they shouldn't appear.
Once they found one suspicious extension, they investigated further. They looked for connections between extensions. They found that multiple extensions were exhibiting similar behavior patterns. They traced those patterns back to a common developer. They discovered that all five extensions were maintained by the same threat actor.
This discovery process highlights how security research actually works. Researchers aren't sitting in a room waiting for attackers to broadcast their location. They're actively investigating the ecosystem, looking for suspicious patterns, making connections between seemingly unrelated pieces of data.
Koi Security's work was important, but it also illustrates a broader point: security researchers are essentially performing triage on a never-ending stream of malware. They can't investigate every extension. They can't prevent every attack. They can only identify threats after they've already been deployed. By the time Koi Security found these extensions, 500,000 accounts were already compromised.
This is why prevention is always better than detection. It's why the Chrome Web Store's review process matters. It's why maintaining tight control over extension permissions is critical. Once a malicious extension is in the wild, detection is playing catch-up.
Platform Response: What Google and VKontakte Did
Once the malicious extensions were discovered, the response was relatively swift.
Google removed at least one of the extensions from the Chrome Web Store. This prevents new installations, but doesn't help users who already have the extension installed. Google likely also disabled or revoked the developer accounts associated with the extensions, preventing that threat actor from uploading new extensions under the same identities.
VKontakte presumably released security updates and reset the accounts that had been compromised. They might have forced password resets. They might have revoked sessions. They might have monitored for suspicious activity in the affected accounts.
But here's what's not clear: Did Google notify users who had installed the extensions? Did VKontakte contact affected users? Were victims given clear guidance on what to do? The public statements from both companies were relatively sparse. The technical details of the attack were pieced together through security research, not through official statements.
This lack of transparency is a recurring problem with major security incidents. Companies are often reluctant to acknowledge breaches because they create liability and reputational damage. But users need this information to protect themselves. There's a fundamental tension between the company's interest in minimizing publicity and users' interest in being informed.
From a policy perspective, this raises interesting questions. Should platform operators (like Google) be required to notify users when malicious software is discovered? Should there be mandatory disclosure timelines? Should there be penalties for slow response? Different jurisdictions have different approaches, but there's no global standard.
The European Union's regulations are stricter than most. The General Data Protection Regulation (GDPR) requires notification of data breaches within 72 hours. The Digital Services Act is pushing for more transparency from large platforms. But the United States, Russia, and many other regions have weaker requirements.
This regulatory fragmentation means that companies often use the strictest requirement as their standard. If they're going to notify users anyway (for GDPR compliance), they might as well notify everyone. But without that pressure, they often minimize disclosure.
Long-Term Solutions: What Needs to Change
We can't fix browser extension security with Band-Aids. The problem is structural.
App store review processes need to be fundamentally redesigned. The current model of human reviewers skimming code is insufficient. We need continuous monitoring of extensions even after they're published. We need behavioral analysis that catches malicious activity in real time. We need better tools for detecting obfuscated or hidden malicious code.
Permissions need to be more granular. Instead of "access all data on all websites," extensions should request specific permissions. "Access VKontakte.com" instead of "access all websites." "Read page content" instead of "read and modify page content." "Monitor network requests" instead of "monitor all network requests." More granular permissions give users meaningful choice.
Browser developers need better extension sandboxing. Extensions should run in an isolated environment with limited capabilities. If an extension wants to modify web content, it should only be able to modify the specific types of content it needs to modify. This is what Manifest V3 is attempting, but the implementation needs to be more robust.
Users need better education. Most people don't understand what browser permissions mean or what extensions can do. Browser vendors need to invest in education, making it clear why extension security matters and what users should be cautious about.
Incident response needs to be faster and more transparent. When malicious extensions are discovered, users should be notified immediately. Browsers should provide easy ways to identify if you have the malicious extension. Platforms should provide clear remediation instructions.
Threat intelligence needs to be shared more openly. Security researchers discovering malware should have easy ways to report it to browser vendors and to the broader security community. Current reporting mechanisms are often slow and unclear.
Regulatory frameworks need to catch up. Right now, there are few legal consequences for publishing malware in an app store. Making it illegal, with teeth behind the law, would at least raise the legal risk for attackers.
Implementing all of these would be expensive and complicated. But continuing with the current approach guarantees more incidents like this. Browser extension security has been a known weak point for years. At some point, the cost of fixing it becomes lower than the cost of continued breaches.
FAQ
What exactly were these malicious Chrome extensions doing?
These five extensions used multi-stage code injection to auto-subscribe users to the attacker's VK groups (which grew to 1.4 million members), manipulate CSRF tokens to bypass VKontakte's security protections, reset account settings every 30 days to override user changes, inject Yandex advertising scripts for direct revenue, and track when users made payments to capture credit card information. Essentially, they provided the attacker complete persistent control over compromised accounts.
How many people were affected by this VKontakte hijacking?
Over 500,000 people installed the malicious extensions from the official Chrome Web Store. All of these installations resulted in account compromise. Additionally, attackers may have sold access to compromised accounts to other cybercriminals, potentially multiplying the impact beyond the initial 500,000 victims.
How did these extensions get past Google's Chrome Web Store review?
The extensions likely used evasion techniques common in sophisticated malware, such as delayed malicious behavior activation after publication, encrypted or obfuscated code that avoided static analysis detection, dynamic code injection from attacker servers, and fingerprinting of the review environment to behave differently during review versus real-world use. Google's review process, while comprehensive, cannot catch every sophisticated evasion technique.
What payment information could be stolen from VKontakte accounts?
The extensions tracked when users attempted to purchase gifts, subscribe to premium features, or make donations. When these transactions occurred, the extensions could capture payment authorization tokens, credit card data, temporary payment identifiers, and sometimes the last four digits of credit cards. This information could be used for direct fraud or sold to other criminals.
Should I stop using browser extensions entirely?
Not necessarily, but you should significantly minimize their use. Every extension increases your attack surface. The best practice is to use only extensions from developers you trust, that serve a critical function, and that request minimal permissions. Many features that users install extensions for (ad blocking, password management, dark mode) are increasingly built into browsers directly.
How can I tell if I have a malicious extension installed?
Google removed at least one of the identified extensions, so checking your installed extensions for the specific malicious ones wouldn't work (because you'd only find them if they're still published). Instead, review all your extensions in chrome://extensions/ and ask: Do I recognize this developer? Do I actually use this extension? Do the permissions match its purpose? If you can't answer yes to all three, remove it. Also check your VKontakte account security log for suspicious login locations or unauthorized changes.
What's the difference between this attack and a data breach?
A data breach typically means an attacker accessed a platform's database and stole user information. In this attack, the attacker gained account access by hijacking user devices (through the malicious extension) and using that device-level access to impersonate users to VKontakte. The attacker didn't need to compromise VKontakte's systems directly. They compromised the users' devices instead, which is a different but equally serious problem.
Can I fix my account if I had one of these extensions installed?
Yes, but the damage may already be done. Remove the extension immediately, change your password from a secure device, review your account activity log for suspicious actions, check your credit card for unauthorized charges, and enable two-factor authentication. Monitor your account for the next several months. If your credit card information was stolen, contact your bank and consider credit monitoring. If the compromised account was used to sign into other services, reset those accounts too.
Are other social networks vulnerable to similar attacks?
Absolutely. Any platform with a payment ecosystem, user-to-user messaging, and a sufficiently large user base is attractive to attackers. Facebook, Instagram, Twitter, Discord, and many others have faced similar extension-based attacks. This is a systematic vulnerability in how browser extensions work, not a VKontakte-specific problem.
What should platform operators do to prevent this?
Platforms can improve by detecting unusual account activity patterns (logins from multiple countries in short timeframes, rapid credential changes, unusual payment transactions), requiring more sophisticated authentication methods (like mandatory two-factor authentication for accounts with payment methods), and actively monitoring for credential theft (by detecting when authentication tokens are being used outside normal patterns). They should also coordinate with browser vendors on blocking malicious extensions.
The VKontakte hijacking demonstrates something that should be obvious but often isn't: your device is a critical part of your security model. No matter how secure a platform is, if the software on your device has been compromised, the attackers can do whatever they want. Your browser extensions are part of your device's security boundary. Treat them as seriously as you'd treat software from any other source.
This attack will be studied in security courses for years. It's a masterclass in how to systematically compromise accounts at scale. It demonstrates the limitations of app store review processes. It shows how sophisticated attackers have become at evading detection. And most importantly, it shows why browser extension security matters.
The practical takeaway: audit your extensions this week. Remove anything you don't actively use. For the ones you keep, research the developers. Check what permissions they're asking for. Enable two-factor authentication on important accounts. Monitor your account activity logs. Don't trust that platforms or browsers have your security completely covered. Because half a million people learned the hard way that sometimes they don't.
Key Takeaways
- Five malicious Chrome extensions hijacked over 500,000 VKontakte accounts through multi-stage code injection and credential theft, maintained by a single threat actor using the GitHub alias '2vk'
- Attackers manipulated CSRF tokens to bypass security, reset account settings every 30 days, stole payment data, auto-subscribed users to a 1.4 million member group, and injected ads for revenue generation
- The campaign went undetected for months because malicious extensions avoid obvious system impact, users don't monitor account activity logs, and detection requires specialized security research
- Browser extension security is structurally weak because of necessary permissions, insufficient review processes, rapid upload volume, and limited user understanding of security implications
- Mitigation requires immediate removal of malicious extensions, password changes, account activity review, credit card monitoring, and long-term investment in better extension permissions, continuous monitoring, and regulatory frameworks
Related Articles
- Fake Chrome AI Extensions: How 300K+ Users Got Compromised [2025]
- Tenga Data Breach 2025: How a Phishing Email Exposed Customer Data
- Japanese Hotel Chain Hit by Ransomware: What You Need to Know [2025]
- EU Parliament Bans AI on Government Devices: Security Concerns [2025]
- Machine Credentials: The Ransomware Playbook Gap [2025]
- Chrome Zero-Day CVE-2026-2441: Critical Security Update Guide [2025]
![Chrome Extensions Hijacking 500K VKontakte Accounts [2025]](https://tryrunable.com/blog/chrome-extensions-hijacking-500k-vkontakte-accounts-2025/image-1-1771343044875.jpg)



