Introduction
In a world where data is the new currency, breaches can be catastrophic. Optimizely, a prominent ad tech firm, recently fell victim to a sophisticated data breach, potentially affecting around 10,000 companies. This incident highlights the persistent vulnerabilities even within advanced digital platforms.
TL; DR
- Breach Overview: Optimizely experienced a data breach impacting approximately 10,000 companies.
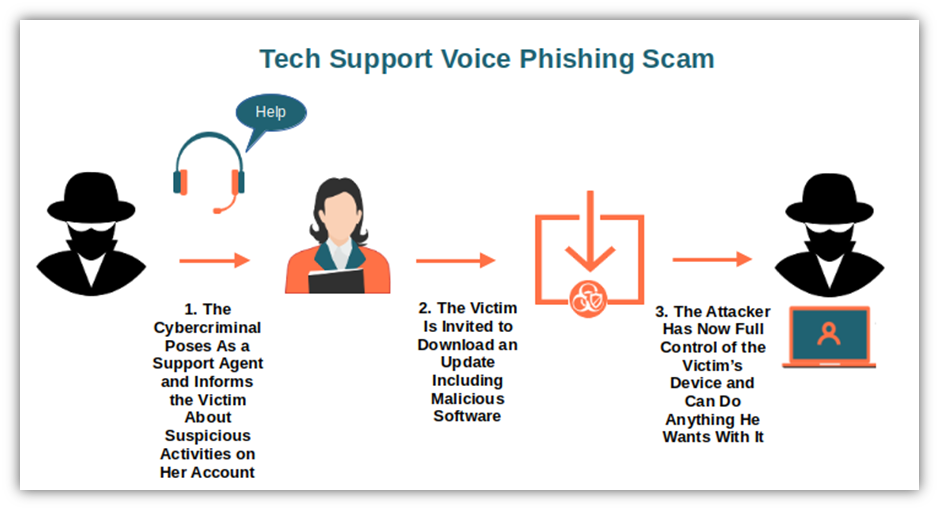
- Methodology: Attackers used a voice-phishing attack to access CRM records and internal documents.
- Data Compromised: No sensitive data was confirmed stolen, but basic customer contact info was leaked.
- Culprits: The attack resembles tactics used by the group Shiny Hunters.
- Response Strategy: Optimizely is enhancing security measures and advising clients on best practices.
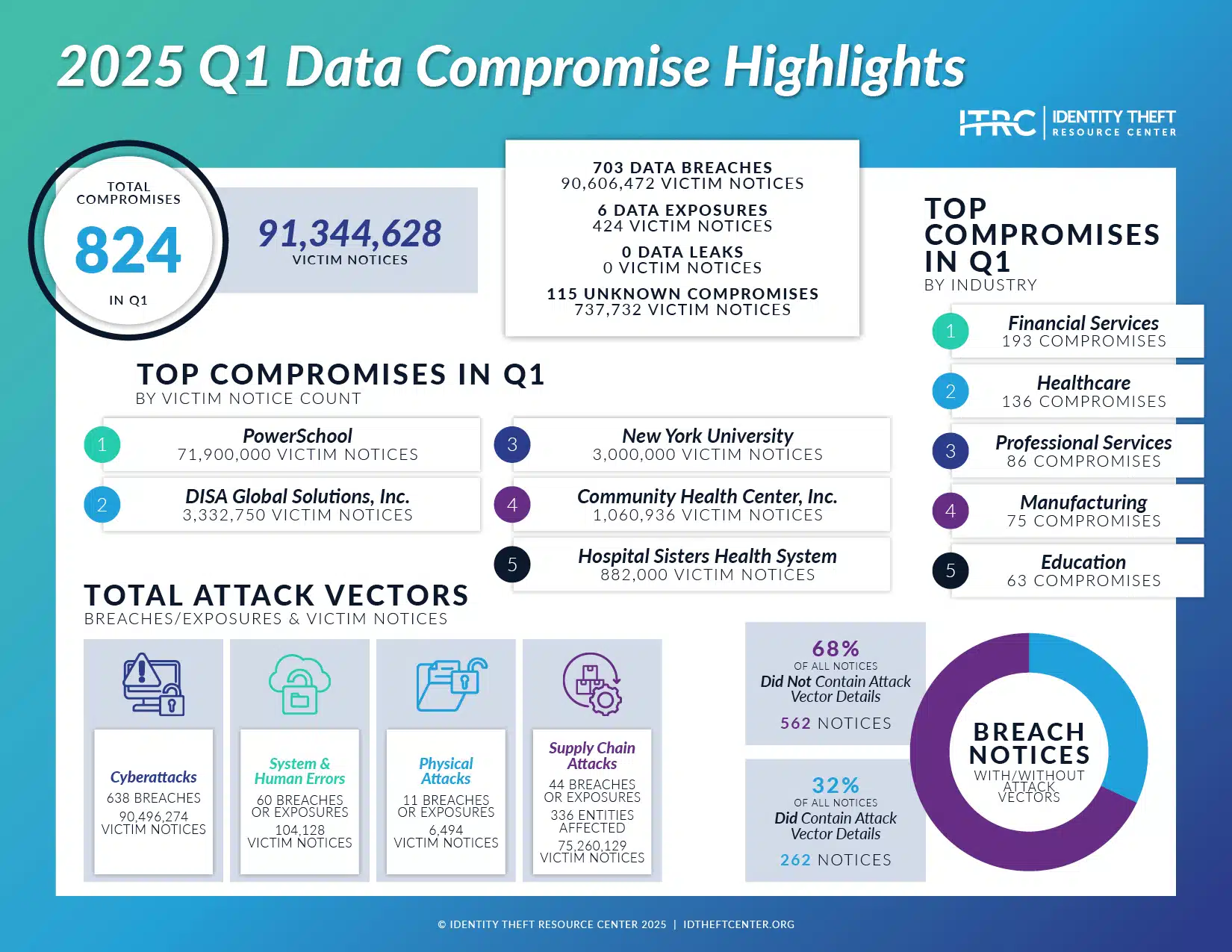
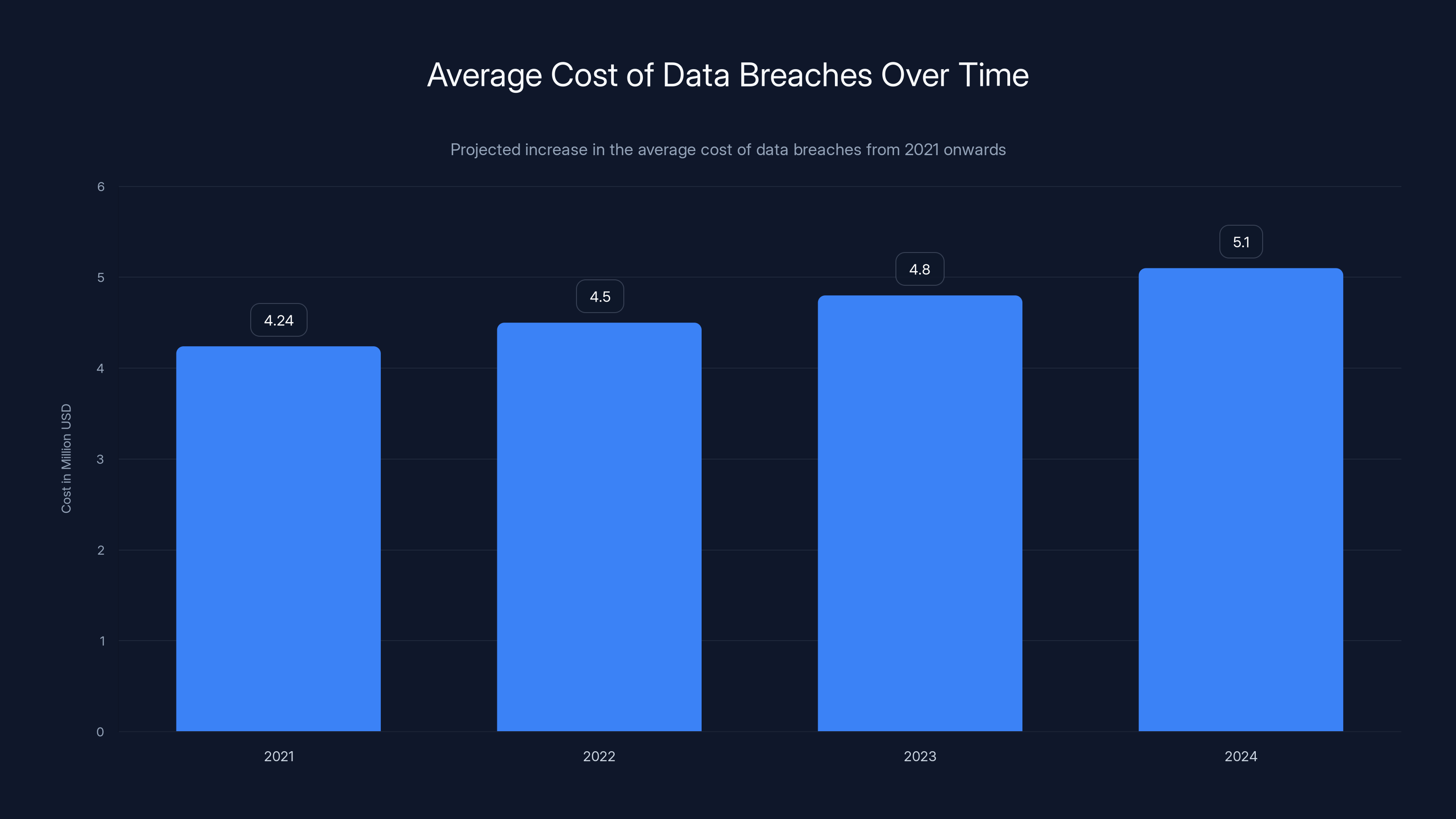
The average cost of data breaches is projected to rise from
The Anatomy of the Breach
Optimizely's Role in Digital Marketing
Optimizely is more than just another ad tech firm. Known for its robust digital experience platform, it helps businesses manage websites and marketing campaigns to boost conversions and customer engagement. Its tools for A/B testing and experimentation are industry benchmarks.
The Attack Unfolds
The breach occurred on February 11, when attackers executed a sophisticated voice-phishing (vishing) campaign. This method involves manipulating victims into revealing confidential information over the phone, often impersonating trusted entities.
What Was Accessed?
While no sensitive data was reportedly stolen, attackers accessed CRM records and internal documents. The leaked information primarily included basic customer contact data.
Who Are the Shiny Hunters?
The breach bears similarities to recent campaigns by the notorious hacking group Shiny Hunters. Known for targeting large corporations, this group specializes in data theft and has been linked to other high-profile breaches.
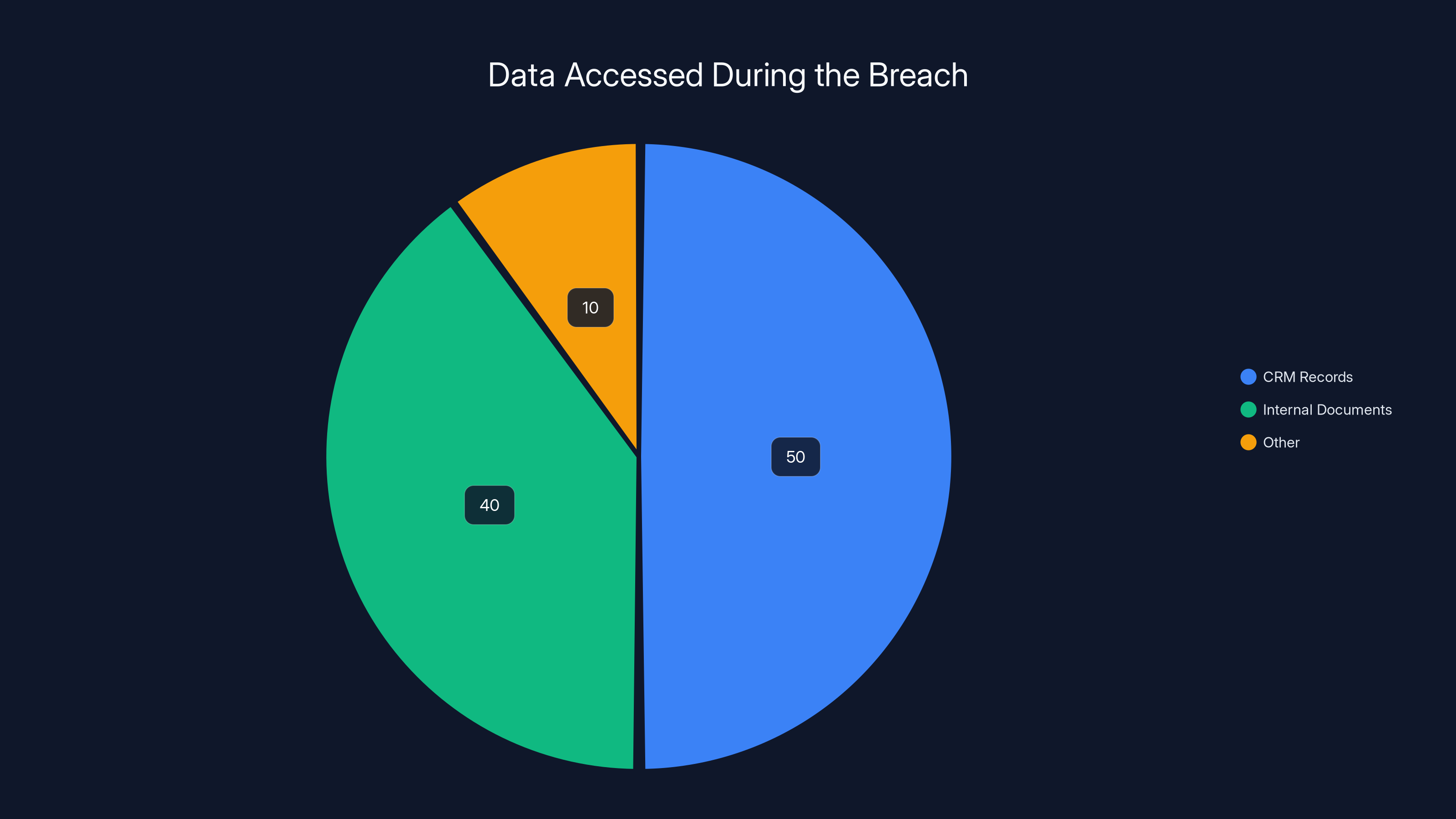
The breach primarily involved access to CRM records (50%) and internal documents (40%), with a small portion categorized as other (10%). Estimated data.
Implications for Businesses
The Impact on Affected Companies
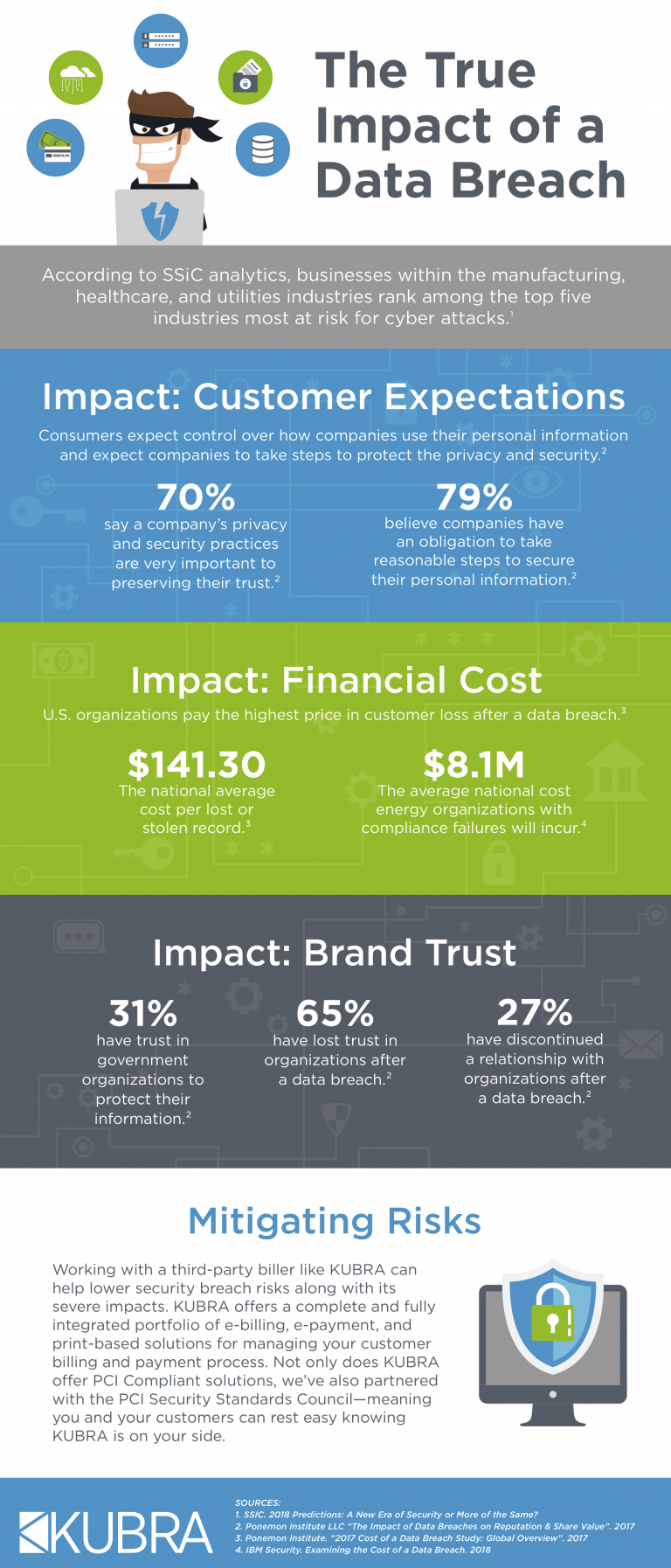
For the 10,000 companies potentially affected, the breach is a wake-up call. While the stolen data might seem trivial, it can lead to phishing attacks, identity theft, and erosion of customer trust.
The Cost of Data Breaches
Data breaches are costly. Beyond immediate financial losses, companies face reputation damage and loss of customer confidence. According to IBM, the average cost of a data breach was $4.24 million in 2021, a figure likely to rise.
Optimizely's Response and Mitigation Strategies
Immediate Actions Taken
Upon discovering the breach, Optimizely immediately alerted affected companies and launched an internal investigation. They also engaged cybersecurity experts to analyze the breach's scope and mitigate further risks.
Enhancing Security Protocols
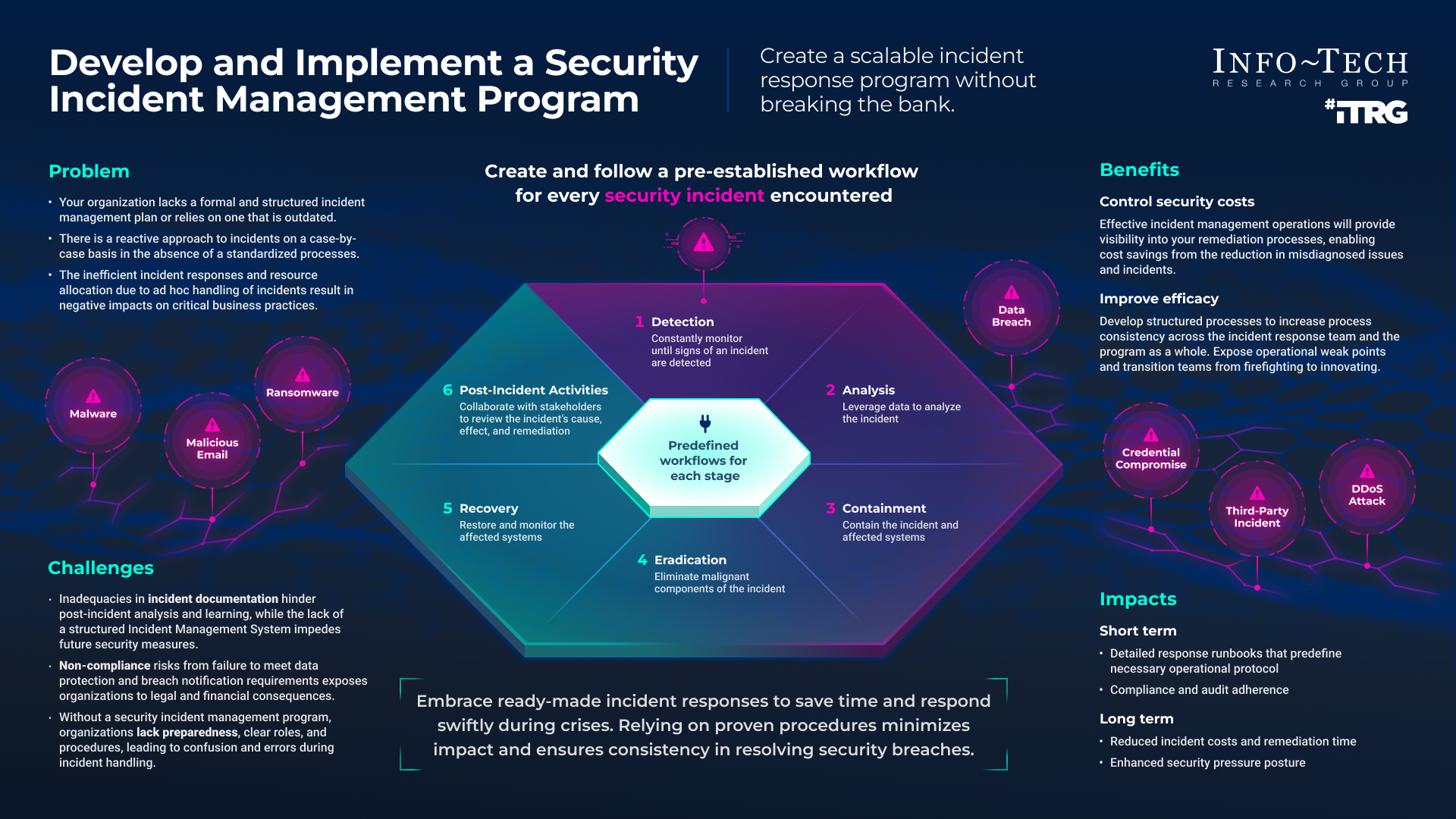
Optimizely is fortifying its security infrastructure. They're increasing network monitoring, strengthening access controls, and conducting regular security audits.
Communication with Affected Parties
Effective communication is crucial in breach scenarios. Optimizely is providing regular updates to its clients, reassuring them of the steps being taken to protect their data.
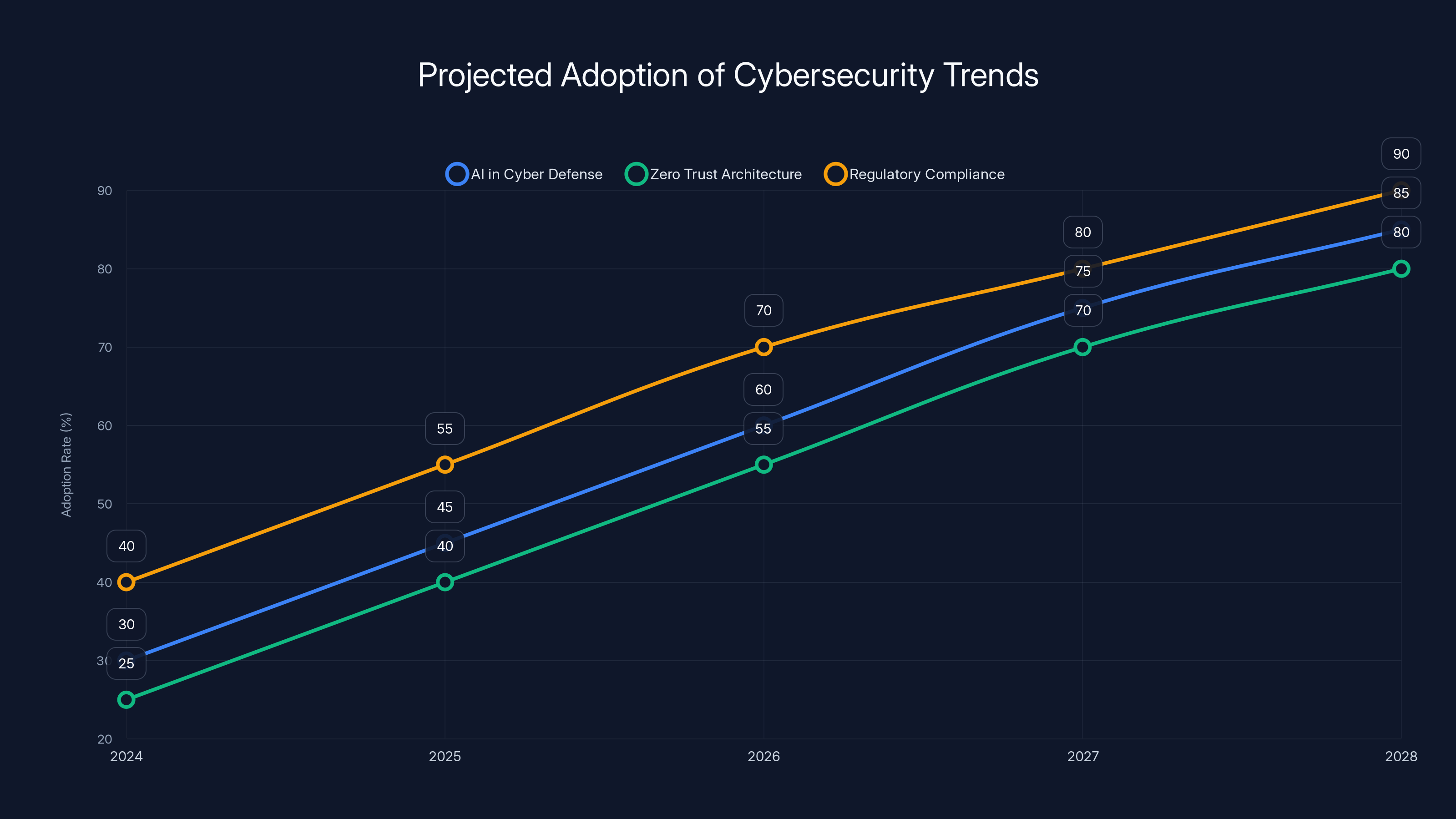
Estimated data suggests that AI in cyber defense, Zero Trust architecture, and regulatory compliance will see significant adoption growth over the next five years.
Best Practices for Safeguarding Your Business
Implementing Stronger Authentication
Businesses should adopt multi-factor authentication (MFA). This adds an extra layer of security, making unauthorized access significantly more challenging.
Regular Security Audits
Conduct regular audits to identify vulnerabilities in your systems. External audits provide an unbiased perspective and can uncover hidden weaknesses.
Employee Training and Awareness
Training employees to recognize phishing attempts is essential. Regular workshops and simulated phishing tests can keep security top of mind.
Data Encryption
Encrypt sensitive data both in transit and at rest. This ensures that even if data is accessed, it remains unreadable without the proper decryption keys.
Future Trends in Cybersecurity
Rise of AI in Cyber Defense
AI and machine learning are increasingly being integrated into cybersecurity strategies. They offer predictive analytics to anticipate and mitigate threats before they materialize.
Zero Trust Architecture
Adopting a Zero Trust model, where every access request is verified regardless of its origin, is becoming standard practice.
Increased Regulatory Scrutiny
Governments worldwide are implementing stricter regulations to protect consumer data, such as the GDPR in Europe. Companies must stay informed and compliant to avoid hefty fines.

Conclusion
The Optimizely data breach serves as a stark reminder of the ever-present cybersecurity risks. By implementing robust security measures and staying informed about emerging threats, businesses can better protect their data and maintain customer trust.
FAQ
What is a data breach?
A data breach occurs when unauthorized individuals gain access to sensitive information. It can result in the theft or exposure of personal, financial, or corporate data.
How can voice-phishing attacks be prevented?
Preventing vishing attacks involves training employees to recognize suspicious calls, verifying the identity of callers, and using secure communication channels.
What are the long-term effects of a data breach?
Long-term effects include financial losses, reputation damage, regulatory penalties, and loss of customer trust, which can take years to rebuild.
Why is multi-factor authentication important?
MFA enhances security by requiring multiple forms of verification before granting access, making it harder for attackers to breach systems.
How does the Zero Trust model improve security?
Zero Trust improves security by eliminating the assumption that internal networks are safe, requiring continuous verification of every access request.
Internal Links
Key Takeaways
- Sophisticated Attacks: Even top-tier firms can fall victim to advanced phishing tactics.
- Comprehensive Response: Swift action and transparency are critical in breach situations.
- Proactive Measures: Regular audits and employee training are essential.
- Technological Advancements: AI and Zero Trust are key trends in future cybersecurity.
- Regulatory Compliance: Staying compliant with data protection laws is non-negotiable.
Future Recommendations
- Invest in AI-driven security tools: These can detect anomalies and potential threats faster than traditional methods.
- Adopt a proactive security stance: Continuous monitoring and improvement of security protocols are necessary.
- Engage in industry collaboration: Sharing threat intelligence with peers can help preempt attacks.
By understanding the intricacies of data breaches and adopting a holistic security approach, businesses can better protect themselves from future threats.

Related Articles
- CarGurus Data Breach: 1.7M Records Stolen by ShinyHunters [2025]
- Figure Data Breach: What Happened to 967,000 Customers [2025]
- Harvard and UPenn Data Breaches: What You Need to Know [2025]
- ShinyHunters Hits Wynn Resorts: $1.5M Ransomware Demand [2025]
- Harvard & UPenn Data Breaches: Inside ShinyHunters' Attack [2025]
- Panera Bread Data Breach: 14 Million Records Exposed [2025]
![Optimizely Data Breach: Implications, Response, and Future Safeguards [2025]](https://tryrunable.com/blog/optimizely-data-breach-implications-response-and-future-safe/image-1-1771950865903.jpg)



