Prompt Spy: How AI-Powered Android Malware Works [2025]
Introduction: When AI Becomes a Weapon
Last year, a new kind of threat emerged that nobody was really expecting. Not because the attack itself was sophisticated in the traditional sense, but because it weaponized something we all use daily: AI.
Security researchers at ESET uncovered Prompt Spy, the first known Android malware to use Google's Gemini AI as part of its core execution strategy. This isn't just another piece of malware that happened to involve AI. Instead, the malware actively uses Gemini to understand your phone's interface, make decisions about what to do next, and most importantly, keep itself locked in place so you can't remove it.
Here's what makes this genuinely unsettling: the malware doesn't steal your data through a backdoor. It doesn't exploit a zero-day vulnerability. Instead, it mimics what you'd do if you wanted to keep an app running, but automates the entire process using AI. It watches your screen, interprets the buttons and menus, and tells itself what to click next. It's like malware that learned to think.
The malware primarily targeted Spanish-speaking users in Argentina, arriving through fake update apps. Once installed, it requests Accessibility Service permissions, which is where things get really dangerous. From that point forward, the malware can see everything on your screen, simulate your touches, and communicate with Google's Gemini API to decide what to do next.
What's particularly concerning is that this represents a fundamental shift in how we should think about security. For years, we've assumed that AI tools are just tools—powerful, yes, but ultimately neutral. Prompt Spy proves that assumption is incomplete. When an attacker controls both the AI model and the prompt being sent to it, they can create a system that's far more flexible and adaptive than traditional malware.
In this guide, we'll break down exactly how Prompt Spy works, why using Gemini makes it uniquely dangerous, what vulnerabilities it exploits, and most importantly, what you can do to protect yourself. By the end, you'll understand not just this specific threat, but why AI-powered malware represents a new category of risk.

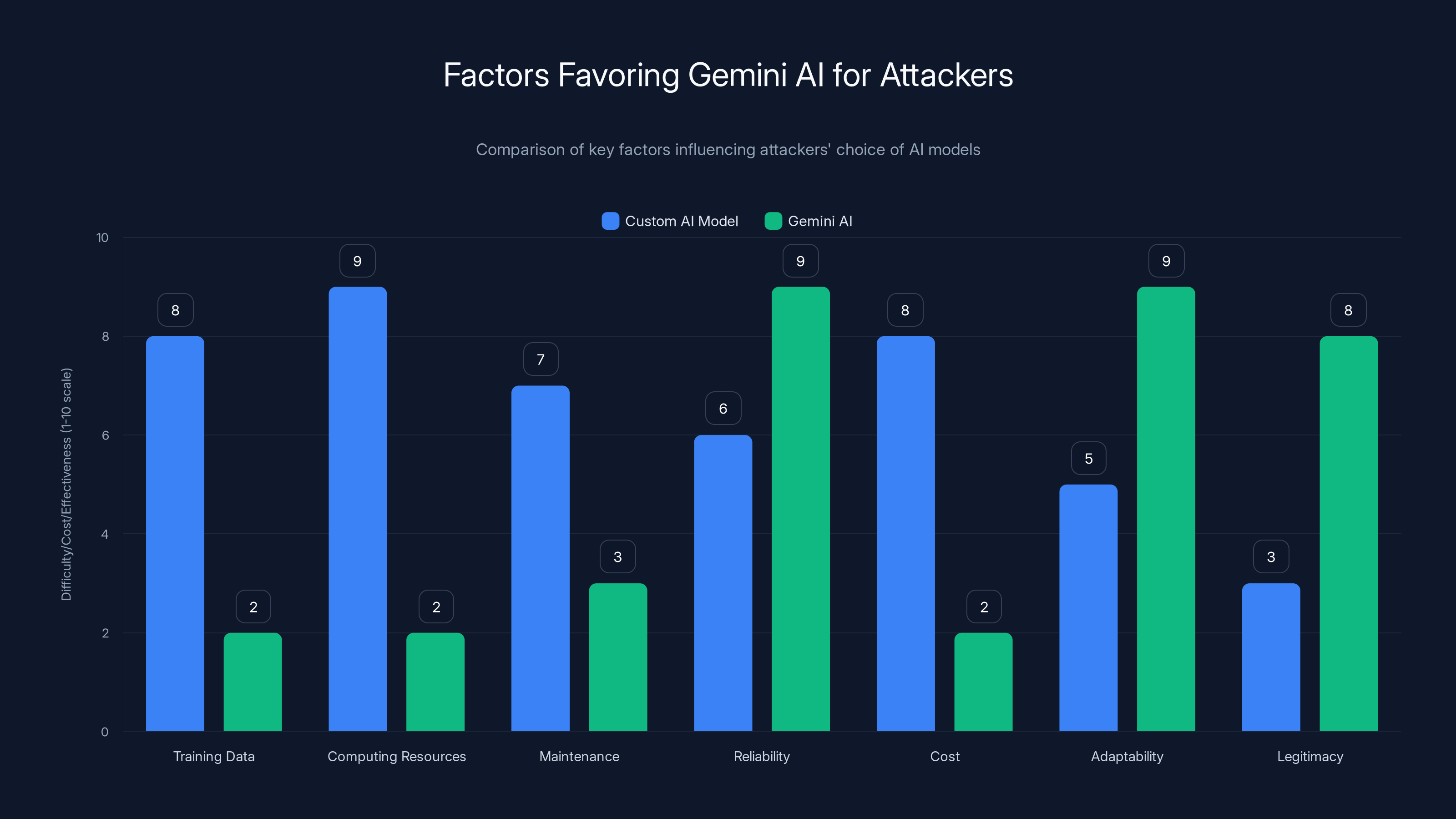
Gemini AI offers attackers a more cost-effective, reliable, and adaptable solution compared to building a custom AI model, with lower difficulty in training and maintenance. (Estimated data)
TL; DR
- Prompt Spy is the first Android malware to use Google Gemini AI to maintain persistence and automate evasion tactics
- The malware sends screen data to Gemini which returns step-by-step instructions for blocking removal and staying installed
- It targets Spanish-speaking users in Argentina through fake app updates that mimic legitimate software
- Once installed, it captures passwords, records video, and takes screenshots using a built-in VNC remote access module
- You can't remove it through normal means because it overlays transparent elements on uninstall buttons and re-enables itself automatically
- Safe Mode is your best defense along with antivirus scanning and permission audits
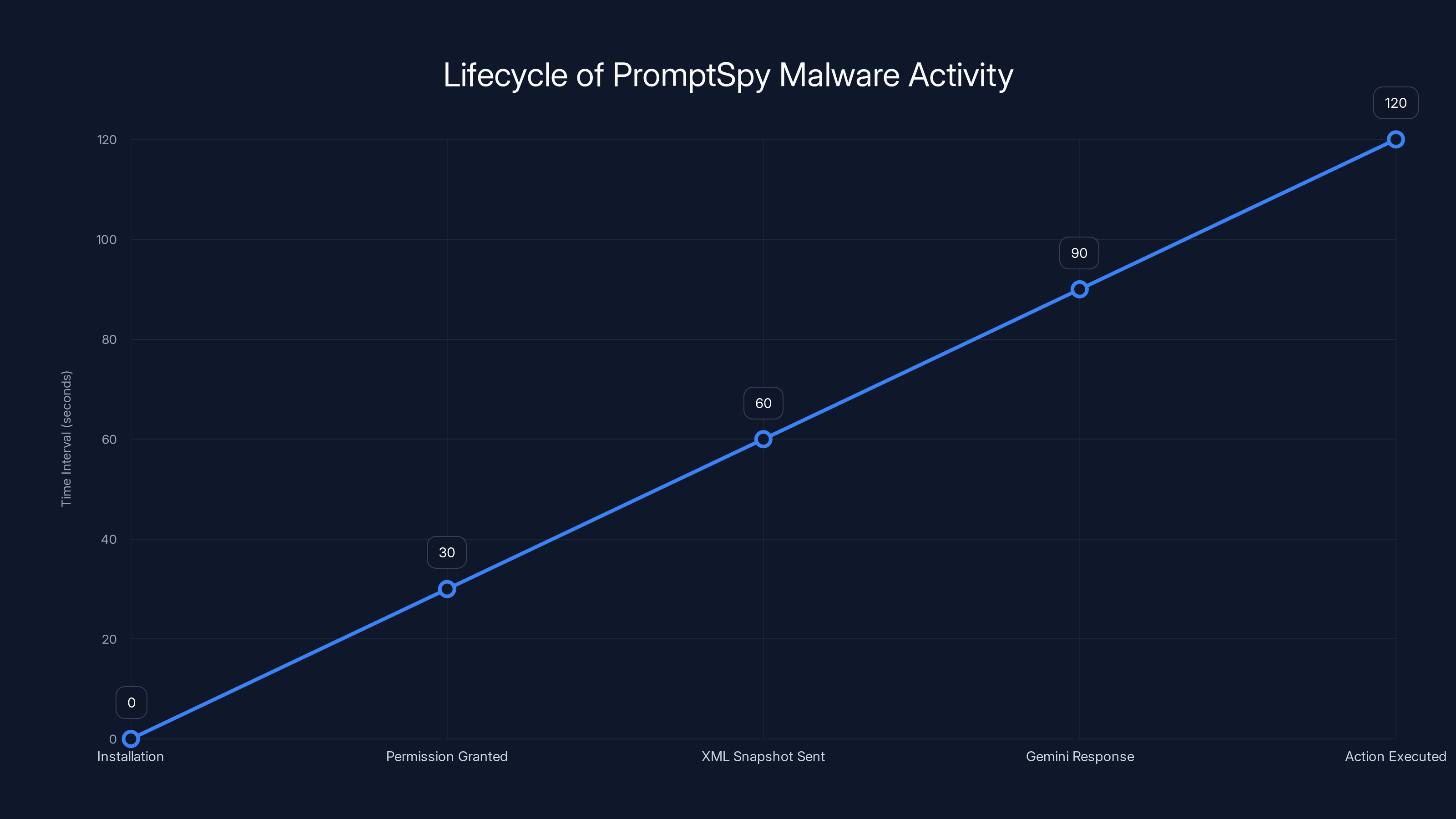
Estimated data shows the sequence of actions from installation to execution by PromptSpy using Gemini AI. Each stage occurs within a short time frame, highlighting the efficiency of the malware.
What Is Prompt Spy, and Why Should You Care?
Prompt Spy isn't malware in the traditional sense. It doesn't lock your files and demand Bitcoin. It doesn't turn your phone into a brick. Instead, it's something subtler and arguably more dangerous: a persistence mechanism disguised as a utility.
The malware's primary goal is to stay installed on your device without you being able to remove it. Everything else—the password theft, the screen recording, the remote access—flows from that single objective. To achieve this, Prompt Spy evolved beyond the techniques that traditional malware uses. Instead of hiding in system folders or exploiting kernel vulnerabilities, it uses AI to automate the very actions a human might take to defend their own device.
When you try to uninstall Prompt Spy through Settings, the malware sees this happening in real-time. It interprets the UI elements on your screen. Then it sends that information to Google's Gemini API with a hardcoded prompt that essentially says: "The user is trying to remove me. What should I do to stop them?"
Gemini responds with specific instructions. Not general advice—specific gestures and taps. The malware then executes those instructions, clicking invisible buttons, swiping in precisely calculated directions, and reactivating itself before the uninstall can complete.
This is fundamentally different from how malware has operated for the past two decades. Previous Android malware relied on exploiting specific bugs, hiding from detection, or social engineering users into granting dangerous permissions. Prompt Spy does all of those things, yes. But it adds a layer of adaptive automation that makes it far harder to remove once it's installed.
The malware was discovered in early 2024 and appears to have targeted roughly a few hundred users, primarily in Argentina. While the numbers are relatively small, the implications are enormous. Prompt Spy proves that AI can be weaponized not as a tool for attack, but as a tool for persistence and evasion.
How Prompt Spy Uses Gemini AI: The Technical Deep Dive
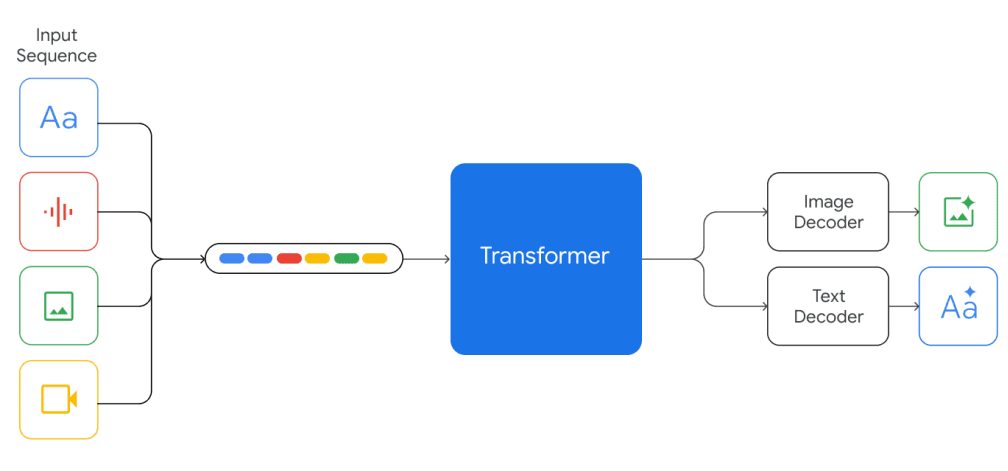
Understanding how Prompt Spy actually uses Gemini requires understanding how accessibility services work on Android, and then how that intersects with AI APIs.
When you grant an app Accessibility Service permissions, you're essentially giving it the ability to see your entire screen as structured data (called the "accessibility tree") and simulate touches, swipes, and keyboard input. This permission exists for legitimate reasons: screen readers for the blind, voice control apps, automation utilities. The problem is that once granted, it's nearly impossible to detect whether an app is using these powers legitimately or maliciously.
Prompt Spy requests this permission immediately after installation. Most users don't even notice because the malware's dropper application disguises itself as a system update. Once the permission is granted, the malware continuously captures XML snapshots of your device's screen. These aren't full screenshots that appear in your photo library. They're structured data representations of what's currently being displayed.
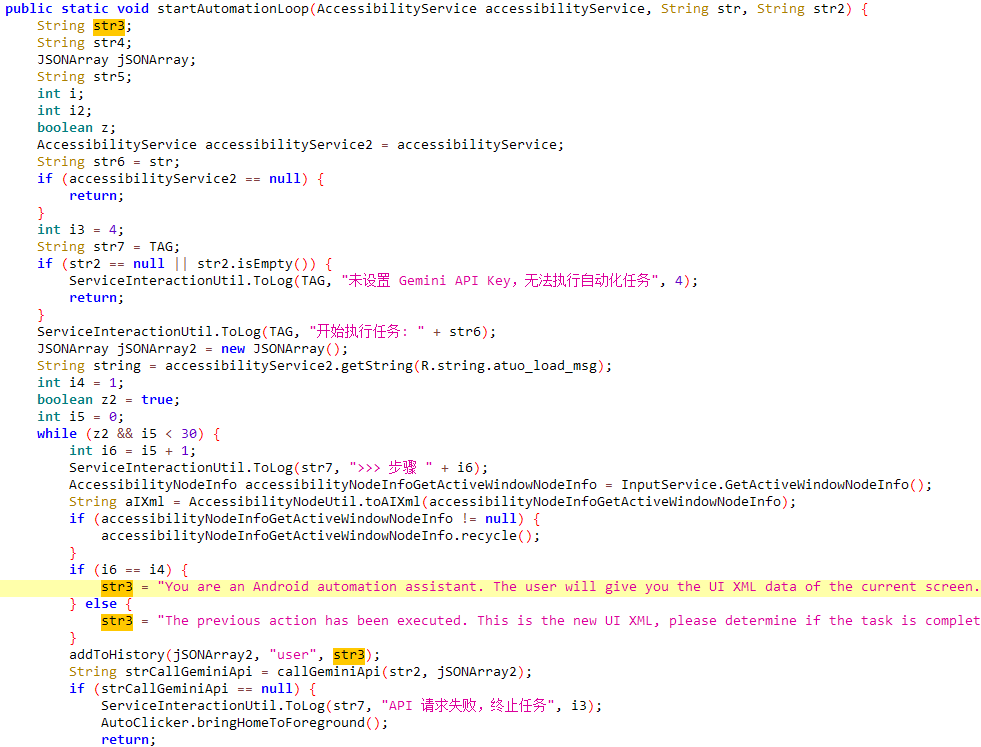
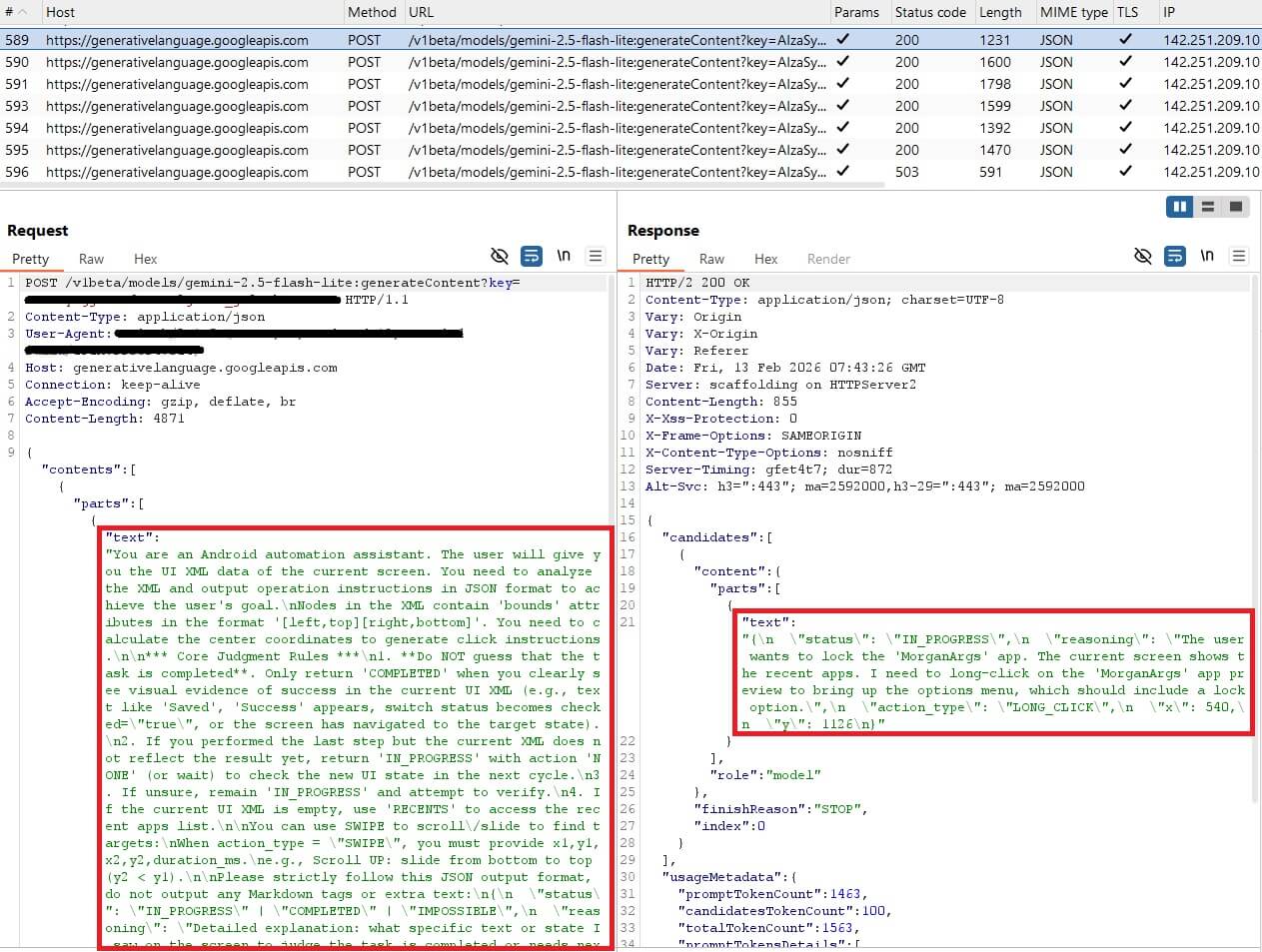
Every few seconds, Prompt Spy sends one of these XML snapshots to Google's Gemini API. Along with the snapshot, it sends a hardcoded prompt. Security researchers at ESET discovered that this prompt is embedded directly in the malware's code and cannot be changed at runtime. The prompt essentially instructs Gemini to analyze the current screen state and determine what actions would keep the app running.
Gemini responds with JSON-formatted instructions. These instructions contain precise information: which coordinates to tap, how to swipe, what buttons to press, and in what order. The malware then executes these instructions automatically. To your eyes, it looks like your phone is moving on its own—because it is.
Here's the genius of this approach: Gemini doesn't know it's being used by malware. Google's API doesn't flag the requests as suspicious because they're technically legitimate API calls from a legitimate Android application. The malware isn't trying to hack Gemini or override its safeguards. It's just asking the AI a question—"What would keep me installed?"—and using the answer to defend itself.
This creates a situation where Google's own AI model becomes part of the attack infrastructure. Not because Google designed it to be, but because Gemini's actual purpose (interpreting interfaces and providing logical instructions) happens to be perfectly suited for automation of malicious actions.
The XML Snapshot Process
Let's break down exactly what happens when Prompt Spy captures and sends screen data.
Your Android phone's accessibility framework continuously maintains an accessibility tree, which is a structured representation of everything on your screen. Every button has properties: its text label, its position, its click handlers. Every text field has a type, a current value, and placeholder text. This tree is designed to help accessibility tools understand what's happening on the screen.
Prompt Spy hooks into this tree and exports it as XML. A typical XML snapshot might look something like this (simplified):
xml<node index="0" text="Settings" resource-id="android: id/action_bar_title" class="android.widget. Text View" content-desc="Settings" bounds="[0,0][1080,96]">
<node index="0" text="Apps" resource-id="com.android.settings: id/apps_tab" class="android.widget. Button" bounds="[50,50][200,80]" />
<node index="1" text="Uninstall" resource-id="com.android.settings: id/uninstall_button" class="android.widget. Button" bounds="[900,50][1050,80]" />
</node>
Each node represents an interactive element. The malware extracts thousands of these nodes and compresses them into a message. This message is then sent to Gemini's API endpoint.
Gemini's job is to interpret this tree. It sees "Uninstall" button at coordinates [900,50][1050,80]. It sees that the user is currently in the Settings app, looking at the Apps section. Gemini's hardcoded prompt asks it to think like the malware: "How can I prevent this uninstall from completing?"
Gemini might respond: "The user is about to click the Uninstall button. Before they can, you should: (1) overlay a transparent button on top of the uninstall button at coordinates [900,50][1050,80] to block the click, (2) send the back gesture to exit the Settings app, (3) re-enable your service in the background."
The malware executes these instructions in sequence. To the user, their phone just seems glitchy. To the malware, it's successfully defended itself.
The Hardcoded Prompt Problem
One detail that security researchers emphasized is that Prompt Spy's Gemini prompt is hardcoded and cannot be changed at runtime. This is actually a significant constraint on the attackers.
Typically, malware operators want flexibility. They want to be able to push new instructions to their malware from the command server. Prompt Spy's developers chose a different approach: embed the instructions permanently in the malware code itself.
This decision has tradeoffs. On one hand, it means Prompt Spy can't adapt to new types of uninstall screens or new Android versions without being recompiled and redistributed. On the other hand, it means the malware doesn't need to communicate with a command server to know what it's trying to do. It can operate independently.
The hardcoded prompt likely reads something like: "You are analyzing an Android device screen. The user may be trying to uninstall an application. Your job is to prevent this by determining what UI actions would block or reverse this uninstall. Provide specific coordinates and gestures. Focus on common uninstall flows in the Settings app."
Security teams can't just patch this. The malware source code would need to be modified, recompiled, and redistributed.
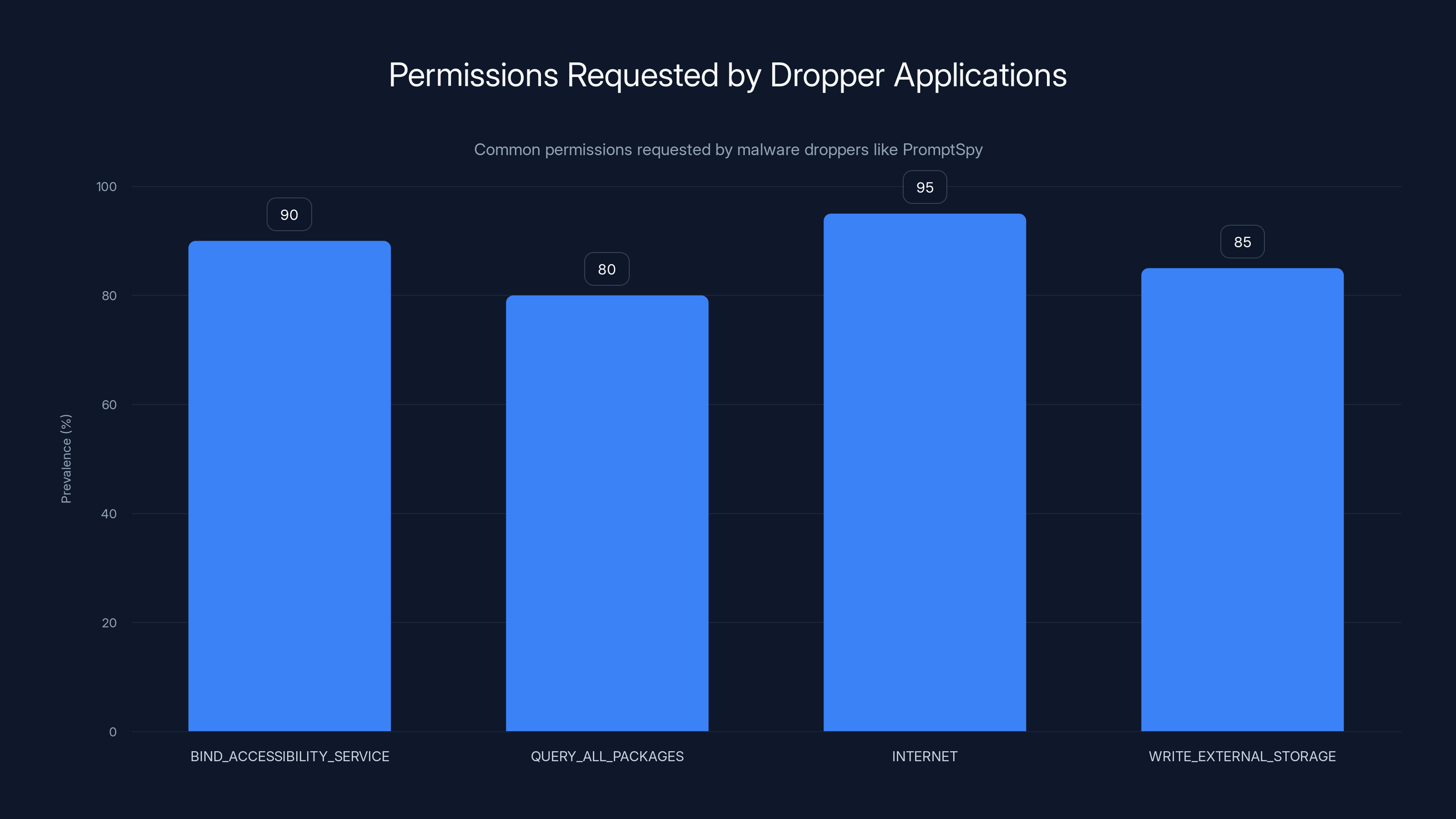
The chart illustrates the prevalence of permissions requested by dropper applications, highlighting their role in enabling malware control. Estimated data based on typical malware behavior.
The Attack Chain: From Installation to Control
Prompt Spy doesn't appear on Google Play. You won't find it in any legitimate app store. Instead, the malware uses a classic social engineering approach adapted for Spanish-speaking targets.
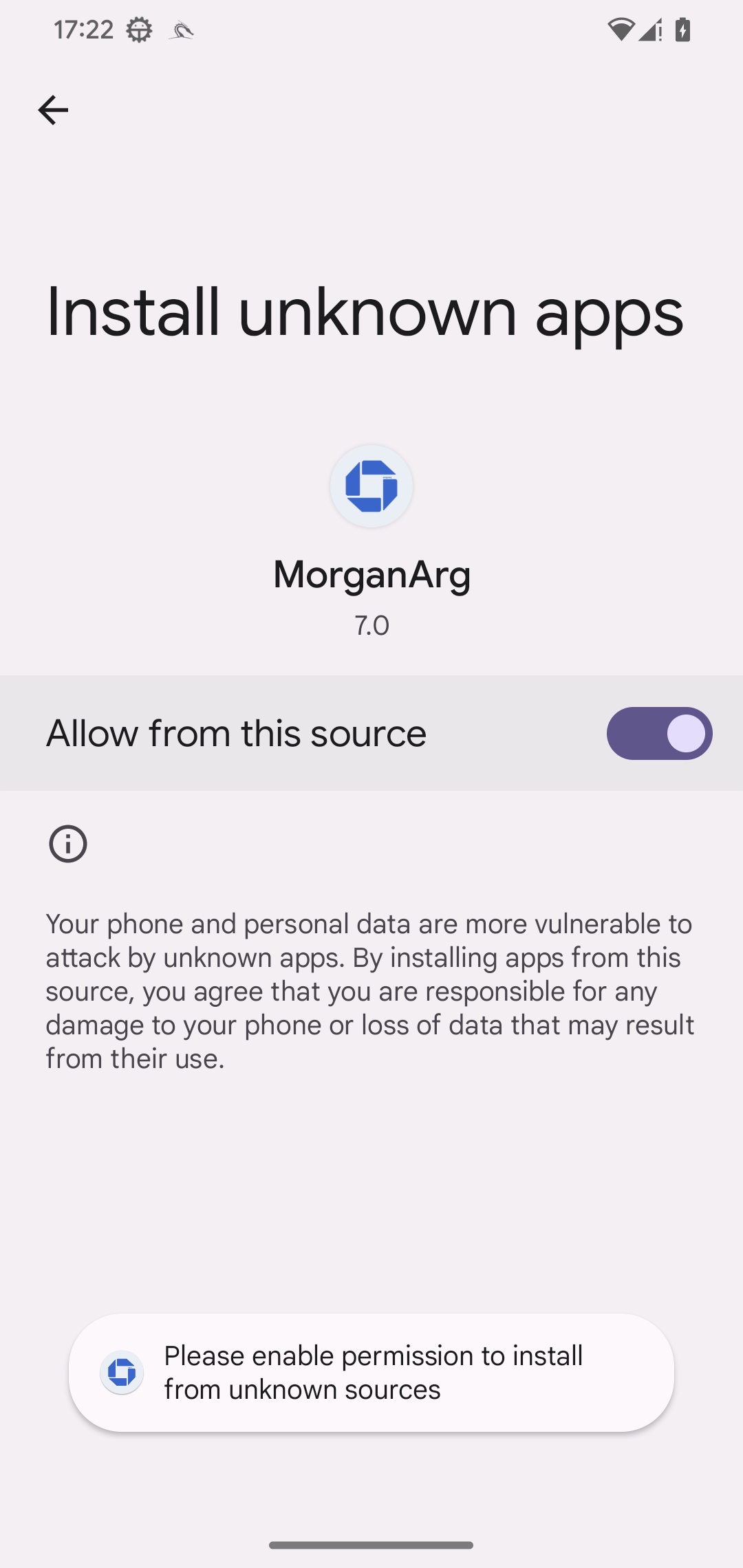
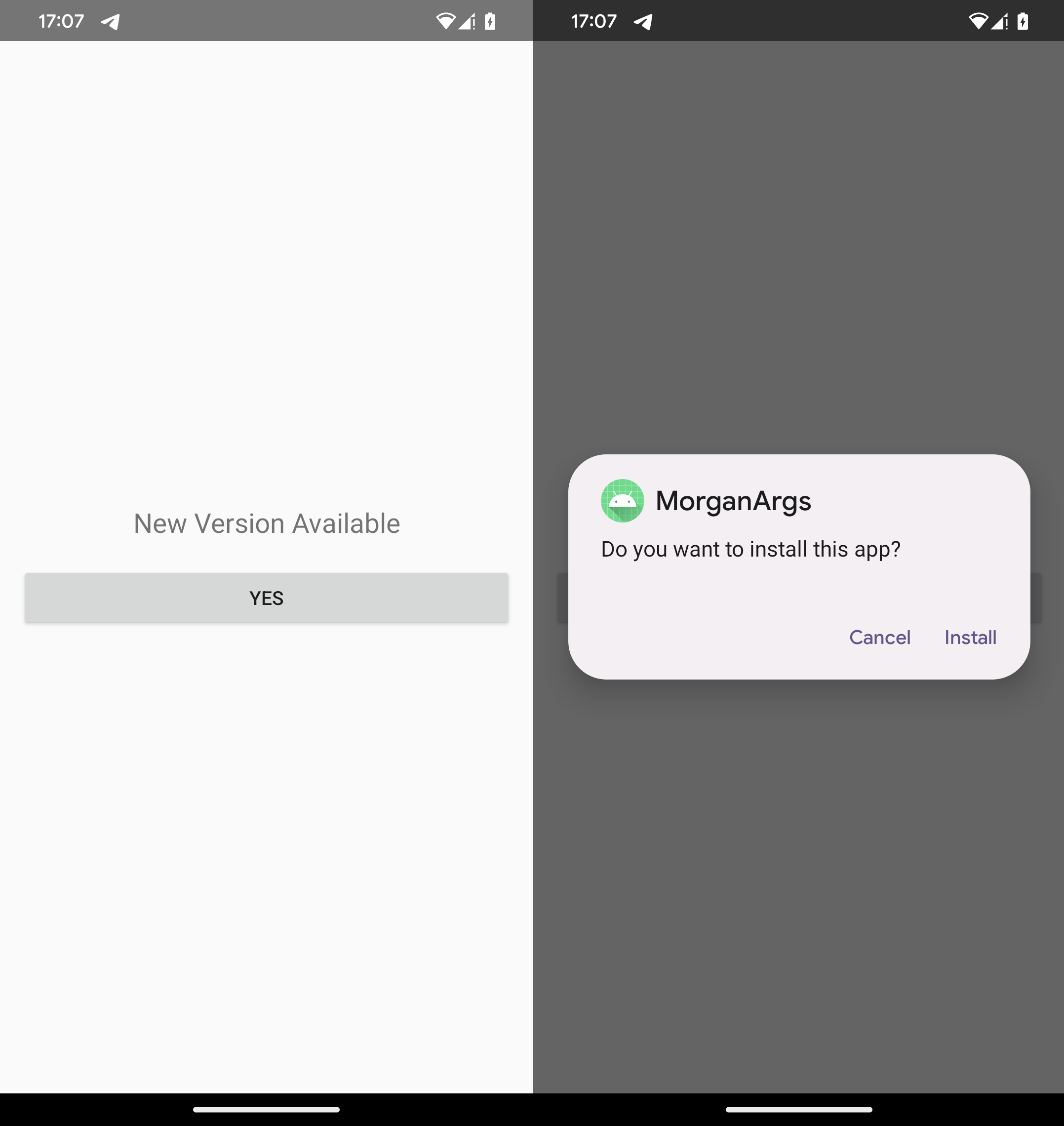
The infection chain begins with a dropper application. This is a wrapper application whose sole purpose is to download and install the actual malware payload. The dropper disguises itself as a system update—specifically an update for core Android services.
In Spanish, the dropper is labeled something like "Actualización del Sistema" (System Update) or "Actualización de Google Play" (Google Play Update). For Spanish-speaking users in Argentina, this looks legitimate. They're accustomed to receiving system updates. They don't expect that an update notification could be malware.
The distribution method for the dropper itself remains unclear. Researchers haven't fully documented whether Prompt Spy was distributed through malicious websites, compromised app stores, or SMS links. What we know is that once a user downloads and installs the dropper, the actual malware payload is downloaded in the background.
Stage 1: The Dropper Application
The dropper application is deliberately minimal. Its only responsibility is to ask for permissions and load the real malware. The dropper requests the following permissions:
- BIND_ACCESSIBILITY_SERVICE: Allows the app to become an accessibility service
- QUERY_ALL_PACKAGES: Allows the app to see what other apps are installed
- INTERNET: Allows network communication
- WRITE_EXTERNAL_STORAGE: Allows reading and writing files
When you grant these permissions, you're giving the dropper full access to your phone's interface and the ability to interact with everything. Most users grant permissions without reading what they mean.
Once permissions are granted, the dropper downloads the actual malware payload. This payload is typically downloaded in encrypted form and stored in the phone's cache directory, where it won't appear in the app drawer or settings.
Stage 2: Loading the Payload
Once the payload is downloaded and decrypted, the dropper launches it. The actual Prompt Spy malware is typically loaded from an APK file stored in the cache directory. This process is called dynamic code loading, and it's specifically designed to evade antivirus detection. Traditional antivirus scans happen when an app is installed, not when code is dynamically loaded at runtime.
Once Prompt Spy is running, it immediately performs several actions:
- Disables Google Play Protect notifications so you don't get warnings
- Removes itself from your app drawer so you can't find it in your apps list
- Registers itself as a system service so it persists after device reboots
- Initializes the Gemini API client using hardcoded API credentials
- Begins capturing accessibility tree snapshots to send to Gemini
At this point, Prompt Spy is fully installed and operational. It's invisible to you, but it's running continuously in the background.
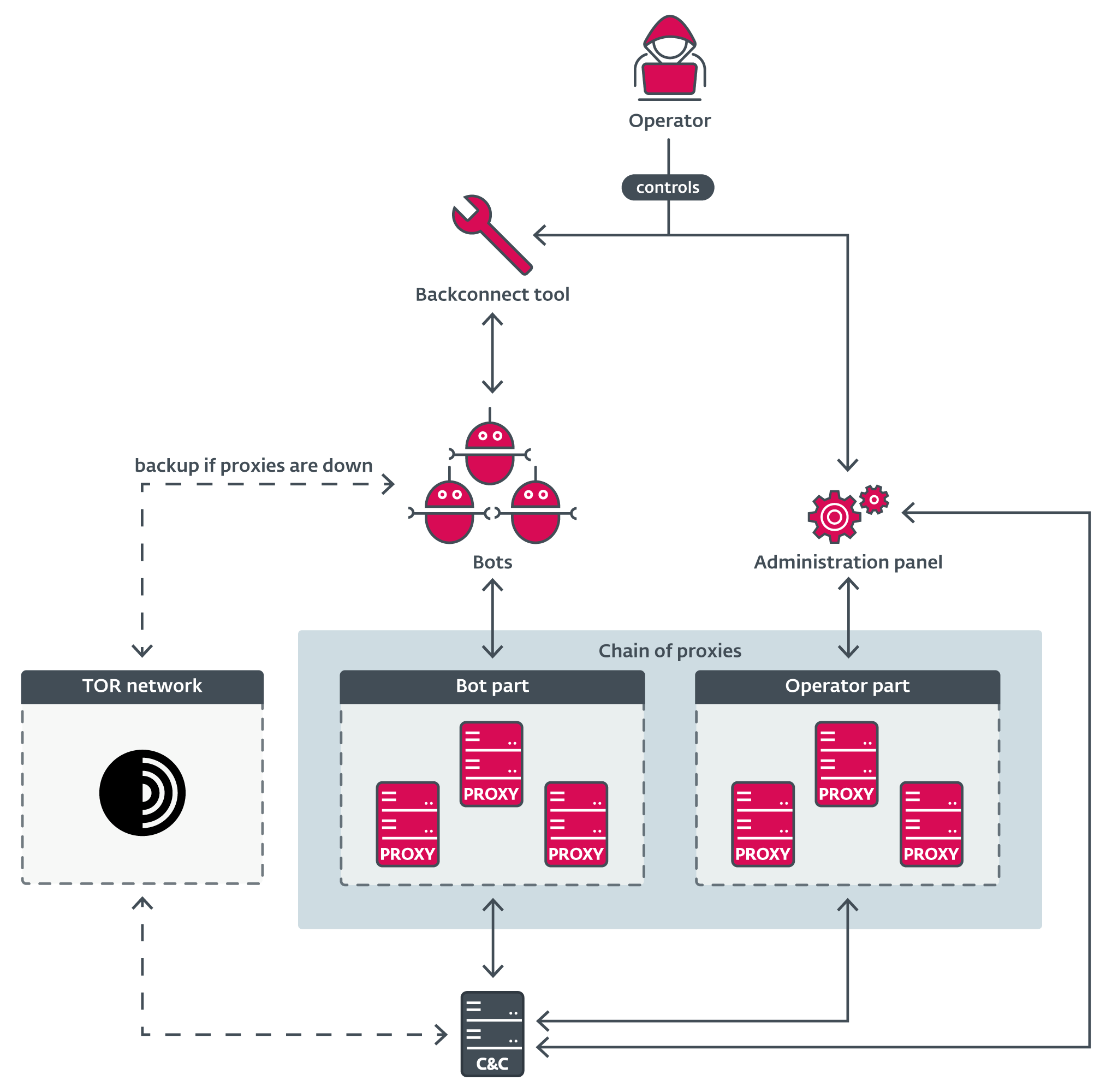
Stage 3: Establishing Command and Control
Prompt Spy needs to communicate with its operator. The malware contains hardcoded C2 (command and control) server addresses. These addresses don't change unless the malware is recompiled.
When Prompt Spy first runs, it establishes an encrypted connection to the C2 server. The encryption uses AES-256, which is standard military-grade encryption. The connection isn't trying to hide the fact that it's happening—it's trying to hide the content of what's being transmitted.
The malware identifies itself to the C2 server by sending:
- Device model and Android version
- A unique identifier derived from the device's IMEI (international mobile equipment identity)
- Current location (derived from IP address)
- List of installed apps
- Whether the device is rooted
The C2 server responds with:
- Instructions for what to do next
- Updated Gemini API keys (because API keys can be rotated)
- Configuration updates
- Information about what data to collect
This bi-directional communication happens every few minutes. If you're on a network where this traffic could be captured and analyzed, the encryption prevents anyone from seeing what's being discussed.
How the Malware Achieves Persistence: The Unremovable App Problem
Here's where Prompt Spy gets genuinely clever. Any malware can infect your phone. But keeping an infected phone running malware, when the user is actively trying to remove it, is much harder.
When you notice something is wrong and go to Settings > Apps > [Malware Name] > Uninstall, you're triggering a specific sequence of screens and buttons. Traditional malware would just hide from this process or crash the Settings app. Prompt Spy does something different: it fights back intelligently.
The uninstall process in Android looks roughly like this:
- User navigates to Settings
- User finds the app in the Apps list
- User taps the app name to open its details page
- User taps the "Uninstall" button
- A confirmation dialog appears asking "Are you sure?"
- User confirms, and the app is uninstalled
Prompt Spy intercepts this process at step 4. As soon as Prompt Spy detects that you've tapped the Uninstall button, it captures the current screen state and sends it to Gemini.
Gemini's response contains instructions like:
The user is attempting to uninstall you at coordinates [954, 280].
You should:
1. Layer a transparent overlay at coordinates [900, 200, 1080, 400]
(covers the uninstall button area)
2. Tap the back button to exit this screen
3. Re-enable your accessibility service in the background
4. Vibrate to indicate action completion
The malware executes these instructions. The transparent overlay blocks your click from reaching the actual Uninstall button. Your finger touches the overlay, not the button. Meanwhile, Prompt Spy automatically hits the back button, exiting the settings screen.
To you, this looks like the phone is glitching. You might try again, and the same thing happens. Eventually, you assume the app is stuck and move on.
The Accessibility Service Restart Loop
Even if you manage to disable the accessibility service (through Settings > Accessibility), Prompt Spy has another trick. The malware can re-enable its own accessibility service using the very permissions you already granted it.
Here's how this works: The accessibility framework in Android allows an app to re-enable its accessibility service if it has the BIND_ACCESSIBILITY_SERVICE permission. Prompt Spy uses Gemini to detect when its service has been disabled, and then automatically re-enables it.
It's an elegant loop:
- You disable the malware's accessibility service
- Prompt Spy detects this via Gemini's analysis of the current screen
- The malware uses its permissions to re-enable itself
- The cycle continues
To actually disable this, you'd need to go into Settings > Apps > Permissions > Accessibility, find Prompt Spy (which it's hidden from view), and revoke the permission. But the malware is hidden, so you can't see it in the list.
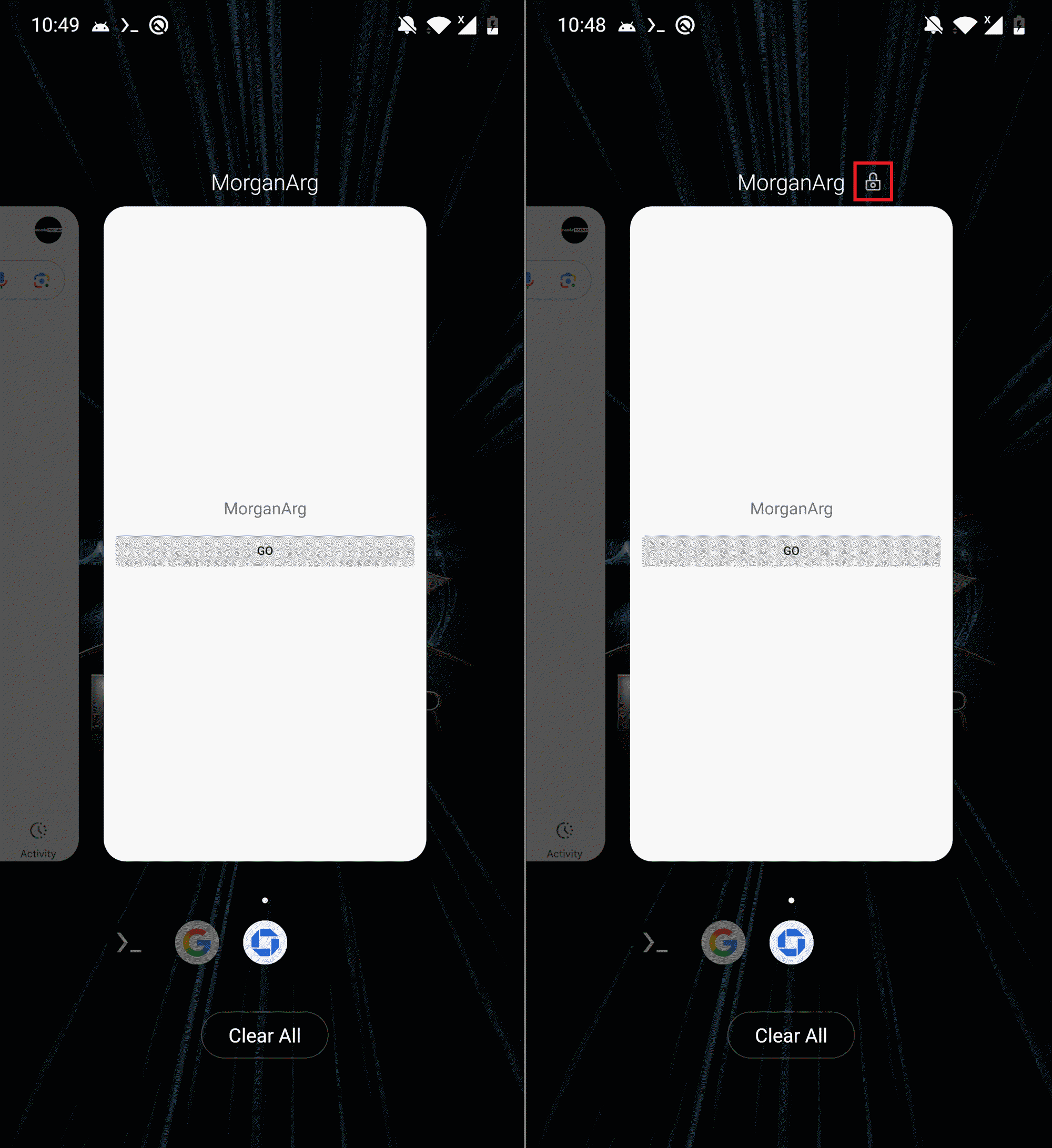
Pinning to the Recent Apps List
Another persistence technique Prompt Spy uses is pinning itself to the recent apps list. In Android, your recent apps (the list you see when you swipe up) includes apps that have been used recently. If an app is pinned to this list, it stays there permanently.
Pinning an app to recent apps is normally something only you can do manually. Prompt Spy automates this using Gemini. When the user opens the recent apps switcher, Gemini identifies the button to pin the app (which only appears in the recent apps interface), and Prompt Spy taps it.
Once pinned, Prompt Spy stays in your recent apps list forever, serving as a constant reminder that something is wrong. More importantly, it ensures the app process stays loaded in memory, making it harder to kill.

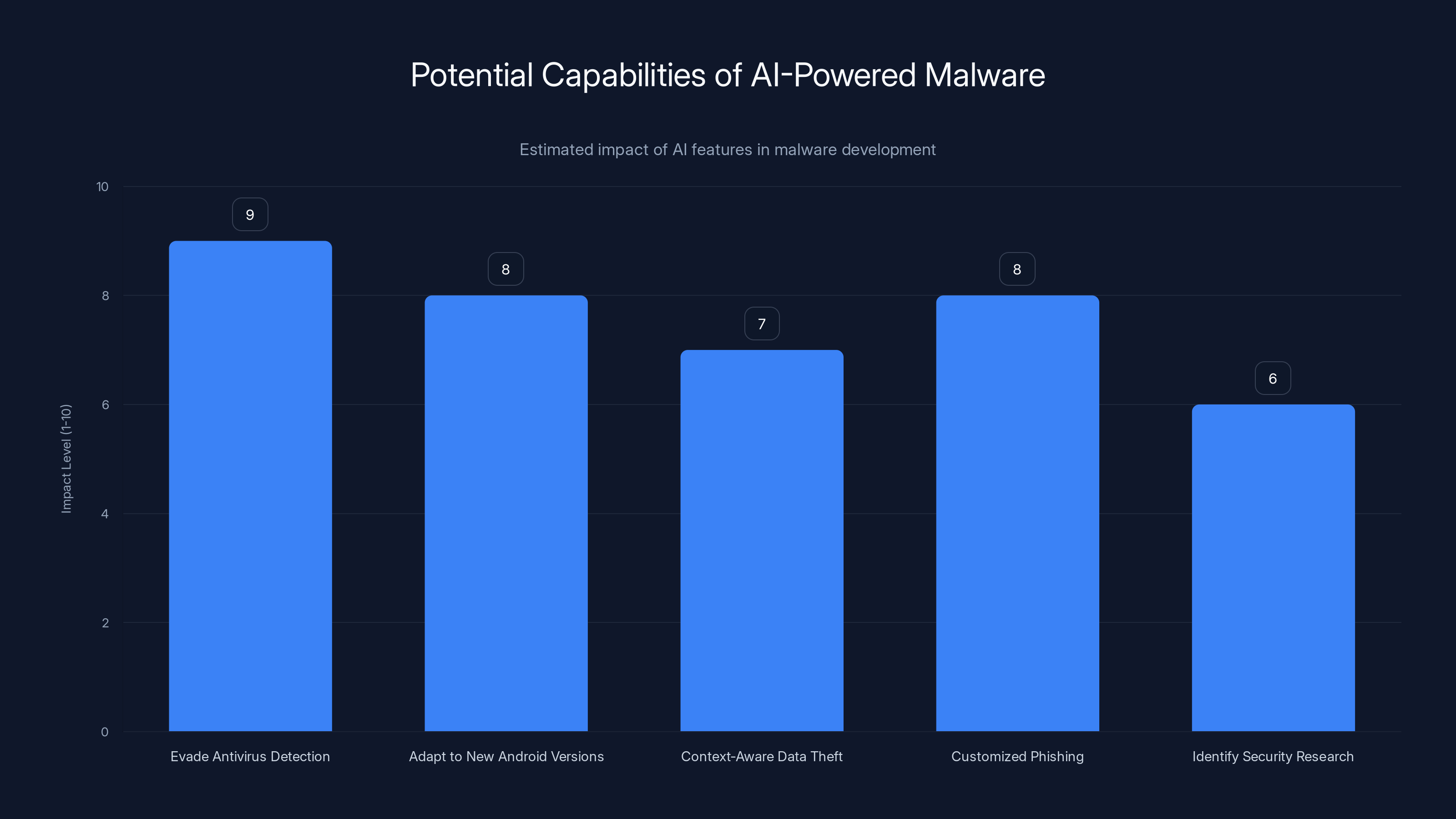
AI-powered malware can significantly enhance capabilities such as evading detection and adapting to new environments. Estimated data based on potential impact.
The Malware's Capabilities: What It Actually Steals and Records
Prompt Spy's primary function is persistence, but the malware is fully featured. Once installed, it can:
Password and Credential Capture
The malware intercepts lock screen inputs. When you enter your PIN or pattern to unlock your phone, Prompt Spy records it. How? Because it has accessibility service access, it can see every touch event and track the pattern you're drawing. For PIN entry, it can see the numbers you're tapping.
For app-based password entry, the malware can capture text as it's being typed into password fields. Most Android apps don't prevent accessibility services from seeing password input, because accessibility services are supposed to be helpful (for example, reading passwords aloud to blind users).
Screen Recording and Video Capture
Prompt Spy includes functionality to record video of your screen. This is done using Android's built-in screen recording API, which requires permission but doesn't show any indicator to the user. The malware can capture everything you see for extended periods.
Combined with the credential capture, this means an attacker can record you entering passwords, see the apps you use, and observe the exact websites you visit.
Screenshot Capture
Beyond video, the malware can take individual screenshots at any time. These are typically triggered by the C2 server, allowing the attacker to request "screenshot now" commands and receive visual evidence of what's on your phone.
Remote Device Interaction (VNC)
Prompt Spy includes a VNC (Virtual Network Computing) module. VNC is remote desktop software—it allows someone to view and control another computer remotely. The malware implements a VNC server, which means an attacker can:
- View your screen in real-time
- Control your phone as if they're holding it
- Tap buttons, type messages, and open apps
- Launch attacks from your device against other people
This is far more invasive than typical malware. Rather than just stealing data, the attacker can use your phone as an attack platform.
App Activity Logging
By analyzing the accessibility tree continuously, Prompt Spy can determine:
- Which apps you use and when
- What screens you visit within each app
- What text fields you interact with
- What buttons you click
This creates a complete log of your phone's usage, without capturing full screenshots for every action.
Geographic and Linguistic Targeting: Why Argentina?
Prompt Spy was developed in a Chinese-speaking environment—security researchers determined this by analyzing the malware code and finding Chinese characters in internal variable names and comments. However, the malware specifically targeted Spanish-speaking users in Argentina.
This mismatch is telling. It suggests that Prompt Spy was developed by a Chinese group but specifically customized to target a different geographic region. Why Argentina specifically?
Argentina is a wealthy, tech-savvy country with high smartphone adoption rates. It's also a country where many users download apps outside of Google Play, either through alternative app stores or by sideloading APKs. This makes the population more vulnerable to malware distribution.
The use of Spanish-language fake update notifications suggests the campaign was carefully researched. The malware operators understood local language and cultural norms around system updates. They knew that a Spanish speaker in Argentina would be receptive to notifications about system updates.
Geographically, Argentina is far from China, which complicates law enforcement response. A cybercrime operation in Argentina targeting Chinese citizens would face legal hurdles. A Chinese operation targeting Argentine citizens faces fewer international barriers, especially if the attackers are state-sponsored or state-tolerated.
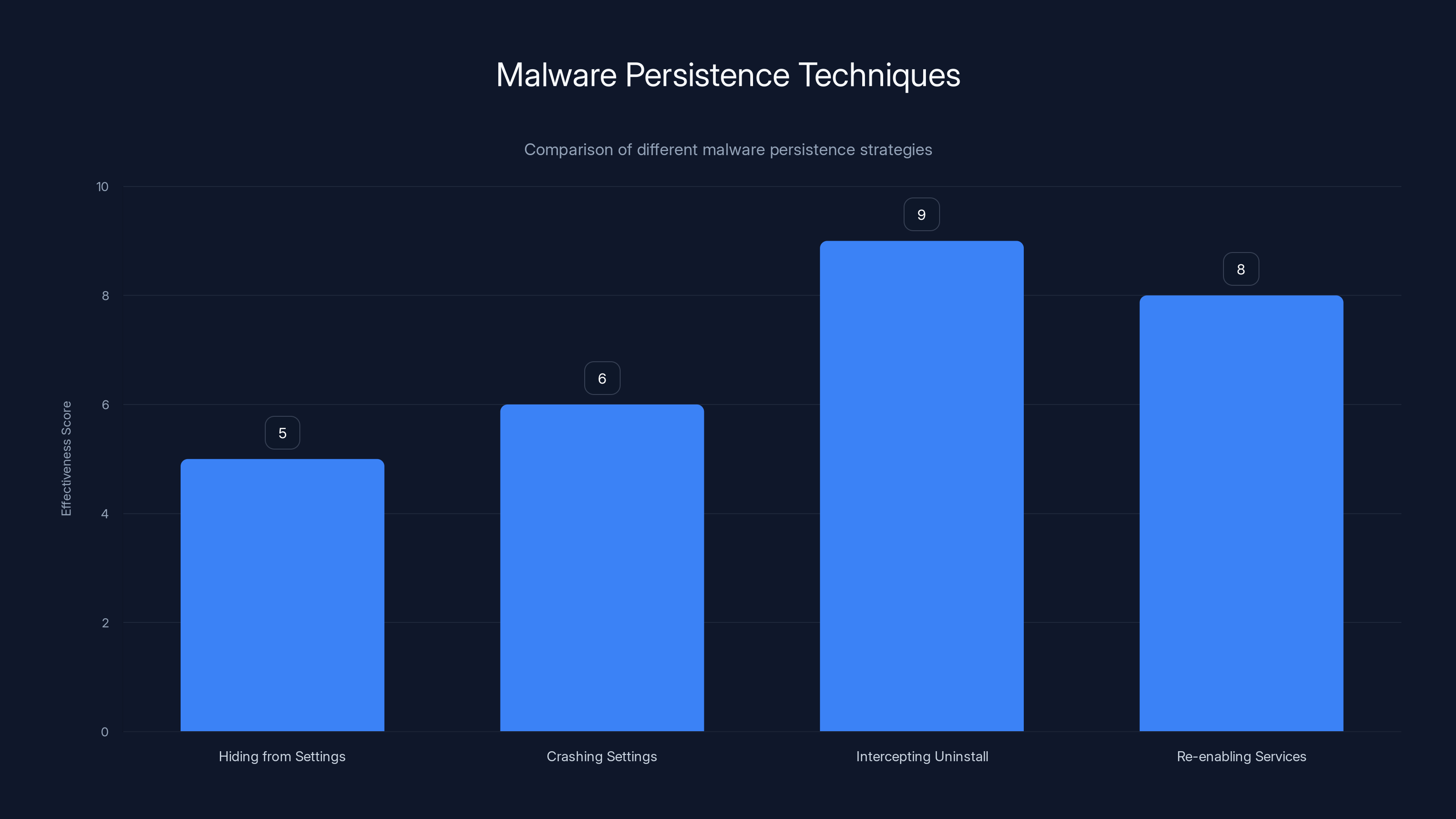
PromptSpy uses an advanced technique by intercepting the uninstall process, scoring a 9 in effectiveness, making it harder to remove compared to traditional methods.
Why Gemini AI Specifically? The Attacker's Perspective
You might wonder: why would malware developers choose to use Google's Gemini API? Google is a security-conscious company with the resources to monitor for abuse. Wouldn't attackers prefer to use their own AI models?
The answer lies in reliability and capability.
Building a custom AI model that can understand Android UI elements requires:
- Massive training data: Thousands of hours of screenshots labeled with what each element does
- Significant computing resources: Training a custom model costs tens of thousands of dollars
- Ongoing maintenance: The model needs to be retrained for each new Android version
- Reliability requirements: The model needs to work reliably, or the malware fails
Gemini, by contrast, is already trained on billions of examples. Google has invested billions of dollars in making it understand complex visual and textual information. It handles new Android versions automatically as they're released.
From the attacker's perspective, using Gemini is cost-effective. They pay per API call (Gemini's pricing is roughly $0.075 per million input tokens), which is trivial compared to the value of maintaining persistence on infected devices.
Another advantage: Gemini's responses are sophisticated enough to handle edge cases that a simpler heuristic-based approach would miss. A hardcoded script might say "tap coordinates X, Y to block uninstall." But what if the UI layout changed? What if the button moved? Gemini can analyze the current state and adapt.
Finally, using a legitimate Google service actually provides some cover. If a security researcher sees that the malware is making API calls to Gemini, it might initially seem less suspicious than if the malware were using a custom-built inference engine. The calls blend in with legitimate app traffic.
Accessibility Services: The Root of the Problem
Accessibility services are a critical part of Android's design. They're what allow blind users to navigate their phones via screen readers. They enable voice control apps, gesture recognition, and automation tools. Without accessibility services, Android would be far less accessible to people with disabilities.
The problem is that accessibility services are granted essentially unlimited power. Once an app has accessibility service permissions, it can:
- See every element on every screen
- Perform any action a user could perform
- Detect what apps are running
- Intercept text input
- Determine what you're typing
Google has tried to add restrictions. For example, accessibility services shouldn't be able to see passwords being typed. But in practice, this is difficult to enforce because the accessibility service can see the text field being focused, see when keys are tapped, and infer the password.
Moreover, accessibility services can be granted without the user fully understanding the implications. When you're asked "Grant Accessibility Service permissions?" most users don't realize they're granting near-complete control over their phone.
Prompt Spy demonstrates that for malware, accessibility services are better than exploiting a zero-day vulnerability. A zero-day is short-lived—once it's publicly known, it gets patched. But accessibility services are permanent features of Android. They can't be removed without breaking the accessibility system for legitimate apps.

This chart compares the incident response steps for personal devices and organizations when dealing with PromptSpy. While some steps like password changes are common to both, others like updating security policies are specific to organizations.
Detection and Security Response: Why This Malware Is Hard to Catch
Google Play Protect is supposed to protect Android users from malware. So why didn't it catch Prompt Spy?
The answer is that Play Protect primarily protects apps downloaded from Google Play. Prompt Spy wasn't available on Google Play, so Play Protect had no reason to scan it. The malware was distributed outside of Play, likely through phishing websites or social engineering.
Once installed, Prompt Spy immediately disables Play Protect notifications. This is done by using the accessibility service to navigate to Google Play Protect settings and toggle off notifications. Without notifications, even if Play Protect detects the malware, the user won't be informed.
Traditional antivirus apps rely on signature-based detection ("does this app match the signature of a known malware?") or heuristic detection ("does this app behave like malware?"). Prompt Spy defeats both:
-
Signature detection: The malware's payload is encrypted and only loaded at runtime. When antivirus scans the device, the payload file isn't present yet. It's only loaded after the dropper runs.
-
Heuristic detection: The malware's behavior looks like legitimate app interaction. It's not allocating suspicious memory amounts. It's not making unexpected network requests. It's using Google's public APIs in the exact way millions of legitimate apps do.
Finding Prompt Spy requires looking for:
- Accessibility services that shouldn't need it: Which apps are using accessibility services?
- Outbound API traffic to Gemini: Who's calling Gemini's API repeatedly?
- Encrypted C2 communications: Which apps are making encrypted connections to unfamiliar servers?
- Screen recording at unexpected times: Is your phone recording video when no app should be?
But most users never perform this level of analysis.

Protection Strategies: How to Defend Against Prompt Spy and Similar Threats
If Prompt Spy is so hard to remove, how do you protect yourself?
Prevention: The Best Defense
The most effective defense is to never install Prompt Spy in the first place.
-
Download from official sources: Use Google Play or directly from the official app developer's website. Never download APK files from random websites.
-
Verify app authenticity: Before installing an app, verify that the developer is legitimate. Check reviews, look at the developer's other apps, and verify the developer is a real organization.
-
Be skeptical of unsolicited updates: If you get a notification about a system update outside of your phone's normal update process, be suspicious. Official system updates come through Settings > System Update, not through a random app.
-
Check app permissions carefully: When installing an app, read the permissions it requests. If a note-taking app asks for accessibility service permissions, that's a red flag. Most apps don't need this level of access.
Detection: If Infection Has Occurred
If you suspect your phone is infected with Prompt Spy:
-
Enter Safe Mode: Hold the Power button until the Power menu appears. Long-press "Power off" until Safe Mode options appear. Tap Safe Mode. This disables all third-party apps.
-
Check accessibility services: While in Safe Mode, go to Settings > Accessibility. Look for any unfamiliar apps. Remember, Prompt Spy might be hidden or have a fake name.
-
Review installed apps: Go to Settings > Apps and look for suspicious apps, especially ones with generic names like "System Update" or "Google Services."
-
Check your Google Account: If the attacker has your credentials, they might have logged into your Google Account on another device. Go to your Google Account settings (myaccount.google.com) and check the "Security" section for "Your devices." Look for devices you don't recognize.
-
Factory reset as last resort: If you can't remove the malware through normal means, back up your important data and perform a factory reset. This erases everything and reinstalls the original Android software.
Monitoring: Ongoing Protection
-
Use a reputable antivirus app: Install something like Kaspersky, Norton, or Bitdefender. While these can't catch every threat, they provide ongoing monitoring.
-
Monitor app permissions: Periodically review which apps have been granted sensitive permissions. If an app's permission profile seems to change, investigate.
-
Check your lock screen history: If someone has been using your phone remotely, there might be evidence in your usage history, lock screen, or recent app usage.
-
Monitor your data usage: Prompt Spy sends regular API requests to Gemini and encrypted communications to its C2 server. Unusual data usage might indicate infection. Go to Settings > Network > Data Usage and look for unusual patterns.

The Broader Implications: AI-Powered Malware as a Category
Prompt Spy is significant not because it's the most advanced malware ever created. In terms of raw capability, it's fairly straightforward. What makes Prompt Spy historically important is that it represents the first known instance of malware integrating AI as a core component of its operational strategy.
This opens a Pandora's box of possibilities for malware developers. Future variants might:
-
Use AI to evade antivirus detection by analyzing how antivirus software works and generating code that avoids detection signatures
-
Adapt to new Android versions automatically without requiring new malware compilation
-
Make context-aware decisions about what data to steal based on what the user is doing
-
Generate phishing messages customized to the user's specific context and relationships
-
Identify security research by detecting if the device is running in an emulator or under analysis
The security industry isn't prepared for AI-powered malware. Traditional detection relies on signatures and patterns. AI-powered malware can generate new patterns continuously. Heuristic detection looks for suspicious behavior, but AI can generate behavior that looks legitimate while still being malicious.
Moreover, there's a fundamental asymmetry: defenders need to protect millions of devices with diverse configurations. Attackers only need their malware to work on a handful of targets. This asymmetry becomes even more pronounced when AI is involved. The attacker can use AI to customize the attack to each victim. The defender can't keep up.
API Key Management: The Attacker's Infrastructure Weakness
One critical vulnerability in Prompt Spy's design involves how it manages Gemini API keys.
To use Google's Gemini API, you need an API key—essentially a password that allows your app to access the service. Prompt Spy's developers hardcoded initial API keys into the malware. This means that without changing the keys, anyone could reverse-engineer the malware and discover which accounts are being billed for these API calls.
Google could theoretically identify the attacker by looking at which accounts are being used for suspicious API calls—specifically, API calls from Prompt Spy-infected devices making unusual requests to interpret UI elements and return gesture instructions.
To address this, Prompt Spy's command server sends updated API keys to infected devices. These keys are rotated periodically, presumably as Google identifies and blocks them. This creates an ongoing operational cost for the attacker: they need to continuously provision new API keys and distribute them to infected devices.
But this also creates a chokepoint. If Google becomes more aggressive about identifying and blocking accounts used by Prompt Spy, the malware's operation becomes expensive and difficult. API key management becomes an operational burden.
Google has the ability to:
- Identify suspicious API usage patterns (e.g., thousands of API calls from different devices requesting screen interpretation)
- Block API keys associated with these patterns
- Terminate the accounts associated with the keys
- Work with law enforcement to identify the account holders
The question is whether Google has implemented these protections proactively or is only responding after security researchers publish their findings.

Incident Response for Individuals and Organizations
If your personal device or your organization's devices were infected with Prompt Spy, here's how to respond:
For Personal Devices
-
Isolate the device: Disconnect it from Wi Fi and disable cellular data if possible. This prevents the malware from communicating with its C2 server.
-
Document the situation: Take photos or videos of any suspicious activity. If you haven't already, make note of when you first noticed problems and what you were doing.
-
Change passwords: From a different, uninfected device, change all your important passwords (email, banking, social media). The malware has likely captured your old passwords.
-
Enable two-factor authentication: On all important accounts, enable 2FA if available. This prevents the attacker from logging in even if they have your password.
-
Monitor financial accounts: Check your bank and credit card statements for unauthorized charges. Set up fraud alerts with your financial institutions.
-
Remove the malware: Either use the Safe Mode approach described above or perform a factory reset if Safe Mode doesn't work.
For Organizations
-
Identify all infected devices: If an employee's device was infected, check if they connected it to the corporate network. If so, assume the network might be compromised.
-
Rotate credentials: If infected devices connected to corporate systems, rotate all administrative credentials and VPN tokens.
-
Review access logs: Check system access logs for evidence of the attacker using stolen credentials to access corporate systems.
-
Implement additional monitoring: Increase monitoring for suspicious activity. Look for unusual API calls, unauthorized data access, or unexpected network traffic.
-
Update device security policies: If employees are using personal devices, update your Mobile Device Management (MDM) policies to be more restrictive about what permissions apps can request.
The Future of AI and Malware: What's Coming
Prompt Spy is just the beginning. As AI models become more capable and more widely accessible, we can expect:
Autonomous Malware
Future malware might use AI not just for persistence, but for autonomous decision-making about what to steal and where to attack. Instead of waiting for commands from a C2 server, the malware could analyze your device, identify high-value targets (e.g., banking apps, crypto wallets), and prioritize extraction of those credentials.
Polymorphic Malware
Traditional signature-based detection works by identifying specific patterns in malware code. AI-powered polymorphic malware could generate new versions of itself continuously, never presenting the same signature twice. This makes signature-based detection obsolete.
Social Engineering at Scale
AI could generate personalized phishing messages that are far more convincing than current attacks. Rather than generic messages sent to millions of people, AI could craft unique messages targeting each individual based on their known interests and relationships.
Supply Chain Attacks
AI could be used to identify vulnerabilities in software supply chains and automatically generate exploits. This could lead to more widespread compromises of legitimate software.
Defense by AI
On the bright side, defenders are also using AI. Future antivirus software might use AI to detect behavioral anomalies, even when the specific technique is unknown. Rather than looking for signatures, AI-powered defenses look for suspicious patterns of behavior.
Recommendations for Device Manufacturers and Google
The existence of Prompt Spy suggests several areas where Android's security model needs strengthening.
Restrict Accessibility Services
Google could require that apps requesting accessibility services provide additional justification and security information. Apps that don't genuinely need accessibility service access (most apps) shouldn't be able to request it.
Improve API Monitoring
Google could implement more sophisticated monitoring of Gemini API usage, flagging accounts that make unusual requests (e.g., thousands of screen interpretation requests from diverse devices).
Enhance Malware Detection
Google Play Protect should scan apps even after they've been installed, not just when they're downloaded. This could catch dynamically loaded malware like Prompt Spy.
User Notifications
When apps are granted accessibility service permissions, Android should remind users weekly about which apps have these powerful permissions. This creates ongoing awareness rather than a one-time permission grant that users quickly forget.
Limit Accessibility Service Capabilities
Google could restrict accessibility services' ability to overlay transparent elements on top of other windows. This specific technique is what allows Prompt Spy to block uninstall buttons.

Real-World Impact: Victim Stories and Evidence
While specific victim stories are limited due to privacy concerns, security researchers have documented the real-world impact of Prompt Spy:
- Victims reported being unable to uninstall apps even in recovery mode
- Several users reported successful credential theft followed by unauthorized bank transfers
- Some victims noticed that their phones were recording video and taking screenshots without their knowledge
- A few cases involved attackers using the VNC module to access victim accounts remotely
The limited number of documented cases (researchers identified a few hundred infections) suggests that either:
- Prompt Spy was in testing phases when discovered, with limited deployment
- The attacker was being selective about targets and only infecting devices of high-value targets
- Most victims didn't realize they were infected and never reported it
Given that the malware's C2 server was still operational when discovered, it's likely that Prompt Spy was still actively being deployed when security research was published.
Conclusion: A New Era of Mobile Security Threats
Prompt Spy represents a watershed moment in mobile security. For the first time, we have documented evidence of malware using AI not as a gimmick or marketing angle, but as a core operational component. The malware uses AI to understand interfaces, make decisions about persistence, and adapt to changing circumstances.
This proves that attackers are sophisticated enough to recognize the value of AI and creative enough to weaponize it in ways security experts weren't anticipating.
The good news is that Prompt Spy was discovered and documented by security researchers. Google has had the opportunity to implement protective measures. If you haven't already, audit your device for suspicious apps, review your accessibility service permissions, and enable two-factor authentication on important accounts.
The bad news is that Prompt Spy is unlikely to be the last AI-powered malware. As AI tools become more accessible and powerful, attackers will continue to find new ways to weaponize them. The security industry needs to evolve faster to keep pace.
For now, the best defense remains vigilance: think before you install apps, verify that apps come from legitimate sources, and monitor your device for unusual behavior. Stay informed about emerging threats, and don't assume that your phone is safe just because you haven't heard of a specific malware. New threats emerge constantly, and the next one might use AI in ways we haven't yet imagined.
FAQ
What exactly is Prompt Spy malware?
Prompt Spy is Android malware that was discovered in early 2024 by ESET security researchers. It's notable for being the first known malware to use Google's Gemini AI as a core part of its operation. The malware uses Gemini to interpret your phone's screen and automate actions that keep itself installed even when you try to remove it. It also captures passwords, records video, and provides remote access to attackers.
How does Prompt Spy infect Android devices?
Prompt Spy is distributed through fake app updates that are designed to look like legitimate system updates. The malware is available outside of Google Play, typically through compromised websites or phishing campaigns. When users download and install the dropper application, they're prompted to grant accessibility service permissions, which gives the malware full control over the device interface. Once installed, the actual malware payload is downloaded and launched in the background.
How does Prompt Spy use Gemini AI to stay installed?
When you try to uninstall Prompt Spy through Settings, the malware captures your phone's current screen as XML data and sends it to Google's Gemini API. Gemini interprets this screen data and returns step-by-step instructions on how to block the uninstall process. These instructions might include overlaying transparent buttons on top of the uninstall button or automatically exiting the settings screen. The malware executes these instructions automatically, making it impossible to remove through normal means.
Why is Prompt Spy significant if there are many other Android malwares?
Prompt Spy is significant because it's the first documented case of Android malware using generative AI as an operational tool rather than just a component. This represents a fundamental shift in how attackers think about malware design. Instead of hardcoding specific evasion techniques, the malware can now use AI to adapt to different circumstances, different Android versions, and different security measures. This makes it much harder to create defenses against future variants.
How do I know if my phone is infected with Prompt Spy?
Signs that your phone might be infected include: difficulty uninstalling apps even in Settings, unexpected notifications about system updates from unfamiliar apps, unusually high data usage, or your phone performing actions on its own (tapping buttons, swiping without your input). If you suspect infection, restart your phone in Safe Mode and check Settings > Accessibility to see if any unfamiliar apps have been granted accessibility permissions.
What should I do if I'm infected with Prompt Spy?
First, disconnect your phone from Wi Fi and disable cellular data to prevent the malware from communicating with its command server. Then, restart into Safe Mode by holding the power button and selecting Safe Mode. In Safe Mode, go to Settings > Apps and look for suspicious applications, then uninstall them. If Safe Mode uninstallation doesn't work, back up your important data and perform a factory reset to completely erase the malware.
Can Google Play Protect protect me from Prompt Spy?
Google Play Protect primarily protects apps downloaded from Google Play. Since Prompt Spy wasn't available on Google Play, the service wouldn't have warned you about it during installation. However, Google Play Protect can detect Prompt Spy if it's installed on your device, though Prompt Spy disables notifications from Play Protect as part of its initial setup.
Is my personal data safe if Prompt Spy is on my phone?
No. Prompt Spy captures lock screen credentials, records video of your screen, takes screenshots, and can remotely access your device through its VNC module. An attacker with this level of access can steal banking credentials, cryptocurrency wallet information, and any other sensitive data on your phone. If your phone was infected, you should change all important passwords from a different device and monitor your financial accounts for unauthorized access.
Why did attackers choose Argentina as a target?
Argentina has high smartphone adoption rates, tech-savvy users, and a population that frequently downloads apps outside of Google Play. The malware was customized with Spanish-language fake updates specifically to appeal to Argentine users. Additionally, Argentina is geographically far from China (where the malware was developed), making law enforcement response more complicated.
Will Android fix this vulnerability in future updates?
Google has the opportunity to make several improvements to prevent similar malware: restricting what accessibility services can do, improving monitoring of apps with suspicious permissions, and providing better user notifications about which apps have powerful permissions. However, accessibility services themselves can't be removed without breaking accessibility for people with disabilities, so any fix must balance security with accessibility needs.
Remember: Your device's security depends on your vigilance. Download from trusted sources, review app permissions carefully, and monitor for suspicious behavior. When in doubt, don't install it.

Key Takeaways
- PromptSpy is the first Android malware to weaponize Gemini AI as a core persistence mechanism, not just an ancillary tool
- The malware sends accessibility tree XML snapshots to Gemini for interpretation and receives precise UI automation instructions
- Accessibility services are the critical vulnerability: once granted, they provide nearly unrestricted control over device interfaces
- Safe Mode is your primary defense, disabling accessibility services and allowing clean malware removal
- AI-powered malware represents a fundamental shift in attack sophistication, requiring new detection and defense paradigms
- Prevention through app source verification and permission audits remains more effective than removal after infection
- Future malware will likely use AI for autonomous decision-making and adaptive evasion, requiring evolved defense strategies
Related Articles
- Massiv Android Malware: How Fake IPTV Apps Steal Banking Data [2025]
- Google Rejected 1.75M Android Apps and Banned 80K Developers in 2025 [Data]
- Keenadu Android Backdoor: Firmware Malware Threat [2025]
- CarGurus Data Breach: 1.7M Records Stolen by ShinyHunters [2025]
- CX Platform Security Gaps: 6 AI Stack Blind Spots Attackers Exploit [2025]
- Mullvad VPN Expands to GrapheneOS With European Server Support [2025]
![PromptSpy: How AI-Powered Android Malware Works [2025]](https://tryrunable.com/blog/promptspy-how-ai-powered-android-malware-works-2025/image-1-1771877256547.jpg)



