The One Fly Data Breach: What Happened and Why It Matters
In early October 2025, something went seriously wrong at One Fly, a travel technology platform that connects airlines and travel agencies to millions of customers worldwide. Security researchers discovered that thousands of sensitive customer records were leaking in real-time through an unsecured database. We're not talking about encrypted hashes or tokenized payment data here. We're talking about full credit card numbers. In plain text. Just sitting there, accessible to anyone who knew where to look.
For travelers who used One Fly's services, this breach represents one of the most dangerous scenarios imaginable: their complete financial and identity information exposed. Names, dates of birth, ID document details, flight bookings, ticket prices, destination airports, JWT authentication tokens, and complete credit card information all leaked from nine internal Java Spring applications through a misconfigured Elasticsearch instance.
What makes this particularly troubling is how easily it could have been prevented. This wasn't sophisticated hacking. This wasn't a zero-day exploit or nation-state-level cyber warfare. This was basic operational security failure. A database exposed to the internet with no access controls, no IP whitelisting, no authentication required. Just open for business to anyone with an internet connection and basic technical knowledge.
One Fly operates at significant scale. The company has between 50 and 200 employees and serves over 100 carriers and major online travel agencies worldwide. That means this breach potentially affects hundreds of thousands of travelers, even though Cybernews researchers identified around 10,000 ID records and 6,000 payment cards during their investigation. Those numbers represent only what they documented during their research window. The actual scope could be far larger.
The timing matters too. Evidence suggests the data was exposed starting in early October 2025, but the exact date remains unclear. That gap between when the breach likely started and when it was discovered is critical. Every day that data sits exposed is another day for bad actors to access it, copy it, and exploit it. The travel industry has been hit hard by breaches in recent years, and One Fly's exposure adds to an already troubling trend.
What's particularly frustrating about this breach is that it represents a failure of basics. Not advanced security measures. Not cutting-edge defense systems. Just fundamental database hygiene. Elasticsearch instances should never be exposed directly to the internet without authentication. This is technology 101. Yet here we are, in 2025, seeing the same preventable mistakes that have caused major breaches for decades.
TL; DR
- One Fly exposed thousands of sensitive records through an unsecured Elasticsearch instance containing full credit card information in plaintext
- At least 10,000 ID records and 6,000 payment cards were identified by researchers, though the actual scope could be significantly larger
- The breach included names, dates of birth, ID documents, flight details, and JWT authentication tokens alongside complete payment information
- Evidence points to early October 2025 as when the data exposure began, though exact timing remains unclear
- One Fly serves over 100 airlines and major travel agencies worldwide, making this a large-scale compromise affecting potentially hundreds of thousands of travelers
- Simple fixes like access controls, IP whitelisting, and basic authentication could have prevented this entirely
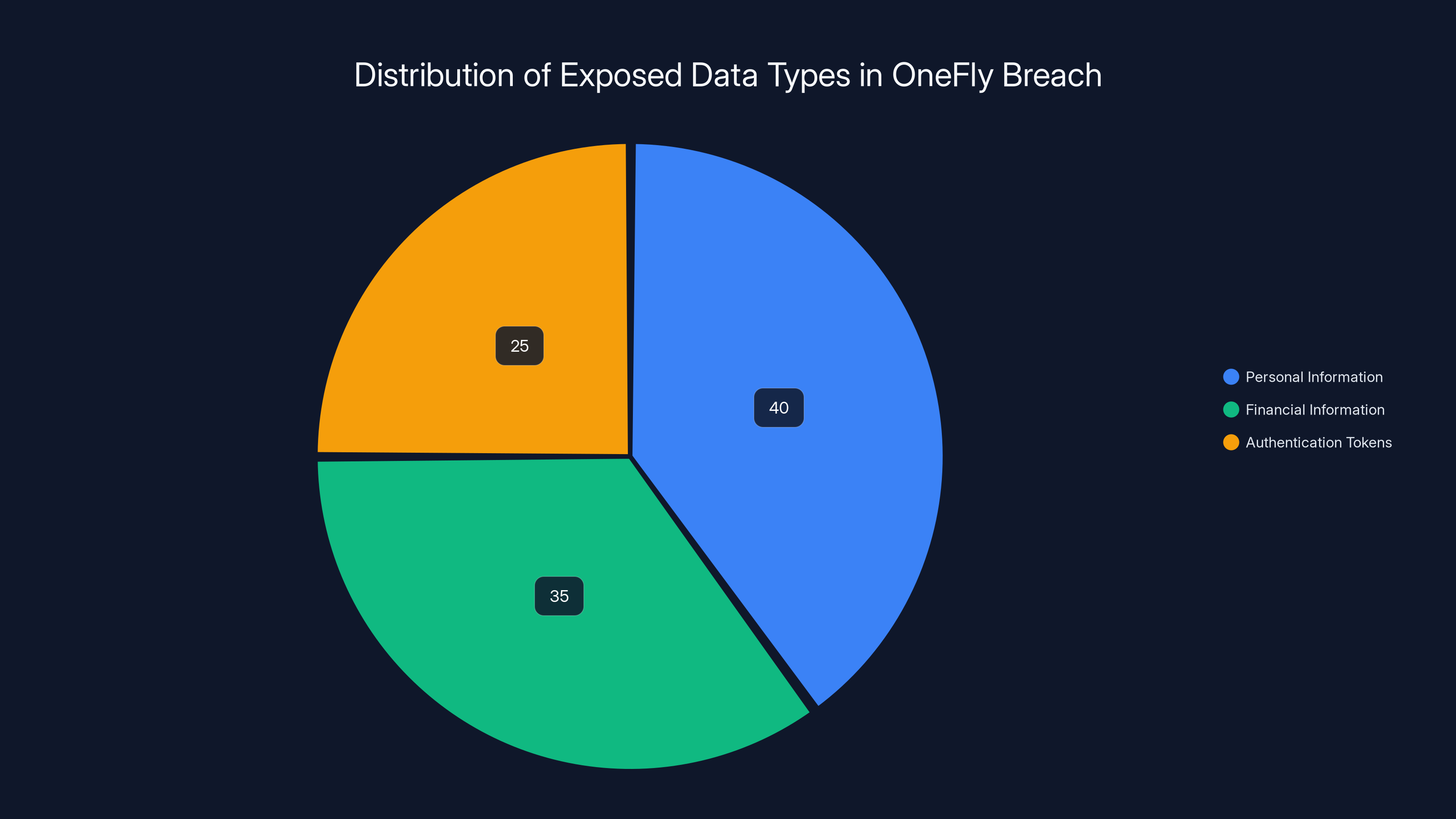
Estimated data shows that personal information was the most exposed type in the OneFly breach, followed by financial details and authentication tokens.
Understanding One Fly: The Company Behind the Breach
One Fly isn't some scrappy startup operating out of a garage. It's a significant player in the travel technology space with substantial operational reach. The company functions as a global travel content aggregator and air-ticket supplier, acting as the connective tissue between airlines, online travel agencies, and travel technology partners.
Think of One Fly as infrastructure for the travel industry. Airlines want to sell tickets through multiple channels. Online travel agencies like Expedia and Kayak want access to inventory from hundreds of carriers. Travel tech companies need flight data to power their platforms. One Fly sits in the middle, providing unified APIs that connect these disparate systems. This middleware position is valuable but also sensitive. They're handling the critical transaction data between booking platforms and payment systems.
The company maintains connections to more than 100 carriers globally and works with major online travel agencies. They provide access to worldwide ticket inventories, including low-cost carrier fares and pricing from the Global Distribution System (GDS). This means their systems touch thousands of bookings daily, each one carrying personal and financial information.
With 50 to 200 employees, One Fly operates as a mid-sized technology company. That size puts them in an awkward position security-wise. They're large enough to handle significant data volumes and manage complex infrastructure, but not always large enough to afford dedicated security teams or best-in-class infrastructure. They likely have the resources to do security right, but the breach suggests they didn't prioritize it.
The company's business model depends entirely on trust. Airlines and travel agencies trust them to handle sensitive booking data. Customers trust that their information is secure when they book flights through platforms using One Fly's services. That trust is now broken. Once payment card data leaks, trust takes years to rebuild, if it rebuilds at all.
One Fly's position in the travel tech ecosystem also means the breach's impact cascades. A customer doesn't necessarily know they booked through One Fly. They might have booked through an OTA like Kiwi.com or a direct airline site that uses One Fly's APIs. Those platforms are now in the uncomfortable position of notifying customers that their data was compromised by a vendor they depend on but that customers never directly chose to trust with their information.
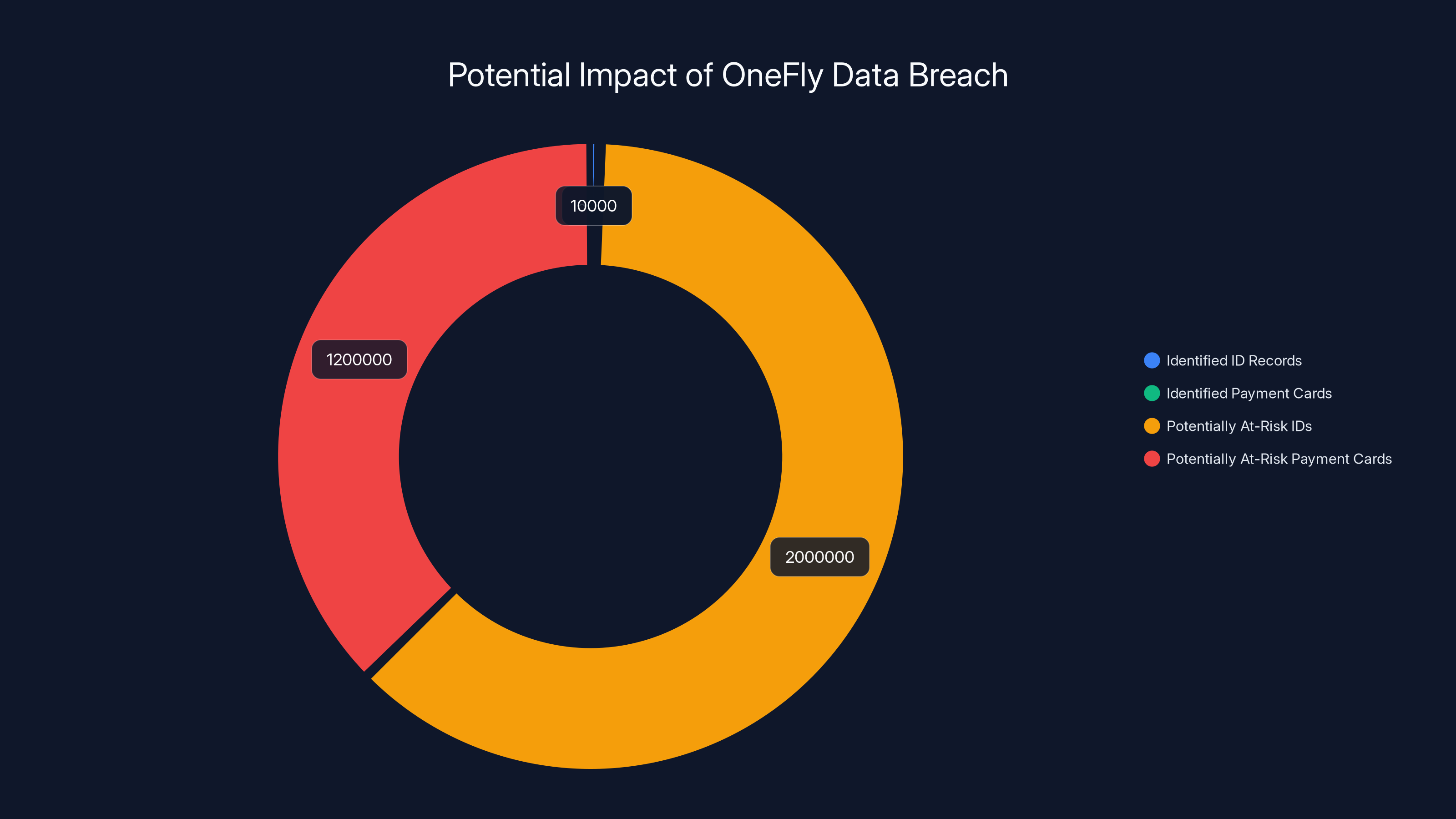
The chart illustrates the scope of the OneFly data breach, with 10,000 ID records and 6,000 payment cards identified. However, millions more could be at risk due to the scale of OneFly's operations. Estimated data.
The Technical Details: How the Breach Happened
The breach occurred through Elasticsearch, a widely-used search and analytics engine that's incredibly powerful but equally dangerous when misconfigured. Elasticsearch is designed to be fast and flexible. It excels at indexing and searching massive datasets. What it's not designed for is sitting on the open internet with no authentication protecting it.
Cybernews researchers discovered unsecured Elasticsearch instances connected to nine internal Java Spring applications. These applications were logging sensitive data directly into Elasticsearch. That's already a risky practice, but it becomes catastrophic when the database itself has no access controls.
The leak wasn't gradual or partial. The researchers found data being exposed "in real-time," meaning anyone with network access could connect to the Elasticsearch instance and query current information as it was being logged. This is the worst-case scenario for a data breach. Not historical data sitting in backups somewhere, but live, active data flowing through systems with zero protection.
Java Spring applications are common in enterprise development. They're reliable, well-supported, and have good security practices baked in at the framework level. But framework-level security only goes so far. If your developers configure those applications to log sensitive data directly to an unprotected database, the framework can't save you. The security failure here was organizational and procedural, not technical.
The data included in those Elasticsearch logs tells a complete story about each traveler. Names, dates of birth, ID document details (passport numbers, driver's license information, national IDs). Flight information including airline names, flight numbers, ticket prices, and destination airports. Full credit card details including card numbers, expiration dates, and CVV codes. And JWT tokens, which are authentication credentials that allow accessing internal systems.
The JWT tokens are particularly dangerous. These tokens are used for user authentication and authorization within One Fly's internal systems. An attacker with valid JWT tokens could impersonate legitimate users, access internal company systems, and extract even more sensitive information beyond what was already exposed. If One Fly's internal systems contain customer service records, account details, or administrative information, those tokens provide keys to unlock all of it.
The researchers note that it was "impossible to determine exactly when the data was generated, or leaked." This fog around timing is common in breaches involving continuous logging systems. Data could have been exposed for weeks or months before discovery. Every day of exposure increases the window for attackers to access the data.
The Scope of the Breach: Thousands Affected, Potentially Millions at Risk
Cybernews researchers identified around 10,000 ID records and approximately 6,000 payment cards during their investigation. The researchers themselves describe this as "rather minimal," which is a telling comment on breach scope. But minimal by what standard? If 10,000 people have their identity information stolen, that's far from minimal from a consumer perspective.
However, the researchers were only examining the exposed instance during a limited time window. They weren't necessarily capturing all data that had ever been exposed. If One Fly's Elasticsearch instance was truly unsecured and accessible, the data could have been accessed, copied, and exfiltrated long before Cybernews found it.
Consider One Fly's operational scope: serving over 100 carriers and major travel agencies globally. Each carrier and OTA processes thousands of bookings daily. Even a modest estimate suggests millions of transactions flowing through One Fly's systems annually. The 10,000 IDs and 6,000 payment cards identified represent only what researchers found. The actual scope could be orders of magnitude larger.
The geographic distribution of affected customers likely spans most countries. Cybernews researchers noted affected records included travelers from numerous regions. People booking international flights, business travelers, leisure tourists, all potentially exposed. The breach doesn't discriminate based on booking amount or customer value. The data was leaking indiscriminately.
What complicates the impact assessment is that many affected individuals may never know their data was compromised. If someone booked a flight through Kayak or Expedia, they might never receive notification that One Fly's systems were breached. The travel agency that sold the ticket might not even know about the breach, or might not be required to notify customers under the laws in their jurisdiction. This creates a dangerous blind spot where affected individuals remain unaware of their exposure.
For the payment cards specifically, 6,000 represents a solid chunk of change for fraudsters. A single stolen card fetches between
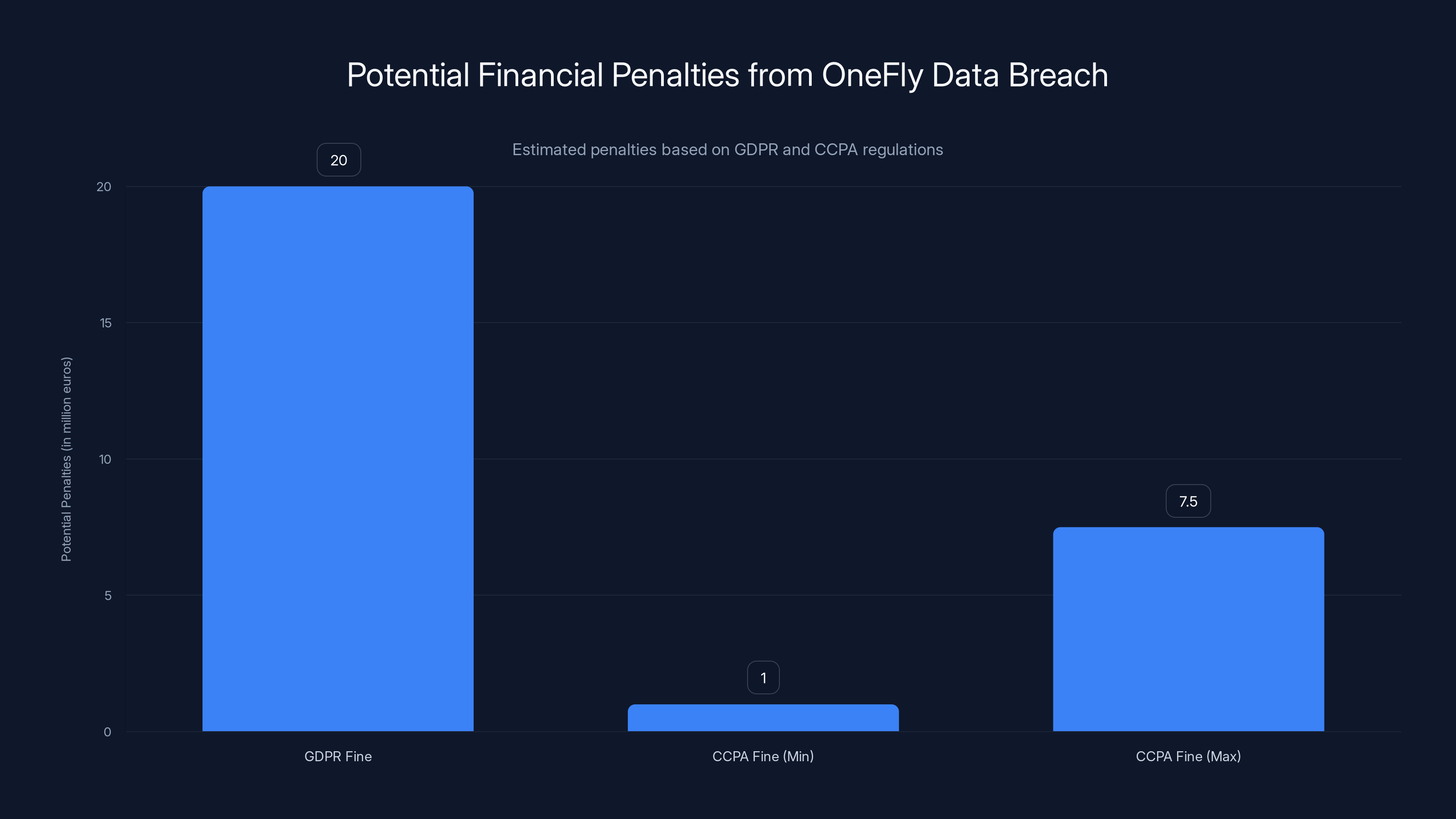
OneFly faces significant financial penalties under GDPR and CCPA, with potential fines ranging from 1 million to 20 million euros. Estimated data based on regulatory guidelines.
Payment Data Exposed: The Most Dangerous Information
Let's be clear about what was exposed: full credit card details in plaintext. Not hashed. Not encrypted. Not tokenized. Actual card numbers sitting in readable text files accessible through a basic internet connection.
This is the worst possible form of payment data exposure. Credit card companies and payment networks like Visa and Mastercard have spent decades developing encryption, tokenization, and fraud detection systems. PCI-DSS (Payment Card Industry Data Security Standard) exists specifically to prevent this. It's not complicated. Don't store full card details. Encrypt everything. Use payment tokens instead of real card numbers. Restrict access. One Fly violated all of these principles.
When full card details are exposed, fraud becomes trivial. An attacker has everything needed for fraudulent transactions: the card number, expiration date, CVV code, and cardholder name. They can make purchases immediately. They can sell the data to other criminals. They can use it for months or even years before the cardholder notices unauthorized activity.
Card fraud has become sophisticated too. Fraudsters don't always make obvious
The fact that this data was in plaintext within logs is particularly egregious. Logging systems shouldn't contain payment data at all. If logging is necessary for debugging, it should use masked or tokenized values. Developers should never see full card details in logs. The fact that raw payment data was being logged and then stored in an unprotected database suggests either a fundamental misunderstanding of security practices or a willful disregard for them.
Fraud liability is complicated. In the United States, cardholders are typically protected from fraudulent charges under federal law (Fair Credit Billing Act), limiting liability to $50 if reported promptly. But that protection applies to legitimate cards used without authorization. When card details are stolen through a breach, the burden of dispute and recovery falls on the customer. Transactions have to be reported, disputes filed, temporary credit issued, new cards issued. The hassle is enormous even though financial liability is limited.
Identity Documents Exposed: The Deeper Threat
Payment card fraud is bad, but identity theft is worse. When a thief has your name, date of birth, and identity document details (passport, driver's license, national ID numbers), they can do far more damage than just fraudulent charges.
Identity theft can take months or years to fully recover from. Criminals can open new accounts in your name, take out loans, establish utility accounts, or file tax returns claiming refunds due to them. They can rent apartments, get phone contracts, or establish credit histories that destroy your financial reputation.
The travel context makes this especially dangerous. People traveling internationally often need to provide identification documents. With names, dates of birth, and ID document numbers, a criminal could potentially book flights, rent cars, or reserve hotels in someone else's name. Worse, if they have the victim's actual passport or ID information, they could potentially use it to move through immigration systems in some cases, creating serious legal complications.
Passport fraud is a major concern in international law enforcement. When passport numbers and personal details are exposed, governments and airlines have to grapple with the possibility of that information being used for fraudulent travel. International travel databases might flag a legitimate passenger as a security risk if someone else traveled using their identity.
Recovery from identity theft typically requires placing fraud alerts with credit bureaus, monitoring credit reports religiously for years, and being prepared to dispute fraudulent accounts. Some people freeze their credit entirely, though this creates its own friction for legitimate activities like getting new phone plans or applying for utility accounts.
The individuals most at risk are those who travel frequently for business. They often have higher credit scores, higher credit limits, and more accounts that can be exploited. A fraudster targeting business travelers specifically could cause significant financial damage.
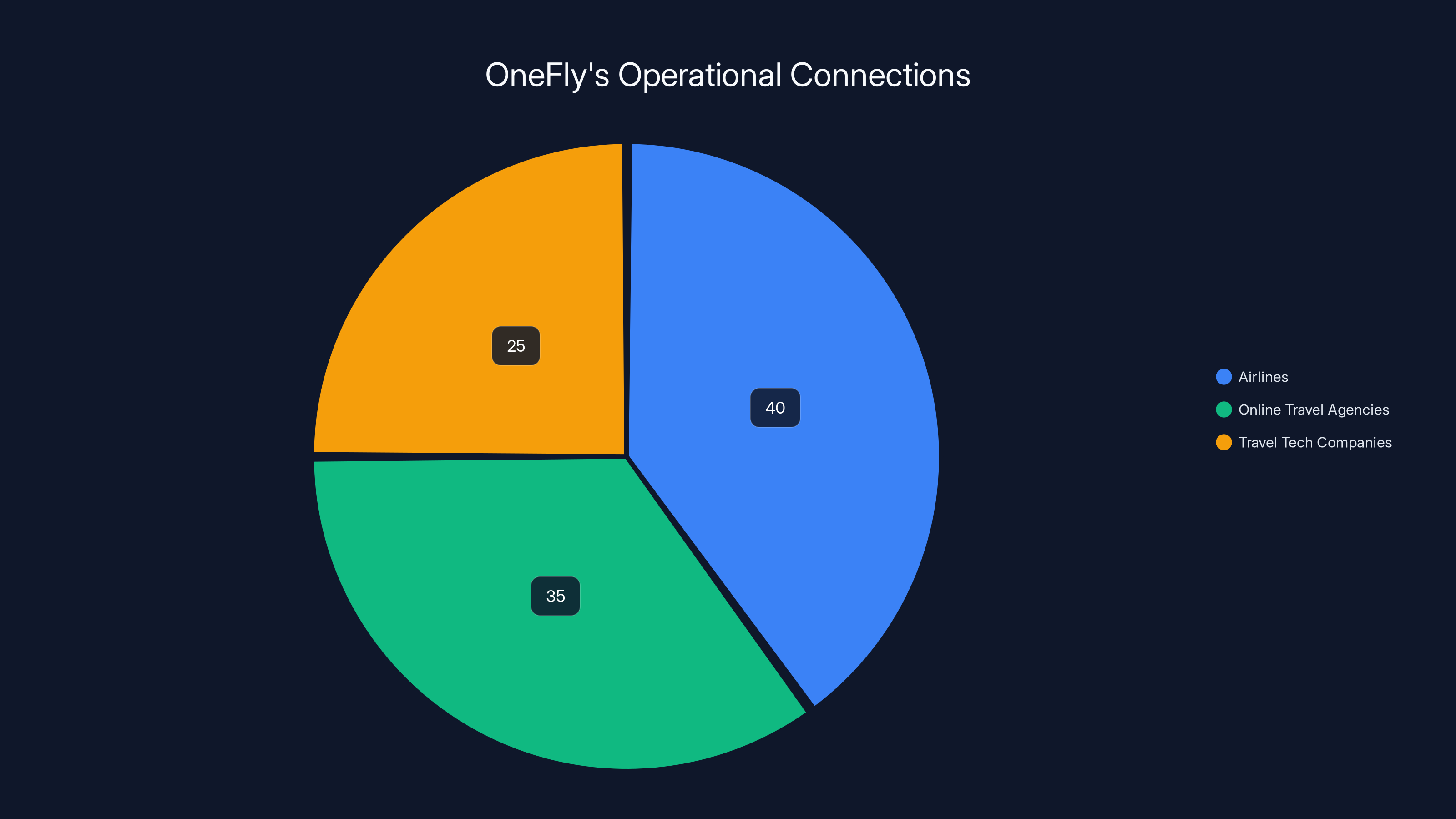
Estimated data shows OneFly's connections are primarily with airlines (40%) and online travel agencies (35%), with travel tech companies making up the remaining 25%.
JWT Tokens and Internal System Access: A Hidden Risk
While payment data and identity documents are obvious targets in a breach, the JWT tokens exposed represent a different class of threat entirely. JWT (JSON Web Token) tokens are credentials. They prove to systems that you are who you claim to be.
If One Fly's internal systems use JWT tokens for authentication, and those tokens were exposed in logs, then attackers could potentially use those tokens to access internal systems. They could impersonate legitimate One Fly employees or customers. They could access customer service systems, account management interfaces, or administrative functions.
The scope of damage depends on what permissions those tokens carry. A customer service representative's token would grant access to customer accounts and support systems. An administrator's token could grant access to system configuration, database management, or billing systems. Even a basic user token could allow access to personal account information.
Cybernews specifically noted that "exposed internal user authentication tokens can be used for user impersonation to obtain more information from internal company systems, given that Elastic is regularly logging currently valid tokens." This is critical. These aren't old expired tokens. They're current, valid tokens actively being logged because they're currently being used.
The attack chain is straightforward: find the exposed Elasticsearch instance, query for JWT tokens, extract valid tokens, and use them to access internal systems. This could happen automatically through bots scanning the internet for exposed services. The tokens could be used to access systems immediately, or stored for later exploitation.
Internal system access could lead to further data extraction. Customer service systems often store notes about customer issues, sometimes including sensitive information. Support tickets might contain conversations where customers provided additional sensitive data while trying to resolve problems. Administrative systems might contain configuration details, API keys, or database connection strings that could be used to access even more data.

The Cascade Effect: How One Company's Breach Affects Entire Industries
One Fly doesn't exist in isolation. They're part of a complex ecosystem of travel technology. When One Fly gets breached, the damage ripples through their entire customer network.
Airlines trust One Fly with booking data. Online travel agencies depend on One Fly's APIs to source flight inventory. Travel tech companies integrate with One Fly to power their flight search and booking features. When One Fly is compromised, all of these partners are potentially exposed.
Consider the customer notification chain. A consumer books a flight through Expedia. Expedia uses One Fly's APIs to source that flight. The booking is completed, payment is processed. Months later, One Fly's breach is discovered. Now Expedia has to decide: do we notify our customers that their data was compromised by our vendor? Do we wait for legal guidance? How do we explain that a company they never directly interacted with had their personal information?
This is where vendor risk management becomes critical. Large companies often have hundreds of third-party vendors with access to sensitive data. Each vendor represents a potential breach vector. One Fly's breach shows why companies need rigorous security requirements for vendors, regular audits of vendor security practices, and clear incident response procedures for when vendors get breached.
The travel industry specifically is a high-value target for cybercriminals. Travelers are often affluent (at least the business travelers are). They have good credit. They travel internationally and might not notice fraudulent charges immediately if they occur while abroad. A single compromised travel company can provide thousands of high-quality victim profiles for criminals to exploit.
This cascading effect also creates regulatory complications. Airlines might be required to notify their customers of the One Fly breach, even though the breach happened at a vendor. Different countries have different notification requirements. GDPR in Europe requires notification of any breach of personal data. CCPA in California has similar requirements. Notifying thousands of affected customers costs money, damages reputation, and creates legal liability.

Estimated data shows that Marriott had the largest breach with 500 million records exposed, highlighting the vulnerability of travel tech companies. Estimated data.
The Negligence Factor: Why This Breach Was Preventable
There's negligence, and then there's the negligence on display in the One Fly breach. This wasn't a sophisticated attack. This wasn't exploitation of a zero-day vulnerability. This was basic operational security failure.
Elasticsearch, by default, runs on port 9200 with no authentication required. This is fine for local development. Running an Elasticsearch instance on the open internet with no authentication and no IP whitelisting is incompetence.
Securing Elasticsearch is straightforward. Enable authentication. Restrict access to specific IP addresses. Use VPCs or security groups to prevent external access. Use TLS encryption for data in transit. Implement role-based access controls. These aren't advanced techniques. They're standard practices documented in Elasticsearch's official security guide.
The fact that this wasn't done suggests either complete lack of security awareness or deliberate negligence. Given that One Fly is a real company with significant operations, lack of awareness seems unlikely. This suggests either that security was deprioritized, or that whoever was responsible for infrastructure security failed catastrophically.
The other negligence factor is logging sensitive data at all. Storing full payment card details in application logs is a violation of PCI-DSS. Period. This shouldn't be a complex decision. PCI-DSS compliance is a requirement for processing credit cards. Any company handling payment data should know this. Yet raw card details were being logged directly into Elasticsearch.
This suggests poor code review practices. Developers wrote code that logged sensitive data. That code either wasn't reviewed, or was reviewed by people who didn't understand PCI-DSS requirements. It was deployed to production. It ran for an unknown period of time. And it created an easily accessible treasure trove of payment data.
The Cybernews recommendation for mitigation captures the negligence perfectly. Access control rules. Refined logging processes. IP whitelisting. These are fundamentals. Cybernews recommends these improvements "while the fixes are ongoing," which implies One Fly wasn't even doing these things initially.

Mitigation Strategies: What Companies Should Do Now
For One Fly specifically, the damage is done. But there are steps they can and should take to limit further damage and prevent recurrence.
First, they need to secure the exposed Elasticsearch instance immediately. This means authentication, IP whitelisting, and network isolation. The instance should be behind a VPN or security group that only allows connections from authorized internal networks.
Second, they need to audit what data was actually exposed and for how long. This is forensic work. They need to check access logs (if any exist) to determine when the instance was first exposed and whether there's evidence of unauthorized access. They need to estimate how many unique records were exposed during the exposure window.
Third, they need to notify affected customers. This is legally required in most jurisdictions and ethically necessary regardless of law. The notification needs to explain what data was exposed, when it was exposed, and what steps customers should take. For payment card data, this means recommending that customers contact their card issuers to request new cards or place fraud alerts.
Fourth, they need to implement comprehensive security improvements. This includes enabling encryption for sensitive data in transit and at rest. It includes implementing proper access controls. It includes revamping logging practices to never log sensitive data directly. It includes implementing PCI-DSS compliance controls if they weren't already in place.
Fifth, they need to conduct a comprehensive security audit of all systems. An external security firm should review infrastructure, application code, access controls, and security practices. Any other exposed databases or unsecured systems need to be identified and fixed.
Sixth, they should offer credit monitoring and identity theft protection services to affected customers. This is becoming standard practice after major breaches and can help mitigate customer harm.
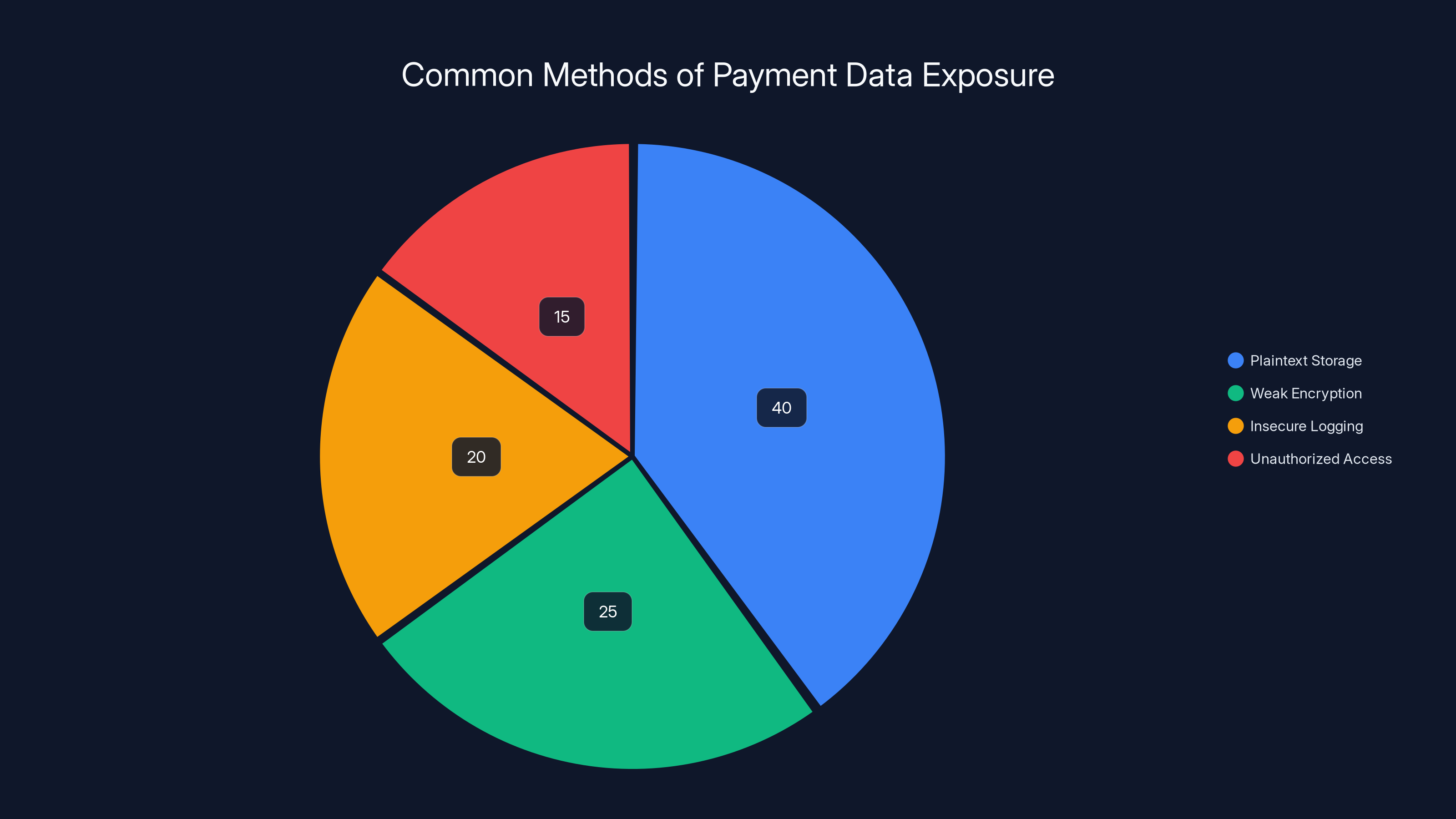
Plaintext storage is estimated to be the most common method of payment data exposure, accounting for 40% of incidents. Estimated data.
What Customers Should Do: Protecting Yourself
If you booked flights through One Fly or through travel agencies that use One Fly (which is most of them), you should take protective action.
First, contact your credit card issuer if you booked flights and paid by credit card. Explain that your card details may have been exposed in a vendor breach. Request a new card with a new number. Most card issuers will do this immediately with no questions asked.
Second, place a fraud alert with the credit bureaus. The three major bureaus in the US are Equifax, Experian, and Trans Union. You can place a fraud alert through any of them and it will be shared across all three. The alert flags your credit report to warn lenders that you may be a victim of identity theft and they should verify your identity before extending credit. This adds a speed bump that makes it harder for fraudsters to open accounts in your name.
Third, obtain a free copy of your credit report from each bureau. Go to Annual Credit Report.com (the federally authorized site). Review your reports for suspicious accounts or inquiries you didn't authorize. Look for accounts you don't recognize, recent hard inquiries from lenders you didn't contact, or collection accounts for debts you didn't incur.
Fourth, monitor your credit card statements closely. Check your statements regularly for unauthorized charges. Most credit card issuers offer online statement review tools that let you check your account in real time rather than waiting for monthly statements.
Fifth, consider placing a credit freeze. A credit freeze prevents new accounts from being opened in your name without your explicit authorization. Unlike fraud alerts, which are temporary, credit freezes last until you explicitly lift them. The tradeoff is that you have to lift the freeze if you want to apply for new credit, which adds friction. But for many people, that friction is worth the security benefit.
Sixth, be cautious of phishing attempts. Scammers often exploit major breaches by sending emails impersonating the breached company or banks, claiming to "verify" your information or "secure" your account. These are phishing attacks. If you receive suspicious emails claiming to be from One Fly, airlines, or banks, don't click links or provide information. Go directly to the official website by typing the URL yourself.
Industry Trends: Why Travel Tech Is a Breach Target
Travel technology companies handle some of the most valuable data in the digital economy. Payment information, identity documents, travel patterns, locations, passport details. For scammers and identity thieves, this is the ideal victim profile.
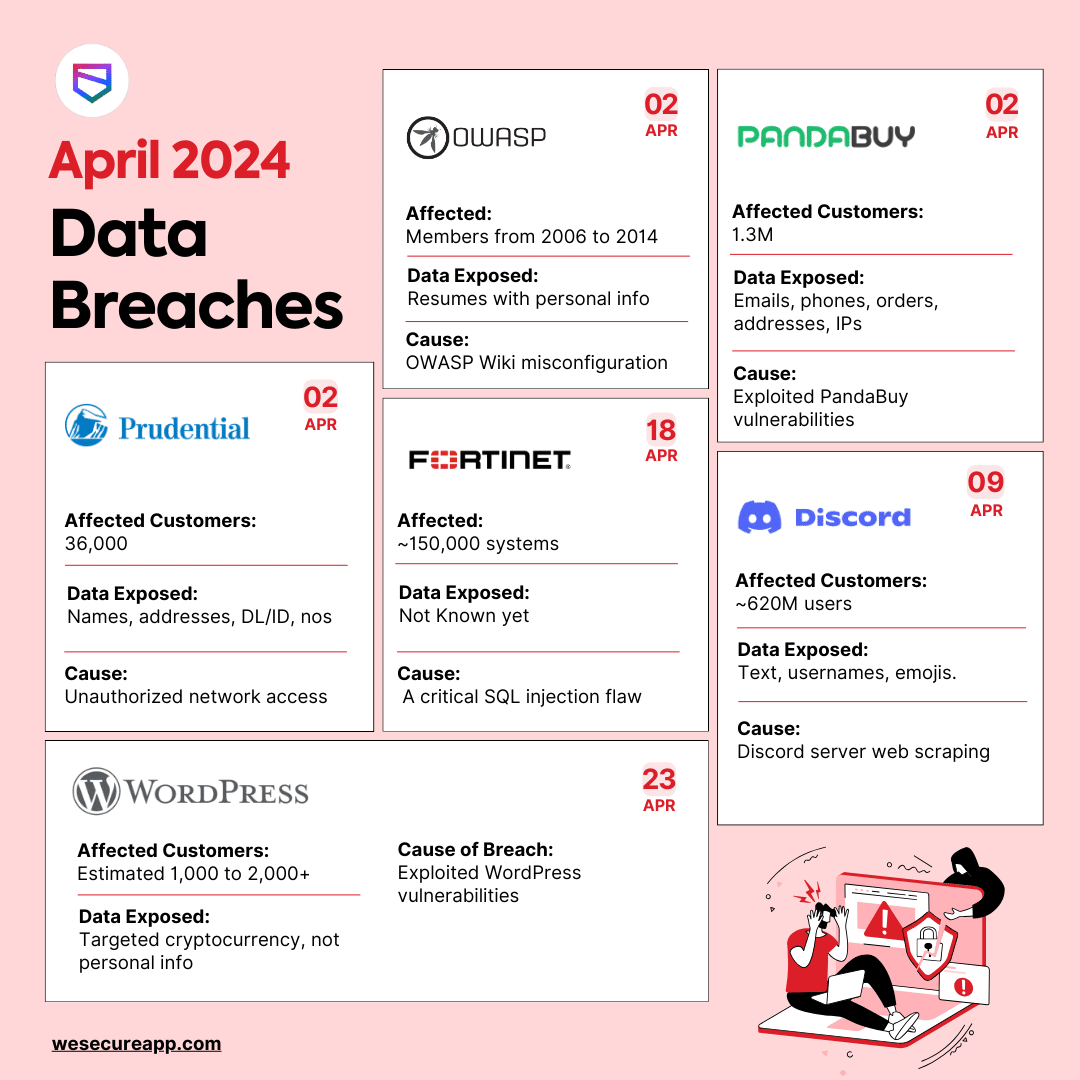
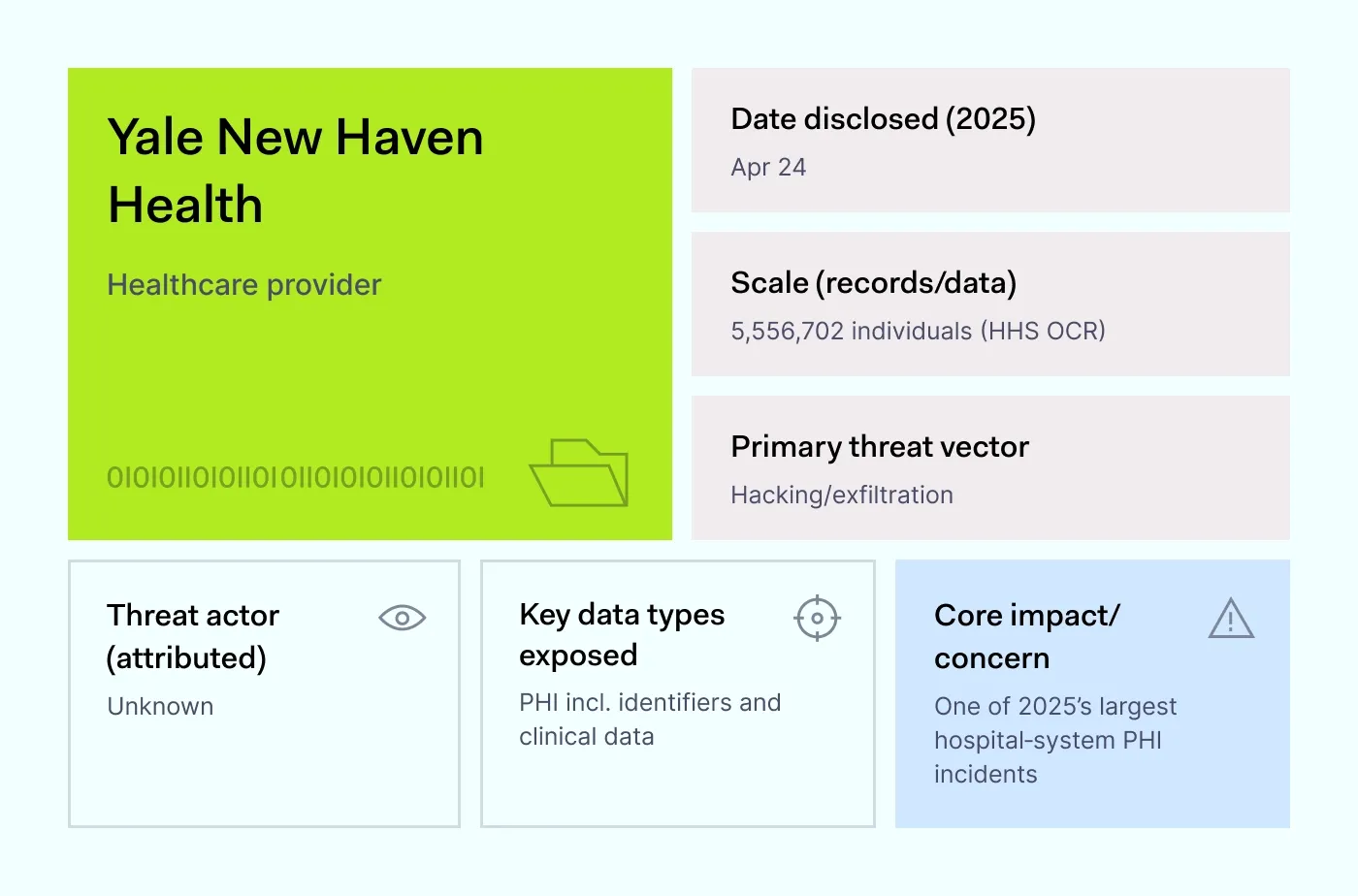
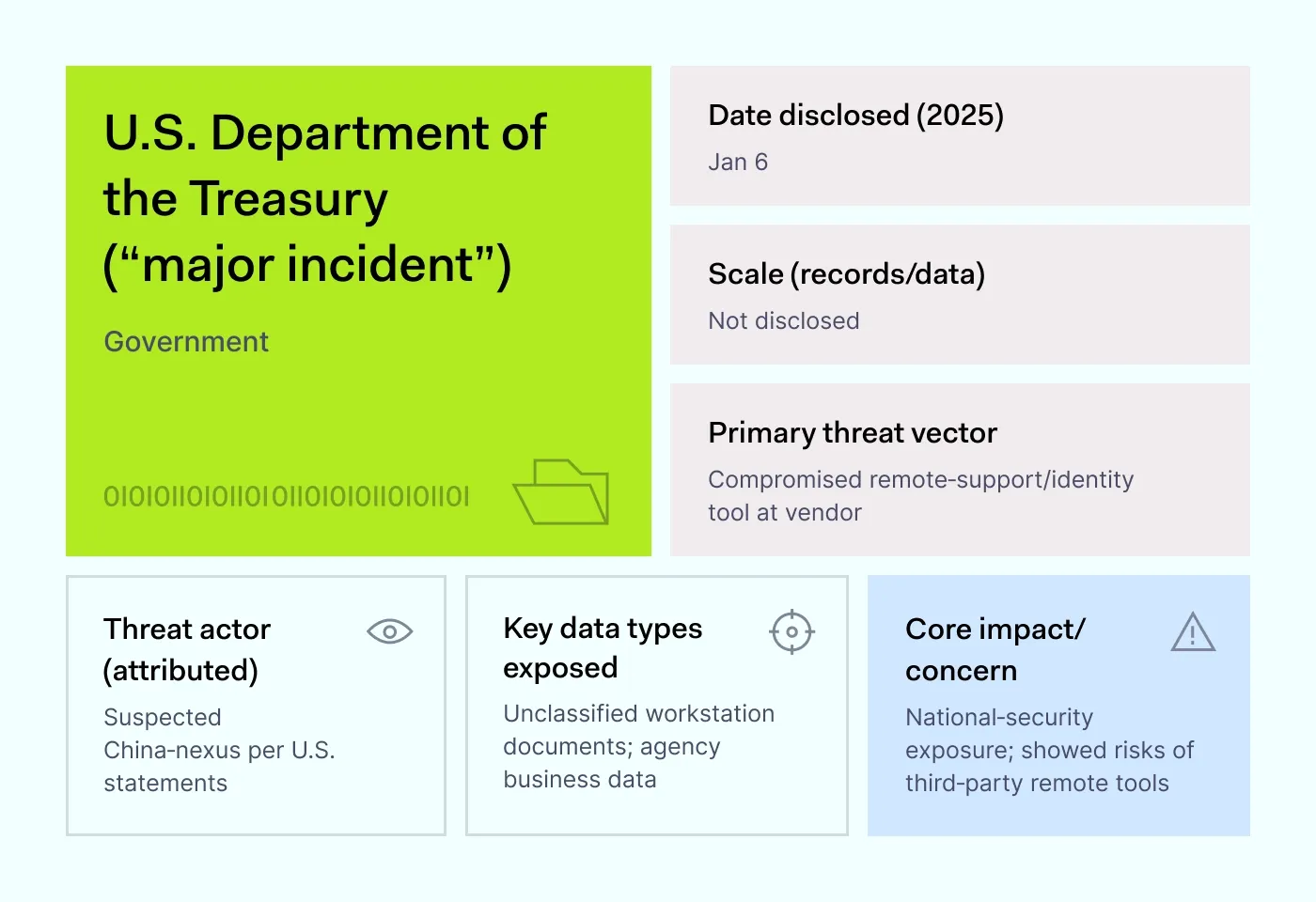
The travel industry has been hit repeatedly by breaches. Marriott revealed a 2014 breach that wasn't discovered until 2018, affecting hundreds of millions of guests. Cathay Pacific confirmed a breach exposing 9.4 million customer records. Korean Air, Thai Airways, and numerous hotel chains have all suffered major breaches. The pattern is consistent: travel companies hold valuable data, are sometimes lax about security, and become attractive targets for attackers.
What makes travel companies particularly vulnerable is the complexity of their technology ecosystems. They integrate with payment processors, airlines, booking systems, hotel chains, rental car companies, and third-party vendors. Each integration represents a potential security weak point. Each vendor relationship adds complexity to security management.
The travel industry is also global, which complicates security and compliance. A travel company operating in 50 countries has to comply with 50 different data protection laws. GDPR in Europe, CCPA in California, LGPD in Brazil, PIPEDA in Canada, and dozens of other frameworks with different requirements. This complexity sometimes leads to security corners being cut because companies are overwhelmed by regulatory complexity.
Mobile booking has also expanded the attack surface. Millions of people now book flights through mobile apps. These apps often store cached data including payment information, making them attractive targets for mobile malware or device compromises. Someone with malware on their phone could have their payment information extracted even if the travel company's servers are secure.
Elasticsearch: Why It's a Common Breach Culprit
Elasticsearch has become synonymous with exposed databases. The search engine is incredibly powerful and useful for its intended purpose: searching and analyzing large datasets. But that power comes with complexity, and complexity creates security risks.
Elasticsearch was originally designed for internal use within organizations. It wasn't built with internet security in mind. The default configuration has minimal security: no authentication, no encryption, no access controls. This worked fine when instances only existed on internal networks.
But as cloud computing became prevalent, companies started running Elasticsearch in the cloud. They'd spin up instances on AWS, Azure, or Google Cloud, expose them to the internet, and assume they'd configure security later. Many companies forgot to configure security at all. Or they configured it incorrectly. Or they misconfigured their cloud security groups.
Researchers periodically scan the internet for exposed databases. Elasticsearch instances are high-value targets. They often contain detailed, searchable data. A researcher can connect to an exposed instance and start querying data immediately without authentication. They can export entire datasets using basic command-line tools.
Elasticsearch's popularity among developers means it's commonly deployed. If even a small percentage of deployments are misconfigured, that creates a large attack surface. Add in the fact that Elasticsearch data is often sensitive (payment information, logs, user data) and you have a recipe for major breaches.
Vendors have gotten better about security defaults in recent years. Newer versions of Elasticsearch require authentication by default. But many companies still run older versions, or they upgrade but don't enable all security features, or they enable features but misconfigure them.
Regulatory Implications and Legal Consequences
The One Fly breach will trigger regulatory investigations and legal liability. Depending on the jurisdictions affected, One Fly could face significant penalties.
In Europe, the GDPR gives data protection authorities the power to fine companies up to 20 million euros or 4% of annual revenue, whichever is higher, for serious violations. The breach exposed personal data (names, dates of birth, ID document numbers) without adequate security measures. This is a clear GDPR violation. One Fly could face substantial fines even if they weren't required to register with any specific European regulator, because they processed data belonging to European residents.
In California, CCPA allows for statutory damages of
Federal law in the US doesn't set statutory damages for data breaches, but it does require breach notification. One Fly will need to notify affected consumers, potentially costing millions in notification expenses alone. They'll also face inevitable class-action lawsuits from affected consumers claiming damages for fraud, negligence, and violation of state consumer protection laws.
Beyond financial penalties, there are reputational consequences. Airlines and travel agencies using One Fly will face pressure from customers to switch to more secure vendors. Business partners will audit One Fly's security practices and potentially terminate relationships. Customer trust, once broken in the security space, is extremely difficult to rebuild.
Regulatory investigations also require significant resources. One Fly will need to hire external security firms to investigate the breach, hire law firms to manage regulatory inquiries and litigation, and spend significant internal resources on remediation. The total cost of managing a breach at this scale typically runs into the millions of dollars.
Best Practices for Preventing Similar Breaches
Companies handling sensitive data should learn from One Fly's failure. Prevention requires attention to multiple areas.
Infrastructure Security: Never expose databases directly to the internet. Always run databases behind firewalls or VPNs. Restrict network access to specific IP addresses. Disable unnecessary ports and services. For cloud deployments, use security groups and network access lists to ensure only authorized systems can connect to databases.
Authentication and Authorization: Every service exposed to any network should require authentication. Use strong authentication mechanisms. Implement role-based access controls so that users only have access to data they need. Regularly audit who has access to what.
Data Handling: Never log sensitive data directly to files or databases that are meant to be kept long-term. If debugging requires sensitive data visibility, use logging services with automatic redaction or masking. Implement data classification systems so teams understand what data is sensitive and how to handle it.
Encryption: Encrypt sensitive data in transit using TLS. Encrypt sensitive data at rest using strong encryption. Use key management systems to protect encryption keys separately from encrypted data. Even if a database is compromised, properly encrypted data remains protected.
Monitoring and Alerting: Monitor for suspicious access patterns. Alert on unusual database queries or unexpected data access. Implement logging that tracks who accessed what data and when. This logging itself needs to be secured and monitored.
Incident Response: Have documented procedures for security incidents. Know who to contact. Know how to preserve evidence. Know how to assess the scope of a breach quickly. Incident response preparedness means the difference between discovering a breach weeks after it starts versus discovering it immediately.
Security Training: Ensure developers understand security basics. Most breaches like One Fly's happen because developers didn't understand PCI-DSS or basic database security. Security training should be regular and practical, not just annual compliance theater.

The Future of Travel Tech Security
The One Fly breach will likely accelerate security improvements across the travel industry. Customers will demand better security. Regulators will scrutinize more carefully. Vendors will face stricter security requirements from their customers.
We're likely to see travel companies investing more in security infrastructure, hiring security professionals, and implementing more rigorous security practices. The cost of breaches is becoming prohibitively expensive, and the reputational damage is severe.
We'll probably also see more consolidation in travel tech. Smaller companies like One Fly will face pressure to improve security or be acquired by larger, better-resourced competitors. The travel tech landscape might shift toward fewer, larger companies with better security capabilities.
International cooperation on cybersecurity is likely to improve. Regulators across different countries are sharing information about breaches and best practices. Companies that operate globally will need to meet the highest standards across all jurisdictions.
Triangulation of security will become standard. Rather than relying on a single vendor, travel companies will diversify their technology partners. Rather than having all booking data flow through a single platform, they'll use multiple platforms to reduce the impact of any single breach.
Long-Term Consequences for Affected Individuals
For the people whose data was exposed, the consequences extend far beyond the initial fraud or identity theft.
Identity theft victims often experience lasting anxiety about their financial security. Even after resolving fraudulent accounts and recovering stolen funds, the experience creates persistent worry about future compromise. Checking credit reports becomes a regular habit. Monitoring financial accounts becomes obsessive. The trust in financial systems doesn't fully return.
Payment fraud can also affect creditworthiness. If fraudulent accounts are opened and then go unpaid before the victim discovers them, those accounts can negatively impact credit scores. Disputing accounts and repairing credit takes time and effort.
International travelers may face complications for years. If their identity information was used fraudulently in another country, they might encounter red flags at border control. Some countries maintain fraud databases that can flag individuals in immigration systems. Clearing your name from these databases can be extremely difficult.
There's also the psychological impact. Knowing that your personal and financial information was compromised by a company you trusted (even indirectly) erodes confidence in digital systems generally. People become more skeptical of online shopping, more hesitant to provide payment information, more worried about privacy.
This is why breach notification and remediation services matter. Companies offer credit monitoring, identity theft protection, and fraud resolution services after breaches. While they don't undo the harm, they provide some mitigation and can help detect problems early.

FAQ
What is the One Fly data breach?
The One Fly data breach is a 2025 security incident where thousands of sensitive customer records were exposed through an unsecured Elasticsearch database. The exposed data included names, dates of birth, ID document details, flight information, full credit card numbers in plaintext, and authentication tokens. One Fly, a travel technology company serving over 100 airlines and major travel agencies worldwide, failed to implement basic security measures like access controls or authentication on their Elasticsearch instance.
How many people were affected by the One Fly breach?
Cybernews researchers identified approximately 10,000 ID records and 6,000 payment cards during their investigation in October 2025. However, these numbers represent only what was documented during the research period. The actual number of affected individuals could be significantly larger since the database was potentially accessible for weeks or months before discovery. Given One Fly's scale and the number of bookings flowing through their systems, the total number of affected customers could number in the hundreds of thousands.
What types of data were exposed in the One Fly breach?
The exposed data included comprehensive personal and financial information: full names, dates of birth, identity document details including passport and driver's license numbers, flight booking information (airlines, flight numbers, ticket prices, destination airports), full credit card details in plaintext (card numbers, expiration dates, CVV codes), and JWT authentication tokens used for internal system access. This combination of data makes the breach particularly dangerous for identity theft and fraud.
What should I do if my information was exposed in the One Fly breach?
If you booked flights through One Fly or through travel agencies that use One Fly, contact your credit card issuer to request a new card with a new number. Place a fraud alert with the credit bureaus (Equifax, Experian, Trans Union) by visiting Annual Credit Report.com or contacting them directly. Review your credit reports for unauthorized accounts or inquiries. Monitor your credit card statements closely for unauthorized charges. Consider placing a credit freeze if you're concerned about identity theft. Be cautious of phishing emails claiming to be from One Fly or related companies.
Why was One Fly's security so inadequate?
One Fly's security failures were fundamental operational negligence. Elasticsearch instances should never be exposed to the internet without authentication and access controls. The fact that One Fly was logging full payment card details directly to Elasticsearch violates PCI-DSS requirements for anyone handling credit card data. The combination of logging sensitive data and failing to secure the database suggests either complete lack of security awareness or willful negligence in prioritizing security. This wasn't exploitation of a sophisticated vulnerability but failure to implement basic, well-documented security practices.
Could this breach have been prevented?
Absolutely. The breach could have been prevented through straightforward security measures: enabling authentication on Elasticsearch, implementing IP whitelisting to restrict access to internal networks only, using encryption for data in transit, not logging sensitive payment data to searchable databases, implementing proper access controls, and conducting regular security audits. These are standard industry practices documented in Elasticsearch's security guide and PCI-DSS compliance requirements. The breach represents a failure to implement known, well-established security fundamentals.
What are the long-term consequences of this breach?
Long-term consequences include potential fraudulent charges on exposed payment cards requiring dispute and credit card replacement, risk of identity theft that could manifest months or years after the breach, potential difficulty with international travel if identity information was used fraudulently in other countries, credit score damage if fraudulent accounts are opened and unpaid, regulatory fines against One Fly under GDPR and CCPA, class-action lawsuits from affected consumers, reputational damage to One Fly that may result in loss of customers and business partners, and broader erosion of trust in travel technology companies.
How does this breach affect travel agencies and airlines using One Fly?
Travel agencies and airlines using One Fly face significant complications. They must notify their own customers of the breach even though the breach occurred at a vendor they depend on. They face regulatory scrutiny regarding their vendor management practices. They'll likely face customer pressure to switch to more secure vendors. They must audit their vendor security practices to ensure similar failures don't occur with other vendors. Some customers may reduce their trust in these platforms due to vendor failures. The industry as a whole faces increased regulatory requirements and security standards that will raise operating costs.
What should companies do to prevent similar breaches?
Companies should implement infrastructure security by never exposing databases directly to the internet, always using firewalls and network access restrictions. They should require authentication and authorization for all systems with proper role-based access controls. They should never log sensitive data directly to long-term storage and should use automated redaction for debugging scenarios. They should encrypt sensitive data both in transit and at rest. They should implement monitoring and alerting for suspicious access patterns. They should have documented incident response procedures. They should provide regular security training to developers. They should conduct regular security audits. They should implement data classification systems so teams understand how to handle sensitive information appropriately.
Why is Elasticsearch frequently involved in data breaches?
Elasticsearch is involved in many breaches because it's a powerful, popular search engine that wasn't originally designed for internet security. Default configurations have no authentication or access controls, which is fine for internal use but dangerous on the internet. Many companies moved Elasticsearch to the cloud but forgot to implement security or misconfigured cloud security settings. The tool's popularity means many instances exist, and if even a small percentage are misconfigured, that creates a large attack surface. Elasticsearch data is often sensitive, making exposed instances valuable targets for attackers. Newer versions have better security defaults, but many companies still run older versions without security enabled.
When did the One Fly breach occur and when was it discovered?
Evidence suggests the data exposure began in early October 2025, though the exact date remains unclear. Cybernews researchers discovered the breach after the fact when they identified unsecured Elasticsearch instances containing sensitive data. The timing gap between when the breach started and when it was discovered is significant because it indicates the data was potentially accessible and being exfiltrated for an unknown period of time before being found by researchers. The exact duration of the exposure window remains undetermined.
Conclusion: Learning From One Fly
The One Fly breach is a stark reminder that in 2025, basic security failures still cause massive damage. This wasn't a cutting-edge cyberattack. It was negligence. A database exposed to the internet with no authentication. Sensitive payment data logged in plaintext. No access controls. No monitoring. No incident response preparedness.
For One Fly, the consequences will be severe. They face regulatory fines, litigation, loss of customers, and reputational damage that may prove insurmountable. Travel agencies and airlines that depend on them face their own complications. Customers whose data was exposed face years of potential fraud concerns and identity theft risk.
But the broader lesson is critical for every company handling sensitive data. Security isn't optional. It's not something you add after building your infrastructure. It's foundational.
The basic practices that would have prevented this breach are well-known, well-documented, and widely available. Secure databases with authentication. Don't log sensitive data. Encrypt everything. Monitor for unauthorized access. Implement access controls. Conduct regular audits. These aren't expensive, complicated practices. They're blocking and tackling.
Yet companies still fail at these basics with alarming frequency. Elasticsearch instances get exposed regularly. Databases with no authentication continue to leak data. Payment information gets logged in plaintext. It's frustrating because it's preventable.
The travel industry will adapt. Security will improve. Customers will demand better protection. Regulators will enforce higher standards. Vendors will face stricter security requirements. But it will take breaches like One Fly to drive that change.
For individuals affected by this breach, the path forward is clear: protect your financial accounts, monitor your credit, be prepared for the possibility of fraudulent activity, and take advantage of offered remediation services. It's not a fun position to be in, but taking action now can prevent far worse consequences later.
For companies, the lesson is equally clear: the cost of security is dramatically lower than the cost of breaches. Invest in security infrastructure, hire security professionals, implement best practices, and take security seriously. Because in 2025, there's no excuse for the negligence that created the One Fly breach.
Key Takeaways
- OneFly exposed at least 10,000 ID records and 6,000 payment cards through an unsecured Elasticsearch database in October 2025
- Full credit card details in plaintext, identity documents, and JWT authentication tokens were accessible without any authentication or access controls
- This was a preventable breach caused by fundamental operational negligence, not sophisticated hacking techniques
- Affected customers should place fraud alerts, monitor credit reports, and request new payment cards immediately
- OneFly faces significant regulatory fines under GDPR and CCPA, plus inevitable class-action litigation from affected customers
Related Articles
- Stalkerware Data Breach: 500,000 Records Leaked by Hacktivists [2025]
- BridgePay Ransomware Attack: What Happened and How to Protect Your Business [2025]
- Flickr Data Breach 2025: What Was Stolen & How to Protect Yourself [2025]
- Conduent Data Breach 2025: What Millions of Americans Need to Know [2026]
- Harvard and UPenn Data Breaches: What You Need to Know [2025]
- Substack Data Breach Exposed Millions: What You Need to Know [2025]
![OneFly Data Breach 2025: Full Payment Details Exposed [2025]](https://tryrunable.com/blog/onefly-data-breach-2025-full-payment-details-exposed-2025/image-1-1770912534506.jpg)



