Unveiling iOS Vulnerabilities: Federal Scrutiny and the Path Forward [2025]
In recent years, the landscape of mobile operating systems has been fraught with challenges, particularly when it comes to security vulnerabilities. iOS, known for its robust security architecture, has nonetheless faced its share of exploits. This article delves into the circumstances under which federal agencies took notice of specific iOS vulnerabilities, the implications of these exploits, and the path forward in securing mobile platforms.
TL; DR
- Federal Action: U.S. agencies are mandated to patch critical iOS vulnerabilities exploited over a 10-month period, as highlighted by the Cybersecurity and Infrastructure Security Agency (CISA).
- Exploit Kit: A sophisticated hacking kit named Coruna was utilized in these campaigns.
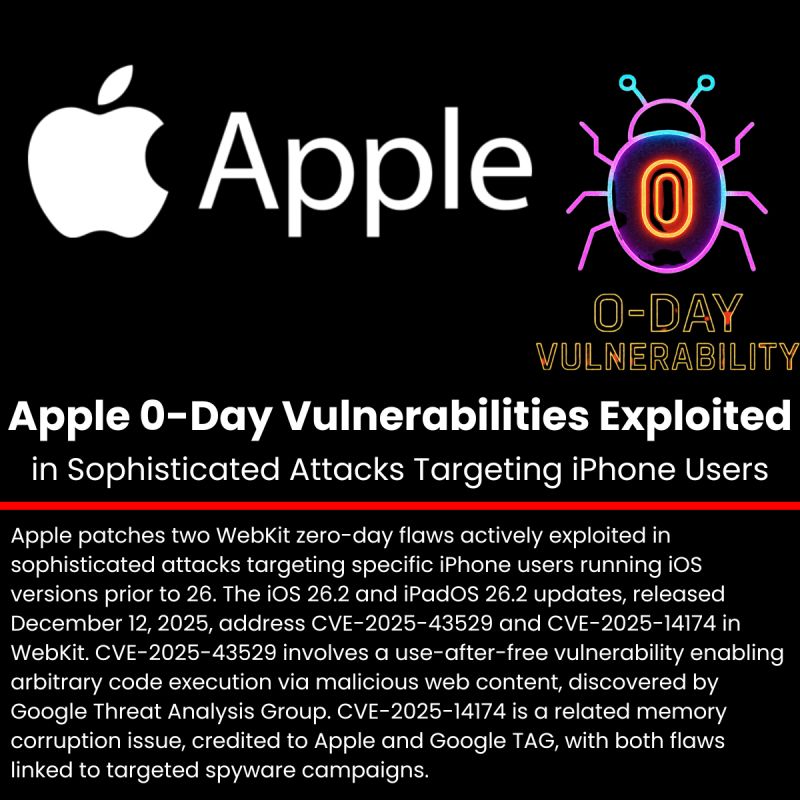
- Zero-Day Vulnerabilities: Some vulnerabilities were previously unknown and exploited before patches were available, as reported by SecurityWeek.
- Security Best Practices: Recommendations for both developers and users to enhance iOS security.
- Future Trends: Emerging security technologies and practices to watch.

AI-powered threat detection is projected to have the highest impact on iOS security, followed by enhanced privacy features and biometric security. Estimated data based on current trends.
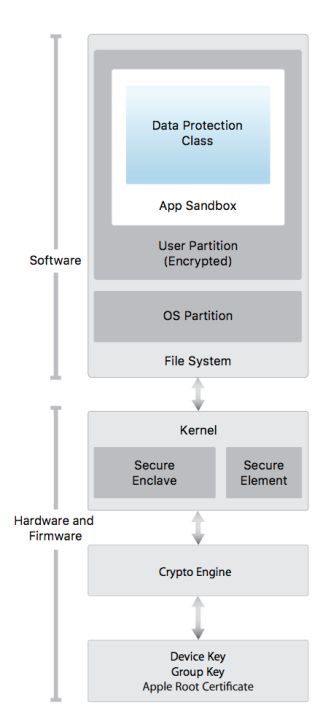
Understanding iOS Security Architecture
To appreciate the significance of these exploits, it's essential to understand the foundational security architecture of iOS. Apple has designed iOS with multiple layers of security to protect both the operating system and the user's data. These layers include:
- Sandboxing: Each app operates in its own space, limiting access to system resources and other apps.
- Code Signing: Ensures that only trusted code can run on the device.
- Data Protection: Encrypts data using keys tied to the user's passcode.
- Secure Boot Chain: Verifies the integrity of the operating system during boot.
Despite these measures, vulnerabilities can and do arise, often in the form of zero-day exploits—security flaws that are unknown to the software vendor and for which no patch exists, as noted by The Hacker News.
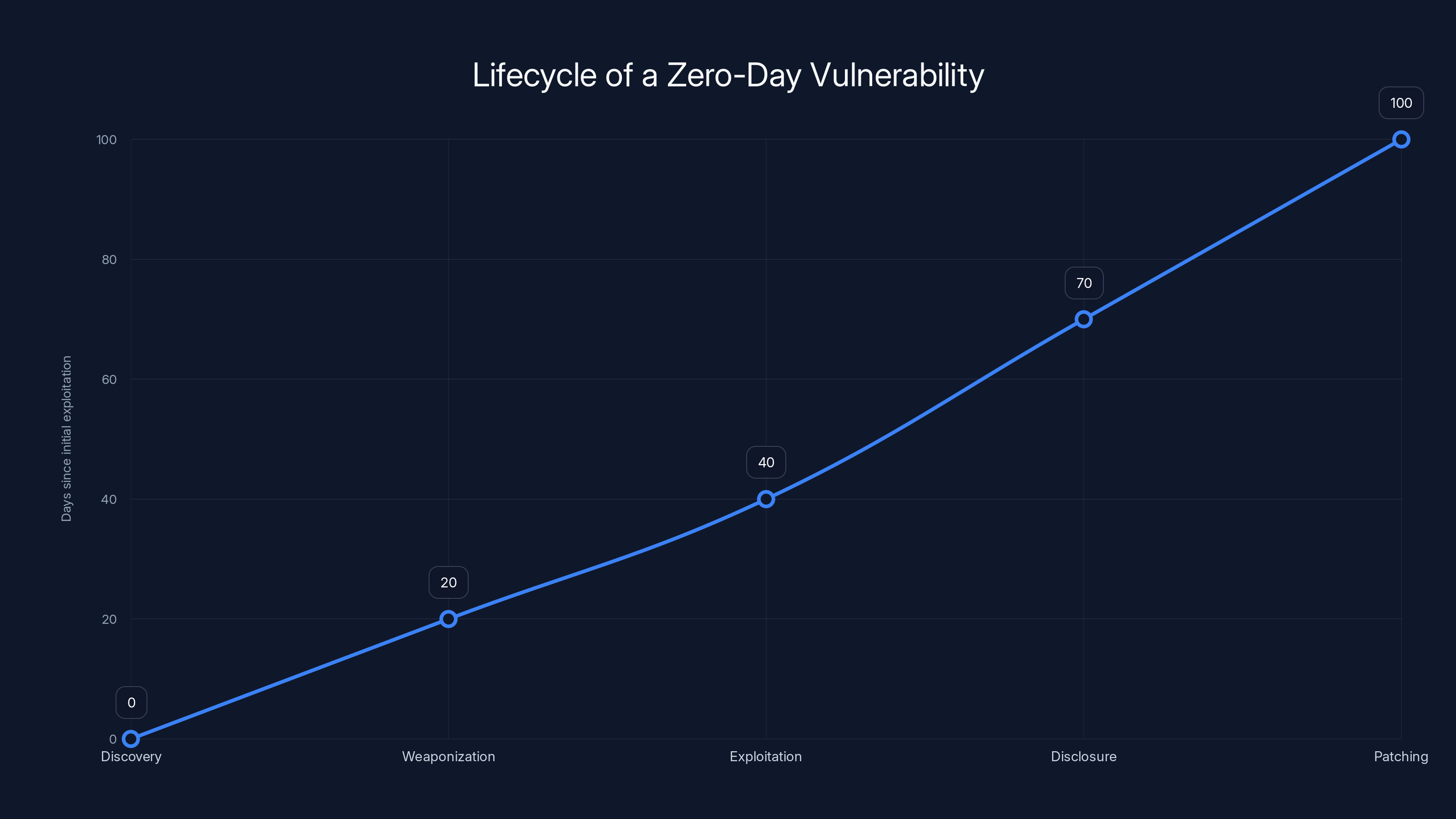
The lifecycle of a zero-day vulnerability typically spans 100 days from discovery to patching, with exploitation occurring early in the timeline. Estimated data based on industry insights.
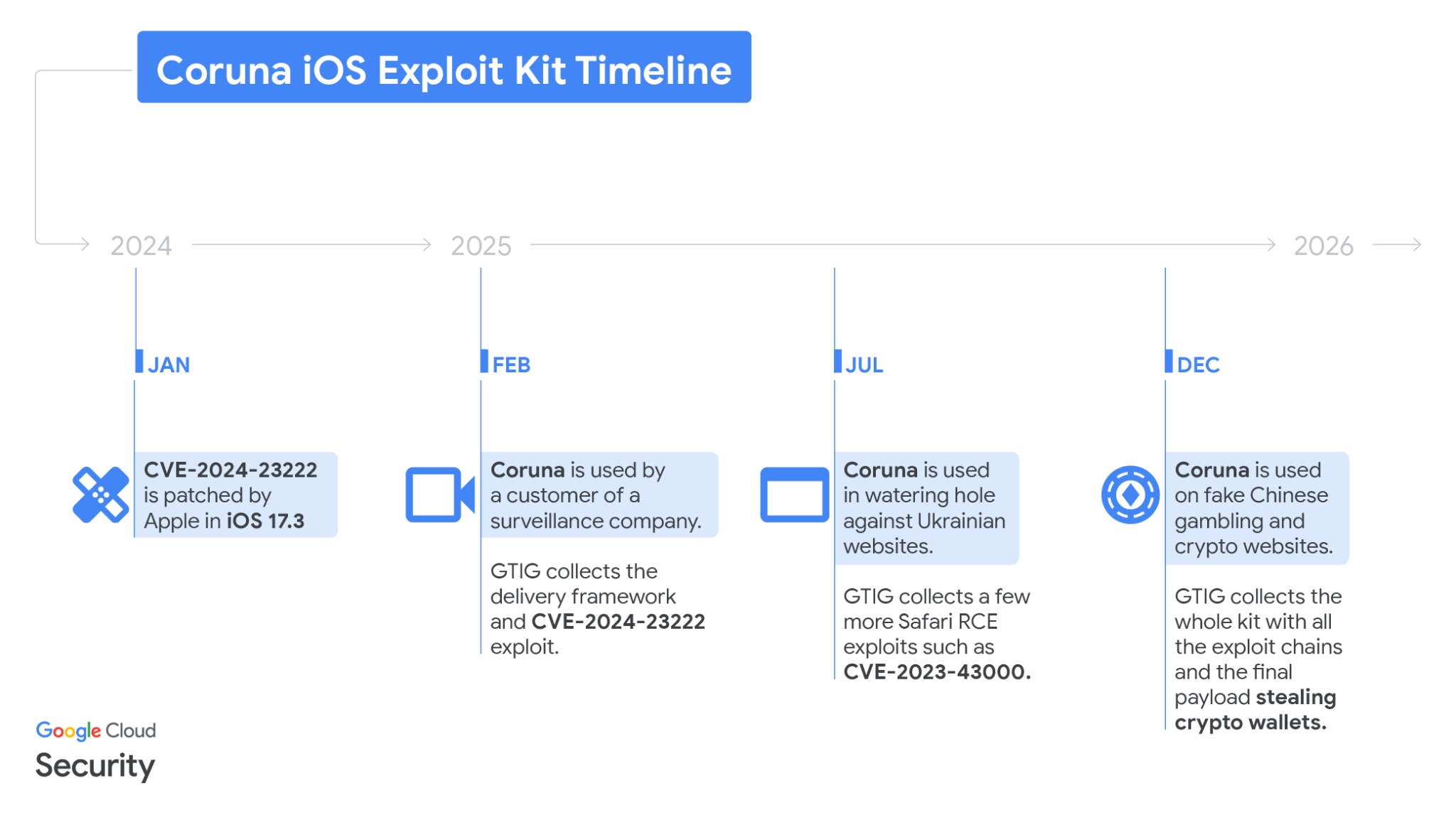
The Rise of Coruna: A Sophisticated Exploit Kit
The exploits in question were part of a toolkit named Coruna, which assembled 23 different iOS exploits into five highly effective exploit chains. These chains were designed to target various components of iOS, including Safari, the kernel, and system daemons. What makes Coruna particularly noteworthy is its ability to exploit both known and previously unknown vulnerabilities.
Key Components of Coruna
- Safari Exploits: Utilized vulnerabilities in the web browser to execute malicious code.
- Kernel Vulnerabilities: Targeted the core of iOS to gain elevated privileges.
- Persistence Mechanisms: Allowed the exploit to survive device reboots, maintaining control over the device.
- Data Exfiltration: Focused on extracting sensitive user data, including messages and location information.
Federal Response and Mandates
The Cybersecurity and Infrastructure Security Agency (CISA) responded to these threats by issuing a directive for federal agencies to patch the affected iOS vulnerabilities immediately. This response underscores the critical nature of these exploits and the potential impact on national security.
Key Actions Taken
- Mandatory Patching: Agencies were required to update all devices to the latest iOS version.
- Risk Assessment: Conducted thorough analyses of potential threats posed by the vulnerabilities.
- Continuous Monitoring: Implemented enhanced monitoring of iOS devices to detect any signs of exploitation.
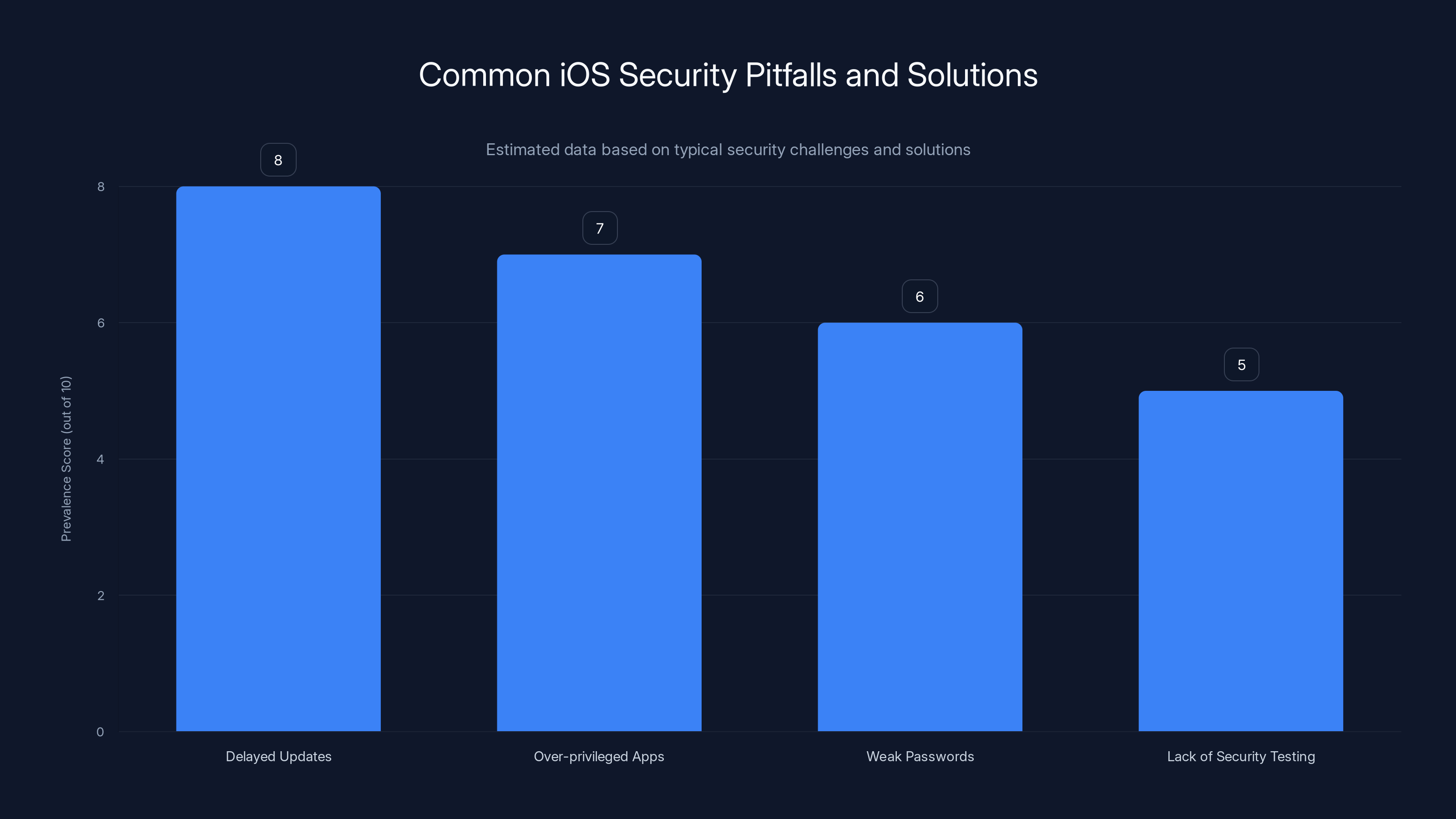
Delayed updates and over-privileged apps are the most common iOS security pitfalls, with scores of 8 and 7 respectively. Estimated data.
Practical Security Practices for iOS Users
For both individual users and organizations, maintaining a secure iOS environment requires vigilance and adherence to best practices.
Best Practices for Users
- Regular Updates: Always update to the latest iOS version to benefit from security patches, as advised by Forbes.
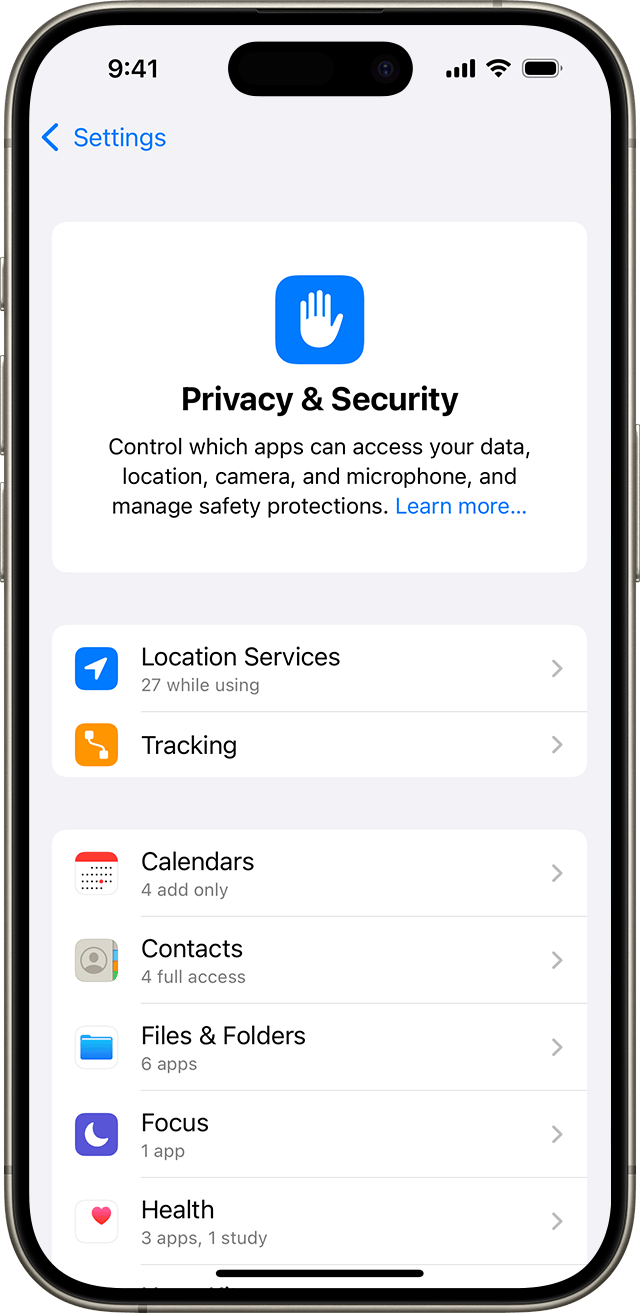
- App Permissions: Review and limit app permissions to the minimum necessary.
- Two-Factor Authentication: Enable 2FA for Apple ID to add an extra layer of security.
- Secure Backups: Regularly back up your device using encrypted backups.
Best Practices for Developers
- Secure Coding: Follow secure coding guidelines to prevent vulnerabilities in apps.
- Regular Testing: Conduct regular security testing, including penetration testing, on apps.
- User Data Protection: Implement strong encryption and data protection measures.
- Security Updates: Release timely updates to address any identified vulnerabilities.
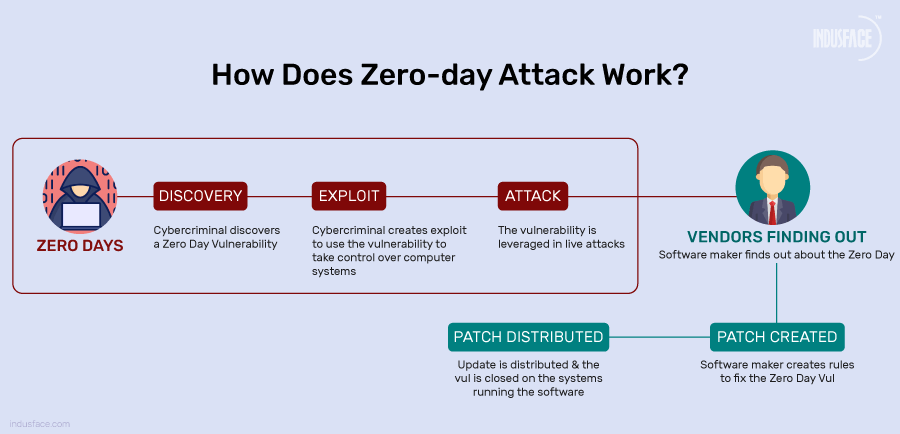
The Role of Zero-Day Vulnerabilities
Zero-day vulnerabilities are particularly dangerous because they are exploited before the vendor is aware of them. In the case of iOS, certain zero-days were used as part of the Coruna kit.
How Zero-Day Exploits Work
- Discovery: A hacker discovers a vulnerability that hasn't been reported to the vendor.
- Weaponization: The vulnerability is developed into an exploit that can be used to attack systems.
- Exploitation: The exploit is used to compromise systems, often stealthily.
- Disclosure: Eventually, the vulnerability may be reported to the vendor, leading to a patch.
Protecting Against Zero-Days
- Behavioral Analysis: Use security software that can detect unusual behavior indicative of an exploit.
- Threat Intelligence: Stay informed about the latest threats and vulnerabilities, as emphasized by IBM's X-Force Threat Index.
- Network Segmentation: Limit the spread of an exploit by segmenting networks.
Common Pitfalls and Solutions
Even with strong security measures, there are common pitfalls that can leave iOS devices vulnerable.
Pitfall 1: Delayed Updates
Many users delay installing updates, leaving devices vulnerable to known exploits.
Solution: Enable automatic updates to ensure devices stay up-to-date.
Pitfall 2: Over-Privileged Apps
Apps that request excessive permissions can compromise privacy and security.
Solution: Regularly review app permissions and revoke unnecessary ones.
Pitfall 3: Weak Passwords
Weak passwords are easily compromised, granting unauthorized access.
Solution: Use strong, unique passwords and a password manager to manage them.
Future Trends in iOS Security
As technology evolves, so too do the strategies for securing mobile platforms. Here are some trends to watch in iOS security.
Trend 1: AI-Powered Threat Detection
Artificial intelligence is increasingly being used to identify and mitigate threats in real-time, as discussed in Google's threat intelligence blog.
Trend 2: Enhanced Privacy Features
Apple continues to introduce new privacy features, such as App Tracking Transparency, to give users greater control over their data, as noted by Apple's newsroom.
Trend 3: Biometric Security
Biometric authentication methods, like Face ID and Touch ID, are becoming more sophisticated and secure, as highlighted by Local 3 News.

The Path Forward: Recommendations
Securing iOS devices is a shared responsibility between users, developers, and Apple. Here are some recommendations to enhance security.
For Users
- Stay Informed: Keep abreast of the latest security news and updates.
- Educate Yourself: Understand the security features of your device and how to use them effectively.
For Developers
- Adopt Security-First Mindset: Make security an integral part of the development process.
- Collaborate with Security Experts: Work with security researchers to identify and fix vulnerabilities.
For Apple
- Proactive Patching: Continue to prioritize timely security updates.
- Bug Bounty Programs: Encourage security research through incentive programs.

Conclusion
The recent exploits targeting iOS highlight the ever-present need for vigilance in mobile security. By understanding the threats and implementing best practices, users and developers can protect their devices and data from malicious actors. As the landscape evolves, staying informed and proactive will be key to maintaining the security of our digital lives.

FAQ
What is a zero-day vulnerability?
A zero-day vulnerability is a security flaw that is unknown to the vendor and has no available patch at the time of discovery, making it highly valuable to attackers.
How can I protect my iOS device from exploits?
Keep your device updated, use strong passwords, enable two-factor authentication, and be cautious of app permissions.
What role does the federal government play in iOS security?
Federal agencies, through CISA, issue directives to ensure government devices are patched against known vulnerabilities to protect national security.
Why are zero-day vulnerabilities so dangerous?
They are exploited before the vendor is aware of them, leaving systems vulnerable. They often fetch high prices on the black market due to their potential impact.
How does Apple address security vulnerabilities?
Through regular software updates, security patches, and features like App Tracking Transparency and biometric authentication.
What are the future trends in iOS security?
Emerging trends include AI-powered threat detection, enhanced privacy features, and more sophisticated biometric security measures.
How can developers ensure their apps are secure?
By following secure coding practices, conducting regular security testing, and promptly addressing any identified vulnerabilities.
What are some common pitfalls in iOS security?
Common pitfalls include delayed updates, over-privileged apps, and weak passwords. Solutions involve enabling automatic updates, reviewing app permissions, and using strong passwords.

Key Takeaways
- Federal agencies must patch critical iOS vulnerabilities to mitigate threats.
- The Coruna exploit kit showcases the complexity of modern hacking tools.
- Zero-day vulnerabilities pose significant risks due to their unknown nature.
- Implementing best practices is crucial for maintaining iOS security.
- AI and biometric technologies are shaping the future of mobile security.
- Continuous updates and user education are key to protecting devices.
Related Articles
- Understanding the March 2026 Android Security Update: Key Vulnerabilities and Protecting Your Device [2026]
- Inside the FBI's Cybersecurity Breach: Unraveling the Hijacking of Wiretaps and Search Warrants [2025]
- Google's 2025 Report on Zero-Day Vulnerabilities: The AI Impact [2025]
- Understanding Phishing Campaigns: How Fake Email Chains Exploit Urgency [2025]
- Understanding the IPVanish VPN Flaw: What It Means for Mac Users [2025]
- The Rise and Fall of Tycoon 2FA: Lessons from a Global Phishing Takedown [2025]
![Unveiling iOS Vulnerabilities: Federal Scrutiny and the Path Forward [2025]](https://tryrunable.com/blog/unveiling-ios-vulnerabilities-federal-scrutiny-and-the-path-/image-1-1772827627604.jpg)



