The Ivanti VPN Breach: Everything You Need to Know About the Chinese Hacking Campaign
Back in February 2021, Ivanti discovered something that should've triggered alarm bells across the entire enterprise security industry. Chinese hackers didn't just slip through one door. They'd installed a secret backdoor in the VPN software that thousands of companies relied on to keep their networks safe. Then they walked through it to compromise not just Ivanti's subsidiary, but 119 other organizations.
That's not a small number. That's not a contained incident. That's a systemic failure that reveals how private equity, cost-cutting, and institutional knowledge gaps can turn a critical infrastructure vendor into a liability.
This breach sat quietly for years before Bloomberg reported the details in 2026. And what the reporting exposed was worse than a simple exploit. It showed a company that had been gutted by layoffs, stripped of security expertise, and left vulnerable to determined adversaries who were already inside the building.
If you're an enterprise relying on VPN technology, or if you're responsible for network security, you need to understand what happened here. Because Ivanti's story isn't unique. It's a warning sign that's being repeated across the industry.
What Makes This Breach Different
Most breaches follow a predictable pattern. Attacker finds vulnerability. Attacker exploits it. Company patches it. Security teams move on. But the Ivanti breach was different in almost every way.
First, the attackers didn't just find a vulnerability. They planted a backdoor directly into the VPN appliance firmware. A backdoor is infrastructure. It's persistence. It's the difference between a burglar breaking a window and someone handing out copies of your front door key to their friends.
Second, the breach wasn't discovered by Ivanti. It was discovered by Mandiant, the incident response firm now owned by Google. Mandiant found evidence that hackers had already been inside Ivanti's subsidiary network and had pivoted from there into 119 other victim organizations. That's not a breach of one company. That's a supply chain compromise that affected an entire ecosystem.
Third, and most damning, the breach happened in February 2021, but the full scope wasn't revealed until 2026. Five years of silence. Five years where other companies didn't know their VPN traffic might be compromised. Five years where the attackers maintained potential access.
The timeline alone tells you something went catastrophically wrong not just with security, but with transparency and incident response.
Understanding Pulse Secure and Why This Matters
Ivanti acquired Pulse Secure in 2020, right before this breach happened. Pulse Secure made VPN appliances, which are essentially the gatekeepers to corporate networks. When you work from home and connect to your company's network through a VPN, you're often connecting through infrastructure that Pulse Secure built.
Think about what that means. Your VPN appliance sees all your traffic. It sees when you log in, what systems you access, what data you move. For attackers, compromising a VPN appliance is like compromising the security guard at the front desk. They're positioned perfectly to monitor, intercept, and redirect anything they want.
Pulse Secure served government agencies and military contractors. These aren't small businesses. These are organizations that handle classified information and critical infrastructure. When Chinese hackers got access to their networks through a backdoored VPN, the implications were staggering.
Mandiant found evidence that the hackers had exploited the backdoor to breach European and U.S. military contractors. Military contractors. That should've been treated as a national security incident from day one.
The Private Equity Connection: How Cost-Cutting Killed Security
Here's where the Ivanti story gets infuriating. The breach didn't happen because Pulse Secure was incompetent. It happened because private equity bought Ivanti and immediately decided that security expertise wasn't worth paying for.
Clearlake Capital acquired Ivanti in 2017. Private equity firms buy companies to extract value, and value extraction at software companies means cutting costs. People are the biggest cost. So starting around 2022, Ivanti laid off significant numbers of employees, particularly those with deep institutional knowledge of the company's products and their security architecture.
Let that sink in. Clearlake took over a company that owned critical VPN infrastructure used by governments and military contractors. Then, in the exact period when cybersecurity threats were accelerating, they decided to cut the security teams.
This wasn't unique to Ivanti. Citrix, another major remote access vendor, went through the same playbook. Elliott Investment Management and Vista Equity Partners bought Citrix in 2022. Within months, massive layoffs hit the security and engineering teams. Now Citrix is dealing with the same cascade of security vulnerabilities and critical flaws that Ivanti is.
Private equity doesn't think long-term about security. Private equity thinks about the exit. How do we cut costs today to show higher margins on the balance sheet for the sale or refinance? Never mind that you're cutting the engineers who understand how your VPN handles encryption. Never mind that you're laying off the security architects who designed the threat model.
When you cut the people who understand your product deeply, your product becomes less secure. It's not complicated. It's cause and effect.
The Backdoor: How Did It Get There?
This is the question that keeps security researchers up at night. A backdoor doesn't appear by accident. Someone put it there. The question is whether it was intentional or whether it was a supply chain compromise at a lower level.
Bloomberg's reporting suggests the backdoor was planted as an attack vector, not as intentional code left by Pulse Secure developers. But how do attackers plant a backdoor in firmware that's supposed to be signed and verified?
There are several possibilities. First, the attackers could have compromised Pulse Secure's build infrastructure or firmware signing process. If you can get access to where the firmware is compiled and packaged, you can inject code before it's even signed. This is terrifying because every copy of the software shipped to customers would contain the backdoor from day one.
Second, the attackers could have exploited an existing zero-day vulnerability, used it to gain initial access to Pulse Secure's network, and then added the backdoor through a supply chain compromise. Once inside, they modify the source code or the compiled binaries to include persistent access.
Third, the backdoor could have come through a third-party dependency or library. Modern software doesn't exist in isolation. It's built on frameworks, libraries, and open-source components. If any of those got compromised, the backdoor travels downstream to every product that depends on it.
What's clear is that the backdoor existed, it worked, and it allowed attackers to maintain access to Pulse Secure's network and pivot to customer networks. The mechanism matters less than the fact that once the attackers were in, they had persistence.
The 119 Organizations: Scale of the Compromise
One hundred nineteen organizations. That's not a number that appears in press releases. It appeared in Mandiant's investigation and in Bloomberg's reporting. But let's think about what that number represents.
If 119 organizations were compromised through Pulse Secure's VPN, and if some of those were military contractors, the geopolitical implications are enormous. Chinese intelligence services weren't just stealing data from one company. They were running a systematic espionage operation against U.S. and European defense infrastructure.
Mandiant is Google's incident response and threat intelligence team. When they tell you that European and U.S. military contractors were compromised through a backdoored VPN, they're not guessing. They've seen the forensic evidence. They've traced the attacker activity. They've found the exfiltrated data.
But here's what's frustrating: we don't know the full list. We don't know which 119 organizations were hit. Ivanti and the organizations themselves have kept that information classified or confidential. That's understandable for national security reasons, but it also means every other organization using the same VPN doesn't know if they were compromised.
If you were using Pulse Secure VPN in 2021, you have to assume you might have been compromised. You have to hunt for indicators of compromise in your logs. You have to assume the attackers had full visibility into your network traffic. This is the nightmare scenario for enterprise security teams.
CISA's Emergency Disconnect Order: The System Breaks
By early 2024, Ivanti had disclosed multiple critical vulnerabilities in its VPN products. The Department of Homeland Security's Cybersecurity and Infrastructure Security Agency (CISA) took the unusual step of ordering all federal agencies to disconnect Ivanti VPN appliances within two days.
Two days. That's an emergency declaration. That's a sign that the vulnerabilities were being actively exploited and that the risk was imminent enough to justify disrupting all federal agency remote access.
This wasn't the first time Ivanti VPN products had been the source of a major incident. In 2020, before the Chinese backdoor breach, there was a major vulnerability in Ivanti's Connect Secure product. Then, after the 2024 CISA order, Ivanti warned customers about yet another critical flaw being exploited in the wild.
Pattern recognition is important here. One vulnerability is a mistake. Two vulnerabilities is bad luck. Three major incidents in four years is a systemic problem with how the product is being developed, maintained, and secured.
When CISA issues an emergency disconnect order, it means they've done the math and decided that the risk of continuing to use the product is higher than the disruption of disconnecting it. For federal agencies, that's a massive decision. Remote access is critical infrastructure. Telling federal employees they can't work from home for 48 hours while they rip out VPN infrastructure is a serious action.
The fact that CISA felt compelled to do it tells you that Ivanti had lost the confidence of the U.S. government. Once you lose that trust, it's extraordinarily hard to get it back.
The Supply Chain Compromise Problem: Why One Backdoor Affected So Many
The Ivanti breach is a textbook example of supply chain compromise. One vendor's security failure cascades across hundreds of customer organizations. Understanding how this happens is critical for anyone managing enterprise security.
When you deploy a third-party VPN appliance, you're trusting that vendor in several ways. First, you're trusting that the hardware wasn't compromised at the manufacturing stage. Second, you're trusting that the firmware is authentic and hasn't been modified. Third, you're trusting that the vendor will promptly inform you of security issues and provide patches.
The Ivanti breach broke all three of those trust relationships simultaneously. The firmware that shipped from Pulse Secure contained a backdoor that allowed attackers to persist on customer networks. Customers didn't even know it was there. They deployed the VPN, configured it, and went about their business thinking they were secure.
Meanwhile, attackers maintained persistent access. They could monitor network traffic, capture credentials, identify valuable targets, and exfiltrate data. All while the supposed security perimeter kept out legitimate threats.
This is the fundamental problem with supply chain compromises. The attacker doesn't need to break into 119 organizations separately. They break into one vendor, modify the product, and when customers deploy the compromised product, they're already compromised.
In cryptography, there's a concept called the "weakest link." Supply chain security works the same way. Your security posture is only as strong as your least secure vendor. If your VPN vendor gets compromised, all the other security controls you've implemented become much less effective.
The Clearlake Connection: Private Equity and Security
Clearlake Capital's acquisition of Ivanti in 2017 should've been a moment to invest in security. Instead, it became a moment to extract value.
After the 2021 breach, Ivanti had years to strengthen its security posture. By 2024, they should've been the most security-focused, security-conscious VPN vendor in the world. Instead, they were disclosing multiple critical vulnerabilities and getting emergency disconnect orders from CISA.
The pattern suggests that Clearlake's management of Ivanti prioritized near-term financial performance over long-term security investments. You can't see security on a balance sheet. You can see headcount reduction. You can see cost savings. You can see improved margins.
But those cost savings come with hidden costs. Every engineer you lay off is expertise you lose. Every security team you reduce is a line of defense you've weakened. Every infrastructure investment you defer is a problem you're pushing to the future.
Private equity has a role to play in the software industry. But when private equity controls companies that provide critical infrastructure for national defense, the incentive structures become misaligned with public safety.
A similar story played out with Citrix. After Elliott Investment Management and Vista Equity Partners took control, they reduced headcount significantly. Now Citrix is dealing with a cascade of security problems in its remote access products. The pattern is consistent across multiple vendors.
Mandiant's Discovery: How We Found Out
Mandiant, the incident response and threat intelligence firm acquired by Google in 2022, was the organization that actually discovered the full scope of the Ivanti compromise. This raises an interesting question: how long would this breach have remained hidden if Mandiant hadn't been investigating something else?
Mandiant was likely brought in to investigate a specific intrusion. They found evidence of the attackers' activity in a victim organization's network. As part of the investigation, they traced the attack back to its entry point and identified the Pulse Secure VPN as the initial compromise vector. Then they realized the VPN itself had been compromised at a deeper level.
This is how many supply chain compromises are discovered. You're investigating one breach and realize the root cause goes much deeper. You're trying to understand how attackers got in, and you discover they came in through infrastructure you thought was secure.
Mandiant's investigation was technically sophisticated. They would have had to reverse engineer the VPN firmware, identify the backdoor code, understand its capabilities, and then trace which other organizations had been compromised through the same backdoor. That's not trivial work.
The fact that this investigation happened at all, and that the results were eventually shared with Bloomberg, is fortunate. But how many other backdoors exist in enterprise infrastructure that haven't been discovered yet? How many VPN vendors, firewall manufacturers, and networking appliance makers have compromised firmware sitting in customer data centers right now?
The Military Contractor Angle: Why This Matters Beyond Business
The breach of European and U.S. military contractors through a backdoored VPN is a national security issue. Military contractors develop weapons systems, design defense infrastructure, and handle classified information. Chinese intelligence services accessing these networks through a compromised VPN isn't industrial espionage. It's a potential threat to national security.
The fact that this information sat for years before being reported raises questions about how these incidents are handled. When does a cybersecurity breach become a matter of national security interest? When should the public be informed? How do you balance transparency with operational security?
Military contractors are supposed to follow strict security protocols. They're supposed to conduct security audits, implement defense-in-depth strategies, and assume that sophisticated adversaries will eventually target them. But if the VPN they're using has a backdoor installed by the manufacturer, even the best security practices can be circumvented.
This highlights a critical gap in how enterprise security is evaluated. Security audits typically focus on how a product is implemented and configured. They don't usually assume that the product itself has been compromised at the supply chain level. You're trusting that the vendor has done their job correctly. When that trust is violated, all bets are off.
The Timing Problem: Five Years of Silence
The breach happened in February 2021. The public reporting came in 2026. That's a five-year gap between when Ivanti discovered the breach and when details became public.
Why the delay? Part of it was likely due to law enforcement investigations. The FBI and intelligence agencies probably asked Ivanti to keep quiet while they investigated the attackers and assessed the damage. Part of it may have been litigation or regulatory processes. Part of it may have been damage control on Ivanti's part.
But five years is a long time. In that time, the attackers could have pivoted to other attacks. They could have sold the information they stole. They could have used the access to identify even more valuable targets. Defenders didn't have the information they needed to hunt for compromises in their own networks.
This timing issue is a fundamental problem with how data breaches are handled in the U.S. There's often an incentive for companies to delay disclosure while they manage the public relations fallout. But that delay comes at a cost to other potential victims.
Europe has addressed this with GDPR, which requires notification within 72 hours. The notification isn't always detailed, but the existence of the incident becomes public quickly. The U.S. has similar requirements in various state laws, but there are often exemptions for law enforcement investigations or national security concerns.
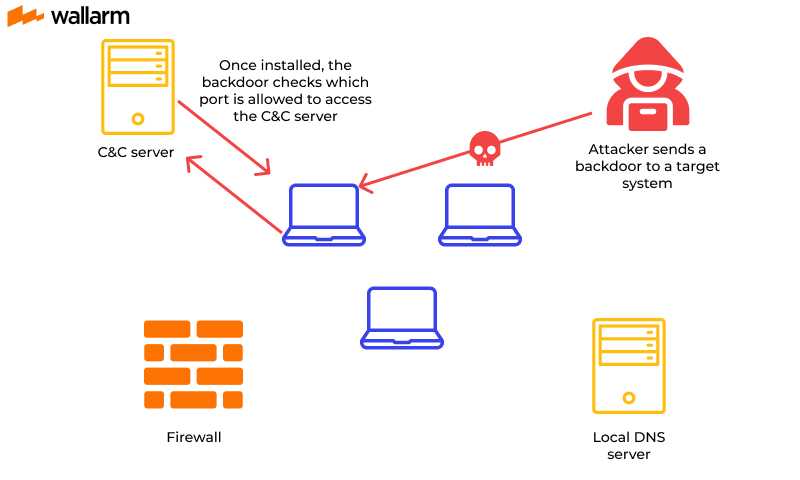
Technical Deep Dive: How VPN Backdoors Work
Understanding how a VPN backdoor actually functions is important for security teams trying to detect similar compromises.
A VPN appliance is essentially a specialized computer running security software. It handles encryption and decryption of all traffic flowing between remote users and the corporate network. It authenticates users, validates certificates, and enforces policies.
If attackers can install a backdoor in the VPN firmware, they can intercept all of that traffic before it's encrypted or after it's decrypted. They can see your usernames and passwords. They can see the data flowing through your network. They can monitor administrative activity.
But a sophisticated backdoor does more than just monitor. It can also proxy connections, allowing attackers to maintain access even if the original entry point gets patched. It can selectively allow or deny traffic. It can log activity for later review. It can communicate back to command and control infrastructure over encrypted channels that blend in with normal VPN traffic.
Detecting such a backdoor requires examining the firmware itself. Security researchers would need to:
- Extract the firmware from the appliance
- Disassemble or decompile the binary code
- Identify suspicious functions or behaviors
- Trace how those functions interact with network traffic
- Compare against known legitimate firmware versions
This is specialized work that requires deep technical expertise. Most enterprise security teams don't have the capability to do firmware analysis. They rely on the vendor to tell them when something is wrong, and they rely on IDS/IPS systems to detect suspicious network behavior.
Both of those defenses failed in the Ivanti case. Ivanti didn't tell customers about the backdoor for years. And the backdoor was sophisticated enough that it didn't trigger typical network-based detection systems.
Detection and Response: What Security Teams Should Have Done
If you were running Pulse Secure VPN in 2021, and if you didn't know about the backdoor, what would have helped you detect it?
Network-based detection would have looked for unusual patterns in VPN traffic. If attackers were exfiltrating large volumes of data, packet analyzers might have caught it. But sophisticated attackers don't exfiltrate terabytes of data. They steal incrementally. They grab the most valuable information and move on.
Host-based detection on the VPN appliance itself could have caught unusual processes or network connections. But if the backdoor is running at the firmware level, traditional host-based detection tools might not even execute. The firmware has more privileges than any application running on top of it.
Log analysis could have revealed suspicious administrative activity. If attackers logged in through the VPN and then created new user accounts or modified firewall rules, those actions would appear in logs. But again, if the attacker had firmware-level access, they might have been able to suppress or modify those logs.
The real protection would have been firmware integrity checking. Vendors should provide cryptographic hashes of legitimate firmware versions. Security teams should regularly verify that the firmware running on their VPN appliances matches those hashes. If the firmware has been modified, the hash won't match, and you know you've been compromised.
But most organizations don't do routine firmware verification. It's technically involved, it requires downtime, and there's often a false sense of security because the appliance seems to be working fine.
The Competitive Landscape: Did Other Vendors Have Similar Issues?
Citrix's story suggests that the problem wasn't unique to Ivanti. Citrix remote access products have had multiple critical vulnerabilities in recent years. Fortinet's FortiGate VPN has been the target of zero-day exploits. Palo Alto Networks' GlobalProtect has had security issues.
The common thread isn't that these vendors are incompetent. It's that remote access infrastructure is inherently complex and difficult to secure. VPN appliances sit at the network perimeter. They're exposed to the internet. They handle authentication, encryption, and network segmentation. They're high-value targets for sophisticated attackers.
But the Ivanti story adds another layer. The company didn't just struggle with security. It was actively de-invested in from a security perspective. Clearlake's management approach made the situation worse.
This raises questions about vendor selection. When evaluating a VPN vendor, you need to understand not just the technical capabilities but also the company's commitment to security. Is this a company that will invest in security teams after an acquisition? Is this a company that will be transparent about vulnerabilities? Is this a company that will prioritize security over short-term cost reduction?
Those are harder questions to answer because vendors won't tell you if they're planning to cut security staff. But you can look at their track record. You can examine their past acquisitions. You can talk to customers about their experience with vulnerability disclosure and patches.
The Broader Implications: Supply Chain Security
The Ivanti breach is a visceral example of why supply chain security matters. Your security posture is only as strong as your least secure vendor. If you outsource a critical function to a third party, you're trusting that third party with your security.
Enterprise security is increasingly moving toward zero-trust architectures. Zero-trust means you don't trust anything by default, even things inside your network. You verify every connection, authenticate every user, and validate every device.
But zero-trust assumes that your core infrastructure, including the VPN that enforces these controls, is actually secure. If the VPN itself is compromised, zero-trust becomes theater.
The solution isn't to stop using VPN appliances. Remote access is critical. But it means demanding more transparency from vendors. It means implementing more rigorous verification of firmware. It means building detection systems that assume core infrastructure could be compromised.
It also means evaluating private equity ownership more carefully. Companies owned by private equity firms that prioritize short-term financial extraction over long-term security investment are higher risk. Not all private equity is bad, but the incentive structures matter.
What Happens Now: Ivanti's Path Forward
Ivanti is still in business. They still make VPN and remote access products. But they've lost market share and customer confidence.
Government agencies have disconnected from Ivanti VPN. Private sector organizations are looking for alternatives. Citrix, Fortinet, Palo Alto Networks, and other vendors are getting more attention from customers who are nervous about Ivanti's track record.
Ivanti needs to rebuild trust. That requires demonstrating a genuine commitment to security. It requires being transparent about vulnerabilities. It requires investing in security teams and infrastructure. It requires changing the perception that the company was hollowed out by private equity cost-cutting.
But rebuilding trust is slow. It takes years of clean security records, transparent disclosures, and consistent investment in security. Ivanti is probably years away from being considered a trusted vendor again, if they ever get back to that position.
The question is whether Clearlake will allow Ivanti to make the investments necessary to rebuild. If Clearlake's focus remains on extracting financial value, Ivanti will continue to struggle.
Key Lessons for Enterprise Security Teams
If you work in enterprise security, what should you take away from the Ivanti story?
First, assume that core infrastructure can be compromised. You can't just verify that your VPN is configured correctly. You need to assume that the VPN itself might be backdoored and operate accordingly.
Second, implement robust firmware verification. Periodically verify that the firmware running on your appliances matches the vendor's published hashes. Build automated checks for this.
Third, monitor for behavioral anomalies in your core infrastructure. If your VPN is suddenly making connections to unfamiliar IP addresses or exfiltrating large volumes of data, that's a signal.
Fourth, implement defense-in-depth behind your VPN. Don't assume that just because traffic came through the VPN that it's trustworthy. Implement additional authentication, authorization, and monitoring inside your network.
Fifth, evaluate vendor ownership and management philosophy. Private equity ownership isn't automatically disqualifying, but it's a factor to consider in your risk assessment.
Sixth, maintain relationships with incident response firms like Mandiant. When you suspect you might have been compromised, they have the expertise to conduct detailed investigations and identify supply chain compromises that you might miss.
The Future of VPN Security
The Ivanti breach will likely accelerate the shift toward zero-trust and software-defined perimeter architectures. Instead of relying on a single VPN appliance as your security gateway, future architectures will distribute authentication and authorization across multiple systems.
We'll probably see more adoption of hardware security modules and firmware attestation. If your VPN can cryptographically prove that it's running unmodified firmware, that's a stronger guarantee than relying on vendor claims.
We'll see more emphasis on supply chain security. Organizations will demand that vendors implement secure coding practices, conduct regular security audits, and maintain security teams even after acquisitions.
We'll see more transparency requirements. Regulators might require that critical infrastructure vendors disclose security team size, investment levels, and past incidents.
But in the near term, organizations need to operate assuming that any third-party infrastructure could be compromised. That's not paranoia. It's what the Ivanti breach teaches us.
Real-World Impact on Affected Organizations
Let's talk about what happened to the 119 organizations that were compromised. We don't know their names, but we can imagine their situation.
They deployed Pulse Secure VPN thinking they'd purchased a security tool. They configured it, trained employees on how to use it, and went about their business. Meanwhile, attackers were monitoring all their VPN traffic. They were seeing which employees accessed which systems. They were identifying the most valuable data and targets within the organization.
By the time they realized they'd been compromised, the attackers had already exfiltrated the information they came for. What happens next is expensive. You have to assume every credential that was used on the VPN is compromised. You have to reset passwords. You have to hunt through logs to identify what data was accessed. You have to notify regulators and customers if you were holding their data. You have to figure out if intellectual property or classified information was stolen.
For military contractors, the implications are even more serious. If your security information was compromised, your operational capabilities might be compromised. Your weapons systems might be less effective. Your defense strategies might be exposed. The costs aren't just financial. They're strategic.
This is why supply chain security matters. One vendor's failure cascades to hundreds of organizations that trusted that vendor.
FAQ
What is the Ivanti VPN breach and when did it occur?
The Ivanti VPN breach occurred in February 2021 when Chinese hackers exploited a secret backdoor in Pulse Secure's VPN software, which Ivanti had acquired. The attackers gained access to Ivanti's subsidiary network and then pivoted to compromise 119 other organizations that used the same VPN product. The breach wasn't publicly detailed until 2026 when Bloomberg reported on the incident based on investigations by Mandiant and Ivanti's security team.
How did the attackers plant the backdoor in the VPN software?
The exact method of how the backdoor was installed isn't fully disclosed, but it likely involved compromising Pulse Secure's build infrastructure, firmware signing process, or source code repositories. Once inside the development environment, attackers could have injected malicious code into the firmware before it was compiled, packaged, and signed. This would mean every copy of the software shipped to customers contained the backdoor from the start, making it nearly impossible for individual organizations to detect without specialized forensic analysis.
What are the implications of this breach for enterprises currently using VPN products?
The breach demonstrates that enterprises can't assume third-party security infrastructure is trustworthy, even from established vendors. Organizations should implement firmware verification, monitor for behavioral anomalies in core infrastructure, maintain defense-in-depth behind their VPN, and evaluate vendor ownership and security investment levels. The breach also highlights the importance of building zero-trust architectures that don't rely entirely on a single security appliance.
Why did it take five years for the public to learn about this breach?
The five-year gap between the February 2021 discovery and the 2026 public reporting likely resulted from law enforcement investigations, FBI involvement, classified material handling, litigation considerations, and regulatory processes. Intelligence agencies probably requested confidentiality to investigate the attackers and assess damage. However, this lengthy delay prevented other potential victims from taking appropriate defensive measures during those years.
How did private equity ownership contribute to the security vulnerabilities?
Clearlake Capital acquired Ivanti in 2017, and following the pattern seen with other private equity acquisitions, the firm cut costs significantly in 2022, including reducing security and engineering teams with deep institutional knowledge. When companies prioritize near-term financial margins over long-term security investment, they lose critical expertise and delay necessary infrastructure upgrades. This cost-cutting likely weakened Ivanti's security posture during the exact period when sophisticated threats were accelerating.
What role did Mandiant play in discovering this breach?
Mandiant, Google's incident response and threat intelligence firm, discovered the full scope of the Ivanti compromise while investigating a specific intrusion at another organization. They traced the attack back to the Pulse Secure VPN as the entry point, then identified that the VPN firmware itself had been backdoored. Mandiant's investigation revealed that 119 organizations had been compromised through the same backdoor, including European and U.S. military contractors, and shared these findings with Ivanti and eventually with Bloomberg.
What was CISA's emergency disconnect order and why was it issued?
In early 2024, the Cybersecurity and Infrastructure Security Agency (CISA) issued an unprecedented emergency order requiring all federal agencies to disconnect Ivanti VPN appliances within two days due to multiple critical vulnerabilities being actively exploited in the wild. This order reflected that the risk of continued use had become higher than the disruption of disconnecting the infrastructure, signaling a complete loss of government confidence in Ivanti's security products.
How can security teams detect if their VPN has been compromised with a firmware backdoor?
Detecting firmware-level backdoors is extremely challenging for most organizations. The most effective method is implementing routine firmware integrity checking by verifying cryptographic hashes against vendor-published legitimate versions. Organizations should also monitor for behavioral anomalies, unusual administrative activity in logs, unexpected network connections from the VPN appliance, and unusual data exfiltration patterns. Professional incident response firms like Mandiant can conduct specialized firmware analysis when compromise is suspected.
What are the broader implications of this breach for supply chain security?
The Ivanti breach exemplifies why supply chain security is critical and why organizations cannot assume that third-party infrastructure is trustworthy. A single compromised vendor cascaded to affect 119 organizations across multiple industries and government sectors. This demonstrates the necessity of zero-trust architectures, rigorous vendor evaluation including assessment of private equity ownership, mandatory transparency from critical infrastructure providers, and implementation of defense-in-depth strategies that don't rely entirely on any single vendor or appliance.
Which other vendors have experienced similar security incidents?
Citrix has faced a similar trajectory following private equity acquisition by Elliott Investment Management and Vista Equity Partners in 2022, resulting in major layoffs and multiple critical security vulnerabilities in remote access products. Fortinet's FortiGate VPN has been targeted by zero-day exploits, and Palo Alto Networks' GlobalProtect has experienced security issues. The common thread isn't vendor incompetence but the inherent complexity of remote access infrastructure combined with private equity cost-cutting in some cases.
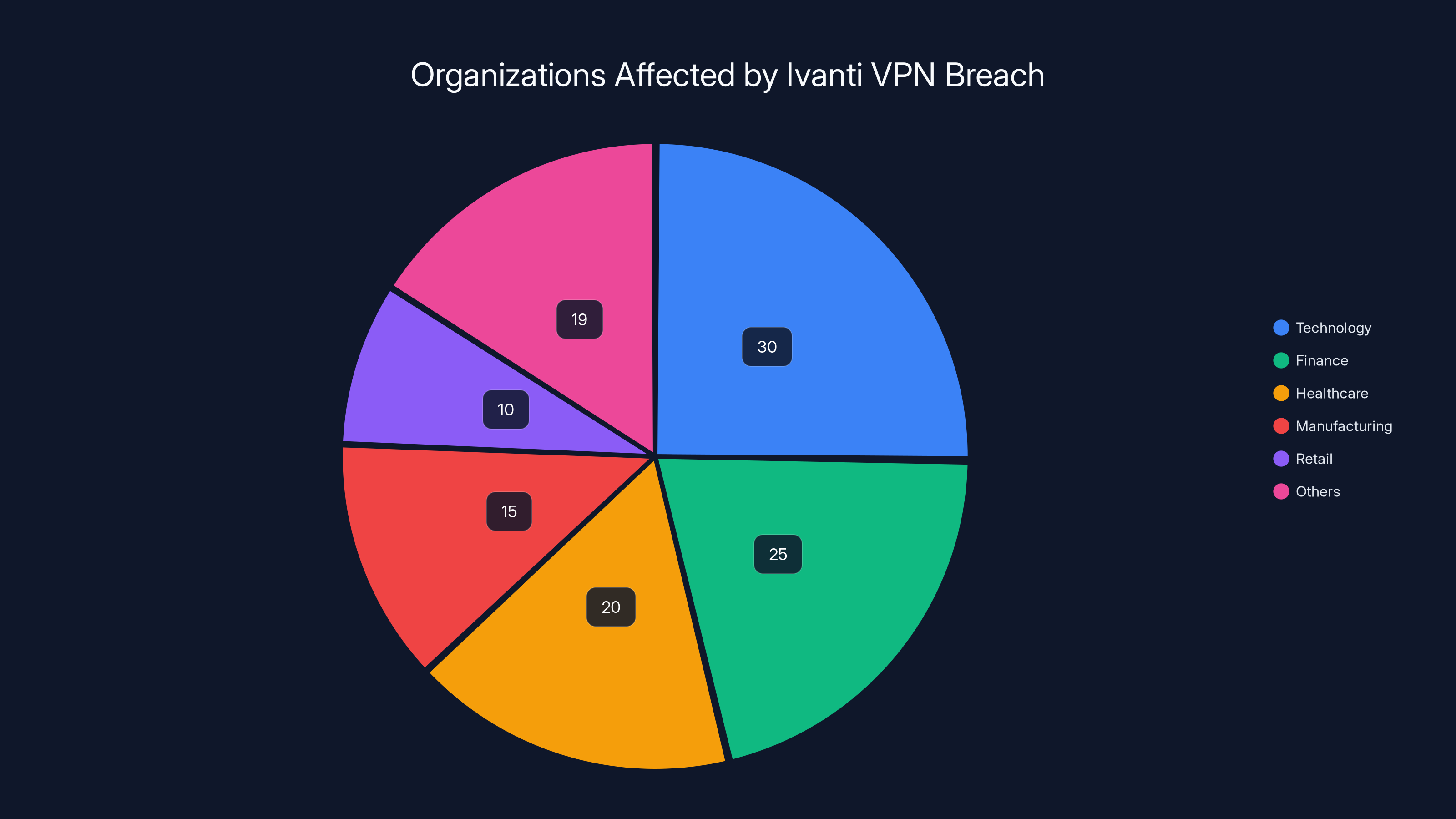
The Ivanti VPN breach affected 119 organizations across various sectors, with technology and finance being the most impacted. (Estimated data)
TL; DR
-
Chinese Backdoor in VPN Firmware: Hackers planted a secret backdoor in Pulse Secure's VPN software, which Ivanti owned, allowing persistent access to customer networks without detection.
-
Cascading Compromise: The backdoor provided entry to 119 organizations, including European and U.S. military contractors, through a single supply chain compromise rather than individual attacks.
-
Private Equity Cost-Cutting: Clearlake Capital's acquisition and subsequent layoffs of security teams in 2022 weakened Ivanti's ability to detect and respond to threats during a critical period.
-
Five-Year Silence: The breach was discovered in February 2021 but not publicly detailed until 2026, giving defenders no opportunity to hunt for compromises in their own networks.
-
Government Lost Confidence: CISA's 2024 emergency disconnect order for all federal agencies using Ivanti VPN reflected complete loss of trust in the vendor's security posture.
-
Bottom Line: Assume core infrastructure can be compromised, implement firmware verification, demand vendor transparency, and evaluate private equity ownership as a security risk factor.
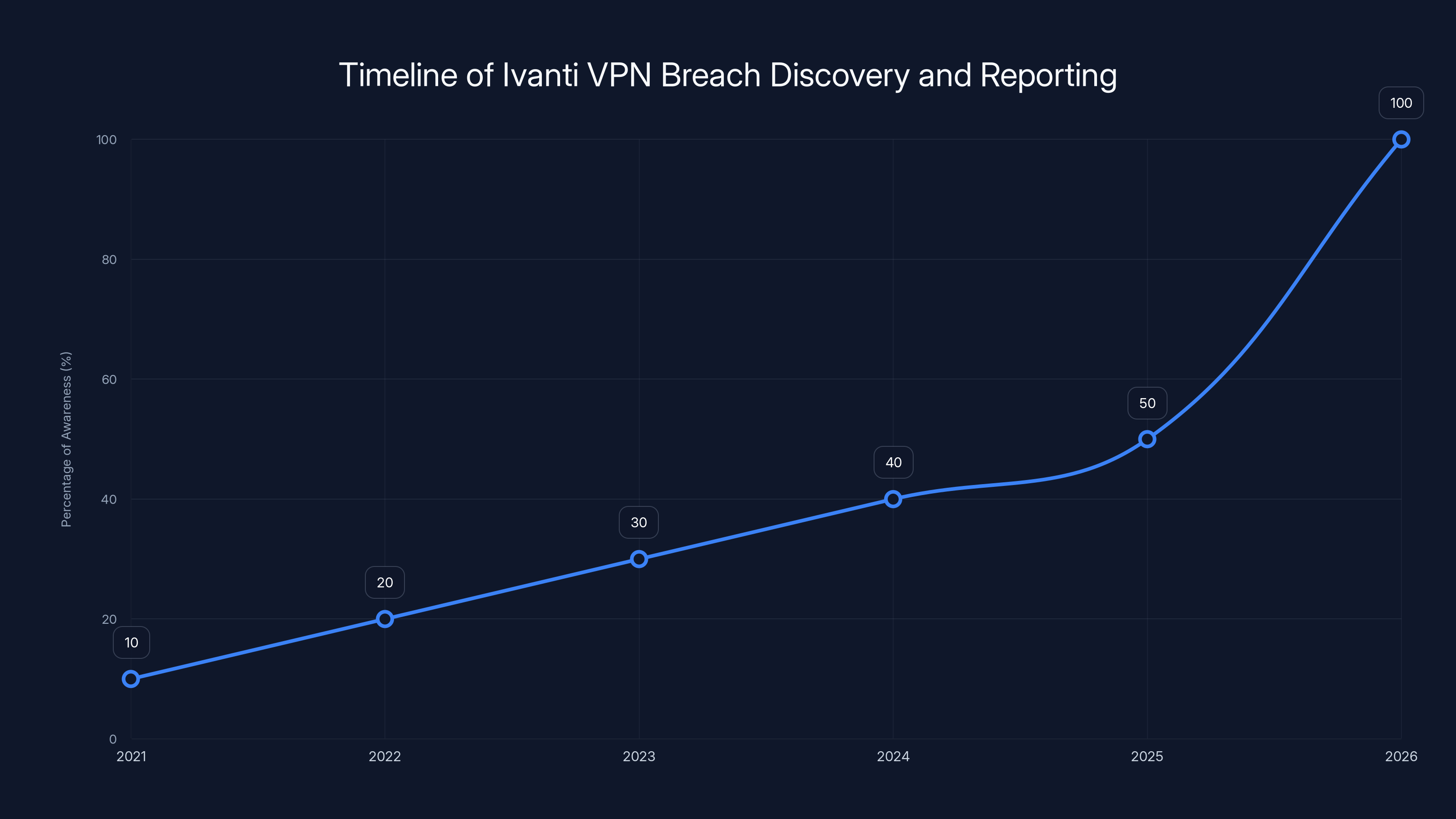
The Ivanti VPN breach was discovered in 2021 but not publicly reported until 2026, indicating a gradual increase in awareness over five years. Estimated data.
Key Takeaways
- A backdoored VPN firmware compromise in Pulse Secure cascaded to affect 119 organizations including U.S. military contractors through a single supply chain attack
- Private equity acquisition and subsequent cost-cutting by Clearlake Capital weakened security teams during critical period of increasing sophisticated threats
- Five-year delay between 2021 breach discovery and 2026 public reporting prevented organizations from conducting timely compromise investigations
- CISA's 2024 emergency disconnect order forcing federal agencies to abandon Ivanti VPN within 48 hours represents unprecedented loss of vendor confidence
- Supply chain security requires assuming core infrastructure can be compromised and implementing defense-in-depth architectures that don't rely on single appliances
Related Articles
- AI-Powered Hacking: How Low-Skill Attackers Break Firewalls [2025]
- CarGurus Data Breach: 1.7M Records Stolen by ShinyHunters [2025]
- Honeywell CCTV Camera Vulnerability: Complete Security Guide [2025]
- Abu Dhabi Finance Summit Data Breach: 700+ Passports Exposed [2025]
- Android AI Photo Editor Data Breach: 2M Users Exposed [2025]
- ExpressVPN's Hybrid VPN Browser Extension and Meta Quest App [2025]
![Ivanti VPN Breach: How Chinese Hackers Hit 119 Customers [2025]](https://tryrunable.com/blog/ivanti-vpn-breach-how-chinese-hackers-hit-119-customers-2025/image-1-1771864695703.jpg)



